Submitted:
09 July 2025
Posted:
11 July 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. General Data Protection Regulation (GDPR)
| Article | Principle | Description |
| GDPR, art. 5.1.a | Lawfulness, fairness and transparency. | Personal data shall be processed lawfully, fairly and in a transparent manner in relation to individuals. |
| GDPR, art. 5.1.b | Purpose limitation. | Personal data shall be collected for specified, explicit and legitimate purposes and not further processed in a manner that is incompatible with those purposes; further processing for archiving purposes in the public interest, scientific or historical research purposes or statistical purposes shall not be considered to be incompatible with the initial purposes. |
| GDPR, art. 5.1.c | Data minimization. | Personal data shall be adequate, relevant and limited to what is necessary in relation to the purposes for which they are processed. |
| GDPR, art. 5.1.d | Accuracy. | Personal data shall be accurate and, where necessary, kept up to date; every reasonable step must be taken to ensure that personal data that are inaccurate, having regard to the purposes for which they are processed, are erased or rectified without delay. |
| GDPR, art. 5.1.e | Storage limitation. | Personal data shall be kept in a form which permits identification of data subjects for no longer than is necessary for the purposes for which the personal data are processed; personal data may be stored for longer periods insofar as the personal data will be processed solely for archiving purposes in the public interest, scientific or historical research purposes or statistical purposes subject to implementation of the appropriate technical and organisational measures required by the GDPR in order to safeguard the rights and freedoms of individuals. |
| GDPR, art. 5.1.f | Integrity and confidentiality (security). | Personal data shall be processed in a manner that ensures appropriate security of the personal data, including protection against unauthorised or unlawful processing and against accidental loss, destruction or damage, using appropriate technical or organisational measures. |
| GDPR, art. 5.2 | Accountability. | The controller shall be responsible for, and be able to demonstrate compliance with. |
| GDPR, art. 16 | Right to rectification. | The data subject shall have the right to obtain from the controller without undue delay the rectification of inaccurate personal data concerning him or her. Taking into account the purposes of the processing, the data subject shall have the right to have incomplete personal data completed, including by means of providing a supplementary statement. |
| GDPR, art. 17 | Right to erasure (right to be forgotten). | The data subject shall have the right to obtain from the controller the erasure of personal data concerning him or her without undue delay and the controller shall have the obligation to erase personal data without undue delay where one of the following grounds applies: (a) the personal data are no longer necessary in relation to the purposes for which they were collected or otherwise processed; (b) the data subject withdraws consent on which the processing is based according to point (a) of Article 6(1), or point (a) of Article 9(2), and where there is no other legal ground for the processing; (c) the data subject objects to the processing pursuant to Article 21(1) and there are no overriding legitimate grounds for the processing, or the data subject objects to the processing pursuant to Article 21(2); (d) the personal data have been unlawfully processed; |
| GDPR, art. 20 | Right to data portability. | The data subject shall have the right to receive the personal data concerning him or her, which he or she has provided to a controller, in a structured, commonly used and machine-readable format and have the right to transmit those data to another controller without hindrance from the controller to which the personal data have been provided |
| GDPR, art. 22 | Right not be subject to a decision based solely on automated processing. | The data subject shall have the right not to be subject to a decision based solely on automated processing, including profiling, which produces legal effects concerning him or her or similarly significantly affects him or her. |
| GDPR, art. 25. | Data protection by design and by default. | Taking into account the state of the art, the cost of implementation and the nature, scope, context and purposes of processing as well as the risks of varying likelihood and severity for rights and freedoms of natural persons posed by the processing, the controller shall, both at the time of the determination of the means for processing and at the time of the processing itself, implement appropriate technical and organisational measures (…) in an effective manner and to integrate the necessary safeguards into the processing in order to meet the requirements of this Regulation and protect the rights of data subjects. |
- Data Subject: This is the natural person who owns the personal data. They have the right to control how their information is collected, used, and protected.
- Data Controller: This is the entity, which can be either an organization or an individual, that decides what personal data is collected, for what purpose it is processed, and what means are used. Although it may outsource processing, it remains the primary guarantor of compliance with the GDPR and must ensure that data processing is legitimate, transparent, and secure.
- Data Processor: This acts on behalf of the Data Controller, performing operations on personal data in accordance with their instructions. They are required to implement appropriate technical and organizational measures to ensure data protection and comply with the provisions of the GDPR. We should point out that personal data processing is any operation or set of operations performed on personal data or sets of personal data, whether or not by automated means, such as collection, recording, organization, structuring, storage, adaptation or alteration, retrieval, consultation, use, disclosure by transmission, dissemination or otherwise making available, alignment or combination, restriction, erasure or destruction, in accordance with Article 4 of the GDPR.
