Submitted:
05 January 2025
Posted:
06 January 2025
You are already at the latest version
Abstract
Keywords:
1. Background
2. Discussion on How Security-Related Technology Works
i. Component
a) Predictive Analysis
b) User Authentication
c) Secure Software Development
d) Machine Learning
e) Advance Threat Detection
f) Endpoint Security
g) Vulnerability Management
ii. Process
a) Data Collection and Preprocessing
- Network Traffic: Monitoring data packets for unusual patterns.
- Endpoint Behavior: Gathering information on user activity and system performance.
- Threat Intelligence: Compiling data from known threats, vulnerabilities, and exploits (Tan et al., 2020).
b) Model Training
- Supervised Learning: In supervised learning, models are trained on labelled datasets to predict outcomes based on input features (Nguyen et al., 2018).
- Unsupervised Learning: Unsupervised learning models analyze unlabeled data to identify patterns or anomalies (Kim et al., 2019).
c) Pattern Recognition with Historical Data for Predictive Threat Detection
d) Real-Time Cyber-Attack Detection and Response with Reinforcement Learning
e) Anomaly Detection with Unsupervised Machine Learning
f) Malware Classification Using Supervised Learning and Generative Models
g) Leveraging NLP in Phishing Detection and Email Security
iii. Threats
a) Malware Attack
b) Phishing Attack Detection
c) Denial Of Service (DOS)
d) Intrusion Detection
iv. Example Security-Related Technologies
a) AI-Powered Intrusion Detection and Prevention Systems (IDPS)
- Endpoint Detection and Response (EDR): Focuses on detecting and responding to threats that come into endpoints such as desktops, laptops, and mobile devices. Unlike IDPS, which monitors the entire network, EDR is localized, making it a good candidate for finding threats that target the endpoints only (Sohail, 2024).
- Security Information and Event Management (SIEM): IDPS is proactive, meaning it's always monitoring network traffic in real-time and actively preventing attacks by stopping malicious activity as it happens (Hall, 2024). SIEM, on the other hand, tends to be more focused on log analysis: aggregating and correlating events after they have occurred to help identify threats retrospectively (Kidd, 2023).
- AI-Powered Antivirus: These are traditional antivirus powered up with AI, which detects and mitigates known threats by basing the detection logic on malware signature and behaviour pattern identification. They do not offer network-wide anomaly detection and automated response capabilities of IDPS.
b) Practical Application (Example of Real-Life Usage)
- Unsupervised Learning in Self-Learning AI
- 2.
- Autonomous Response with Antigena
- 3.
- Comprehensive Network Visibility
- 4.
- Early Threat Detection
- 5.
- Reduced Human Intervention
c) Drawbacks of Darktrace
v. False Positives
vi. High Cost
vii. Complexity and Learning Curve
viii. Limited Transparency in AI decisions
ix. Dependence on Data Quality
x. Integration with Existing Security Tools
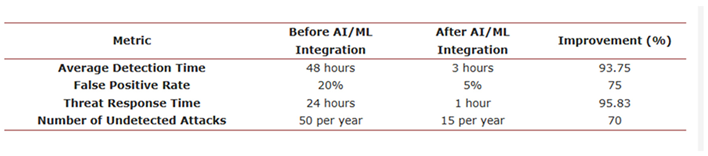
3. Discussion on the Impact
i. Benefits
ii. Limitations
iii. Future Potentials
a) Predictive Analysis for Threat Forecasting
b) AI-Powered Privacy Safeguards and Regulatory Compliance
c) Quantum-Enhanced Threat Detection
d) Automatic and Autonomous Cyber Defense
e) Self-Learning and Adaptive Security Systems
f) AI-Driven Biometric and Behavioural Authentication
4. Discussion on Security Countermeasures
i. Security Countermeasures
ii. Multi-Layered Defence Strategy
iii. Regular Threat Intelligence Updates
iv. Continuous AI Model Training and Tuning
v. Reducing False Positives with Advanced Analytics
vi. Human Oversight and Response Teams
vii. Incident Response Planning and Simulation
viii. Security of Integration with Other Systems
ix. Enhanced Data Encryption and Access Controls
x. Analysis of Effectiveness and Challenges
5. Proposed Countermeasures
- Lattice-Based Cryptography: Algorithms like Learning with Errors (LWE) and Ring-LWE rely on the hardness of lattice problems, such as the Shortest Vector Problem (SVP). (Amirkhanova, Iavich, & Mamyrbayev, 2024; Babbar et al., 2021). These problems remain computationally intractable even for quantum computers, offering a foundation for encryption schemes, digital signatures, and homomorphic encryption. In AI security, lattice-based cryptography could encrypt AI model parameters and datasets, ensuring confidentiality even against quantum attacks.
