Submitted:
09 January 2025
Posted:
09 January 2025
You are already at the latest version
Abstract
Keywords:
1.0. Background
2.0. Detailed Discussion on How Security-Related Technology Works
2.1. Component
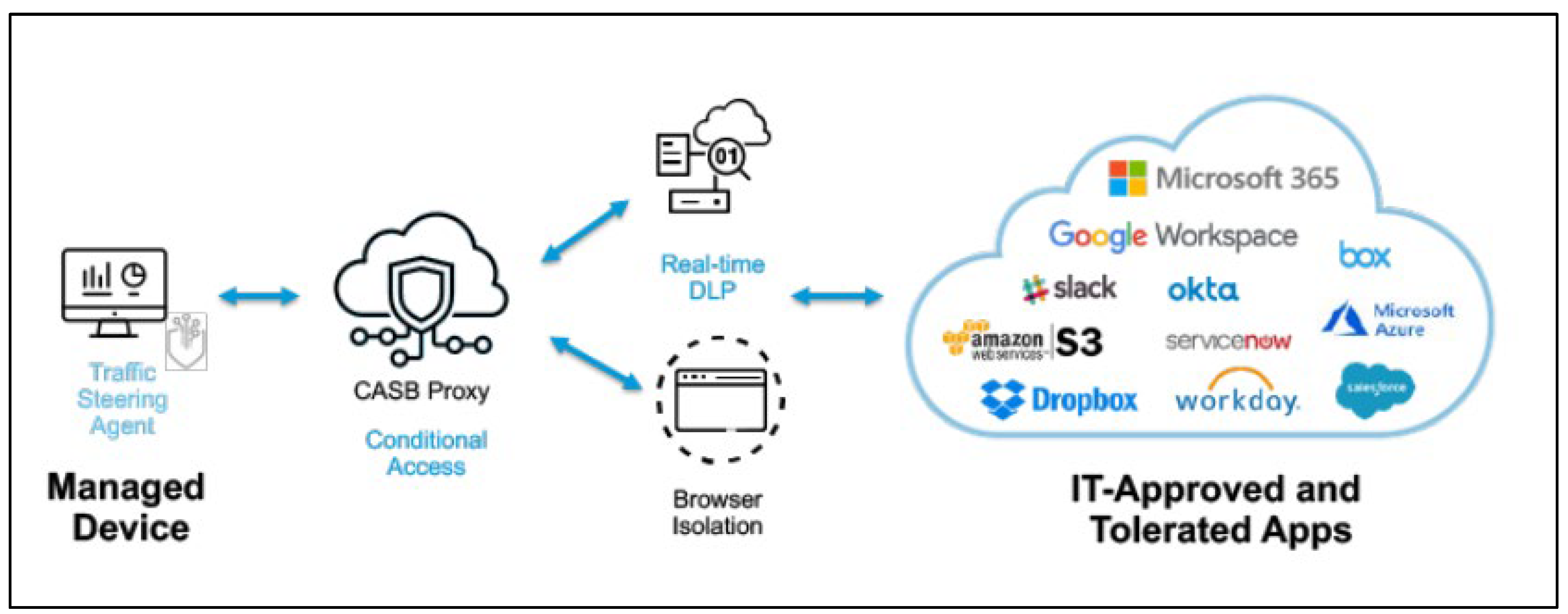
Introduction to the Components in Cloud Computing Security
The Core Components of Cloud Security
Integration of Components for Comprehensive Cloud Security
2.2. Process
Private Cloud
Public Cloud
Hybrid Cloud
2.3. Threat
- Data Breaches: Unauthorised access to sensitive data or theft of data stored in the cloud can lead to information theft or misuse. (SentinelOne, 2024)
- Insider Threats: Malicious actions and use of resources by individuals within the organisation with access to critical systems and data. (SentinelOne, 2024)
- Account Hijacking: Unauthorised access to accounts through identity theft, phishing, or social engineering or other ways and use of such accounts. (SentinelOne, 2024)
- Insecure Interfaces and APIs: Vulnerabilities in the software or source code that allow outside attackers to exploit and use the resources and services in the cloud. (SentinelOne, 2024)
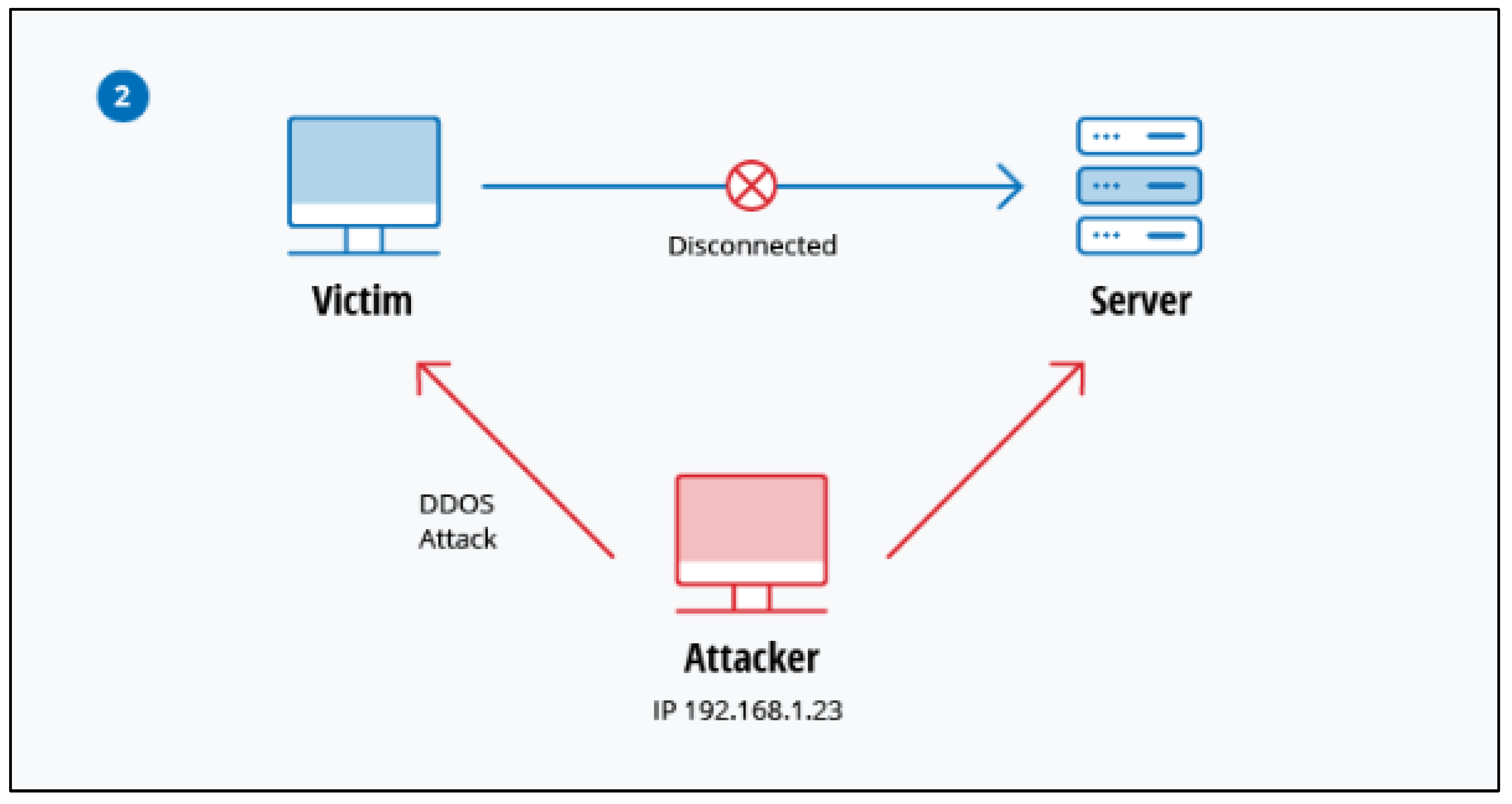
- Denial of Service (DoS) Attacks: Attacks that overload cloud services using floods of packets and then making the cloud unavailable and unusable to real users. (SentinelOne, 2024)
- Advanced Persistent Threats (APTs): Prolonged cyberattacks made in such a way that it can infiltrate and steal data from cloud environments over time. (David Puzas, 2024)
