Submitted:
06 November 2025
Posted:
07 November 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
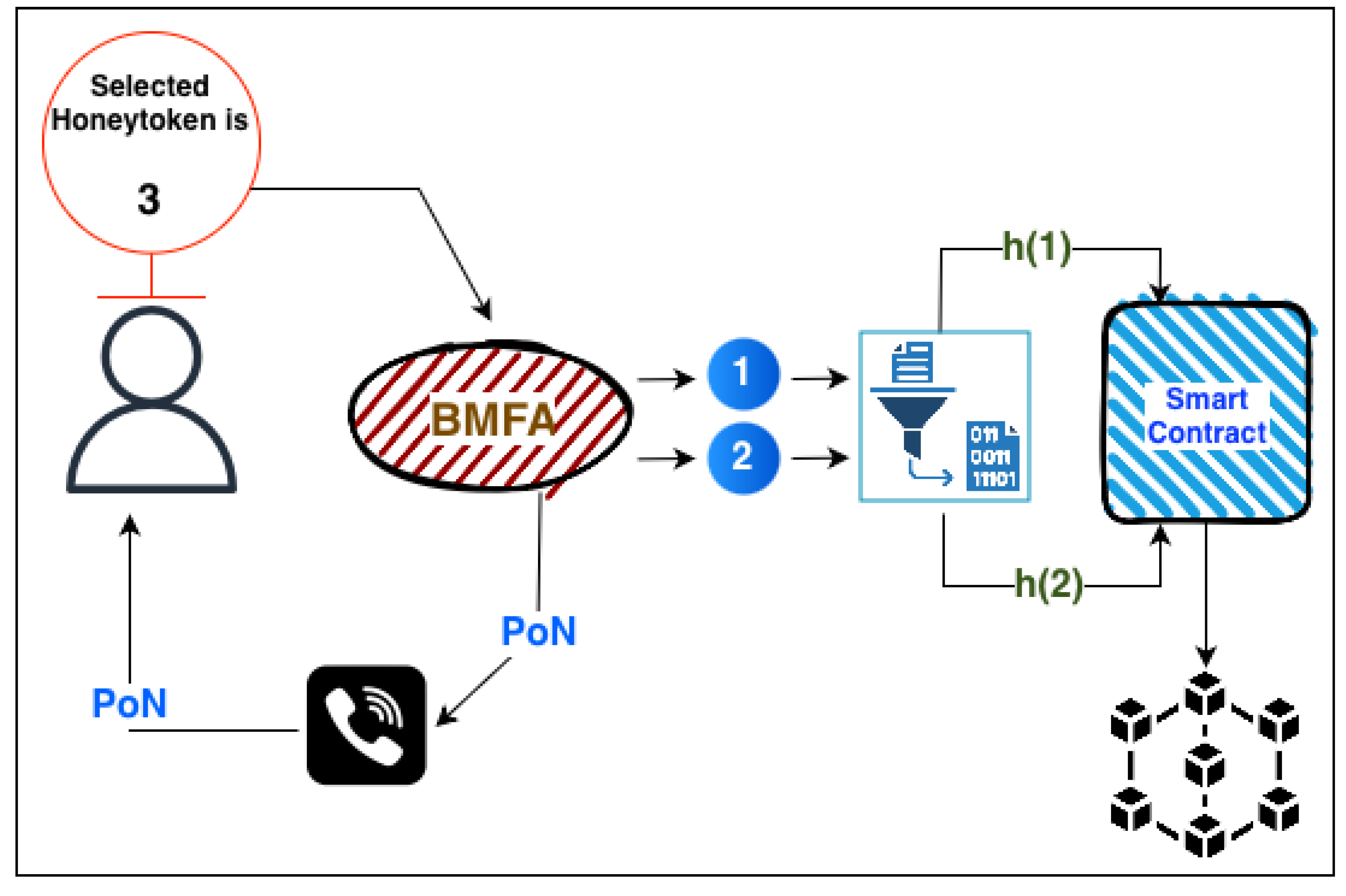
- Honeytokens and Ethereum: The proposed BMFA method incorporates the Ethereum blockchain technology to provide multifactor authentication (MFA) and combines the Honeytoken technology to enhance security. The selected novel approach strengthens user authentication mechanisms included in a decentralized ecosystem and adds extra levels of security.
- Honeytoken Integration into Smart Contracts: The integration of honeytokens into smart contracts provides a secure and unchangeable environment [6], properties inherited from blockchain technology, known as the immutability feature [7]. Beyond user identity verification, smart contracts strengthen authentication mechanisms by including an additional tamper-resistance layer that prevents illegal access or alterations.
