Submitted:
17 April 2025
Posted:
21 April 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Research Background and Motivation
1.2. Challenges in Financial Transaction Privacy Protection
1.3. Research Objectives and Contributions
2. Related Work and Preliminaries
2.1. Financial Transaction Pattern Recognition
2.2. Differential Privacy Fundamentals
2.3. Privacy-preserving Machine Learning
2.4. Existing Methods Review
3. Privacy-preserving Framework Design
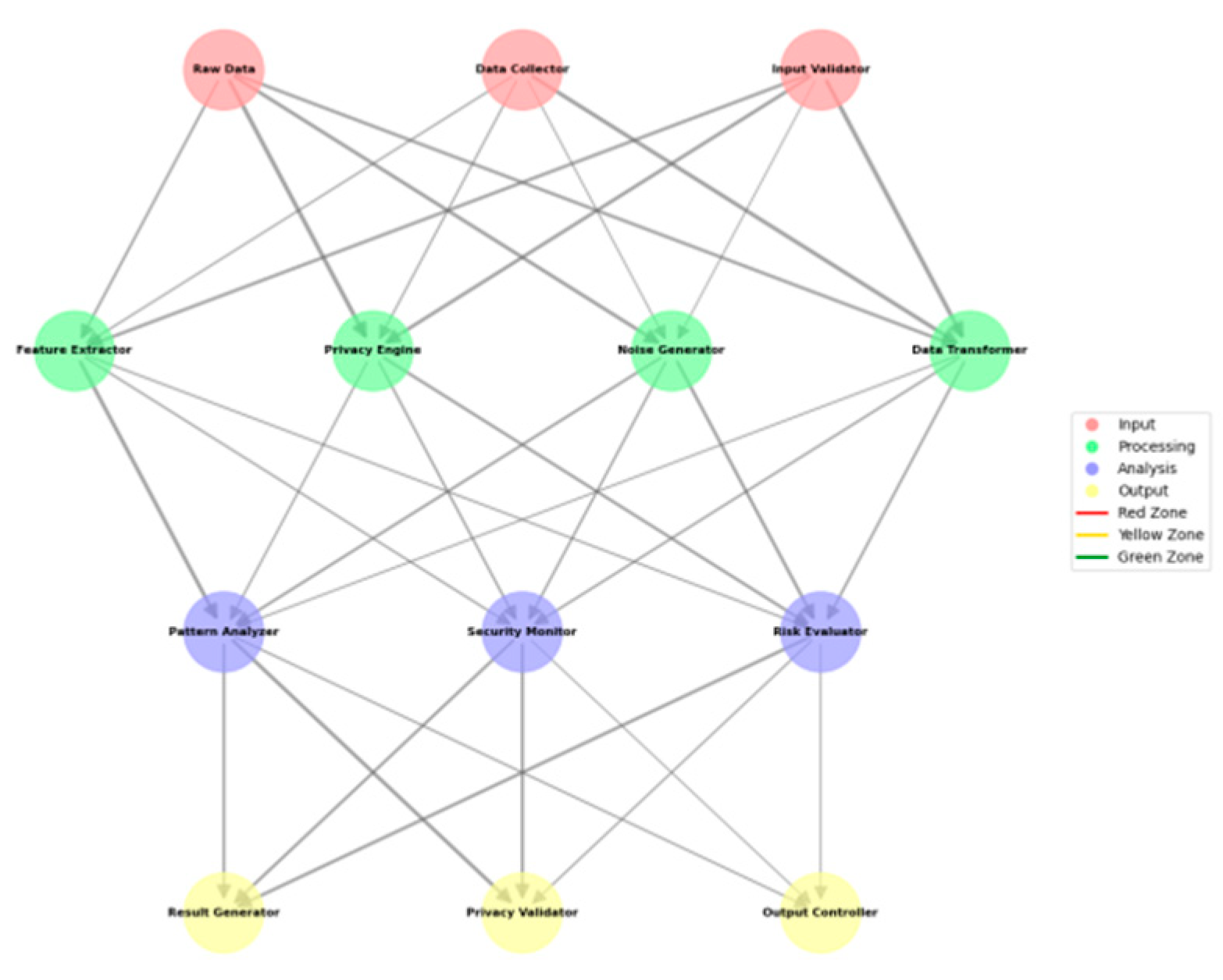
3.1. System Architecture Overview
3.2. Differential Privacy Mechanism Design