- Hash-Based Cryptography: Merkle tree-based schemes enable secure digital signatures using collision-resistant hash functions. These signatures are highly efficient and quantum-resistant, making them ideal for verifying model authenticity and integrity in distributed AI systems. (Farooq, Altaf, Iqbal, Bautista Thompson, Ramírez Vargas, de la Torre Díez, & Ashraf, 2023)
- Code-Based Cryptography: Techniques such as McEliece cryptosystems leverage the decoding problem in error-correcting codes. These schemes can be utilized to secure large-scale AI systems that rely on extensive data exchanges, such as federated learning architectures.
- Multivariate Quadratic Cryptography (MQC): By solving multivariate polynomial equations over finite fields, MQC-based cryptography secures lightweight AI applications deployed on resource-constrained devices. (Farooq, Altaf, Iqbal, Bautista Thompson, Ramírez Vargas, de la Torre Díez, & Ashraf, 2023; Alkinani et al., 2021)
- Employ lattice-based encryption to protect AI model parameters during the training and inference phases. This ensures confidentiality even when models traverse untrusted environments. (Sreerangapuri, 2024; Alex et al., 2022)
- Replace existing RSA-based digital signatures in biometric systems with hash-based or lattice-based schemes. This protects user data against quantum-enabled impersonation attacks. (Sreerangapuri, 2024; Alferidah & Jhanjhi, 2020)
- Lattice-based homomorphic encryption enables computations on encrypted data without decryption. AI systems using federated learning can perform collaborative model training while preserving data privacy across clients.
- Use quantum-resistant key exchange mechanisms, such as LWE-based key exchange protocols, to establish secure communication channels between AI modules and external systems.
- Quantum-resistant algorithms typically require larger key sizes and higher computational resources than classical counterparts. For instance, McEliece cryptosystems demand significant storage for public keys, which could strain resource-constrained AI systems.
- Although QRE algorithms are improving, they are still being reviewed and standardized by organizations like NIST. It’s important to ensure they can work smoothly across different AI systems for widespread adoption.
- While QRE secures data against Shor's algorithm, emerging quantum attacks may target its underlying mathematical constructs. Continuous research into cryptographic resilience is essential.
6. Conclusion
References
- Adams, M. Adams, M. (2022). Understanding the Advanced Encryption Standard: Enhancing Your Data Security. [online] Businesstechweekly.com. Available at: https://www.businesstechweekly.com/cybersecurity/data-security/advanced-encryption-standard/.
- Adebola Folorunso, Temitope Adewumi, Adeola Adewa, Roy Okonkwo and Tayo Nathaniel Olawumi (2024). Impact of AI on cybersecurity and security compliance. Global Journal of Engineering and Technology Advances, 21(1), pp.167–184. [CrossRef]
- Akbanov, M., Vassilakis, V.G. and Logothetis, M.D. (2019). WannaCry Ransomware: Analysis of Infection, Persistence, Recovery Prevention and Propagation Mechanisms. Journal of Telecommunications and Information Technology, [online] 1(1), pp.113–124. [CrossRef]
- Alex, S. A., Jhanjhi, N., Humayun, M., Ibrahim, A. O., & Abulfaraj, A. W. (2022). Deep LSTM Model for Diabetes Prediction with Class Balancing by SMOTE. Electronics, 11(17), 2737. [CrossRef]
- Alferidah, D. K., & Jhanjhi, N. (2020). Cybersecurity Impact over Bigdata and IoT Growth. 2020 International Conference on Computational Intelligence (ICCI). [CrossRef]
- Alkinani, M. H., Almazroi, A. A., Jhanjhi, N., & Khan, N. A. (2021). 5G and IoT Based Reporting and Accident Detection (RAD) System to Deliver First Aid Box Using Unmanned Aerial Vehicle. Sensors, 21(20), 6905. [CrossRef]
- Allen, J. (2023). The Human and AI Partnership: Collaborating for Enhanced Cybersecurity. [online] Available at: https://www.isaca.org/resources/news-and-trends/industry-news/2023/the-human-and-ai-partnership-collaborating-for-enhanced-cybersecurity.
- Alvero, K. M. (2021). What Role do Humans Play in Ensuring Cybersecurity? [online] Available at: https://www.isaca.org/resources/isaca-journal/issues/2021/volume-5/what-role-do-humans-play-in-ensuring-cybersecurity.
- Ananna, F. F., Nowreen, R., Jahwari, S. S. R. A., Costa, E. A., Angeline, L., & Sindiramutty, S. R. (2023). Analysing Influential factors in student academic achievement: Prediction modelling and insight. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence, 2(1). [CrossRef]
- Aryaman Pattnayak (2023). AZoAi. [online] AZoAi. Available at: https://www.azoai.com/article/Biometric-AI-Advantages-and-Challenges.aspx?form=MG0AV3.