1.2. Blockchain
- Public blockchain: These are completely open networks where any user can participate by sending transactions, operating nodes, or even mining new blocks. Although this model guarantees high transparency and censorship resistance, it has significant limitations in terms of scalability and privacy. All stored information is visible to all participants, which implies total data exposure. Although encryption can be used, its use in immutable environments poses future risks due to the obsolescence of cryptographic algorithms, especially with the emergence of technologies such as quantum computing. Representative examples of this model are Bitcoin and Ethereum [11].
- Private blockchain: Unlike the previous model, private blockchains are managed by a centralized organization that restricts access to authorized nodes. This type of implementation allows for greater control over the network, improving both efficiency and privacy. Frameworks such as the Linux Foundation's Hyperledger Fabric [12] enable the development of these types of solutions, adapted to contexts where confidentiality and performance are essential, such as in the financial or corporate sectors.
- Consortium or federated blockchain: This approach combines elements of public and private networks. They are maintained by a group of organizations that share governance of the system. Although participation is restricted, certain levels of openness for public consultation can be enabled. This balance between controlled decentralization and privacy enables its use in inter-institutional collaborative contexts, such as higher education.
3. Methodology
3.1. Legal-Technical Evaluation Process
- Initial Consultation: Meetings with technical developers and legal experts to understand the architectural blueprint.
- Document Review: Evaluation of system specifications, privacy policies, and technical diagrams.
- Regulatory Mapping: Analysis of GDPR articles, relevant case law, and guidance from the European Data Protection Board (EDPB)[1], The Spanish Data Protection Agency (Agencia Española de Protección de datos – AEPD)[2], and European Data Protection Supervisor (EDPS)[3].
- Iterative Feedback: Drafting of a preliminary legal report, integration of stakeholder feedback, and generation of a final report.
3.2. Analytical Framework
2. Related Works
2.1. Blockchain in Education
2.2. GDPR Challenges in Blockchain Systems
- A participation policy that establishes the conditions under which and with what role one participates in the network.
- A distributed information storage policy.
- A data sharing policy.
- A consensus policy to validate new information in the system.
- An information integrity management policy.
- Who can access or participate in the network,
- With what permissions,
- What levels of service are provided,
- Block validation strategies,
- Traceability of information, etc.
- Recording transactions on the blockchain, which requires transforming the data into operations valid for the blockchain.
- Validating transaction blocks, proceeding to verify them according to the selected consensus mechanism.
- Implementing other additional processing operations that a node can perform on transactions, such as managing pending transactions, reordering them, storing historical data, processing events associated with smart contracts, providing data and services to applications, etc. In this sense, the use of a specific blockchain infrastructure as an element for the processing of personal data could generate specific non-compliance and risks to the rights and freedoms of data subjects. One of its key aspects is ensuring compliance with data protection principles, as well as allowing the exercise of data subjects' rights, and particularly the principle of accuracy, the principle of retention, and the rights of rectification and erasure.
- 1)
- ensuring regulatory compliance and, once achieved,
- 2)
- evaluating and assessing the risks, some of which can be mitigated with legal, organizational, and technical measures. In cases of high risk, the assessment of the suitability, necessity, and proportionality of the processing must be completed.”
