Submitted:
21 April 2025
Posted:
22 April 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. The Cryptographic Pillars of Blockchain Technology
2.1. Hashing Algorithms
- Preimage resistance: Given a hash value, it should be computationally infeasible to find the original input that produced that hash [4]. This property ensures that one cannot easily reverse the hashing process to obtain the original data.
- Second preimage resistance: For a given input, it should be computationally infeasible to find a different input that produces the same hash value [4]. This prevents malicious actors from substituting one piece of data for another while maintaining the same hash.
- Collision resistance: It should be computationally infeasible to find two distinct inputs that produce the same hash value [3]. While theoretically collisions might exist due to the fixed-size output for a variable-size input, a strong cryptographic hash function makes finding such collisions computationally prohibitive.
2.2. Asymmetric Cryptography (Public and Private Keys)
2.3. Digital Signatures
2.4. Symmetric Cryptography
|
Cryptographic Method |
Core Concepts |
Key Algorithms/Technique s |
Role in Blockchain |
|---|---|---|---|
|
Hashing Algorithms |
Fixed-size output (hash) for any input; preimage, second preimage, collision resistance |
SHA-256, Keccak-256, BLAKE3 |
Linking blocks, ensuring data integrity, Merkle trees for efficient transaction verification |
|
Asymmetric Cryptography |
Public key (encryption/verification) , private key (decryption/signing) |
RSA, ECC |
User identification, secure communication, generating and verifying digital signatures, controlling access to digital assets |
|
Digital Signatures |
Private key signing of data hash; public key verification of authenticity |
RSA signatures, ECDSA |
Authenticating transactions, ensuring non-repudiation, verifying the integrity of data, securing smart contracts, supply chains, and voting systems |
|
Symmetric Cryptography |
Single secret key for encryption and decryption |
AES |
Encrypting transaction content (especially in permissioned blockchains), secure communication channels within specific network configurations |
3. Strengths and Limitations of Cryptography in Blockchain
3.1. Strengths of Cryptography in Blockchain
3.2. Limitations of Cryptography in Blockchain
4. Real-World Applications and Use Cases
4.1. Supply Chain Management
4.2. Healthcare
|
Application Area |
Specific Example |
Key Cryptographic Methods Used |
How Cryptography Ensures Security/Functionality |
|---|---|---|---|
|
Supply Chain Management |
IBM Food Trust |
SHA-256 hashing, Digital Signatures (likely ECDSA or RSA) |
Ensures tamper-proof tracking of food products, authenticates participants in the supply chain, verifies the integrity of information added to the blockchain. |
|
Luxury Goods Tracking |
Aura Consortium |
Hashing (likely SHA- 256), Asymmetric Cryptography (unspecified) |
Creates unique digital identities for products, records their history immutably, allows Verification of authenticity, preventing counterfeiting. |
|
Healthcare |
MedRec |
Encryption (likely AES or similar), Digital Signatures (unspecified) |
Encrypts patient medical records, controls access to data based on patient consent via digital signatures, ensures only authorized professionals can view sensitive information. |
|
National EHR System |
Estonia’s EHR System |
Decentralized blockchain, Cryptographic security (unspecified) |
Provides a secure and tamper-proof infrastructure for managing national health records, ensuring data integrity and confidentiality. |
5. Future Directions and Potential Advancements
5.1. Post-Quantum Cryptography
5.2. Enhanced Privacy-Preserving Techniques
5.3. Advancements in Consensus Mechanisms
5.4. Integration with Other Technologies
6. Conclusions
7. Recommendations for Future Research
- Post-Quantum Cryptography for Blockchain: Continued research and standardization efforts are needed to identify and implement robust post-quantum cryptographic algorithms that are specifically tailored to the requirements and constraints of blockchain environments.
- Practical Privacy-Preserving Techniques: Further development and optimization of advanced privacy-preserving cryptographic techniques, such as homomorphic encryption and zero-knowledge proofs, are essential to make them practical and efficient for real-world blockchain applications [5].
- Security of Integrated Systems: Research should focus on thoroughly investigating the security implications and potential vulnerabilities that may arise from the increasing integration of blockchain with other emerging technologies like the Internet of Things (IoT) and Artificial Intelligence (AI), with a particular emphasis on the role of cryptography in securing these integrated systems [4].
- Scalable and Efficient Consensus Mechanisms: Continued exploration of novel cryptographic approaches within the design of blockchain consensus mechanisms is crucial to enhance their scalability, energy efficiency, and overall performance while maintaining a high level of security [4].
- Long-Term Security and Resilience: Ongoing studies are needed to assess the long-term security and resilience of blockchain systems against evolving cryptographic threats, including the potential impact of future advancements in computing power.
- User-Friendly Key Management Solutions: Research should be directed towards developing more user-friendly and secure key management solutions to improve the accessibility and security of blockchain technology for a broader audience, addressing a significant barrier to wider adoption [4].
