Submitted:
08 July 2025
Posted:
09 July 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Review
3. Discussion
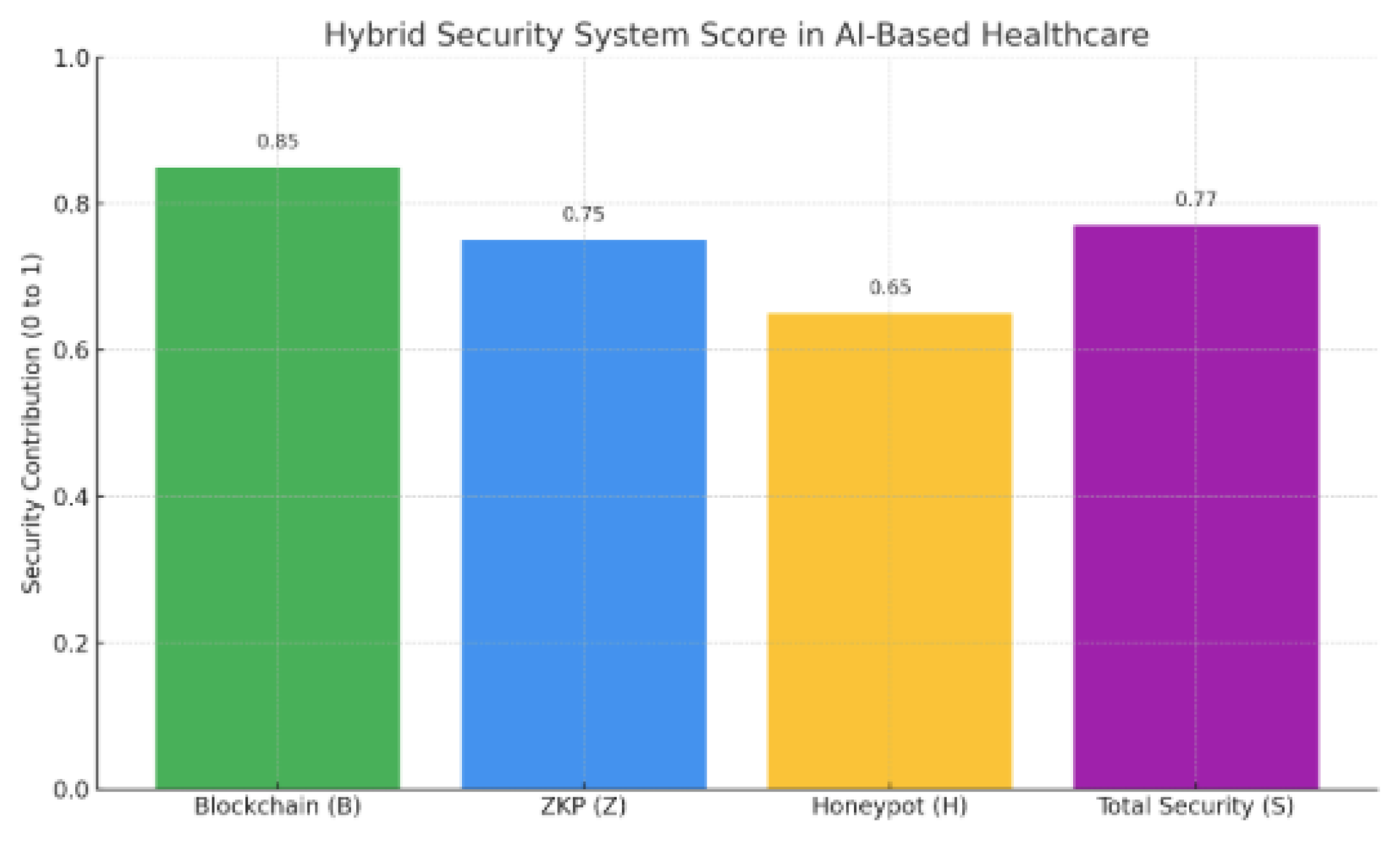
3.1. Formatting of Mathematical Components of Our Hybrid Security System
- S: Overall security level of the AI-based healthcare system.
