Submitted:
16 September 2024
Posted:
20 September 2024
You are already at the latest version
Abstract
Keywords:
Distributed Denial of Service (DDOS) Background
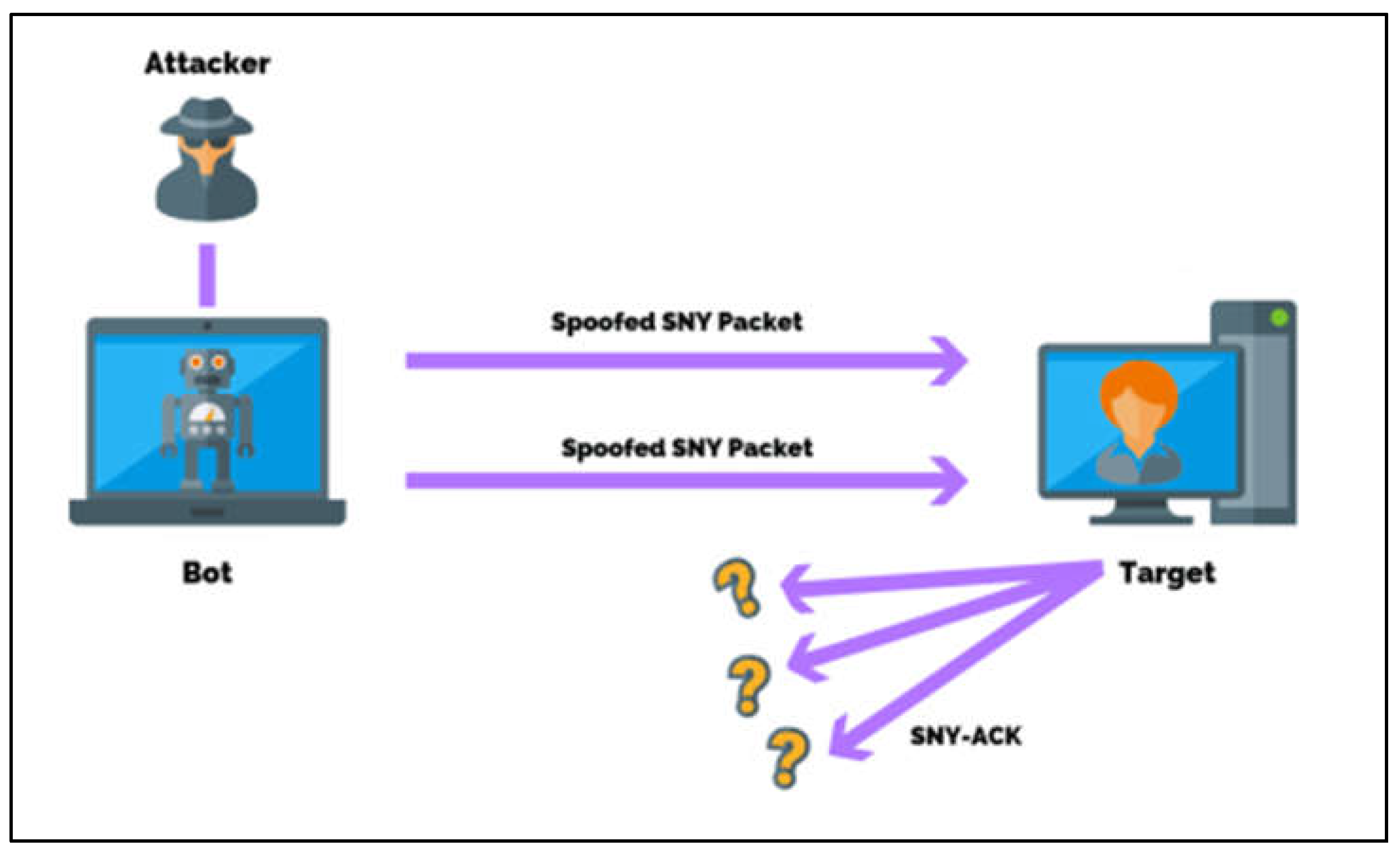