- Dynamic Honeytokens: In the realm of contemporary cybersecurity, the strategic utilization of honeytokens has emerged as a critical line of defense against potential threats. In our pursuit of heightened security measures, we have devised an innovative approach to honeytoken implementation — a dynamic system wherein the token undergoes continuous change with each user login. The proposed mechanism introduces an element of adaptability, generating a distinctive token for every login instance. This dynamic feature not only elevates the overall security posture but also ensures that users consistently receive the accurate honeytoken on one communication channel while encountering a set of three distinct honeytokens on another. This multifaceted approach adds complexity against potential adversaries, fortifying defenses against unauthorized access and malicious activities. As we advance cybersecurity protocols, the dynamic honeytoken system is robust against evolving threats.
- Honeytokens for Early Threat Detection: Decoy data, known as honeytokens, have been deliberately inserted into a system and aim at luring attackers. Organizations can lure the attackers by integrating honeytokens into smart contracts, which, upon activation, raise alerts to any potential security incident. The early detection and mitigation of such threats are feasible when this technique is applied.
- Time Delay Smart contracts usually have time delays that range from 1 second to 1 minute [6]. Specifically, Ethereum has a block time of around 15 seconds. On average, a new block is added to the Ethereum blockchain approximately every 15 seconds. However, during periods of high network congestion or if users set lower gas fees, it might take longer for a transaction to be confirmed. Similarly, Bitcoin has a longer block time, approximately 10 minutes. This means that, on average, a new block is mined every 10 minutes, and smart contract capabilities on Bitcoin are more limited compared to platforms like Ethereum. The proposed authentication mechanism overcomes these time delays, and its operation is not affected by them.