- Data Loss: Accidental deletion, hardware failure, or natural disasters along with the lack of backups of data, resulting in the permanent loss of data. (SentinelOne, 2024)
- Malware Injection: Malware scripts or codes injected into cloud services that can steal data and gain control. (Wayne Jansen, 2011)
- Lateral Movement Attacks: Attackers move within the network and escalate privileges to gain access to the resources in the cloud. (Wayne Jansen, 2011)
- Configuration Vulnerabilities: Weak or misconfigured settings that make cloud services vulnerable to outside networks and makes the data or services exploitable by unauthorized individuals. (David Puzas, 2024)
- Inadequate Identity, Credential, and Access Management: Poorly managed IAM settings that creates vulnerabilities, allowing unauthorised users to access sensitive resources and use or steal the data in the cloud. (David Puzas, 2024)
- Lack of Cloud Security Policy: lack of policies and regulations can cause improper practices and management of the cloud system and that can lead to gaps in security. (David Puzas, 2024)
- Weak Encryption and Key Management: improper management of encryption keys could allow unauthorised users to access and steal the sensitive data within the cloud. (Wayne Jansen, 2011)
- Insufficient Compliance Controls: being unable to follow industry standards and regulatory rules can make cloud systems vulnerable to newer exploits which can result in data breaches and legal issues. (David Puzas, 2024)
- Inadequate Logging and Monitoring: not being able to detect unauthorised activity or attacks because of the lack of monitoring or skilled individuals for it. (Wayne Jansen, 2011)