3.3. Transaction Pattern Feature Extraction
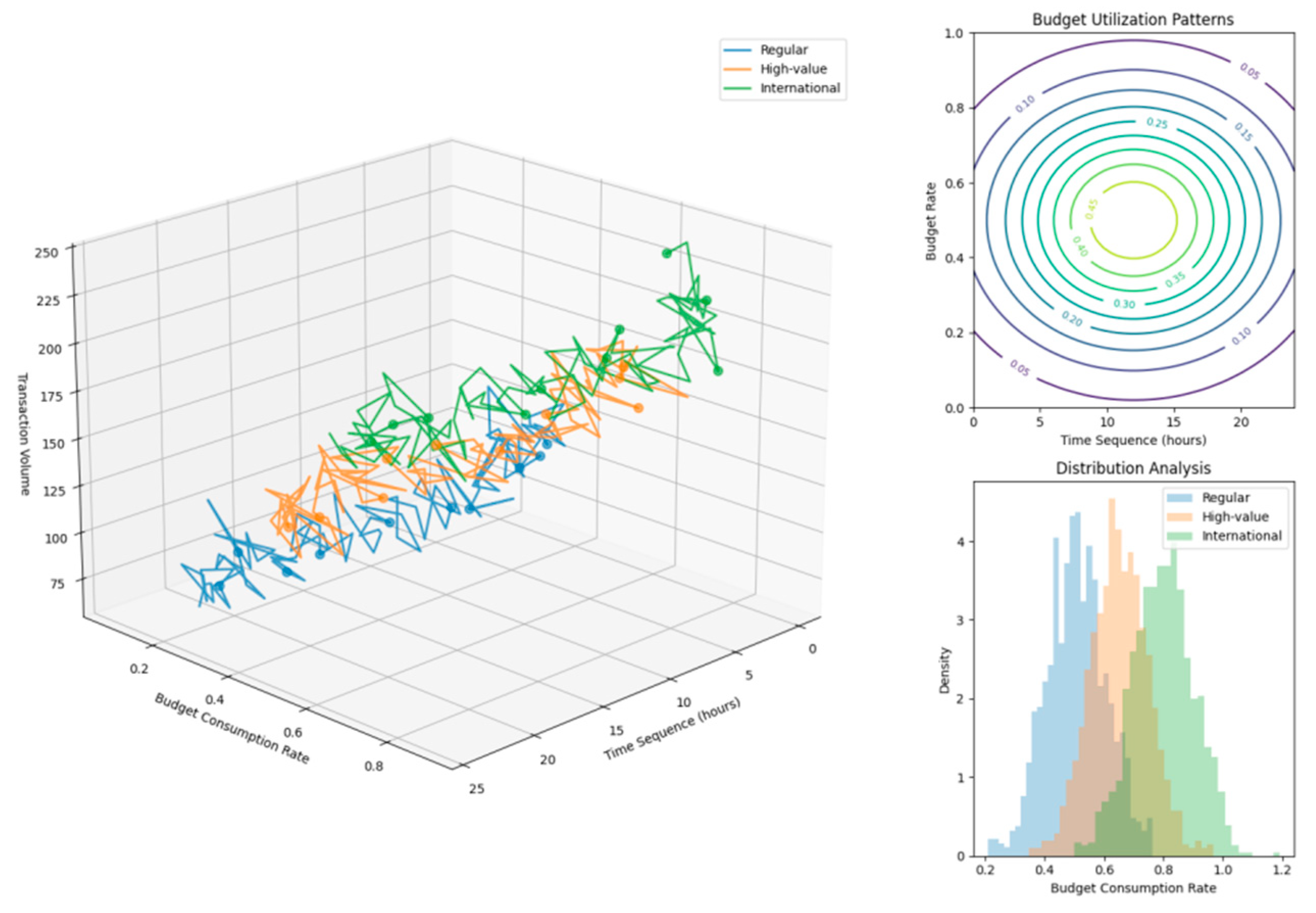
3.4. Privacy Budget Allocation Strategy
4. Privacy-preserving Pattern Recognition Implementation
4.1. Transaction Data Preprocessing
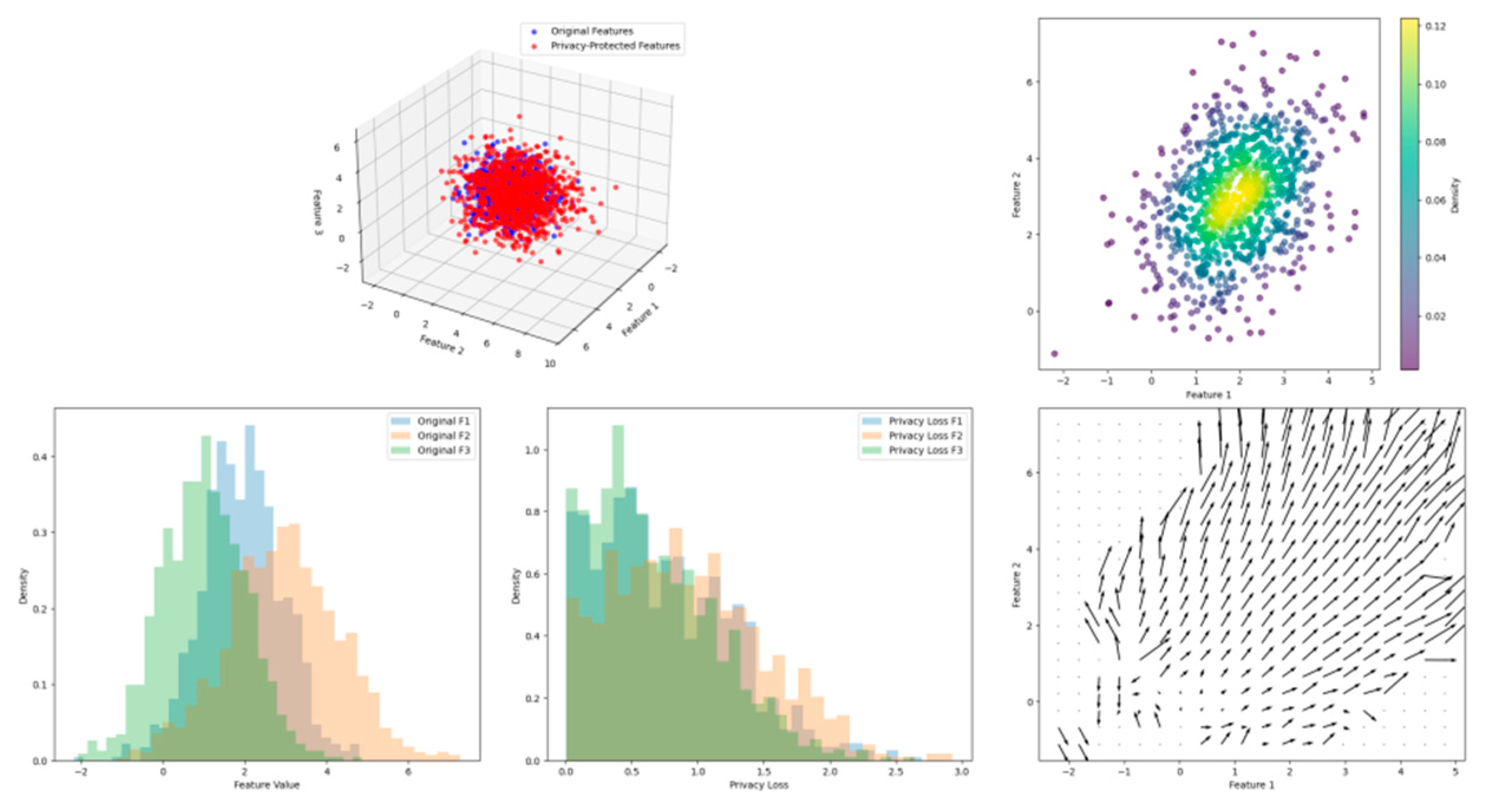
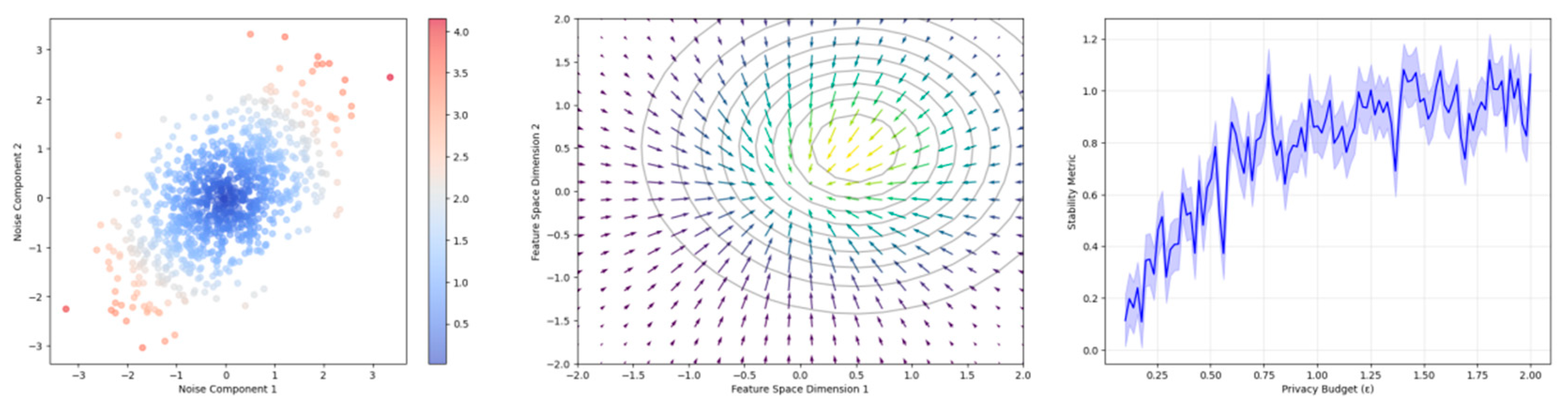
4.2. Noise Addition Mechanism
4.3. Pattern Recognition Model Design
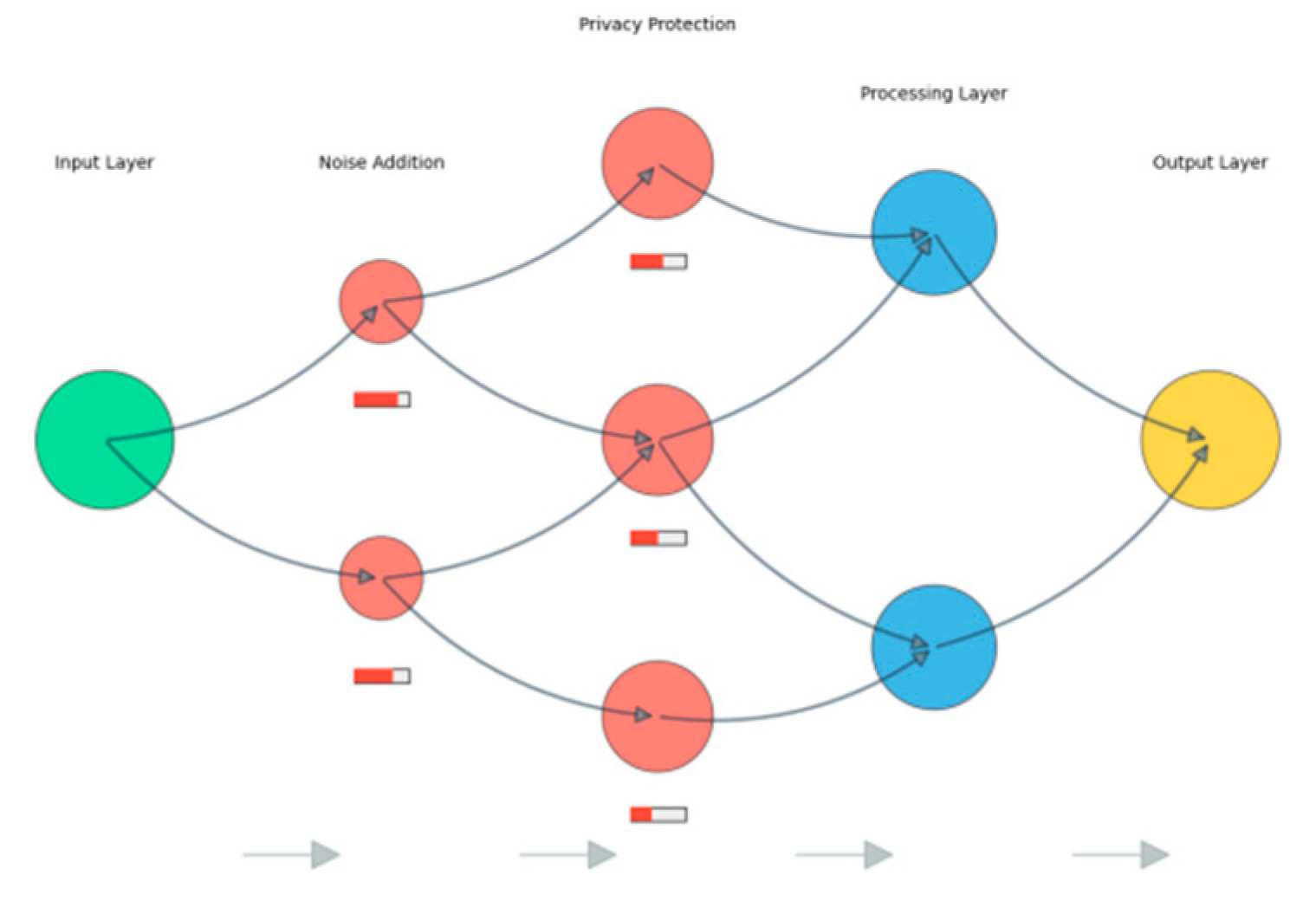
4.4. Privacy Protection Analysis
5. Experimental Evaluation and Analysis
5.1. Experimental Setup and Dataset
5.2. Performance Metrics and Evaluation
