Submitted:
11 September 2025
Posted:
15 September 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- What is the definition of fraud within the context of P2P lending?
- Which machine learning and AI techniques and schemes are suited for P2P lending fraud detection and prevention?
- What are the managerial and ethical implications?
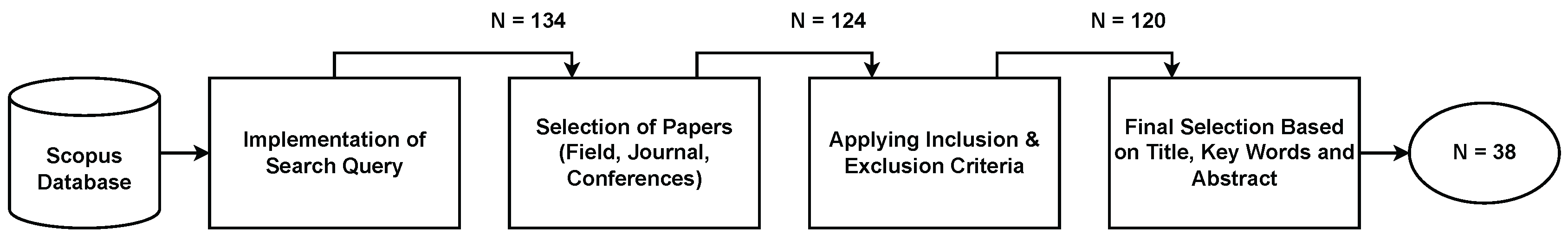
2. Methodology
- First, we define the study problem by formulating research questions.
- Second, we establish and verify a systematic approach for reviewing to offer direction for our data exploration and examination (i.e., we draw a research map, more details in Figure ??).
- The third step involves conducting a thorough analysis and exploration of the relevant literature, ensuring a comprehensive examination of the subject area.
- Fourth, we use certain criteria to carefully evaluate the collected studies for inclusion, ensuring their relevance and high quality.
- The fifth step involves a thorough evaluation of the quality of each selected study.
- Sixth, the data extraction procedure begins, when pertinent information is systematically gathered from each study.
- The seventh step, data analysis and synthesis, allows us to combine findings and extract meaningful insights.
- In the eighth and final step, we summarize the results in detailed reports, presenting our findings in a systematic and easily comprehensible manner.
- (“Fraud" OR “Fraudulent Activities" OR “Fraud Detection") AND (“P2P Lending" OR “P2P" OR “Alternative Financ*")
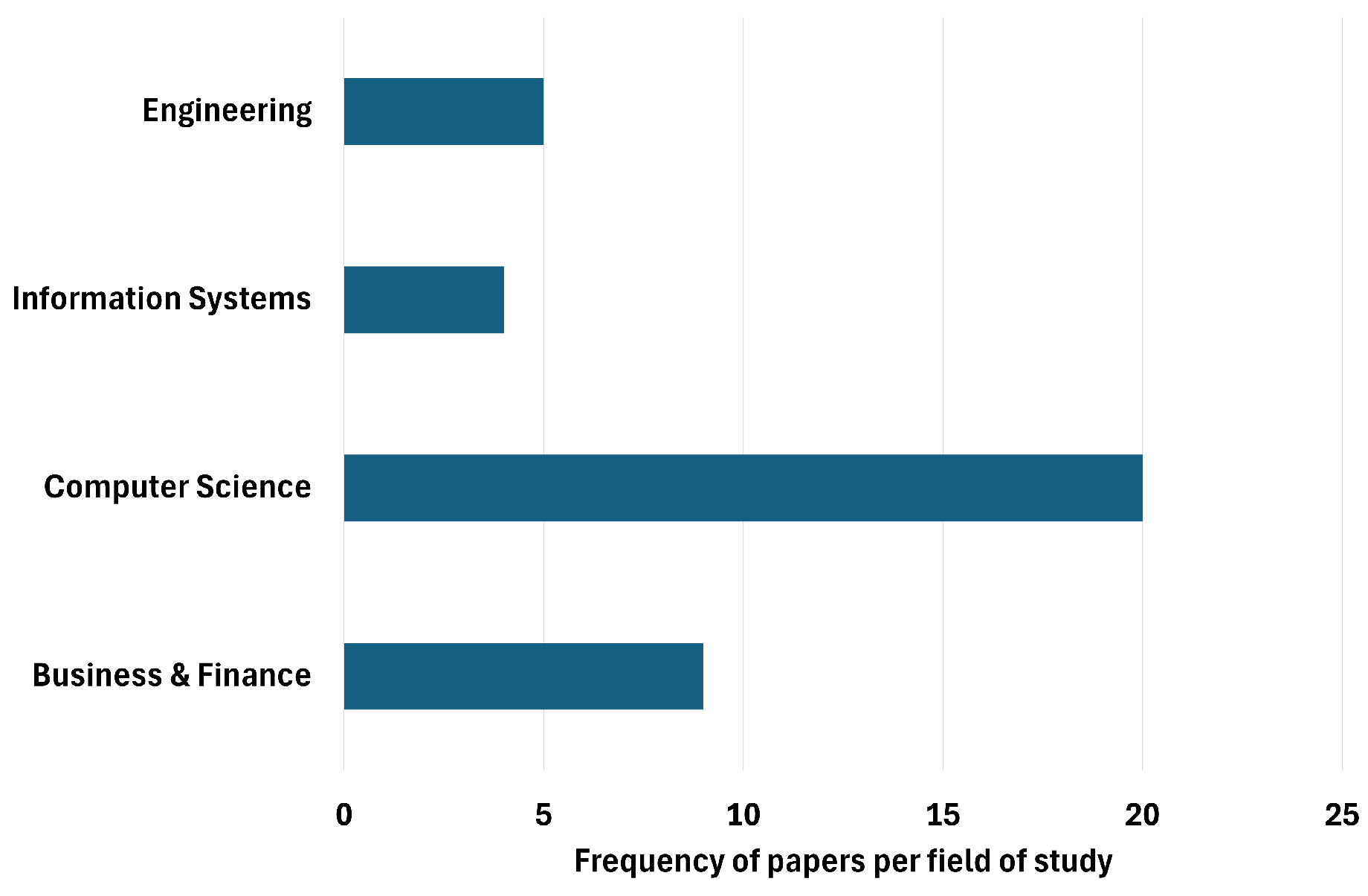
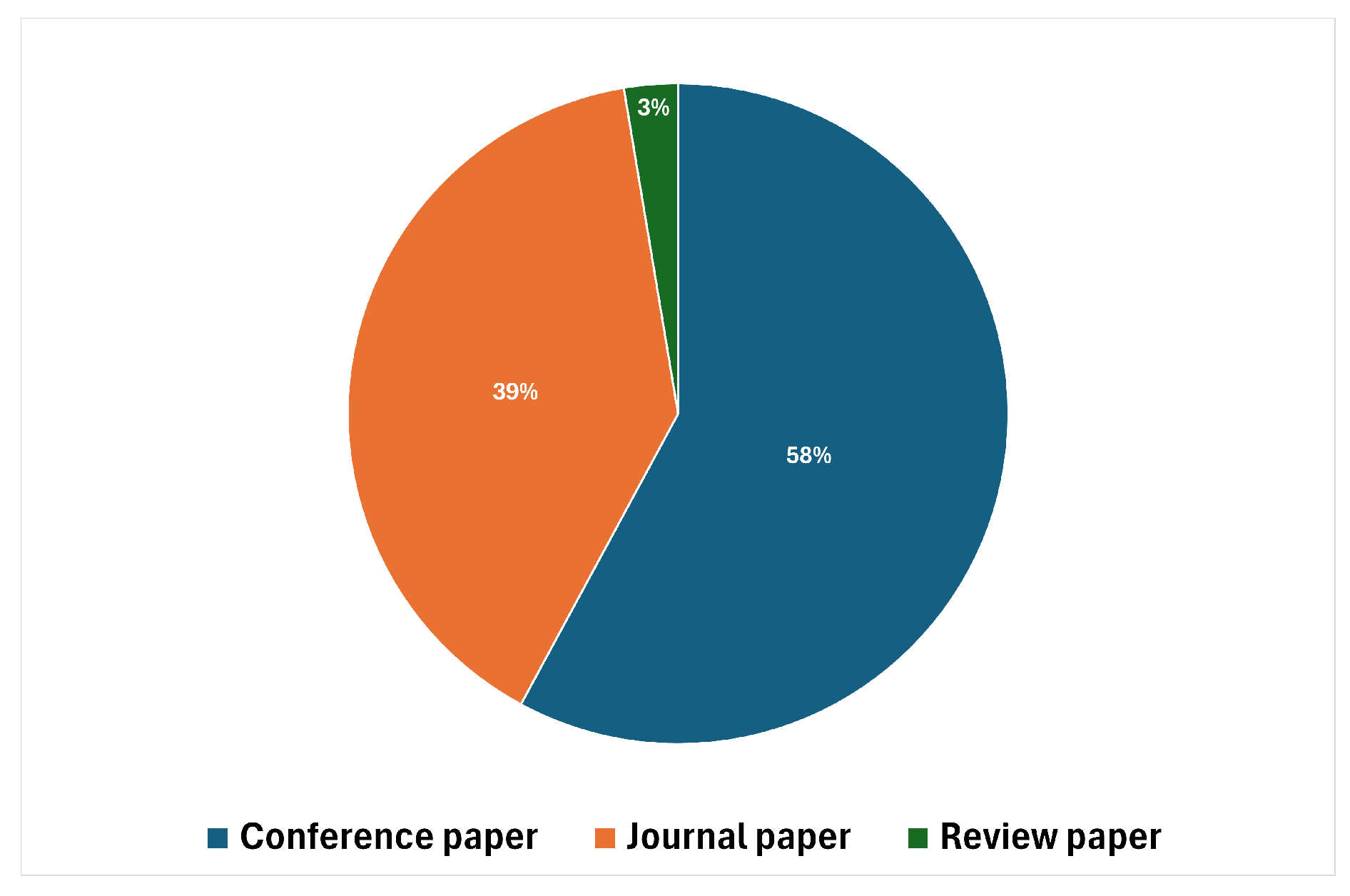
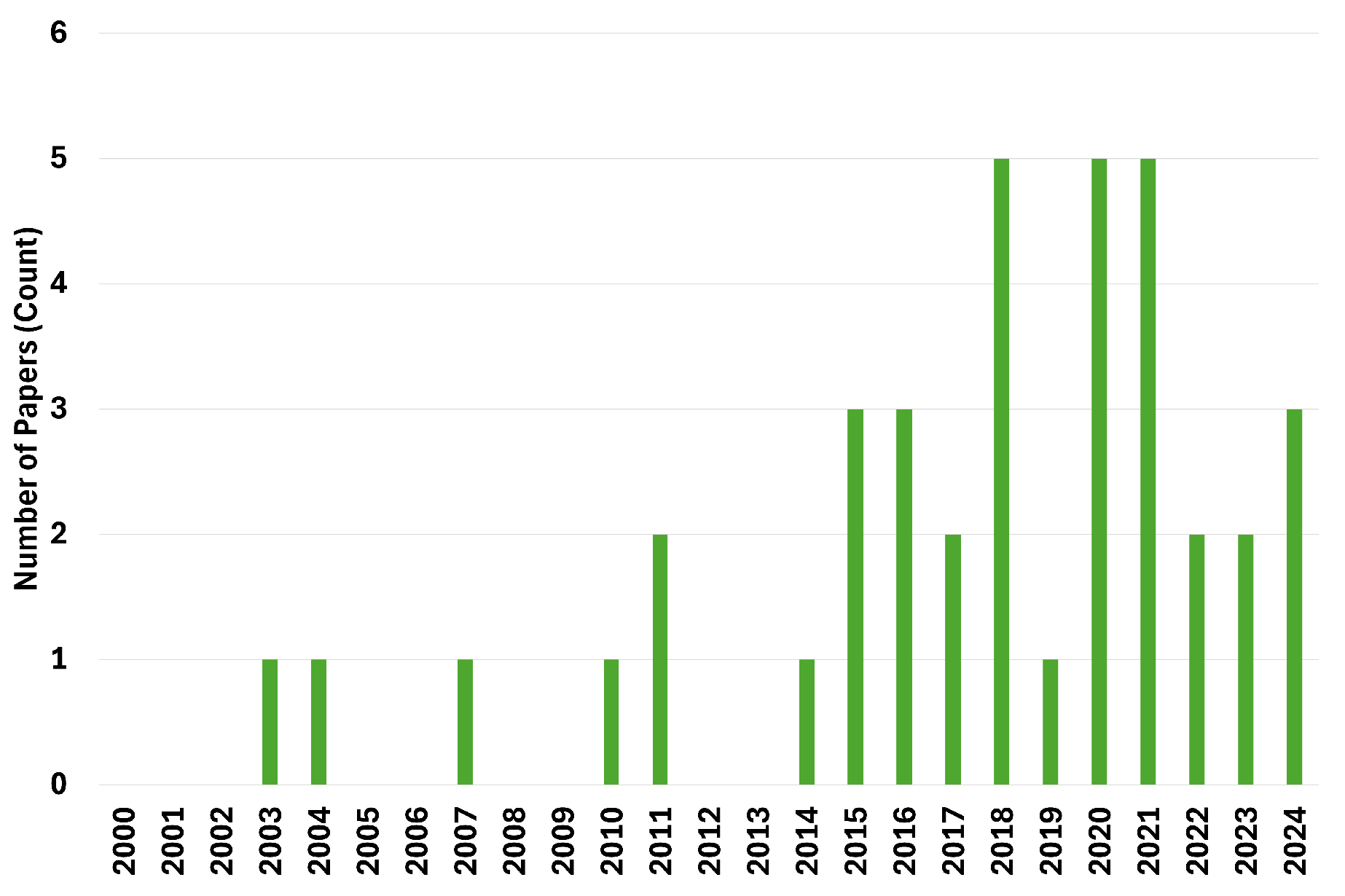
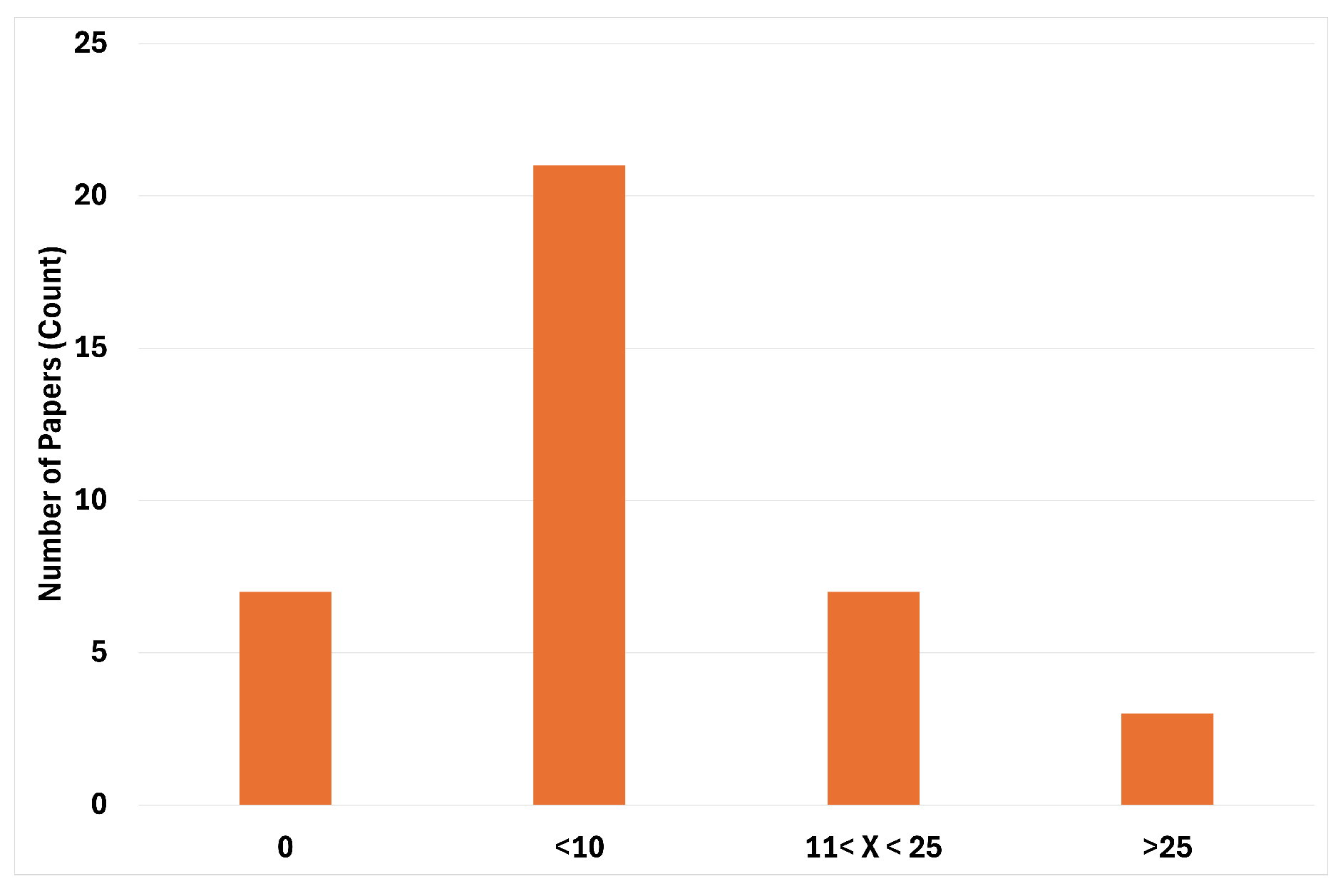
3. Deconstructing the Research Landscape
| Category | Paper(s) | Advantages | Limitations | Applications |
|---|---|---|---|---|
| Data-Driven Analysis | Wang Y.; Li F.; Hu J.; Zhuang D. | Correctly detects fraud users and creates mean index combinations for fraud recognition. | Classification of fraud is limited; sample size limited to one website and one cryptocurrency. | Fraud detection in P2P lending by identifying users with negative ratings. |
| Xu J.J.; Lu Y.; Chau M. | Potential use of many different methods and a unique dataset. | Work in progress, potential bias form sample bias - single platform China. | (Potential) Fraud detection in P2P lending using meta-learning and classification algorithms. | |
| Tsuchiya T.; Cuevas A.; Christin N. | Builds machine learning models to predict account suspension. | limited transferability across markets. | Predicting account suspension on P2P platforms. | |
| Chen Y.; Wang D. | Designs and analyzes the detailed design process of the prototype system of anti-fraud. | Needs more classifiers for AdaBoost. | Anti-fraud system design in P2P lending. | |
| Chengeta K.; Mabika E.R. | XGBoost, Deep Learning, and CatBoost performed better in classifying P2P lending defaults; identifies key parameters leading to loan defaults. | Suggest future work in quantum ML, cloud computing. | Classifying P2P lending defaults and identifying key risk factors. | |
| Wang H.; Wang Z.; Zhang B.; Zhou J. | Provides an overview of a data collection system for anti-fraud in P2P financial markets, addressing challenges like ActiveX controllers and JavaScript encryption. | Does not specify detailed validation methods. | Data collection for anti-fraud systems in P2P lending. | |
| Folino F.; Folino G.; Pontieri L. | Introduces an incremental learning framework for detecting deviant business process instances; demonstrates scalability with a distributed peer-to-peer architecture. | Performance can be improved. | Detecting deviant business process instances in P2P systems. | |
| Lu S.; Xu X.; Wang H.; Zhao J.; Wu Z. | Unsupervised learning approach to extract groups that exhibit potentially fraudulent behavior. | No advanced labels; relies on clustering methods. | Identifying potentially fraudulent groups in P2P lending. | |
| Wang H. | Study shows that standard ML methods yield quite good predictions (AUC > 0.780). | Fraudulent users and users with overdue payments are labeled, but it is not mentioned how; only features from transaction data; only Chinese market. | Fraud detection using standard ML methods. | |
| Xu J.J.; Chen D.; Chau M.; Li L.; Zheng H. | Empirical evidence of features that predict P2P loan fraud based on meaningful fraud labels. | Needs more borrower behavior features. | Predicting P2P loan fraud using various ML models. | |
| Yang B.; Garcia-Molina H. | Robust scheme that makes fraudulent behavior unattractive and protects against it. | No data (theoretical instance). | Preventing coin fraud using rule-based detection. | |
