Submitted:
03 June 2025
Posted:
04 June 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- 1)
- Integrates LLM-based anomaly detection with semantic explanation to unify diverse log formats and support interpretable, context-aware threat analysis.
- 2)
- Employs Retrieval-Augmented Generation (RAG) and a suite of internal tools for recursive, multi-step investigation across heterogeneous logs.
- 3)
- Integrates a planning-capable LLM agent that generates human-readable explanations, allowing transparent and autonomous threat interpretation.
1.1. Research Challenges
- 1)
- Analyzing Heterogeneous and Unstructured Logs (Q1)
- 2)
- Lack of Interpretability in Log Anomaly Detection (Q2)
- 3)
- Limits of Static and Passive Inference Models (Q3)
1.2. Contributions
- Template-free Semantic Log Interpretation (C1)
- 2.
- Context-enriched Semantic Reasoning for Explanation (C2)
- 3.
- Autonomous and Recursive Threat Investigation (C3)
2. Related Works
2.1. Traditional and Deep Learning-Based Log Anomaly Detection
2.2. Trnasformer-Based Log Anomaly Detection
2.3. LLM Based AI Agent
3. Proposed Method
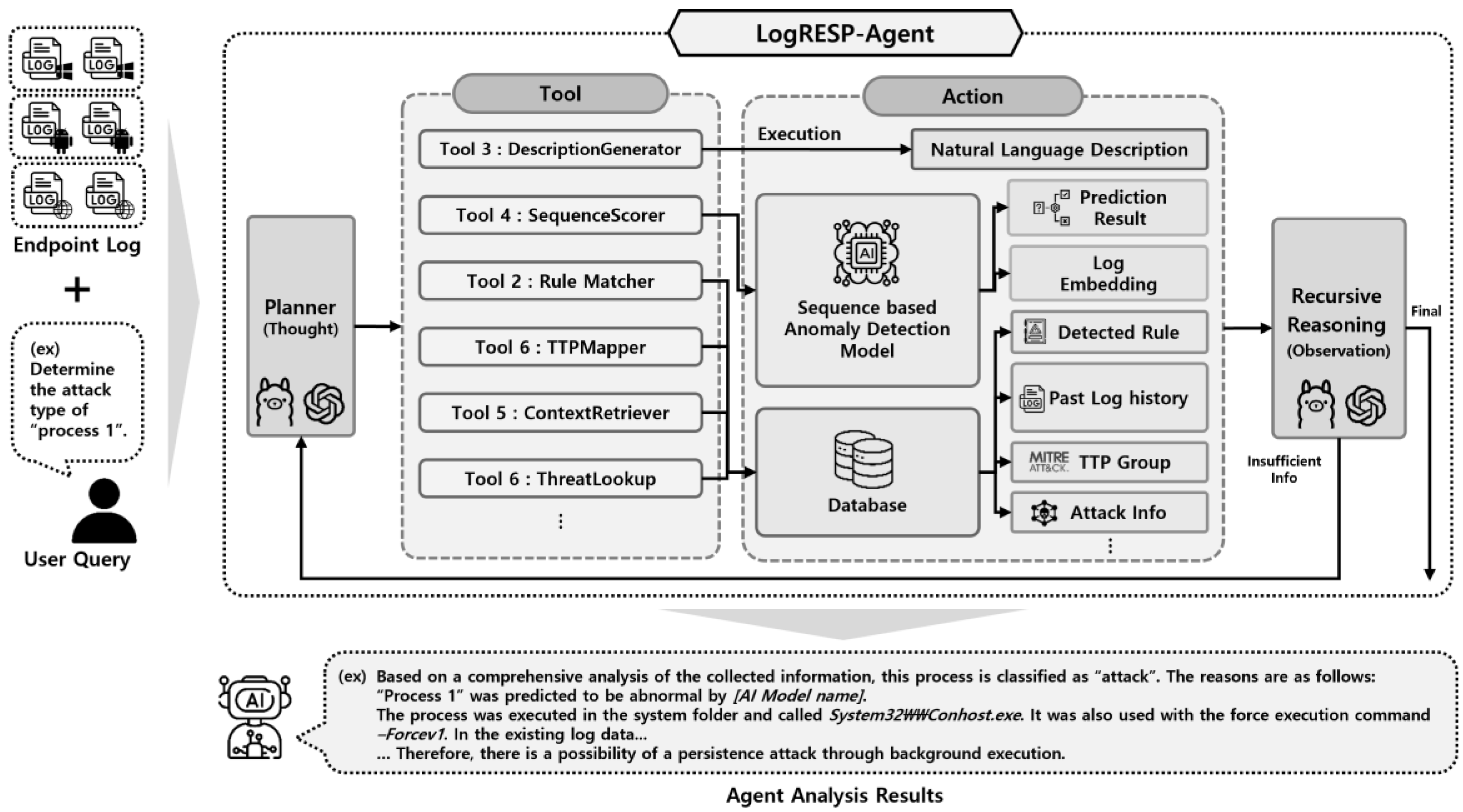
3.1. Recursive Reasoning Framework for Log Analysis
| Algorithm 1: Recursive Anomaly Analysis Loop | |
|
Input: Semantic Log Description D, Analysis Goal G Output: Final Explanation E 1. Initialize ObservationList ← [ ] 2. Initialize ThoughtHistory ← [ ] 3. While True do Stage 1: Planning a. Generate a new hypothesis ht: thought ← GenerateThought(D, G, ObservationList) b. Select the most relevant tool: tool ← SelectTool(thought) Stage 2: Execution c. Invoke the selected tool and get result: result ← Invoke(tool, D) Stage 3: Reasoning d. Update observation and thought history: ObservationList ← ObservationList ∪ {result} ThoughtHistory ← ThoughtHistory ∪ {thought} e. Determine if reasoning can be concluded: if IsSufficient(result, ObservationList): E ← GenerateExplanation(D, G, ObservationList) break 4. Return E |
- 1)
- Planning Strategy Formulation
- 2)
- Context-Aware Execution
- 3)
- Reasoning via Recursive Threat Interpretation
- Autonomous Planning: The agent independently determines which tools to invoke and in what order.
