Submitted:
24 December 2024
Posted:
26 December 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
- A novel, lightweight dual attestation mechanism that validates the integrity of both the device and the ML model, facilitating trust verification by a remote entity.
- Propose a new ML attestation token format based on EAT, containing claims that attest to both general ML use cases and sensitive ML parameters, such as architecture and weights.
2. Related Work
3. Background
3.1. Platform Security Architecture
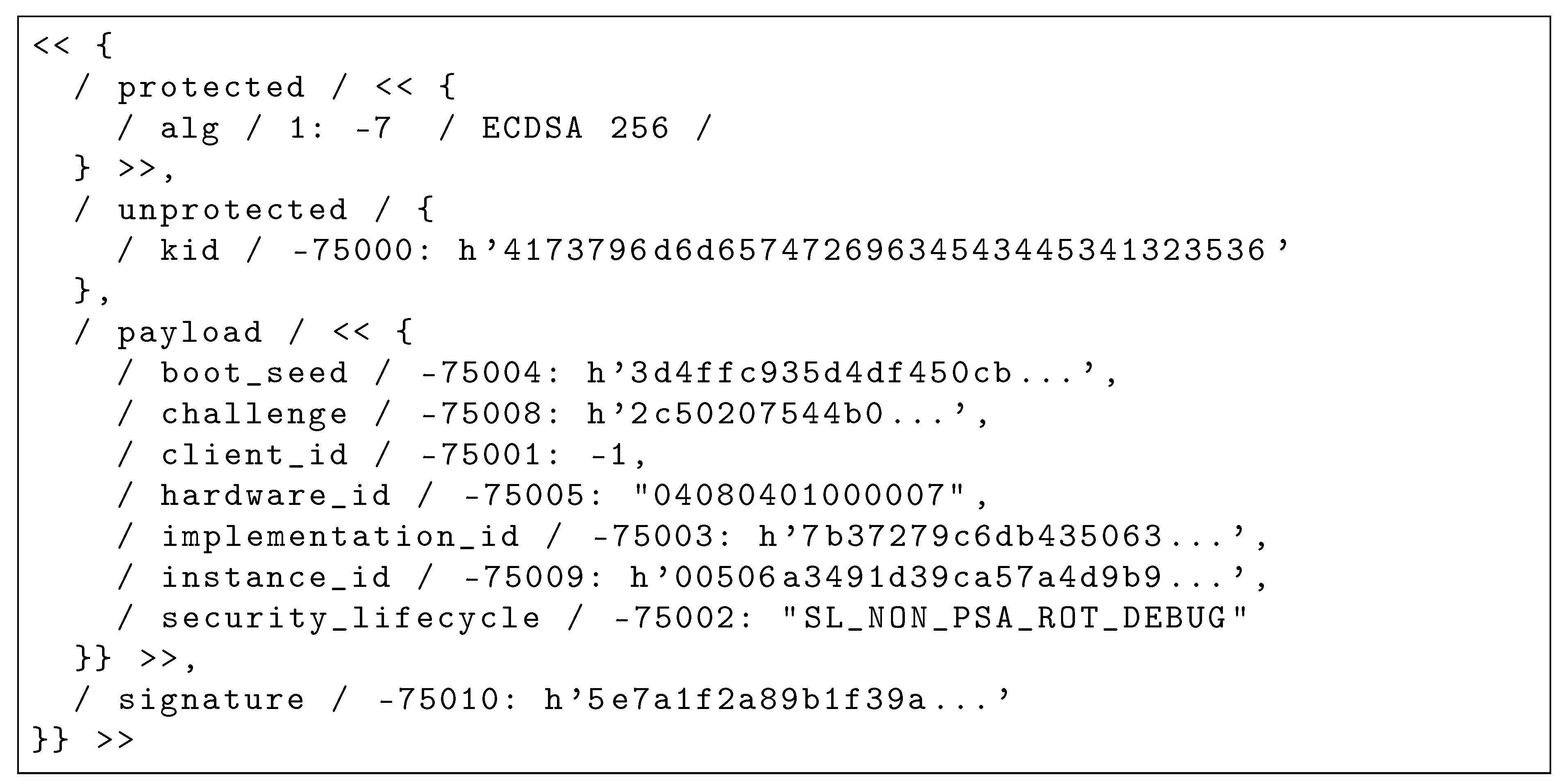
3.2. Attestation tokens
3.3. EAT Token Structure and Encoding
- Standardized claims, where there is widespread agreement on how the information should be structured
- Claims that require standardization to ensure interoperability
- Claims that can be defined by individual parties according to their specific needs
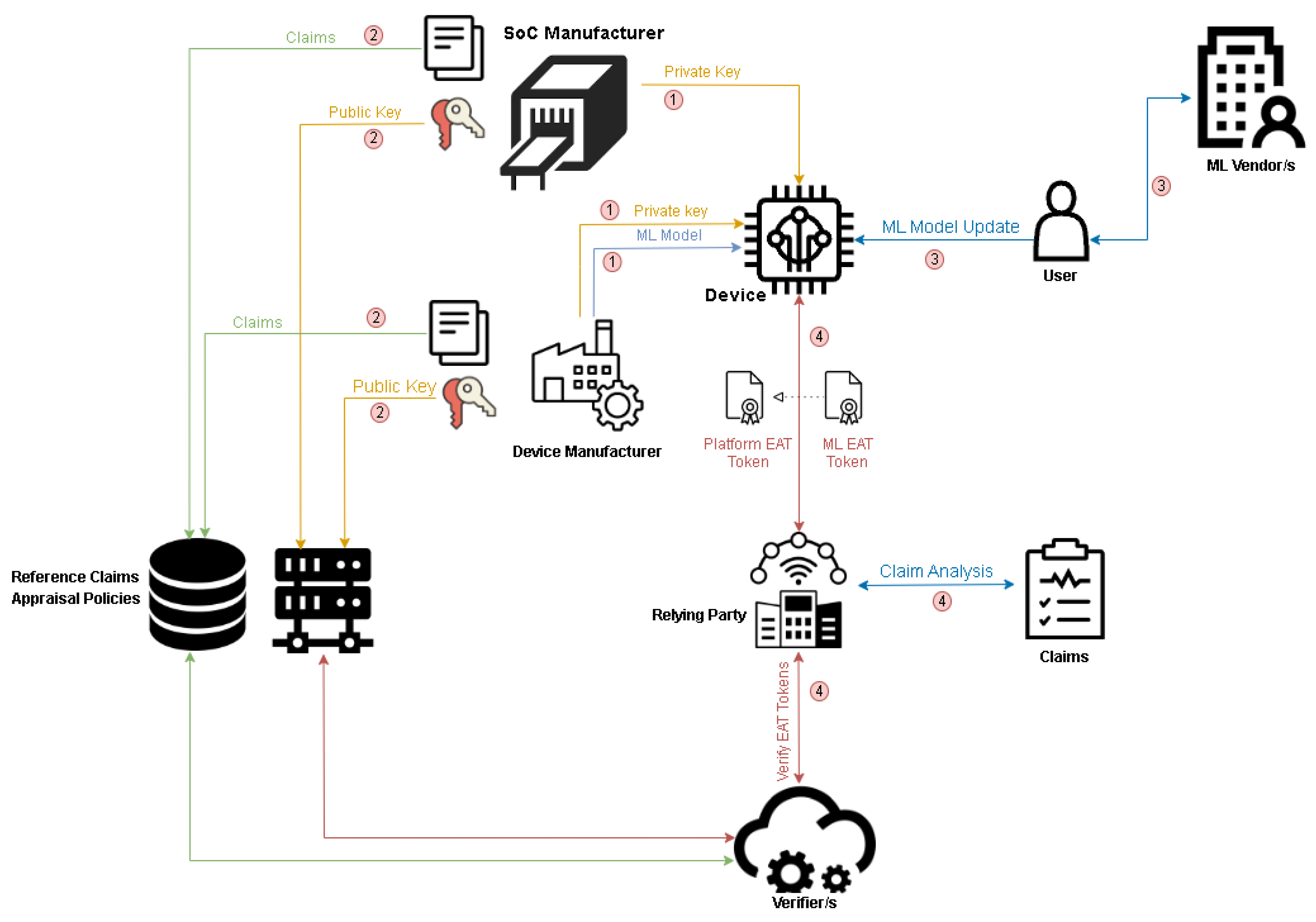
4. Proposed ML Attestation Method and Workflow
