Submitted:
05 January 2025
Posted:
06 January 2025
You are already at the latest version
Abstract
Keywords:
1. Background Studies
- Overview of Blockchain
- II.
- History of Blockchain
- III.
- Revolutionary Period
2. Types of Blockchain
- Permissionless Blockchain
- II.
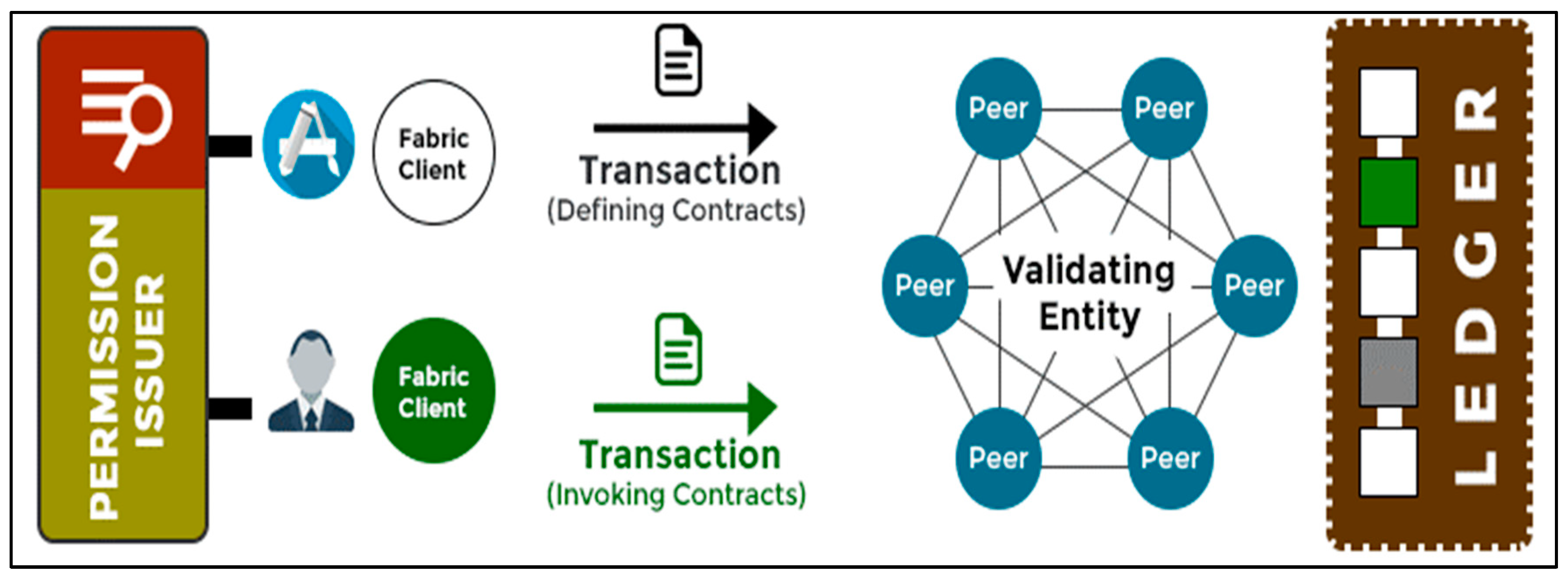
- Permissioned Blockchain
- III.
- Consortium Blockchain
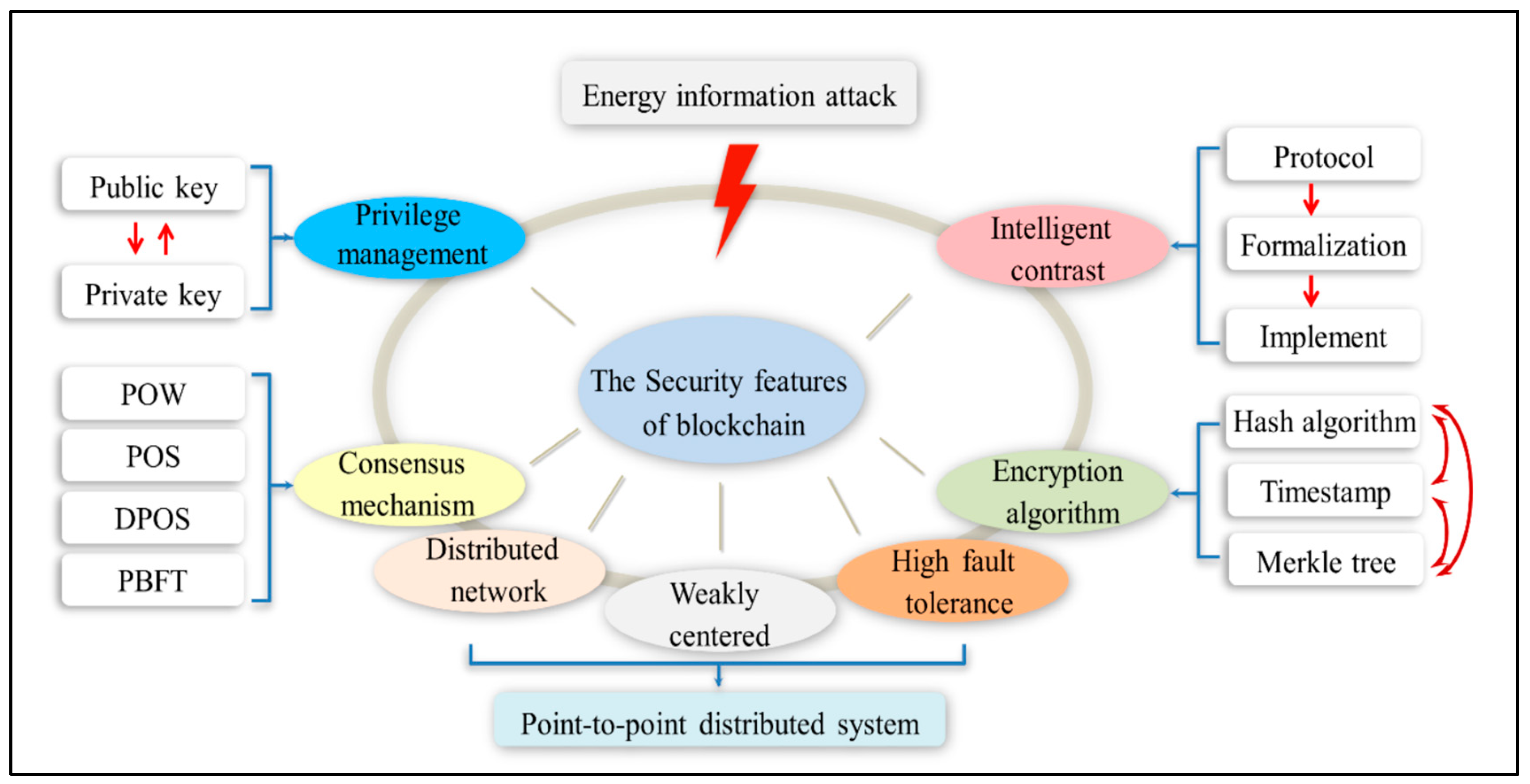
3. How Blockchain Security Works
- Components
- II.