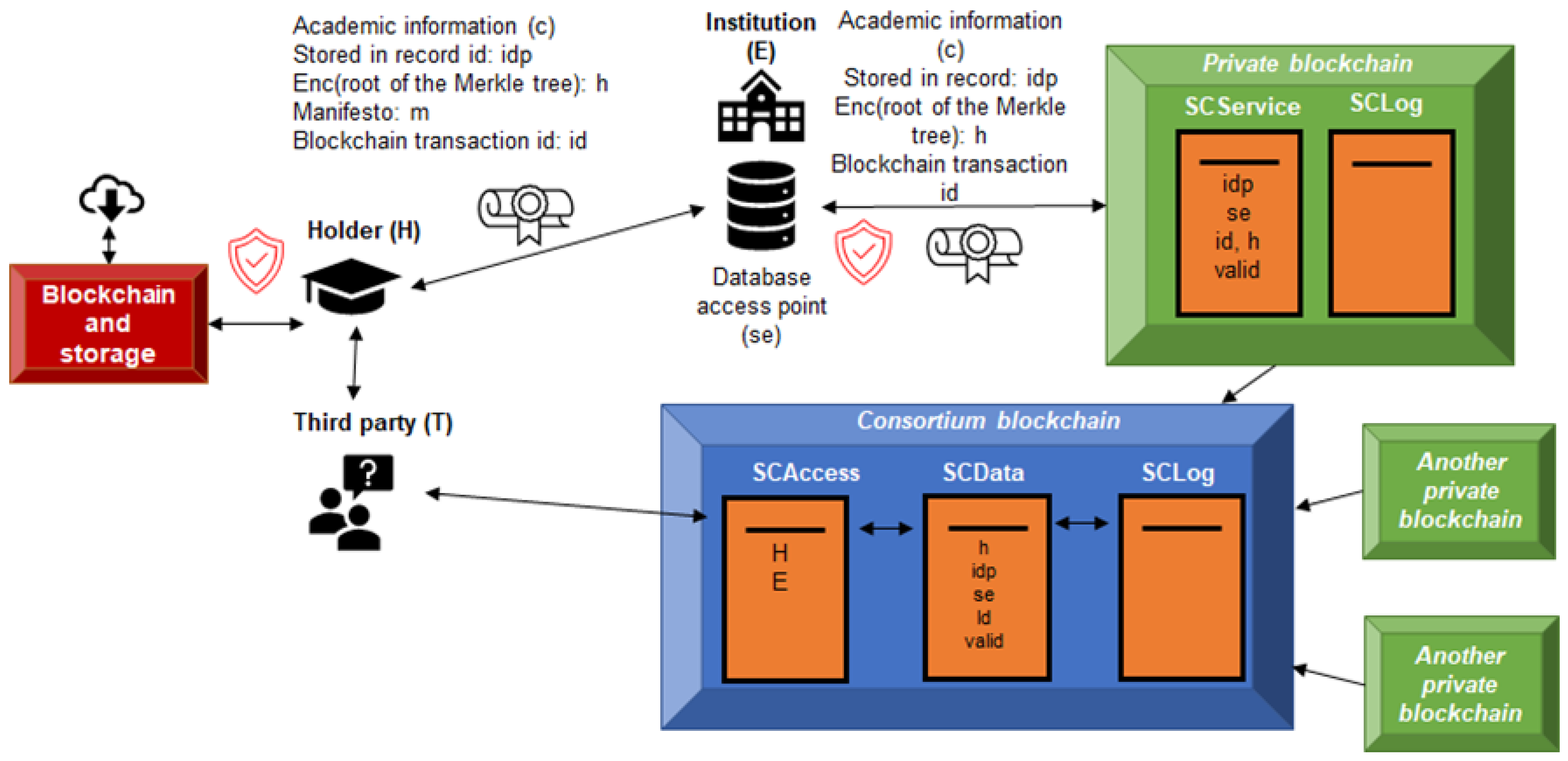
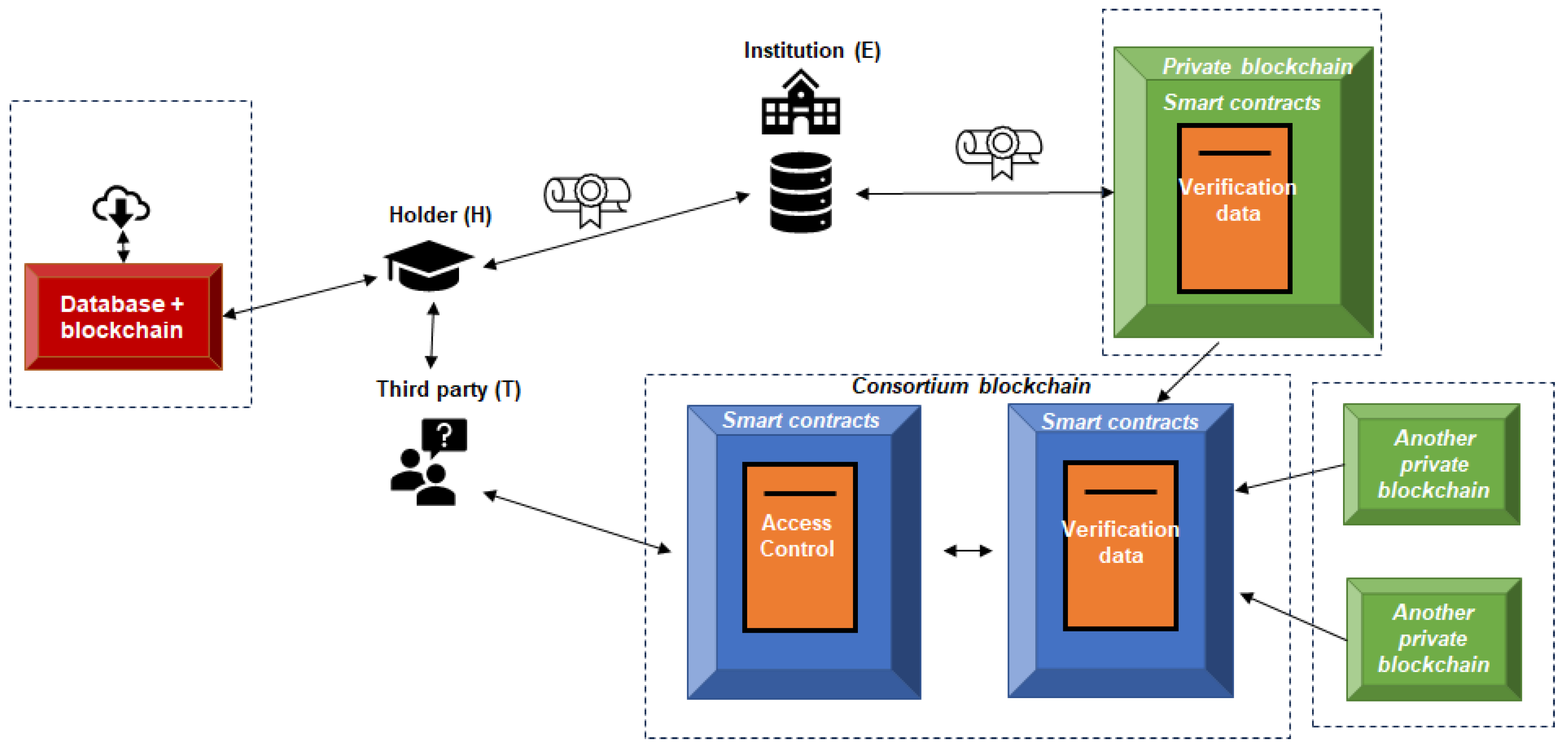
4. Technical Architecture of the GAVIN Model
- It must be possible to use this system without modifying the existing information systems of academic/training institutions or other organizations that issue certificates or academic information and accreditations.
- It must be possible to verify the validity of the certificate content and associated accreditations even after the dissolution of the institution that originally issued the certificate and all its information systems.
- It must be usable in all types of education: formal, non-formal, and informal.
- It must be flexible enough to accommodate different types of academic information, accreditations, etc., regardless of the underlying information models.
- It must be scalable and capable of supporting transactions and operations related to the registration, verification, and query of information by the model's end users.
- It must comply with personal data protection regulations, and particularly with the General Data Protection Regulation (GDPR) in cases where it affects individuals located in the European Union, which is the subject of validation in this report.
4.1. Off-Chain Data Storage
4.2. Blockchain Layers,Access Control and Use Escenarios
- SCData: A smart contract stored on a consortium blockchain that stores the anonymized values of credentials, implemented using HMACs in the developed prototype.
- SCAccess: A smart contract stored on the consortium blockchain that verifies access permissions granted by data subjects. In the current implementation of the project a Blockchain Application Firewall (BAF) [38] controls data queries and enforces user permissions, functioning as a decentralized access gateway, but this element could not be necessarily used in other implementations.
- SCLog: A smart contract in charge of registering all the accesses to the information.
- Scenario 1: Full verification: H sends T the full certificate along with the manifest (m), including all the keys necessary to reconstruct the Merkle tree. T requests the encrypted value (h) from the SCAccess contract, verifies it against SCData, and checks its integrity.
- Scenario 2: Partial verification: H decides to share only part of the academic content. To do so, he transmits to T only the relevant elements and verification paths of the Merkle tree. After receiving the encrypted tree root from SCData (after authorization validated by SCAccess), T can verify that the partial information corresponds to a valid, unrevoked certificate.
- Scenario 3: Direct query to the issuing authority: H delegates the delivery of the information to T to E. In this case, T accesses the database pointer (stored in SCData), and after its authorization is validated in SCAccess, it can obtain the certificate (c) directly from E. This interaction is logged in SCLog.
- Store any type of academic information in a free format.
- Implement smart contracts on the platform.
- Allow the interconnection of blockchains (consortium).
- Implement storage with a blockchain-based access control system, where data is stored encrypted and access is restricted to the data subject.
4.3. Consortium Governance, Interconnection and Scalability
- Multiple private blockchains, managed by academic institutions.
- A central consortium blockchain aggregating anonymized information to verify academic information and verifying access rights.