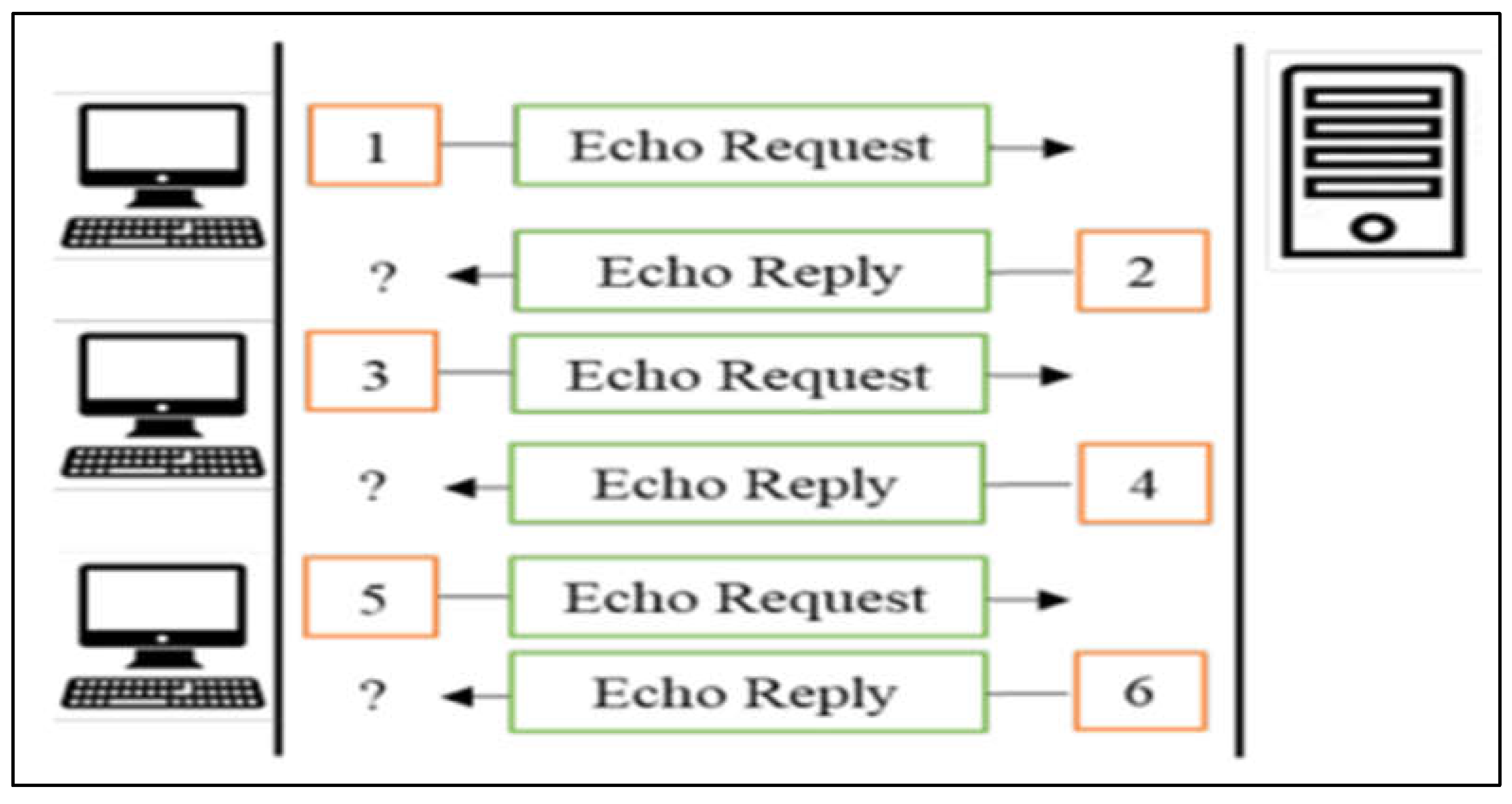
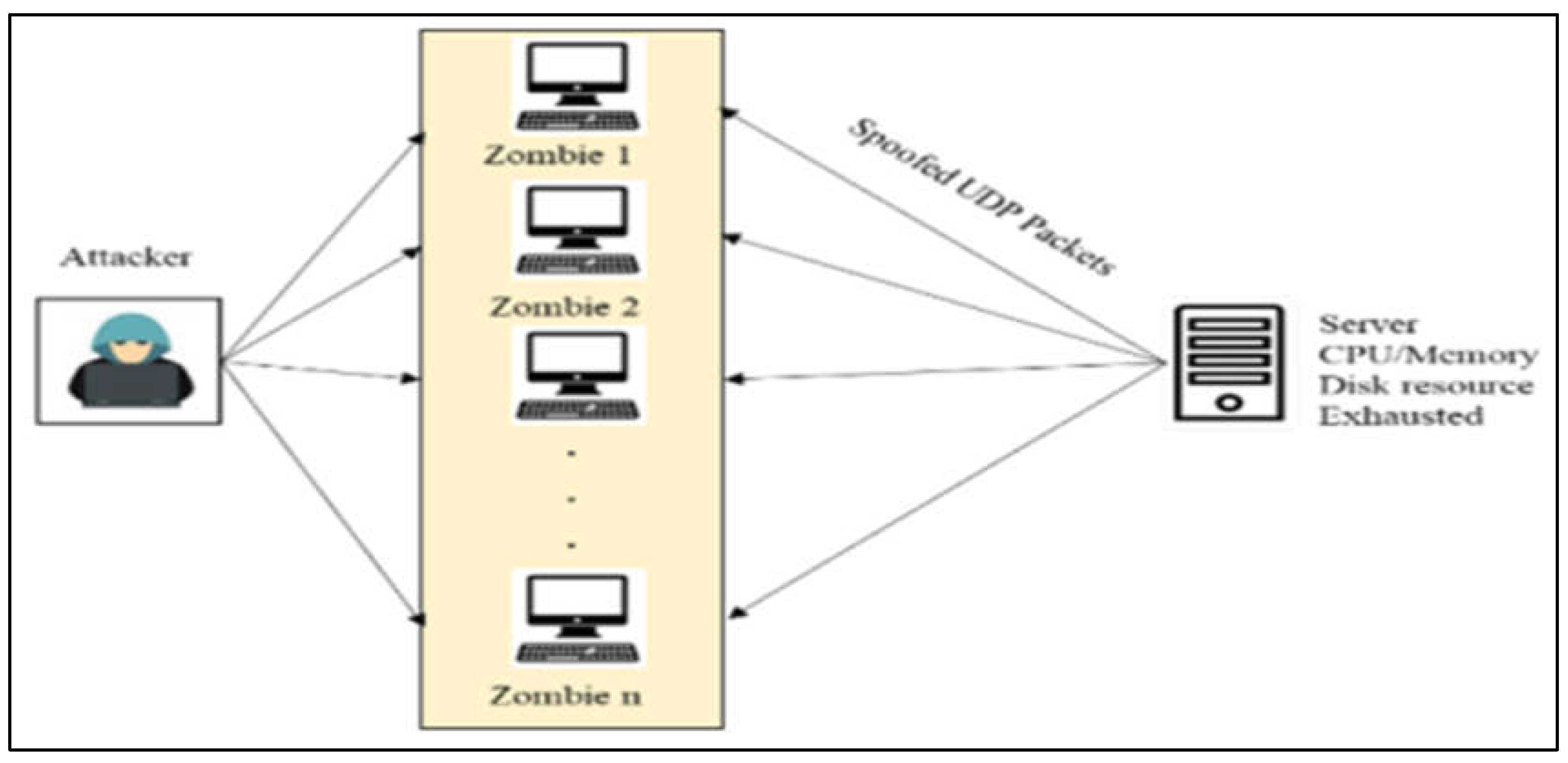
Case 1—DDoS
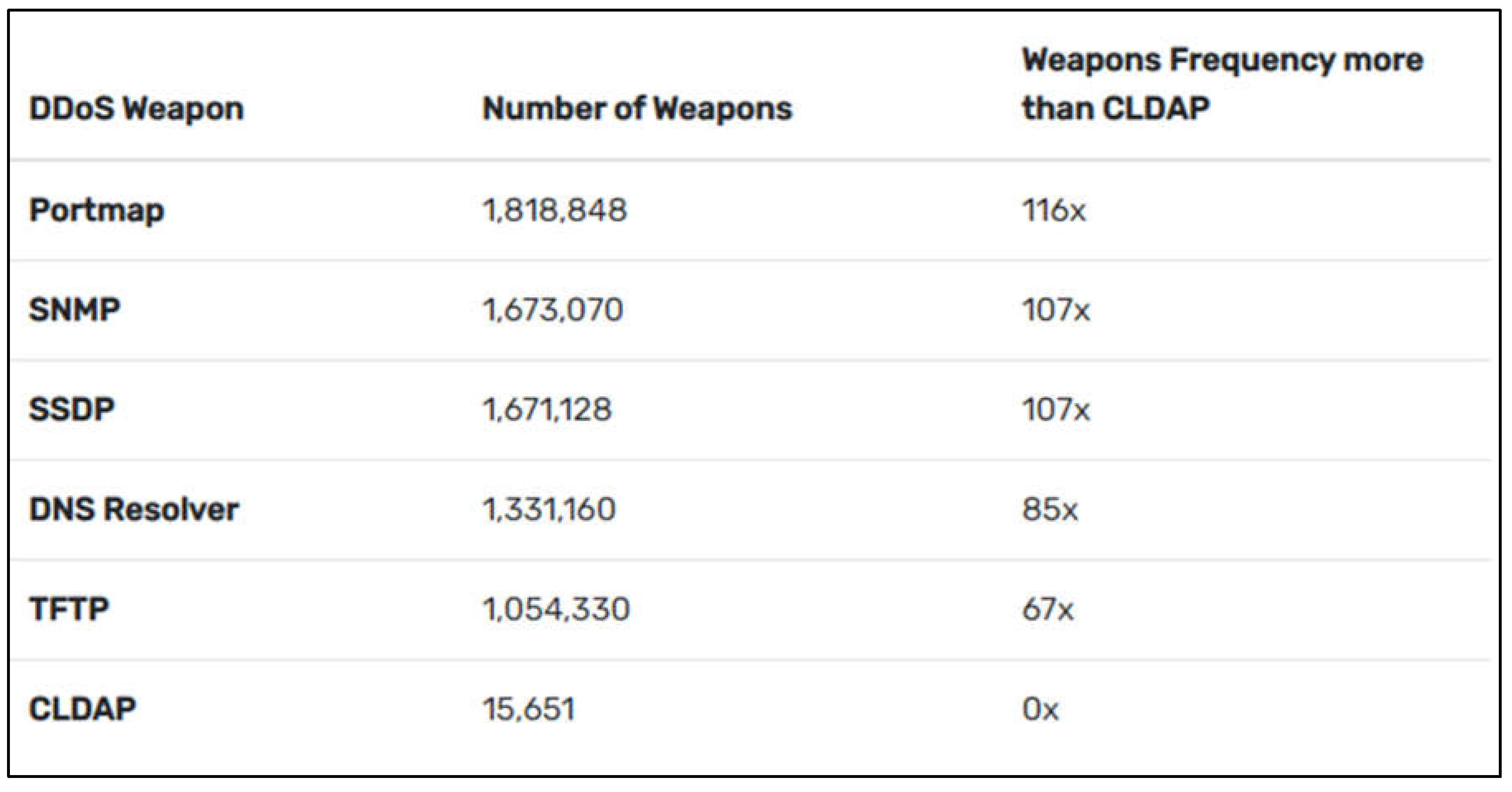
What Is a CLDAP DDoS Attack?