- Azam, H., Dulloo, M. I., Majeed, M. H., Wan, J. P. H., Xin, L. T., & Sindiramutty, S. R. (2023). Cybercrime Unmasked: Investigating cases and digital evidence. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence, 2(1). [CrossRef]
- Azam, H., Dulloo, M. I., Majeed, M. H., Wan, J. P. H., Xin, L. T., Tajwar, M. A., & Sindiramutty, S. R. (2023). Defending the digital Frontier: IDPS and the battle against Cyber threat. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence, 2(1). [CrossRef]
- Azam, H., Tajwar, M. A., Mayhialagan, S., Davis, A. J., Yik, C. J., Ali, D., & Sindiramutty, S. R. (2023). Innovations in Security: A study of cloud Computing and IoT. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence, 2(1). [CrossRef]
- Azam, H., Tan, M., Pin, L. T., Syahmi, M. A., Qian, A. L. W., Jingyan, H., Uddin, M. F., & Sindiramutty, S. R. (2023). Wireless Technology Security and Privacy: A Comprehensive Study. Preprints.org. [CrossRef]
- Babbar, H., Rani, S., Masud, M., Verma, S., Anand, D., & Jhanjhi, N. (2021). Load balancing algorithm for migrating switches in software-defined vehicular networks. Computers, Materials & Continua/Computers, Materials & Continua (Print), 67(1), 1301–1316. [CrossRef]
- Basit, A., Zafar, M., Liu, X., Javed, A.R., Jalil, Z. and Kifayat, K. (2020). A comprehensive survey of AI-enabled phishing attacks detection techniques. Telecommunication Systems, [online] 76(1). [CrossRef]
- Bhudata, T. (2024) Integration Security: Safeguarding your data in connected systems. https://exalate.com/blog/integration-security/.
- Bowman, K. and Tunks, J. (2024). Understanding Data Access Control: A Comprehensive Guide. [online] Available at: https://pathlock.com/learn/data-access-control/.
- Brohi, S. N., Jhanjhi, N., Brohi, N. N., & Brohi, M. N. (2020). Key Applications of State-of-the-Art Technologies to Mitigate and Eliminate COVID-19.pdf. TECHRxiv. [CrossRef]
- Centre for Emerging Technology and Security. (2024). Autonomous Cyber Defence Phase II. [online] Available at: https://cetas.turing.ac.uk/publications/autonomous-cyber-defence-autonomous-agents.
- Chesti, I. A., Humayun, M., Sama, N. U., & Jhanjhi, N. (2020). Evolution, Mitigation, and Prevention of Ransomware. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- CISA (2021). Understanding Denial-of-Service Attacks. [online] Cybersecurity and Infrastructure Security Agency. Available at: https://www.cisa.gov/news-events/news/understanding-denial-service-attacks.
- CISA (2024). Incident Response Plan (IRP) Basics | CISA. [online] www.cisa.gov. Available at: https://www.cisa.gov/resources-tools/resources/incident-response-plan-irp-basics.
- CISCO (2024). What Is Malware? - Definition and Examples. [online] Cisco. Available at: https://www.cisco.com/site/us/en/learn/topics/security/what-is-malware.html.
- CloudFlare (2023). What is a Phishing attack? Cloudflare. [online] Available at: https://www.cloudflare.com/learning/access-management/phishing-attack/.
- Cost of a data breach 2024 | IBM (no date). https://www.ibm.com/reports/data-breach.
- Crouse, M. (2023). IBM Report: Average Cost of a Data Breach Rises to $4.45 Million. [online] TechRepublic. Available at: https://www.techrepublic.com/article/ibm-data-breach-cost/.
- Cybersecurity and AI: The challenges and opportunities (2024). https://www.weforum.org/agenda/2023/06/cybersecurity-and-ai-challenges-opportunities/.
- Dana Sairangazhykyzy Amirkhanova, Maksim Iavich and Orken Mamyrbayev (2024). Lattice-Based Post-Quantum Public Key Encryption Scheme Using ElGamal’s Principles. Cryptography, 8(3), pp.31–31. [CrossRef]
- Dansimp (2023). Incident response planning. [online] learn.microsoft.com. Available at: https://learn.microsoft.com/en-us/security/operations/incident-response-planning.
- Darktrace (2019). Pros and Cons of Darktrace 2024 | PeerSpot. [online] Peerspot.com. Available at: https://www.peerspot.com/products/darktrace-pros-and-cons.
- Darktrace Enterprise PRODUCT OVERVIEW Enterprise Immune System. (n.d.). Available at: https://apexassembly.com/wp-content/uploads/2018/07/Darktrace-Enterprise_-Product-Overview.pdf.
- Darktrace.com. (2024). Darktrace. [online] Available at: https://darktrace.com/cyber-ai-glossary/.
- darktrace.com. (n.d.). The State of AI in Cybersecurity: How AI will impact the cyber threat landscape in 2024 | Darktrace Blog. [online] Available at: https://darktrace.com/blog/the-state-of-ai-in-cybersecurity-how-ai-will-impact-the-cyber-threat-landscape-in-2024.