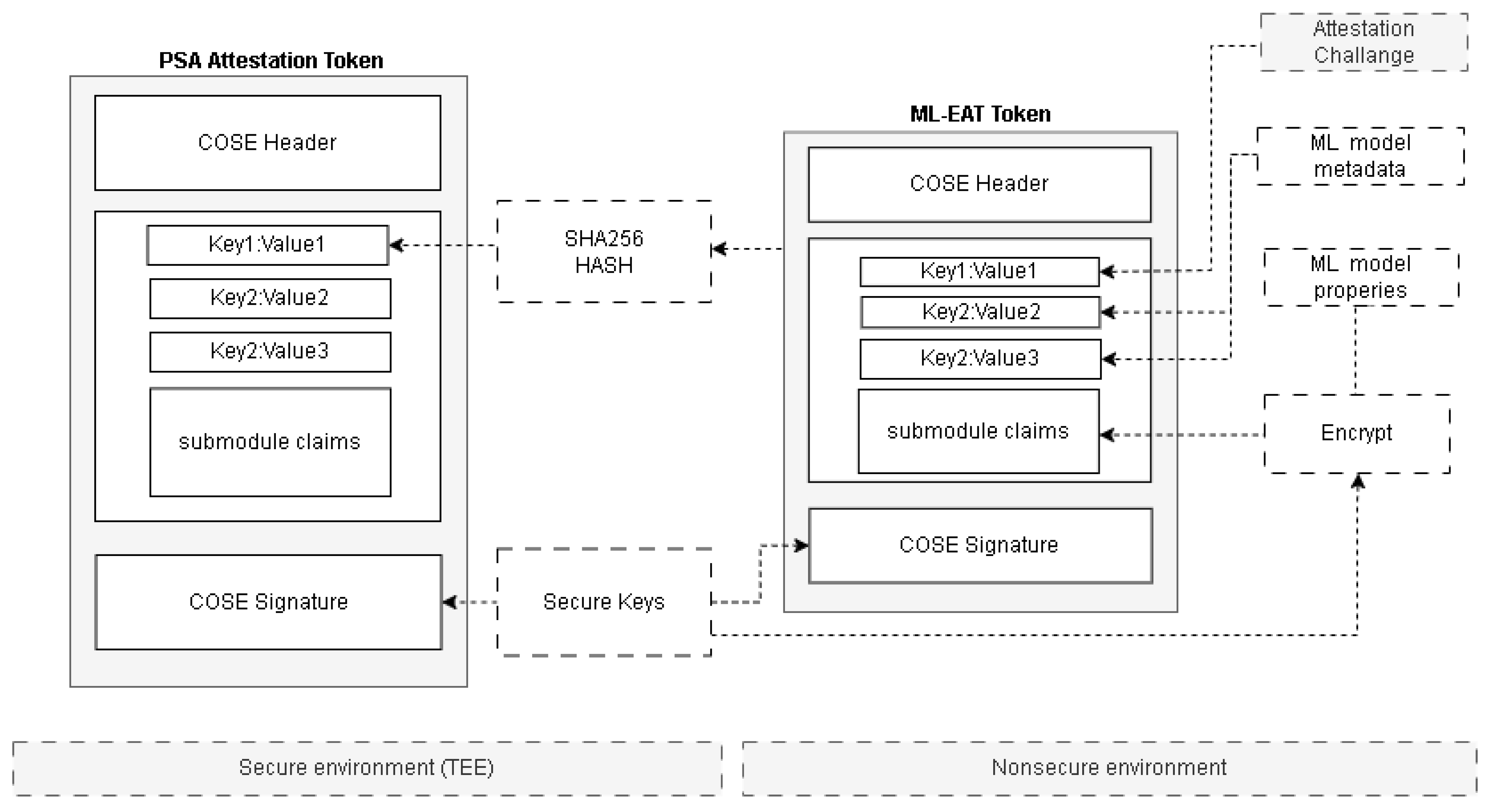
4.1. Dual-Token attestation method
4.2. ML Attestation Token
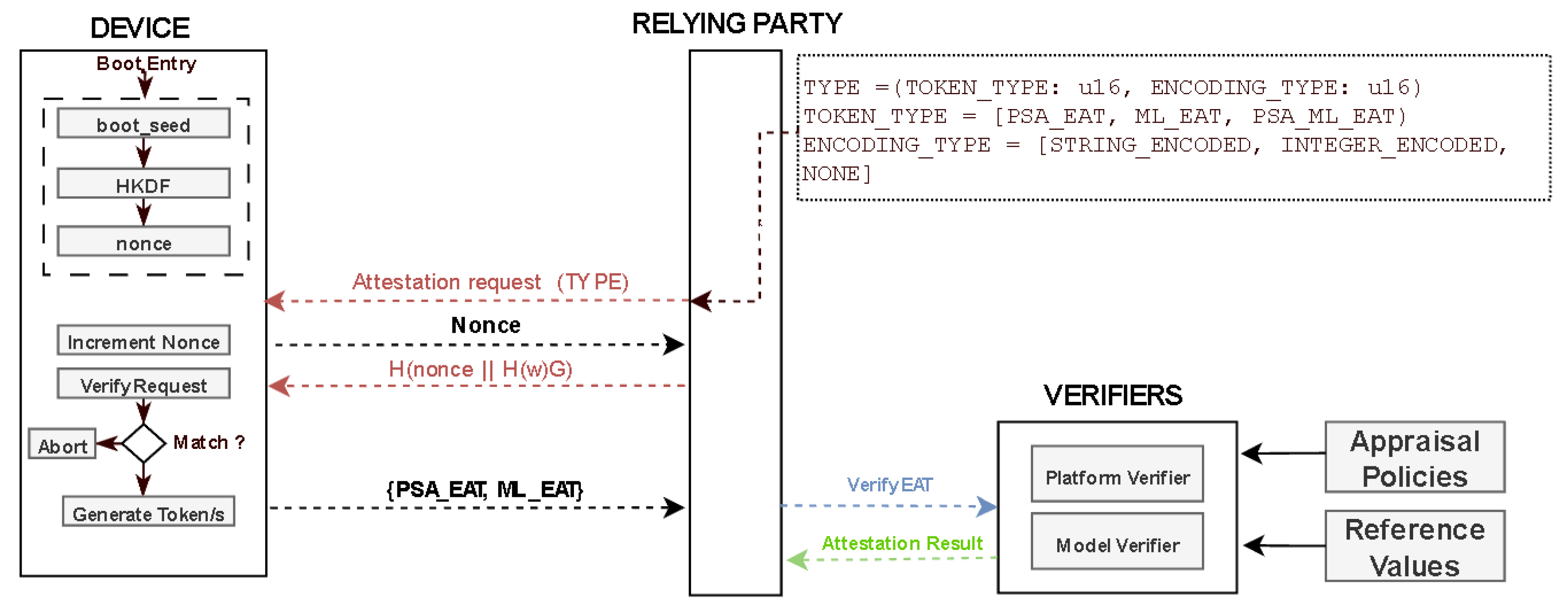
4.3. Remote attestation workflow
5. Methodology
5.1. System Overview
5.1.1. Platform
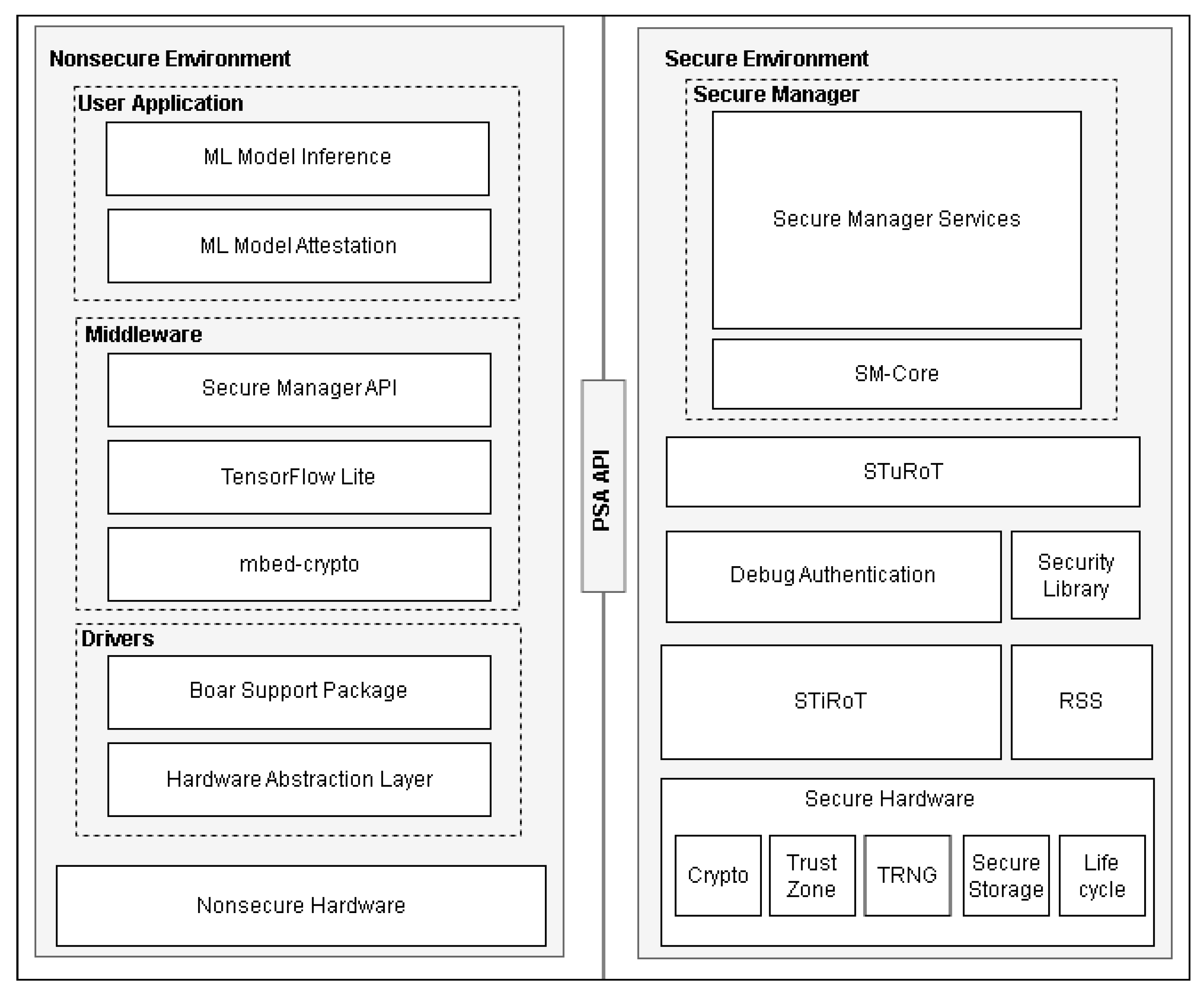
5.1.2. Software components
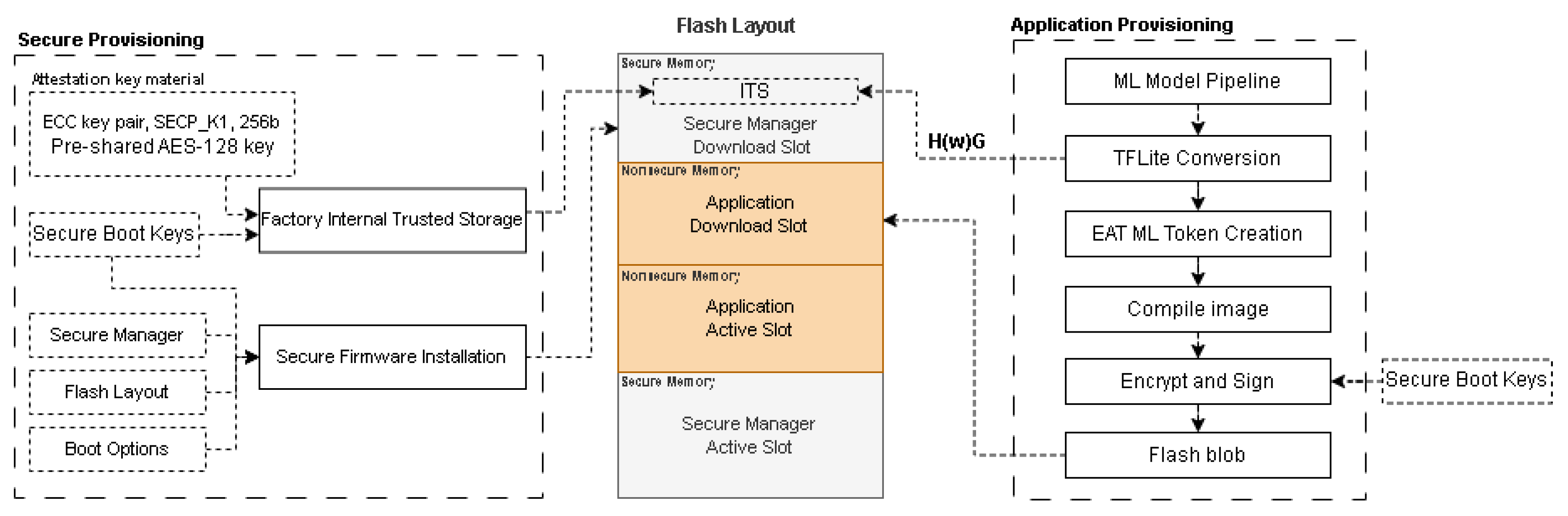
5.1.3. Device provisioning
5.1.4. Secure Boot
5.1.5. PSA initial attestation token
5.2. Description and implementation of the model under test
5.3. Evaluation metrics
- A cloud-based service, acting as a relying party, wants to verify the device’s trustworthiness and obtain high-level details about the ML model, such as vendor, version, accuracy, and the latest update. It is not interested in the detailed specifics of the model itself.
- A federated learning system queries a device that has just joined the collaborative network for the weights it has trained. In this scenario, the system needs to verify both the trustworthiness of the device and