5. Legal Analysis
5.1. Scope of the GDPR
- On the one hand, to the processing of personal data when the controller or processor (RT/ET) has an establishment in the EU, regardless of whether the processing takes place in the Union or not.
- On the other hand, to the processing of personal data of data subjects located in the Union by a controller or processor not established in the Union, when the processing activities are related to:
- o the offering of goods or services to said data subjects in the Union, regardless of whether payment is required from them, or
- o the monitoring of their behavior, to the extent that this takes place in the Union.
5.2. Personal Data Processed by the GAVIN Project
- Registration Identifier (Code).
- University Registration Identifier (Code).
- National Registration Identifier (Code).
- Surname.
- First Name.
- Identity Document.
- Gender.
- Date of Birth.
- Country of Birth.
- City of Birth.
- Country where the student currently resides.
- Student's current city of residence.
- Postal Code.
- Student's email address.
- Student's phone number.
- Type of study.
- Degree.
- Area of specialization.
- Study ID.
- Issuing Entity ID.
- Start date of studies.
- End date of studies.
- Hours dedicated to completion.
- Number of academic credits (ECTS or equivalent).
- Language of study.
- Program subjects and content description.
5.3. Implications for Compliance with the Principles of Article 5 of the GDPR
5.4. Data Flows in the Model and Characterization of the Participants as Data Controllers, Processors, or co-Controllers
- Where two or more controllers jointly determine the purposes and means of processing, they shall be considered joint controllers. The joint controllers shall determine, in a transparent manner and by mutual agreement, their respective responsibilities for compliance with the obligations imposed by this Regulation, in particular with regard to the exercise of data subject rights and their respective obligations to provide information referred to in Articles 13 and 14, unless and to the extent that their respective responsibilities are governed by Union or Member State law to which they apply. Such agreement may designate a contact point for data subjects.
- The agreement referred to in paragraph 1 shall duly reflect the respective roles and relationships of the joint controllers in relation to the data subjects. The essential aspects of the agreement shall be made available to the data subject.
- Regardless of the terms of the agreement referred to in paragraph 1, data subjects may exercise their rights under this Regulation against and against each of the controllers.
5.5. Application of GDPR Principles
- Lawfulness, Fairness, and Transparency (Art. 5.1.a): Clear privacy policies, user-informed consent, and transparent data processing.
- Purpose Limitation (Art. 5.1.b): Academic certification as the sole purpose, no other purposes being contemplated at present.
- Data Minimization (Art. 5.1.c): Only essential data is processed and stored off-chain. The data processed is only the HMAC (as recommended by AEPD [40]) and the final result is additionally encrypted before being saved on the blockchain.
- Accuracy (Art. 5.1.d): Regarding this right, the GAVIN project model can fulfill this right by deleting the HMAC of the previous academic certificate, rendering the data arbitrary, which would effectively amount to deletion. A new academic certificate could subsequently be generated with the correct data. In any case, it is worth mentioning that the issuing institution (I) should delete the data from its off-chain systems if permitted by law. It also marks the certificate as invalid, and access control mechanisms ensure that no one can access it, in addition to deleting all related information.
- Storage Limitation (Art. 5.1.e): Data remains available only while necessary or archived under public interest exceptions.
- Integrity and Confidentiality (Art. 5.1.f): According to this article of GDPR, personal data must be processed in a manner that ensures appropriate security of the personal data, including protection against unauthorized or unlawful processing and against accidental loss, destruction, or damage, by applying appropriate technical or organizational measures ("integrity and confidentiality"). The principle of data integrity is fulfilled by the blockchain technique. Furthermore, we must note that confidentiality is also guaranteed, since the academic transcript data is not visible on the blockchain since an HMAC function has been applied to it and it has been subsequently encrypted. The developed prototype implements a firewall, specifically the so-called "BAF" (Blockchain Application Firewall) [38], which prevents unauthorized access to verification data, although it is true that it is an element outside the consortium blockchain. The BAF performs filtering and access control, verifying which resources can be accessed within SCAccess. In this way, any user with access to said blockchain is prevented from viewing data requested by other entities, thus limiting access to information for which they do not have permissions. This is because with current blockchain technology it is not possible to perform this dynamic segmentation of permissions between accounts considered in the proposed model, so this perfectly valid technological solution is used for its real implementation in the reference technical model. In summary, encryption, access logs, and tamper-proof chains ensure data security.