- BYOD (Bring Your Own Device) Security Risks: Devices connecting to the cloud without proper security measures can cause the increase of exposure to outside threats and also makes the cloud more vulnerable to attacks like DDoS. (Wayne Jansen, 2011)
- External Threats: cyber threats like hacking, phishing, or ransomware from external elements. (David Puzas, 2024)
- Insecure Data Transfer: not transferring data in a secure way that lacks proper encryptions or poor network security can cause theft or alteration of the data by outside elements. (SentinelOne, 2024)
- Application Vulnerabilities: Bugs and vulnerabilities in the application layer that makes the application exploitable can be exploited by outside users. (Wayne Jansen, 2011)
- Lack of Physical Security for Data Centers: Unauthorised physical access to data centres or server devices that store cloud data can make it possible to cause harm physically. (Wayne Jansen, 2011)
- Cross-tenant Data Access: In a multi-tenant cloud environment where the environment is shared between the users, if one user gains unauthorised access to another user’s data it can lead to hacking. (SentinelOne, 2024)
- Vulnerability of Virtual Machines (VMs): exploitable variables in the systems of the VMs can make it possible for attackers to exploit the VMs itself and access cloud resources.
- Shadow IT: Unmonitored cloud applications and resources that are being used or illegally used without authorisation and the knowledge of IT management can increase risk by making the cloud more vulnerable from outside individuals. (David Puzas, 2024)