the model architecture. Depending on the security requirements of the model, the token claims can either be encrypted or unencrypted. Additionally, the system may either recognize standardized ML claims (integer-encoded) related to the model architecture or rely on string-encoded claims that align with the structure of the ML framework.
6. Results
6.1. Memory footprint
6.2. Secure boot
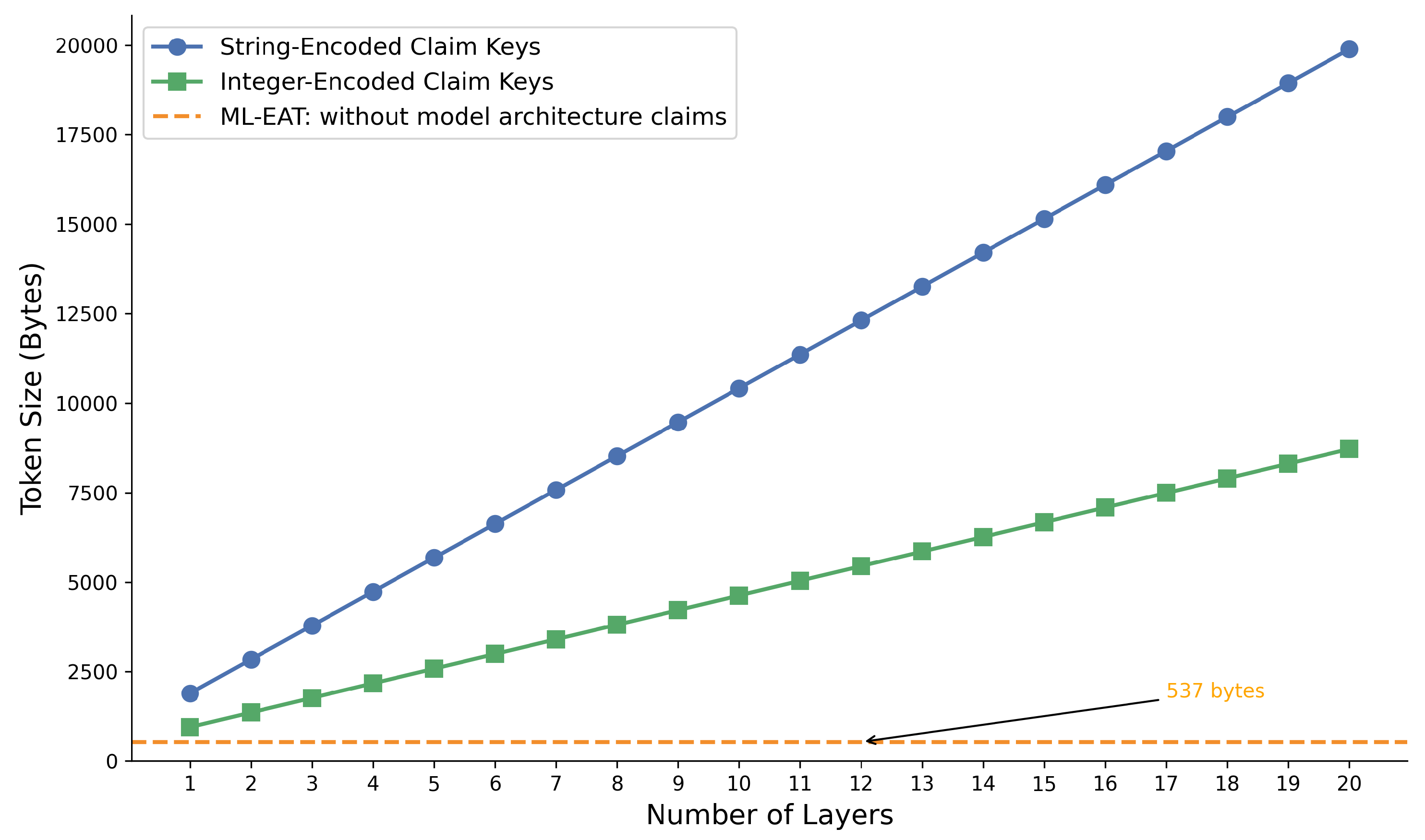
6.3. Attestation tokens size
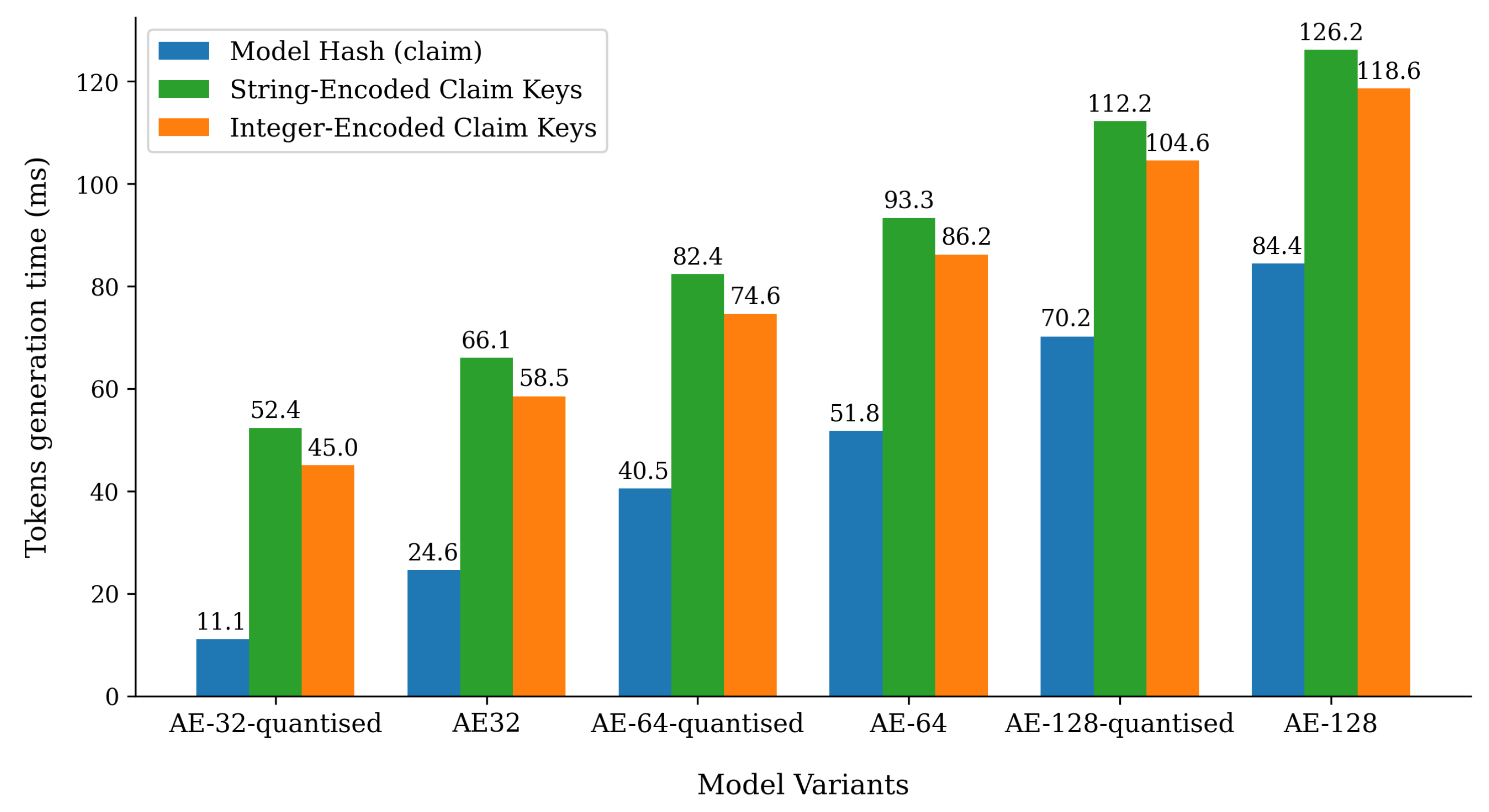
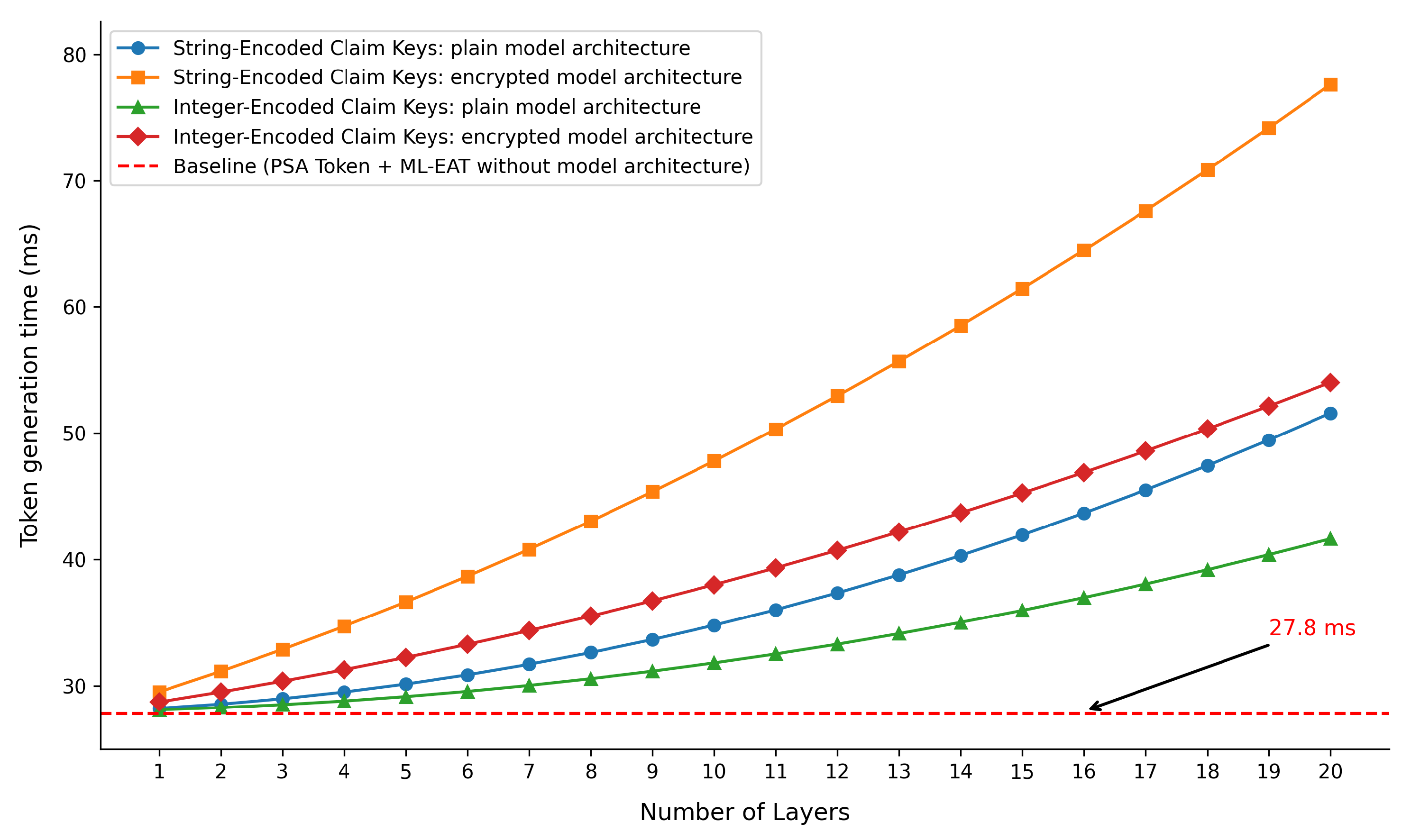
6.4. Attestation time
6.5. Discussion
- In the first scenario, the token generation time of 27.8 ms on the device would not affect the real-time requirements of the anomaly detection system. Given that the inference time is between 15-20 ms and the attestation is not performed frequently, the impact remains negligible. Furthermore, the token size is small, consisting of 1084 bytes, which includes both the PSA and ML-EAT tokens.
