Submitted:
18 June 2025
Posted:
20 June 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Methods
2.1. Data Collection
2.2. Algorithm Implementation
2.2.1. Encryption and Authentication Protocols
2.2.2. Intrusion Detection Systems
2.3. Evaluation Procedures
3. Classification of Wireless LAN Security Vulnerabilities
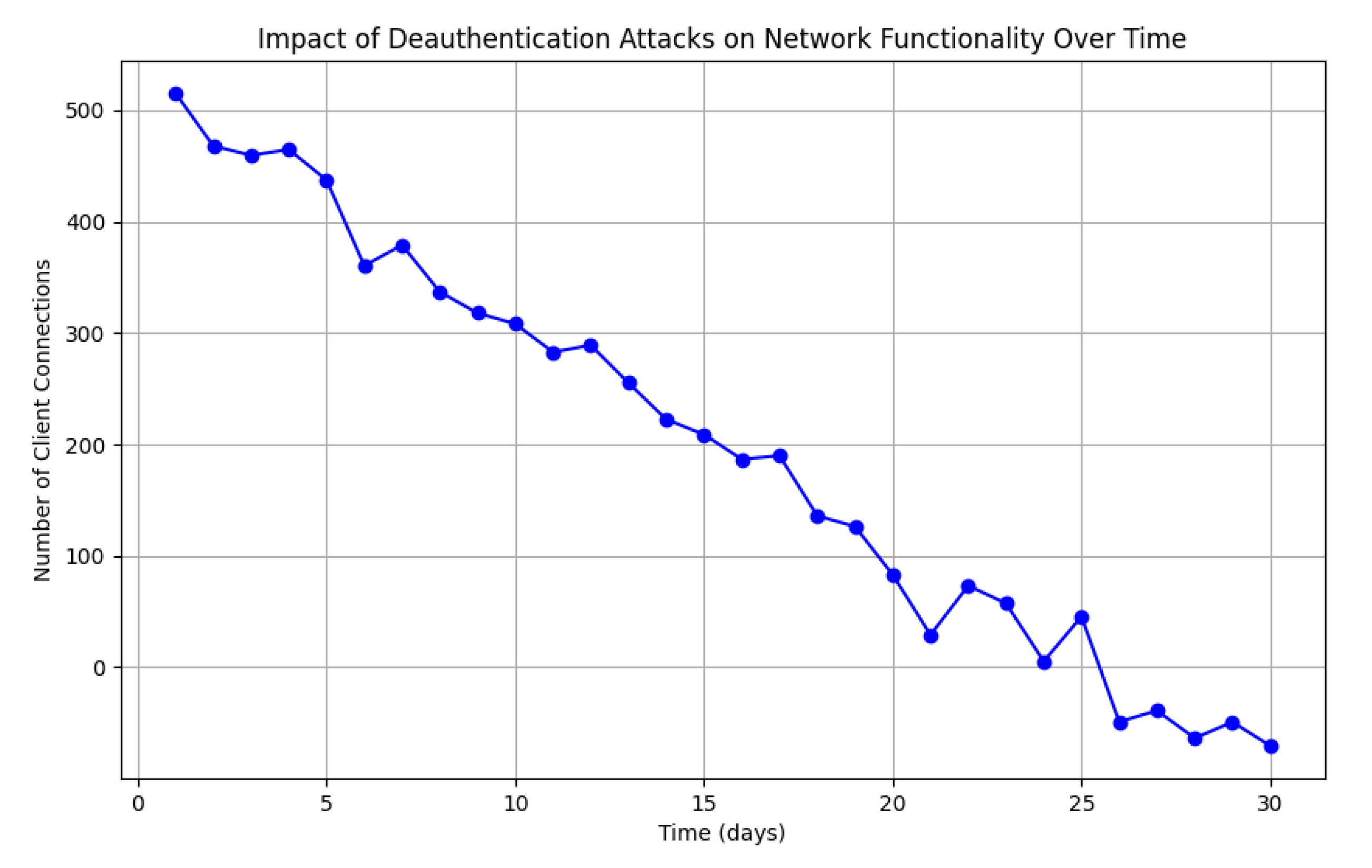
3.1. Service Disruption via Resource Exhaustion
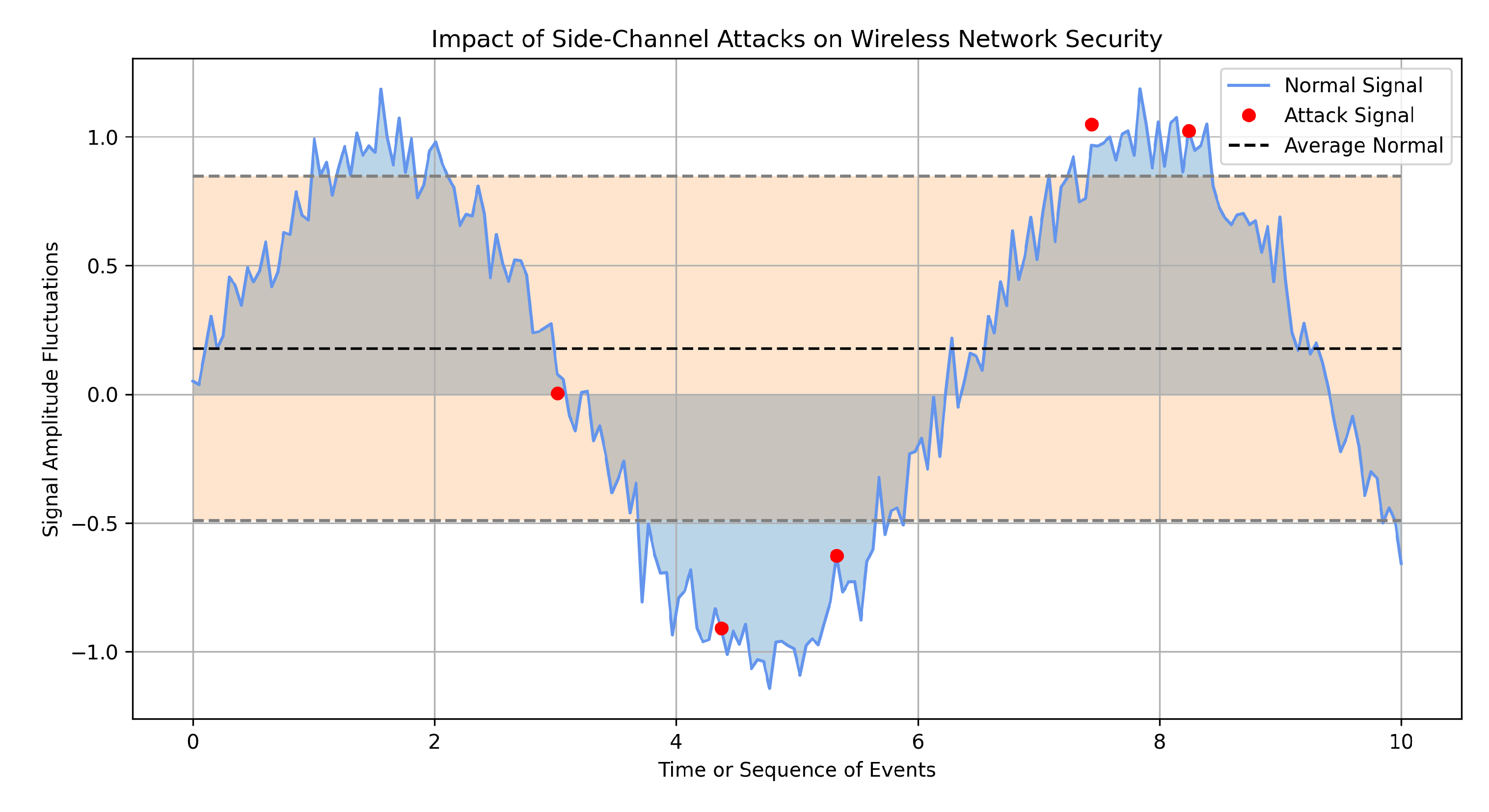
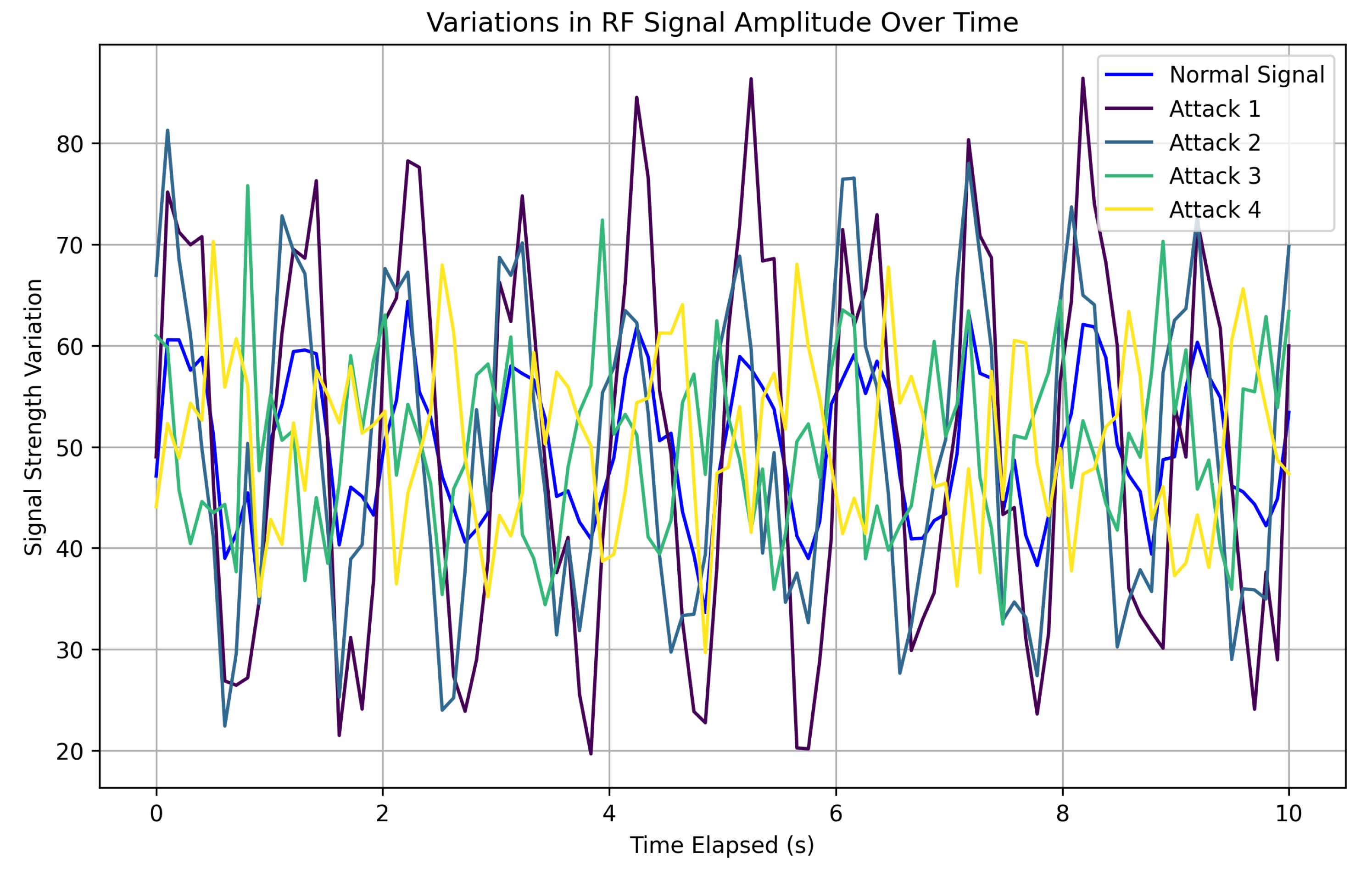
3.2. Data Interception via Channel Exploitation
3.3. Infiltration Through Unauthorized Access Points
4. Contemporary Challenges in Wireless Network Security