How to Protect Ourselves from CLDAP DDoS Attack
Potential Security Threats
Countermeasures—DDoS
Proposed Countermeasures
- 1.
- Collaborative Management
- 2.
- Integrated protection
- 3.
- Distributed Multipoint Detection
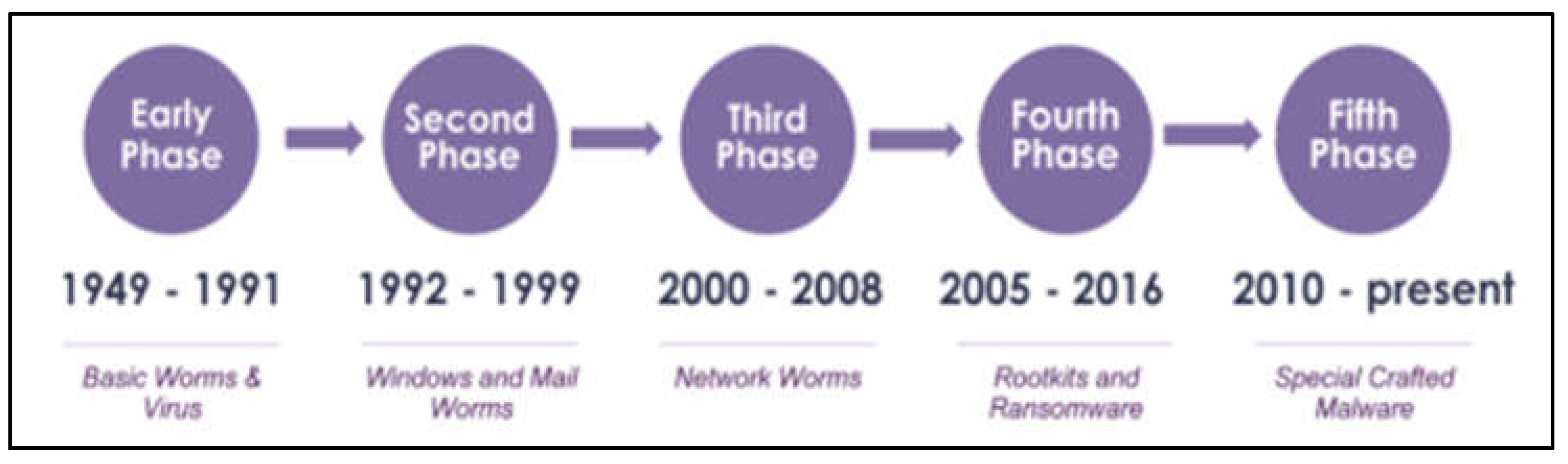
Malware Background
Case 2—Ransomware
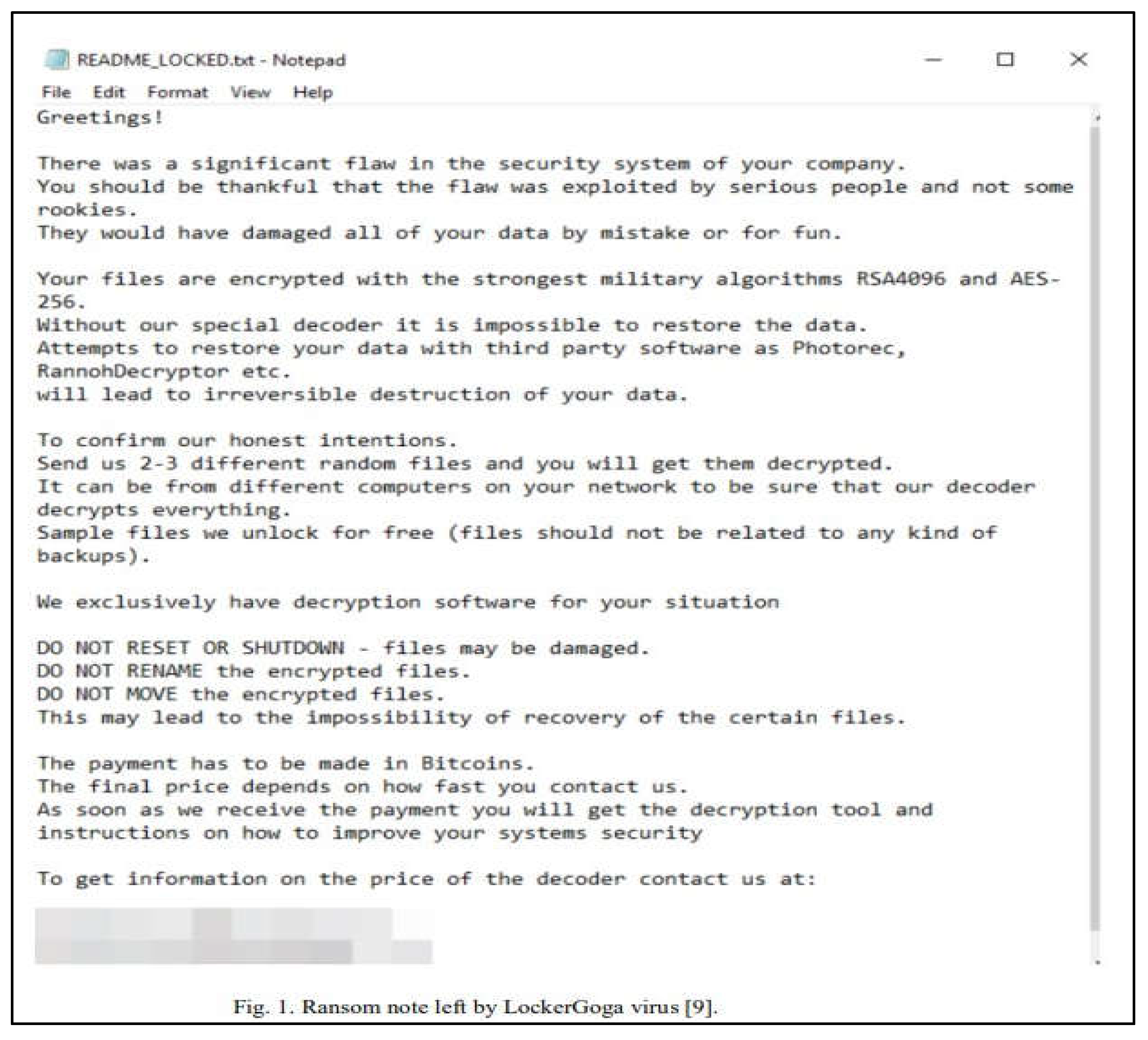
What Is LockerGoga Ransomware and How Does It Work?
Countermeasures
- i.
- If there is a highly competent attacker and a malevolent insider, keeping them from accessing the network and system is insufficient even with high-level security measures. To ascertain and comprehend what is happening in the network, it is crucial to monitor and follow an attack’s Cyber Kill Chain (CKC). The system should use a variety of monitoring tools, such as an Intrusion Detection System (IDS) that can track, gather data, examine, and quickly identify an attack. Thus, every interface of the edge gateway should have an IDS sensor installed (Al-Hawawreh et al., 2019; Humayun, Sujatha, et al., 2022).
- ii.
- In the chain of cyber defence, humans are the weakest link. We lose focus when we are busy or distracted, click on links, or access malicious attachments. To overcome this, it is required that security awareness training be provided in the Learning Management Systems (LMS) of every firm to guarantee that staff members can react appropriately to threats (Ghotbi, P, 2021). This act may assist users in changing from being targets to defenders who can recognize, avoid, and report fraudulent attachments by keeping them informed of the strategies and tactics used by cybercriminals. This contributes to the security of the company’s operations, finances, and data. User awareness should emphasize safe computer procedures and precautions. Users should be trained to recognize suspicious activity because they are the last line of protection. Furthermore, to help users, increase their knowledge and awareness of typical security concerns, they should also consider adopting solutions that offer routine microlearning (Papez and Shields, 2021). Organizations should routinely check their employee’s knowledge as well. It has been shown that awareness and training are insufficient if there aren’t regular knowledge assessments. Running internal phishing campaigns is a common strategy to determine user preparedness and response. This technique involves sending employees a carefully designed phishing email. A warning page is displayed after a person clicks the link. This would help to educate them practically as well (Ghotbi, P, 2021).