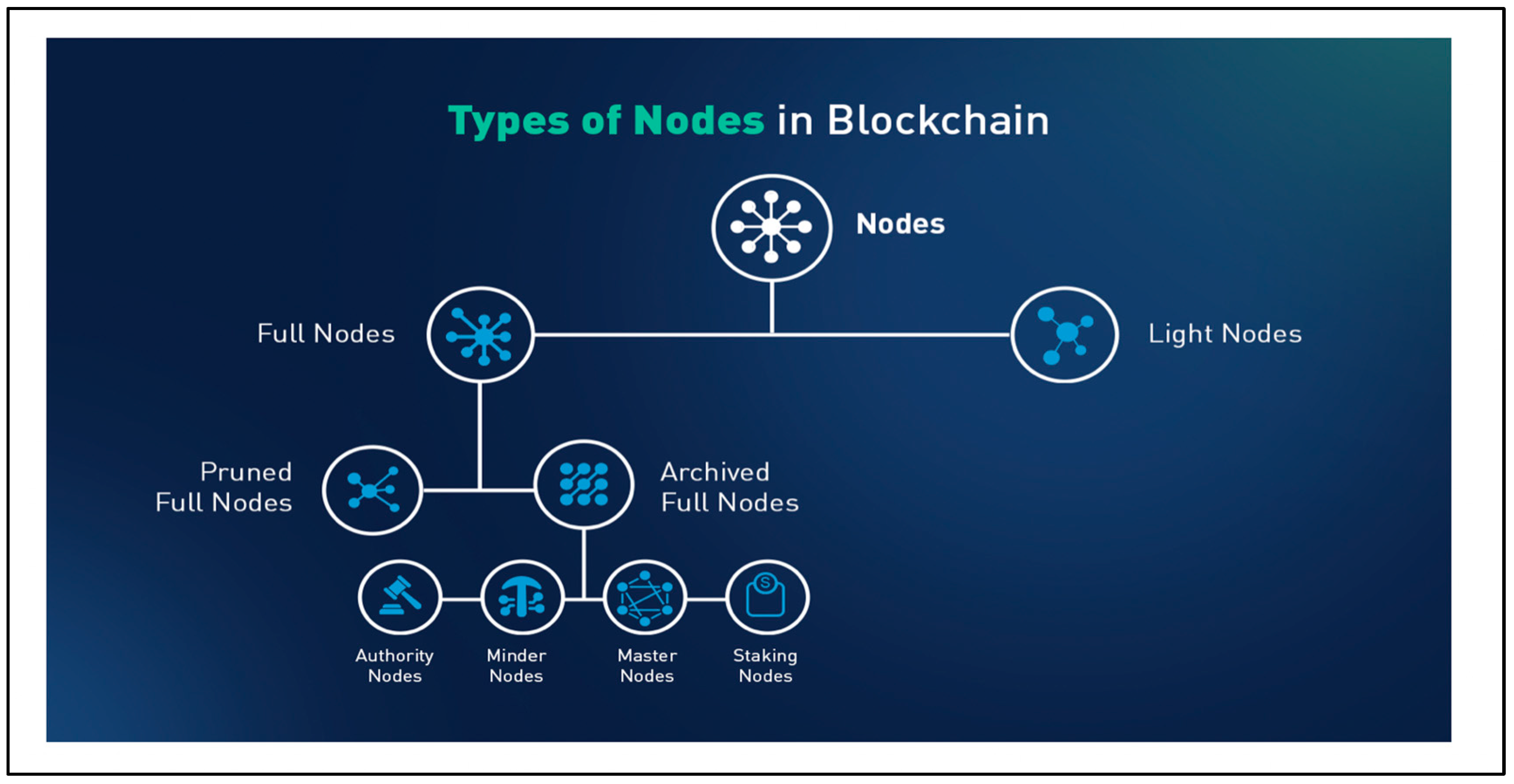
- Nodes
- III.
- Ledgers
- IV.
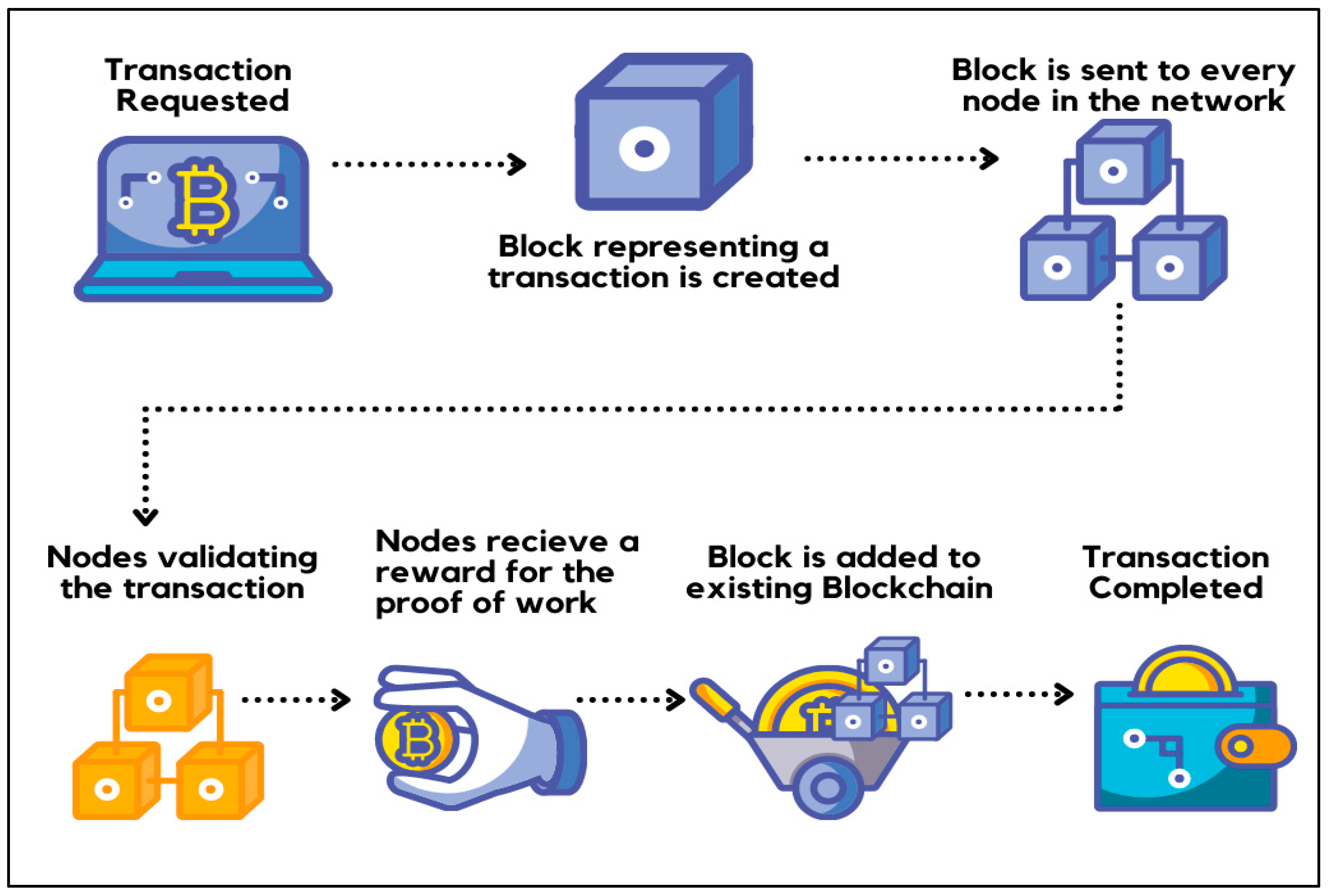
- Transactions
- V.