4.1. Exploitation via Peripheral Communication Channels
4.2. Threats in IoT Network Configurations
4.3. Exploitation of AI-Enhanced Security Frameworks
5. Defensive Architectures and Evaluation Metrics for Network Security
5.1. Advanced Encryption Frameworks and Authentication Systems
5.2. Intelligent Threat Detection Using Machine Learning
5.3. Network Segmentation and Access Control Policies
6. Analytical Assessment of WLAN Security Frameworks
6.1. Cryptographic Protocols: Performance Evaluation
6.2. Assessment of Machine Learning-Based Intrusion Detection Systems
6.3. Influence of Network Segmentation and Access Control Measures
6.4. Comprehensive Security Frameworks and Strategic Conclusions
7. Synthesis and Prospective Directions
7.1. Reassessment of Principal Findings
7.2. Constraints and Research Methodology
7.3. Implications and Future Research Avenues
References
- Stallings, W. Wireless Communication Technologies; Pearson Education: Boston, 2013. [Google Scholar]
- Gast, M.S. 802.11 Wireless Networks: The Definitive Guide; O’Reilly Media: Sebastopol, CA, 2012. [Google Scholar]
- Fluhrer, S.; Mantin, I.; Shamir, A. Weaknesses in the WEP Protocol. In Proceedings of the Proceedings of the 8th Annual International Workshop on Selected Areas in Cryptography, 2001, pp.1–24.