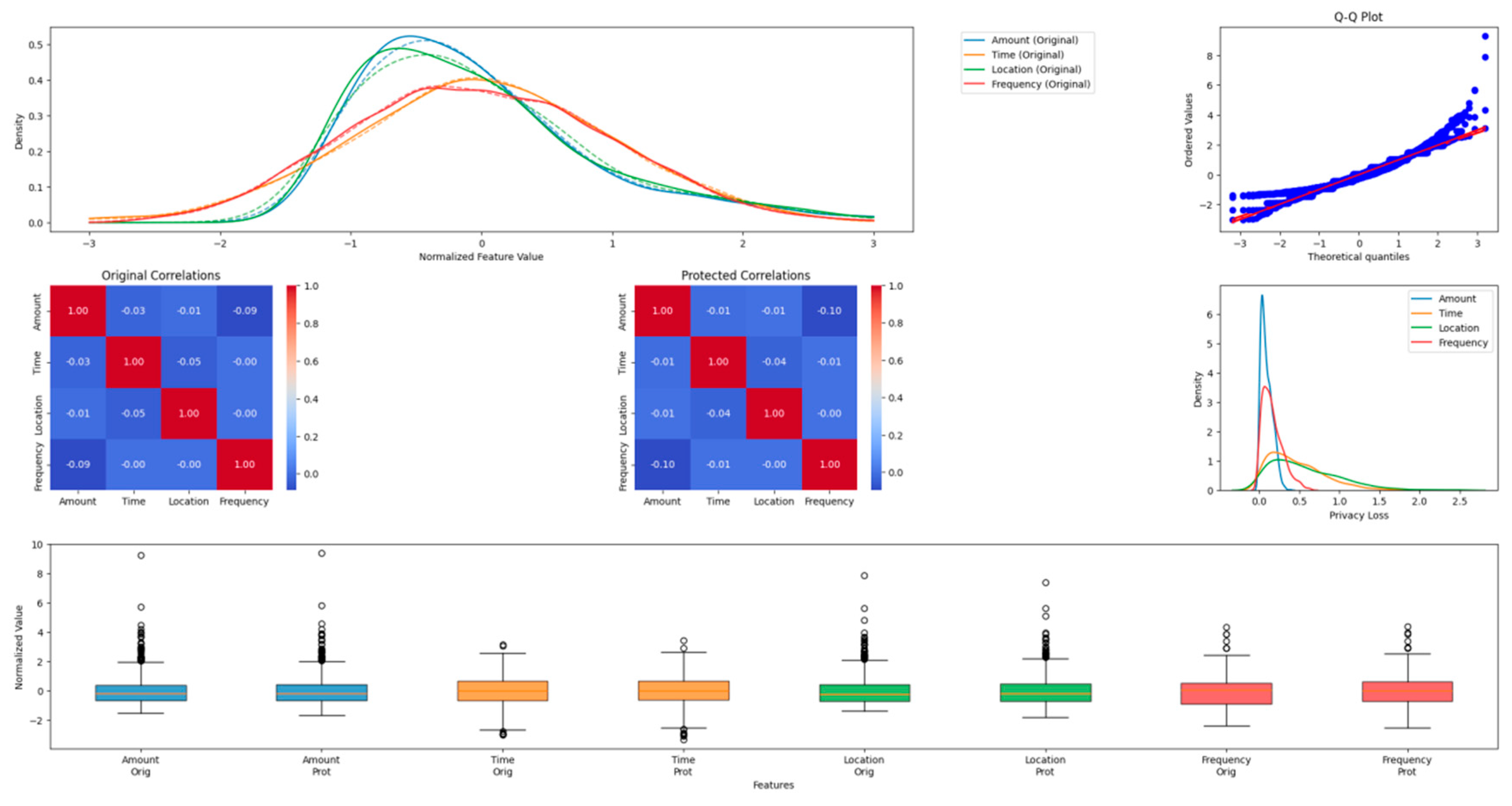
5.3. Privacy Protection Analysis
Acknowledgments
References
- Shi, S. , Cao, X., & Zhang, Q. (2023, August). Privacy-Preserving Average Consensus for Multi-Agent System with Event-Triggered Method. In 2023 IEEE 6th International Conference on Pattern Recognition and Artificial Intelligence (PRAI) (pp. 943-948). IEEE.
- Nakachi, T. , Wang, Y., & Kiya, H. (2020, May). Privacy-preserving pattern recognition using encrypted sparse representations in L0 norm minimization. In ICASSP 2020-2020 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP) (pp. 2697-2701). IEEE.