- Dynamic Context Expansion: Relevant external information is retrieved as needed to fill knowledge gaps.
- Recursive Hypothesis Refinement: Each cycle incorporates new observations to update and improve its hypothesis
- Goal-Directed Reasoning: All steps are explicitly tied to the initial analysis objective, ensuring coherence
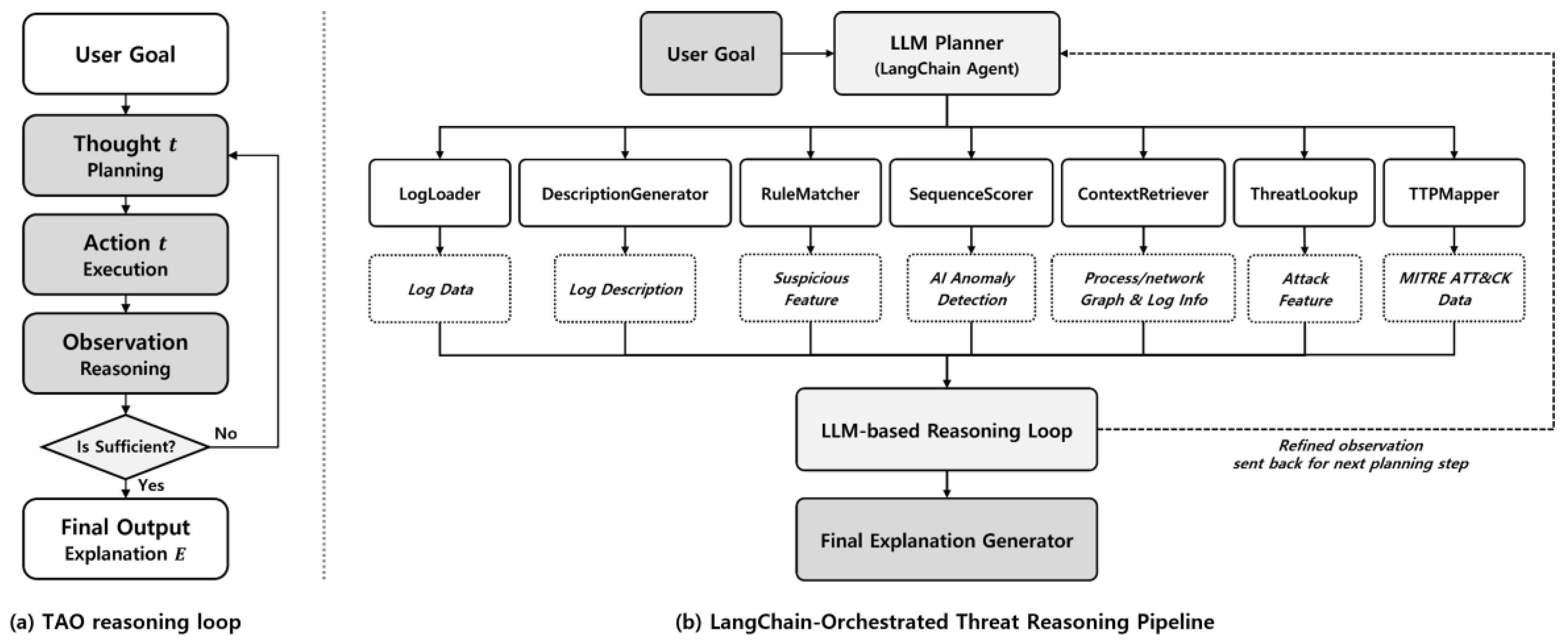
1.2. Tool-Oriented Semantic Transformation and Anomaly Detection
3.3. Dynamic Analysis Cycle and Final Reasoning Output
- (a)
- Summary: A high-level decision that characterizes the event as benign, suspicious, or indicative of an attack.
- (b)
- Evidence: A focused set of key observations that played a central role in guiding the agent’s assessment.
- (c)
- Reasoning Trace: A chronological outline of the agent’s investigative steps, detailing the sequence of tool invocations and the conclusions drawn at each stage.
- (d)
- Mapped Threat Context (if any): Behavioral correlations to known adversarial techniques, such as MITRE ATT&CK tactics, malware families, or threat actor patterns.
4. Implementation
4.1. Datasets
- 1.
- Monster-THC Endpoint Log
- 2.
- EVTX-ATTACK-SAMPLES [42]
| Dataset | Category (Process/Tactic) |
Benign | Malicious | Total |
|---|---|---|---|---|
| Monster-THC | Chrome | 30,036 | 150 | 30,186 |
| Edge | 1,192 | 61 | 1,253 | |
| Hwp | 2,044 | 76 | 2,120 | |
| EVTX-ATTACK-SAMPLE | Command and Control | - | 440 | 440 |
| Credential Access | - | 218 | 218 | |
| Defense Evasion | - | 283 | 283 | |
| Discovery | - | 146 | 146 | |
| Execution | - | 381 | 381 | |
| Lateral Movement | - | 1,122 | 1,122 | |
| Persistence | - | 163 | 163 | |
| Privilege Escalation | - | 414 | 414 |
4.2. Experimental Configuration: Agent Components and Baselines
- 1)
- AI Agent Architecture
- 2)
- Baseline Methods
- (a)
- Unsupervised anomaly detection models. We included an Autoencoder and LogBERT as representative unsupervised methods. The Autoencoder detects anomalies based on reconstruction error, while LogBERT leverages masked language modeling to identify sequence-level deviations in system logs.