2. Related Work
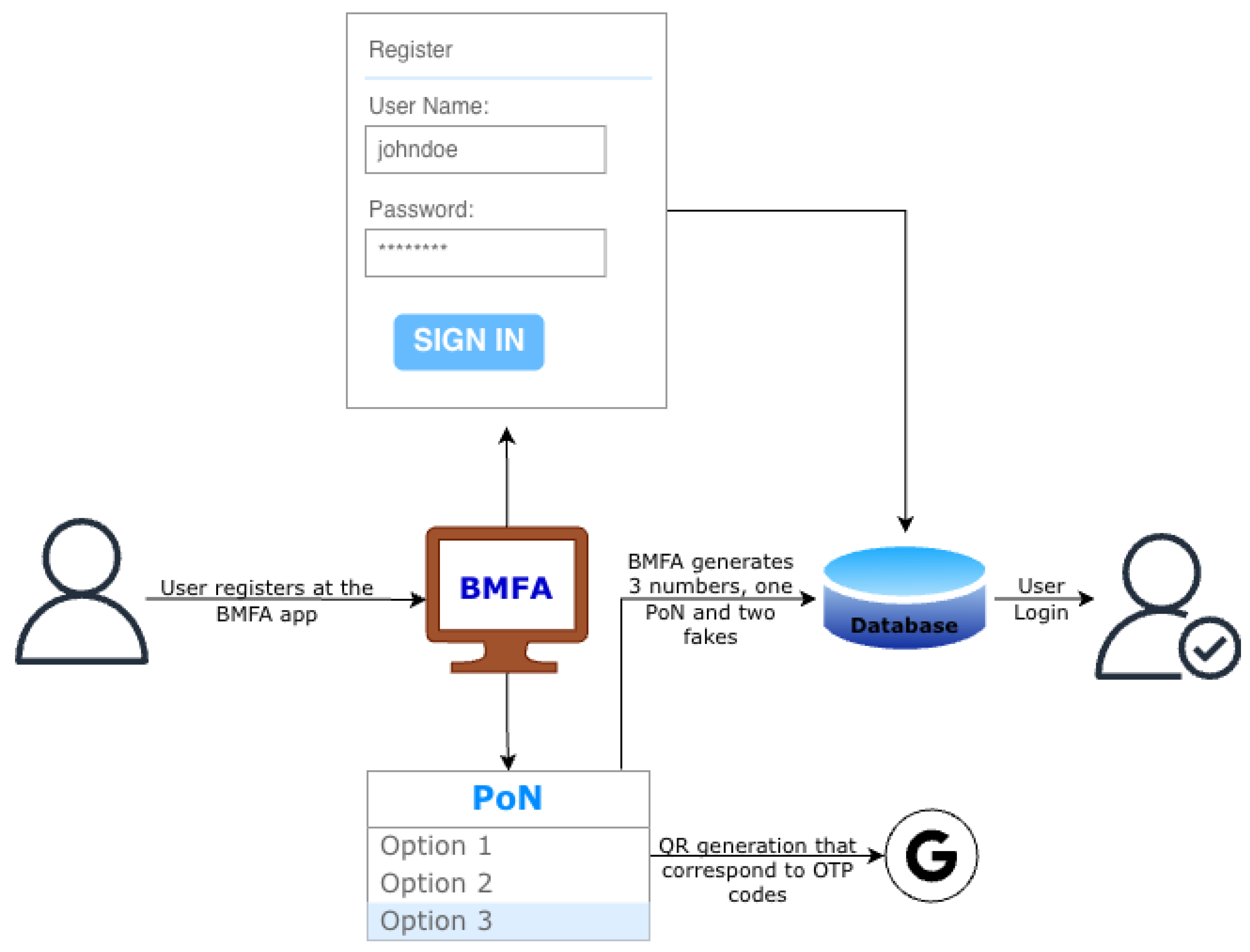
3. The BMFA Mechanism
3.1. Outline of the Design
3.2. Components and Interoperability
3.3. Honeytoken Integration into Smart Contracts
3.4. Secure Delivery of Honeytoken
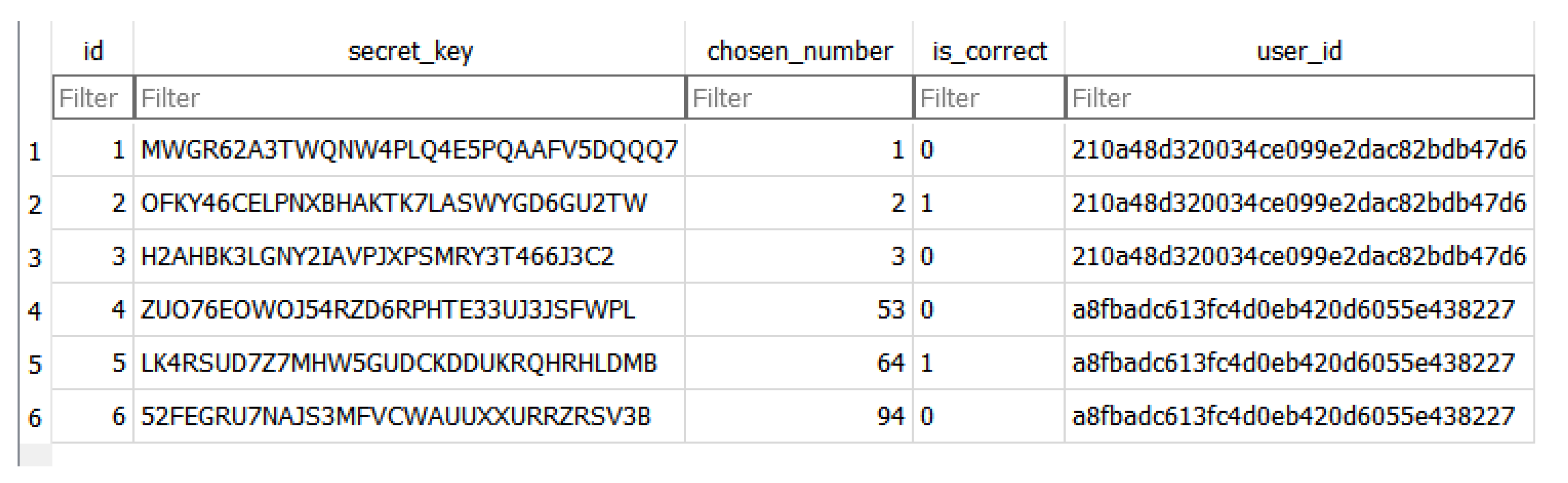
3.5. Mechanism Implementation and Functionality
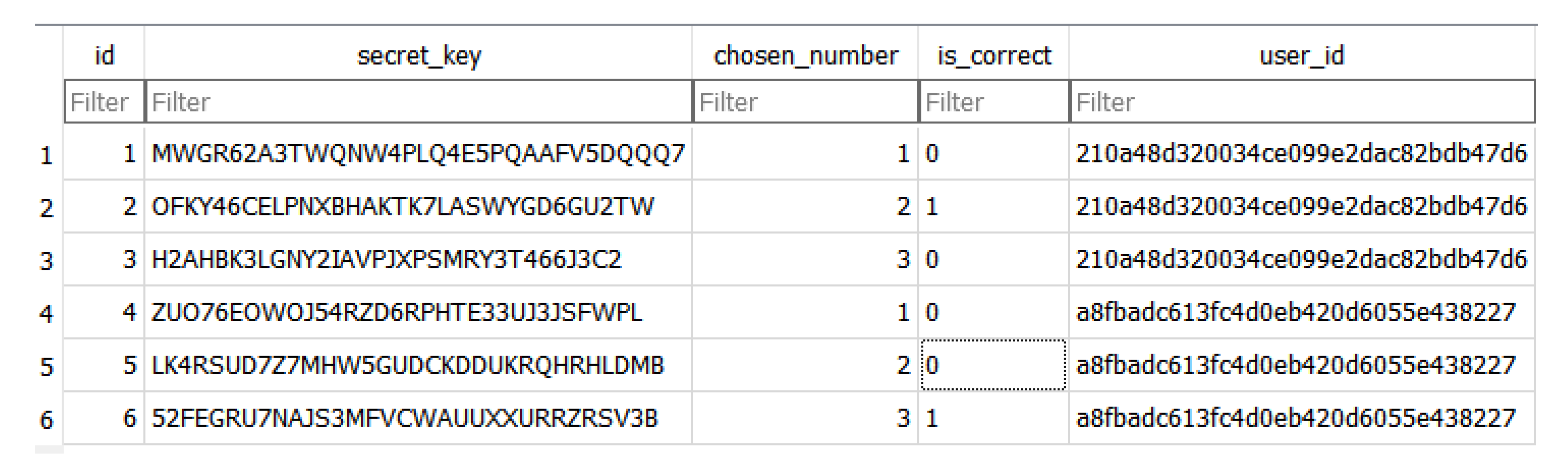
3.5.1. Registation Phase
3.5.2. Login Phase
| Algorithm 1 Smart Contract Data Validation and Retrieval |
|
4. Evaluation of the BMFA Dynamic Mechanism
4.1. Evaluation Criteria and Selection Justifications
4.1.1. Threat Selection
- Low Risk: The attack is hard to carry out, has little effect, or is well countered by existing defenses.
- Medium Risk: The assault is doable but necessitates particular circumstances, has a moderate effect, or can be lessened with further security.
- High Risk: The assault has serious repercussions, is simple to carry out, or lacks appropriate mitigation techniques.
- 51% Attack: An extra line of protection can be added to the blockchain system by introducing honeytokens. In essence, honeytokens are lure assets that mimic real ones to potential attackers. An attacker may interact with these honeytokens if their main goal is system manipulation [23], which could notify the network of their presence and possibly lead to the activation of countermeasures.
- Sybil Attack: By making it expensive to generate numerous false identities, Ethereum’s PoS mechanism helps prevent Sybil assaults [24]. However, attackers might still target OTP delivery systems by flooding the system with phony accounts. The system can identify and report questionable authentication attempts from these phony identities by using honeytokens as decoy credentials. The system can recognize and react to Sybil-based threats by keeping an eye on interactions with honeytokens.
- Smart Contract Exploits: By incorporating honeytokens into smart contracts, vulnerabilities can be found early on [25]. An attacker may unintentionally set off the honeytoken, indicating the existence of malicious behavior, if they try to take advantage of a smart contract.