- B: Blockchain security contribution (data integrity and immutability).
- Z: Zero-Knowledge Proof (ZKP) contribution (data confidentiality and privacy).
- H: Honeypot contribution (detection and analysis of threats).
- : Weight coefficients representing the importance of each method, such that:
3.2. Hybrid Security Score
- T: Data traceability
- I: Immutability
- P: Privacy protection
- V: Verification accuracy
- D: Threat detection rate
- A: Adversarial behavior analysis
- : Scaling factors where
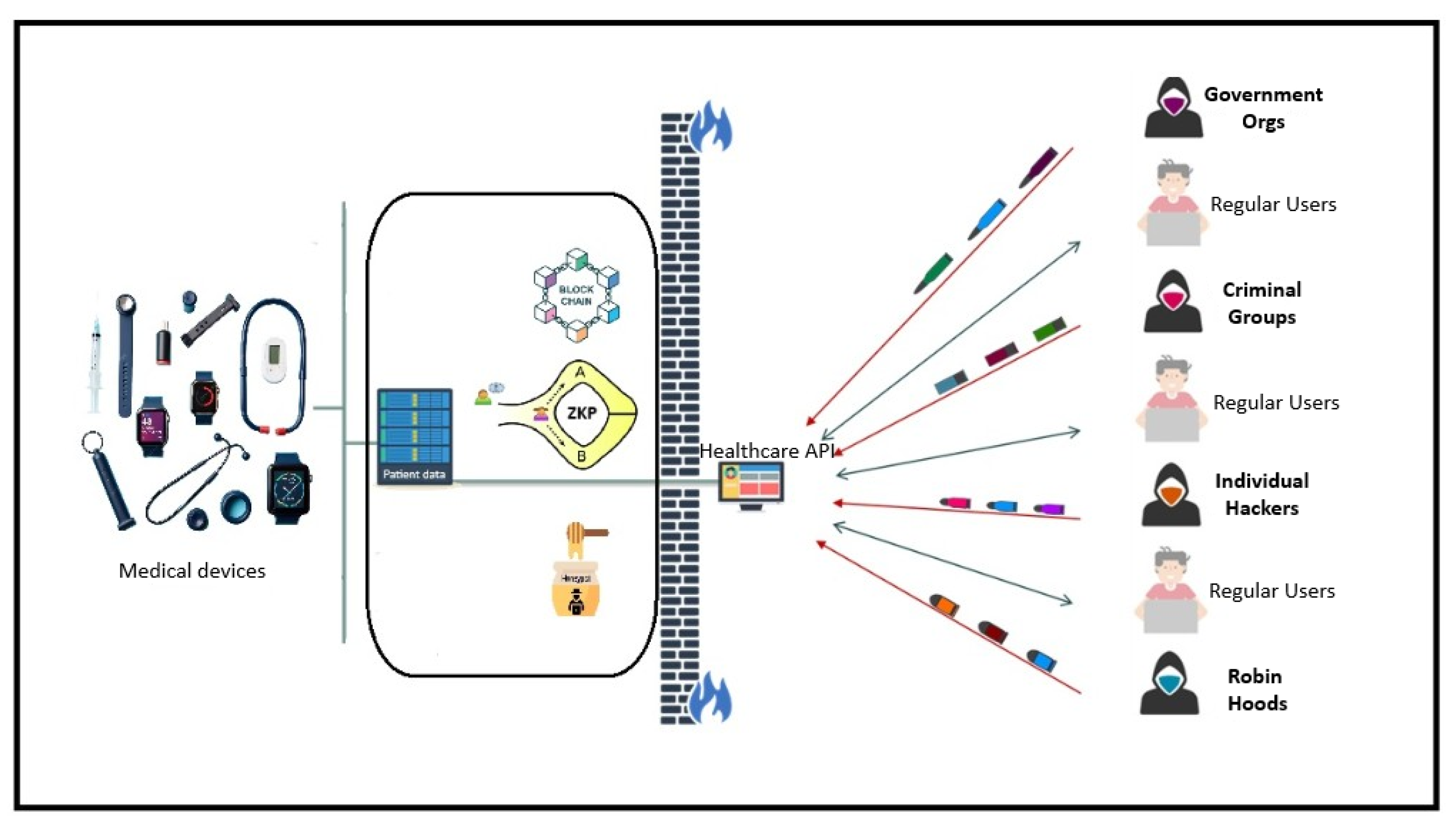
3.3. Explanation
- Blockchain (B) ensures that once data is recorded, it cannot be altered (immutability), and that every interaction is logged (traceability).