| Behavioral Analysis | Liu F.; You Y. | Leverages social network and consumption data. | Few ML models tested. | Fraud detection based on consumption behavior. |
| Islam M.M.; Sohag A.; Hasan M.; Islam M.K.; Sultan M.N. | Random Forest outperforms other algorithms; uses XAI tools to find the explainability of the datasets with the top-score model. | Models and explanations derived from this study are specific to the dataset used. | Fraud detection using behavioral data and explainable AI. | |
| Lai W. | Provides a new method that combines feature extraction with imbalanced data processing, and verifies the effectiveness of this combination. | Model robustness and applicability need further validation. | Fraud detection using imbalanced data processing. | |
| Fu X.; Zhang S.; Chen J.; Ouyang T.; Wu J. | It is helpful to use changes in investor sentiment to study trading volume; this data may provide important reference information for government and enterprises. | Precision and recall values still have room for improvement. | Using investor sentiment to detect fraud. | |
| Text Analysis | Li L.; Zhao T.; Xie Y.; Feng Y. | Mixes text method and theory from behavioral theory to not only detect but also try to explain why companies are fraudulent. | Only applies when there is a lot of text describing the company. | Fraud detection using text analysis and behavioral theory. |
| Network Analysis | Li Y.; Bu H.; Wu J. | Novel approach using company ownership structure. | Only Chinese firms, features are country specific. | Fraud detection using ego-network models. |
| Musau F.; Wang G.; Abdullahi M.B. | Model can deal with malicious attacks efficiently compared with existing models. | Reliance on simulations; real-world applicability and scalability need further validation. | Fraud detection using trust mechanisms and simulation techniques. | |
| Wang Q.; Liu Y. | Contributes a new approach to incorporating graph and text data for P2P lending fraud detection; demonstrates improved performance over existing methods. | The complexity of the attention mechanisms may require significant computational resources. | Fraud detection using graph attentive networks. | |
| Trust and Reputation Analysis | Acampora G.; Alghazzawi D.; Hagras H.; Vitiello A. | Proposes a new method (type-2 fuzzy logic) to evaluate reputation; aims at not only buyers but also sellers in the P2P environment. | No cross platform validation, lacks comparison with other methods. | Classifying fraudulent users in P2P environments using fuzzy logic. |
| Wang Y.; Yang J.; Qi L. | This model imitates real P2P platforms by allowing sellers to be of different types with type information unavailable to buyers. | Sample size; how steady-state equilibria can be approximately reached in a finite time. | Modeling P2P platforms using game theory. | |
| Pereira R.H.; Gonçalves M.J.A.; Coelho M.A.G.M. | Comprehensive framework in classification of fraud, methods, and validation techniques. | Theoretical, needs empirical development. | Theoretical discussion on fraud classification. | |
| Musau F.; Wang G.; Abdullahi M.B. | Reduces malicious behaviors by comparing | Simulation - based, assumes honest peers, scallability and generalisibility concerns | Trust model based on neighbor similarity |
| Category | Description |
| Basic Principles Covered | Includes Data-Driven Analysis, Behavioral Analysis, Text Analysis, Network Analysis, Trust and Reputation Analysis, Risk Assessment, Ensemble Methods, Feature Engineering, and Explainable AI (XAI). |
| Using ML (Yes) | k-means algorithm, logistic regression, Ego-network, Ad boost, random forest, meta-learning algorithm, decision trees, SVM, NN, text logistic regression, CNN LSTM, LIME model, type-2 fuzzy logic, Imbalance-XGBoost, XGBoost, NGBoost, AdaBoost GBDT, Graph Attentive Network model (FDNE), ensemble-based deviance detection model. |
| Using ML (No) | Analytic Hierarchy Process (AHP), game theory model, CFA and SEM analysis, trust mechanisms and simulation techniques, Cox Hazard Model, qualitative analysis, unsupervised learning and clustering, reputation models, collaborative filtering, auctions, social networking, rule-based detection (invariants). |
| Data-Driven Analysis | Wang Y.; Li F.; Hu J.; Zhuang D. (using k-means), Xu J.J.; Lu Y.; Chau M. (potential use of meta-learning), Tsuchiya T.; Cuevas A.; Christin N. (building ML models). Applications: Fraud detection in P2P lending, predicting account suspension, anti-fraud system design. |