- Borisov, N.; Goldberg, I.; Wagner, D. Sniffing out the correct SSID: an improved attack on the 802.11 wireless encryption protocol. Proceedings of the 7th ACM conference on Computer and communications security 2001, pp. 180–189.
- Arbaugh, W.A. Your 802. In 11 Network Has No Clothes. In Proceedings of the IEEE Wireless Communications, Vol. 9; 2003; pp. 70–72. [Google Scholar]
- Vanhoef, M.; Piessens, F. Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2. In Proceedings of the Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, 2017, pp.1313–1328.
- Lai, A.; Giustiniano, D. Rogue Access Point Detection through Multiple Channel Spectral Analysis. In Proceedings of the Proceedings of IEEE INFOCOM, 2014, pp. 1267–1275.
- Hossain, M.M.; Fotouhi, M.; Hasan, R. Towards an Analysis of Security Issues, Challenges, and Open Problems in the Internet of Things. Future Generation Computer Systems 2018, 82, 395–411. [Google Scholar]
- Sicari, S.; Rizzardi, A.; Grieco, L.A.; Coen-Porisini, A. Security, privacy and trust in Internet of Things: The Road Ahead. Computer Networks 2015, 76, 146–164. [Google Scholar] [CrossRef]
- Kolias, C.; Kambourakis, G.; Stavrou, A. DDoS in the IoT: Mirai and Other Botnets. Computer 2017, 50, 80–84. [Google Scholar] [CrossRef]
- Zeng, K.; Yu, Y.; Lai, Y.C. WiFi Side-Channel Estimation for Indoor Localization. IEEE Transactions on Signal Processing 2010, 58, 3082–3094. [Google Scholar]
- Vanhoef, M.; Ronen, E. Dragonblood: Analysing the Dragonfly Handshake of WPA3 and EAP-pwd. Proceedings of the 40th IEEE Symposium on Security and Privacy 2019, pp. 517–533.
- Gardiner, A.; Nagarajan, R. A Survey of Machine Learning Techniques for Cybersecurity Intrusion Detection. IEEE Communication Surveys & Tutorials 2016, 18, 1153–1176. [Google Scholar]
- Christiansen, H.; Martinenghi, D. Simplification of Database Integrity Constraints Revisited: A Transformational Approach. Logic Based Program Synthesis and Transformation, 13th International Symposium LOPSTR 2003, Uppsala, Sweden, August 25-27, 2003, Revised Selected Papers 2004, pp. 178–197.
- Christiansen, H.; Martinenghi, D. Simplification of integrity constraints for data integration. Foundations of Information and Knowledge Systems, Third International Symposium, FoIKS 2004, Wilhelminenburg Castle, Austria, February 17-20, 2004, Proceedings 2004, 2942, 31–48. [Google Scholar]
- Bozzon, A.; Catallo, I.; Ciceri, E.; Fraternali, P.; Martinenghi, D.; Tagliasacchi, M. A Framework for Crowdsourced Multimedia Processing and Querying. Proceedings of the First International Workshop on Crowdsourcing Web Search, Lyon, France, April 17, 2012 2012, pp. 42–47.
- Calì, A.; Martinenghi, D. Conjunctive Query Containment under Access Limitations. Proceedings of Conceptual Modeling - ER 2008, 27th International Conference on Conceptual Modeling, Barcelona, Spain, October 20-24, 2008 2008, pp. 326–340.
- Scrivano, A. A Comparative Study of Recommender Systems under Big Data Constraints. arXiv preprint arXiv:2504.08457, arXiv:2504.08457 2025.