-
In the second scenario, it is evident that both the ML-EAT token size and the encoding type of the claim keys play a crucial role. For the evaluated model architecture, the ML-EAT token size can be reduced from 9468 bytes to 4218 bytes, resulting in shorter attestation times and a smaller token size that needs to be transmitted.Moreover, for the models evaluated, the attestation time may impact the real-time requirements of the anomaly detection system on the device, as the attestation time can be up to six times longer than the assumed inference time. However, in a TinyML federated learning system, the attestation process may occur less frequently, since the model may not require frequent updates due to the stability of the patterns being learned across updates.
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Mikhaylov, D.; Polonelli, T.; Magno, M. On-Sensor TinyML Event-Based Fault Detection Strategies on Wind Turbine Blades. In Proceedings of the 2024 IEEE Sensors Applications Symposium (SAS). IEEE; 2024; pp. 1–6. [Google Scholar]
- Gkogkidis, A.; Tsoukas, V.; Papafotikas, S.; Boumpa, E.; Kakarountas, A. A TinyML-based system for gas leakage detection. In Proceedings of the 2022 11th international conference on modern circuits and systems technologies (MOCAST). IEEE; 2022; pp. 1–5. [Google Scholar]
- Huckelberry, J.; Zhang, Y.; Sansone, A.; Mickens, J.; Beerel, P.A.; Reddi, V.J. TinyML Security: Exploring Vulnerabilities in Resource-Constrained Machine Learning Systems. arXiv preprint, 2024; arXiv:2411.07114. [Google Scholar]
- Confidential Computing Consortium. Confidential Computing: Outreach Whitepaper, 2022. Accessed: 2024-11-21.
- Segers, L.; Talebi, B.; da Silva, B.; Touhafi, A.; Braeken, A. Trustworthy Environmental Monitoring Using Hardware-Assisted Security Mechanisms. Sensors (Basel, Switzerland) 2024, 24. [Google Scholar] [CrossRef] [PubMed]
- Costan, V. Intel SGX explained. IACR Cryptol, EPrint Arch, 2016. [Google Scholar]
- Sev-Snp, A. Strengthening VM isolation with integrity protection and more. White Paper, January 2020, 53, 1450–1465. [Google Scholar]
- Pinto, S.; Santos, N. Demystifying arm trustzone: A comprehensive survey. ACM computing surveys (CSUR) 2019, 51, 1–36. [Google Scholar] [CrossRef]
- Cheang, K.; Rasmussen, C.; Lee, D.; Kohlbrenner, D.W.; Asanović, K.; Seshia, S.A. Verifying RISC-V physical memory protection. arXiv preprint, 2022; arXiv:2211.02179. [Google Scholar]
- Confidential Computing Consortium. Common Terminology for Confidential Computing, 2022. Accessed: 2024-11-18.
- Birkholz, H.; Thaler, D.; Richardson, M.; Smith, N.; Pan, W. Remote attestation procedures (RATS) architecture. RFC 9334 2023. [Google Scholar]
- Weidner, J. ARM Confidential Compute Architecture.
- Trusted Firmware-M Documentation, 2024. Accessed: 2024-11-23.
- Silicon Labs Gecko Platform: Secure Element Manager API Documentation, 2024. Accessed: 2024-11-23.
