Submitted:
10 November 2025
Posted:
11 November 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Literature Review
3. Methodology
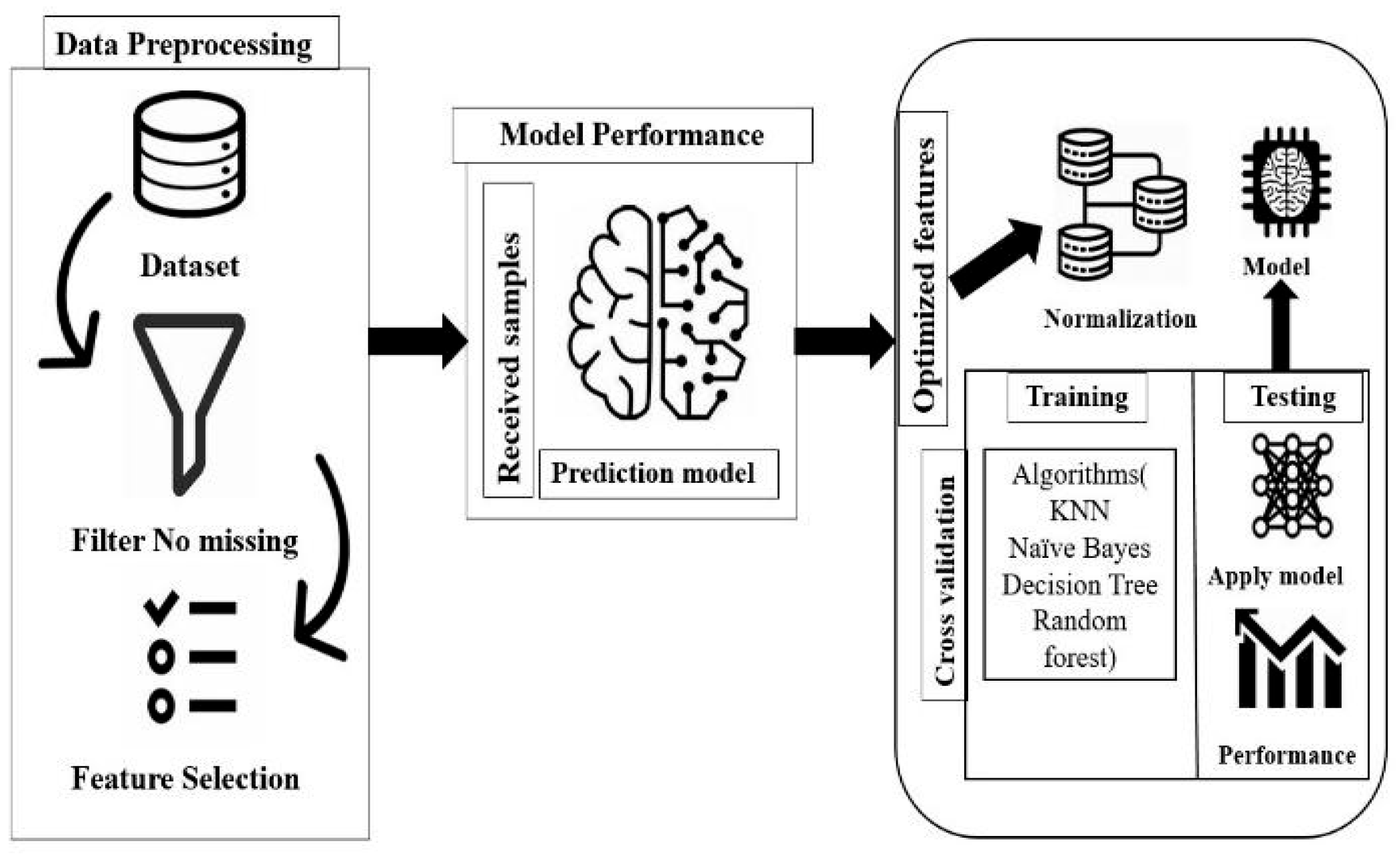
3.1. Data Preprocessing
3.2. Feature Selection
3.3. Normalization
3.4. Cross-Validation
3.5. Algorithms
4. Results
4.1. Performance Evaluation
4.2. Model Training
5. Conclusion
References
- H. Sarker, Y. B. Abushark, F. Alsolami, and A. I. Khan, “IntruDTree: A machine learning-based cybersecurity intrusion detection model,” Symmetry, vol. 12, no. 5, May 2020. [CrossRef]
- N. Aboueata, S. Alrasbi, A. Erbad, A. Kassler, and D. Bhamare, “Supervised machine learning techniques for efficient network intrusion detection,” in Proc. Int. Conf. on Computer Communications and Networks (ICCCN), IEEE, Jul. 2019. [CrossRef]
- M. T. Abdelaziz et al., “Enhancing network threat detection with Random Forest-based NIDS and permutation feature importance,” J. Network and Systems Management, vol. 33, no. 1, Mar. 2025. [CrossRef]
- [Author Unknown], “Optimized intrusion detection model for identifying known and innovative cyber attacks using support vector machine (SVM) algorithms,” Introduction, 2024.
