Submitted:
14 July 2025
Posted:
15 July 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background
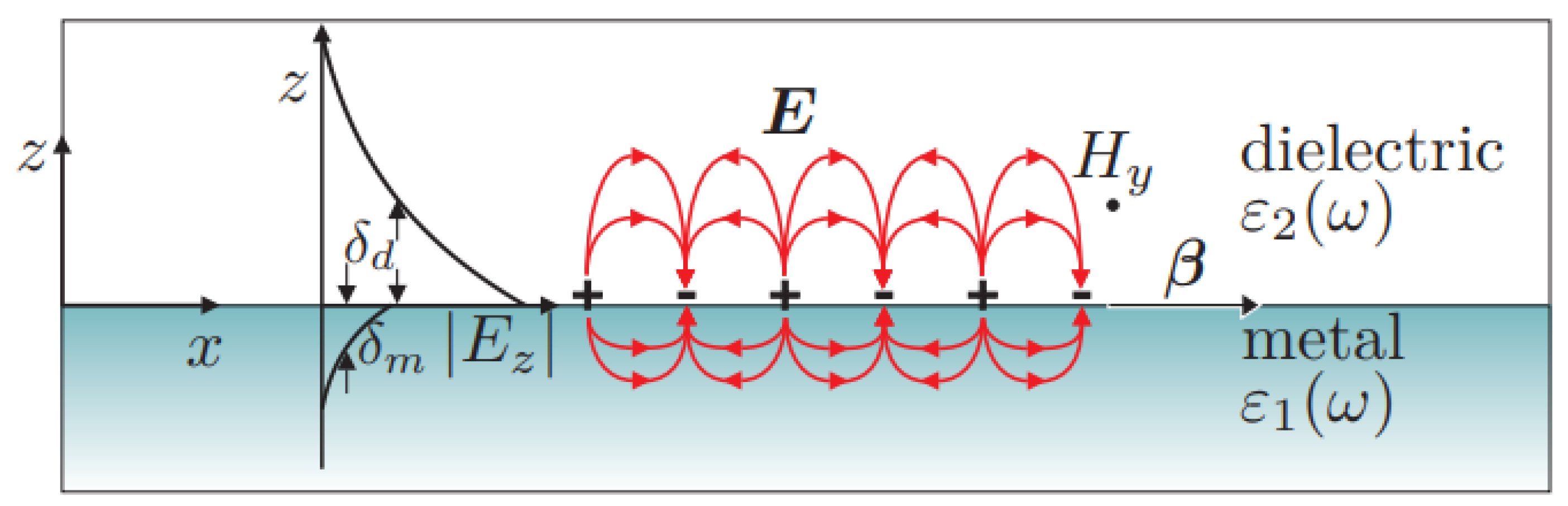
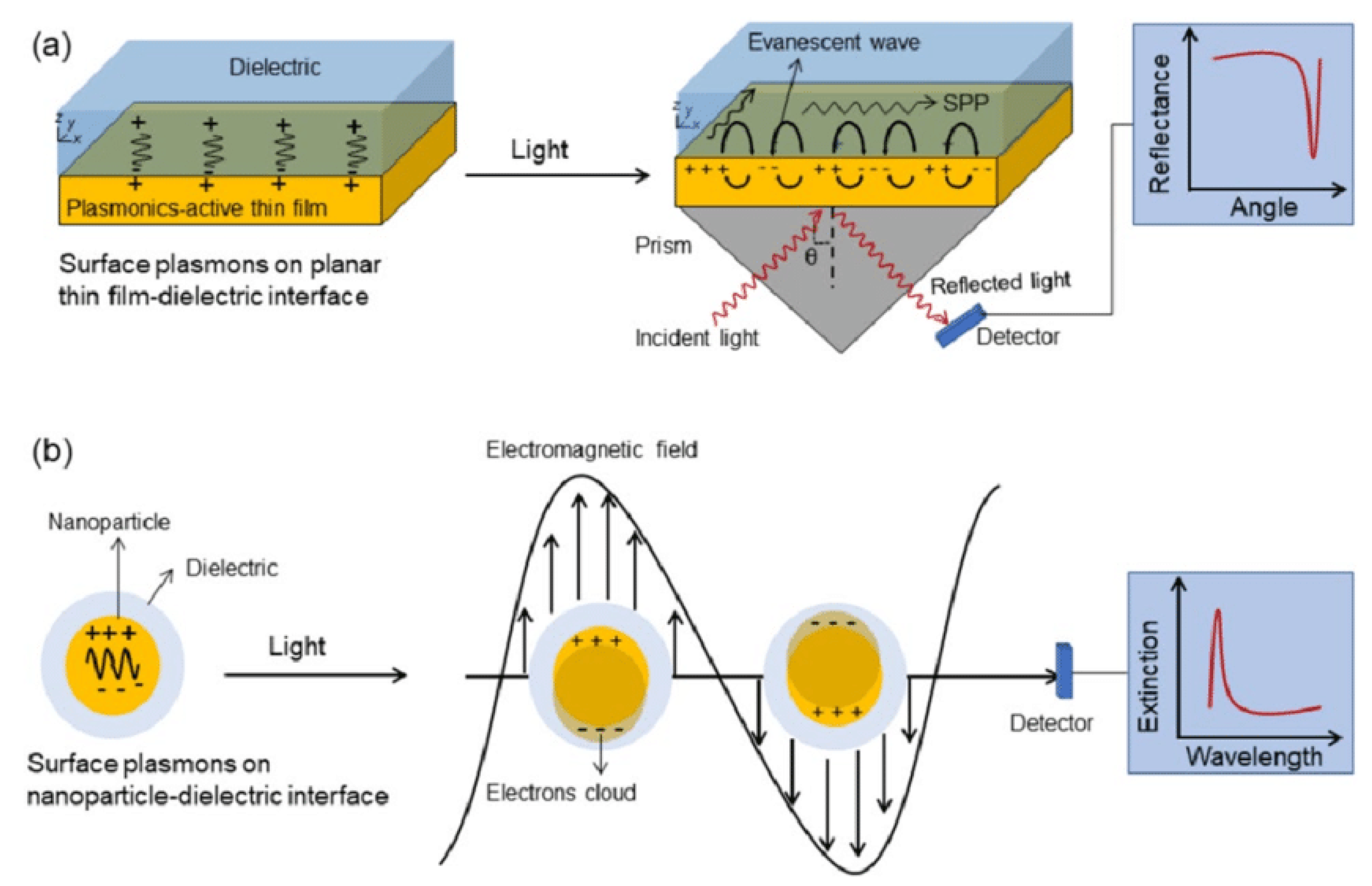
2.1. Nanoantennas in Wireless Communications
2.2. Security in Wireless Communication
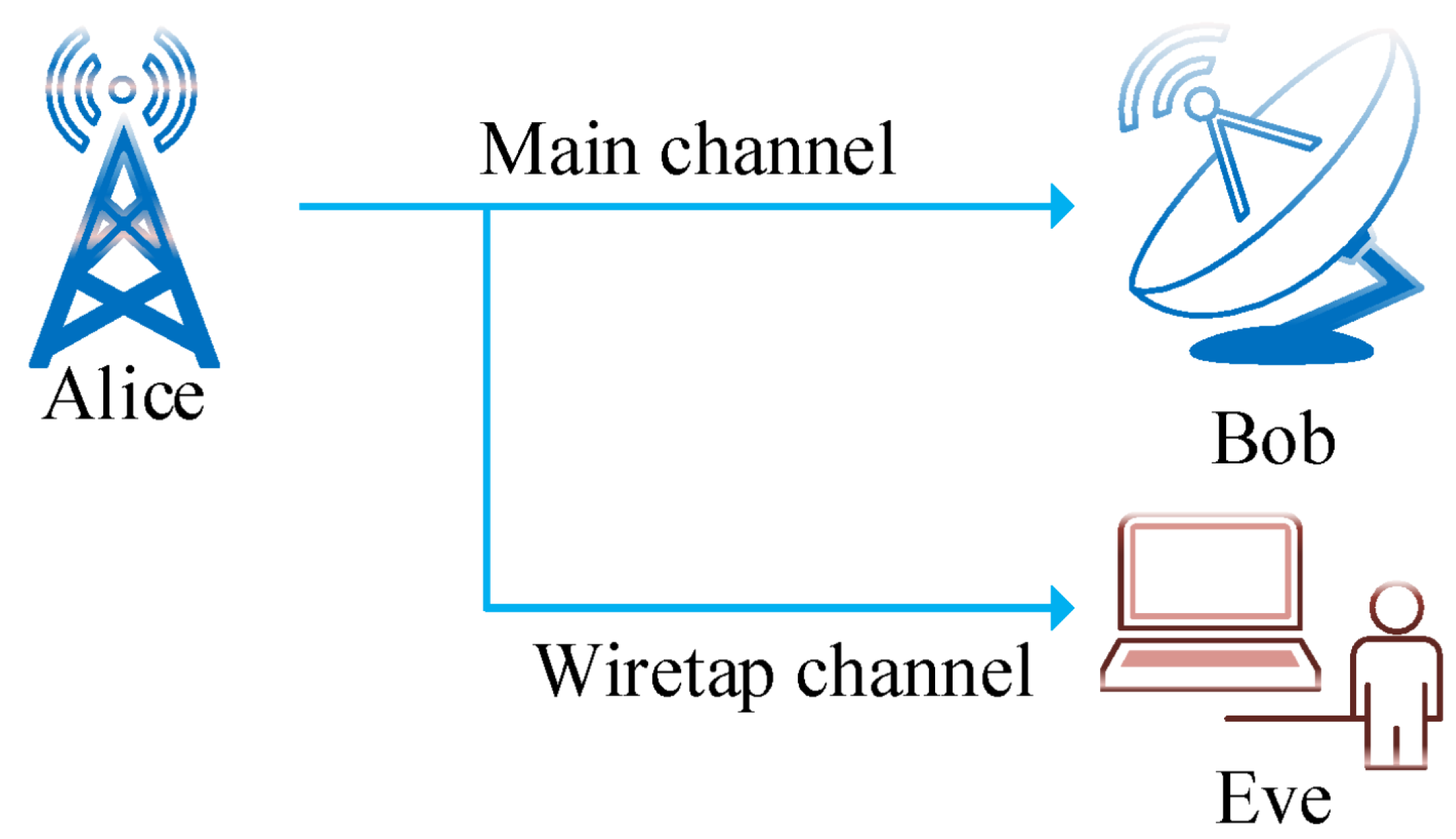
2.2.1. Physical Layer Security
3. Related Work
3.1. Electromagnetic Analysis for Cryptography
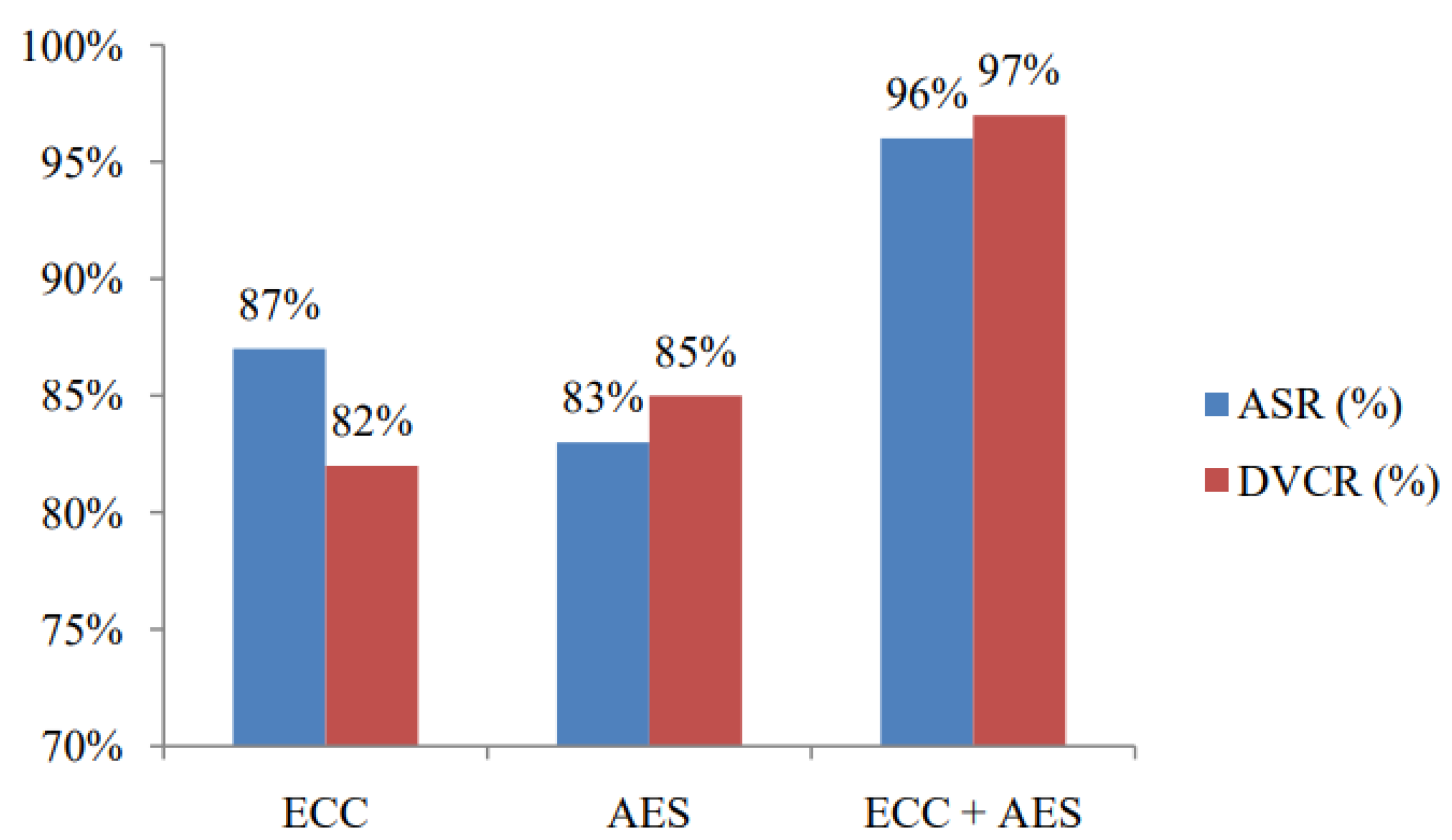
3.2. Knapsack Encryption with Elliptic Curve Cryptography (ECC) Based Secured Wireless Network
3.3. Elevating Security Using ECC and Advanced Encryption Standard (AES) Algorithms
4. Proposed Model
-
Block 1 – Nanoantenna Response Characterization:The process initiates with the design and full-wave modeling of a nanoantenna, developed from fundamental principles. The structure will be used to amplify the signal transmitted.