- Consensus mechanisms
- VI.
- Peer-to-Peer Network
- VII.
- Process of Blockchain
4. Threats to Blockhain
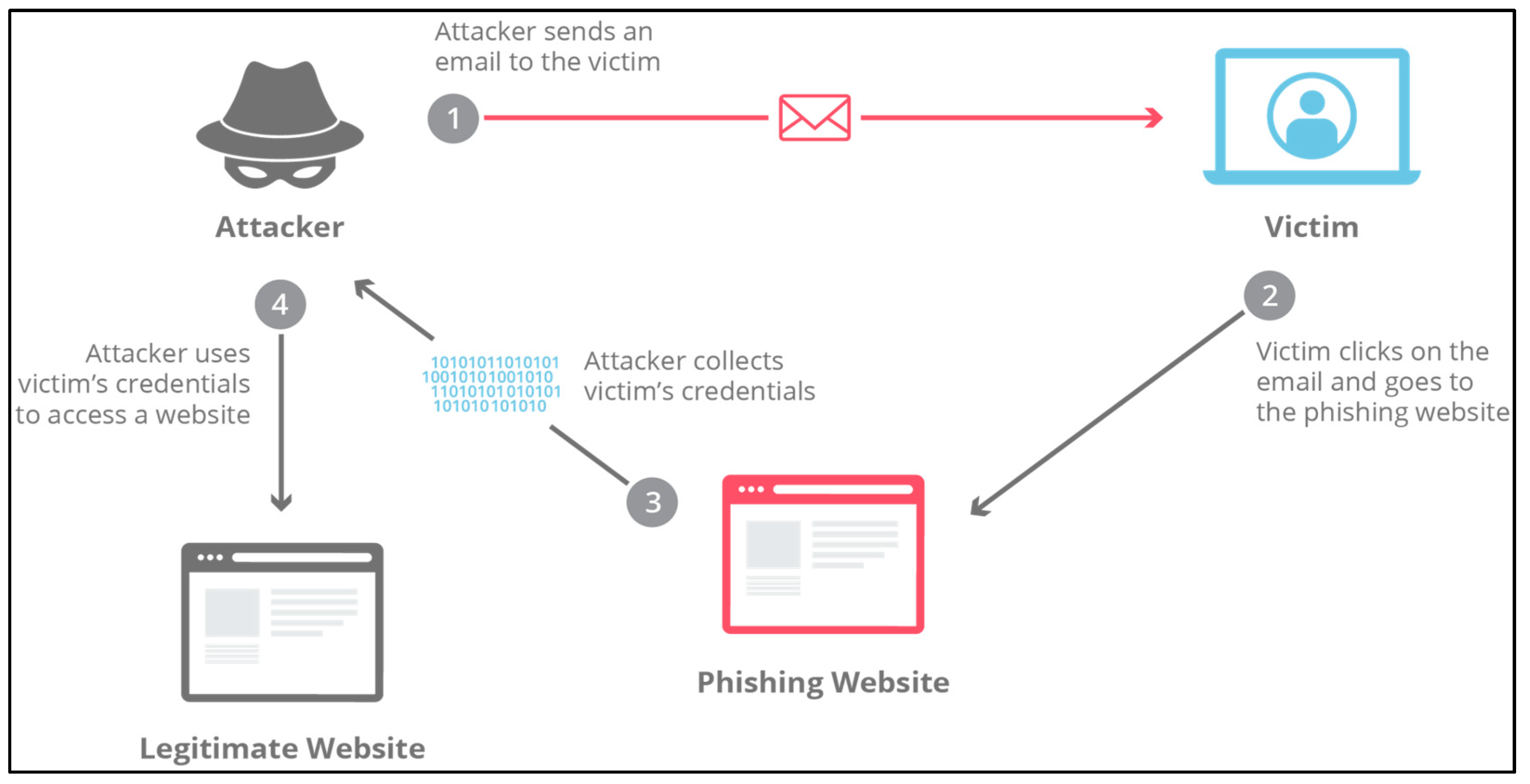
- Phishing attacks
- II.
- Routing attacks
- III.
- Sybil attacks
- IV.
- 51% attacks
5. Examples of Blockchain Security
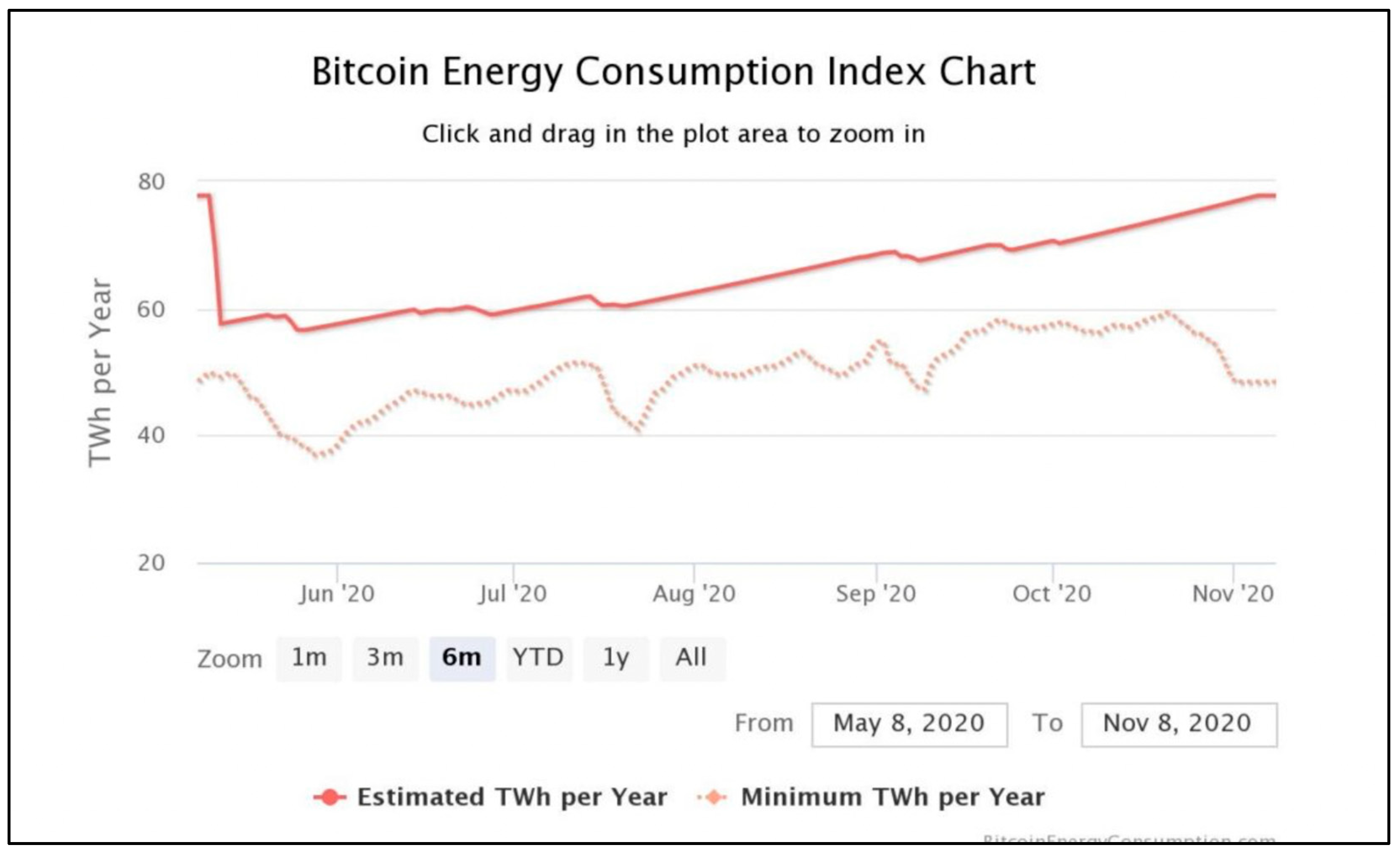
- Bitcoin Blockchain
- II.