- darktrace.com. (n.d.). The State of AI in Cybersecurity: The Impact of AI on Cybersecurity Solutions | Darktrace Blog. [online] Available at: https://darktrace.com/blog/the-state-of-ai-in-cybersecurity-the-impact-of-ai-on-cybersecurity-solutions.
- darktrace.com. (n.d.). The State of AI in Cybersecurity: The Impact of AI on Cybersecurity Solutions | Darktrace Blog. [online] Available at: https://darktrace.com/blog/the-state-of-ai-in-cybersecurity-the-impact-of-ai-on-cybersecurity-solutions.
- darktrace.com. (n.d.). Darktrace | Cyber security that learns you. [online] Available at: https://www.darktrace.com.
- darktrace.com. (n.d.). Darktrace Launches Enterprise Immune System Version 4 • Darktrace Newsroom. [online] Available at: https://darktrace.com/news/darktrace-launches-enterprise-immune-system-version-4.
- Djenna, A., Bouridane, A., Rubab, S. and Marou, I.M. (2023). Artificial Intelligence-Based Malware Detection, Analysis, and Mitigation. Symmetry, 15(3), p.677. [CrossRef]
- Dogra, V., Singh, A., Verma, S., Kavita, N., Jhanjhi, N. Z., & Talib, M. N. (2021). Analyzing DistilBERT for Sentiment Classification of Banking Financial News. In Lecture notes in networks and systems (pp. 501–510). [CrossRef]
- E. Bertino and N. Islam, "Botnets and Internet of Things Security," in Computer, vol. 50, no. 2, pp. 76-79, Feb. 2017. [CrossRef]
- Farooq, S., Altaf, A., Iqbal, F., Ernesto Bautista Thompson, Vargas, D., Isabel and Ashraf, I. (2023). Resilience Optimization of Post-Quantum Cryptography Key Encapsulation Algorithms. Sensors, 23(12), pp.5379–5379. [CrossRef]
- Fatima-Tuz-Zahra, N., Jhanjhi, N., Brohi, S. N., Malik, N. A., & Humayun, M. (2020). Proposing a Hybrid RPL Protocol for Rank and Wormhole Attack Mitigation using Machine Learning. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- Frankenfield, J. Frankenfield, J. (2020). Denial-of-Service (DoS) Attack Definition. [online] Investopedia. Available at: https://www.investopedia.com/terms/d/denial-service-attack-dos.asp.
- Fruhlinger, J. (2022) Defense in depth explained: Layering tools and processes for better security. https://www.csoonline.com/article/573221/defense-in-depth-explained-layering-tools-and-processes-for-better-security.html.
- General Data Protection Regulation (GDPR). (n.d.). Fines / Penalties. [online] Available at: https://gdpr-info.eu/issues/fines-penalties.
- Gonsalves, B. (2023) The Power of Cybersecurity Product Technology Integrations: Strengthening our digital defenses. https://blogs.cisco.com/security/the-power-of-cybersecurity-product-technology-integrations-strengthening-our-digital-defenses.
- Gopi, R., Sathiyamoorthi, V., Selvakumar, S., Manikandan, R., Chatterjee, P., Jhanjhi, N. Z., & Luhach, A. K. (2021). Enhanced method of ANN based model for detection of DDoS attacks on multimedia internet of things. Multimedia Tools and Applications, 81(19), 26739–26757. [CrossRef]
- Gouda, W., Almurafeh, M., Humayun, M., & Jhanjhi, N. Z. (2022). Detection of COVID-19 based on chest x-rays using deep learning. Healthcare, 10(2), 343. [CrossRef]
- Greengard, S. (2023). Pegasus (spyware) | Description, Origins, Spying, & Controversies | Britannica. [online] www.britannica.com. Available at: https://www.britannica.com/topic/Pegasus-spyware.
- H, S. (2024). The Role of Intrusion Detection and Prevention Systems in Cybersecurity - More Cybersecurity. [online] More Cybersecurity. Available at: https://morecybersecurity.com/the-role-of-intrusion-detection-and-prevention-systems-in-cybersecurity/?form=MG0AV3.
- Humayun, M., Sujatha, R., Almuayqil, S. N., & Jhanjhi, N. Z. (2022). A Transfer Learning Approach with a Convolutional Neural Network for the Classification of Lung Carcinoma. Healthcare, 10(6), 1058. [CrossRef]
- Hussain, K., Rahmatyar, A. R., Riskhan, B., Sheikh, M. a. U., & Sindiramutty, S. R. (2024). Threats and Vulnerabilities of Wireless Networks in the Internet of Things (IoT). 2024 IEEE 1st Karachi Section Humanitarian Technology Conference (KHI-HTC), 2, 1–8. [CrossRef]
- IBM (2019). uk-en_homepage. [online] Ibm.com. Available at: https://www.ibm.com.
- IBM (2023). What is an intrusion detection system (IDS)? [online] www.ibm.com. Available at: https://www.ibm.com/topics/intrusion-detection-system.