- Supply Chain Attacks: Vulnerabilities from third-party softwares or services which can be legal or illegal can mix up into the cloud environment making it vulnerable from outside. (SentinelOne, 2024)
- Resource Exploitation: Unauthorised use of cloud resources can lead to increased costs and security risks that can be exploited. (Wayne Jansen, 2011)
- Lack of regular updates: Lack of regular updates of cloud software can make it vulnerable to newer threats as newer exploits are usually undetectable and unpreventable by older technologies and softwares. (Wayne Jansen, 2011)
- Lack of regular testing: Lack of regular penetration testing can make the cloud vulnerable as management does not get aware of new threats and exploits to the older software. (Wayne Jansen, 2011)
- Lack of security systems: Lack of properly updated firewalls and IDS can make the cloud highly vulnerable to newer outside threats. (David Puzas, 2024)
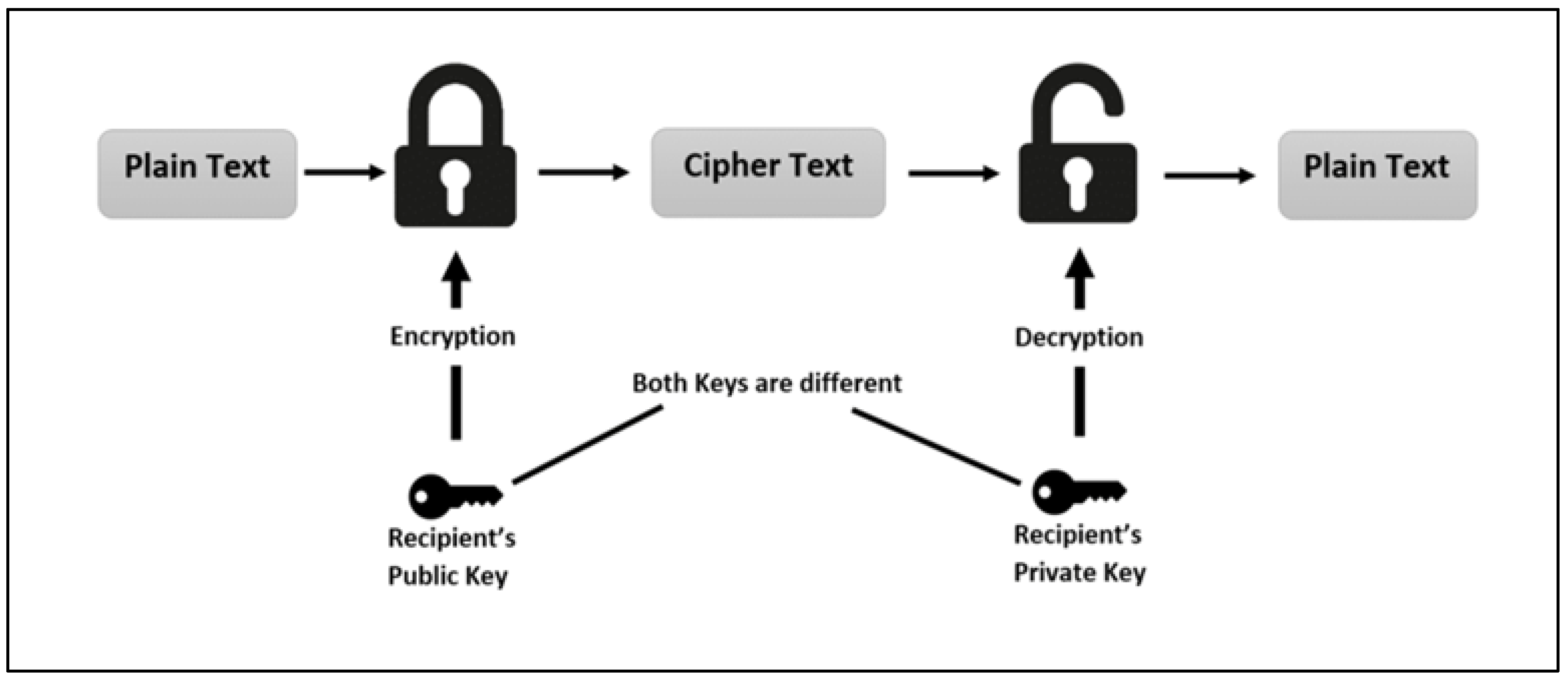
2.4. Example Security-Related Technology
Examples MPLS Security-Related Technology Related to Cloud Computing Security:
- Select two prime numbers, ppp and qqq.
- Calculate nnn, where n=p×qn = p \times qn=p×q.
- Compute Euler’s Totient, w(n)=(p−1)×(q−1)w(n) = (p-1) \times (q-1)w(n)=(p−1)×(q−1).
- Choose an encryption key, eee, such that e<w(n)e < w(n)e<w(n) and GCD(e,w(n))=1\text{GCD}(e, w(n)) = 1GCD(e,w(n))=1.
- Determine the decryption key, ddd, where d×e≡1mod w(n)d \times e \equiv 1 \mod w(n)d×e≡1modw(n).
- Encrypt the message, computing cipher text CCC using the formula C=Memod nC = M^e \mod nC=Memodn.