- iii.
- In comparison to a typical firewall, next-generation firewalls include more distinctive features, such as enhanced traffic filtering that involves a more thorough examination of packets up to the application layer in an Open System Interconnect (OSI) paradigm or the transport and framework levels. Additionally, they incorporate stateful inspection, NAT, port and protocol filtering, virtual private networks, and anti-malware security (Al-Hawawreh et al., 2019).
- iv.
- Backup systems are another common defence against ransomware assaults. Even though almost all businesses have several backup systems, they frequently fail to function when ransomware outbreaks occur. Data on the victim’s computer will initially be encrypted when it becomes infected with destructive ransomware. The ransomware will then encrypt the data kept on the NAS (Network Attached Storage) and Internet-based cloud file systems that are mounted on the victim’s PC remotely. Since those remote storages are virtually often used to store backup data and since they are typically automatically mounted on the victim’s machine. As a result, both the source data and the backup data are often encrypted in destructive ransomware attacks, making data recovery difficult. Given the potential of damaging ransomware and the requirement for data recovery, a safe and reliable backup system with high usability is necessary (Jin et al., 2018; Javaid et al., 2022; Jayakumar et al., 2021; Jhanjhi et al., 2020).
- v.
- All hardware, mobile devices, operating systems, software, and applications, including cloud storage and content management systems (CMS), should be patched and kept up to date. If can, use a central patch management system. Apart from that, to stop programmes from running in frequent ransomware sites like temporary files, implement application whitelisting and software restriction policies (SRP). Furthermore, w We can also impose restrictions on Internet usage. We should consider ad-blocking software and use a proxy server when accessing the Internet. We should limit access to popular entry points for ransomware, like social networking sites and personal email accounts (Ransomware: Facts, threats, and countermeasures, 2019).
- vi.
- Despite extensive training and ongoing talks about ransomware, businesses continue to fall prey to these attacks. To manage cyber events, the National Institute of Standards and Technology (NIST) offers a reference framework. Having a strong “react” and “recovery” plan is necessary for ransomware attacks, even though putting in place detective and protective procedures is crucial. To deal with ransomware assaults and defend against the most recent ransomware threats, it is important to have a thorough plan and step-by-step runbooks (Ghotbi, P, 2021).
- vii.
- When ransomware is discovered in a portion of the network, breaking the network up into smaller sections enables us to keep it under control. Many legacy networks continue to operate as sizable /8 or /16 flat subnets. When ransomware infiltrates those networks, it can quickly infect many hosts. In this circumstance, it will be challenging to separate and contain the affected endpoints (Ghotbi, P, 2021).
- viii.
- An efficient antimalware suite should be used. Security technologies are available that can spot ransomware-specific behaviour and stop the infection before any damage is done (Wisser, 2020).
- ix.
- As was already established, the objective is to manage and contain infected hosts as soon as they are discovered. Isolating a host may be simpler in virtual settings. However, to investigate and take corrective action in physical environments, we might need to physically unplug the network connection and operate on the computer console. The remediation strategy and runbooks should be very specific about the isolation and confinement procedures for various environments (Ghotbi, P, 2021).
- x.