- Ethereum Blockchain
- III.
- Hyperledger Fabric for Healthcare
6. Impact of Blockchain Security
- Benefits of Blockchain Security
- II.
- Decentralized Architecture
- III.
- Cryptography and Consensus Mechanisms
- IV.
- Smart contracts
7. Limitations of Blockchain Security
- Scalability
- II.
- System Failures
8. Future Potentials
- Integration of AI and ML
- II.
- Improve Cybersecurity
- III.
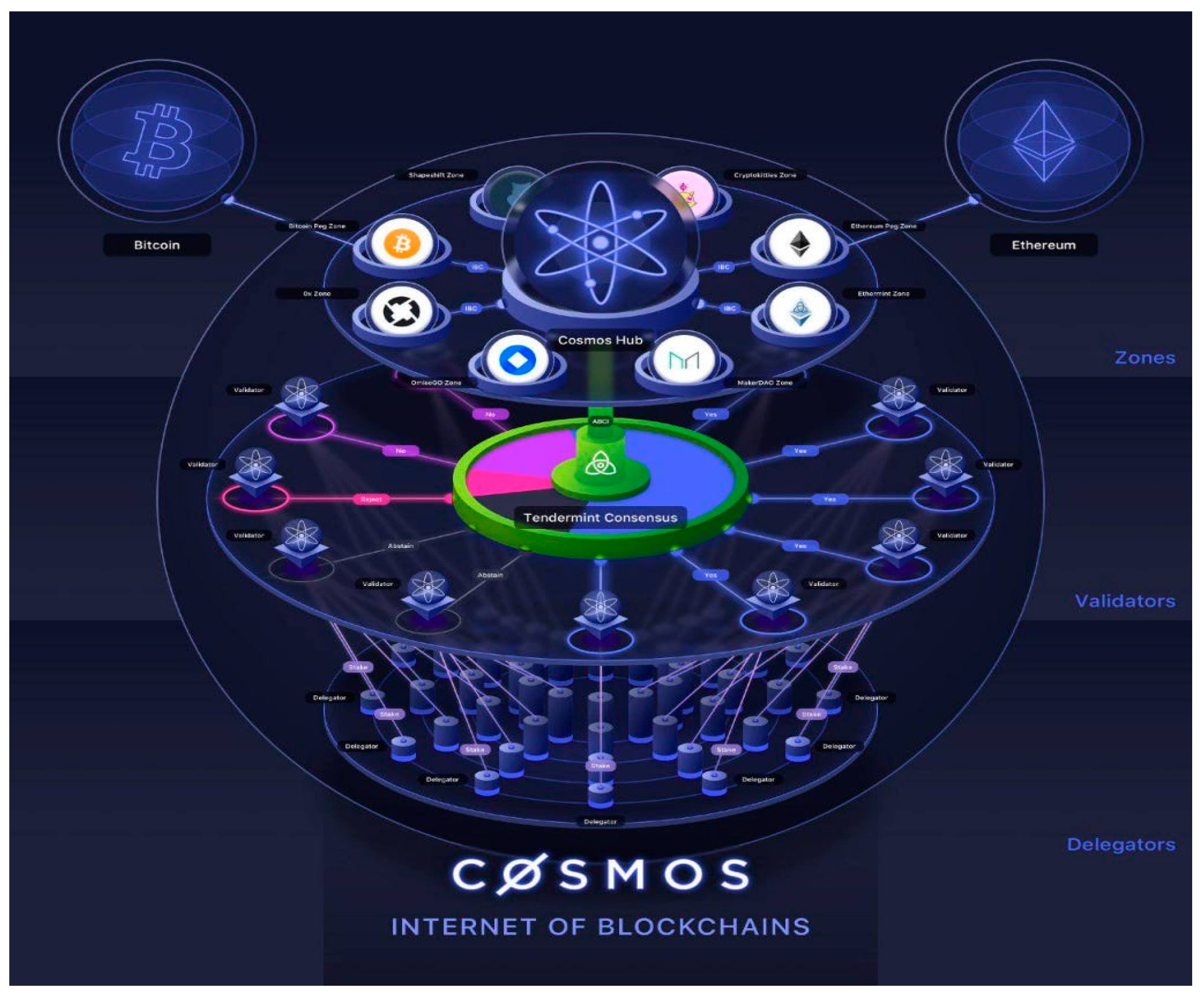
- Improve Interoperability
- IV.
- Decentralized File Storage
9. Security Measures
- Existing Security Measures
- II.
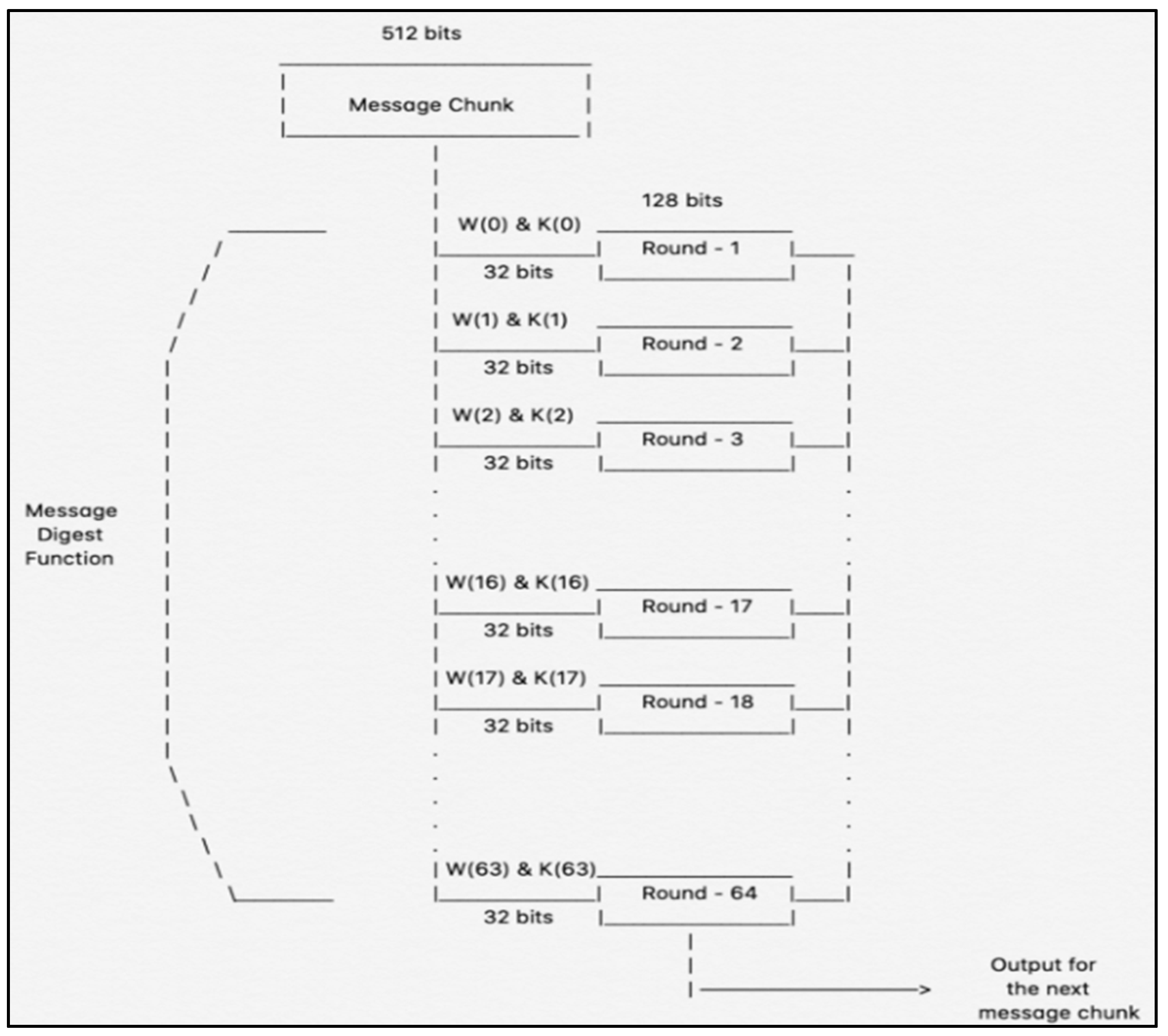
- Cryptographic Hashing
- III.