- Zero-Knowledge Proofs (Z) allow verification of computation without exposing underlying data, thereby enhancing privacy.
- Honeypots (H) serve as decoys to attract attackers and study intrusion techniques, improving adaptive response.
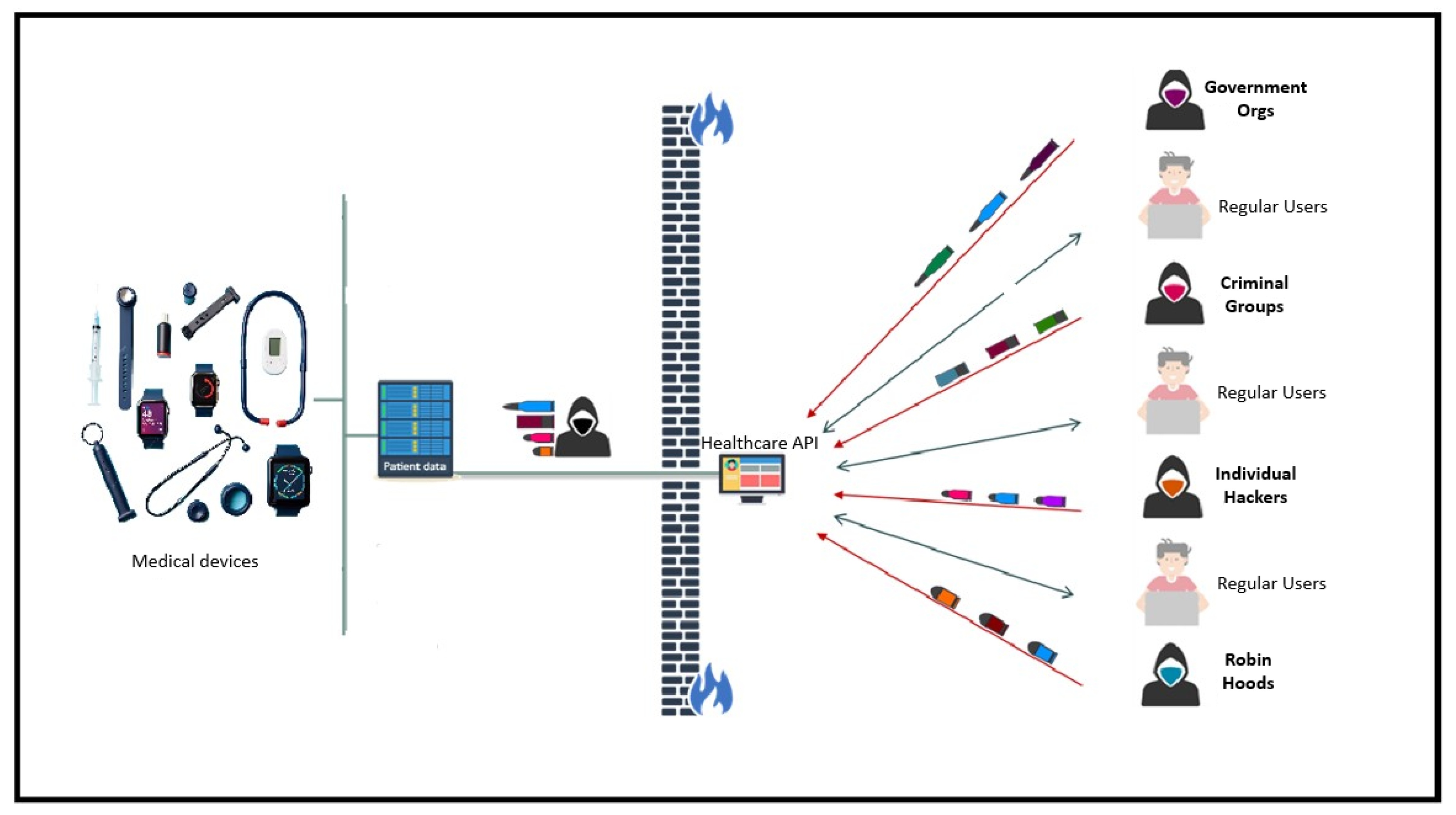
3.4. Use Case Scenario
- , ,
- , ,
3.5. Future Work
4. Conclusions
Funding
Conflicts of Interest
References
- Shinde, R.; Patil, S.; Kotecha, K.; Potdar, V.; Selvachandran, G.; Abraham, A. Securing AI-based Healthcare Systems using Blockchain Technology: A State-of-the-Art Systematic Literature Review and Future Research Directions. arXiv 2022, arXiv:2206.04793. [Google Scholar] [CrossRef]
- Petrosino, L.; Masi, L.; D’Antoni, F.; Merone, M.; Vollero, L. A zero-knowledge proof federated learning on DLT for healthcare data. Journal of Parallel and Distributed Computing 2024, 196, 104992. [Google Scholar] [CrossRef]
- Younis, F.; Miri, A. Using Honeypots in a Decentralized Framework to Defend Against Adversarial Machine-Learning Attacks. In Lecture Notes in Computer Science; 2019; pp. 24–48. [CrossRef]
- Bathula, A.; Gupta, S.K.; Merugu, S.; Saba, L.; Khanna, N.N.; Laird, J.R.; Sanagala, S.S.; Singh, R.; Garg, D.; Fouda, M.M.; et al. Blockchain, artificial intelligence, and healthcare: the tripod of future—a narrative review. Artificial Intelligence Review 2024, 57. [Google Scholar] [CrossRef]
- Arefin, S. Strengthening Healthcare Data Security with AI-Powered Threat Detection. International Journal of Scientific Research and Management (IJSRM) 2024, 12, 1477–1483. [Google Scholar] [CrossRef]
- Gerardo, E. Healthcare Cybersecurity: Data Poisoning in the Age of AI, 2024. [CrossRef]
- Arefin, S.; Simcox, M. AI-Driven Solutions for Safeguarding Healthcare Data: Innovations in Cybersecurity. International Business Research 2024, 17, 74. [Google Scholar] [CrossRef]
- Hu, Y.; Kuang, W.; Qin, Z.; Li, K.; Zhang, J.; Gao, Y.; Li, W.; Li, K. Artificial Intelligence Security: Threats and Countermeasures. ACM Computing Surveys 2021, 55, 1–36. [Google Scholar] [CrossRef]
- Martínez, A.L.; Pérez, M.G.; Ruiz-Martínez, A. A comprehensive review of the state of the art on security and privacy issues in Healthcare. ACM Computing Surveys 2022. [Google Scholar] [CrossRef]