- Accountability (Art. 5.2): The GAVIN project has defined and implemented appropriate technical and organizational measures to ensure and demonstrate that the processing complies with this Regulation, since, as explained, a robust pseudonymization or anonymization system is in place. Therefore, the impact of an attack or security breach would be low, given that the data stored in the blockchain is the result of several HMAC generation processes with different keys and has been subjected to an encryption process. Furthermore, the BAF mechanism is in place, which provides additional security. It should be noted that the prototype records access notarization information (a hash summary of the log recorded in the BAF to potentially detect tampering) on a blockchain (equivalent to SLog, defined in the model) so that traceability of what has happened to their data can be maintained. Likewise, the holder can always check in SCAccess who has access permission to their academic information, and the BAF records the accesses and periodically notarizes them on a blockchain to detect potential tampering. In this way, the holder could check who has accessed specific academic information and when. This is done because current blockchain technology does not allow reading operations to be recorded, only those that modify data. This is how this article is fulfilled in the GAVIN Project.
5.5. Privacy by Default
- As explained, both the conceptual theoretical model and the prototype developed at GAVIN comply with the principles of the GDPR, including minimization, retention limitation, and purpose limitation, as already explained.
- Regarding access, the model restricts access to only authorized users to consult the information, which is also implemented with the BAF in the reference technical model.
- Access to data by service providers is managed by users, who can choose when to provide such access and can restrict it at any time. Furthermore, all access to the blockchain is recorded.
5.8. Data Subject Rights
- Right to Access (Art. 15): The model's design allows for automatic access by the user (holder) at any time, without the need for third-party intervention. Furthermore, access to certification records that may be stored on the blockchain by third parties other than the data subject must be authorized by the data subject, who can also revoke this authorization at any time. In this sense, we can clearly infer that the GAVIN project is ready to fulfill this right.
- Right to Rectification (Art. 16): This right can be fulfilled in two ways, as explained in the project:
- o One way to fulfill this right would be to remove the keys used to generate the HMACs for the different fields, meaning that the data stored in the blockchain would become arbitrary and dissociated, and therefore could not be associated with a holder. From this point on, the new information could be uploaded to the blockchain, meaning the academic certification would be "rectified" and the data would be accurate, thus complying with the principle of accuracy.
- o On the other hand, the project's blockchain could also fulfill this right by generating the new information and linking it to the previous information using the transaction identifier or other data.
- Right to Erasure (Art. 17): It is possible to exercise this right by deleting the keys and data used to generate the HMACs of the Merkle tree, whose signed HMAC was stored in the blockchain, such that the data stored in the blockchain now becomes arbitrary and dissociated data, without the possibility of recovering the original data from it (and access is withdrawn from everyone in SCAccess and, in addition, it is marked as invalid).
- Right to Portability (Art. 20): The Implementation in the reference technical model of the project GAVIN would also guarantee this right, as it allows the download of information in a structured, commonly used, and machine-readable data format.
- Right not be subject to a decision based solely on automated processing. (Art. 22): This right would not apply since the proposed model does not consider automated processes on or off-chain. The model proposes that, for the issuance of a new certificate, the issuing institution is responsible for executing this issuance. Furthermore, the interested party is the only one who can grant or revoke access permissions to their information. Finally, to verify data, the verifying entity is the one who actively interacts with the blockchain. Automated decisions are not made, nor are data subject profiles created. This is not applicable since there is no automated decision-making by either the promoters of the initiative or third parties, as mass access to user data is not possible, as the theoretical model and the technical implementation of the prototype have adequate access control mechanisms. Specifically, in the theoretical model, the record is made in the SCLog, while in the technical reference model, the record is achieved with the BAF, since read accesses are not recorded in the blockchain.
5.6. Roles and Responsibilities
5.7. Cross-Border Data Flows
6. Discussion
6.1. Innovations and Contributions
6.2. Technical and Legal Challenges
- Inmutability vs. Erasure: This challenge is achieved through deletion of off-chain data and hash revocation.
- Shared Responsibility: The final deployment of the model proposed by the GAVIN project requires robust legal frameworks among consortia.
- International Hosting: It is clearly an ongoing risk due to limited global GDPR harmonization.
- At the legal level, GAVIN also successfully addresses the complexities arising from co-responsibility in consortium networks. The proposal to formalize co-responsibility agreements between participating institutions and the correct identification of roles in data processing constitute a solid starting point that can be replicated in other institutional contexts.