- Decentralisation
- IV.
- Public-Key Cryptography (PKC)
- V.
- Proof Of Work (PoW)
- VI.
- Smart Contracts
10. Proposed Security Measures
- Proofs of Zero-Knowledge (ZKPs)
- II.
- AI-Powered Threat Detection
- III.
- Adaptive Consensus Mechanisms
- IV.
- Layered Security Architecture
11. Conclusion
Future Improvement Suggestions
References
- @coinbase. (2024a). What is blockchain interoperability? Available online: https://www.coinbase.com/en-gb/learn/crypto-glossary/what-is-blockchain-interoperability.
- @coinbase. (2024b). What is Delegated Proof of Stake (DPoS)? Available online: https://www.coinbase.com/en-gb/learn/crypto-glossary/what-is-delegated-proof-of-stake-dpos.
- A S, R. (2022). What is Blockchain Technology and How Does It Work? [online] Simplilearn.com. Available online: https://www.simplilearn.com/tutorials/blockchain-tutorial/blockchain-technology.
- Aimasterclass.com. (2024). What is Blockchain for AI Security? Available online: https://www.aimasterclass.com/glossary/blockchain-for-ai-security.
- Alex, S. A. , Jhanjhi, N., Humayun, M., Ibrahim, A. O., & Abulfaraj, A. W. Deep LSTM Model for Diabetes Prediction with Class Balancing by SMOTE. Electronics 2022, 11, 2737. [Google Scholar] [CrossRef]
- Alexandra, S. (2023). What is Phishing and How to Prevent It? [online] GlobalSign. Available online: https://www.globalsign.com/en/blog/what-is-phishing.
- Alferidah, D. K. , & Jhanjhi, N. (2020). Cybersecurity Impact over Bigdata and IoT Growth. 2020 International Conference on Computational Intelligence (ICCI). [CrossRef]
- Alkinani, M. H. , Almazroi, A. A., Jhanjhi, N., & Khan, N. A. 5G and IoT Based Reporting and Accident Detection (RAD) System to Deliver First Aid Box Using Unmanned Aerial Vehicle. Sensors 2021, 21, 6905. [Google Scholar] [CrossRef]
- Amazon Web Services, Inc. (2022). What is Ethereum? - Ethereum Explained - AWS. Available online: https://aws.amazon.com/web3/what-is-ethereum/.
- Ananna, F. F. , Nowreen, R., Jahwari, S. S. R. A., Costa, E. A., Angeline, L., & Sindiramutty, S. R. Analysing Influential factors in student academic achievement: Prediction modelling and insight. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence. [CrossRef]
- Antwi, M. , Adnane, A., Ahmad, F., Hussain, R., Habib ur Rehman, M. and Kerrache, C.A. The Case of HyperLedger Fabric as a Blockchain Solution for Healthcare Applications. Blockchain: Research and Applications 2021, 2, 100012. [Google Scholar] [CrossRef]
- Anwar, S. , Anayat, S., Butt, S., Butt, S. and Saad, M. Generation Analysis of Blockchain Technology: Bitcoin and Ethereum. International Journal of Information Engineering and Electronic Business 2020, 12, 30–39. [Google Scholar] [CrossRef]
- Appinventiv.com. (2024). Available online: https://appinventiv.com/wp-content/uploads/2023/03/How-blockchain-resolves-data-privacy-and-security-issues-for-businesses-04.webp.
- Azam, H. , Dulloo, M. I., Majeed, M. H., Wan, J. P. H., Xin, L. T., & Sindiramutty, S. R. Cybercrime Unmasked: Investigating cases and digital evidence. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence. [CrossRef]
- Azam, H. , Dulloo, M. I., Majeed, M. H., Wan, J. P. H., Xin, L. T., Tajwar, M. A., & Sindiramutty, S. R. Defending the digital Frontier: IDPS and the battle against Cyber threat. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence. [CrossRef]
- Azam, H. , Tajwar, M. A., Mayhialagan, S., Davis, A. J., Yik, C. J., Ali, D., & Sindiramutty, S. R. Innovations in Security: A study of cloud Computing and IoT. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence. [CrossRef]
- Azam, H. , Tan, M., Pin, L. T., Syahmi, M. A., Qian, A. L. W., Jingyan, H., Uddin, M. F., & Sindiramutty, S. R. (2023). Wireless Technology Security and Privacy: A Comprehensive Study. Preprints.org. [CrossRef]
- Babbar, H. , Rani, S., Masud, M., Verma, S., Anand, D., & Jhanjhi, N. Load balancing algorithm for migrating switches in software-defined vehicular networks. Computers, Materials & Continua/Computers, Materials & Continua (Print) 2021, 67, 1301–1316. [Google Scholar] [CrossRef]
- Becher, B. (2024). What Is Blockchain Technology? How Does Blockchain Work? | Built In. [online] Builtin.com. Available online: https://builtin.com/blockchain.
- Berlove, O. (2021). What are public and private key pairs and how do they work. [online] PreVeil. Available online: https://www.preveil.com/blog/public-and-private-key/.
- Bitcoin Store. (n.d.). What is Proof-of-Work? The definition, features, and benefits. Available online: https://www.bitstore.net/en/blog/what-is-proof-of-work/.
- Brohi, S. N. , Jhanjhi, N., Brohi, N. N., & Brohi, M. N. (2020). Key Applications of State-of-the-Art Technologies to Mitigate and Eliminate COVID-19.pdf. TECHRxiv. [CrossRef]
- CEPF®, T.T. , BSc (n.d.). Decentralization in Blockchain | Definition, How It Works. [online] Finance Strategists. Available online: https://www.financestrategists.com/wealth-management/blockchain/decentralization-in-blockchain/.
- Chainlink (2024). What Is a Sybil Attack? [online] Chain.link. Available online: https://chain.link/education-hub/sybil-attack.