- (b)
- Supervised machine learning classifiers. For multi-class classification, we trained standard classifiers including MLP, Random Forest, and XGBoost using structured log features. These models were selected for their widespread use in intrusion detection tasks and their strong performance on tabular data.
- (c)
- Agent-based ensemble variants. In addition to standalone models, we evaluated two configurations of the proposed AI Agent: one using LogBERT for binary anomaly detection, and the others using either Random Forest or XGBoost for multi-class classification. These variants retain the same modular reasoning structure, with only the scoring component replaced.
4.3. Detection Performance Evaluation
- 1)
- Anomaly Detection Performance on Monster-THC Dataset
- Chrome logs: LogRESP-Agent achieved perfect detection (TPR = 1.0, F1 = 1.0) with zero false positives, whereas LogBERT and Autoencoder recorded significantly lower F1-scores (0.81 and 0.73, respectively).
- Edge logs: The agent maintained strong performance (F1 = 0.94, TPR = 0.88), outperforming both baselines, which had comparable F1-scores (0.86) but lower recall.
- Hwp: On this more diverse process type, LogRESP-Agent again led with TPR 0.94 and F1-score 0.97, while LogBERT underperformed (TPR 0.68, F1 0.81), and Autoencoder plateaued at F1 0.86.
- 2)
- Multi-class Classification Performance on EVTX-ATTACK-SAMPLES
- Command and Control: All models performed well (F1 ≥ 0.98), but only the agent variant achieved perfect detection (TPR = 1.0, F1 = 1.0) with zero false positives.