- K. Shaukat, S. Luo, V. Varadharajan, I. A. Hameed, and M. Xu, “A survey on machine learning techniques for cybersecurity in the last decade,” IEEE Access, vol. 8, pp. 222310–222354, 2020. [CrossRef]
- A.Atadoga, E. O. Sodiya, U. J. Umoga, and O. O. Amoo, “A comprehensive review of machine learning’s role in enhancing network security and threat detection,” World J. Adv. Res. Rev., vol. 21, no. 2, pp. 877–886, Feb. 2024. [CrossRef]
- A. Khanza, F. D. Yulian, N. Khairunnisa, and N. A. Yusuf, “Evaluating the effectiveness of machine learning in cyber threat detection,” J. Comput. Sci. Technol. Appl. (CORISINTA), vol. 1, no. 2, pp. 172–179, 2024. Available: https://journal.corisinta.org/index.
- F. Alrowais, S. Althahabi, S. S. Alotaibi, A. Mohamed, M. A. Hamza, and R. Marzouk, “Automated machine learning-enabled cybersecurity threat detection in Internet of Things environments,” Comput. Syst. Sci. Eng., vol. 45, no. 1, pp. 687–700, 2023. [CrossRef]
- H. M. Farooq and N. M. Otaibi, “Optimal machine learning algorithms for cyber threat detection,” in Proc. UKSim-AMSS 20th Int. Conf. on Modelling and Simulation, IEEE, Dec. 2018, pp. 32–37. [CrossRef]
- T. R. Bammidi, “Enhanced cybersecurity: AI models for instant threat detection,” unpublished.
- N. Al-Taleb and N. A. Saqib, “Towards a hybrid machine learning model for intelligent cyber threat identification in smart city environments,” Appl. Sci., vol. 12, no. 4, Feb. 2022. [CrossRef]
- E. Kocyigit, M. Korkmaz, O. K. Sahingoz, and B. Diri, “Real-time content-based cyber threat detection with machine learning,” in Proc. 2021, pp. 1394–1403. [CrossRef]
- F. Bouchama and M. Kamal, “Cyber threat detection through machine learning-based behavioral modeling of network traffic patterns,” 2021.
- S. S. Balantrapu, “Exploring machine learning techniques for cyber threat detection,” Int. J. Sustain. Dev. Through AI, ML and IoT, [Online]. Available: https://ijsdai.com/index.php/IJSDAI/index.
- M. R. Labu and M. F. Ahammed, “Next-generation cyber threat detection and mitigation strategies: A focus on artificial intelligence and machine learning,” 2024. [CrossRef]
- D. Mahendiran, “Cyber threat detection using AI,” Int. J. Multidiscip. Res. Explorer (IJMRE), vol. 4, 2024. [CrossRef]
- C. Ravikumar et al., “Exploring machine learning algorithms for robust cyber threat detection and classification: A comprehensive evaluation,” in Proc. Int. Conf. on Intelligent Systems for Cybersecurity (ISCS), IEEE, 2024. [CrossRef]
- Wayne, “AI and machine learning in cyber threat detection,” Corrosion Management, [Online]. Available: https://corrosion-management.com/.
- Almulhim, M. , Islam, N., & Zaman, N. (2019). A lightweight and secure authentication scheme for IoT based e-health applications. International Journal of Computer Science and Network Security, 19(1), 107-120.
- Zaman, N. , Low, T. J., & Alghamdi, T. (2014, February). Energy efficient routing protocol for wireless sensor network. In 16th international conference on advanced communication technology (pp. 808-814). IEEE.
- Azeem, M. , Ullah, A., Ashraf, H., Jhanjhi, N. Z., Humayun, M., Aljahdali, S., & Tabbakh, T. A. (2021). Fog-oriented secure and lightweight data aggregation in iomt. IEEE Access, 9, 111072-111082.
- Ahmed, Q. W. , Garg, S., Rai, A., Ramachandran, M., Jhanjhi, N. Z., Masud, M., & Baz, M. (2022). Ai-based resource allocation techniques in wireless sensor internet of things networks in energy efficiency with data optimization. Electronics, 11(13), 2071.
- Khan, N. A. , Jhanjhi, N. Z., Brohi, S. N., Almazroi, A. A., & Almazroi, A. A. (2022). A secure communication protocol for unmanned aerial vehicles. CMC-Computers Materials & Continua, 70(1), 601-618.
- Muzafar, S. , & Jhanjhi, N. Z. (2020). Success stories of ICT implementation in Saudi Arabia. In Employing Recent Technologies for Improved Digital Governance (pp. 151-163). IGI Global Scientific Publishing.
- Jabeen, T., Jabeen, I., Ashraf, H., Jhanjhi, N. Z., Yassine, A., & Hossain, M. S. (2023). An intelligent healthcare system using IoT in wireless sensor network. Sensors, 23(11), 5055.
- Shah, I. A. , Jhanjhi, N. Z., & Laraib, A. (2023). Cybersecurity and blockchain usage in contemporary business. In Handbook of Research on Cybersecurity Issues and Challenges for Business and FinTech Applications (pp. 49-64). IGI Global.