- Decrypt the cipher text, retrieving the plaintext MMM using the formula M=Cdmod nM = C^d \mod nM=C d mod n.
3.0. Discussion on the Impact
3.1. Benefits of Cloud Computing Security
Enhanced Data Protection and Compliance
Scalability of Security Solutions
Cost-Effectiveness and Efficiency
Improved Disaster Recovery and Business Continuity
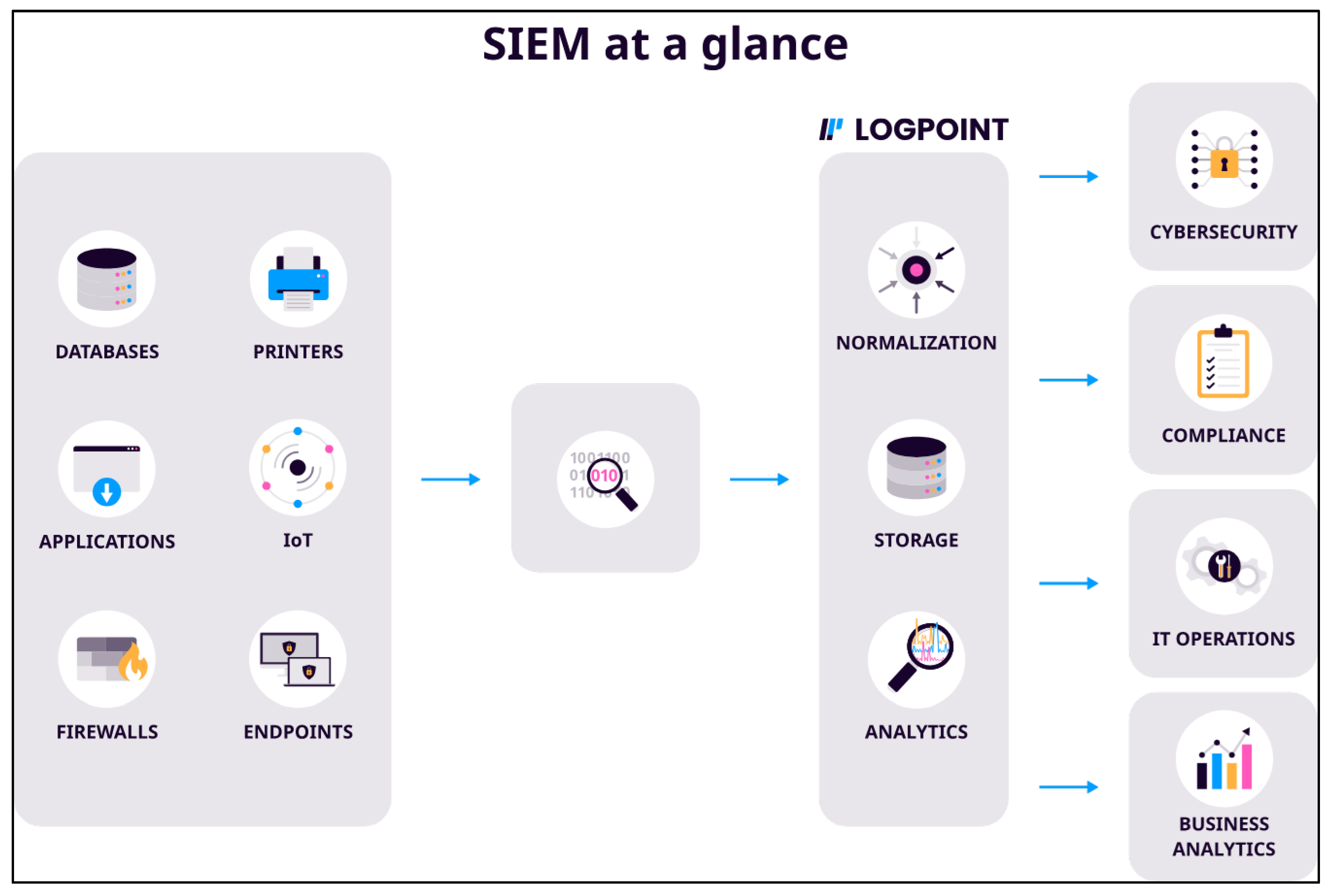
Advanced Threat Detection and Prevention
3.2. Limitations of Cloud Computing Security
Complex Compliance and Regulatory Challenges
Increased Risk of Data Breaches
Dependence on Third-Party Providers
Limited Customization of Security Controls
3.3. Future Potentials of Cloud Computing Security
Advances in Artificial Intelligence and Machine Learning
Quantum-Resistant Encryption
Expansion of Zero-Trust Architecture
Increased Use of Blockchain for Data Security
4.0. Discussion on Security Countermeasures
4.1. Security Countermeasures
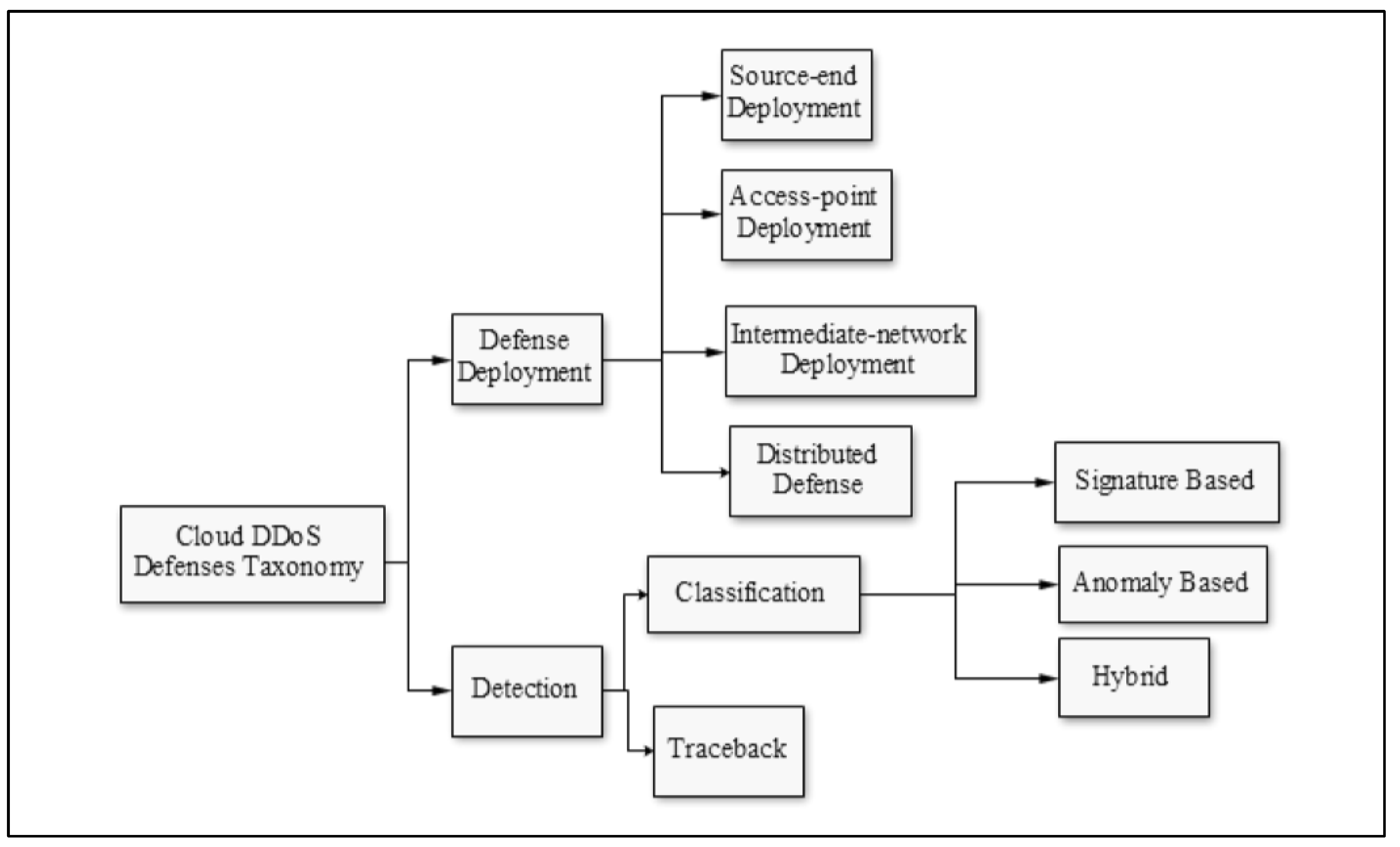
Countermeasures for DDoS Attacks
Countermeasures for Data Breaches
4.2. Proposed Countermeasures (Defense Solution)
Proposed Countermeasures Cloud DDos Attack (Defense Solution)
Proposed Countermeasures Data Breach Attack
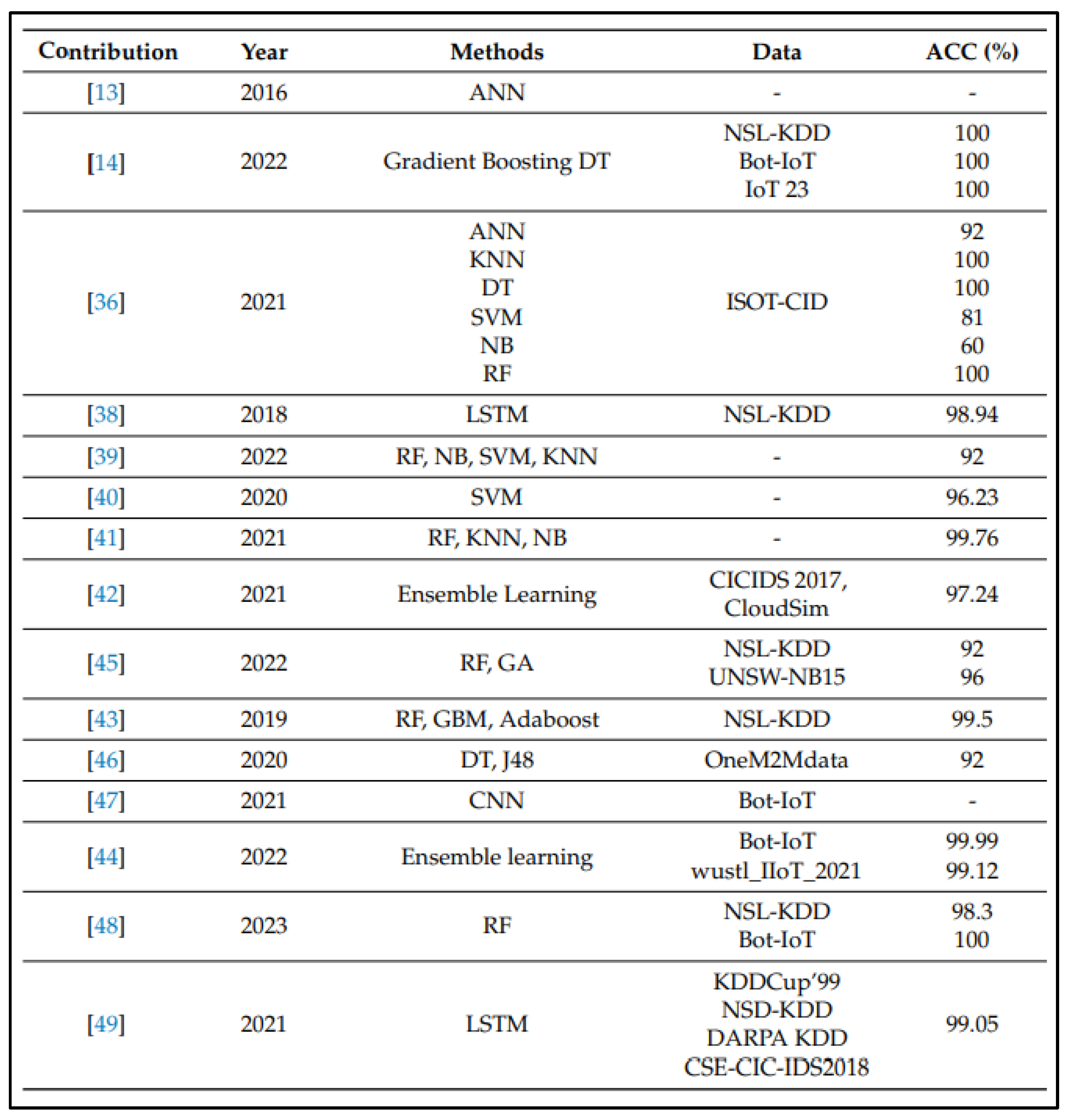
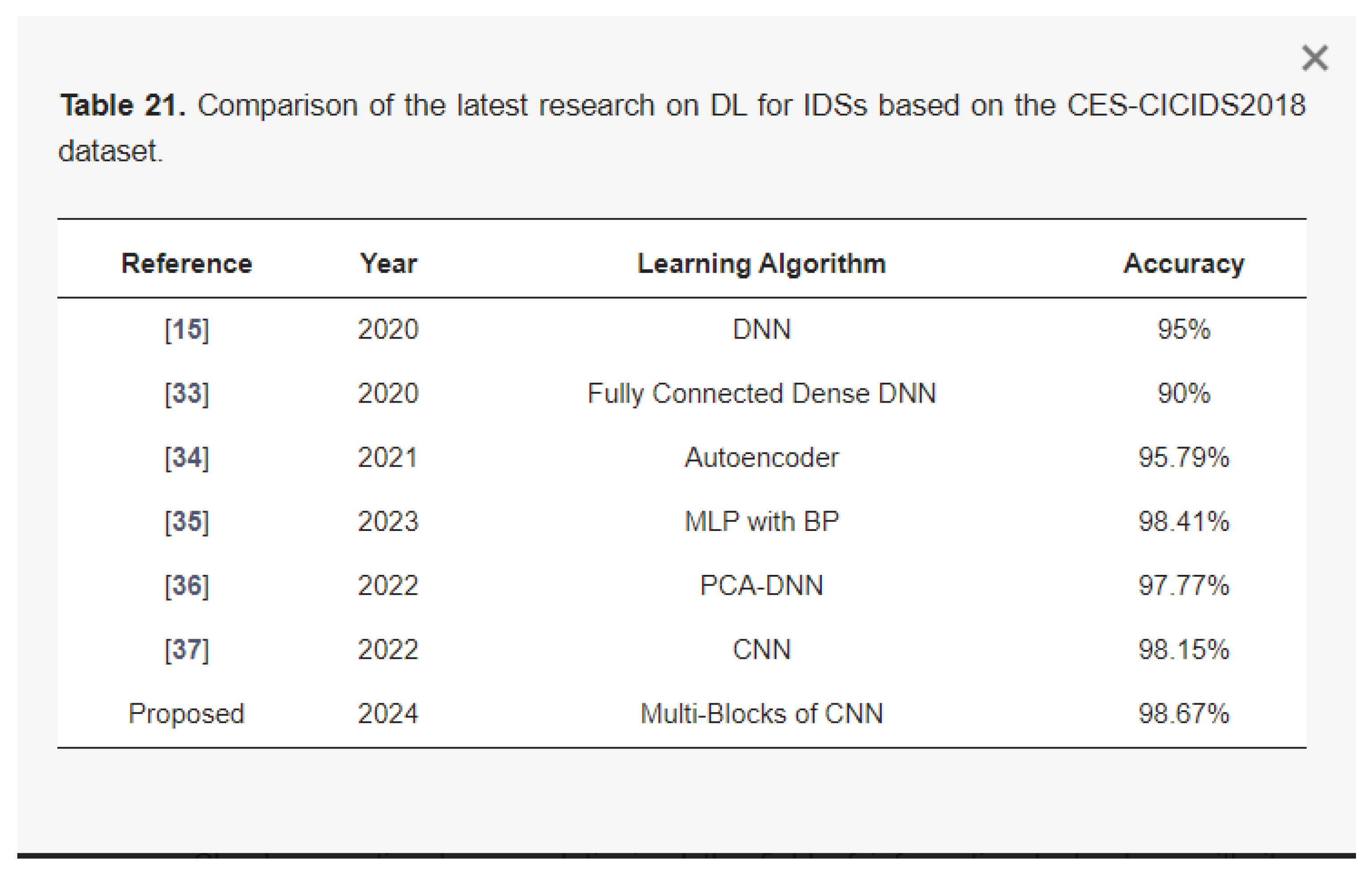
Proposed Countermeasure (IDS)
5.0. Conclusions
References
- A Systematic Literature Review on Cloud Computing Security: Threats and Mitigation Strategies. (2021). IEEE Journals & Magazine | IEEE Xplore. https://ieeexplore.ieee.org/abstract/document/9404177. [CrossRef]
- Academy, C. (2023). The Data Encryption Standard (DES). Retrieved from Cryptography Academy: https://cryptographyacademy.com/des/.