- Credential Access: A challenging tactic for baselines—MLP and RF scored F1 ≤ 0.87. The agent variants improved this to 0.96 (RF) and 0.97 (XGBoost) with very low FPRs (≤ 0.002).
- Defense Evasion and Persistence: Involving stealthy or multi-stage behaviors, these classes saw consistent improvements from the agent variants, reaching F1 = 0.97 while keeping FPRs ≤ 0.003.
- Discovery and Execution: Easier to detect, all models performed well, but LogRESP-Agent again maintained near-perfect scores (F1 ≥ 0.99, FPR = 0.0).
- In Lateral Movement and Privilege Escalation: While some baselines showed reduced F1 (0.87–0.90), LogRESP-Agent sustained F1 = 0.99–1.0 with minimal false positives.
4.4. Explanation Analysis and Interpretability Evaluation
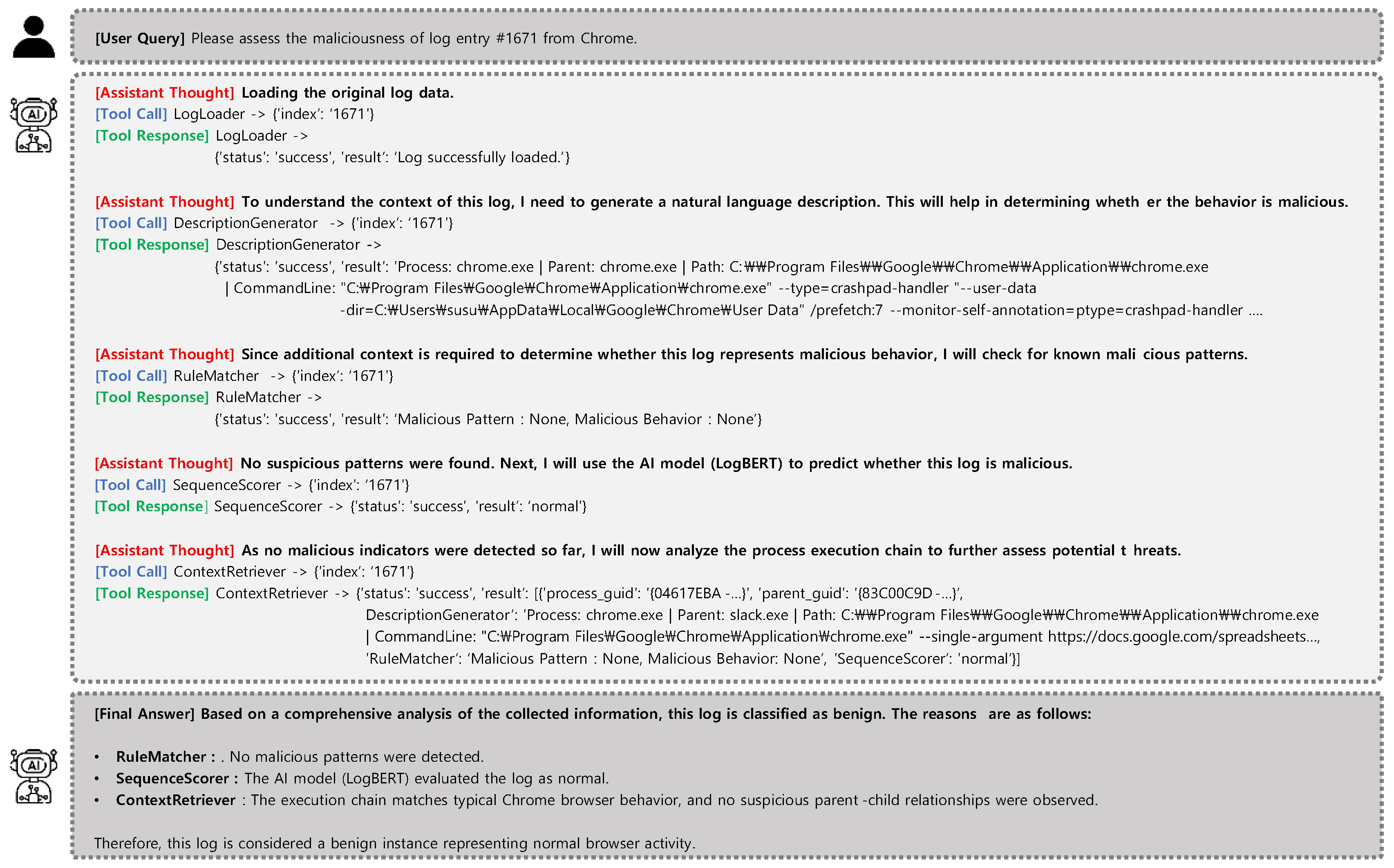
- 1)
- Case 1. Normal Chrome Execution (Monster-THC, Log ID: 1671)
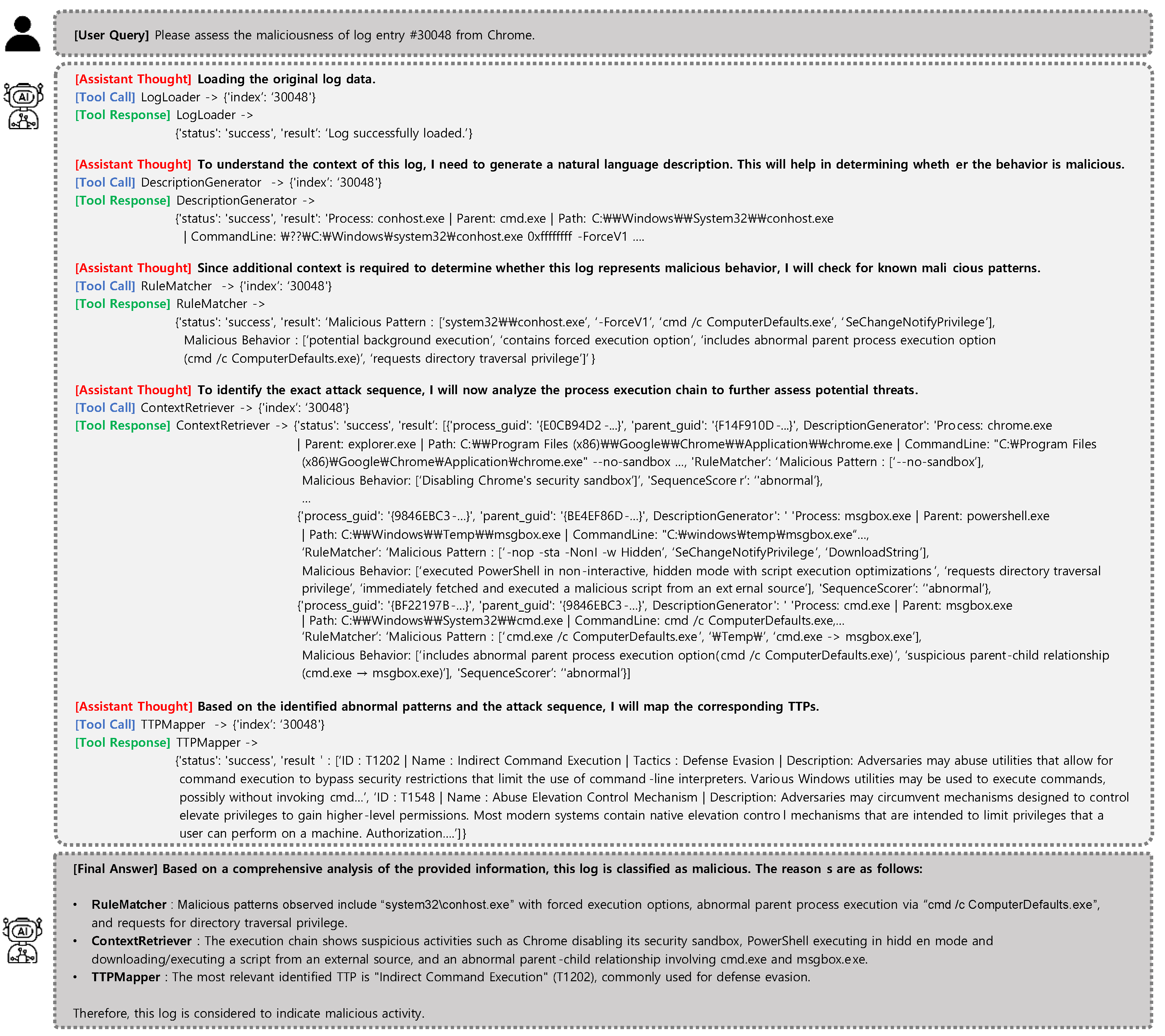
- 2)
- Case 2. Privilege Escalation via Chrome (Monster-THC, Log ID: 30048)
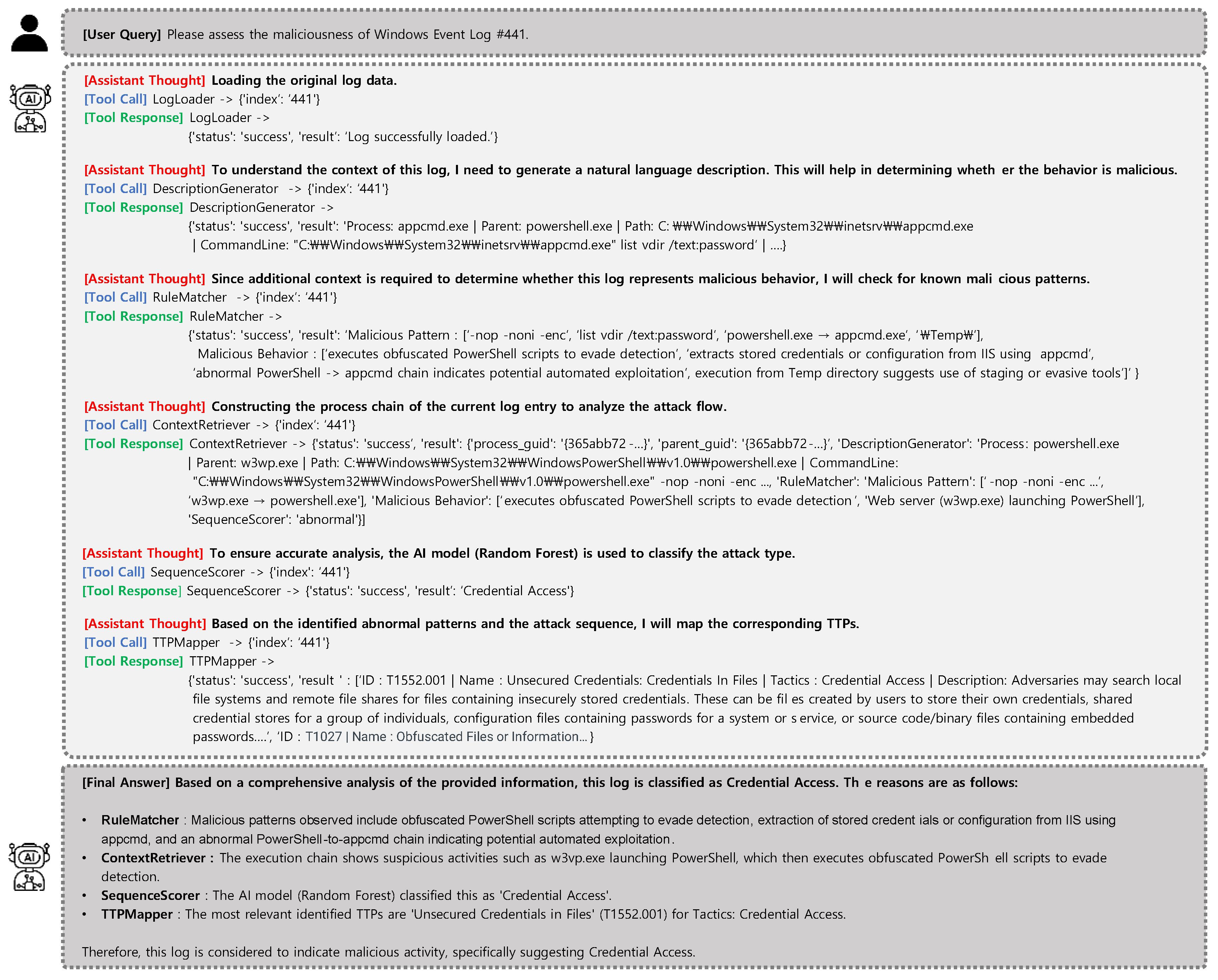
- 3)
- Case 3. Credential Access via IIS Tooling (EVTX, Log ID: 441)
5. Discussion
- 1)
- Practical Value and Comparative Advantages
- 2)
- Current
- 3)
- Limitations and Future Directions
6. Conclusion
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Mandru, S. K. Machine Learning and AI in Endpoint Security: Analyzing the use of AI and machine learning algorithms for anomaly detection and threat prediction in endpoint security. Journal of Scientific and Engineering Research 2021, 8(3), 264-270.
- Karantzas, G.; & Patsakis, C. An empirical assessment of endpoint detection and response systems against advanced persistent threats attack vectors. Journal of Cybersecurity and Privacy 2021, 1(3), 387-421. [CrossRef]