- To stop infection spread, we must quickly detach the infected system from the network. In addition, we need to identify the data that was impacted since some sensitive data may call for further reporting or mitigation efforts. We can also try to find out if a decryptor is accessible. No More Ransom! and other online sites can be helpful. If not, we should try recovering files from routinely kept backups. Finally, such ransomware attacks should be reported (Ransomware: Facts, threats, and countermeasures, 2019; Fatima-Tuz-Zahra et al., 2020).
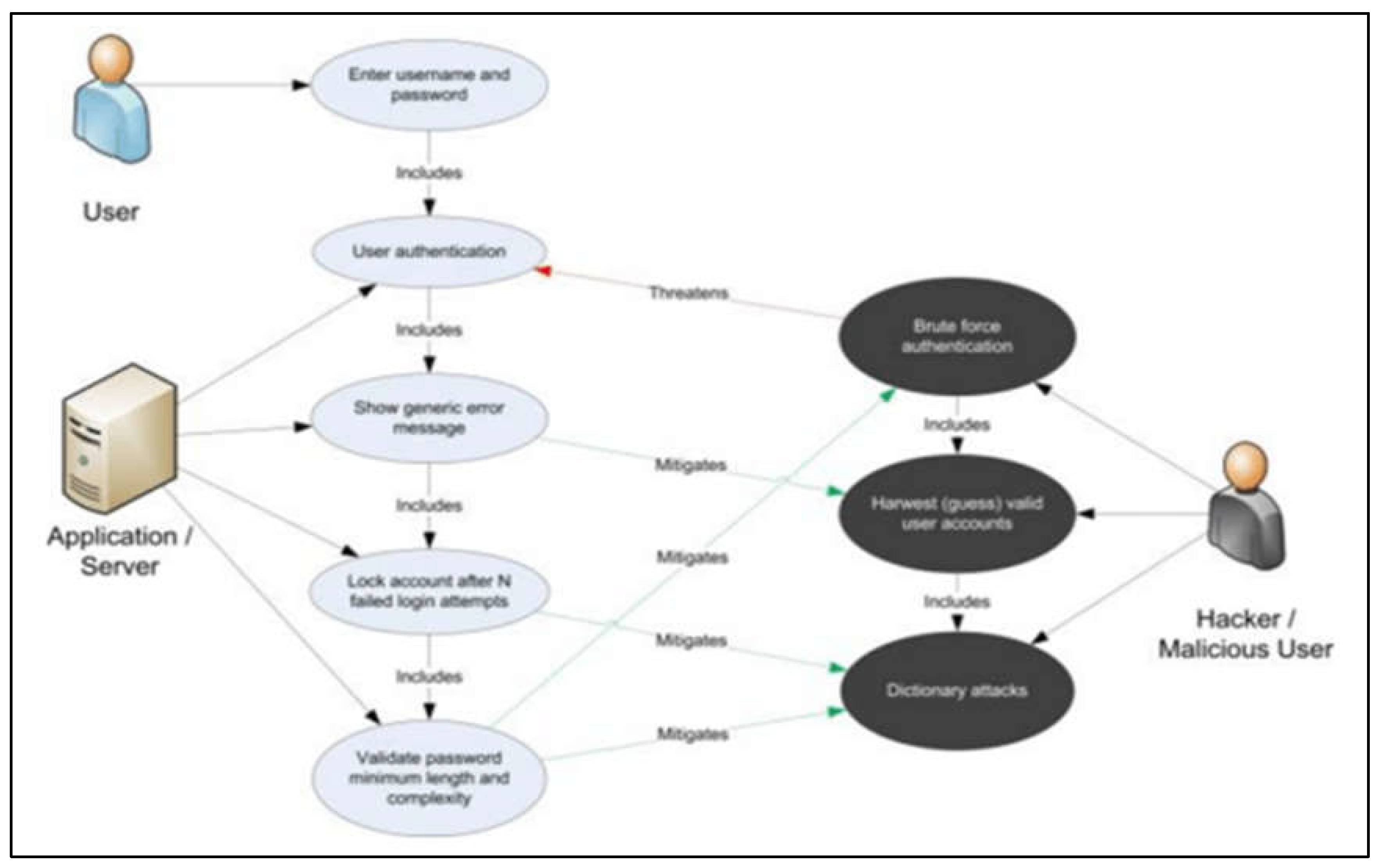
Case 3—Trojan Horse
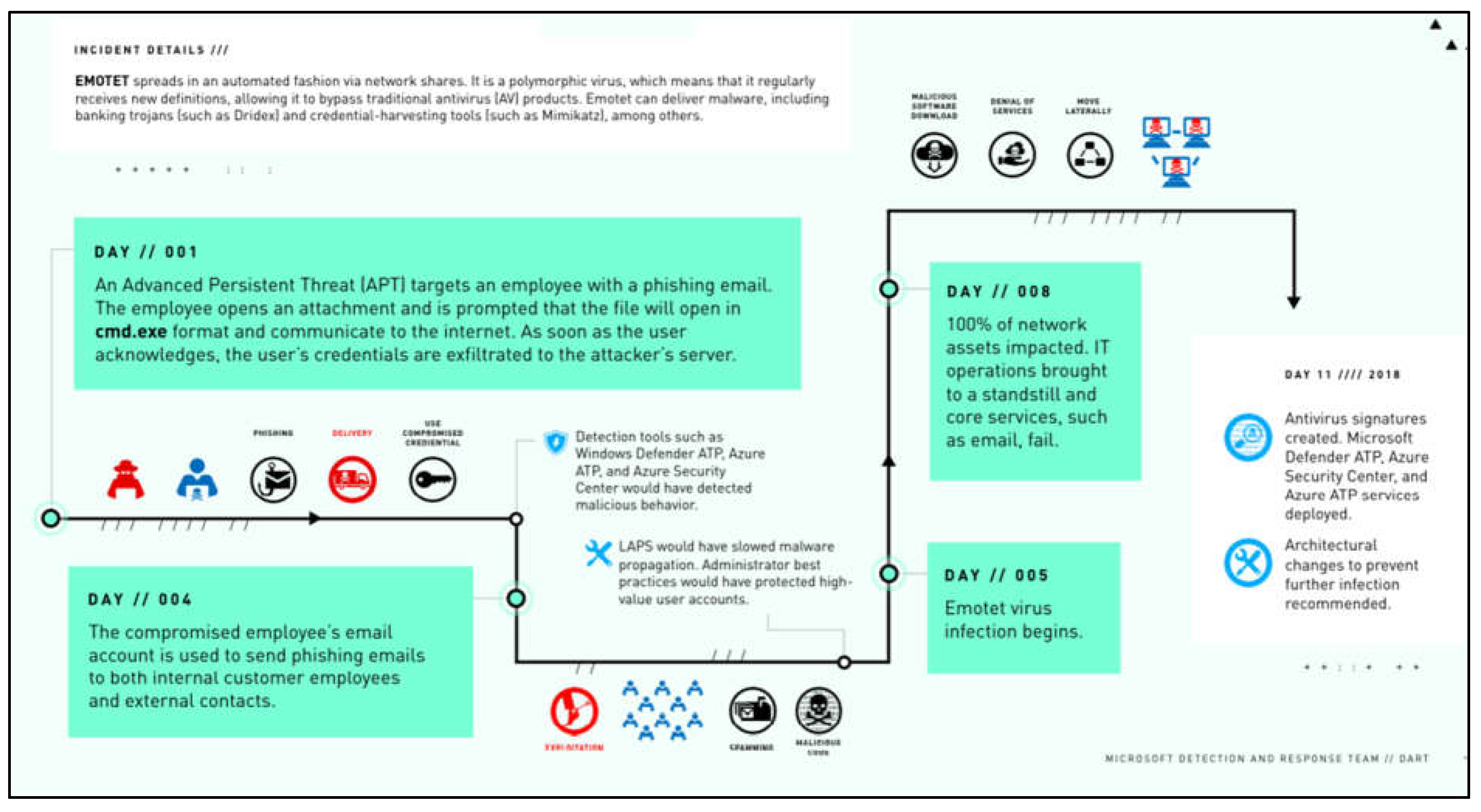
Security Issues
Countermeasures
Conclusion
References
- 8 tips for DDoS protection, mitigation, and defense : Indusface blog (2022) Indusface. Available at: https://www.indusface.com/blog/ddos-protection-mitigation-and-defense-8-essential-tips/#1_Mitigate_DDoS_Attacks_with_Multi-Layered_Multi-Module_Defense.
- A, PS, S, SP, B, H. (2024) ‘DDoS and Botnet Attacks: A Survey of Detection and Prevention Techniques’. 2024 International Conference on Advances in Data Engineering and Intelligent Computing Systems (ADICS). [CrossRef]
- Alenezi, M.N.; et al. (2022) ‘Evolution of Malware Threats and Techniques: a Review’. International Journal of Communication Networks and Information Security (IJCNIS). [CrossRef]
- Al-Hawawreh, M.; Hartog Fden Sitnikova, E. “Targeted ransomware: A new cyber threat to edge system of Brownfield Industrial Internet of Things”. IEEE Internet of Things Journal 2019, 6, 7137–7151. [Google Scholar] [CrossRef]
- Alkinani, M.H.; et al. ‘5G and IoT Based Reporting and Accident Detection (RAD) System to Deliver First Aid Box Using Unmanned Aerial Vehicle’. Sensors 2021, 21, 6905. [Google Scholar] [CrossRef] [PubMed]
- Almusaylim, Z.A.; Zaman, N.; Jung, L.T. (2018) ‘Proposing A Data Privacy Aware Protocol for Roadside Accident Video Reporting Service Using 5G In Vehicular Cloud Networks Environment’. 2018 4th International Conference on Computer and Information Sciences (ICCOINS). [CrossRef]
- Ali, S.; Hafeez, Y.; Humayun, M.; Jhanjhi, N.Z.; Le, D.N. Towards aspect based requirements mining for trace retrieval of component-based software management process in globally distributed environment. Information Technology and Management 2022, 23, 151–165. [Google Scholar] [CrossRef]
- Almoysheer, N.; Humayun, M.; Jhanjhi, N.Z. “Enhancing Cloud Data Security using Multilevel Encryption Techniques”. Turkish Online Journal of Qualitative Inquiry 2021, 12, 3. [Google Scholar]
- Alsharif Mohammed, H.; Jahid, A.; Kelechi, A.H.; Kannadasan, R. “Green IoT: A review and future research directions”. Symmetry 2023, 15, 757. [Google Scholar] [CrossRef]
- Altulaihan, E.; Almaiah, M.A.; Aljughaiman, A. ‘Anomaly Detection IDS for detecting DOS attacks in IoT networks based on machine learning algorithms’. Sensors 2024, 24, 713. [Google Scholar] [CrossRef]
- Aslan, Ö.; et al. ‘A comprehensive review of cyber security vulnerabilities, threats, attacks, and solutions’. Electronics 2023, 12, 1333. [Google Scholar] [CrossRef]
- BasuMallick, C. (2022) What is a trojan horse? meaning, examples, and prevention best practices for 2022, Trojan Horse Meaning, Examples, Prevention. Available at: https://www.spiceworks.com/it-security/application-security/articles/what-is-trojan-horse/.
- Bhol, S.G.; Mohanty, J.; Pattnaik, P.K. ‘Taxonomy of cyber security metrics to measure strength of cyber security’. Materials Today Proceedings 2023, 80, 2274–2279. [Google Scholar] [CrossRef]
- Chahal, J.K.; Bhandari, A.; Behal, S. ‘DDoS attacks & defense mechanisms in SDN-enabled cloud: Taxonomy, review and research challenges’. Computer Science Review 2024, 53, 100644. [Google Scholar] [CrossRef]
- Chesti, I.A.; et al. (2020) ‘Evolution, Mitigation, and Prevention of Ransomware’. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- DART, *!!! REPLACE !!!*; MDand, R.T. DART; MDand, R.T. (2020) FULL OPERATIONAL SHUTDOWN. rep. ZDNET. Available at: https://www.zdnet.com/article/microsoft-how-one-emotet-infection-took-out-this-organizations-entire-network/.