-
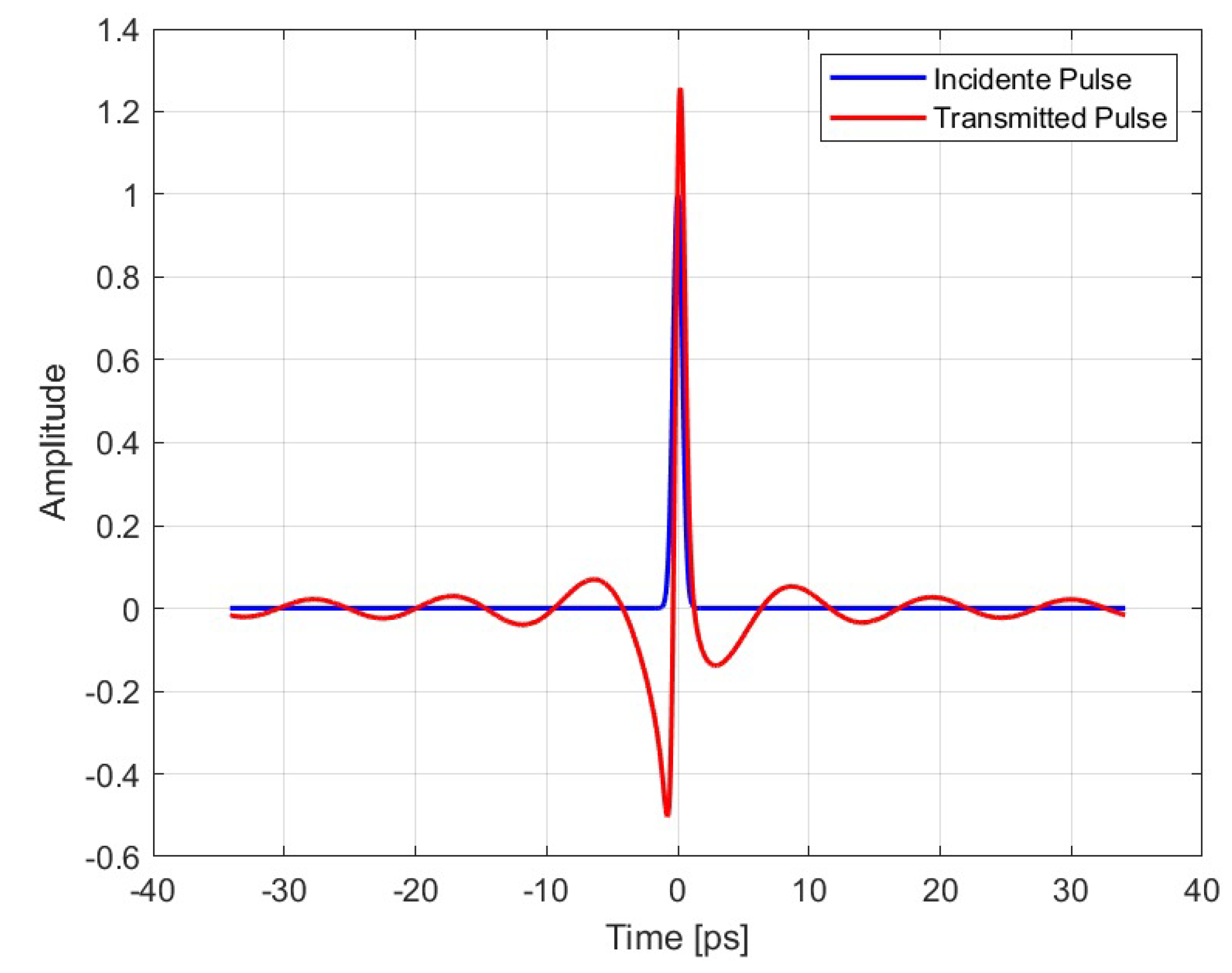
Block 2 – Signal Quantization and Error Correction:The electromagnetic response at the output of the nanoantenna is captured, normalized, and quantized, resulting in a digital bitstream. Subsequently, the stream undergoes processing by an error correction module that is based on Hamming (8,12) coding. This coding provides resilience against transmission errors.
-
Block 3 – Pseudo-Random Key Generation and Bitwise Encryption:A pseudo-random key is generated, and a bitwise encryption is performed using the XOR operation, ensuring basic confidentiality and resistance to statistical attacks.
-
Block 4 – Arnold Transform Encryption:In order to achieve enhanced cryptographic robustness, the encrypted bitstream undergoes an Arnold Transform, thereby introducing an additional layer of security based on permutations.
-
Block 5 – Signal Recovery at the Receiver:The receiver module is responsible for implementing the inverse operations, with the objective of recovering and reconstructing the original signal. This process is integral to the completion of the secure communication process from end to end.