- Achar, S. (2022). Cloud Computing Security for Multi-Cloud Service Providers: Controls and Techniques in our Modern Threat Landscape. Zenodo (CERN European Organization for Nuclear Research). [CrossRef]
- Alex, S. A., Jhanjhi, N., Humayun, M., Ibrahim, A. O., & Abulfaraj, A. W. (2022). Deep LSTM Model for Diabetes Prediction with Class Balancing by SMOTE. Electronics, 11(17), 2737. [CrossRef]
- Alferidah, D. K., & Jhanjhi, N. (2020). Cybersecurity Impact over Bigdata and IoT Growth. 2020 International Conference on Computational Intelligence (ICCI). [CrossRef]
- Aljuaid, W.H. and Alshamrani, S.S. (2024). A Deep Learning Approach for Intrusion Detection Systems in Cloud Computing Environments. Applied Sciences, [online] 14(13), p.5381. [CrossRef]
- Aljumah, A., & Ahanger, T. A. (2020). Cyber security threats, challenges and defence mechanisms in cloud computing. IET Communications, 14(7), 1185–1191. [CrossRef]
- Alkinani, M. H., Almazroi, A. A., Jhanjhi, N., & Khan, N. A. (2021). 5G and IoT Based Reporting and Accident Detection (RAD) System to Deliver First Aid Box Using Unmanned Aerial Vehicle. Sensors, 21(20), 6905. [CrossRef]
- America’s Cyber Defense Agency. (n.d.). Cybersecurity Best Practices | Cybersecurity and Infrastructure Security Agency CISA. https://www.cisa.gov/topics/cybersecurity-best-practices.
- Ananna, F. F., Nowreen, R., Jahwari, S. S. R. A., Costa, E. A., Angeline, L., & Sindiramutty, S. R. (2023). Analysing Influential factors in student academic achievement: Prediction modelling and insight. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence, 2(1). [CrossRef]
- Attacks from the Cloud. (25 September, 2024). Retrieved from ISC2: https://www.isc2.org/Insights/2024/09/Cloud-Security-INSIGHTS-Attacks-from-the-Cloud#.
- Attou, H., Mohy-eddine, M., Guezzaz, A., Benkirane, S., Azrour, M., Alabdultif, A. and Almusallam, N. (2023). Towards an Intelligent Intrusion Detection System to Detect Malicious Activities in Cloud Computing. Applied Sciences, [online] 13(17), p.9588. [CrossRef]
- Aweda, Z. I. (2024, January 3). What is Cloud Computing? Introduction to the Cloud for Beginners. freeCodeCamp.org. https://www.freecodecamp.org/news/what-is-cloud-computing/.
- Azam, H., Dulloo, M. I., Majeed, M. H., Wan, J. P. H., Xin, L. T., & Sindiramutty, S. R. (2023). Cybercrime Unmasked: Investigating cases and digital evidence. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence, 2(1). [CrossRef]
- Azam, H., Dulloo, M. I., Majeed, M. H., Wan, J. P. H., Xin, L. T., Tajwar, M. A., & Sindiramutty, S. R. (2023). Defending the digital Frontier: IDPS and the battle against Cyber threat. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence, 2(1). [CrossRef]
- Azam, H., Tajwar, M. A., Mayhialagan, S., Davis, A. J., Yik, C. J., Ali, D., & Sindiramutty, S. R. (2023). Innovations in Security: A study of cloud Computing and IoT. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence, 2(1). [CrossRef]
- Azam, H., Tan, M., Pin, L. T., Syahmi, M. A., Qian, A. L. W., Jingyan, H., Uddin, M. F., & Sindiramutty, S. R. (2023). Wireless Technology Security and Privacy: A Comprehensive Study. Preprints.org. [CrossRef]
- Babbar, H., Rani, S., Masud, M., Verma, S., Anand, D., & Jhanjhi, N. (2021). Load balancing algorithm for migrating switches in software-defined vehicular networks. Computers, Materials & Continua/Computers, Materials & Continua (Print), 67(1), 1301–1316. [CrossRef]
- Balbix. (2024, October 21). What is NIST Cybersecurity Framework (CSF) 2.0? https://www.balbix.com/insights/nist-cybersecurity-framework/.
- Beltozar-Clemente, S., Iparraguirre-Villanueva, O., Félix Pucuhuayla-Revatta, Zapata-Paulini, J. and Cabanillas-Carbonell, M. (2024). Predicting Customer Abandonment in Recurrent Neural Networks using Short-Term Memory. Journal of open innovation, 10(1), pp.100237–100237. [CrossRef]
- Brohi, S. N., Jhanjhi, N., Brohi, N. N., & Brohi, M. N. (2020). Key Applications of State-of-the-Art Technologies to Mitigate and Eliminate COVID-19.pdf. TECHRxiv. [CrossRef]
- CDNetworks. (2020, December 23). 7 Biggest Cloud Security Benefits. CDNetworks. https://www.cdnetworks.com/blog/cloud-security/what-is-cloud-security-and-what-are-the-benefits/.
- Chesti, I. A., Humayun, M., Sama, N. U., & Jhanjhi, N. (2020). Evolution, Mitigation, and Prevention of Ransomware. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- Chiba, Z., Abghour, N., Moussaid, K., omri, A.E. and Rida, M. (2016). A Cooperative and Hybrid Network Intrusion Detection Framework in Cloud Computing Based on Snort and Optimized Back Propagation Neural Network. Procedia Computer Science, 83, pp.1200–1206. [CrossRef]
- Chinnasamy, V. (2024, March 4). Understanding cloud security – challenges, best practices and benefits. Indusface. https://www.indusface.com/blog/what-is-cloud-security-and-what-are-the-benefits/.
- Dalgaard, M. (2024, July 29). What is SIEM? A complete beginners guide to SIEM and Logpoint. Logpoint. https://www.logpoint.com/en/what-is-siem/.
- David Puzas (2024, April 01). 12 Cloud Security Issues: Risks, Threats, and Challenges. https://www.crowdstrike.com/en-us/cybersecurity-101/cloud-security/cloud-security-risks/.
- Davis, L. (2024, November 20). What is cloud computing? The ultimate guide. Forbes Advisor. https://www.forbes.com/advisor/business/what-is-cloud-computing/.
- Dogra, V., Singh, A., Verma, S., Kavita, N., Jhanjhi, N. Z., & Talib, M. N. (2021). Analyzing DistilBERT for Sentiment Classification of Banking Financial News. In Lecture notes in networks and systems (pp. 501–510). [CrossRef]
- Fandrick, B. (7 November, 2024). HIPAA vs. PCI DSS requirements for data protection. Retrieved from Liquid Web: https://www.liquidweb.com/blog/hipaa-vs-pci/#:~:text=Data%20protection%20standards%20and%20security%20controls&text=HIPAA%20requires%20covered%20entities%20to,expiration%20dates%2C%20and%20security%20codes.
- Fatima-Tuz-Zahra, N., Jhanjhi, N., Brohi, S. N., Malik, N. A., & Humayun, M. (2020). Proposing a Hybrid RPL Protocol for Rank and Wormhole Attack Mitigation using Machine Learning. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- Fortinet. (n.d.). What is a Data Breach and How to Prevent It? | Fortinet. https://www.fortinet.com/resources/cyberglossary/data-breach.