- STM32 MCU Secure Manager Documentation, 2024. Accessed: 2024-11-23.
- Asokan, N.; Brasser, F.; Ibrahim, A.; Sadeghi, A.R.; Schunter, M.; Tsudik, G.; Wachsmann, C. Seda: Scalable embedded device attestation. In Proceedings of the Proceedings of the 22nd ACM SIGSAC conference on computer and communications security. 2015; 964–975. [Google Scholar]
- Ficco, M.; Guerriero, A.; Milite, E.; Palmieri, F.; Pietrantuono, R.; Russo, S. Federated learning for IoT devices: Enhancing TinyML with on-board training. Information Fusion 2024, 104, 102189. [Google Scholar] [CrossRef]
- Lundblade, L.; Mandyam, G.; O’Donoghue, J.; Wallace, C. The Entity Attestation Token (EAT).
- Schaad, J. Cbor object signing and encryption (cose). Technical report, 2017.
- Ul Haq, S.; Singh, Y.; Sharma, A.; Gupta, R.; Gupta, D. A survey on IoT & embedded device firmware security: architecture, extraction techniques, and vulnerability analysis frameworks. Discover Internet of Things 2023, 3, 17. [Google Scholar]
- Costin, A.; Zaddach, J.; Francillon, A.; Balzarotti, D. A Large-scale analysis of the security of embedded firmwares. In Proceedings of the 23rd USENIX security symposium (USENIX Security 14); 2014; pp. 95–110. [Google Scholar]
- Ankergård, S.F.J.J.; Dushku, E.; Dragoni, N. State-of-the-art software-based remote attestation: Opportunities and open issues for Internet of Things. Sensors 2021, 21, 1598. [Google Scholar] [CrossRef] [PubMed]
- Kohnhäuser, F.; Büscher, N.; Katzenbeisser, S. A practical attestation protocol for autonomous embedded systems. In Proceedings of the 2019 IEEE European Symposium on Security and Privacy (EuroS&P). IEEE. 2019; 263–278. [Google Scholar]
- Eldefrawy, K.; Tsudik, G.; Francillon, A.; Perito, D. Smart: secure and minimal architecture for (establishing dynamic) root of trust. In Proceedings of the Ndss. 2012; 12, 1–15. [Google Scholar]
- Koeberl, P.; Schulz, S.; Sadeghi, A.R.; Varadharajan, V. TrustLite: A security architecture for tiny embedded devices. In Proceedings of the Proceedings of the Ninth European Conference on Computer Systems. 2014; pp. 1–14. [Google Scholar]
- Ling, Z.; Yan, H.; Shao, X.; Luo, J.; Xu, Y.; Pearson, B.; Fu, X. Secure boot, trusted boot and remote attestation for ARM TrustZone-based IoT Nodes. Journal of Systems Architecture 2021, 119, 102240. [Google Scholar] [CrossRef]
- Ott, S.; Kamhuber, M.; Pecholt, J.; Wessel, S. Universal Remote Attestation for Cloud and Edge Platforms. In Proceedings of the Proceedings of the 18th International Conference on Availability, Reliability and Security. 2023; 1–11. [Google Scholar]
- Ferro, L.; Lioy, A.; et al. Standard-Based Remote Attestation: The Veraison Project. In Proceedings of the Proceedings of The Italian Conference on Cybersecurity (ITASEC 2024). CEUR-WS. 2024; 1–13. [Google Scholar]
- RATS, L.L. The Entity Attestation Token (EAT), 2024. Accessed: 2024-11-21.
- Jones, M.; Camarillo, G.; Bormann, C. CBOR Web Token (CWT). https://www.rfc-editor.org/rfc/rfc8392.html, 2018. Accessed: 2024-12-24.
- Internet Assigned Numbers Authority (IANA). JSON Web Token (JWT) Claims Registry. https://www.iana.org/assignments/jwt/jwt.xhtml. Accessed: 2024-12-24.
- Bormann, C.; Hoffman, P. Concise Binary Object Representation (CBOR). https://www.rfc-editor.org/rfc/rfc8949.html, 2020. Accessed: 2024-12-24.
- Internet Assigned Numbers Authority (IANA). CWT (CBOR Web Token) Parameters, 2024. Accessed: 2024-12-22.
- Tschofenig, H.; Smith, N.; Frost, S.; Fuchs, A. Attestation Token for PSA. Internet-Draft draft-tschofenig-rats-psa-token-05, 2020. Expires: May 6, 2021.
- O’Donoghue, J. Towards Lightweight and Interoperable Trust Models: The Entity Attestation Token 2019.
- Internet Assigned Numbers Authority (IANA). COSE (Concise Binary Object Representation) Parameters, 2024. Accessed: 2024-12-24.
- STMicroelectronics. Discovery Kit with STM32H573II MCU. https://www.st.com/resource/en/user_manual/um3143-discovery-kit-with-stm32h573ii-mcu-stmicroelectronics.pdf, 2020. Accessed: 2024-12-24.
- Trusted Firmware, M. Trusted Firmware M Documentation. https://trustedfirmware-m.readthedocs.io/en/latest/index.html, 2024. Accessed: 2024-12-24.
- Baciu, V.E.; Stiens, J.; da Silva, B. MLino bench: A comprehensive benchmarking tool for evaluating ML models on edge devices. Journal of Systems Architecture 2024, 155, 103262. [Google Scholar] [CrossRef]
- David, R.; Duke, J.; Jain, A.; Reddi, V.; Jeffries, N.; Li, J.; Kreeger, N.; Nappier, I.; Natraj, M.; Regev, S.; et al. Tensorflow lite micro: Embedded machine learning on tinyml systems. arXiv 2020. arXiv preprint, 2010; arXiv:2010.08678. [Google Scholar]
- Tanabe, R.; Purohit, H.; Dohi, K.; Endo, T.; Nikaido, Y.; Nakamura, T.; Kawaguchi, Y. MIMII DUE: Sound dataset for malfunctioning industrial machine investigation and inspection with domain shifts due to changes in operational and environmental conditions. In Proceedings of the 2021 IEEE Workshop on Applications of Signal Processing to Audio and Acoustics (WASPAA). IEEE. 2021; 21–25. [Google Scholar]
- Purohit, H.; Tanabe, R.; Ichige, K.; Endo, T.; Nikaido, Y.; Suefusa, K.; Kawaguchi, Y. MIMII Dataset: Sound dataset for malfunctioning industrial machine investigation and inspection. arXiv preprint, 2019; arXiv:1909.09347. [Google Scholar]
- Banbury, C.; Reddi, V.J.; Torelli, P.; Holleman, J.; Jeffries, N.; Kiraly, C.; Montino, P.; Kanter, D.; Ahmed, S.; Pau, D.; et al. Mlperf tiny benchmark. arXiv preprint, 2021; arXiv:2106.07597. [Google Scholar]
- Novac, P.E.; Boukli Hacene, G.; Pegatoquet, A.; Miramond, B.; Gripon, V. Quantization and deployment of deep neural networks on microcontrollers. Sensors 2021, 21, 2984. [Google Scholar] [CrossRef] [PubMed]
- tflite-find-arena-size. https://github.com/edgeimpulse/tflite-find-arena-size, 2024. Accessed: 2024-12-22.
