Submitted:
30 April 2025
Posted:
12 May 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Cybersecurity Challenges in Kyrgyzstan
3. The Malware Information Sharing Platform (MISP): An Overview
4. Literature Review
5. Methodology
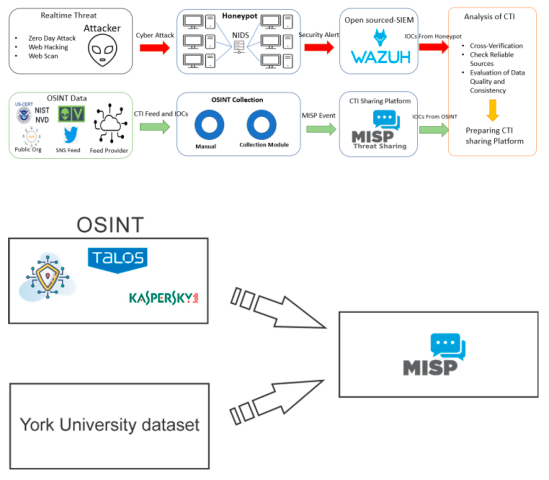
A. Research Framework
B. Technical Implementation
C. Technical Limitations and Future Enhancements
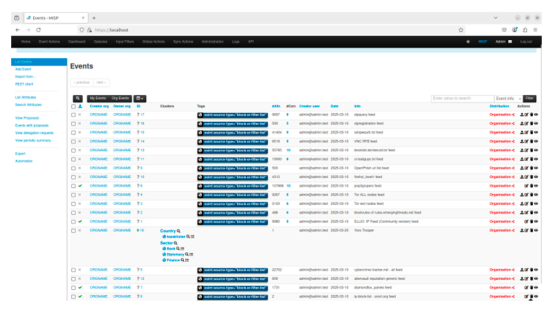
6. Results
7. Conclusions
References
- Ibrahim Yahya Alzahrani, Seokhee Lee, and Kyounggon Kim, “Enhancing Cyber-Threat Intelligence in the Arab World: Leveraging IoC and MISP Integration,” Electronics, June 2024.
- Marc Schmitt, “Securing the digital world: Protecting smart infrastructures and digital industries with artificial intelligence (AI)-enabled malware and intrusion detection,” Journal of Industrial Information Integration, vol. 36., 2023.
- Mostofa Ahsan, Kendall E. Nygard, Rahul Gomes, Md Minhaz Chowdhury, Nafiz Rifat and Jayden F Connolly, “Cybersecurity Threats and Their Mitigation Approaches Using Machine Learning—A Review,” Journal of Cybersecurity and Privacy, vol. 2, 2022.
- Zimin Igor, “Cybersecurity analysis of Kyrgyz Republic,” esa-conference.ru, 2019.
- Cholpon Jumalieva, “Improving the Digital Transformation in the Sphere of Public Administration and Ensuring Information Security,” Alatoo Academic Studies., vol. 23, 2023.
- Naeem AllahRakha, “Cross-Border E-Crimes: Jurisdiction and Due Process Challenges,” Adliya: Jurnal Hukum dan Kemanusiaan, vol. 18, September 2024.
- Kimberly, K. Watson, “Assessing the Potential Value of Cyber Threats Intelligence (CTI) Feeds,” December 2020.
- Katja Henttonen, Juri Rajamaki, “CTI Sharing Practices and MISP Adoption in Finland’s Critical Infrastructure Protection,” Proceedings of the 23rd European Conference on Cyberwarfare and Security., 2024.
- Ana, I. Cerezo, Javier Lopez, Ahmed Patel, “International Cooperation to Fight Transnational Cybercrime,” Annual Workshop on Digital Forensics and Incident Analysis, 2007.
- Fran Casino, Claudia Pina, Pablo Lopez-Aguilar, Edgar Batista, Agusti Solanas, Constantinos Patsakis, “SoK: cross-border criminal investigations and Digital Evidence,” Journal of Cybersecurity, 2022.
- https://www.axios.com/2025/03/24/microsoft-ai-agents-cybersecurity, “Microsoft AI Agents Cybersecurity,”, 2025.
- Financial Times, “Criminals use AI in ‘proxy’ attacks for hostile powers, warns Europol,” https://www.ft.com/content/755593c8-8614-4953-a4b2-09a0d2794684.
- CISA, “CISA Cybersecurity Awareness Program,” https://www.cisa.gov/resources-tools/programs/cisa-cybersecurity-awareness-program, 2025.
- CIRCL, “Computer Incident Response Center Luxemburg,” https://www.circl.lu, 2025.
- ENISA, “ENISA Cybersecurity Information Sharing,” https://enisa.europa.eu/activities/cert/support/information-sharing/cybersecurity-information-sharing/at download/fullReport,2025.
- Israel Government, “Israel Cyber Doctrine,” https://www.gov.il/BlobFolder/generalpage/cyber security methodology 2/he/ICDM%20V2.pdf, 2025.
- CISA, “CISA TLP RULES,” https://www.cisa.gov/news-events/news/traffic-light-protocol-tlp-definitions-and-usage.
- NIST, “NIST Cybersecurity Framework 2.0,” https://www.nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.29.pdf.
- Ministry of Justice of Kyrgyz Republic, “Kyrgyz Republic Cybersecurity Strategy,” https://cbd.minjust.gov.kg/15479/edition/962966/ru.
- CIRCL, “CIRCL MISP Guide,” https://www.circl.lu/doc/misp/book.pdf.
- York University, “Cybersecurity Database,” https://www.yorku.ca/research/bccc/ucs-technical/cybersecurity-datasets-cds/.
- Isakhin Georgii, Karunas Anna, “Threat intelligence and Security Operation Centers on ELK Stack,” Modern Science, XXI International Scientific Conference, http://naukaip.ru.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