- Driouch, O.; Bah, S.; Guennoun, Z. ‘CANSat-IDS: An adaptive distributed Intrusion Detection System for satellites, based on combined classification of CAN traffic’. Computers & Security 2024, 146, 104033. [Google Scholar] [CrossRef]
- Dogra, V.; Singh, A.; Verma, S.; Kavita Jhanjhi, N.Z.; Talib, M.N. (2021). Analyzing DistilBERT for Sentiment Classification of Banking Financial News. In: Peng, SL., Hsieh, SY., Gopalakrishnan, S., Duraisamy, B. (eds) Intelligent Computing and Innovation on Data Science. Lecture Notes in Networks and Systems, vol 248. Springer, Singapore. [CrossRef]
- Dsm (no date) DDoS prevention: The 5 best tips, DSM. Available at: https://www.dsm.net/it-solutions-blog/prevent-ddos-attacks.
- Express Data Path”, UNIVERSITY OF TWENTE STUDENT THESES, pp.1-57. Available at: http://essay.utwente.nl/80125/ (Accessed November 5, 2022).
- Fatima-Tuz-Zahra, N.; et al. (2020) ‘Proposing a Hybrid RPL Protocol for Rank and Wormhole Attack Mitigation using Machine Learning’. 2020 2nd International Conference on Computer and Information Sciences (ICCIS) [Preprint]. [CrossRef]
- Felix, N.O.O. ‘TCP/IP stack transport layer performance, privacy, and security issues’. World Journal of Advanced Engineering Technology and Sciences 2024, 11, 175–200. [Google Scholar] [CrossRef]
- Ferdous, J.; et al. ‘A review of State-of-the-Art malware attack trends and defense Mechanisms’. IEEE Access 2023, 11, 121118–121141. [Google Scholar] [CrossRef]
- Froutan, P. (2004) How to defend against ddos attacks, Computerworld. Computerworld. Available at: https://www.computerworld.com/article/2564424/how-to-defend-against-ddos-attacks.html.
- Fruhlinger, J. (2022). DDoS attacks: Definition, examples, and techniques. [online] CSO Online. Available at: https://www.csoonline.com/article/3648530/ddos-attacks-definition-examples-and-techniques.html.
- Gaur, L.; Jhanjhi, N.Z. (Eds.). (2023). Digital Twins and Healthcare: Trends, Techniques, and Challenges. IGI Global. [CrossRef]
- Ghosh, G.; et al. ‘Secure surveillance system using chaotic image encryption technique’. IOP Conference Series Materials Science and Engineering 2020, 993, 012062. [Google Scholar] [CrossRef]
- Ghani; Abdul, N. B.; Hamid, S.; Ahmad, M.; Saadi, Y.; Jhanjhi, N.Z.; Alzain, M.A.; Masud, M. “Tracking Dengue on Twitter Using Hybrid Filtration-Polarity and Apache Flume”. Comput. Syst. Sci. Eng. 2022, 40, 913–926. [Google Scholar] [CrossRef]
- Gouda; Walaa; Almurafeh, M. ; Humayun, M.; Jhanjhi, N.Z. “Detection of COVID-19 based on chest X-rays using deep learning”. Healthcare 2022, 10, 343.
- Ghotbi, P. Ghotbi, P. (2021) Ransomware: Statistics, latest threats and countermeasures, Online Masters Programs from St. Bonaventure University. Available at: https://online.sbu.edu/news/ransomware-statistics-latest-threats-countermeasures (Accessed: November 6, 2022).
- Glamoslija, K. (2021) How to defend your PC and devices against a trojan horse virus, SafetyDetectives. Safety Detectives. Available at: https://www.safetydetectives.com/blog/what-is-a-trojan-horse-and-how-to-protect-against-it/.
- Gojali, A.M.; et al. (2024) ANALYSIS OF THE EFFECTIVENESS OF THE COMBINATION OF FAIL2BAN AND MODSECURITY IN MITIGATION OF DDOS ATTACKS ON WEB SERVERS. http://eksplorasi.org/index.php/nre/article/view/214.
- Gopi, R.; et al. ‘Enhanced method of ANN based model for detection of DDoS attacks on multimedia internet of things’. Multimedia Tools and Applications 2021, 81, 26739–26757. [Google Scholar] [CrossRef]
- Guenane, F.; Nogueira, M.; Serhrouchni, A. (2015) ‘DDOS Mitigation Cloud-Based Service’. 2015 IEEE Trustcom/BigDataSE/ISPA [Preprint]. [CrossRef]
- Ashraf, H.; Khan, F.; Ihsan, U.; Al-Quayed, F.; Jhanjhi, N.Z.; Humayun, M. “MABPD: Mobile Agent-Based Prevention and Black Hole Attack Detection in Wireless Sensor Networks”. 2023 International Conference on Business Analytics for Technology and Security (ICBATS), Dubai, United Arab Emirates, 2023, pp. 1–11. [CrossRef]
- Ashraf, H.; Hanif, M.; Ihsan, U.; Al-Quayed, F.; Humayun, M.; Jhanjhi, N. “A Secure and Reliable Supply chain management approach integrated with IoT and Blockchain”. 2023 International Conference on Business Analytics for Technology and Security (ICBATS), Dubai, United Arab Emirates, 2023, pp. 1–9. [CrossRef]
- Humayun, M.; Jhanjhi, N.Z.; Hamid, B.; Ahmed, G.. Emerging smart logistics and transportation using IoT and blockchain. IEEE Internet of Things Magazine 2020, 3, 58–62. [Google Scholar] [CrossRef]
- Humayun, M.; Khalil, M.I.; Alwakid, G.; Jhanjhi, N.Z. Superlative feature selection based image classification using deep learning in medical imaging. Journal of Healthcare Engineering 2022, 2022, 7028717. [Google Scholar] [CrossRef]
- Hansen, P.; et al. (2024) ‘Guarding the Galaxy: Satellite Ransomware and Countermeasures’. 2024 IEEE Aerospace Conference [Preprint]. [CrossRef]
- Herati, D.A.; Bojamma, A.M.; Gandhi, I. (2018) “Countermeasures to Ransomware Threat”, ResearchGate, pp.1-7. Available at: https://www.researchgate.net/publication/324690703_Countermeasures_to_Ransomware_Threats (Accessed: November 5, 2022).
- Hnamte, V.; et al. ‘DDoS attack detection and mitigation using deep neural network in SDN environment’. Computers & Security 2024, 138, 103661. [Google Scholar] [CrossRef]
- How to prevent ddos attacks (2022) Embroker. Available at: https://www.embroker.com/blog/how-to-prevent-ddos-attacks/.
- Humayun, M.; Ashfaq, F.; et al. ‘Traffic management: Multi-Scale vehicle detection in varying weather conditions using YOLOV4 and spatial pyramid pooling network’. Electronics 2022, 11, 2748. [Google Scholar] [CrossRef]
- Humayun, M.; Sujatha, R.; et al. ‘A Transfer Learning Approach with a Convolutional Neural Network for the Classification of Lung Carcinoma’. Healthcare 2022, 10, 1058. [Google Scholar] [CrossRef] [PubMed]
- Hussain, K.; et al. (2024) ‘Threats and Vulnerabilities of Wireless Networks in the Internet of Things (IoT)’. 2024 IEEE 1st Karachi Section Humanitarian Technology Conference (KHI-HTC). [CrossRef]
- Iqbal, A.; et al. (2024) ‘Unveiling the connection between malware and pirated software in Southeast Asian countries: a case study’. IEEE Open Journal of the Computer Society. [CrossRef]
- Ismail, S.; Hassen, H.; Just, M.; Zantout, H. (2021) “A review of amplification-based distributed denial of service attacks and their mitigation”. Computers & Security, 109, article no:102380. [CrossRef]
- Javaid, M.; Haleem, A.; Singh, R.P.; Khan, S.; Suman, R. An extensive study on Internet of Behavior (IoB) enabled Healthcare-Systems: Features, facilitators, and challenges. BenchCouncil Transactions on Benchmarks, Standards and Evaluations 2022, 2, 100085. [Google Scholar] [CrossRef]
- Jayakumar, P.; Brohi, S.N.; Jhanjhi, N.Z. (2021). Artificial intelligence and military applications: Innovations, cybersecurity challenges & open research areas.