- Fouda, M., Ksantini, R. and Elmedany, W. (2022). A Novel Intrusion Detection System for Internet of Healthcare Things Based on Deep Subclasses Dispersion Information. IEEE Internet of Things Journal, pp.1–1. [CrossRef]
- GeeksforGeeks. (2020, June 24). Advantages and Disadvantages of cloud security. GeeksforGeeks. https://www.geeksforgeeks.org/advantages-and-disadvantages-of-cloud-security/.
- Gill, S. H., Sheikh, N. A., Rajpar, S., Jhanjhi, N. Z., Ahmad, M., Razzaq, M. A.,... & Jaafar, F. (2021). Extended Forgery Detection Framework for COVID-19 Medical Data Using Convolutional Neural Network. Computers, Materials & Continua, 68(3).
- Gopi, R., Sathiyamoorthi, V., Selvakumar, S., Manikandan, R., Chatterjee, P., Jhanjhi, N. Z., & Luhach, A. K. (2021). Enhanced method of ANN based model for detection of DDoS attacks on multimedia internet of things. Multimedia Tools and Applications, 81(19), 26739–26757. [CrossRef]
- Gouda, W., Almurafeh, M., Humayun, M., & Jhanjhi, N. Z. (2022). Detection of COVID-19 based on chest x-rays using deep learning. Healthcare, 10(2), 343. [CrossRef]
- Gruber, D. & TechTarget, Inc. (2024). Advances in Endpoint Security (By Broadcom). https://docs.broadcom.com/doc/advances-in-endpoint-security.
- Gupta, P. (2023, March 26). What is Cloud Access Security Broker (CASB)? - Pradeep Gupta - Medium. Medium. https://medium.com/@pradeepgupta_9558/what-is-cloud-access-security-broker-casb-a6bbbf468dd1.
- Hidayat, T., & Mahardiko, R. (2020). A Systematic Literature Review Method on AES Algorithm for Data Sharing Encryption on Cloud Computing. International Journal of Artificial Intelligence Research, 4(1). [CrossRef]
- Humayun, M., Sujatha, R., Almuayqil, S. N., & Jhanjhi, N. Z. (2022). A Transfer Learning Approach with a Convolutional Neural Network for the Classification of Lung Carcinoma. Healthcare, 10(6), 1058. [CrossRef]
- Humayun, M., Jhanjhi, N. Z., Hamid, B., & Ahmed, G. (2020). Emerging smart logistics and transportation using IoT and blockchain. IEEE Internet of Things Magazine, 3(2), 58-62.
- Hussain, K., Rahmatyar, A. R., Riskhan, B., Sheikh, M. a. U., & Sindiramutty, S. R. (2024). Threats and Vulnerabilities of Wireless Networks in the Internet of Things (IoT). 2024 IEEE 1st Karachi Section Humanitarian Technology Conference (KHI-HTC), 2, 1–8. [CrossRef]
- Jhanjhi, N., Humayun, M., & Almuayqil, S. N. (2021). Cyber security and privacy issues in industrial internet of things. Computer Systems Science and Engineering, 37(3), 361–380. [CrossRef]
- Jun, A. Y. M., Jinu, B. A., Seng, L. K., Maharaiq, M. H. F. B. Z., Khongsuwan, W., Junn, B. T. K., Hao, A. a. W., & Sindiramutty, S. R. (2024). Exploring the Impact of Crypto-Ransomware on Critical Industries: Case Studies and Solutions. Preprints.org. [CrossRef]
- Kafhali, S.E., Mir, I.E., Hanini, M., 2021. Security Threats, Defense Mechanisms, Challenges, and Future Directions in Cloud Computing. Archives of Computational Methods in Engineering 29, 223–246. [CrossRef]
- Khan, N., Mohmand, M.I., Rehman, S. ur, Ullah, Z., Khan, Z. and Wadii Boulila (2024). Advancements in intrusion detection: A lightweight hybrid RNN-RF model. PLoS ONE, 19(6), pp.e0299666–e0299666. [CrossRef]
- Kumar, M. S., Vimal, S., Jhanjhi, N., Dhanabalan, S. S., & Alhumyani, H. A. (2021). Blockchain based peer to peer communication in autonomous drone operation. Energy Reports, 7, 7925–7939. [CrossRef]
- Li, J., Goh, W., Jhanjhi, N. Z., Isa, F., & Balakrishnan, S. (2021). An empirical study on challenges faced by the elderly in care centres. EAI Endorsed Transactions on Pervasive Health and Technology, 7(28).
- Lim, M., Abdullah, A., Jhanjhi, N., Khan, M. K., & Supramaniam, M. (2019). Link Prediction in Time-Evolving Criminal Network with deep Reinforcement learning technique. IEEE Access, 7, 184797–184807. [CrossRef]
- Liu, H. and Lang, B. (2019). Machine Learning and Deep Learning Methods for Intrusion Detection Systems: A Survey. Applied Sciences, [online] 9(20), p.4396. [CrossRef]
- Maine Basan. (May 28, 2024). Top Cloud Security Issues: Threats, Risks, Challenges & Solutions. https://www.esecurityplanet.com/cloud/cloud-security-threats/.
- Manchuri, A., Kakera, A., Saleh, A., & Raja, S. (2024). pplication of Supervised Machine Learning Models in Biodiesel Production Research - A Short Review. Borneo Journal of Sciences and Technology. [CrossRef]
- Media, T. (23 February, 2023). Why the Cloud is Potentially Vulnerable. Retrieved from ThriveDX: https://thrivedx.com/resources/blog/why-the-cloud-is-potentially-vulnerable#:~:text=Lack%20of%20Physical%20Control,-Cloud%20data%20and&text=There%20is%20limited%20control%20over,is%20so%20vulnerable%20to%20cybercriminals.
- Mohammed, I.A. (2019) (PDF) Cloud Identity and Access Management - A Model Proposal, CLOUD IDENTITY AND ACCESS MANAGEMENT – A MODEL PROPOSAL. Available at: https://www.researchgate.net/publication/353887567_CLOUD_IDENTITY_AND_ACCESS_MANAGEMENT_-_A_MODEL_PROPOSA.
- Muzafar, S. (2021). Energy harvesting models and techniques for green IoT: A review. Role of IoT in Green Energy Systems, 117-143.
- Nayyar, A., Gadhavi, L., & Zaman, N. (2021). Machine learning in healthcare: review, opportunities and challenges. In Elsevier eBooks (pp. 23–45). [CrossRef]
- Ot, A. (2023, July 11). The Ultimate guide to cloud Computing. Datamation. https://www.datamation.com/cloud/what-is-cloud-computing/.