- Routing Attack: Attackers may be able to obtain authentication codes by intercepting OTP packets while they are being transmitted [26]. The system can use offline OTP techniques that don’t depend on network delivery, like Google Authenticator, to tackle this. When an attacker tries to use a honeytoken, it indicates that the OTP was intercepted, enabling the system to implement countermeasures such as preventing access from dubious sources. Honeytokens can also be presented as phony OTPs.
- Phishing Attack: Using phony websites or misleading messages, attackers can try to fool users into revealing their login credentials [27]. By functioning as bait, honeytokens can be a potent defense. If an attacker unintentionally uses a honeytoken credential, the system can quickly identify the phishing attempt and take the appropriate action. This strategy strengthens defenses against phishing attempts when paired with password managers and user education.
- Reentrancy Attack: If authentication depends on contract logic, reentrancy attacks [28] could still be dangerous, even though their main target is smart contracts that retain money. By adhering to best practices such as the Checks-Effects-Interaction pattern [29], the system can reduce this. By being incorporated into smart contracts, honeytokens can further enhance security. If an attacker initiates a honeytoken interaction through recursive calls, the system can identify and stop the attack before it goes out of control.
- Eclipse Attack: By postponing or altering authentication replies, attackers may try to block an Ethereum node from the network [30]. If blockchain data is used via authentication methods, this could be risky. By being inserted into network interactions regularly, honeytokens can aid in the detection of such assaults. Should an anticipated honeytoken interaction not take place as planned, it may signal that a node is being attacked, triggering defensive measures such as node switching or peer connection refreshes.