- BM (2023). What is an intrusion prevention system (IPS)? | IBM. [online] www.ibm.com. Available at: https://www.ibm.com/topics/intrusion-prevention-system.
- IBM. (n.d.). The quantum-safe clock is ticking. [online] Available at: https://www.ibm.com/thought-leadership/institute-business-value/en-us/report/quantum-safe.
- Insights2Techinfo. (2024). AI-Based Intrusion Detection Systems. [online] Available at: https://insights2techinfo.com/ai-based-intrusion-detection-systems/.
- Jhanjhi, N., Humayun, M., & Almuayqil, S. N. (2021). Cyber security and privacy issues in industrial internet of things. Computer Systems Science and Engineering, 37(3), 361–380. [CrossRef]
- Jun, A. Y. M., Jinu, B. A., Seng, L. K., Maharaiq, M. H. F. B. Z., Khongsuwan, W., Junn, B. T. K., Hao, A. a. W., & Sindiramutty, S. R. (2024). Exploring the Impact of Crypto-Ransomware on Critical Industries: Case Studies and Solutions. Preprints.org. [CrossRef]
- Kaiyue (2024). How Does AI Help Detect and Prevent DDoS Attacks in Modern Networks - Kaiyue October 23, 2024 Accelerate, Secure & Compute Your Global Business Streaming Content Data File Downloads Take your edge, to the next level. [online] Edgenext - Accelerate, Secure & Compute Your Global Business Streaming Content Data File Downloads Take your edge, to the next level. Available at: https://www.edgenext.com/how-does-ai-help-detect-and-prevent-ddos-attacks-in-modern-networks/.
- Katiyar, D.N., Tripathi, M.S., Kumar, M.P., Verma, M.S., Sahu, D.A.K. and Saxena, D.S. (2024). AI and Cyber-Security: Enhancing threat detection and response with machine learning. Educational Administration: Theory and Practice, [online] 30(4), pp.6273–6282. [CrossRef]
- Kaur, H. Kaur, H. and Tiwari, R. (2021). Endpoint detection and response using machine learning. Journal of Physics: Conference Series, 2062(1), p.012013. [CrossRef]
- Kim, A. (2024) Enhancing your cyber defense: comparing simulations and tabletop exercises. https://www.sans.org/blog/enhancing-your-cyber-defense-comparing-simulations-and-tabletop-exercises/.
- Kumar, M. S., Vimal, S., Jhanjhi, N., Dhanabalan, S. S., & Alhumyani, H. A. (2021). Blockchain based peer to peer communication in autonomous drone operation. Energy Reports, 7, 7925–7939. [CrossRef]
- Legrand, J. (2022). Humans and cybersecurity— the weakest link or the best defense? [online] ISACA. Available at: https://www.isaca.org/resources/isaca-journal/issues/2022/volume-1/humans-and-cybersecurity-the-weakest-link-or-the-best-defense.
- Li, W., Jin, J. and Lee, J.-H. (2019). Analysis of Botnet Domain Names for IoT Cybersecurity. IEEE Access, [online] 7, pp.94658–94665. [CrossRef]
- Lim, M., Abdullah, A., Jhanjhi, N., Khan, M. K., & Supramaniam, M. (2019). Link Prediction in Time-Evolving Criminal Network with deep Reinforcement learning technique. IEEE Access, 7, 184797–184807. [CrossRef]
- Luffy, M.D. (2024). AI technology: Opportunities and challenges in DDoS mitigation. [online] Opportunities and challenges of applying AI to DDoS attack mitigation. Available at: https://www.vnetwork.vn/en-US/news/ung-dung-ai-trong-chong-tan-cong-ddos/.
- Manchuri, A., Kakera, A., Saleh, A., & Raja, S. (2024). pplication of Supervised Machine Learning Models in Biodiesel Production Research - A Short Review. Borneo Journal of Sciences and Technology. [CrossRef]
- Masoumeh Abolfathi, Zohreh Raghebi, Haadi Jafarian and Farnoush Banaei-Kashani (2021). A Scalable Role Mining Approach for Large Organizations. Proceedings of the 2021 ACM Workshop on Security and Privacy Analytics. [CrossRef]
- Maués, R. (2024). Artificial Intelligence on Secure Software Development. [online] Conviso AppSec. Available at: https://blog.convisoappsec.com/en/artificial-intelligence-on-secure-software-development/.
- MicrosoftGuyJFlo (2024). What is Microsoft Entra ID Protection? - Microsoft Entra ID Protection. [online] learn.microsoft.com. Available at: https://learn.microsoft.com/en-us/entra/id-protection/overview-identity-protection.
- MixMode. (2022). What is self-learning AI, and how is it applied to cybersecurity? [online] Available at: https://mixmode.ai/what-is/self-learning-ai/.
- Mounica S (2024). Big Data For Fraud Detection and Prevention. [online] hyperverge.co. Available at: https://hyperverge.co/blog/big-data-fraud-detection/.