- Ye, Q. , Hu, H., Meng, X., Zheng, H., Huang, K., Fang, C., & Shi, J. PrivKVM*: Revisiting key-value statistics estimation with local differential privacy. IEEE Transactions on Dependable and Secure Computing, 2021, 20, 17–35. [Google Scholar]
- Lin, J. , Niu, J., & Liu, X. (2020, June). Protecting Consumption Habits with Differential Privacy. In ICC 2020-2020 IEEE International Conference on Communications (ICC) (pp. 1-6). IEEE.
- Fei, Y. , & Wang, H. (2024, November). Research on Financial Transaction Data Protection and Intelligent Risk Assessment Based on Differential Privacy. In 2024 6th International Conference on Machine Learning, Big Data and Business Intelligence (MLBDBI) (pp. 185-188). IEEE.
- Xia, S., Zhu, Y., Zheng, S., Lu, T., & Ke, X. A Deep Learning-based Model for P2P Microloan Default Risk Prediction. International Journal of Innovative Research in Engineering and Management, 2024, 11, 110–120.
- Li, S., Xu, H., Lu, T., Cao, G., & Zhang, X. Emerging Technologies in Finance: Revolutionizing Investment Strategies and Tax Management in the Digital Era. Management Journal for Advanced Research, 2024, 4, 35–49.
- Liu, Y. , Xu, Y., & Zhou, S. (2024). Enhancing User Experience through Machine Learning-Based Personalized Recommendation Systems: Behavior Data-Driven UI Design. Authorea Preprints.
- Xu, Y. , Liu, Y., Wu, J., & Zhan, X. Privacy by Design in Machine Learning Data Collection: An Experiment on Enhancing User Experience. Applied and Computational Engineering, 2024, 97, 64–68. [Google Scholar]
- Xu, X. , Xu, Z., Yu, P., & Wang, J. (2025). Enhancing User Intent for Recommendation Systems via Large Language Models. Preprints.