| Behavioral Analysis | Liu F.; You Y. (using Random Forest), Islam M.M.; Sohag A.; Hasan M.; Islam M.K.; Sultan M.N. (using 10 ML algorithms), Lai W. (using Imbalance-XGBoost). Applications: Fraud detection based on consumption behavior, using behavioral data and explainable AI, using imbalanced data processing. |
| Text Analysis | Li L.; Zhao T.; Xie Y.; Feng Y. (using text logistic regression, SVM, CNN LSTM). Applications: Fraud detection using text analysis and behavioral theory. |
| Network Analysis | Li Y.; Bu H.; Wu J. (using logistic regression, Ego-network), Musau F.; Wang G.; Abdullahi M.B. (using trust mechanisms), Wang Q.; Liu Y. (using Graph Attentive Network model FDNE). Applications: Fraud detection using ego-network models, trust mechanisms, and graph attentive networks. |
| Trust and Reputation Analysis | Acampora G.; Alghazzawi D.; Hagras H.; Vitiello A. (using type-2 fuzzy logic), Wang Y.; Yang J.; Qi L. (using a game theory model), Li J.; Liu L.; Xu J. (using a Fuzzy-Rep model). Applications: Classifying fraudulent users using fuzzy logic, modeling P2P platforms using game theory, improving P2P e-commerce security. |
| Risk Assessment | Xie X.L. (using Analytic Hierarchy Process), Shen L.H.; Khan H.U.; Hammami H. (using CFA and SEM analysis), Li J.; Hsu S.; Chen Z.; Chen Y. (using Cox Hazard Model). Applications: Detecting fraud, understanding lenders’ perceptions, analyzing the relation among survival, interest rate, and capital. |
| Authors | Model/Method Used |
|---|---|
| Wang Y.; Li F.; Hu J.; Zhuang D. | k-means algorithm |
| Li Y.; Bu H.; Wu J. | logistic regression models, Ego-network, Ad boost, random forest |
| Xu J.J.; Lu Y.; Chau M. | meta-learning algorithm, decision trees, SVM, NN |
| Liu F.; You Y. | Random Forest |
| Li L.; Zhao T.; Xie Y.; Feng Y. | text logistic regression, SVM, CNN LSTM, decision tree, LIME model |
| Acampora G.; Alghazzawi D.; Hagras H.; Vitiello A. | type-2 fuzzy logic |
| Islam M.M.; Sohag A.; Hasan M.; Islam M.K.; Sultan M.N. | 10 well-known ML algorithms, four XAI tools (Random Forest outperforms) |
| Tsuchiya T.; Cuevas A.; Christin N. | random forest, gradient boosting |
| Lai W. | Imbalance-XGBoost, XGBoost, NGBoost, AdaBoost GBDT |
| Chen Y.; Wang D. | Ad Boost algorithm |
| Fu X.; Zhang S.; Chen J.; Ouyang T.; Wu J. | CNN |
| Chengeta K.; Mabika E.R. | supervised learning techniques, deep convolution neural networks (CNN), XGBoost, Deep Learning, CatBoost |
| Xu J.; Chen D.; Chau M. | Blacklisting, Random Forest (RF), Support Vector Machines (SVM) |
| Li J.; Liu L.; Xu J. | Fuzzy-Rep model, fuzzy logic |
| Wang H.; Wang Z.; Zhang B.; Zhou J. | Bayesian Networks, Logistic Regression, other machine learning techniques |
| Wang Q.; Liu Y. | Graph Attentive Network model called FDNE |
| Folino F.; Folino G.; Pontieri L. | ensemble-based deviance detection model (AODE and other classification algorithms) |
| Wang H. | supervised ML methods based on feature engineering, random forest, gradient boosting decision tree |
| Xu J.J.; Chen D.; Chau M.; Li L.; Zheng H. | random forest (RF), XGBoost (XGB), deep neural network (DNN), Long Short Term Memory (LSTM) neural network |
| Kim H.-J.; Jung J.J.; Jo G.-S. | cosine similarity, Recommend-Feedback-Re-recommend (RFR) algorithm |
| Yadav A.S.; Kushwaha D.S | (No specific model listed) |
| Xie X.L. | Analytic Hierarchy Process (AHP) |
| Wang Y.; Yang J.; Qi L. | game theory model |
| Pereira R.H.; Gonçalves M.J.A.; Coelho M.A.G.M. | (Theoretical discussion on ML methods) |
| Shen L.H.; Khan H.U.; Hammami H. | CFA and SEM analysis |
| Musau F.; Wang G.; Abdullahi M.B. | trust mechanisms and simulation techniques |
| Li J.; Hsu S.; Chen Z.; Chen Y. | Cox Hazard Model |
| Cekerevac Z.; Dvorak Z.; Prigoda L.; Cekerevac P. | (No specific model listed) |
| Chen D.; Deakin S.; Johnston A.; Wang B. | (Qualitative analysis) |
| Lu S.; Xu X.; Wang H.; Zhao J.; Wu Z. | Unsupervised learning, Minimum spanning tree extraction |
| Zhong Q.-Q.; Wei W.-H. | (No specific model listed) |
| Sundaresan N. | reputation models, collaborative filtering, auctions, social networking |
| Yang B.; Garcia-Molina H. | rule-based detection (invariants) |
4. The Role of AI in P2P Fraud Detection
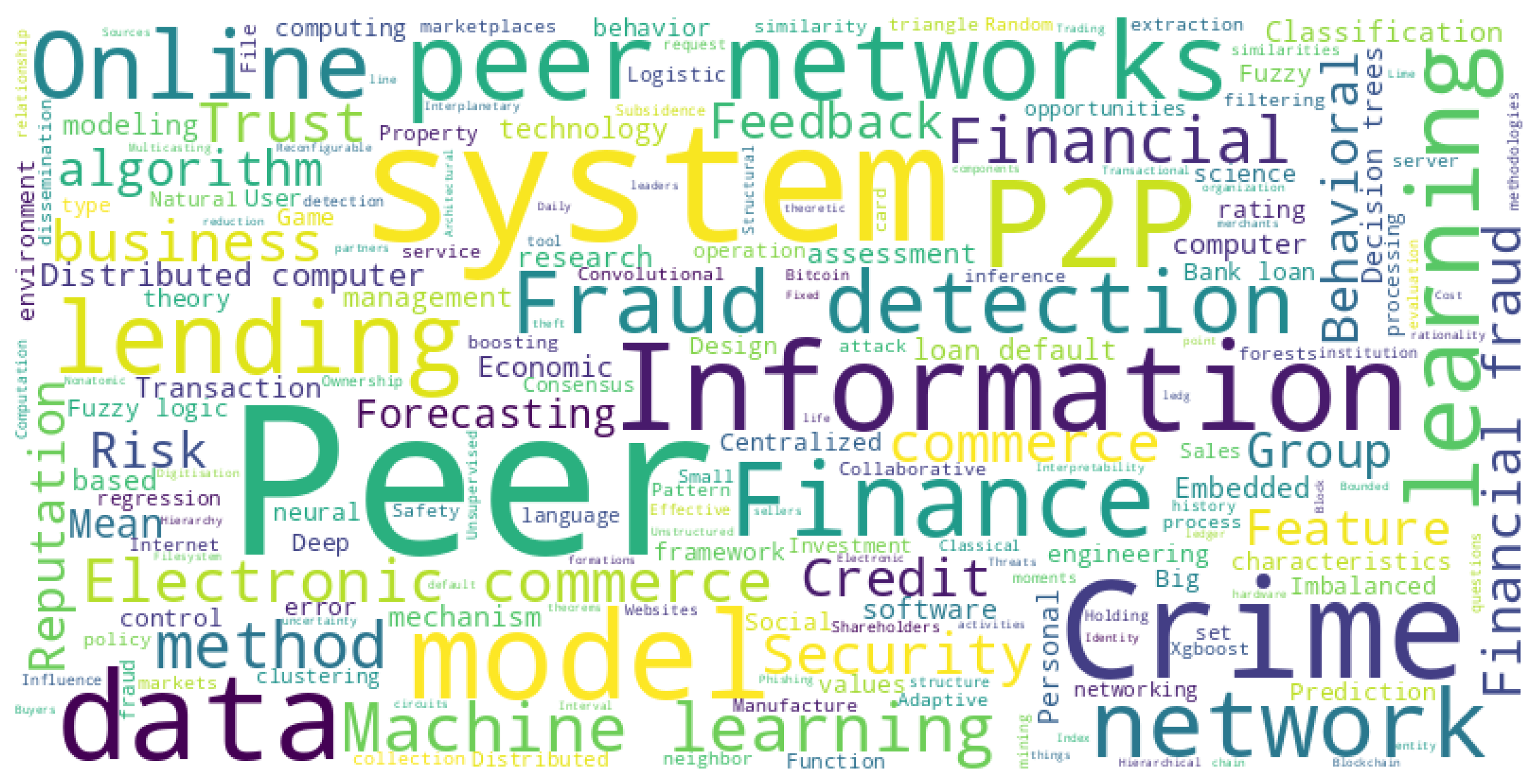
5. Predominant Themes in Literature
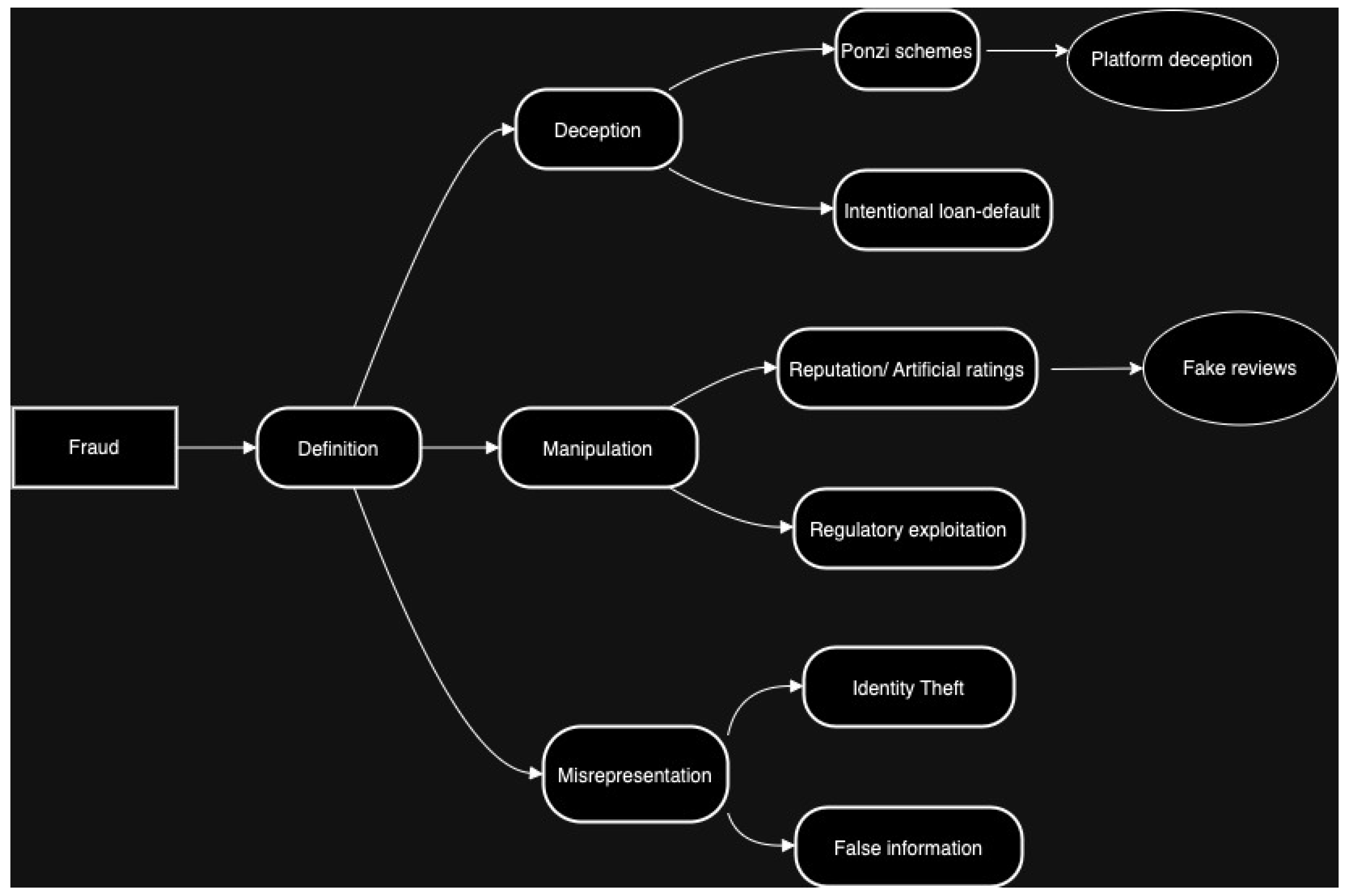
5.1. Defining Fraud in P2P Platforms
5.2. P2P Lending Platform and Fraud Divtersity
5.3. Big Data and ML/AI Solutions for P2P Fraud Detection
5.4. Evaluation Methods Analysis
6. Managerial Implications
7. Conclusion
7.1. Limitations and Future Recommendations
Acknowledgments
Appendix A