- Hanif, M. , Ashraf, H., Jalil, Z., Jhanjhi, N. Z., Humayun, M., Saeed, S., & Almuhaideb, A. M. (2022). AI-based wormhole attack detection techniques in wireless sensor networks. Electronics, 11(15), 2324.
- Shah, I. A. , Jhanjhi, N. Z., Amsaad, F., & Razaque, A. (2022). The role of cutting-edge technologies in industry 4.0. In Cyber Security Applications for Industry 4.0 (pp. 97-109). Chapman and Hall/CRC.
- Humayun, M., Almufareh, M. F., & Jhanjhi, N. Z. (2022). Autonomous traffic system for emergency vehicles. Electronics, 11(4), 510.
- Muzammal, S. M. , Murugesan, R. K., Jhanjhi, N. Z., & Jung, L. T. (2020, October). SMTrust: Proposing trust-based secure routing protocol for RPL attacks for IoT applications. In 2020 International Conference on Computational Intelligence (ICCI) (pp. 305-310). IEEE.
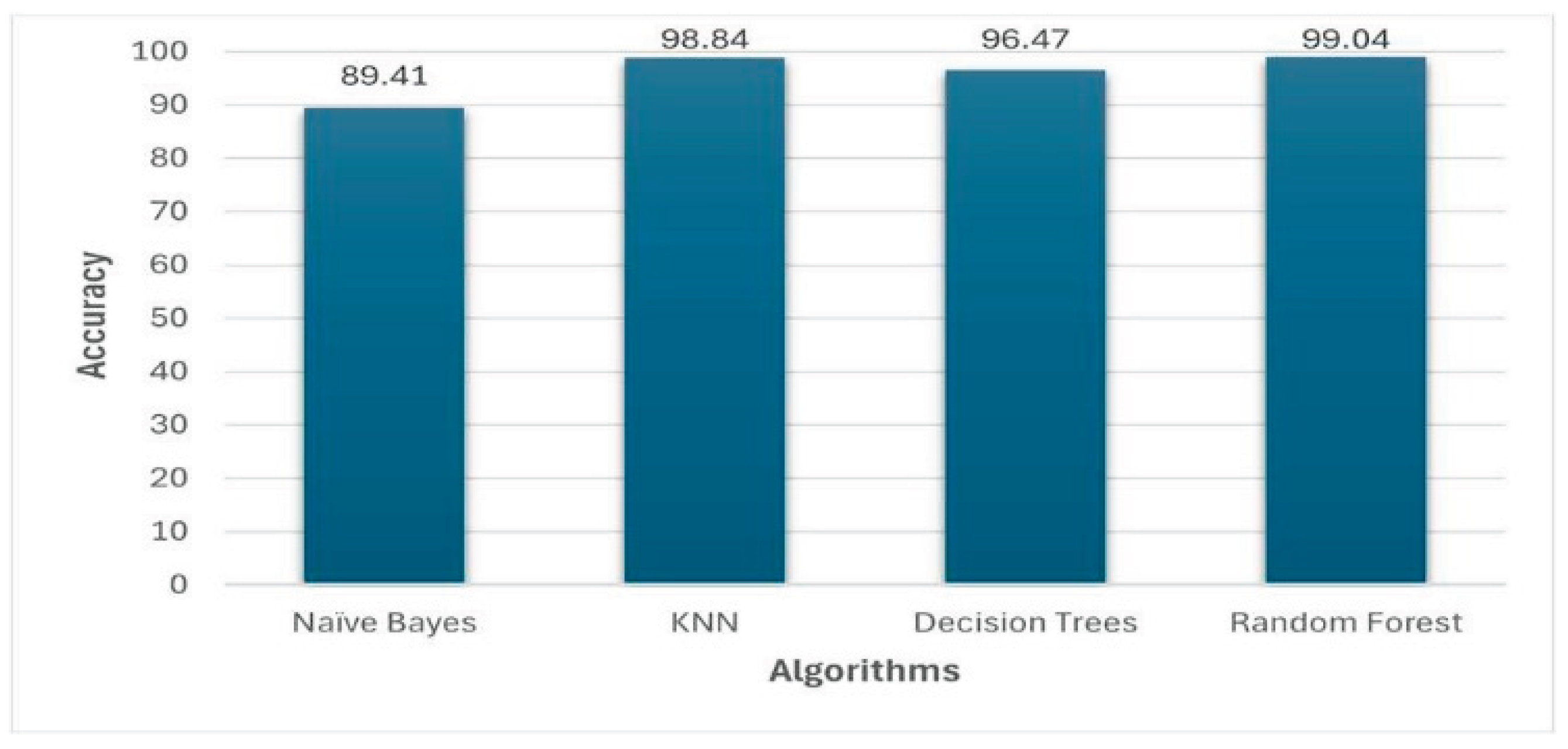
| Algorithm | Accuracy (%) | Precision | Recall |
| Naive bayes |
89.41 | 89.37 | 89.51 |
| Decision trees |
96.47 | 97.26 | 96.85 |
| K nearest neighbors |
98.84 | 99.01 | 99.00 |
| Random Forest |
99.04 | 99.09 | 98.98 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