- Chesti, I. A. , Humayun, M., Sama, N. U., & Jhanjhi, N. (2020). Evolution, Mitigation, and Prevention of Ransomware. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- CloudFlare (2023). What is a Phishing attack? Cloudflare. Available online: https://www.cloudflare.com/learning/access-management/phishing-attack/.
- Cointelegraph. (2024). Wormhole Price Today, W to USD Live Price, Market Cap & Chart. Available online: https://cointelegraph.com/learn/articles/stablecoins-101-what-are-crypto-stablecoins-and-how-do-they-work.
- Cosmos Network. (n.d.). Cosmos Network - Internet of Blockchains. Available online: https://v1.cosmos.network/intro.
- Delwiche, O. (2023). Blockchain Technology and its Future Implications | OxJournal. [online] www.oxjournal.org. Available online: https://www.oxjournal.org/blockchain-technology-and-its-future-implications/.
- Dogra, V. , Singh, A., Verma, S., Kavita, N., Jhanjhi, N. Z., & Talib, M. N. (2021). Analyzing DistilBERT for Sentiment Classification of Banking Financial News. In Lecture notes in networks and systems (pp. 501–510). [CrossRef]
- Fatima-Tuz-Zahra, N. , Jhanjhi, N., Brohi, S. N., Malik, N. A., & Humayun, M. (2020). Proposing a Hybrid RPL Protocol for Rank and Wormhole Attack Mitigation using Machine Learning. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- Frankenfield, J. (2019). 51% Attack. [online] Investopedia. Available online: https://www.investopedia.com/terms/1/51-attack.asp.
- Frankenfield, J. (2021a). Cryptographic hash functions definition. [online] Investopedia. Available online: https://www.investopedia.com/news/cryptographic-hash-functions/.
- Frankenfield, J. (2021b). Ethereum. [online] Investopedia. Available online: https://www.investopedia.com/terms/e/ethereum.asp.
- Frankenfield, J. (2021c). What Is Proof of Work (PoW) in Blockchain? [online] Investopedia. Available online: https://www.investopedia.com/terms/p/proof-work.asp.
- Frankenfield, J. (2023). Smart Contracts. [online] Investopedia. Available at: https://www.investopedia.com/terms/s/smart-contracts.asp.
- Fueler. (2022). How Does Blockchain Security Work? Available online: https://fueler.io/blog/how-does-blockchain-security-work.
- Garnett, A.G. (2023). Britannica Money. [online] www.britannica.com. Available online: https://www.britannica.com/money/how-smart-contracts-work.
- GeeksforGeeks. (2019). Blockchain - Proof of Work (PoW). [online] Available online: https://www.geeksforgeeks.org/blockchain-proof-of-work-pow/.
- GeeksforGeeks. (2021). Components of Blockchain Network. Available online: https://www.geeksforgeeks.org/components-of-blockchain-network/.
- GeeksforGeeks. (2022). Blockchain Interoperability. Available online: https://www.geeksforgeeks.org/blockchain-interoperability/.
- Gemini. (n.d.). Public and Private Keys: What Are They? Available online: https://www.gemini.com/cryptopedia/public-private-keys-cryptography.
- GmbH, micobo (2018). Technical difference between Ethereum, Hyperledger fabric and R3 Corda. [online] Medium. Available online: https://micobo.medium.com/technical-difference-between-ethereum-hyperledger-fabric-and-r3-corda-5a58d0a6e347.
- Google Books. (2020). Digital Finance. Available online: https://books.google.com.my/books?hl=en&lr=&id=5W0DEAAAQBAJ&oi=fnd&pg=PR9&dq=tokens+components+for+blockchain+security&ots=dMvo6x2zaW&sig=GsETSDBw9M4DmDG_mdtT4UG8T6A#v=onepage&q=tokens%20components%20for%20blockchain%20security&f=false.
- Gopi, R. , Sathiyamoorthi, V., Selvakumar, S., Manikandan, R., Chatterjee, P., Jhanjhi, N. Z., & Luhach, A. K. Enhanced method of ANN based model for detection of DDoS attacks on multimedia internet of things. Multimedia Tools and Applications 2021, 81, 26739–26757. [Google Scholar] [CrossRef]
- Gouda, W. , Almurafeh, M., Humayun, M., & Jhanjhi, N. Z. Detection of COVID-19 based on chest x-rays using deep learning. Healthcare 2022, 10, 343. [Google Scholar] [CrossRef]
- Hameed, T.M. (2022). Study of the Impacts of Block Chain Technology on Private Sector Banks Performance. Available online: https://www.researchgate.net/publication/364715545_Study_of_the_Impacts_of_Block_Chain_Technology_on_Private_Sector_Banks_Performance.
- Hayes, A. (2024). Blockchain Facts: What Is It, How It Works, and How It Can Be Used. [online] Investopedia. Available online: https://www.investopedia.com/terms/b/blockchain.asp.
- Hendrickson, L. (2023a). What Are Smart Contracts on the Blockchain? [online] Identity. Available online: https://www.identity.com/what-are-smart-contracts/.
- Hendrickson, L. (2023b). What Is Hashing (Hash) in Blockchain? [online] Identity. Available online: https://www.identity.com/what-is-hashing-in-blockchain/.
- Henry, W. and Pawczuk, L. (2021). Blockchain: Ready for business. [online] Deloitte Insights. Available online: https://www2.deloitte.com/us/en/insights/focus/tech-trends/2022/blockchain-trends.html.
- Humayun, M. , Sujatha, R., Almuayqil, S. N., & Jhanjhi, N. Z. A Transfer Learning Approach with a Convolutional Neural Network for the Classification of Lung Carcinoma. Healthcare 2022, 10, 1058. [Google Scholar] [CrossRef]
- Hussain, K. , Rahmatyar, A. R., Riskhan, B., Sheikh, M. a. U., & Sindiramutty, S. R. Threats and Vulnerabilities of Wireless Networks in the Internet of Things (IoT). 2024 IEEE 1st Karachi Section Humanitarian Technology Conference (KHI-HTC) 2024, 2, 1–8. [Google Scholar] [CrossRef]
- Hyperledger Foundation (2023). Hyperledger Fabric. [online] Lfdecentralizedtrust.org. Available online: https://www.lfdecentralizedtrust.org/projects/fabric.
- IBM (2021). What is Blockchain Security? [online] IBM. Available online: https://www.ibm.com/topics/blockchain-security.
- IBM (2023). What is Hyperledger Fabric. [online] www.ibm.com. Available online: https://www.ibm.com/topics/hyperledger.
- ImmuneBytes (2020). Consensus Mechanisms Explained. [online] ImmuneBytes - Best Smart Contract Auditing | Blockchain Auditing Services. Available online: https://www.immunebytes.com/blog/consensus-mechanisms-explained/.
- Imperva (n.d.). What Is a Sybil Attack | Examples & Prevention | Imperva. [online] Learning Center. Available online: https://www.imperva.com/learn/application-security/sybil-attack/.
- Jena, B.K. (2023). What Is SHA-256 Algorithm: How it Works & Applications | Simplilearn. [online] Simplilearn.com. Available online: https://www.simplilearn.com/tutorials/cyber-security-tutorial/sha-256-algorithm.