| Study Authors | Fraud definition? | Datasets sources | Label fraud? If so, how? | Fraud detection methods | ML methods used in the study | Validation methods used | Main contributions | Main limitations |
| (Wan 2018) | Defined as users with negative ratings. | Bitcoin Exchange (https://www.bitcoin-otc.com), 35,592 obs., 5,881 users. | Based on negative ratings. | Rating-based method. | k-means. | N/A | Combines different detection algorithms; accurate in identifying fraud. | Sample size limited to one website; may not generalize well. |
| (Li et al. 2020) | Fraud risk linked to failed companies. | Qichacha business database, WDZJ.com (2,107 platforms). | Based on company failure. | Logistic regression, Ego-networks. | Adaboost, Random Forest. | 10-fold cross-validation. | Regulatory tool for fraud detection in P2P lending firms. | Limited to Chinese data; difficult to apply globally. |
| (Xu et al. 2015) | Dictionary definition of fraud. | PPDai.com dataset. | Not yet labeled. | Meta-learning, decision trees, SVM, NN. | N/A | N/A | Proposes diverse methods; unique dataset. | Work-in-progress; more features needed for improvement. |
| (Liu and You 2020) | Differentiated by consumption behavior. | Consumption, social, and status datasets (346,920 obs.). | Based on consumption ratings (0-3). | Based on consumption types. | Random Forest. | Cross-validation. | Predicts fraud using social network and consumption data. | High-dimensional sample issues; more ML methods needed. |
| (Li et al. 2020) | Psychological fraud intentions more likely for companies with low-quality executive profiles | 4,554 P2P companies from the Home of Network Loan (https://www.wdzj.com). | Yes, based on the size of the extracted text. | Text models (NLP). | Logistic regression, SVM, CNN, LSTM. | Decision tree and LIME model. | Combines ML and behavioural theory to both detect and explain why companies are fraudulent. | Lacks depth on the validation methods. Only applicable when text describing the company is abundant. |
| (Acampora et al. 2016) | Reputation of buyers/sellers. | eBay-like datasets. | Based on eBay labels. | Type-2 fuzzy logic. | N/A | Comparison statistical procedures (e.g., Friedman test). | Proposes new method to evaluate reputation and detect fraud. | Needs testing on non-Ebay platforms; compare with other methods. |
| (Xie 2017) | Not explicitly defined. | N/A (theoretical model). | Based on features defined in the model. | Analytic Hierarchy Process (AHP). | N/A | N/A | Proposes features to consider for future fraud detection. | Theoretical; needs testing with real data. |
| (Wang et al. 2017) | Not directly defined; feedback system between sellers and buyers. | N/A (theoretical model). | Proportion of cheating sellers. | Reputation feedback systems. | Game theory model (non-atomic game setup). | Proof of lemma. | Models real P2P platforms with diverse seller types. | Needs realistic modeling of trader entries/exits. |
| (Pereira et al. 2023) | Deceptive practices undermining reputation systems. | Simulated data. | Based on various fraud types (e.g., Sybil attacks). | Systematic review. | Theoretical discussion on ML methods. | N/A | Classifies fraud, methods, and validation techniques. | Framework needs development. |
| (Shen et al. 2021) | Misrepresentation, Ponzi schemes, identity theft, platform misconduct. | Questionnaire survey. | Based on perceptions of trust and risk. | CFA, SEM analysis. | N/A | Identifies factors influencing P2P lending intentions. | Sample bias, limited scope, self-reporting data. | |
| (Musau et al. 2011) | Various deceptive practices in P2P e-commerce. | Simulated data. | Based on risk management techniques. | Trust model based on neighbor similarity. | N/A | Simulation experiments. | Reduces malicious behavior via neighbor similarity. | Simulated validation; scalability and generalizability concerns. |
| (Islam et al. 2024) | Behavioral fraud in P2P lending. | Online data on customer behavior. | Based on enterprise credit, residential status. | 10 ML algorithms with XAI tools. | Random Forest, SHAP, LIME. | Cross-validation (accuracy, precision, recall, F1). | Random Forest outperforms; highlights explainability. | Generalizability, transparency, explainability tool limitations. |
| (Tsuchiya et al. 2024) | Vendor deceptive practices. | Paxful, LocalCoinSwap platforms. | Based on scams, payment reversals, etc. | Various ML methods. | Random Forest, Gradient Boosting. | Cross-validation, confusion matrix, ROC, AUC. | High accuracy in predicting account suspension. | Limited transferability across markets. |