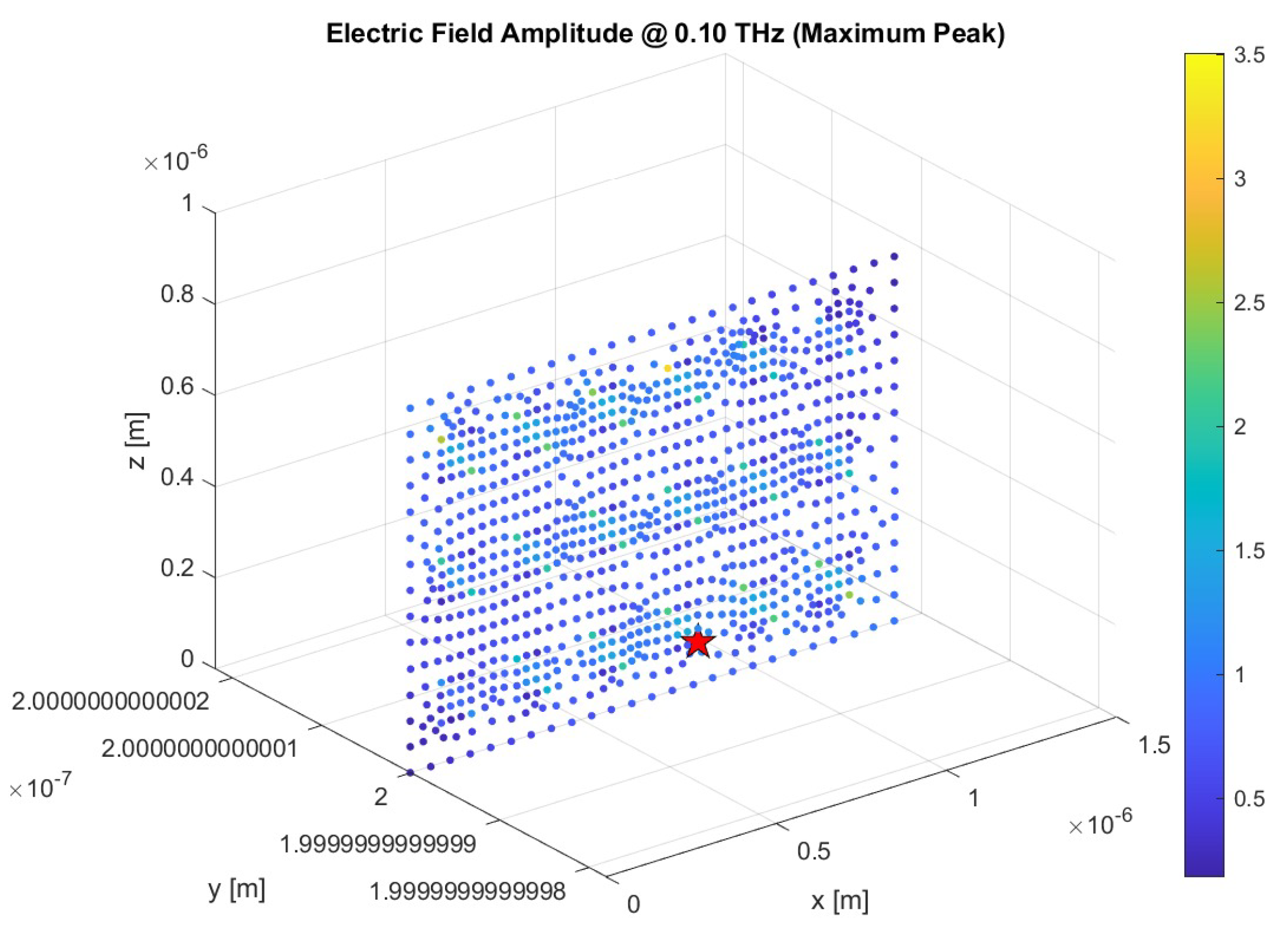
4.1. Block 1 – Nanoantenna Response Characterization
4.2. Block 2 – Signal Quantization and Error Correction
4.3. Block 3 – Pseudo-Random Key Generation and Bitwise Encryption
4.4. Block 4 – Arnold Transform Encryption
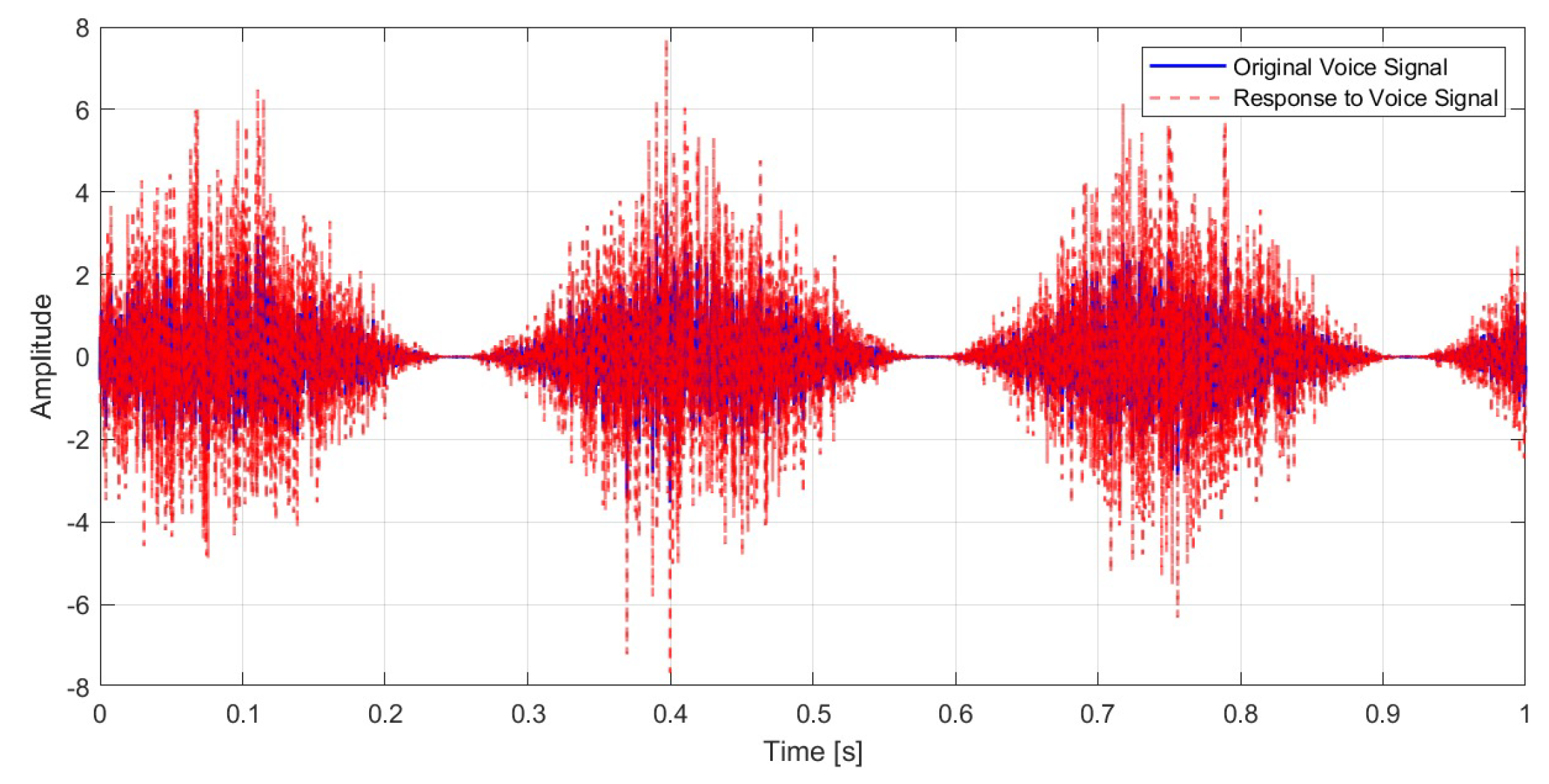
4.5. Block 5 – Signal Recovery at the Receiver