- Kara, I. Read the digital fingerprints: log analysis for digital forensics and security. Computer Fraud & Security 2021, 2021(7), 11-16. [CrossRef]
- Smiliotopoulos, C.; Kambourakis, G.; Kolias, C. Detecting lateral movement: A systematic survey. Heliyon 2024, 10(4). [CrossRef]
- Lee, W.; Stolfo, S. J. A framework for constructing features and models for intrusion detection systems. ACM transactions on Information and system security (TiSSEC) 2000, 3(4), 227-261. [CrossRef]
- Hofmeyr, S. A.; Forrest, S.; Somayaji, A. Intrusion detection using sequences of system calls. Journal of computer security 1998, 6(3), 151-180. [CrossRef].
- Hussein, S. A.; Sándor, R. R. Anomaly detection in log files based on machine learning techniques. Journal of Electrical Systems 2024, 20(3s), 1299-1311.
- Himler, P.; Landauer, M.; Skopik, F.; Wurzenberger, M. Anomaly detection in log-event sequences: A federated deep learning approach and open challenges. Machine Learning with Applications 2024, 16, 100554. [CrossRef]
- Wang, Z.; Tian, J.; Fang, H.; Chen, L.; Qin, J. LightLog: A lightweight temporal convolutional network for log anomaly detection on the edge. Computer Networks 2022, 203, 108616. [CrossRef]
- Lu, S.; Wei, X.; Li, Y.; Wang, L. Detecting anomaly in big data system logs using convolutional neural network. In 2018 IEEE 16th Intl Conf on Dependable, Autonomic and Secure Computing, 16th Intl Conf on Pervasive Intelligence and Computing, 4th Intl Conf on Big Data Intelligence and Computing and Cyber Science and Technology Congress (DASC/PiCom/DataCom/CyberSciTech), Athens, Greece, 12-15 August 2018 (pp. 151-158). IEEE. [CrossRef].