- Timejacking Attack: To obtain an edge, an attacker can alter the timestamps of the blockchain, which could have an impact on time-sensitive authentication systems [31]. This risk is reduced by timestamp validation techniques, which make sure that the system will not accept changed time values. By including timestamps in decoy transactions, honeytokens can strengthen this defense. Should a honeytoken interaction take place with an inaccurate timestamp, the system can identify the anomaly and reject the transaction.
- Dusting Attack: Sending small amounts of cryptocurrency to wallets to track transactions and de-anonymize users is known as a "dusting attack" [32]. Honeytokens could be used as bait transactions to find and identify attackers trying to track user activity, even though this kind of attack has nothing to do with authentication. The system can keep an eye on an attacker’s activities and take action if they use honeytoken dust transactions.
- double-spending Attack: It is possible to deliberately insert honeytokens into the blockchain to serve as bait for prospective double-spending attacks [33]. If an attacker tries to engage in double-spending through these honeytoken interactions, the network can identify the irregularity and initiate remedial measures, such as stopping transactions or notifying administrators.
- Bridge Attack: By taking advantage of flaws in the systems that move assets between blockchains, bridge attacks target cross-chain solutions [34]. This danger is negligible if cross-chain activities are not used in the authentication system. If cross-chain interactions are included in the future, honeytokens can be used as test transactions to find anomalies and help find weaknesses before attackers take advantage of them.
- Flash Loan Attack: These attacks, which use uncollateralized loans to influence market circumstances, are primarily pertinent to DeFi applications [35]. This kind of attack is not a particular problem because the authentication process does not entail loans or financial transactions. On the other hand, honeytokens might be used to mimic transactions and spot possible vulnerabilities before they are taken advantage of if financial activities are eventually incorporated.
- Man-in-the-Middle (MITM) Attack: The BMFA mechanism secures against MITM attacks [36] by employing a physical instance for secure number communication. The presented research work, though not directly addressing MITM attacks, benefits from the use of blockchain and smart contracts, contributing to overall security.
- Brute Force Attack: The BMFA mechanism introduces complexity by the use of the Bcrypt hashing algorithm and by employing user-specific numbers, making brute force attacks more challenging. This research work, while not explicitly mentioning defense against brute force attacks [37], aligns with the principle of the Bcrypt hashing algorithm for advanced security.
- Honeytokens: The BMFA mechanism introduces decoy numbers, adding an extra layer of confusion for potential attackers, a unique aspect not explicitly covered in the related works.
4.2. Evaluation
- Smart-Contract Exploits — because any logic or storage placed on-chain (even transiently) introduces contract-level risk (bugs, access-control flaws) that may invalidate authentication guarantees;
- Routing Attacks — because OTP/PoN delivery often traverses third-party carriers or messaging platforms (SMS, Viber, email), so interception or routing manipulation can directly enable account takeover;
- Phishing Attacks — because social-engineering remains the dominant human vector and honeytokens are explicitly designed to detect it;
- Eclipse Attacks — because node isolation can distort the on-chain view used for timeliness or rotation assurances;
- Man-in-the-Middle (MITM) Attacks — because mixed on-chain/off-chain flows create multiple channels where message integrity and endpoint authentication are required;
- Brute-Force Attacks — because passwords, PoN choices, and OTP configurations determine resistance to offline/online guessing; and
- Private Key / Secret Compromise — because leakage of signing or long-lived secrets is catastrophic for systems that rely on cryptographic identity or immutable ledgers.
- Probability of Occurrence, or likelihood: How frequently does the attack happen in actual situations? Is it possible with the security measures in place now?
- Impact (Attack’s Repercussion): What harm might result from a successful attack? Does it result in system compromise, data exposure, or monetary loss?
- Exploitability (Easy to Implement): How challenging would it be for an attacker to execute this attack? Does it call for a lot of money or sophisticated knowledge?
- Availability of Mitigation (Defense Mechanisms in Place): Are there any countermeasures in place that render the attack useless or drastically lower the likelihood that it will succeed?
- Attack Surface (Scope of Vulnerability): Does the assault impact the entire system or network (big scope) or just a single component (small scope)?
4.3. Outstanding Security Considerations
4.3.1. Is Finding the Smart Contract a Real Threat?
- Find the relevant smart contract among millions of transactions.
- Extract the hashed PoN from the contract.
- Attempt to brute-force the PoN within 30 seconds (since OTP expires quickly).