- Jhanjhi, N.Z.; Sahil Verma, M.N. Talib, and Gagandeep Kaur. “A canvass of 5G network slicing: Architecture and security concern”. IOP Conference Series: Materials Science and Engineering 2020, 993, 012060. [Google Scholar]
- Jin, Y.; Tomoishi, M.; Matsuura, S.; Kitaguchi, Y. (2018) “A secure container-based backup mechanism to survive destructive ransomware attacks”. 2018 International Conference on Computing, Networking and Communications (ICNC), pp. 1–6. [CrossRef]
- Kaspersky (2021) Avoiding a trojan virus: Keeping the gates closed, www.kaspersky.com. Available at: https://www.kaspersky.com/resource-center/preemptive-safety/avoiding-a-trojan-virus.
- Kaur, K.; et al. (2024) ‘Unveiling the core of IoT: comprehensive review on data security challenges and mitigation strategies’. Frontiers in Computer Science. [CrossRef]
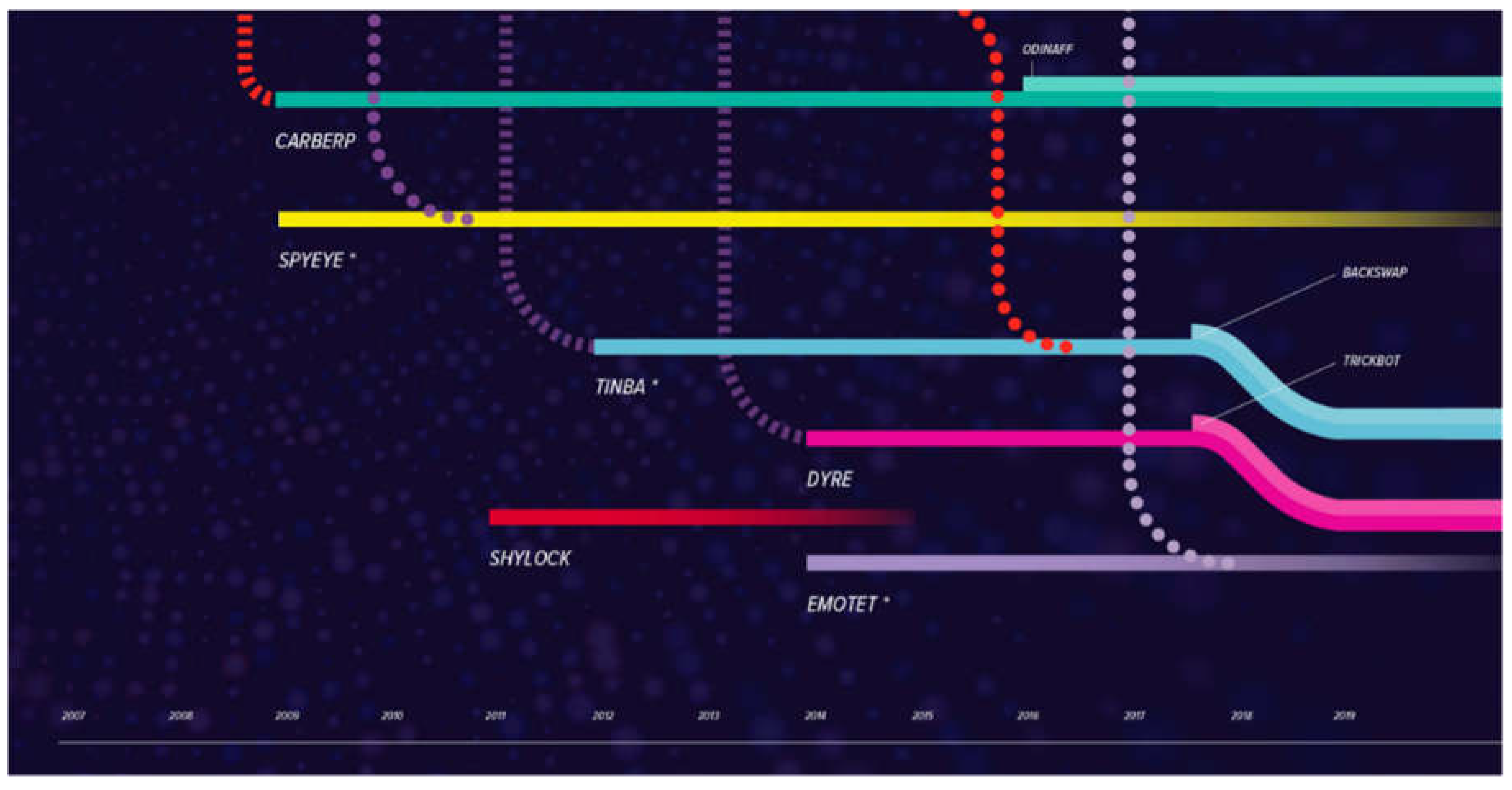
- Kessem, L. (2020) Banking trojans and ransomware—a treacherous matrimony bound to get worse, Security Intelligence. SecurityIntelligence. Available at: https://securityintelligence.com/posts/banking-trojans-and-ransomware-a-treacherous-matrimony-bound-to-get-worse/.
- Kizza, J.M. (2024) ‘System Intrusion Detection and Prevention’. in Texts in computer science, pp. 295–323. [CrossRef]
- Khairandish, M.O.; Sharma, M.; Jain, V.; Chatterjee, J.M.; Jhanjhi, N.Z. A hybrid CNN-SVM threshold segmentation approach for tumor detection and classification of MRI brain images. IRBM 2022, 43, 290–299. [Google Scholar] [CrossRef]
- Kok, S.H.; Abdullah, A.; Jhanjhi, N.Z.; Supramaniam, M. A review of intrusion detection system using machine learning approach. International Journal of Engineering Research and Technology 2019, 12, 8–15. [Google Scholar]
- Knapp, E.D.; Langill, J.T. (2011) Industrial Network Security: Securing critical infrastructure networks for smart grid, SCADA, and other industrial control systems. http://cds.cern.ch/record/1988553.
- Kumar, S.; Keshari, A.K. (2024) ‘An effective DDOS attack mitigation of IoT using Optimization-Based adaptive Security model’. Knowledge-Based Systems, p. 112052. [CrossRef]
- Kumar, S.; et al. ‘A comprehensive review of vulnerabilities and AI-enabled defense against DDoS attacks for securing cloud services’. Computer Science Review 2024, 53, 100661. [Google Scholar] [CrossRef]
- Learning Center. (n.d.). What does DDoS Mean? | Distributed Denial of Service Explained | Imperva. [online] Available at: https://www.imperva.com/learn/ddos/denial-of-service/#:~:text=DDoS%20meaning%3A%20What%20is%20DDoS.
- Ling, X.; et al. ‘Adversarial attacks against Windows PE malware detection: A survey of the state-of-the-art’. Computers & Security 2023, 128, 103134. [Google Scholar] [CrossRef]
- Lim, M.; Abdullah, A.; Jhanjhi, N.Z.; Khan, M.K.; Supramaniam, M. “Link prediction in time-evolving criminal network with deep reinforcement learning technique”. IEEE Access 2019, 7, 184797–184807. [Google Scholar] [CrossRef]
- Mairs, T. (2018) 3 mandatory email security best practices for the Financial Services Industry, SparkPost. Available at: https://www.sparkpost.com/blog/3-email-security-best-practices-financial-services-industry/.