- Nayyar, A., Gadhavi, L., & Zaman, N. (2021). Machine learning in healthcare: review, opportunities and challenges. In Elsevier eBooks (pp. 23–45). [CrossRef]
- Olubudo, P. (2024). Advanced Threat Detection Techniques Using Machine Learning: Exploring the Use of AI and ML in Identifying... [online] ResearchGate. Available at: https://www.researchgate.net/publication/380743475_Advanced_Threat_Detection_Techniques_Using_Machine_Learning_Exploring_the_Use_of_AI_and_ML_in_Identifying_and_Mitigating_Advanced_Persistent_Threats_APTs.
- Palo Alto Networks (n.d.). What are the Risks and Benefits of Artificial Intelligence (AI) in Cybersecurity? [online] Palo Alto Networks. Available at: https://www.paloaltonetworks.com/cyberpedia/ai-risks-and-benefits-in-cybersecurity.
- Palo Alto Networks (n.d.). What is the Role of AI in Threat Detection? [online] Palo Alto Networks. Available at: https://www.paloaltonetworks.com/cyberpedia/ai-in-threat-detection.
- Palo Alto Networks (n.d.). What is the Role of AI in Threat Detection? [online] Palo Alto Networks. Available at: https://www.paloaltonetworks.com/cyberpedia/ai-in-threat-detection.
- Palo Alto Networks. (n.d.). What Is Precision AITM? [online] Available at: https://www.paloaltonetworks.com/cyberpedia/what-is-precision-ai.
- PgCert, A.R. (2024). 1. Introduction In an increasingly digital world, the need for robust, reliable, and user-friendly authentication and security measures has never been more critical. [online] Linkedin.com. Available at: https://www.linkedin.com/pulse/ai-powered-behavioral-biometrics-andre-ripla-pgcert-5x5te/.
- Pluralsight.com. (2023). The impact of AI: Cybersecurity challenges and opportunities. [online] Available at: https://www.pluralsight.com/resources/blog/cybersecurity/ai-impact-cybersecurity.
- R. Sommer and V. Paxson, "Outside the Closed World: On Using Machine Learning for Network Intrusion Detection," 2010 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 2010, pp. 305-316. [CrossRef]
- Raimundo, R. and Rosário, A. (2021). The Impact of Artificial Intelligence on Data System Security: A Literature Review. Sensors, [online] 21(21), p.7029. [CrossRef]
- Ravichandran, N., Tewaraja, T., Rajasegaran, V., Kumar, S. S., Gunasekar, S. K. L., & Sindiramutty, S. R. (2024). Comprehensive Review Analysis and Countermeasures for Cybersecurity Threats: DDoS, Ransomware, and Trojan Horse Attacks. Preprints.org. [CrossRef]
- Reasonlabs.com. (2023). What are Enhanced security measures? Comprehensive Cybersecurity Strategies. [online] Available at: https://cyberpedia.reasonlabs.com/EN/enhanced%20security%20measures.html.
- Research Gate (2021). 130+ million publications organized by topic on ResearchGate. [online] ResearchGate. Available at: https://www.researchgate.net/publication.
- ResearchGate. (2019). Vinayakumar RAVI | Assistant Research Professor | Assistant Research Professor | Prince Mohammad University, Khobar | Center for Artificial Intelligence | Research profile. [online] Available at: https://www.researchgate.net/profile/Vinayakumar-Ravi.
- ResearchGate. (2020). Joao Paulo JAVIDI DA COSTA | Professor | Dr.-Ing. | Hochschule Hamm-Lippstadt, Hamm | Department 2 | Research profile. [online] Available at: https://www.researchgate.net/profile/Joao-Paulo-Javidi-Da-Costa.
- ResearchGate. (2020). Toan NGUYEN | Ph.D. | Research profile. [online] Available at: https://www.researchgate.net/profile/Toan-Nguyen-26.
- ResearchGate. (2024). Bandar ALOTAIBI | Professor (Associate) | University of Tabuk, Tabuk | Department of Computer Science | Research profile. [online] Available at: https://www.researchgate.net/profile/Bandar-Alotaibi-4.
- Richberg, J. (2024). The Power and Limitations of AI in Cybersecurity | CISO Collective. [online] Fortinet Blog. Available at: https://www.fortinet.com/blog/ciso-collective/power-and-limitations-of-ai-in-cybersecurity.
- Roshanaei, M., Khan, M.R. and Sylvester, N.N. (2024). Enhancing Cybersecurity through AI and ML: Strategies, Challenges, and Future Directions. Journal of Information Security, [online] 15(3), pp.320–339. [CrossRef]
- Salem, A.H. et al. (2024) 'Advancing cybersecurity: a comprehensive review of AI-driven detection techniques,' Journal of Big Data, 11(1). [CrossRef]
- Salem, A.H., Azzam, S.M., Emam, O.E. and Abohany, A.A. (2024). Advancing cybersecurity: a comprehensive review of AI-driven detection techniques. Journal Of Big Data, [online] 11(1). [CrossRef]
- Salem, A.H., Azzam, S.M., Emam, O.E. and Abohany, A.A. (2024). Advancing cybersecurity: a comprehensive review of AI-driven detection techniques. Journal Of Big Data, [online] 11(1). [CrossRef]
- Sanchez, P. (2023). Denial Of Service (DoS) Attacks: A Complete Guide. [online] CovertSwarm. Available at: https://www.covertswarm.com/post/denial-of-service-attack.