| (Lai 2023) | Deliberate actions deceiving lenders. | Lending Club platform dataset. | Based on false information, identity theft, payment evasion. | Imbalance-XGBoost, real-time monitoring. | XGBoost, NGBoost, AdaBoost, GBDT. | Cross-validation, confusion matrix, ROC, AUC. | Combines feature extraction with imbalanced data processing. | Robustness and applicability of models. |
| (Li et al. 2016) | Based on survival, interest rate, capital. | WDZJ.com platform data. | Not labeled as fraud. | Cox Hazard Model. | N/A | Log Likelihood. | Links capital increase with reduced fraud risk. | Limited access to national credit system data. |
| (Cekerevac et al. 2015) | Risks and benefits of Bitcoin use. | blockchain.info, MeasuringWorth.com. | Not labeled as fraud. | Not in scope. | N/A | N/A | Discusses Bitcoin’s risks and benefits. | Uncertainty about Bitcoin. |
| (Chen and Wang 2020) | Perceived from a mathematical perspective. | Multiple data sources (discrete/continuous data). | Based on individual characteristics. | AdaBoost algorithm. | N/A | System performance. | Designs a prototype anti-fraud system. | More classifiers needed for AdaBoost algorithm. |
| (Fu et al. 2019) | Misrepresentation or blind expansion by operators. | Sina Weibo, Baidu Post Bar, P2P info websites. | Based on positive/negative sentiment. | Text engineering. | CNN. | Precision, Recall, F1. | Uses investor sentiment for market prediction. | Precision and recall need improvement. |
| (Chengeta and Mabika 2021) | Based on loan status (defaulting/non-defaulting). | Prosper and Lending Club datasets. | Based on loan status. | Supervised learning (loan specifics). | XGBoost, Deep Learning, CatBoost. | TPR, ROC, FPR, MAE, F-measure, MCC, Recall, PRC. | Identifies key parameters for loan defaults. | Recommends quantum ML and cloud computing for future studies. |
| (Musau et al. 2014) | Dishonest negotiation, exploiting advantages. | Peer group data. | Based on risk management technique. | Trust mechanisms, neighborhood graph. | Various graph models. | Eigen Group Trust model comparison. | Efficiently handles malicious attacks. | Needs more research on social communities and game theory. |
| (Xu et al. 2016) | Misleading ratings, loan description, wrong info. | MyLending platform. | Based on learning, past performance, social networking, manipulation. | Blacklisting. | Random Forest, SVM. | Precision, F-measure. | Outperforms baseline features in detecting fraud. | Needs more features for borrower behavior and credibility. |
| (Li et al. 2010) | Vicious trust recommendation within P2P e-commerce | Simulated data, no external sources | No explicit labeling of data as "fraud" or "non-fraud"; trust is evaluated through the Fuzzy-Rep model. | Fuzzy-Rep model using direct trust, indirect reputation, fuzzy logic, and penalty mechanisms. | Fuzzy logic is the primary method used. | Validation through simulation experiments | Introduces a fuzzy logic-based reputation model to improve P2P e-commerce security. | Reliance on simulations; real-world applicability and scalability need further validation. |
| (Wang 2019) | Not directly mentioned, allusion to high fraud rate in Chinese P2P markets. | Data from various Chinese websites (e.g., People’s Bank of China, China Mobile) via web crawling. | No explicit fraud labels; data is used as input for anti-fraud processes. | Anti-fraud methods include feature engineering on collected data and applying machine learning-based prediction methods. | Bayesian Networks, Logistic Regression, etc. | Robustness and efficiency metrics for the data collection system. | Data collection system for anti-fraud in P2P financial markets, addressing challenges such as encryption. | Security measures on websites, complexity of maintaining up-to-date crawlers, technical limitations of current tools. |
| (Li et al. 2021) | "Runaway" platforms: shutting down, losing contact, or being involved in economic crimes. | Scraped data on Chinese P2P-lending platforms (2007- 2016): company information, news, announcements, etc. | Platforms are labeled as "runaways" based on conditions such as stopping business, website shutdown, fraud, etc. | Regression analysis on the relationship between business friendliness, law enforcement, and P2P platform runaways. | Statistical regression models. | Statistical relation between predictive variables and incidence of P2P runaways. | Established link between business-friendly policies, weak law enforcement and higher rates of P2P platform failures. | Potential measurement biases in the business friendliness index and the generalizability of the results to other contexts. |