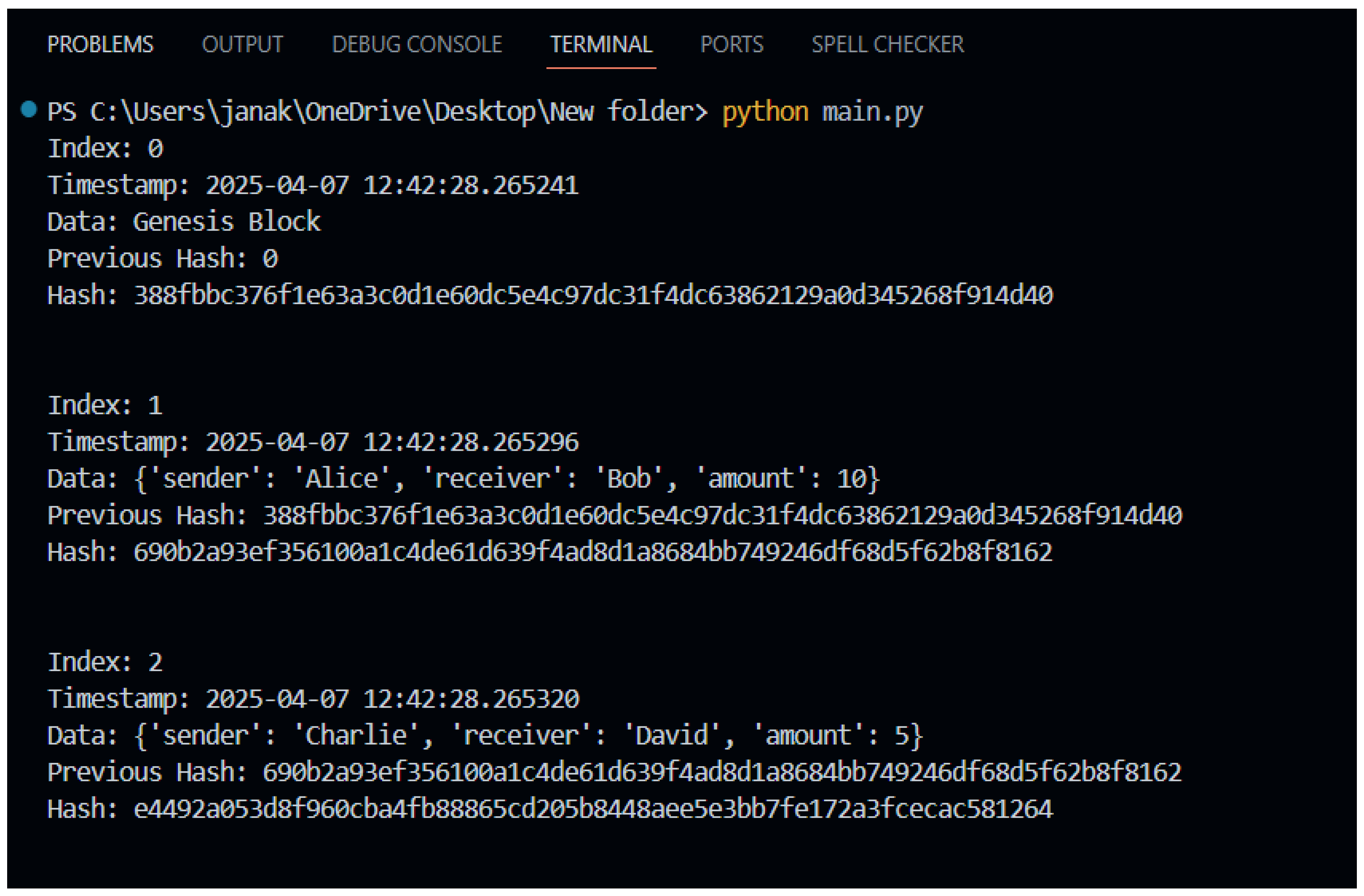
8. Proof of Concept
8.1. Detailed Explanation of Steps
- Define the Block Structure: A Block class is created to represent each block in the blockchain. Each block contains an index (its position in the chain), a timestamp (when the block was created), data (representing the transactions or information stored in the block), a previous_hash (the hash of the preceding block), and its own hash.
- Implement Hashing Function: A function calculate_hash is implemented using the hashlib library in Python. This function takes a block as input and generates its SHA-256 hash based on its index, previous hash, timestamp, and data. This cryptographic hash acts as the digital fingerprint of the block.
- Create the Blockchain Class: A Blockchain class is created to manage the chain of Block objects. It initializes with an empty list called chain.
- Create the Genesis Block: A method create_genesis_block is implemented within the Blockchain class to create the very first block in the chain. This block has a fixed index of 0 and a previous_hash of “0”.