5. Results
5.1. Nanoantenna Response to Signals
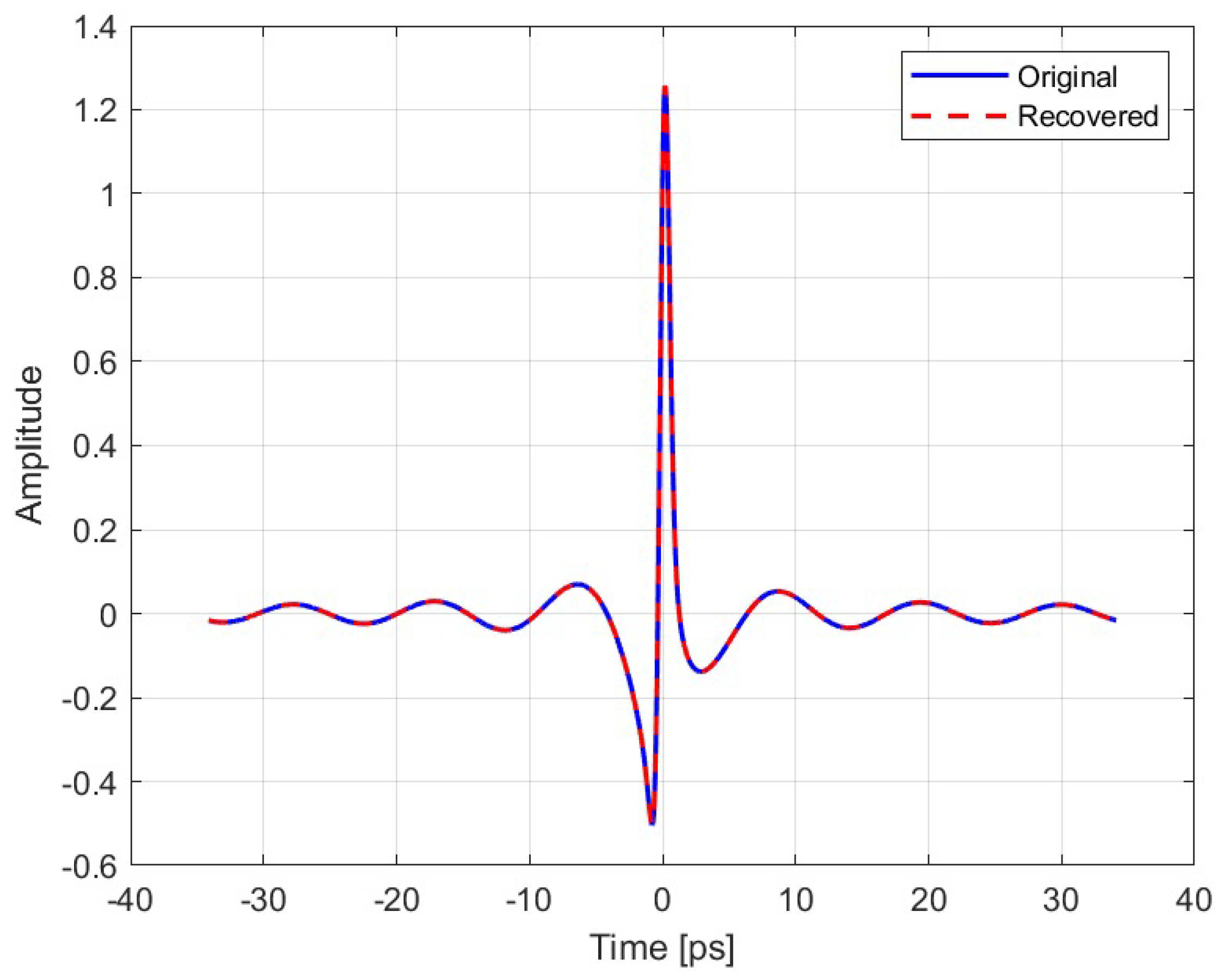
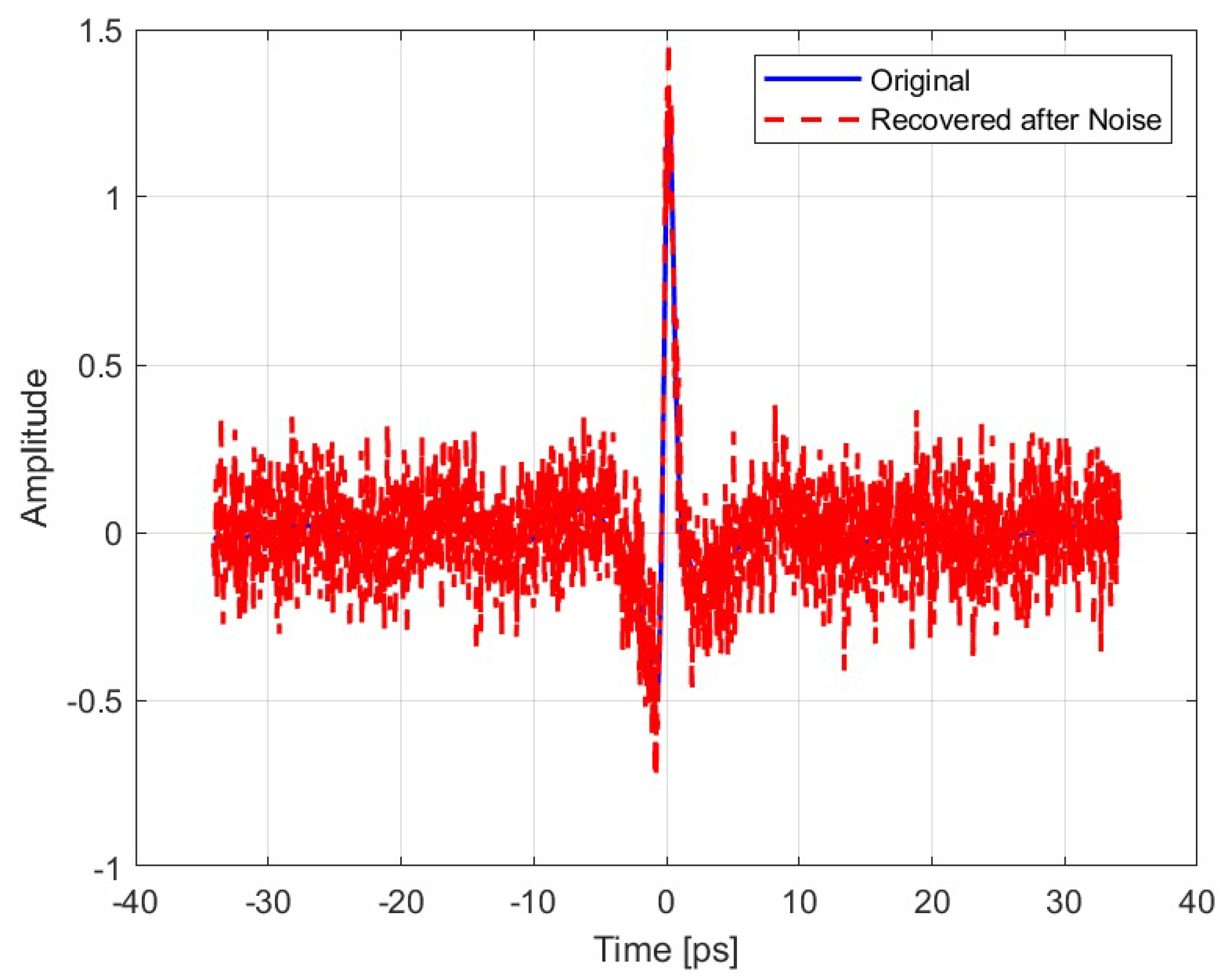
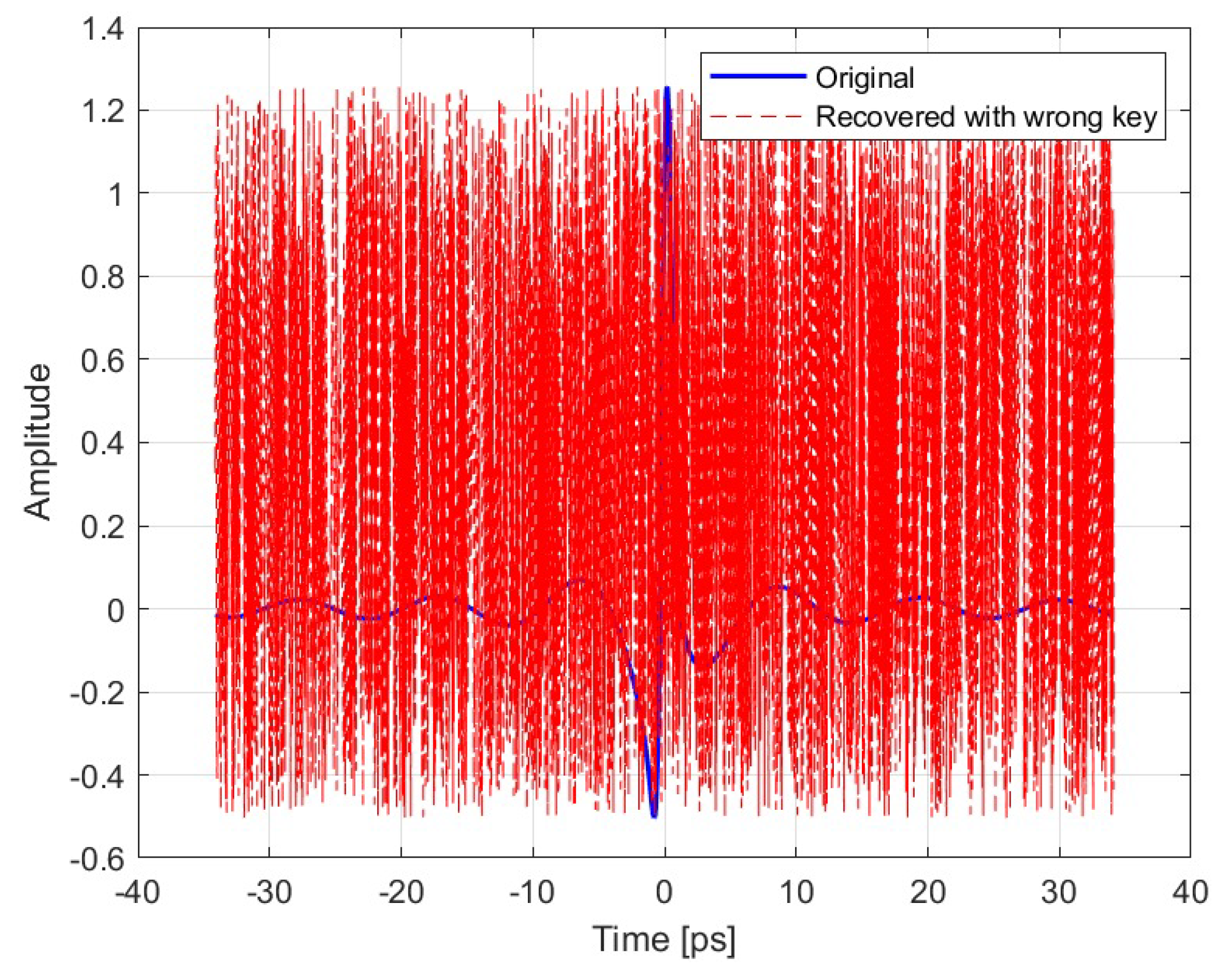
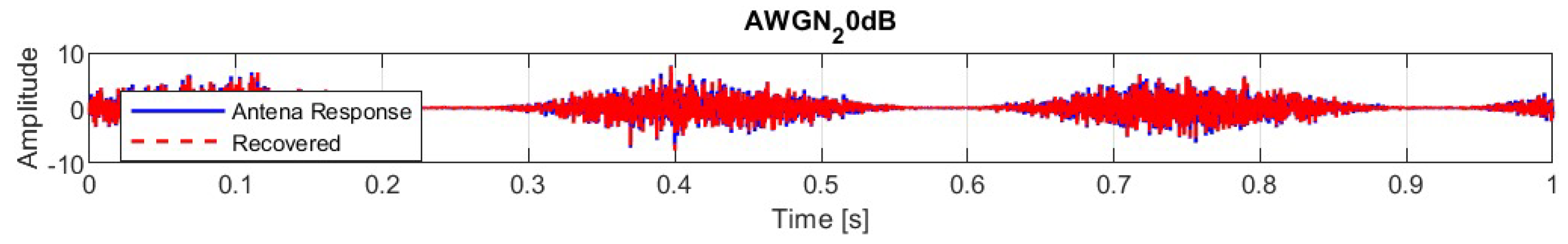
5.2. Proposed Cryptography Model Test
6. Discussion
7. Conclusions
- Replace the current key scheduling mechanism with a dynamic key exchange system based on elliptic curve Diffie–Hellman (ECDH).
- Integrate a cryptographically secure pseudorandom number generator to enhance unpredictability.
- Extend the analysis to other classes of signals, including video or biomedical data.
- Evaluate resilience under active adversarial models and simulate attack scenarios.