- Finding the Smart Contract — If the contract address is well-hidden (not tied to a public user ID), an attacker must sift through a lot of data. However, if they monitor all recent transactions, they can track which ones are used for authentication and target them.
- Extracting the Hashed PoN — Since Ethereum is transparent, once they find the contract, they can see the stored hashed PoN.
- Brute-Forcing the PoN (Hash Cracking) — Bcrypt is slow, which is great for security. It makes brute-force attacks difficult. However, hashing a number from 1-3 is weak. Since there are only 3 possible PoN values, an attacker could pre-compute their hashes and produce pre-computed hash tables (rainbow table attack) and instantly match them. The real security comes from brute-forcing the OTP (6-digit code, 1 million combinations). But if they learn the correct PoN quickly, they only have to guess 6 digits.
4.3.2. Can an Attacker Decrypt the OTP Within 30 Seconds?
5. Conclusions and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Wang, D.; Wang, P. Two birds with one stone: Two-factor authentication with security beyond conventional bound. IEEE Transactions on Dependable and Secure Computing 2016, 15, 708–722. [Google Scholar] [CrossRef]
- Petrunić, A.R. Honeytokens as active defense. In Proceedings of the 2015 38th International Convention on Information and Communication Technology, Electronics and Microelectronics (MIPRO). IEEE; 2015; pp. 1313–1317. [Google Scholar]
- Papaspirou, V.; Maglaras, L.; Ferrag, M.A.; Kantzavelou, I.; Janicke, H.; Douligeris, C. A novel two-factor honeytoken authentication mechanism. In Proceedings of the 2021 International Conference on Computer Communications and Networks (ICCCN). IEEE; 2021; pp. 1–7. [Google Scholar]
- Li, Q.; Zhang, Q.; Huang, H.; Zhang, W.; Chen, W.; Wang, H. Secure, efficient, and weighted access control for cloud-assisted industrial IoT. IEEE Internet of Things Journal 2022, 9, 16917–16927. [Google Scholar] [CrossRef]
- Papaspirou, V.; Kantzavelou, I.; Yigit, Y.; Maglaras, L.; Katsikas, S. A Blockchain-based Multi-Factor Honeytoken Dynamic Authentication Mechanism. In Proceedings of the Proceedings of the 19th International Conference on Availability, Reliability and Security, 2024, pp. 1–9.
- Rouhani, S.; Deters, R. Security, performance, and applications of smart contracts: A systematic survey. IEEE Access 2019, 7, 50759–50779. [Google Scholar] [CrossRef]
- Bhutta, M.N.M.; Khwaja, A.A.; Nadeem, A.; Ahmad, H.F.; Khan, M.K.; Hanif, M.A.; Song, H.; Alshamari, M.; Cao, Y. A survey on blockchain technology: Evolution, architecture and security. Ieee Access 2021, 9, 61048–61073. [Google Scholar] [CrossRef]
- Amrutiya, V.; Jhamb, S.; Priyadarshi, P.; Bhatia, A. Trustless two-factor authentication using smart contracts in blockchains. In Proceedings of the 2019 international conference on information networking (ICOIN). IEEE; 2019; pp. 66–71. [Google Scholar]
- Evans, M.; He, Y.; Maglaras, L.; Yevseyeva, I.; Janicke, H. Evaluating information security core human error causes (IS-CHEC) technique in public sector and comparison with the private sector. International journal of medical informatics 2019, 127, 109–119. [Google Scholar] [CrossRef] [PubMed]
- Sun, H.; Sun, K.; Wang, Y.; Jing, J. TrustOTP: Transforming smartphones into secure one-time password. In Proceedings of the Proceedings of the 22nd ACM SIGSAC Conference on Computer and Communications Security, 2015, pp. 976–988.
- ALSaleem, B.O.; Alshoshan, A.I. Multi-factor authentication to systems login. In Proceedings of the 2021 National Computing Colleges Conference (NCCC). IEEE; 2021; pp. 1–4. [Google Scholar]
- Thompson, A.; Abayomi, A.; Gabriel, A.J. Multifactor IoT Authentication System for Smart Homes Using Visual Cryptography, Digital Memory, and Blockchain Technologies. In Blockchain Applications in the Smart Era; Springer, 2022; pp. 273–290.