- Meng, W.; Liu, Y.; Zhu, Y.; Zhang, S.; Pei, D.; Liu, Y.; etc. Loganomaly: Unsupervised detection of sequential and quantitative anomalies in unstructured logs. In IJCAI, Macao, China, 10-16 August 2019 (Vol. 19, No. 7, pp. 4739-4745).
- Zhang, X.; Xu, Y.; Lin, Q.; Qiao, B.; Zhang, H.; Dang, Y.; etc. Robust log-based anomaly detection on unstable log data. In Proceedings of the 2019 27th ACM joint meeting on European software engineering conference and symposium on the foundations of software engineering, Tallinn, Estonia, 26 – 30 August 2019 (pp. 807-817). [CrossRef].
- Gu, S.; Chu, Y.; Zhang, W.; Liu, P.; Yin, Q.; Li, Q. Research on system log anomaly detection combining two-way slice GRU and GA-attention mechanism. In 2021 4th International Conference on Artificial Intelligence and Big Data (ICAIBD), Chengdu, China , 28-31 May 2021 (pp. 577-583). [CrossRef].
- Farzad, A., & Gulliver, T. A. Unsupervised log message anomaly detection. ICT Express 2020, 6(3), 229-237. [CrossRef]
- Du, M.; Li, F.; Zheng, G.; Srikumar, V. Deeplog: Anomaly detection and diagnosis from system logs through deep learning. In Proceedings of the 2017 ACM SIGSAC conference on computer and communications security, Dallas, Texas, USA, 30 October 2017- 3 November 2017 (pp. 1285-1298). [CrossRef].
- Wan, Y.; Liu, Y.; Wang, D.; Wen, Y. Glad-paw: Graph-based log anomaly detection by position aware weighted graph attention network. In Pacific-asia conference on knowledge discovery and data mining, Delhi, India , 11-14 May 2021 (pp. 66-77).
- Guo, H.; Yuan, S.; Wu, X. Logbert: Log anomaly detection via bert. In 2021 international joint conference on neural networks (IJCNN), Shenzhen, China, 18-22 July 2021 (pp. 1-8). [CrossRef].
- Han, X.; Yuan, S.; Trabelsi, M. Loggpt: Log anomaly detection via gpt. In 2023 IEEE International Conference on Big Data (BigData), Sorrento, Italy, 15-18 December 2023 (pp. 1117-1122). [CrossRef].
- Almodovar, C.; Sabrina, F.; Karimi, S.; Azad, S. LogFiT: Log anomaly detection using fine-tuned language models. IEEE Transactions on Network and Service Management 2024, 21(2), 1715-1723. [CrossRef].
- Ma, X.; Li, Y.; Keung, J.; Yu, X.; Zou, H.; Yang, Z.; etc. Practitioners' Expectations on Log Anomaly Detection. arXiv preprint arXiv:2412.01066 2024.
- Zamanzadeh Darban, Z.; Webb, G. I.; Pan, S.; Aggarwal, C.; Salehi, M. Deep learning for time series anomaly detection: A survey. ACM Computing Surveys 2024, 57(1), 1-42.
- Zang, R.; Guo, H.; Yang, J.; Liu, J.; Li, Z.; Zheng, T.; etc. MLAD: A Unified Model for Multi-system Log Anomaly Detection. arXiv preprint arXiv:2401.07655 2024.
- Yue, M. A Survey of Large Language Model Agents for Question Answering. arXiv preprint arXiv:2503.19213 2025.
- Masterman, T.; Besen, S.; Sawtell, M.; Chao, A. The landscape of emerging ai agent architectures for reasoning, planning, and tool calling: A survey. arXiv preprint arXiv:2404.11584 2024.
- Cemri, M.; Pan, M. Z.; Yang, S.; Agrawal, L. A.; Chopra, B.; Tiwari, R.; etc. Why Do Multi-Agent LLM Systems Fail?. arXiv preprint arXiv:2503.13657 2025.
- Liang, Y.; Zhang, Y.; Xiong, H.; Sahoo, R. Failure prediction in ibm bluegene/l event logs. Seventh IEEE International Conference on Data Mining (ICDM 2007). Omaha, Nebraska. 28-31 October 2007 (pp. 583-588). [CrossRef].
- Wang, J.; Tang, Y.; He, S.; Zhao, C.; Sharma, P. K.; Alfarraj, O.; Tolba, A. LogEvent2vec: LogEvent-to-vector based anomaly detection for large-scale logs in internet of things. Sensors 2020. 20(9), 2451. [CrossRef]
- Chen, M.; Zheng, A. X.; Lloyd, J.; Jordan, M. I.; Brewer, E. Failure diagnosis using decision trees. In International Conference on Autonomic Computing, New York, USA, 17-18 May 2004 (pp. 36-43) [CrossRef].
- Dani, M. C.; Doreau, H.; Alt, S. K-means application for anomaly detection and log classification in hpc. In Advances in Artificial Intelligence: From Theory to Practice: 30th International Conference on Industrial Engineering and Other Applications of Applied Intelligent Systems, Arras, France, 27-30 June 2017 (Part 2, 30, pp. 201-210).
- Mishra, A. K.; Bagla, P.; Sharma, R.; Pandey, N. K.; Tripathi, N. Anomaly Detection from Web Log Data Using Machine Learning Model. In 2023 7th International Conference on Computer Applications in Electrical Engineering-Recent Advances (CERA), Roorkee, India, 27-29 October 2023 (pp. 1-6). [CrossRef].