- Li, L. , Xiong, K., Wang, G., & Shi, J. AI-Enhanced Security for Large-Scale Kubernetes Clusters: Advanced Defense and Authentication for National Cloud Infrastructure. Journal of Theory and Practice of Engineering Science, 2024, 4, 33–47. [Google Scholar]
- Yu, P. , Xu, X., & Wang, J. Applications of Large Language Models in Multimodal Learning. Journal of Computer Technology and Applied Mathematics, 2024, 1, 108–116. [Google Scholar]
- Shen, Q. , Zhang, Y., & Xi, Y. Deep Learning-Based Investment Risk Assessment Model for Distributed Photovoltaic Projects. Journal of Advanced Computing Systems, 2024, 4, 31–46. [Google Scholar]
- Chen, J. , Zhang, Y., & Wang, S. Deep Reinforcement Learning-Based Optimization for IC Layout Design Rule Verification. Journal of Advanced Computing Systems, 2024, 4, 16–30. [Google Scholar]
- Ju, C. A Machine Learning Approach to Supply Chain Vulnerability Early Warning System: Evidence from US Semiconductor Industry. Journal of Advanced Computing Systems, 2023, 3, 21–35. [Google Scholar] [CrossRef]
- Xiong, K. , Wu, Z., & Jia, X. DeepContainer: A Deep Learning-based Framework for Real-time Anomaly Detection in Cloud-Native Container Environments. Journal of Advanced Computing Systems, 2025, 5, 1–17. [Google Scholar]
- Wang, S. , Hu, C., & Jia, G. Deep Learning-Based Saliency Assessment Model for Product Placement in Video Advertisements. Journal of Advanced Computing Systems, 2024, 4, 27–41. [Google Scholar]
- Pu, Y. , Chen, Y., & Fan, J. P2P Lending Default Risk Prediction Using Attention-Enhanced Graph Neural Networks. Journal of Advanced Computing Systems, 2023, 3, 8–20. [Google Scholar]
- Chen, J. , Yan, L., Wang, S., & Zheng, W. (2024). Deep Reinforcement Learning-Based Automatic Test Case Generation for Hardware Verification. Journal of Artificial Intelligence General science (JAIGS) ISSN: 3006-4023, 6(1), 409-429.
- Liang, X., & Chen, H. (2024, July). One cloud subscription-based software license management and protection mechanism. In Proceedings of the 2024 International Conference on Image Processing, Intelligent Control and Computer Engineering (pp. 199-203).
- Xu, J. , Wang, Y., Chen, H., & Shen, Z. (2025). Adversarial Machine Learning in Cybersecurity: Attacks and Defenses. International Journal of Management Science Research, 8(2), 26-33.
- Chen, H. , Shen, Z., Wang, Y., & Xu, J. (2024). Threat Detection Driven by Artificial Intelligence: Enhancing Cybersecurity with Machine Learning Algorithms.
- Xiao, Jue, Wei Xu, and Jianlong Chen. "Social media emotional state classification prediction based on Arctic Puffin Algorithm (APO) optimization of Transformer mode." Authorea Preprints (2024).
- Chen, J. , Xu, W., Ding, Z., Xu, J., Yan, H., & Zhang, X. (2024). Advancing Prompt Recovery in NLP: A Deep Dive into the Integration of Gemma-2b-it and Phi2 Models. arXiv:2407.05233.
- Xu,J.;Chen,H.;Xiao,X.;Zhao,M.;Liu,B. (2025).Gesture Object Detection and Recognition Based on YOLOv11.Applied and Computational Engineering,133,81-89.
- Weng, J., & Jiang, X. (2024). Research on Movement Fluidity Assessment for Professional Dancers Based on Artificial Intelligence Technology. Artificial Intelligence and Machine Learning Review, 5(4), 41-54.
- Jiang, C. , Jia, G., & Hu, C. (2024). AI-Driven Cultural Sensitivity Analysis for Game Localization: A Case Study of Player Feedback in East Asian Markets. Artificial Intelligence and Machine Learning Review, 5(4), 26-40.
- Ma, D. (2024). AI-Driven Optimization of Intergenerational Community Services: An Empirical Analysis of Elderly Care Communities in Los Angeles. Artificial Intelligence and Machine Learning Review, 5(4), 10-25.
- Wang, P. , Varvello, M., Ni, C., Yu, R., & Kuzmanovic, A. (2021, May). Web-lego: trading content strictness for faster webpages. In IEEE INFOCOM 2021-IEEE Conference on Computer Communications (pp. 1-10). IEEE.
- Wang, Z., Shen, Q., Bi, S., & Fu, C. (2024). AI Empowers Data Mining Models for Financial Fraud Detection and Prevention Systems. Procedia Computer Science, 243, 891-899.