- Kebande, V.R.; Awaysheh, F.M.; Ikuesan, R.A.; Alawadi, S.A.; Alshehri, M.D. A blockchain-based multi-factor authentication model for a cloud-enabled internet of vehicles. Sensors 2021, 21, 6018. [Google Scholar] [CrossRef] [PubMed]
- Buccafurri, F.; De Angelis, V.; Nardone, R. Securing mqtt by blockchain-based otp authentication. Sensors 2020, 20, 2002. [Google Scholar] [CrossRef] [PubMed]
- Microsoft. Multi-Factor Authentication Number Matching, 2024. Accessed: 2024-01-31.
- Putri, M.C.I.; Sukarno, P.; Wardana, A.A. Two factor authentication framework based on ethereum blockchain with dApp as token generation system instead of third-party on web application. Register 2020, 6, 74–85. [Google Scholar] [CrossRef]
- Mercan, S.; Cebe, M.; Akkaya, K.; Zuluaga, J. Blockchain-Based Two-Factor Authentication for Credit Card Validation. In Proceedings of the International Workshop on Data Privacy Management. Springer; 2021; pp. 319–327. [Google Scholar]
- Akanda, M.M.R.R.; Lacy, A.; Saxena, N. {SoK}: Inaccessible & Insecure: An Exposition of Authentication Challenges Faced by Blind and Visually Impaired Users in {State-of-the-Art} Academic Proposals. In Proceedings of the 34th USENIX Security Symposium (USENIX Security 25), 2025, pp. 1393–1413.
- Papaspirou, V.; Papathanasaki, M.; Maglaras, L.; Kantzavelou, I.; Douligeris, C.; Ferrag, M.A.; Janicke, H. Security Revisited: Honeytokens meet Google Authenticator. In Proceedings of the 2022 7th South-East Europe Design Automation, Computer Engineering, 2022, Computer Networks and Social Media Conference (SEEDA-CECNSM). IEEE; pp. 1–8.
- Otta, S.P.; Panda, S.; Gupta, M.; Hota, C. A systematic survey of multi-factor authentication for cloud infrastructure. Future Internet 2023, 15, 146. [Google Scholar] [CrossRef]
- Ross, R.S. Guide for conducting risk assessments, 2012.
- Initiative, J.T.F.T.; et al. SP 800-39. managing information security risk: Organization, mission, and information system view; National Institute of Standards & Technology, 2011.
- Aponte-Novoa, F.A.; Orozco, A.L.S.; Villanueva-Polanco, R.; Wightman, P. The 51% attack on blockchains: A mining behavior study. IEEE access 2021, 9, 140549–140564. [Google Scholar] [CrossRef]
- Platt, M.; McBurney, P. Sybil in the haystack: A comprehensive review of blockchain consensus mechanisms in search of strong Sybil attack resistance. Algorithms 2023, 16, 34. [Google Scholar] [CrossRef]
- Kushwaha, S.S.; Joshi, S.; Singh, D.; Kaur, M.; Lee, H.N. Systematic review of security vulnerabilities in ethereum blockchain smart contract. Ieee Access 2022, 10, 6605–6621. [Google Scholar] [CrossRef]
- Aggarwal, S.; Kumar, N. Attacks on blockchain. In Advances in computers; Elsevier, 2021; Vol. 121, pp. 399–410.
- Joshi, K.; Bhatt, C.; Shah, K.; Parmar, D.; Corchado, J.M.; Bruno, A.; Mazzeo, P.L. Machine-learning techniques for predicting phishing attacks in blockchain networks: A comparative study. Algorithms 2023, 16, 366. [Google Scholar] [CrossRef]
- Alkhalifah, A.; Ng, A.; Watters, P.A.; Kayes, A. A mechanism to detect and prevent ethereum blockchain smart contract reentrancy attacks. Frontiers in Computer Science 2021, 3, 598780. [Google Scholar] [CrossRef]
- Solidity. Security Considerations: Reentrancy, 2022.
- Alangot, B.; Reijsbergen, D.; Venugopalan, S.; Szalachowski, P.; Yeo, K.S. Decentralized and lightweight approach to detect eclipse attacks on proof of work blockchains. IEEE Transactions on Network and Service Management 2021, 18, 1659–1672. [Google Scholar] [CrossRef]
- Dwivedi, K.; Agrawal, A.; Bhatia, A.; Tiwari, K. A novel classification of attacks on blockchain layers: Vulnerabilities, attacks, mitigations, and research directions 2024. arXiv preprint arXiv:2404.18090, arXiv:2404.18090.