- Jhanjhi, N. , Humayun, M., & Almuayqil, S. N. Cyber security and privacy issues in industrial internet of things. Computer Systems Science and Engineering 2021, 37, 361–380. [Google Scholar] [CrossRef]
- Jun, A. Y. M. , Jinu, B. A., Seng, L. K., Maharaiq, M. H. F. B. Z., Khongsuwan, W., Junn, B. T. K., Hao, A. a. W., & Sindiramutty, S. R. (2024). Exploring the Impact of Crypto-Ransomware on Critical Industries: Case Studies and Solutions. Preprints.org. [CrossRef]
- Kumar, M. S. , Vimal, S., Jhanjhi, N., Dhanabalan, S. S., & Alhumyani, H. A. Blockchain based peer to peer communication in autonomous drone operation. Energy Reports 2021, 7, 7925–7939. [Google Scholar] [CrossRef]
- Ledger (2019). Blockchain Security & Beyond | Ledger. [online] Ledger. Available online: https://www.ledger.com/blockchain-security-beyond.
- Ledger. (2024). Routing Attack Meaning | Ledger. Available online: https://www.ledger.com/academy/glossary/routing-attack.
- Lim, M. , Abdullah, A., Jhanjhi, N., Khan, M. K., & Supramaniam, M. Link Prediction in Time-Evolving Criminal Network with deep Reinforcement learning technique. IEEE Access 2019, 7, 184797–184807. [Google Scholar] [CrossRef]
- Ltd, M.C. (n.d.). Security in Blockchain: The Benefits of Blockchain Security Services | Microminder Cybersecurity | Holistic Cybersecurity Services. [online] Microminder Cybersecurity. Available online: https://www.micromindercs.com/blog/security-in-blockchain-the-benefits-of-block-chain-security-services.
- Manchuri, A. , Kakera, A., Saleh, A., & Raja, S. (2024). pplication of Supervised Machine Learning Models in Biodiesel Production Research - A Short Review. Borneo Journal of Sciences and Technology. [CrossRef]
- Marr, B. (2023). The 5 Biggest Problems With Blockchain Technology Everyone Must Know About. [online] Forbes. Available online: https://www.forbes.com/sites/bernardmarr/2023/04/14/the-5-biggest-problems-with-blockchain-technology-everyone-must-know-about/.
- McCann, K. (2024). Top 10 Uses of Blockchain in Cybersecurity. [online] Cybermagazine.com. Available online: https://cybermagazine.com/articles/top-10-blockchain-strategies.
- McKinsey & Company. (2022). What is blockchain? Available online: https://mckinsey.com/featured-insights/mckinsey-explainers/what-is-blockchain#/.
- Medium. (2024). Medium. Available online: https://juliankoh.medium.com/a-deep-look-into-cosmos-the-internet-of-blockchains-af3aa1a97a5 (accessed on 29 November 2024).
- Merehead. (n.d.). Benefits of Blockchain Hyperledger Fabric. Available online: https://merehead.com/blog/benefits-of-blockchain-hyperledger-fabric/.
- Microminder Cybersecurity Ltd (2024). Future of Blockchain Cybersecurity: Emerging Trends and Solutions | Microminder Cybersecurity | Holistic Cybersecurity Services. [online] Microminder Cybersecurity. Available online: https://www.micromindercs.com/blog/future-of-block-chain-cybersecurity-emerging-trends-and-solutions.
- Mitra, M. (2018). 6 Challenges of Blockchain. [online] Mantra Labs. Available online: https://www.mantralabsglobal.com/blog/challenges-of-blockchain/.
- mpeintner (2024). [New research] How well does SHA256 protect against modern password cracking? [online] Specops Software. Available online: https://specopssoft.com/blog/sha256-hashing-password-cracking/.
- Nayyar, A. , Gadhavi, L., & Zaman, N. (2021). Machine learning in healthcare: review, opportunities and challenges. In Elsevier eBooks (pp. 23–45). [CrossRef]
- nordlayer.com. (n.d.). Common blockchain security issues and how to prevent them. [online] Available online: https://nordlayer.com/blog/blockchain-security-issues/.
- OKX (2023). Delegated Proof of Stake (DPoS) Explained. [online] OKX. Available online: https://www.okx.com/learn/delegated-proof-of-stake-explained.
- Prashant Gangwal (2019). AI and ML Technologies: What They Mean For Federal Agencies. [online] Simplilearn.com. Available online: https://www.simplilearn.com/what-ai-and-ml-technologies-mean-for-federal-agencies-article.
- Pratt, M.K. (2023). What is blockchain and how does it work? [online] SearchCIO. Available online: https://www.techtarget.com/searchcio/definition/blockchain.
- Ram, B. and Verma, P. Application of blockchain technology in data security. IP Indian Journal of Library Science and Information Technology 2024, 9, 51–55. [Google Scholar] [CrossRef]
- Ravichandran, N. , Tewaraja, T., Rajasegaran, V., Kumar, S. S., Gunasekar, S. K. L., & Sindiramutty, S. R. (2024). Comprehensive Review Analysis and Countermeasures for Cybersecurity Threats: DDoS, Ransomware, and Trojan Horse Attacks. Preprints.org. [CrossRef]
- Review on Blockchain Technology: Architecture, Characteristics, Benefits, Algorithms, Challenges and Applications. Mesopotamian Journal of Cyber Security 2023, 73–85. [CrossRef]
- Sangfor Technologies. (2024). Blockchain Security: Key Concepts, Threats, and Future Trends. Available online: https://www.sangfor.com/glossary/cybersecurity/blockchain-security-key-concepts-threats-and-future-trends.
- Satpal Singh Kushwaha, Amit Kumar Bairwa, Sandeep Chaurasia, Soni, V. and Shankar, V.G. (2022). Security Measures for Blockchain Technology. CRC Press eBooks, pp.79–94. [CrossRef]
- Science Direct (2024). ScienceDirect.com | Science, Health and Medical journals, Full Text Articles and books. [online] Sciencedirect.com. Available online: https://www.sciencedirect.com/.
- SearchStorage. (n.d.). 7 decentralized data storage networks compared. Available online: https://www.techtarget.com/searchstorage/tip/Comparing-4-decentralized-data-storage-offerings.
- Seng, Y. J. , Cen, T. Y., Raslan, M. a. H. B. M., Subramaniam, M. R., Xin, L. Y., Kin, S. J., Long, M. S., & Sindiramutty, S. R. (2024). In-Depth Analysis and Countermeasures for Ransomware Attacks: Case Studies and Recommendations. Preprints.org. [CrossRef]
- Shah, I. A. , Jhanjhi, N. Z., & Laraib, A. (2022). Cybersecurity and blockchain usage in contemporary business. In Advances in information security, privacy, and ethics book series (pp. 49–64). [CrossRef]
- Sharma, R. , Singh, A. , Kavita, N., Jhanjhi, N. Z., Masud, M., Jaha, E. S., & Verma, S. Plant disease diagnosis and image classification using deep learning. Computers, Materials & Continua/Computers, Materials & Continua (Print) 2021, 71, 2125–2140. [Google Scholar] [CrossRef]
- Sharma, S. , Rosmin, P. and Bhagat, A. (2021). Blockchain Technology. Blockchain Applications in IoT Security, pp.140–151. [CrossRef]
- Sheldon, R. (2021). A timeline and history of blockchain technology. [online] WhatIs.com. Available online: https://www.techtarget.com/whatis/feature/A-timeline-and-history-of-blockchain-technology.
- Sheth, H. and Dattani, J. (2019). Overview of Blockchain Technology. Asian Journal For Convergence In Technology (AJCT) ISSN -2350-1146. Available online: http://asianssr.org/index.php/ajct/article/view/728.