Funding
Conflicts of Interest
Abbreviations
| AES | Advanced Encryption Standard |
| AWGN | Additive White Gaussian Noise |
| ECC | Elliptic Curve Cryptography |
| ECDH | Elliptic Curve Diffie–Hellman |
| EM | Electromagnetic |
| EOT | Extraordinary Optical Transmission |
| FFT | Fast Fourier Transform |
| IFFT | Inverse Fast Fourier Transform |
| LSPR | Localized Surface Plasmon Resonance |
| PEC | Perfect Electric Conductor |
| PLS | Physical Layer Security |
| PSNR | Peak Signal-to-Noise Ratio |
| RF | Radio-Frequency |
| RMSE | Root Mean Square Error |
| SPP | Surface Plasmonic Polaritons |
References
- Gomes, R.D.F.R.; Martins, M.J.; Baptista, A.; Torres, J.P.N. Study of a nano optical antenna for intersatellite communications. Optical and Quantum Electronics 2017, 49, 1–22. [Google Scholar] [CrossRef]
- Rawat, B.S.; Bhat, A.; Pištora, J. THz band nanoantennas for future mobile communication. In Proceedings of the 2013 International Conference on Signal Processing and Communication (ICSC). IEEE; 2013; pp. 48–52. [Google Scholar]
- Alves, A.; Melo, M.C.; Siqueira, J.; Zanella, F.; Mejía-Salazar, J.R.; Arismar, C.S. Plasmonic nanoantennas for 6G intra/inter-chip optical-wireless communications. In Proceedings of the 2020 2nd 6G wireless summit (6G SUMMIT). IEEE; 2020; pp. 1–4. [Google Scholar]
- Wu, Q. 4g communication technology wireless network secure communication. In Proceedings of the 2021 International Wireless Communications and Mobile Computing (IWCMC). IEEE; 2021; pp. 915–918. [Google Scholar]
- Balanis, C.A. Antenna theory: A review. Proceedings of the IEEE 1992, 80, 7–23. [Google Scholar] [CrossRef]
- Kavankova, I.; Kovar, S.; Valouch, J.; Adamek, M. Review of nanoantennas application. Prz. Elektrotechniczny 2023, 1, 13–17. [Google Scholar] [CrossRef]
- Maksymov, I.S. Magneto-plasmonic nanoantennas: Basics and applications. Reviews in Physics 2016, 1, 36–51. [Google Scholar] [CrossRef]
- Fakhimi, M.J.; Akan, O.B. Nanoantennas and Nanoradars: The Future of Integrated Sensing and Communication at the Nanoscale. IEEE Transactions on Molecular, Biological, and Multi-Scale Communications 2024, 10, 493–516. [Google Scholar] [CrossRef]
- Ebbesen, T.; Lezec, H.; Ghaemi, H.; Thio, T.; Wolff, P. Extraordinary Optical Transmission Through Sub-Wavelength Hole Arrays. Nature 1998, 391, 667–669. [Google Scholar] [CrossRef]
- Wen, J. Excitation and detection of highly confined plasmonic gap modes with subwavelength dimensions; Friedrich-Alexander-Universitaet Erlangen-Nuernberg (Germany), 2011.
- Maier, S.A.; et al. Plasmonics: fundamentals and applications; Vol. 1, Springer, 2007.
- Raether, H.; et al. Surface Plasmons on Smooth and Rough Surfaces and on Gratings [electronic resource].
- Piltan, S.; Sievenpiper, D. Field enhancement in plasmonic nanostructures. Journal of Optics 2018, 20, 055401. [Google Scholar] [CrossRef]
- Geshev, P.; Klein, S.; Witting, T.; Dickmann, K.; Hietschold, M. Calculation of the electric-field enhancement at nanoparticles of arbitrary shape in close proximity to a metallic surface. Physical Review B (Condensed Matter and Materials Physics) 2004, 70, 75402. [Google Scholar] [CrossRef]