- Karev, D.; McCubbin, C.; Vaulin, R. Cyber threat hunting through the use of an isolation forest. In Proceedings of the 18th international conference on computer systems and technologies, Ruse, Bulgaria, 23 – 24 June 2017 (pp. 163-170). [CrossRef].
- Zhang, L.; Cushing, R.; de Laat, C.; Grosso, P. A real-time intrusion detection system based on OC-SVM for containerized applications. In 2021 IEEE 24th international conference on computational science and engineering (CSE), Shenyang, China, 20-22 October 2021 (pp. 138-145). [CrossRef].
- Kramer, M. A. Nonlinear principal component analysis using autoassociative neural networks. AIChE journal 1991, 37(2), 233-243. [CrossRef]
- Du, M.; Li, F.; Zheng, G.; Srikumar, V. Deeplog: Anomaly detection and diagnosis from system logs through deep learning. In Proceedings of the 2017 ACM SIGSAC conference on computer and communications security, Dallas, Texas, USA, 30 October 2017- 3 November 2017 (pp. 1285-1298). [CrossRef].
- Meng, W.; Liu, Y.; Zhu, Y.; Zhang, S.; Pei, D.; Liu, Y.; etc. Loganomaly: Unsupervised detection of sequential and quantitative anomalies in unstructured logs. In IJCAI, Macao, China, 10-16 August 2019 (Vol. 19, No. 7, pp. 4739-4745).
- Huang, S.; Liu, Y.; Fung, C.; He, R.; Zhao, Y.; Yang, H.; Luan, Z. Hitanomaly: Hierarchical transformers for anomaly detection in system log. IEEE transactions on network and service management 2020, 17(4), 2064-2076. [CrossRef].
- Le, V. H.; Zhang, H. Log-based anomaly detection without log parsing. In 2021 36th IEEE/ACM International Conference on Automated Software Engineering (ASE), Melbourne, Australia, 15-19 November 2021 (pp. 492-504) [CrossRef].
- Chen, S.; Liao, H. Bert-log: Anomaly detection for system logs based on pre-trained language model. Applied Artificial Intelligence 2022, 36(1), 2145642. [CrossRef]
- Li, Y.; Xiang, Z.; Bastian, N. D.; Song, D.; Li, B. IDS-Agent: An LLM Agent for Explainable Intrusion Detection in IoT Networks. In NeurIPS 2024 Workshop on Open-World Agents 2024.
- Kurnia, R.; Widyatama, F.; Wibawa, I. M.; Brata, Z. A.; Nelistiani, G. A.; Kim, H. Enhancing Security Operations Center: Wazuh Security Event Response with Retrieval-Augmented-Generation-Driven Copilot. Sensors (Basel, Switzerland) 2025, 25(3), 870. [CrossRef]
- Song, C.; Ma, L.; Zheng, J.; Liao, J.; Kuang, H.; Yang, L. Audit-LLM: Multi-Agent Collaboration for Log-based Insider Threat Detection. arXiv preprint arXiv:2408.08902 2024.
- EVTX-ATTACK-SAMPLES. Available online: https://github.com/sbousseaden/EVTX-ATTACK-SAMPLES (accessed on 30 May 2025).
| Tool | Function |
|---|---|
| LogLoader | Structures raw log data from system or endpoint sources for further analysis |
| RuleMatcher | Applies rules to identify known malicious signatures |
| DescriptionGenerator | Converts structured logs into natural language event summaries |
| SequenceScorer | Scores log sequences based on behavioral anomalies using pretrained models |
| ContextRetriever | Gathers related process logs (e.g., parent/child) to support correlation |
| TTPMapper | Maps observed behaviors to MITRE ATT&CK TTPs |
| ThreatLookup | Fetches background information on threats or attacker tools from threat intel |
| Scenario | Agent Behavior | Final Output |
|---|---|---|
| Attack | • Aggregate anomaly indicators • Cross-validate with TTP patterns • Confirm malicious intent |
Identifies associated MITRE ATT&CK TTP(s) and describes supporting evidence in a structured explanation |
| Benign | • Review contextual consistency • Rule out attack hypotheses • Confirm benign justification |
Explains why the event is benign (e.g., scheduled task, admin script), referencing safe patterns or known whitelist behaviors |
|
Ambiguous /Low Confidence |
• Detect insufficient or conflictingsignals • Identify missing context • Defer or extend analysis |
Continues reasoning or outputs "inconclusive" with explanation of missing context or low-confidence factors |
| Tool Name | Role in Reasoning Loop |
Function | Output Format |
|---|---|---|---|
| LogLoader | Data ingestion | Standardizes input logs into a unified format for downstream processing | Structured log in standard format |
| RuleMatcher | Signature-based detection (early stage) |
Applies YARA/Sigma/custom rules to detect known suspicious patterns in process logs | Match result, rule metadata |