- binti Malik, M.; Zolkipli, M.F. Blockchain Threats: A Look into the Most Common Forms of Cryptocurrency Attacks. Borneo International Journal eISSN 2636-9826 2023, 6, 20–32. [Google Scholar]
- Iqbal, M.; Matulevičius, R. Exploring sybil and double-spending risks in blockchain systems. IEEE Access 2021, 9, 76153–76177. [Google Scholar]
- Zhang, M.; Zhang, X.; Zhang, Y.; Lin, Z. Security of cross-chain bridges: Attack surfaces, defenses, and open problems. In Proceedings of the Proceedings of the 27th International Symposium on Research in Attacks, Intrusions and Defenses, 2024, pp. 298–316.
- Qin, K.; Zhou, L.; Livshits, B.; Gervais, A. Attacking the defi ecosystem with flash loans for fun and profit. In Proceedings of the International conference on financial cryptography and data security. Springer; 2021; pp. 3–32. [Google Scholar]
- Choi, J.; Ahn, B.; Bere, G.; Ahmad, S.; Mantooth, H.A.; Kim, T. Blockchain-based man-in-the-middle (MITM) attack detection for photovoltaic systems. In Proceedings of the 2021 IEEE Design Methodologies Conference (DMC). IEEE; 2021; pp. 1–6. [Google Scholar]
- Byun, H.; Kim, J.; Jeong, Y.; Seok, B.; Gong, S.; Lee, C. A Security Analysis of Cryptocurrency Wallets against Password Brute-Force Attacks. Electronics 2024, 13, 2433. [Google Scholar] [CrossRef]
- Razikin, K.; Soewito, B. Cybersecurity decision support model to designing information technology security system based on risk analysis and cybersecurity framework. Egyptian Informatics Journal 2022, 23, 383–404. [Google Scholar] [CrossRef]
- Spanos, A.; Kantzavelou, I. EtherVote: A Secure Smart Contract-based E-Voting System. Wireless Netw 2025, 31, 1279–1299. [Google Scholar] [CrossRef]

| Features | Related Works | BMFA |
|---|---|---|
| Honeytoken | × | ✓ |
| Smart Contract | ✓ | ✓ |
| Protection Against MITM Attacks | ✓ | ✓ |
| Attack Type | Risk Level | Description and Justification |
|---|---|---|
| 51% Attack | Low | Ethereum is PoS(Proof-of-stake) and makes a 51% attack nearly impossible. |
| Sybil Attack | Low | Ethereum resists Sybil attacks, but OTP delivery could be targeted. |
| Smart Contract Exploits | Medium | Vulnerabilities in Solidity (e.g., reentrancy bug) could be exploited. |
| Routing Attack | Medium | OTP messages could be intercepted. Use Google Authenticator. |
| Phishing Attack | Medium | Attackers could trick users. Recommend password managers. |
| Reentrancy Attack | Low | Mostly applies to contracts holding funds. |
| Eclipse Attack | Medium | Attack on Ethereum nodes could delay authentication. |
| Timejacking Attack | Low | Mitigated with timestamp validation. |
| Dusting Attack | Low | Not relevant to our implementation. |
| Double-Spending Attack | Low | Not handling payments, so this isn’t a concern. |
| Bridge Attack | Low | Relevant only for cross-chain solutions. |
| Flash Loan Attack | Low | Only applies to DeFi transactions. |
| Man-in-the-Middle (MITM) Attack | Medium | Attackers may intercept authentication messages. Using a physical instance for secure number communication prevents interception. |
| Brute Force Attack | Medium | Bcrypt hashing and user-specific numbers make brute-force attacks difficult. |
| Attack Type | Risk Level | Related Papers | BMFA | [5] | [31] | [4] | [8] | [20] | [27] | [19] |
|---|---|---|---|---|---|---|---|---|---|---|
| Smart Contract Exploits | Medium | [5], [8], [27], [19] | 3 | 2 | N/A | N/A | 3 | N/A | 2 | 4 |
| Routing Attack | Medium | [8], [19] | 2 | 3 | 5 | N/A | 2 | 4 | 3 | 4 |
| Phishing Attack | Medium | [4], [20], Azure | 3 | 2 | 4 | 3 | 3 | 4 | 2 | 3 |
| Eclipse Attack | Medium | [8], [27], [19] | 2 | 3 | N/A | N/A | 3 | N/A | 3 | 3 |
| Man-in-the-Middle (MITM) Attack | Medium | [31], [19], [20] | 3 | 3 | 5 | 3 | 2 | 4 | 3 | 4 |
| Brute Force Attack | Medium | [31], [4], [20] | 4 | 3 | 4 | 4 | 4 | 4 | 3 | 3 |
| Private Key / Secret Compromise | High | [31], [19], [8] | 2 | 2 | 5 | N/A | 2 | 3 | 2 | 3 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