- Santos, O. (2023) Securing AI: navigating the complex landscape of models, Fine-Tuning, and RAG. https://blogs.cisco.com/security/securing-ai-navigating-the-complex-landscape-of-models-fine-tuning-and-rag.
- Seng, Y. J., Cen, T. Y., Raslan, M. a. H. B. M., Subramaniam, M. R., Xin, L. Y., Kin, S. J., Long, M. S., & Sindiramutty, S. R. (2024). In-Depth Analysis and Countermeasures for Ransomware Attacks: Case Studies and Recommendations. Preprints.org. [CrossRef]
- Serkan Salturk and Kahraman, N. (2024). Deep learning-powered multimodal biometric authentication: integrating dynamic signatures and facial data for enhanced online security. Neural Computing and Applications, 36(19), pp.11311–11322. [CrossRef]
- Shah, I. A., Jhanjhi, N. Z., & Laraib, A. (2022). Cybersecurity and blockchain usage in contemporary business. In Advances in information security, privacy, and ethics book series (pp. 49–64). [CrossRef]
- Sharma, R., Singh, A., Kavita, N., Jhanjhi, N. Z., Masud, M., Jaha, E. S., & Verma, S. (2021). Plant disease diagnosis and image classification using deep learning. Computers, Materials & Continua/Computers, Materials & Continua (Print), 71(2), 2125–2140. [CrossRef]
- Sharma, V., Shah, D., Sharma, S. and Gautam, S. (2024). Artificial Intelligence based Intrusion Detection System – A Detailed Survey. ITM Web of Conferences, 65, p.04002. [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Shah, B., & Manchuri, A. R. (2024). Cybersecurity measures for logistics industry. In Advances in information security, privacy, and ethics book series (pp. 1–58). [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Shah, B., Yun, K. J., Ray, S. K., Jazri, H., & Hussain, M. (2024). Future trends and emerging threats in drone cybersecurity. In Advances in information security, privacy, and ethics book series (pp. 148–195). [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Yun, K. J., Manchuri, A. R., Ashraf, H., Murugesan, R. K., Tee, W. J., & Hussain, M. (2024). Data security and privacy concerns in drone operations. In Advances in information security, privacy, and ethics book series (pp. 236–290). [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N., Tan, C. E., Lau, S. P., Muniandy, L., Gharib, A. H., Ashraf, H., & Murugesan, R. K. (2024). Industry 4.0. In Advances in logistics, operations, and management science book series (pp. 342–405). [CrossRef]
- Sindiramutty, S. R., Tan, C. E., & Wei, G. W. (2024). Eyes in the sky. In Advances in information security, privacy, and ethics book series (pp. 405–451). [CrossRef]
- Sindiramutty, S. R., Tan, C. E., Shah, B., Khan, N. A., Gharib, A. H., Manchuri, A. R., Muniandy, L., Ray, S. K., & Jazri, H. (2024). Ethical considerations in drone cybersecurity. In Advances in information security, privacy, and ethics book series (pp. 42–87). [CrossRef]
- Singhal, V., Jain, S. S., Anand, D., Singh, A., Verma, S., Kavita, N., Rodrigues, J. J. P. C., Jhanjhi, N. Z., Ghosh, U., Jo, O., & Iwendi, C. (2020). Artificial Intelligence Enabled Road Vehicle-Train Collision Risk Assessment Framework for Unmanned railway level crossings. IEEE Access, 8, 113790–113806. [CrossRef]
- Splunk. (2023). SIEM: Security Information & Event Management Explained | Splunk. [online] Available at: https://www.splunk.com/en_us/blog/learn/siem-security-information-event-management.
- Sreerangapuri, A. (2024). Post-Quantum Cryptography for AI-Driven Cloud Security Solutions. IJFMR240529032, [online] 6(5). Available at: https://www.ijfmr.com/papers/2024/5/29032.pdf.
- Stanham, L. (2023). AI-Powered Behavioral Analysis in Cybersecurity | CrowdStrike. [online] Available at: https://www.crowdstrike.com/en-us/cybersecurity-101/artificial-intelligence/ai-powered-behavioral-analysis/.
- T. M. Fernández-Caramés, "From Pre-Quantum to Post-Quantum IoT Security: A Survey on Quantum-Resistant Cryptosystems for the Internet of Things," in IEEE Internet of Things Journal, vol. 7, no. 7, pp. 6457-6480, July 2020. [CrossRef]
- Technology and Operations Management. (2018). Darktrace: Can Artificial Intelligence lead the fight against Cyber Crime? - Technology and Operations Management. [online] Available at: https://d3.harvard.edu/platform-rctom/submission/darktrace-can-artificial-intelligence-lead-the-fight-against-cyber-crime/.