| Description Generator |
Semantic summarization | Generates natural language summaries by pairing key log features with values to support semantic reasoning | Natural language sentence |
| SequenceScorer | Behavior modeling | Computes anomaly scores using LogBERT (anomaly detection) or classifies using RF/XGBoost (multi-class) | Score (0–1) or class label |
| ContextRetriever | Context expansion | Gathers related events (parent/child processes) to support behavioral correlation. | Related logs information (dict) |
| TTPMapper | Threat behavior mapping |
Maps log behavior to MITRE ATT&CK techniques via cosine similarity between log descriptions and TTP embeddings (MiniLM-L12-v2). | Mapped TTP ID and label, Description |
| ThreatLookup | Intelligence enrichment |
Provides concise descriptions of known TTPs and malware for enriched interpretation. | Textual threat summary |
| Process | Autoencoder | LogBERT | LogRESP-Agent (Proposed) | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| TPR | FPR | Acc | F1 | TPR | FPR | Acc | F1 | TPR | FPR | Acc | F1 | |
| Chrome | 0.79 | 0.002 | 0.99 | 0.73 | 0.71 | 0.0002 | 0.99 | 0.81 | 1.0 | 0.0 | 1.0 | 1.0 |
| Edge | 0.78 | 0.002 | 0.98 | 0.86 | 0.75 | 0.0 | 0.98 | 0.86 | 0.88 | 0.0 | 0.99 | 0.94 |
| Hwp | 0.78 | 0.002 | 0.99 | 0.86 | 0.68 | 0.0005 | 0.99 | 0.81 | 0.94 | 0.0 | 0.99 | 0.97 |
| All | 0.78 | 0.0002 | 0.98 | 0.82 | 0.71 | 0.0002 | 0.99 | 0.83 | 0.94 | 0.0 | 0.99 | 0.97 |
| Tactic | MLP | RF | XGBoost | LogRESP-Agent + RF (Proposed) |
LogRESP-Agent + XGBoost (Proposed) |
|||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| TPR | FPR | Acc | F1 | TPR | FPR | Acc | F1 | TPR | FPR | Acc | F1 | TPR | FPR | Acc | F1 | TPR | FPR | Acc | F1 | |
| Command and Control | 0.98 | 0.004 | 0.99 | 0.98 | 0.97 | 0.0 | 0.99 | 0.98 | 0.99 | 0.0 | 0.99 | 0.99 | 0.99 | 0.0 | 0.99 | 0.99 | 1.0 | 0.0 | 1.0 | 1.00 |
| Credential Access | 0.81 | 0.017 | 0.97 | 0.80 | 0.81 | 0.003 | 0.98 | 0.87 | 0.96 | 0.003 | 0.99 | 0.96 | 0.96 | 0.002 | 0.98 | 0.96 | 0.97 | 0.002 | 0.99 | 0.97 |
| Defense Evasion | 0.87 | 0.007 | 0.98 | 0.90 | 0.91 | 0.008 | 0.98 | 0.91 | 0.95 | 0.003 | 0.99 | 0.95 | 0.94 | 0.001 | 0.98 | 0.95 | 0.97 | 0.003 | 0.99 | 0.97 |
| Discovery | 0.93 | 0.0 | 0.99 | 0.96 | 0.96 | 0.0 | 0.99 | 0.98 | 1.0 | 0.0 | 1.0 | 1.0 | 0.99 | 0.0 | 0.99 | 0.99 | 1.0 | 0.0 | 1.0 | 1.0 |
| Execution | 0.97 | 0.0 | 0.99 | 0.98 | 0.96 | 0.0 | 0.99 | 0.97 | 0.98 | 0.002 | 0.99 | 0.98 | 0.99 | 0.0 | 0.99 | 0.99 | 0.99 | 0.0 | 0.99 | 0.99 |
| Lateral Movement | 0.96 | 0.02 | 0.97 | 0.96 | 0.98 | 0.01 | 0.98 | 0.97 | 0.99 | 0.005 | 0.99 | 0.99 | 0.99 | 0.004 | 0.99 | 0.99 | 0.99 | 0.001 | 0.99 | 0.99 |
| Persistence | 0.75 | 0.008 | 0.97 | 0.79 | 0.78 | 0.003 | 0.98 | 0.85 | 0.94 | 0.002 | 0.99 | 0.95 | 0.97 | 0.0 | 0.98 | 0.97 | 0.99 | 0.002 | 0.99 | 0.99 |
| Privilege Escalation |
0.95 | 0.02 | 0.97 | 0.90 | 0.95 | 0.03 | 0.96 | 0.87 | 1.0 | 0.002 | 0.99 | 0.99 | 0.98 | 0.008 | 0.98 | 0.98 | 1.0 | 0.0 | 1.0 | 1.0 |
| All | 0.9 | 0.01 | 0.98 | 0.91 | 0.92 | 0.007 | 0.98 | 0.93 | 0.98 | 0.002 | 0.99 | 0.98 | 0.98 | 0.002 | 0.99 | 0.98 | 0.99 | 0.001 | 0.99 | 0.99 |
| Model | Unstructured Log Support |
Parser-Free Operation |
Recursive Reasoning | Autonomous Analysis Flow | Goal Replanning |
Multi-log Integration | Extensibility (Tool Integration + Automation) | Event-Level Reasoning | Inference Type | Output-Level Explainability |
|---|---|---|---|---|---|---|---|---|---|---|
| HitAnomaly [36] | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ | △ | Static | ○ |
| NeuralLog [37] | △ | △ | ✕ | ✕ | ✕ | ✕ | ✕ | △ | Static | △ |
| LogBERT [17] | △ | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ | Static | △ |
| BERT-Log [38] | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ | △ | Static | △ |
| LogGPT [18] | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ | △ | Static | △ |
| LogFiT [19] | ○ | ○ | ✕ | ✕ | ✕ | ✕ | ✕ | △ | Static | △ |
| IDS-Agent [39] | △ | △ | ✕ | △ | ✕ | △ | △ | △ | Partially Dynamic | ○ |
| SERC [40] | ✕ | △ | ✕ | △ | ✕ | △ | ○ | △ | Partially Dynamic | ○ |
| Audit-LLM [41] | △ | △ | ✕ | △ | ✕ | △ | △ | ○ | Partially Dynamic | △ |
| LogRESP-Agent (Proposed) |
○ | ○ | ○ | ○ | ○ | ○ | ○ | ○ | Dynamic | ○ |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