- Jiang, W.; Guo, Z.; Ma, Y.; Sang, N. Measurement-based research on cryptographic algorithms for embedded real-time systems. Journal of Systems Architecture 2013, 59, 1394–1404. [Google Scholar] [CrossRef]
| CLAIM FIELD | TYPE (CBOR) | DESCRIPTION |
|---|---|---|
| Challenge | Byte String (3) | An unique 32-byte value from the verifier to mitigate reply attacks |
| Model information (Array of maps) | ||
| Model ID | Text String (3) | An unique model identifier (e.g DOI, Name||Creation date) |
| Model version | Text String (3) | Version of the model (e.g. "1.0.0") |
| Model publisher | Text String (3) | Publisher or creator of the model |
| Hash algorithm | Text String (3) | Cryptographic hash (e.g., SHA256) used for the following claims |
| Model hash | Byte String (2) | Hash of the model weights and nounce H(w||nounce) |
| Hash of public key | Byte String (2) | Hash of the public key used for secure updates |
| Training Summary (Array of maps) | ||
| Dataset name | Text String (3) | Dataset name as per the creator or DOI |
| Dataset identifier | Byte String (2) | Identifier of the dataset used for training (e.g UUID, hash) |
| Last update | Tag (6) | Standard Date/Time string |
| Performance (Array of maps) | ||
| Accuracy | Floating-point (7) | Accuracy of the model |
| F1-Score | Floating-point (7) | F1-Score of the model |
| SRAM footprint | Unsigned Integer (0) | Memory footprint of the model at runtime |
| FLASH footprint | Unsigned Integer (0) | Flash memory used by the model |
| Inference latency | Floating-point (7) | Average inference time on device |
| Model Parameters (Array of maps) | ||
| Input format | Array (4) | The format of the model input. Array of unsigned integers. |
| Output format | Array (4) | The format of the model output. Array of unsigned integers. |
| Quantization | List(4) | Quantization details |
| Method | Text String (3) | The quantization method used. E.g., "8-bit", "Binary", "Float16" |
| Bits | Unsigned Integer (0) | Number of bits used for quantization. E.g., 8 |
| Weight Quantization | Text String (3) | Describes the quantization method for the model weights. E.g., "uniform", "asymmetric" |
| Activation Quantization | Text String (3) | Describes the quantization method for activations. E.g., "symmetric", "asymmetric" |
| Post training | Unsigned Integer (0) | Indicates if post-training quantization was used. E.g., 1 (true), 0 (false) |
| ML Framework (Array of maps) | ||
| Name | Text String (3) | The name of the machine learning framework used. E.g., "TensorFlow", "PyTorch", "ONNX" |
| Version | Text String (3) | The version of the machine learning framework. E.g., "2.8.0" |
| Runtime | Text String (3) | he runtime environment of the framework. E.g., "TensorFlow Lite", "uTensor", "uTVM" |
| Hardware acceleration | Unsigned Integer (0) | Indicates if the model uses hardware accelerators (NPU, DSP) |
| Supported operators | List (4) | List of operators supported by the runtime framework |
| Operation N | Text String (3) | Name of each supported operation. E.g., "Conv2D", "BatchNorm", "Dense" |
| Model architecture (Array of maps) | ||
| ... | ... | ... |
| Claim Name | Details | Possible Values |
|---|---|---|
| measurement_description | Describes the type of hash algorithm used for the measurement. | "SHA256", "SHA512", etc. |
| measurement_value | Computed hash value of the software component | Any valid byte array |
| signer_id | Hash of the public key used to verify the software component. | Any valid byte array |
| sw_component_type | Specifies the type of the software component being described. | "NSPE" (ML application) "SPE" (STM SM) "BL" (STuRoT) |
| sw_component_version | Version of the software component. | Any valid version string (e.g., "1.0.0", "1.1.0"). |
| SW Component | Flash [kB] | SRAM [kB] | |
|---|---|---|---|
| Secure Environment | Secure Manager | 360 | 140 |
| NS/S Area | - | 16 | |
| Non-secure Environment | Application Components | 358.2 | 4.7 |
| Model AE-32 | 198.27 | 7.48 | |
| Model AE-32-quantized | 57.6 | 6.46 | |
| Model AE-64 | 438.9 | 7.61 | |
| Model AE-64-quantized | 120 | 6.49 | |
| Model AE-128 | 1067.64 | 7.87 | |
| Model AE-128-quantized | 257.72 | 6.63 |
| Component | Image Size (kB) | Boot Time (ms) |
|---|---|---|
| Application + AE-32 | 556.47 | 50.82 |
| Application + AE-32-quantized | 415.8 | 51.25 |
| Application + AE-64 | 797.1 | 52.63 |
| Application + AE-64-quantized | 478.2 | 51.25 |
| Application + AE-128 | 1425.84 | 53.06 |
| Application + AE-128-quantized | 615.92 | 51.69 |
| Layer | String-Encoded Claim Keys | Integer-Encoded Claim Keys |
|---|---|---|
| Activation | 158 | 95 |
| Add | 125 | 70 |
| BatchNormalization | 660 | 327 |
| Conv2D | 544 | 243 |
| Dense | 427 | 207 |
| Dropout | 166 | 98 |
| Flatten | 159 | 95 |
| LSTM | 801 | 358 |
| MaxPooling2D | 210 | 117 |
| Multiply | 135 | 80 |
| Input | 89 | 49 |
| ReLU | 182 | 101 |
| Softmax | 139 | 82 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