| (Teichmann et al. 2024) | Fake loans or identity theft. | Data scraped from various P2P platforms, primarily focused on Chinese markets. | Fraudulent loans are labeled based on government reports and news announcements. | Logistic regression and support vector machines (SVM). | Logistic regression, SVM. | ROC curves, confusion matrices for validation. | Combines financial and textual data to predict fraudulent behavior in platforms. | Focus on the Chinese market limits global applicability. |
| (Wang and Liu 2015) | Fraudulent transactions or failures of P2P platforms. | Data collected through web scraping and official records from several platforms. | Platforms are labeled based on transaction anomalies and failures. | Decision trees, support vector machines (SVM), and random forests. | Decision trees, SVM, random forests. | Cross-validation, precision, recall, F1-scores. | Proposes new decision tree approaches for fraud detection. | Lack of scalability and complexity in global markets. |
| (Wang et al. 2020) | Identity theft and false reporting. | Data from various Chinese platforms using scraped information on user activities. | Labels based on false user identities and reports. | Supervised learning approaches with a focus on detecting behavioral anomalies. | Random Forest, XGBoost. | Precision, recall, F1-scores, ROC curves. | Identifies key behavioral patterns leading to fraudulent activities. | Relies on Chinese datasets; needs validation in broader markets. |
| (Chen et al. 2021) | False reporting and loan defaults. | Data scraped from Chinese P2P platforms, focusing on loan requests and repayment histories. | Labeled based on loan defaults and repayment fraud. | Supervised learning models for fraud detection in loan data. | XGBoost, Random Forest. | Cross-validation, ROC curves, AUC scores. | High accuracy in predicting fraudulent behavior in loan requests. | Limited to the Chinese market; may not be applicable elsewhere. |
| (Folino et al. 2018) | False reporting and loan defaults. | Data from LendingClub and Prosper, focused on default patterns. | Labels based on loan defaults. | Supervised ML approaches, decision trees, ensemble methods. | Decision trees, Random Forest. | Precision, recall, F1-scores, AUC curves. | Highlights the role of ensemble methods in improving fraud detection accuracy. | Needs further exploration in non-lending platforms. |
| (Lu et al. 2018) | Not directly defined; Ponzi scheme mentioned. | WDZJ.com platform data (March 2016-February 2017). | No advanced labels; clustering method. | Unsupervised learning. | Minimum spanning tree extraction. | Distance metric. | Clusters applicants for potential fraudulent behavior. | No explicit fraud labels; systemic metrics not used. |
| (Zhong and Wei 2011) | Misrepresentation of creditworthiness. | N/A (theoretical work). | Misrepresentation of creditworthiness. | N/A | N/A | Authenticity, robustness, efficiency. | Efficient communication protocol; prevents fraud. | Theoretical work, needs real-world application. |
| (Wang 2019) | Identity theft and overdue payments. | HC Financial Group, 60K overdue payments, 50K fraud users. | Fraudulent/overdue users labeled, unclear how. | Supervised ML methods. | Random Forest, Gradient Boosting. | AUC. | Good predictions (AUC > 0.780). | Feature engineering needed; no deep learning. |
| (Xu et al. 2022) | Deliberate creation of fraudulent loan requests. | EasyLoans dataset (June 2007-December 2014). | Blacklisted in EasyLoans database. | Based on borrower features. | Random Forest, XGBoost, DNN, LSTM. | F1 Measure, AUC. | Identifies key features predicting P2P loan fraud. | Limited to Chinese market data. |
| (Sundaresan 2007) | Proxied through trust/reputation. | N/A | Trust and reputation as proxies. | Reputation models, collaborative filtering. | Collaborative filtering. | Circles of trust, degrees of freedom. | Overview of trust/reputation as fraud proxies. | Introductory tutorial; lacks real content. |
| (Kim et al. 2004) | Fraudulent ratings. | MovieLens dataset. | Fraudulent ratings based on collaborative filtering. | RFR algorithm (recommendation-based). | Cosine similarity clustering. | F1 Measure, MAE. | Enhances robustness with collaborative filtering. | Poor performance at higher fraud rates. |
| (Yang and Garcia-Molina 2003) | Coin fraud: replication, denial of assignment, double spending. | N/A (theoretical instance). | Coin fraud defined as per description. | Rule-based detection (invariants). | N/A | Credit loss. | Robust scheme against fraudulent behavior. | Theoretical work; needs real-world application. |
References
- Morse, A. Peer-to-peer crowdfunding: Information and the potential for disruption in consumer lending. Annual Review of Financial Economics 2015, 7, 463–482.