- Kshetri, N.; Hutson, J.; G, R. healthAIChain: Improving security and safety using Blockchain Technology applications in AI-based healthcare systems. arXiv 2023. [Google Scholar] [CrossRef]
- Ali, M. Artificial Intelligence in Healthcare: Safeguarding Data and Enhancing Information Access through Cybersecurity. Global Insights in Artificial Intelligence and Computing 2025, 1, 57–80. [Google Scholar] [CrossRef]
- Ratnawita, R. Cybersecurity in the AI Era Measures Deepfake Threats and Artificial Intelligence-Based Attacks. Journal of the American Institute 2025, 2, 180–189. [Google Scholar] [CrossRef]
- Mutalib, N.H.A.; Sabri, A.Q.M.; Wahab, A.W.A.; Abdullah, E.R.M.F.; AlDahoul, N. Explainable deep learning approach for advanced persistent threats (APTs) detection in cybersecurity: a review. Artificial Intelligence Review 2024, 57. [Google Scholar] [CrossRef]
| Publication details | Attack vectors | Mitigation technique | Author conclusion |
|---|---|---|---|
| Strengthening Healthcare Data Security with AI-Powered Threat Detection [5] | Cyber threats, network anomalies | AI-driven solutions (ML, anomaly detection), continuous network monitoring, predictive analytics | AI enables proactive identification of cyber threats, automated incident response, and enhanced data security. |
| Healthcare Cybersecurity: Data Poisoning in the Age of AI [6] | Data poisoning | Innovative solutions to protect patients and institutions | Highlights security protocol weaknesses and the urgent need for innovative solutions. |
| AI-Driven Solutions for Safeguarding Healthcare Data: Innovations in Cybersecurity [7] | Cybercriminals targeting electronic health records, telemedicine, and mobile health apps | AI in healthcare data security | AI is a significant development for securing patient information in the face of increasing cyber threats. |
| Blockchain, artificial intelligence, and healthcare: the tripod of future—a narrative review [4] | Data breaches, lack of data privacy | Blockchain for secure EHR management, patient identity management, and secure data transmission; AI for clinical analysis and prediction | The fusion of blockchain and AI can address critical challenges in securing EHRs, ensuring data privacy, and facilitating secure data transmission. |