- Zhang, C.; Wang, L.; Shi, Y.; Zhang, N.; Huang, W.; Yang, B.; Zhang, X.; Wu, K.; Ji, C. A Survey on Machine Learning for Neuromorphic Computing: Algorithms and Architectures. IEEE Access 2019, 7, 64820–64834. [Google Scholar]
- Vieira, M.A.; Vieira, L.N.; Loureiro, A.A.F. Security mechanisms and issues for mobile ad hoc networks: threats, attacks and solutions. International Journal of Wireless and Mobile Computing 2009, 3, 388–399. [Google Scholar]
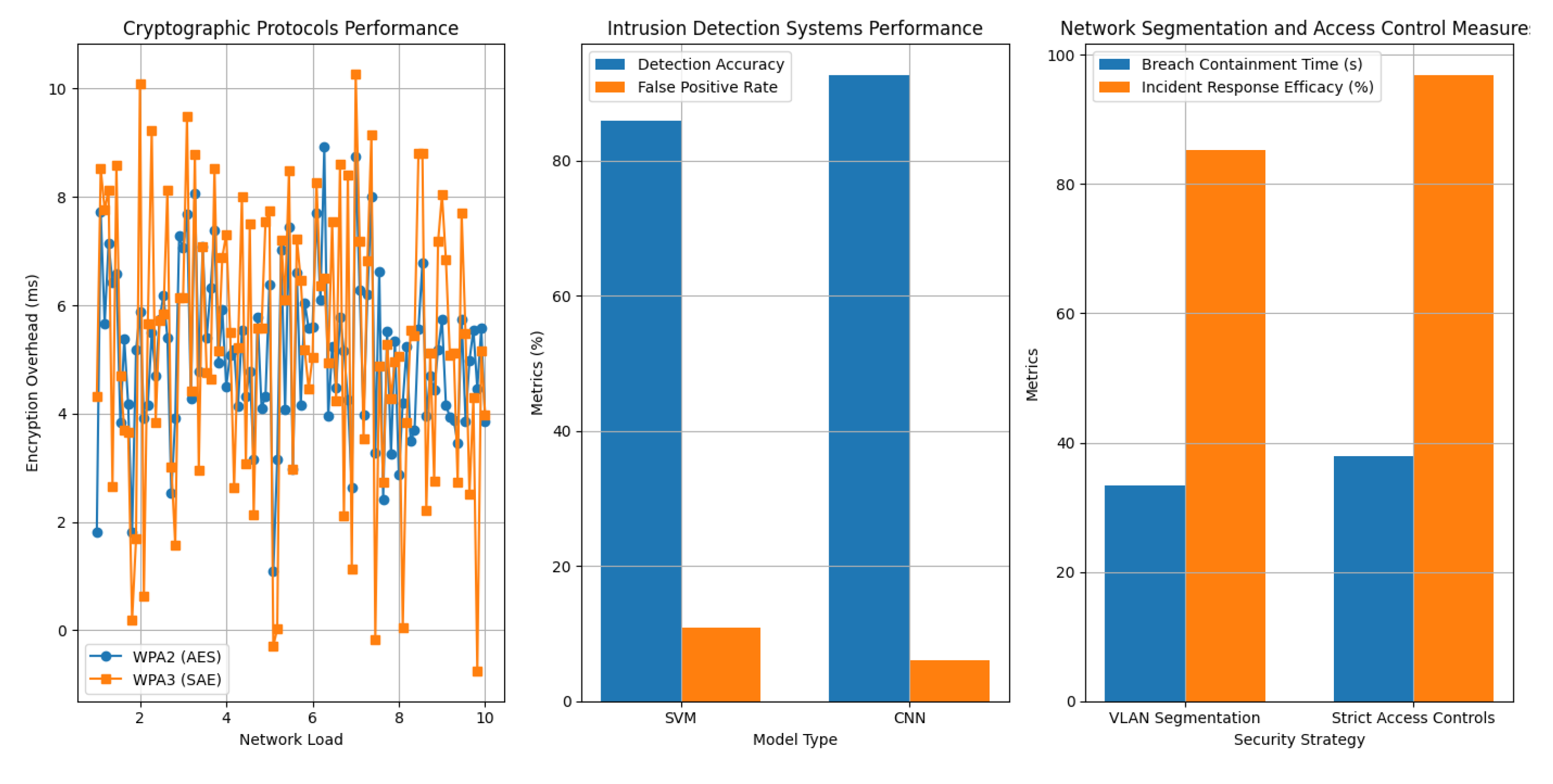
| Protocol | Encryption Overhead (ms) | Throughput (Mbps) | Handshake Success Rate (%) |
|---|---|---|---|
| WPA2 (AES) | 5.6 | 150 | 98 |
| WPA3 (SAE) | 6.2 | 145 | 99 |
| Model | Detection Accuracy (%) | False Positive Rate (%) | Recall (%) |
|---|---|---|---|
| SVM | 93 | 7.5 | 90 |
| CNN | 96 | 5.2 | 94 |
| Security Strategy | Breach Containment Time (s) | Incident Response Efficacy (%) |
|---|---|---|
| VLAN Segmentation | 22 | 91 |
| Strict Access Controls | 18 | 94 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