- Shoemaker, P. (2024). What Is a Peer-to-Peer (P2P) Network? [online] Identity. Available online: https://www.identity.com/peer-to-peer-network/#What_Are_the_Types_of_Peer-to-Peer_P2P_Networks.
- Simplilearn (2009). Online Certification Training Courses for Professionals | Simplilearn. [online] Simplilearn.com. Available online: https://www.simplilearn.com/.
- Simplilearn.com. (n.d.). What is Ethereum: Understanding Its Features and Applications. Available online: https://www.simplilearn.com/tutorials/blockchain-tutorial/what-is-ethereum.
- Sindiramutty, S. R. , Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Shah, B., & Manchuri, A. R. (2024). Cybersecurity measures for logistics industry. In Advances in information security, privacy, and ethics book series (pp. 1–58). [CrossRef]
- Sindiramutty, S. R. , Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Shah, B., Yun, K. J., Ray, S. K., Jazri, H., & Hussain, M. (2024). Future trends and emerging threats in drone cybersecurity. In Advances in information security, privacy, and ethics book series (pp. 148–195). [CrossRef]
- Sindiramutty, S. R. , Jhanjhi, N. Z., Tan, C. E., Yun, K. J., Manchuri, A. R., Ashraf, H., Murugesan, R. K., Tee, W. J., & Hussain, M. (2024). Data security and privacy concerns in drone operations. In Advances in information security, privacy, and ethics book series (pp. 236–290). [CrossRef]
- Sindiramutty, S. R. , Jhanjhi, N., Tan, C. E., Lau, S. P., Muniandy, L., Gharib, A. H., Ashraf, H., & Murugesan, R. K. (2024). Industry 4.0. In Advances in logistics, operations, and management science book series (pp. 342–405). [CrossRef]
- Sindiramutty, S. R. , Tan, C. E., & Wei, G. W. (2024). Eyes in the sky. In Advances in information security, privacy, and ethics book series (pp. 405–451). [CrossRef]
- Sindiramutty, S. R. , Tan, C. E., Shah, B., Khan, N. A., Gharib, A. H., Manchuri, A. R., Muniandy, L., Ray, S. K., & Jazri, H. (2024). Ethical considerations in drone cybersecurity. In Advances in information security, privacy, and ethics book series (pp. 42–87). [CrossRef]
- Singhal, V. , Jain, S. S., Anand, D., Singh, A., Verma, S., Kavita, N., Rodrigues, J. J. P. C., Jhanjhi, N. Z., Ghosh, U., Jo, O., & Iwendi, C. Artificial Intelligence Enabled Road Vehicle-Train Collision Risk Assessment Framework for Unmanned railway level crossings. IEEE Access 2020, 8, 113790–113806. [Google Scholar] [CrossRef]
- Starknet (2024). Understanding Staking in Blockchain. [online] Starknet.io. Available online: https://www.starknet.io/blog/understanding-staking-in-blockchain/ (accessed on 29 November 2024).
- Tagade, K. (2021). An Introduction to Blockchain Security. [online] www.getastra.com. Available online: https://www.getastra.com/blog/knowledge-base/blockchain-security/.
- Team, C. (2023). The Importance of Blockchain Security - Chainalysis. [online] Chainalysis. Available online: https://www.chainalysis.com/blog/blockchain-security/#The%20future%20of%20blockchain%20security.
- Team, L.C.X. (2024a). Blockchain Security: Transaction Data Safety. [online] LCX. Available online: https://www.lcx.com/blockchain-security-transaction-data-safety/.
- Team, L.C.X. (2024b). What is Decentralization in Blockchain. [online] LCX. Available online: https://www.lcx.com/what-is-decentralization-in-blockchain/.
- Team, M. A. (2024, ). Exploring the types of nodes in blockchain networks. MaskEX Blog. Available online: https://blog.maskex. 14 June.
- Techopedia. (2023). SHA-256. Available online: https://www.techopedia.com/definition/sha-256.
- Tripathi, G. , Ahad, M.A. and Casalino, G. A Comprehensive Review of Blockchain technology: Underlying Principles and Historical Background with Future Challenges. Decision Analytics Journal 2023, 9, 100344. [Google Scholar] [CrossRef]
- Tripathi, V. (2021). How Bitcoin Works | Cryptocurrency Technologies. [online] Trendpickle. Available online: https://trendpickle.com/how-bitcoin-works-cryptocurrency-technology/.
- Uddin, M., S. Memon, M. , Memon, I., Ali, I., Memon, J., Abdelhaq, M. and Alsaqour, R. Hyperledger Fabric Blockchain: Secure and Efficient Solution for Electronic Health Records. Computers, Materials & Continua 2021, 68, 2377–2397. [Google Scholar] [CrossRef]
- Ujjawal, A. (2018). How Does the Blockchain Work? [online] GeeksforGeeks. Available online: https://www.geeksforgeeks.org/how-does-the-blockchain-work/.
- vietnamblockchain.asia. (n.d.). Vietnam Blockchain Corporation. Available online: https://vietnamblockchain.asia/post/5666316/5-basic-components-of-blockchain.
- Waheed, A. , Seegolam, B., Jowaheer, M. F., Sze, C. L. X., Hua, E. T. F., & Sindiramutty, S. R. (2024). Zero-Day Exploits in Cybersecurity: Case Studies and Countermeasure. preprints.org. [CrossRef]
- Wen, B. O. T. , Syahriza, N., Xian, N. C. W., Wei, N. G., Shen, T. Z., Hin, Y. Z., Sindiramutty, S. R., & Nicole, T. Y. F. (2023). Detecting cyber threats with a Graph-Based NIDPS. In Advances in logistics, operations, and management science book series (pp. 36–74). [CrossRef]
- Wissen, D.; (2024). The intersection of Artificial Intelligence (AI) and Blockchain technology represents a transformative frontier with the potential to redefine industries, from finance and healthcare to supply chain and beyond. While both technologies are powerful in their own right—AI for its data-driven intelligen. [online] Linkedin.com. Available online: https://www.linkedin.com/pulse/ai-blockchain-revolutionizing-security-efficiency-decentralization-yyjpf/ (accessed on 29 November 2024).
- www.dock.io. (n.d.). Decentralized Identifiers (DIDs): The Ultimate Beginner’s Guide 2023. Available online: https://www.dock.io/post/decentralized-identifiers.
- www.google.com. (n.d.). Redirect Notice. Available online: https://www.google.com/url?q=https://www.bing.com/ck/a?
- www.techtarget.com. (n.d.). Data security and privacy | Resources and Information from TechTarget. Available online: https://www.techtarget.com/searchsecurity/resources/Data-security-and-privacy.
- www.tripwire.com. (n.d.). Blockchain Security: Understanding vulnerabilities and mitigating risks | Tripwire. Available online: https://www.tripwire.com/state-of-security/blockchain-security-understanding-vulnerabilities-and-mitigating-risks.
- Yaga, D. , Mell, P., Roby, N. and Scarfone, K. Blockchain Technology Overview. National Institute of Standards and Technology. [CrossRef]
- Zeng, Z. , Li, Y., Cao, Y., Zhao, Y., Zhong, J., Sidorov, D. and Zeng, X. Blockchain Technology for Information Security of the Energy Internet: Fundamentals, Features, Strategy and Application. Energies 2020, 13, 881. [Google Scholar] [CrossRef]

Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