| Artificial Intelligence Security: Threats and Countermeasures [8] | Data poisoning, adversarial attacks, data breaches, AI bias | Detection & Filtering, Data Provenance & Standardized Logging, ROBN, Homomorphic encryption, E2E differential privacy, Model watermarking, Learning fair models, Bias diagnostic | AI-based systems are vulnerable to various security threats throughout the whole process, ranging from data collection to training, inference, and final deployment. |
| A Comprehensive Review of the State-of-the-Art on Security and Privacy Issues in Healthcare [9] | Malicious activities, damaging attacks, unauthorized access | Enhanced security protocols, monitoring tools, intrusion detection systems | Cybersecurity in healthcare is critical due to the sensitive nature of patient data and the increasing sophistication of cyberattacks. |
| healthAIChain: Improving security and safety using Blockchain Technology applications in AI-based healthcare systems [10] | Threats to online data, medical and patient data | Blockchain technology | Blockchain can promote highly configurable openness while retaining the highest levels of security. |
| Artificial Intelligence in Healthcare: Safeguarding Data and Enhancing Information Access through Cybersecurity [11] | Emerging cyber threats | AI for risk prediction, vulnerability detection, cryptography, compliance with essential security requirements, blockchain | AI can proactively predict risks and block chain enhances data integrity. |
| Cybersecurity in the AI Era Measures Deepfake Threats and Artificial Intelligence-Based Attacks [12] | Deepfake attacks and AI-based cyberattacks | Enhanced security protocols | Deepfake technology enables video and audio manipulation with a high level of realism, which can be used for disinformation, fraud, and threats to digital security systems. |
| Securing AI-based Healthcare Systems using Blockchain Technology: A State-of-the-Art Systematic Literature Review and Future Research Directions [13] | Lack of medical datasets for training AI models, adversarial attacks, and a lack of trust due to its black box working style | Blockchain technology | Blockchain technology can improve the reliability and trustworthiness of AI-based healthcare. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