- Xu, J.J.; Chen, D.; Chau, M.; Li, L.; Zheng, H. Peer-to-Peer Loan Fraud Detection: Constructing Features from Transaction Data. MIS Quarterly: Management Information Systems 2022, 46, 1777 – 1792. Cited by: 6, . [CrossRef]
- Bello, H.O.; Idemudia, C.; Iyelolu, T.V. Integrating machine learning and blockchain: Conceptual frameworks for real-time fraud detection and prevention. World Journal of Advanced Research and Reviews 2024, 23, 056–068.
- Hassan, M.; Aziz, L.A.R.; Andriansyah, Y. The role artificial intelligence in modern banking: an exploration of AI-driven approaches for enhanced fraud prevention, risk management, and regulatory compliance. Reviews of Contemporary Business Analytics 2023, 6, 110–132.
- Wu, Y.; Xie, Z.; Ji, S.; Liu, Z.; Zhang, X.; Lin, C.; Deng, S.; Zhou, J.; Wang, T.; Beyah, R. Fraud-agents detection in online microfinance: a large-scale empirical study. IEEE Transactions on Dependable and Secure Computing 2022, 20, 1169–1185.
- Jayathilaka, H.; Krintz, C.; Wolski, R. Detecting performance anomalies in cloud platform applications. IEEE Transactions on Cloud Computing 2018, 8, 764–777.
- Xu, J.J.; Lu, Y.; Chau, M. P2P lending fraud detection: A big data approach. In Proceedings of the Intelligence and Security Informatics: Pacific Asia Workshop, PAISI 2015, Ho Chi Minh City, Vietnam, May 19, 2015. Proceedings. Springer, 2015, pp. 71–81.
- Xu, J.; Chen, D.; Chau, M. Identifying features for detecting fraudulent loan requests on P2P platforms. In Proceedings of the 2016 IEEE Conference on Intelligence and Security Informatics (ISI). IEEE, 2016, pp. 79–84.
- Wenzlaff, K.; Odorović, A.; Riethmüller, T.; Wambold, P. On the merits of the Key Investment Information Sheet in the ECSPR. In Regulation on European Crowdfunding Service Providers for Business; Elgar commentaries in financial law series, Edward Elgar Publishing: Northampton, 2022; p. 310.
- Alibrandi, A.S.; Grossule, E. Crowdfunding and consumer credit protection in the EU. In Regulation on European Crowdfunding Service Providers for Business; Edward Elgar Publishing, 2022; pp. 591–606. Section: Regulation on European Crowdfunding Service Providers for Business.
- Louisse, M. Due diligence of project owners (Art 5). In Regulation on European Crowdfunding Service Providers for Business; Edward Elgar Publishing, 2022; pp. 105–112. Section: Regulation on European Crowdfunding Service Providers for Business.
- Ferretti, R. Individual portfolio management of loans (Art 6). In Regulation on European Crowdfunding Service Providers for Business; Edward Elgar Publishing, 2022; pp. 113–129. Section: Regulation on European Crowdfunding Service Providers for Business.
- Cumming, D.; Hornuf, L.; Karami, M.; Schweizer, D. Disentangling crowdfunding from fraudfunding. Journal of Business Ethics 2021, pp. 1–26.
- Machado, M.; Coita, I.F.; Bolesta, K.; Filipovska, O.; van Heeswijk, W.; Muñiz, J.A.; Bernard, F.S.; Osterrieder, J. What do we Know About Fraud Detection in Peer-to-Peer Lending? A Systematic Literature Review. A Systematic Literature Review (September 06, 2024) 2024.
- Liu, Y.; Baals, L.J.; Osterrieder, J.; Hadji-Misheva, B. Network centrality and credit risk: A comprehensive analysis of peer-to-peer lending dynamics. Finance Research Letters 2024, 63, 105308.
- Agarwal, S.; Zhang, J. FinTech, lending and payment innovation: A review. Asia-Pacific Journal of Financial Studies 2020, 49, 353–367.
- Varsha, P.; Chakraborty, A.; Kar, A.K. How to undertake an impactful literature review: Understanding review approaches and guidelines for high-impact systematic literature reviews. South Asian Journal of Business and Management Cases 2024, 13, 18–35.
- Amato, A.; Osterrieder, J.R.; Machado, M.R. How can artificial intelligence help customer intelligence for credit portfolio management? A systematic literature review. International Journal of Information Management Data Insights 2024, 4, 100234.
- Kushwaha, A.K.; Kar, A.K.; Dwivedi, Y.K. Applications of big data in emerging management disciplines: A literature review using text mining. International Journal of Information Management Data Insights 2021, 1, 100017.
- Ngai, E.W.; Xiu, L.; Chau, D.C. Application of data mining techniques in customer relationship management: A literature review and classification. Expert systems with applications 2009, 36, 2592–2602.
- Xu, J.J.; Lu, Y.; Chau, M. P2P lending fraud detection: A big data approach. Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) 2015, 9074, 71 – 81. Cited by: 18, . [CrossRef]
- Liu, F.; You, Y. A big data-based anti-fraud model for internet finance. Revue d’Intelligence Artificielle 2020, 34, 501 – 506. Cited by: 2; All Open Access, Bronze Open Access, . [CrossRef]
- Chen, Y.; Wang, D. Research on anti-Financial fraud Technology based on Machine learning. Proceedings - 2020 2nd International Conference on Information Technology and Computer Application, ITCA 2020 2020, p. 105 – 108. Cited by: 0, . [CrossRef]
- Pereira, R.H.; Gonçalves, M.J.A.; Coelho, M.A.G.M. Reputation Systems: A framework for attacks and frauds classification. Journal of Information Systems Engineering and Management 2023, 8. Cited by: 2; All Open Access, Gold Open Access, . [CrossRef]
- Wang, H. Detection of fraudulent users in P2P financial market. arXiv preprint arXiv:1910.02010 2019.
- Li, Y.; Bu, H.; Wu, J. Identifying P2P Lending Frauds Based on Ownership Structure. Proceedings of the IEEE International Conference on Software Engineering and Service Sciences, ICSESS 2020, 2020-October, 250 – 253. Cited by: 2, . [CrossRef]
- Teichmann, F.M.J.; Boticiu, S.R.; Sergi, B.S. Compliance concerns in sustainable finance: an analysis of peer-to-peer (P2P) lending platforms and sustainability. Journal of Financial Crime 2024, 31, 993 – 1001. [CrossRef]
- Yadav, P.; Bhosale, R.; Sahoo, R.; Khanzode, V.; Tiwari, M.K. Advances in Air Cargo Financing Using a Consortium Blockchain. IFAC-PapersOnLine 2022, 55, 737–742.