6.3. Policy and Standardization Implications
7. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- W. Gräther, S. W. Gräther, S. Kolvenbach, R. Ruland, J. Schütte, C. F. Torres, and F. Wendland, “Blockchain for Education: Lifelong Learning Passport,” 1st ERCIM Blockchain Work. 2018, Reports Eur. Soc. Soc. Embed. Technol., no. 10, pp. 2018; 8. [Google Scholar] [CrossRef]
- BLOCKCHAIN BASED FRAMEWORK FOR EDUCATIONAL CERTIFICATES VERIFICATION. J. Crit. Rev. 2020, 7. [CrossRef]
- Tan, E.; Lerouge, E.; Du Caju, J.; Du Seuil, D. Verification of Education Credentials on European Blockchain Services Infrastructure (EBSI): Action Research in a Cross-Border Use Case between Belgium and Italy. Big Data Cogn. Comput. 2023, 7, 79. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. bitcoin.org. Available online, 20 November. [CrossRef]
- T. Lyons, L. T. Lyons, L. Courcelas, and K. Timsit, Blockchain and the GDPR. The European Union Blockchain Observatory and Forum, 2018.
- Delgado-Von-Eitzen, C.; Anido-Rifón, L.; Fernández-Iglesias, M.J. Application of Blockchain in Education: GDPR-Compliant and Scalable Certification and Verification of Academic Information. Appl. Sci. 2021, 11, 4537. [Google Scholar] [CrossRef]
- P. Voigt and A. Von dem Bussche, The EU General Data Protection Regulation (GDPR). Springer Cham, 2017.
- Casino, F.; Dasaklis, T.K.; Patsakis, C. A systematic literature review of blockchain-based applications: Current status, classification and open issues. Telematics Informatics 2019, 36, 55–81. [Google Scholar] [CrossRef]
- Khezr, S.; Moniruzzaman, M.; Yassine, A.; Benlamri, R. Blockchain Technology in Healthcare: A Comprehensive Review and Directions for Future Research. Appl. Sci. 2019, 9, 1736. [Google Scholar] [CrossRef]
- A Zetzsche, D.; Arner, D.W.; Buckley, R.P. Decentralized Finance. J. Financial Regul. 2020, 6, 172–203. [Google Scholar] [CrossRef]
- X. Wu, Z. X. Wu, Z. Zou, and D. Song, “Ethereum Tools and Frameworks,” in Learn Ethereum: Build your own decentralized applications with Ethereum and Smart Contracts, Packt, 2019, pp. 294–335.
- HYPERLEDGER, “Whitepaper Introduction Hyperledger,” 18, 2018. https://www.hyperledger.org/learn/white-papers. 20 July.
- Szabo, N. Formalizing and Securing Relationships on Public Networks. First Monday 1997, 2. [Google Scholar] [CrossRef]
- Grech and A., F. Camilleri, “Blockchain in Education,” Publications Office of the European Union, Luxembourg, 2017. [CrossRef]
- Sharples, M.; Domingue, J. The Blockchain and Kudos: A Distributed System for Educational Record, Reputation and Reward. In European Conference on Technology Enhanced Learning; Springer, Cham, Switzerland, 2016; pp. [CrossRef]
- Turkanovic, M.; Holbl, M.; Kosic, K.; Hericko, M.; Kamisalic, A. EduCTX: A Blockchain-Based Higher Education Credit Platform. IEEE Access 2018, 6, 5112–5127. [Google Scholar] [CrossRef]
- Alammary, A.; Alhazmi, S.; Almasri, M.; Gillani, S. Blockchain-Based Applications in Education: A Systematic Review. Appl. Sci. 2019, 9, 2400. [Google Scholar] [CrossRef]
- Bhaskar, P.; Tiwari, C.K.; Joshi, A. Blockchain in education management: present and future applications. Interact. Technol. Smart Educ. 2020. [Google Scholar] [CrossRef]
- Ocheja, P.; Agbo, F.J.; Oyelere, S.S.; Flanagan, B.; Ogata, H. Blockchain in Education: A Systematic Review and Practical Case Studies. IEEE Access 2022, 10, 99525–99540. [Google Scholar] [CrossRef]
- Raimundo, R.; Rosário, A. Blockchain System in the Higher Education. Eur. J. Investig. Heal. Psychol. Educ. 2021, 11, 276–293. [Google Scholar] [CrossRef] [PubMed]
- B. Razia and B. Awwad, “A Comprehensive Review of Blockchain Technology and Its Related Aspects in Higher Education BT - Technologies, Artificial Intelligence and the Future of Learning Post-COVID-19: The Crucial Role of International Accreditation,” A. Hamdan, A. E. Hassanien, T. Mescon, and B. Alareeni, Eds. Cham: Springer International Publishing, 2022, pp. 553–571.