- Pramanik, S., Samantha, D., M, V., & Guha, A. (2022). Cyber security and network security. In Wiley eBooks. [CrossRef]
- Ranger, S. (2022, February 25). What is cloud computing? Everything you need to know about the cloud explained. ZDNET. https://www.zdnet.com/article/what-is-cloud-computing-everything-you-need-to-know-about-the-cloud/.
- Ravichandran, N., Tewaraja, T., Rajasegaran, V., Kumar, S. S., Gunasekar, S. K. L., & Sindiramutty, S. R. (2024). Comprehensive Review Analysis and Countermeasures for Cybersecurity Threats: DDoS, Ransomware, and Trojan Horse Attacks. Preprints.org. [CrossRef]
- Richman, A. (9 October, 2023). Data Masking vs Encryption: What You Need to Know. Retrieved from K2View: https://www.k2view.com/blog/data-masking-vs-encryption.
- Saleh, M., Jhanjhi, N., & Abdullah, A. (2020, February). Fatima-tuz-Zahra,‘‘Proposing a privacy protection model in case of civilian drone,’’. In Proc. 22nd Int. Conf. Adv. Commun. Technol.(ICACT) (pp. 596-602).
- Sama, N. U., Zen, K., Humayun, M., Jhanjhi, N. Z., & Rahman, A. U. (2022). Security in wireless body sensor network: A multivocal literature study. Applied System Innovation, 5(4), 79.
- Seng, Y. J., Cen, T. Y., Raslan, M. a. H. B. M., Subramaniam, M. R., Xin, L. Y., Kin, S. J., Long, M. S., & Sindiramutty, S. R. (2024). In-Depth Analysis and Countermeasures for Ransomware Attacks: Case Studies and Recommendations. Preprints.org. [CrossRef]
- SentinelOne (2024, October 25). 17 Security Risks of Cloud Computing in 2024. https://www.sentinelone.com/cybersecurity-101/cloud-security/security-risks-of-cloud-computing/.
- Shah, I. A., Jhanjhi, N. Z., & Laraib, A. (2022). Cybersecurity and blockchain usage in contemporary business. In Advances in information security, privacy, and ethics book series (pp. 49–64). [CrossRef]
- Sharma, R., Singh, A., Kavita, N., Jhanjhi, N. Z., Masud, M., Jaha, E. S., & Verma, S. (2021). Plant disease diagnosis and image classification using deep learning. Computers, Materials & Continua/Computers, Materials & Continua (Print), 71(2), 2125–2140. [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Shah, B., & Manchuri, A. R. (2024). Cybersecurity measures for logistics industry. In Advances in information security, privacy, and ethics book series (pp. 1–58). [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Shah, B., Yun, K. J., Ray, S. K., Jazri, H., & Hussain, M. (2024). Future trends and emerging threats in drone cybersecurity. In Advances in information security, privacy, and ethics book series (pp. 148–195). [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Yun, K. J., Manchuri, A. R., Ashraf, H., Murugesan, R. K., Tee, W. J., & Hussain, M. (2024). Data security and privacy concerns in drone operations. In Advances in information security, privacy, and ethics book series (pp. 236–290). [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N., Tan, C. E., Lau, S. P., Muniandy, L., Gharib, A. H., Ashraf, H., & Murugesan, R. K. (2024). Industry 4.0. In Advances in logistics, operations, and management science book series (pp. 342–405). [CrossRef]
- Sindiramutty, S. R., Tan, C. E., & Wei, G. W. (2024). Eyes in the sky. In Advances in information security, privacy, and ethics book series (pp. 405–451). [CrossRef]
- Sindiramutty, S. R., Tan, C. E., Shah, B., Khan, N. A., Gharib, A. H., Manchuri, A. R., Muniandy, L., Ray, S. K., & Jazri, H. (2024). Ethical considerations in drone cybersecurity. In Advances in information security, privacy, and ethics book series (pp. 42–87). [CrossRef]
- Singh Solanki, P., Singh, A., Sao, S., & Atkekar, N. D. (2024). Int. J. of Sci. Research in Network Security and Communication (Vol. 12). Prof. (Dr.) Umesh Kumar Singh. [CrossRef]
- Singhal, V., Jain, S. S., Anand, D., Singh, A., Verma, S., Kavita, N., Rodrigues, J. J. P. C., Jhanjhi, N. Z., Ghosh, U., Jo, O., & Iwendi, C. (2020). Artificial Intelligence Enabled Road Vehicle-Train Collision Risk Assessment Framework for Unmanned railway level crossings. IEEE Access, 8, 113790–113806. [CrossRef]
- Srinivasan, K., Garg, L., Chen, B. Y., Alaboudi, A. A., Jhanjhi, N. Z., Chang, C. T.,... & Deepa, N. (2021). Expert System for Stable Power Generation Prediction in Microbial Fuel Cell. Intelligent Automation & Soft Computing, 30(1).
- Sushmith. (2024, October 21). Data breaches in cloud computing | Tips to Prevent. Sprintzeal.com. https://www.sprintzeal.com/blog/data-breaches-in-cloud-computing.
- View of A Survey on Cloud Computing Security Threats, Attacks and Countermeasures: A Review [WWW Document], n.d. URL https://www.milestoneresearch.in/JOURNALS/index.php/IJHCI/article/view/34/46.
- Waheed, A., Seegolam, B., Jowaheer, M. F., Sze, C. L. X., Hua, E. T. F., & Sindiramutty, S. R. (2024). Zero-Day Exploits in Cybersecurity: Case Studies and Countermeasure. preprints.org. [CrossRef]
- Wayne Jansen, Timothy Grance (2011, Dec), National Institute of Standards and Technology, US. Guidelines on Security and Privacy in Public Cloud Computing. https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-144.pdf.
- Wen, B. O. T., Syahriza, N., Xian, N. C. W., Wei, N. G., Shen, T. Z., Hin, Y. Z., Sindiramutty, S. R., & Nicole, T. Y. F. (2023). Detecting cyber threats with a Graph-Based NIDPS. In Advances in logistics, operations, and management science book series (pp. 36–74). [CrossRef]
- What are the benefirs of Cloud Computing. (May28, 2024). Retrieved from prosimo.io: https://prosimo.io/what-are-the-benefits-of-cloud-computing/.
- What are the Benefits of Cloud Security? (2021, August 25). Utimaco. https://utimaco.com/service/knowledge-base/cloud-security/what-are-benefits-cloud-security.
- What is Cloud Backup? How It Works, Benefits and Best Practices. (5 February, 2024). Retrieved from Spanning: https://www.spanning.com/blog/cloud-backup/.
- Why is the cloud so cost-effective? (4 Febuary, 2023). Retrieved from Box Blogs: https://blog.box.com/why-is-the-cloud-so-cost-effective.
- Yasar, K., Froehlich, A., & Shea, S. (2024, June 13). cloud security. Search Security. https://www.techtarget.com/searchsecurity/definition/cloud-security.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