- Bhattarai, J.; Maruf, H.U.; Stine, K. Plasmonic-Active Nanostructured Thin Films. Processes 2020, 8, 115. [Google Scholar] [CrossRef]
- Anitha, G.; Nirmala, P.; Ramesh, S.; Tamilselvi, M.; Ramkumar, G. A Novel Data Communication with Security Enhancement using Threat Management Scheme over Wireless Mobile Networks. In Proceedings of the 2022 International Conference on Advances in Computing, Communication and Applied Informatics (ACCAI). IEEE; 2022; pp. 1–6. [Google Scholar]
- Bassily, R.; Ekrem, E.; He, X.; Tekin, E.; Xie, J.; Bloch, M.R.; Ulukus, S.; Yener, A. Cooperative Security at the Physical Layer: A Summary of Recent Advances. IEEE Signal Processing Magazine 2013, 30, 16–28. [Google Scholar] [CrossRef]
- Sanenga, A.; Mapunda, G.A.; Jacob, T.M.L.; Marata, L.; Basutli, B.; Chuma, J.M. An overview of key technologies in physical layer security. Entropy 2020, 22, 1261. [Google Scholar] [CrossRef] [PubMed]
- Hoseini, S.A.; Bouhafs, F.; den Hartog, F. A practical implementation of physical layer security in wireless networks. In Proceedings of the 2022 IEEE 19th Annual Consumer Communications & Networking Conference (CCNC). IEEE; 2022; pp. 1–4. [Google Scholar]
- Gunathilake, N.A.; Al-Dubai, A.; Buchanan, W.J.; Lo, O. Electromagnetic analysis of an ultra-lightweight cipher: Present. arXiv preprint arXiv:2106.15225, 2021; arXiv:2106.15225. [Google Scholar]
- Arun, V.; Kuppusamy, P.; Naveen, G.; Santhuja, P. Knapsack Encryption with Elliptic Curve Cryptography Based Secured Wireless Network. In Proceedings of the 2023 2nd International Conference on Edge Computing and Applications (ICECAA); 2023; pp. 298–302. [Google Scholar] [CrossRef]
- Dayana, D.S.; Pandian, R.; Babu, A.R.; Nirmalraj, S.; Jebaseelan, S.D.S.; V, M. Elevating Security in Wireless Sensor Networks using ECC and AES Cryptographic Techniques. In Proceedings of the 2023 International Conference on Innovative Computing, Intelligent Communication and Smart Electrical Systems (ICSES); 2023; pp. 1–6. [Google Scholar] [CrossRef]
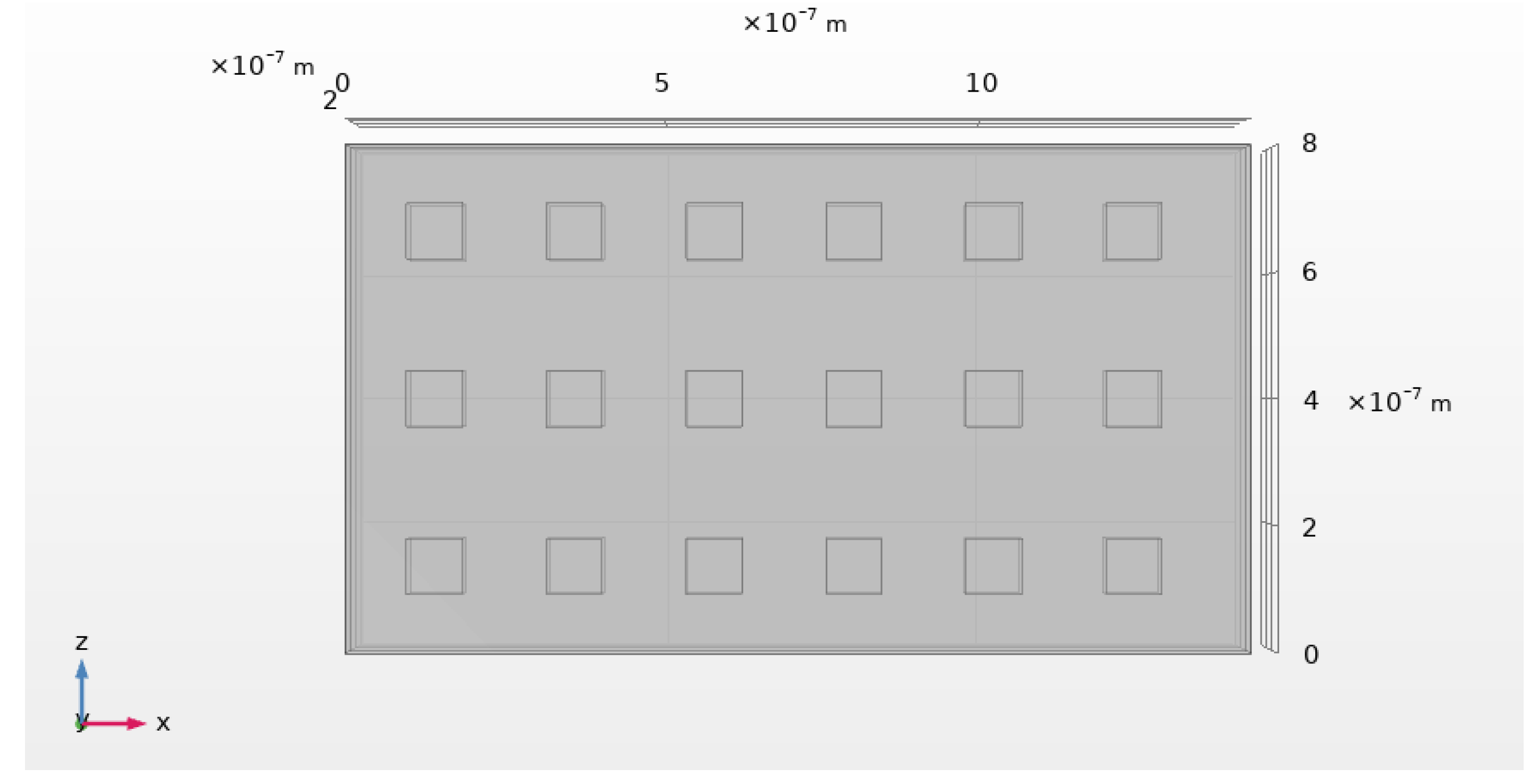
| Name | Value | Unit | Description |
|---|---|---|---|
| E | m | Metal thickness | |
| m | Dielectric thickness | ||
| m | Design wavelength | ||
| L | m | Total length of the structure | |
| m | Side length of the apertures | ||
| m | Spacing between apertures | ||
| m | Aperture width | ||
| 3 | – | Number of apertures along x | |
| 6 | – | Number of apertures along z |
| Scenario | Correlation | RMSE | PSNR (dB) | |
|---|---|---|---|---|
| Gaussian Signal | Ideal | 1.00 | 104.27 | |
| Noisy environment of 0.2 V/m | 0.7507 | 20.70 | ||
| Wrong key | 0.0118 | 5.78 | ||
| Voice Signal | AWGN | 0.99504 | 0.12914 | 35.527 |
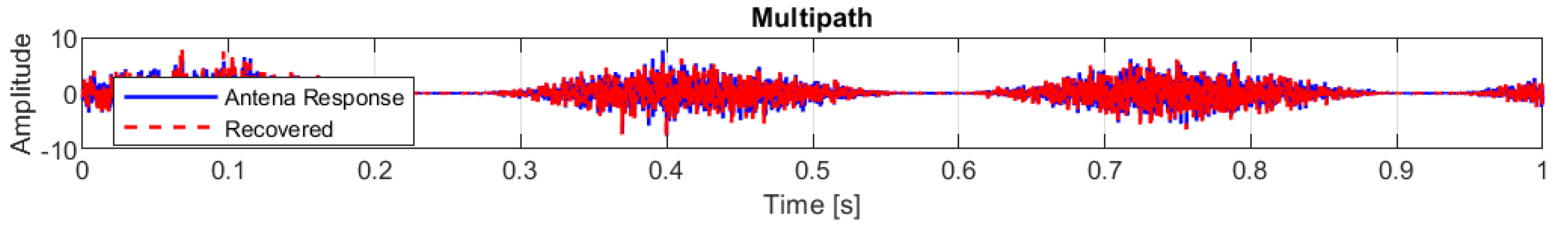
| Multipath Propagation | 0.25789 | 1.6329 | 13.489 | |
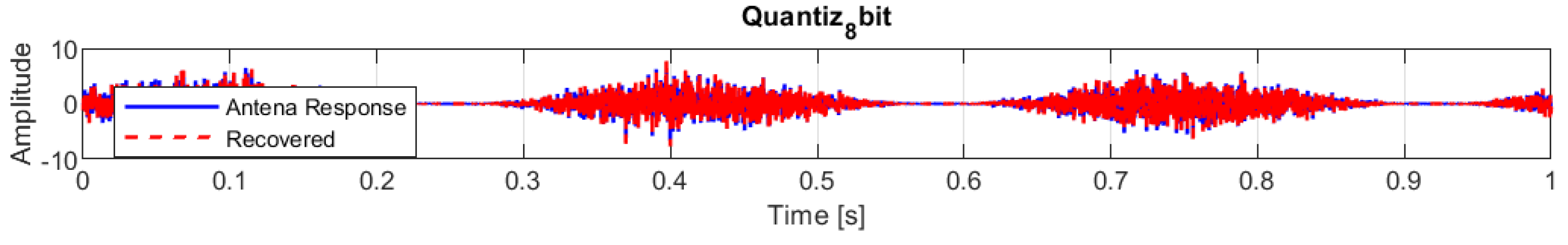
| Quantization | 0.99991 | 0.017303 | 52.986 | |
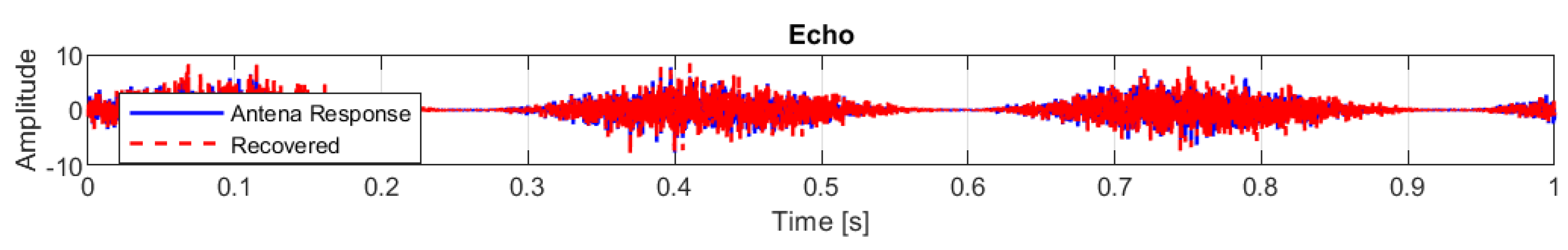
| Echo | 0.85855 | 0.77097 | 20.008 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