- Acampora, G.; Alghazzawi, D.; Hagras, H.; Vitiello, A. An interval type-2 fuzzy logic based framework for reputation management in Peer-to-Peer e-commerce. Information Sciences 2016, 333, 88 – 107. Cited by: 37; All Open Access, Green Open Access, . [CrossRef]
- Wang, Y.; Yang, J.; Qi, L. A game-theoretic model for the role of reputation feedback systems in peer-to-peer commerce. International Journal of Production Economics 2017, 191, 178 – 193. Cited by: 9, . [CrossRef]
- Folino, F.; Folino, G.; Pontieri, L. An ensemble-based P2P framework for the detection of deviant business process instances. Proceedings - 2018 International Conference on High Performance Computing and Simulation, HPCS 2018 2018, p. 122 – 129. Cited by: 5, . [CrossRef]
- Zhong, Q.Q.; Wei, W.H. A credit model on P2P network based on comments group. Proceedings - International Conference on Machine Learning and Cybernetics 2011, 1, 344 – 347. Cited by: 0, . [CrossRef]
- Lai, W. Default Prediction of Internet Finance Users Based on Imbalance-XGBoost. Tehnicki Vjesnik 2023, 30, 779 – 786. Cited by: 2; All Open Access, Gold Open Access, . [CrossRef]
- Xu, J.; Chen, D.; Chau, M. Identifying features for detecting fraudulent loan requests on P2P platforms. IEEE International Conference on Intelligence and Security Informatics: Cybersecurity and Big Data, ISI 2016 2016, p. 79 – 84. Cited by: 15, . [CrossRef]
- Tsuchiya, T.; Cuevas, A.; Christin, N. Identifying Risky Vendors in Cryptocurrency P2P Marketplaces. WWW 2024 - Proceedings of the ACM Web Conference 2024, p. 99 – 110. Cited by: 0, . [CrossRef]
- Beekun, R.; Hamdy, R.; Westerman, J.; Hassabelnaby, H. An Exploration of Ethical Decision-making Processes in the United States and Egypt. Journal of Business Ethics 2008, 82, 587–605. [CrossRef]
- Li, J.; Liu, L.; Xu, J. A P2P e-commerce reputation model based on fuzzy logic. Proceedings - 10th IEEE International Conference on Computer and Information Technology, CIT-2010, 7th IEEE International Conference on Embedded Software and Systems, ICESS-2010, ScalCom-2010 2010, p. 1275 – 1279. Cited by: 7, . [CrossRef]
- Chengeta, K.; Mabika, E.R. Peer to Peer Social Lending Default Prediction with Convolutional Neural Networks. icABCD 2021 - 4th International Conference on Artificial Intelligence, Big Data, Computing and Data Communication Systems, Proceedings 2021. Cited by: 3, . [CrossRef]
- Li, L.; Zhao, T.; Xie, Y.; Feng, Y. Interpretable Machine Learning Based on Integration of NLP and Psychology in Peer-to-Peer Lending Risk Evaluation. Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) 2020, 12431 LNAI, 429 – 441. Cited by: 2, . [CrossRef]
- Islam, M.M.; Sohag, A.; Hasan, M.; Islam, M.K.; Sultan, M.N. XAI-Driven Model Explainability and Prediction of P2P Bank Loan Default Network. Lecture Notes in Networks and Systems 2024, 867 LNNS, 109 – 121. Cited by: 0, . [CrossRef]
- Li, J.; Hsu, S.; Chen, Z.; Chen, Y. Risks of P2P Lending Platforms in China: Modeling Failure Using a Cox Hazard Model. Chinese Economy 2016, 49, 161 – 172. Cited by: 27, . [CrossRef]
- Cekerevac, Z.; Dvorak, Z.; Prigoda, L.; Cekerevac, P. Risks of bitcoin virtual currency. Communications - Scientific Letters of the University of Žilina 2015, 17, 93 – 98. Cited by: 1.
- Fu, X.; Zhang, S.; Chen, J.; Ouyang, T.; Wu, J. A Sentiment-Aware Trading Volume Prediction Model for P2P Market Using LSTM. IEEE Access 2019, 7, 81934 – 81944. Cited by: 16; All Open Access, Gold Open Access, . [CrossRef]
- Wang, Q.; Liu, H.; He, J.; Du, X. A graph attentive network model for P2P lending fraud detection. Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) 2020, 12274 LNAI, 316 – 327. Cited by: 2, . [CrossRef]
- Chen, D.; Deakin, S.; Johnston, A.; Wang, B. Too Much Technology and Too Little Regulation? The Spectacular Demise of P2P Lending in China. Accounting, Economics and Law: A Convivium 2021. Cited by: 7; All Open Access, Green Open Access, Hybrid Gold Open Access, . [CrossRef]
- Li, M.; Phan, P.H.; Sun, X. Business friendliness: A double-edged sword. Sustainability (Switzerland) 2021, 13, 1 – 22. Cited by: 0; All Open Access, Gold Open Access, . [CrossRef]
- Xu, J.J.; Chen, D.; Chau, M.; Li, L.; Zheng, H. PEER-TO-PEER LOAN FRAUD DETECTION: CONSTRUCTING FEATURES FROM TRANSACTION DATA. MIS quarterly 2022, 46.
- Lo, T.W.; Kan, W.S. How to win trust: The case of P2P financial fraud in China. Journal of Criminology 2023, 56, 116–135.
- Shen, L.H.; Khan, H.U.; Hammami, H. An empirical study of lenders’ perception of Chinese online peer-to-peer (P2P) lending platforms. Journal of Alternative Investments 2021, 23, 152 – 175. Cited by: 7, . [CrossRef]
- K-means algorithm for recognizing fraud users on a bitcoin exchange platform, Vol. 2018-December, 2018. Cited by: 2.
- Musau, F.; Wang, G.; Abdullahi, M.B. Group formation with neighbor similarity trust in P2P E-commerce. Proc. 10th IEEE Int. Conf. on Trust, Security and Privacy in Computing and Communications, TrustCom 2011, 8th IEEE Int. Conf. on Embedded Software and Systems, ICESS 2011, 6th Int. Conf. on FCST 2011 2011, p. 835 – 840. Cited by: 7, . [CrossRef]
- Musau, F.; Wang, G.; Abdullahi, M.B. Group formation with neighbor similarity trust in P2P E-commerce. Peer-to-Peer Networking and Applications 2014, 7, 295 – 310. Cited by: 6, . [CrossRef]
- Wang, Q.; Liu, Y. The research on the peer-to-peer trust model under the internet financial environment. Computing, Control, Information and Education Engineering - Proceedings of the 2015 2nd International Conference on Computer, Intelligent and Education Technology, CICET 2015 2015, p. 745 – 748. Cited by: 0, . [CrossRef]
- Sundaresan, N. Online trust and reputation systems. EC’07 - Proceedings of the Eighth Annual Conference on Electronic Commerce 2007, p. 366 – 367. Cited by: 19, . [CrossRef]
- Raghavan, P.; El Gayar, N. Fraud detection using machine learning and deep learning. In Proceedings of the 2019 international conference on computational intelligence and knowledge economy (ICCIKE). IEEE, 2019, pp. 334–339.
- Al-dahasi, E.M.; Alsheikh, R.K.; Khan, F.A.; Jeon, G. Optimizing fraud detection in financial transactions with machine learning and imbalance mitigation. Expert Systems 2024, p. e13682.
- Cirqueira, D.; Helfert, M.; Bezbradica, M. Towards design principles for user-centric explainable AI in fraud detection. In Proceedings of the International Conference on Human-Computer Interaction. Springer, 2021, pp. 21–40.
- Gade, K.; Geyik, S.C.; Kenthapadi, K.; Mithal, V.; Taly, A. Explainable AI in industry. In Proceedings of the Proceedings of the 25th ACM SIGKDD international conference on knowledge discovery & data mining, 2019, pp. 3203–3204.
- Malik, E.F.; Khaw, K.W.; Belaton, B.; Wong, W.P.; Chew, X. Credit card fraud detection using a new hybrid machine learning architecture. Mathematics 2022, 10, 1480.
- Pourhabibi, T.; Ong, K.L.; Kam, B.H.; Boo, Y.L. Fraud detection: A systematic literature review of graph-based anomaly detection approaches. Decision Support Systems 2020, 133, 113303.
- Esenogho, E.; Mienye, I.D.; Swart, T.G.; Aruleba, K.; Obaido, G. A neural network ensemble with feature engineering for improved credit card fraud detection. IEEE Access 2022, 10, 16400–16407.
- Chai, C.; Cao, L.; Li, G.; Li, J.; Luo, Y.; Madden, S. Human-in-the-loop outlier detection. In Proceedings of the Proceedings of the 2020 ACM SIGMOD international conference on management of data, 2020, pp. 19–33.
- Xie, X.L. Creditability assessment of dealers in P2P e-commerce. Proceedings of 2016 IEEE Advanced Information Management, Communicates, Electronic and Automation Control Conference, IMCEC 2016 2017, p. 1326 – 1333. Cited by: 1, . [CrossRef]
- Lu, S.; Xu, X.; Wang, H.; Zhao, J.; Wu, Z. Detecting Systemically Important Platforms in P2P Market of China. 2018 15th International Conference on Service Systems and Service Management, ICSSSM 2018 2018. Cited by: 0, . [CrossRef]
- Kim, H.J.; Jung, J.J.; Jo, G.S. Conceptual framework for recommendation system based on distributed user ratings. Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) 2004, 3032, 115 – 122. Cited by: 9, . [CrossRef]
- Yang, B.; Garcia-Molina, H. PPay: Micropayments for peer-to-peer systems. Proceedings of the ACM Conference on Computer and Communications Security 2003, p. 300 – 310. Cited by: 174.
| 1 |
| Criteria | Decision |
| Inclusion of pre-defined keywords in title, abstract, or keyword list | Inclusion |
| Article publication in a scientific journal | Inclusion |
| Article written in English | Inclusion |
| Duplicates of an original article | Exclusion |
| Relevance of abstract, title, and content to research objective | Exclusion |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).