- Add New Blocks: A method add_block is implemented to add new blocks to the blockchain. When a new block is added, its previous_hash is set to the hash of the last block in the chain, establishing the cryptographic link. The new block’s own hash is then calculated using the calculate_hash function.
8.2. Code and Relevant Details
8.3. Outputs
Appendix A
Purpose
Overview
- Language: Python
-
Key Components:
- o
- Block class: Defines a block with attributes like index, data, and a hash linking to the prior block.
- o
- calculate_hash function: Computes the SHA-256 hash for each block.
- o
- Blockchain class: Manages the chain, starting with a genesis block and adding subsequent blocks.
- Functionality: Creates a blockchain and demonstrates block chaining via hashing.
- Prerequisites
- Requires Python 3.x with standard libraries hashlib and datetime (no external dependencies).
Note
-
import hashlibimport datetime
-
class Block:def __init__(self, index, timestamp, data, previous_hash):self.index = indexself.timestamp = timestampself.data = dataself.previous_hash = previous_hashself.hash = self.calculate_hash()
-
def calculate_hash(self):block_string = str(self.index) + str(self.timestamp) + str(self.data) + str(self.previous_hash)return hashlib.sha256(block_string.encode()).hexdigest()class Blockchain:def __init__(self):self.chain = [self.create_genesis_block()].
-
def create_genesis_block(self):return Block(0, datetime.datetime.now(), “Genesis Block”, “0”)
-
def get_last_block(self):return self.chain[-1].
-
def add_block(self, new_block):new_block.previous_hash = self.get_last_block().hashnew_block.hash = new_block.calculate_hash()self.chain.append(new_block)
-
# Example Usagemy_blockchain = Blockchain()
-
# Add first blockfirst_block_data = {“sender”: “Alice”, “receiver”: “Bob”, “amount”: 10}first_block = Block(1, datetime.datetime.now(), first_block_data, my_blockchain.get_last_block().hash)my_blockchain.add_block(first_block)
-
# Add second blocksecond_block_data = {“sender”: “Charlie”, “receiver”: “David”, “amount”: 5}second_block = Block(2, datetime.datetime.now(), second_block_data, my_blockchain.get_last_block().hash)my_blockchain.add_block(second_block)
-
# Print the blockchainfor block in my_blockchain.chain:print(“Index:”, block.index)print(“Timestamp:”, block.timestamp)print(“Data:”, block.data)print(“Previous Hash:”, block.previous_hash)print(“Hash:”, block.hash)print(“\n”)
References
- F. Mohammad Saeidia, M. H. Zahedi, and E. Farahani, “A Secure and Reliable Model for Financial Documents Using Digital Signature and Blockchain Technology,” AI and Tech in Behavioral and Social Sciences, vol. 3, no. 1, pp. 23–33, 2025.
- National Institute of Standards and Technology, “Blockchain Technology Overview,” NIST Interagency Report 8202, 2018.
- J. Aumasson, L. Henzen, W. Meier, and M. Naya-Plasencia, “Quark: A lightweight hash function,” in Cryptographic Hardware and Embedded Systems – CHES 2013, R. Avanzi, L. Knudsen, and C. Paar, Eds. Berlin, Heidelberg: Springer, 2013, pp. 186–201.
- S. W. Lo, Y. Wang, and D. K. C. Lee, “Cryptography and Blockchain Technology,” in Foundations for Fintech, Singapore: World Scientific, 2021, pp. 1–30.
- G. Wood, “Ethereum: A secure decentralised generalised transaction ledger,” University of Toronto, 2014.
- V. Buterin, “Ethereum: A secure decentralised generalised transaction ledger,” University of Toronto, 2014.
- S. Nakamoto, “Bitcoin: A peer-to-peer electronic cash system,” 2008.
- Z. Zheng, S. Xie, H.-N. Dai, and X. Chen, “An overview of blockchain technology: Architecture, consensus, and future trends,” in 2017 IEEE International Congress on Big Data (BigData Congress), 2017, pp. 557–564.
- A. C. H. Chen, “Evaluation of Hash Algorithm Performance for Cryptocurrency Exchanges Based on Blockchain System,” arXiv preprint arXiv:2408.11950, 2024.
- M. Mohana, “An Adaptive Elliptical Curve Cryptography-Rivest-Shamir-Adleman- based Encryption for IoT Healthcare Security Model with Blockchain Technology,” Journal of Mechanics in Medicine and Biology, vol. 23, no. 07, 2023.
- S. Nakamoto, “Bitcoin: A peer-to-peer electronic cash system,” 2008.
- A. Reyna, C. Martín, J. Chen, E. Soler, and M. Díaz, “On blockchain and its integration with IoT,” Sensors, vol. 18, no. 8, p. 2284, 2018.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