- Thesciencebrigade.com. (2024). View of The Impact of AI on Cybersecurity: Emerging Threats and Solutions. [online] Available at: https://thesciencebrigade.com/jst/article/view/232/226.
- TLP:CLEAR TLP:CLEAR Joint Cybersecurity Information Deploying AI Systems Securely Best Practices for Deploying Secure and Resilient AI Systems. (n.d.). Available at: https://media.defense.gov/2024/Apr/15/2003439257/-1/-1/0/CSI-DEPLOYING-AI-SYSTEMS-SECURELY.PDF.
- Traill, R. (2024). Get The Drop On Phishing Attacks Abusing Dropbox. [online] Darktrace.com. Available at: https://darktrace.com/blog/legitimate-services-malicious-intentions-getting-the-drop-on-phishing-attacks-abusing-dropbox.
- Vinod, D. and Ashwin Adepu (2024). Leveraging Artificial Intelligence for Predictive Cyber Threat Intelligence. International Journal of Creative Research In Computer Technology and Design, [online] 6(6), pp.1–19. Available at: https://jrctd.in/index.php/IJRCTD/article/view/64.
- Waheed, A., Seegolam, B., Jowaheer, M. F., Sze, C. L. X., Hua, E. T. F., & Sindiramutty, S. R. (2024). Zero-Day Exploits in Cybersecurity: Case Studies and Countermeasure. preprints.org. [CrossRef]
- Wan, S., Meta Platforms, Inc., Saxe, J., Meta Platforms, Inc., Gomes, C., Meta Platforms, Inc., Chennabasappa, S., Meta Platforms, Inc., Rath, A., The University of Texas at Dallas, Sun, K., George Mason University, Wang, X., & The University of Texas at Dallas. (2024). Bridging the Gap: A Study of AI-based Vulnerability Management between Industry and Academia [Journal-article]. Bridging the Gap: A Study of AI-based Vulnerability Management Between Industry and Academia.
- Wen, B. O. T., Syahriza, N., Xian, N. C. W., Wei, N. G., Shen, T. Z., Hin, Y. Z., Sindiramutty, S. R., & Nicole, T. Y. F. (2023). Detecting cyber threats with a Graph-Based NIDPS. In Advances in logistics, operations, and management science book series (pp. 36–74). [CrossRef]
- What is Cyber Threat Intelligence? (2024). https://www.sentinelone.com/cybersecurity-101/threat-intelligence/cyber-threat-intelligence/.
- What is Multi-layered security? - Comprehensive Cybersecurity (no date). https://cyberpedia.reasonlabs.com/EN/multi-layered%20security.html.
- Wlosinski, L. (2022). Cybersecurity Incident Response Exercise Guidance. [online] ISACA. Available at: https://www.isaca.org/resources/isaca-journal/issues/2022/volume-1/cybersecurity-incident-response-exercise-guidance.
- Wolf Eye Shell. (2023). Regular Software Updates and Patch Management In Cyber Security - Wolf Eye Shell. [online] Available at: https://wolfeyeshell.com/regular-software-updates-and-patch-management-in-cyber-security/.
- World Economic Forum (2024). Global Cybersecurity Outlook 2024. [online] World Economic Forum. Available at: https://www3.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2024.pdf.
- www.biia.com. (n.d.). Harnessing Predictive Analytics In Cybersecurity | BIIA.com | Business Information Industry Association. [online] Available at: https://www.biia.com/harnessing-predictive-analytics-in-cybersecurity/.
- www.future-processing.com. (2023). Artificial intelligence usage in multi-factor authentication | Blog - Future Processing. [online] Available at: https://www.future-processing.com/blog/artificial-intelligence-usage-in-multi-factor-authentication/.
- www.linkedin.com. (n.d.). Protecting Your Castle: Understanding IDS, IPS, and EDR. [online] Available at: https://www.linkedin.com/pulse/protecting-your-castle-understanding-ids-ips-edr-sohail-%D1%85%D0%B0%D0%BA%D0%B5%D1%80--ifhtf/.
- www.screeb.app. (n.d.). Understanding User Behavior Analytics (UBA) and Its Applications for Improved User Experience. [online] Available at: https://screeb.app/blog/user-behavior-analytics-definition-methods-and-use-cases.
| Strengths | Weaknesses |
| Self-learning AI that adapts over time. | False positives can overwhelm security teams. |
| Autonomous threat response with Antigena. | High costs may be prohibitive for smaller businesses. |
| Comprehensive network-wide visibility. | Complexity and learning curves for users. |
| Early detection of emerging threats. | Limited transparency in AI decision-making. |
| Reduces human intervention needs. | Dependence on data quality for accuracy. |
 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