- Talat, M.; Riaz, S.; Farooq, M.S. Effect of Blockchain on Education: A Systemic Literature Review. VFAST Trans. Softw. Eng. 2022, 10, 116–124. [Google Scholar] [CrossRef]
- H. Yumna, M. M. H. Yumna, M. M. Khan, M. Ikram, and S. Ilyas, “Use of Blockchain in Education: A Systematic Literature Review,” vol. 11432, N. T. Nguyen, F. L. Gaol, T.-P. Hong, and B. Trawiński, Eds. Springer, Cham, 2019, pp. 191–202.
- Caldarelli, G.; Ellul, J. Trusted Academic Transcripts on the Blockchain: A Systematic Literature Review. Appl. Sci. 2021, 11, 1842. [Google Scholar] [CrossRef]
- Castro, R.Q.; Au-Yong-Oliveira, M. Blockchain and Higher Education Diplomas. Eur. J. Investig. Heal. Psychol. Educ. 2021, 11, 154–167. [Google Scholar] [CrossRef] [PubMed]
- Dash, M.K.; Panda, G.; Kumar, A.; Luthra, S. Applications of blockchain in government education sector: a comprehensive review and future research potentials. J. Glob. Oper. Strat. Sourc. 2022, 15, 449–472. [Google Scholar] [CrossRef]
- Delgado-Von-Eitzen, C.; Anido-Rifón, L.; Fernández-Iglesias, M.J. Blockchain Applications in Education: A Systematic Literature Review. Appl. Sci. 2021, 11, 11811. [Google Scholar] [CrossRef]
- Hameed, B.; Murad, M.; Noman, A.; Javed, M.; Ramzan, M.; Ashfaq, F.; Usman, H.; Yousaf, M. A Review of Blockchain based Educational Projects. Int. J. Adv. Comput. Sci. Appl. 2019, 10. [Google Scholar] [CrossRef]
- Kabashi, F.; Snopce, H.; Aliu, A.; Luma, A.; Shkurti, L. A Systematic Literature Review of Blockchain for Higher Education. 2023 International Conference on IT Innovation and Knowledge Discovery (ITIKD). LOCATION OF CONFERENCE, BahrainDATE OF CONFERENCE; pp. 1–6.
- Loukil, F.; Abed, M.; Boukadi, K. Blockchain adoption in education: a systematic literature review. Educ. Inf. Technol. 2021, 26, 5779–5797. [Google Scholar] [CrossRef]
- Malibari, N.A. A Survey on Blockchain-based Applications in Education. 2020 7th International Conference on Computing for Sustainable Global Development (INDIACom). LOCATION OF CONFERENCE, IndiaDATE OF CONFERENCE; pp. 266–270.
- Molina, F.; Betarte, G.; Luna, C. A Blockchain based and GDPR-compliant design of a system for digital education certificates. CLEI Electron. J. 2023, 26, 3:1–3:23. [Google Scholar] [CrossRef]
- Delgado-Von-Eitzen, C.; Anido-Rifón, L.; Fernández-Iglesias, M.J. NFTs for the Issuance and Validation of Academic Information That Complies with the GDPR. Appl. Sci. 2024, 14, 706. [Google Scholar] [CrossRef]
- M. Finck, “Blockchain and the General Data Protection Regulation. Can distributed ledgers be squared with European data protection law?,” 2019. [CrossRef]
- Agencia española de protección de datos (AEPD), “Proof of concept Blockchain and the right to erasure,” 2024. [Online]. Available: https://www.aepd.es/guias/Tech-note-blockchain.pdf.
- Krawczyk, H.; Bellare, M.; Canetti, R. 1997.
- Liu, H.; Luo, X.; Liu, H.; Xia, X. Merkle Tree: A Fundamental Component of Blockchains. 2021 International Conference on Electronic Information Engineering and Computer Science (EIECS). LOCATION OF CONFERENCE, ChinaDATE OF CONFERENCE; pp. 556–561.
- Delgado-Von-Eitzen, C.; Fernández-Iglesias, M.J.; Anido-Rifón, L.; Mikic-Fonte, F.A. Blockchain beyond immutability: Application firewalls on ethereum-based platforms. Comput. Stand. Interfaces 2025, 95. [Google Scholar] [CrossRef]
- E. Kenler and F. Razzoli, MariaDB Essentials. Packt Publishing Ltd, 2015.
- Agencia española de protección de datos (AEPD) and European Data Protection Supervisor (EDPS), “Introduction to the hash function as a personal data pseudonymisation technique,” 2019.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