- Diao, S. , Wan, Y., Huang, D., Huang, S., Sadiq, T., Khan, M. S.,... & Mazhar, T. Optimizing Bi-LSTM networks for improved lung cancer detection accuracy. PloS one, 2025, 20, e0316136. [Google Scholar]
- Chen, Y. , Feng, E., & Ling, Z. Secure Resource Allocation Optimization in Cloud Computing Using Deep Reinforcement Learning. Journal of Advanced Computing Systems, 2024, 4, 15–29. [Google Scholar]
- Ju, C. , & Ma, X. Real-time Cross-border Payment Fraud Detection Using Temporal Graph Neural Networks: A DeepLearning Approach. JUTIE (Jurnal Teknologi Sistem Informasi dan Ekonomi), 2024, 2, 81–104. [Google Scholar]
| Layer | Components | Primary Functions |
|---|---|---|
| Data Preprocessing | Data Cleaner, Feature Extractor | Data normalization, Feature standardization |
| Privacy Protection | Noise Generator, Budget Allocator | Differential privacy implementation, Privacy budget management |
| Pattern Recognition | Pattern Analyzer, Model Trainer | Transaction pattern identification, Model optimization |
| Result Evaluation | Performance Evaluator, Privacy Validator | Accuracy assessment, Privacy guarantee verification |
| Zone | Protection Level | Access Control | Data Type |
|---|---|---|---|
| Red | Maximum | Strict | Raw transaction data |
| Yellow | Medium | Moderate | Processed features |
| Green | Basic | Regular | Aggregated results |
| Attribute Type | Distribution | Scale Parameter | Shape Parameter |
|---|---|---|---|
| Amount | Laplace | 0.5 | 1.2 |
| Time | Gaussian | 0.3 | 0.8 |
| Location | Exponential | 0.4 | 1.0 |
| Transaction Type | Base Sensitivity | Adjustment Factor | Maximum Threshold |
|---|---|---|---|
| Regular | 0.1 | 1.2 | 0.5 |
| High-value | 0.3 | 1.5 | 0.8 |
| International | 0.4 | 1.8 | 1.0 |
| Stage | Processing Operation | Privacy Mechanism | Error Bound |
|---|---|---|---|
| Cleaning | Outlier Removal | Local Sensitivity | ±0.05 |
| Normalization | Min-Max Scaling | Global Sensitivity | ±0.03 |
| Encoding | Feature Transformation | Adaptive Noise | ±0.02 |
| Aggregation | Temporal Grouping | Budget Splitting | ±0.04 |
| Feature Type | Scale Range | Privacy Sensitivity | Noise Level |
|---|---|---|---|
| Amount | [0,1] | High | 0.15 |
| Frequency | [0,1] | Medium | 0.10 |
| Time Interval | [0,1] | Low | 0.05 |
| Location | [0,1] | High | 0.15 |
| Privacy Level | Distribution Type | Scale Parameter | Location Parameter |
|---|---|---|---|
| Critical | Laplace | 1.5 | 0.0 |
| High | Gaussian | 1.2 | 0.0 |
| Medium | Exponential | 0.8 | 0.0 |
| Low | Uniform | 0.5 | 0.0 |
| Layer | Units | Activation | Privacy Budget | Noise Scale |
|---|---|---|---|---|
| Input | 64 | ReLU | 0.2 | 0.05 |
| Hidden-1 | 128 | Tanh | 0.3 | 0.08 |
| Hidden-2 | 256 | ReLU | 0.3 | 0.08 |
| Output | 32 | Softmax | 0.2 | 0.05 |
| Data Attribute | Value Range | Distribution Type | Missing Rate |
|---|---|---|---|
| Amount | $0-100,000 | Log-normal | 0.02% |
| Time Interval | 0-24h | Normal | 0.00% |
| Location Codes | 1-500 | Discrete | 0.05% |
| Category Labels | 1-50 | Categorical | 0.01% |
| Privacy Budget | Accuracy | Precision | Recall | F1-Score |
|---|---|---|---|---|
| ε = 0.1 | 0.912 | 0.893 | 0.901 | 0.897 |
| ε = 0.5 | 0.934 | 0.921 | 0.928 | 0.924 |
| ε = 1.0 | 0.951 | 0.943 | 0.947 | 0.945 |
| Attribute | Information Loss | Pattern Distortion | Privacy Guarantee |
|---|---|---|---|
| Amount | 0.152 | 0.143 | 0.982 |
| Time | 0.134 | 0.128 | 0.991 |
| Location | 0.167 | 0.159 | 0.975 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