- Merkebaiuly, M. (2024) ‘Overview of Distributed Denial of Service (DDoS) attack types and mitigation methods’. InterConf, (43(193)), pp. 494–508. [CrossRef]
- Micro, T. (ed.) (2018) Malware attack will reportedly cost Allentown, PA. US$1 million, Security News. Trend Micro. Available at: https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/malware-attack-will-reportedly-cost-allentown-pa-us-1-million.
- Ming, L.; Leau, Y.-B.; Xie, Y. (2024) ‘Distributed Denial of Service attack in HTTP/2: Review on security issues and future challenges’. IEEE Access, p. 1. [CrossRef]
- Mirre, A. (2021) “Protecting internet networks against DOS attacks”, digilib.k.utb.cz, pp. 8–47. Available at: https://digilib.k.utb.cz/bitstream/handle/10563/46175/mirre_2021_dp.pdf?sequence=-1 (Accessed: November 5, 2022).
- Mohiddin, S.K.; Midhunchakkaravarthy, D.; Hussain, M.A. ‘TSWA: a unique approach to overcome interest flooding attacks in the cloud using a combination of TSW and attack detection’. Multimedia Tools and Applications 2023, 83, 32673–32713. [Google Scholar] [CrossRef]
- Saleh, M.; Jhanjhi, N.; Abdullah, A.; Saher, R. “IoTES (A Machine learning model) Design dependent encryption selection for IoT devices”. 2022 24th International Conference on Advanced Communication Technology (ICACT), PyeongChang Kwangwoon_Do, Korea, Republic of, 2022, pp. 239–246. [CrossRef]
- Mott, G.; et al. (2024) ‘‘There was a bit of PTSD every time I walked through the office door’: Ransomware harms and the factors that influence the victim organization’s experience’. Journal of Cybersecurity, 10(1). [CrossRef]
- Nafea Alhammadi(2021) Researchgate.net. Available at: https://www.researchgate.net/publication/356786133_A_Review_of_the_Common_DDoS_Attack_Types_and_Protection_Approaches_Based_on_Artificial_Intelligence.
- Majeed, N.A.; Zaboon, K.H; Abdullah, A.A. (2021) ‘A Review of the Common DDoS Attack: Types and Protection Approaches Based on Artificial Intelligence’. Research Gate, pp. 08–14. [CrossRef]
- Nayak, T. (2019, June 3). The LockerGoga Ransomware Attack: A worst-case scenario for industrial operations. AXA XL. https://axaxl.com/fast-fast-forward/articles/the-lockergoga-ransomware-attack_a-worst-case-scenario-for-industrial-operations.
- Nayyar, A.; Gadhavi, L.; Zaman, N. (2021) ‘Machine learning in healthcare: review, opportunities and challenges’. in Elsevier eBooks, pp. 23–45. [CrossRef]
- Nicholson, P. (2018). 5 Most Famous DDoS Attacks | A10 Networks. [online] A10 Networks. Available at: https://www.a10networks.com/blog/5-most-famous-ddos-attacks/.
- Papez, N.; Shields, R. (2021) Ransomware countermeasures—mitigation strategies: Proofpoint US, Proofpoint. Available at: https://www.proofpoint.com/us/blog/security-awareness-training/countermeasures-ransomware (Accessed: November 6, 2022).
- Petcu, A.G. (2022) Emotet malware over the years: The history of an infamous Cyber-Threat, Heimdal Security Blog. Heimdal Security. Available at: https://heimdalsecurity.com/blog/emotet-malware-history/.
- Pillai, S.E.V.S.; Polimetla, K. (2024) ‘Mitigating DDoS Attacks using SDN-based Network Security Measures’. 2024 International Conference on Integrated Circuits and Communication Systems (ICICACS) [Preprint]. [CrossRef]
- Porter, J. (2020) Amazon says it mitigated the largest ddos attack ever recorded, The Verge. The Verge. Available at: https://www.theverge.com/2020/6/18/21295337/amazon-aws-biggest-ddos-attack-ever-2-3-tbps-shield-github-netscout-arbor.
- Ransomware: Facts threats countermeasures (2019), C.I.S. Available at: https://www.cisecurity.org/insights/blog/ransomware-facts-threats-and-countermeasures (Accessed: November 6, 2022).
- Ramanjot Mittal, U.; Wadhawan, A.; Singla, J.; Jhanjhi, N.Z.; Ghoniem, R.M.; Abdelmaboud, A. Plant disease detection and classification: A systematic literature review. Sensors 2023, 23, 4769. [Google Scholar] [CrossRef]
- Ransomware: Facts threats countermeasures (2019), C.I.S. Available at: https://www.cisecurity.org/insights/blog/ransomware-facts-threats-and-countermeasures.
- Reblaze (2022). What is DDoS? [online] Available at: https://www.reblaze.com/wiki/ddos/what-is-ddos/#:~:text=What%20is%20DDoS%3F.
- Riadi, I.; Sunardi, N.; Aprilliansyah, D. ‘Analysis of Anubis Trojan attack on Android banking application using mobile security labware’. International Journal of Safety and Security Engineering 2023, 13, 31–38. [Google Scholar] [CrossRef]
- Shahid, H.; et al. ‘Energy Optimised Security against Wormhole Attack in IoT-Based Wireless Sensor Networks’. Computers, Materials & Continua/Computers, Materials & Continua (Print) 2021, 68, 1967–1981. [Google Scholar] [CrossRef]
- Shete, V.; Gosavi, S. (2021) “Cloud Computing—Threats On Cloud Storage” Mahratta, 1(2), pp.1-15. Available at: http://www.mahratta.org/CurrIssue/2021_Sept_2/Vol%202_Paper19_Vaidehi_Cloud%20Computing%20-%20Threats%20On%20Cloud%20Storage.pdf (Accessed: November 6, 2022).
- Saeed, S.; Abdullah, A.; Jhanjhi, N.Z.; Naqvi, M.; Masud, M.; AlZain, M.A. Hybrid GrabCut Hidden Markov Model for Segmentation. Computers, Materials & Continua 2022, 72, 1. [Google Scholar]
- Saeed, S.; Haron, H.; Jhanjhi, N.Z.; Naqvi, M.; Alhumyani, H.A.; Masud, M. Improve correlation matrix of discrete fourier transformation technique for finding the missing values of mri images. Mathematical Biosciences and Engineering 2022, 19, 9039–9059. [Google Scholar] [CrossRef]
- Sangkaran; Theyvaa; Abdullah, A. ; Jhanjhi, N.Z. “Criminal community detection based on isomorphic subgraph analytics”. Open Computer Science 2020, 10, 164–174.
- Sangkaran; Theyvaa; Abdullah, A. ; JhanJhi, N.Z.; Supramaniam, M. “Survey on isomorphic graph algorithms for graph analytics”. International Journal of Computer Science and Network Security 2019, 19, 85–92.
- Shah, I.A.; Jhanjhi, N.Z.; Brohi, S.N. (2024). Use of AI-Based Drones in Smart Cities. In I. Shah & N. Jhanjhi (Eds.), Cybersecurity Issues and Challenges in the Drone Industry (pp. 362-380). IGI Global. [CrossRef]
- Shah, I.A.; Jhanjhi, N.Z.; Ujjan, R.M. (2024). Drone Technology in the Context of the Internet of Things. In I. Shah & N. Jhanjhi (Eds.), Cybersecurity Issues and Challenges in the Drone Industry (pp. 88-107). IGI Global. [CrossRef]
- Shah, I.A.; Jhanjhi, N.Z.; Ray, S.K. (2024). Artificial Intelligence Applications in the Context of the Security Framework for the Logistics Industry. In M. Ghonge, N. Pradeep, N. Jhanjhi, & P. Kulkarni (Eds.), Advances in Explainable AI Applications for Smart Cities (pp. 297-316). IGI Global. [CrossRef]
- Sindiramutty, S.R.; Jhanjhi, N.Z.; Tan, C.E.; Khan, N.A.; Gharib, A.H.; Yun, K.J. (2024). Applications of Blockchain Technology in Supply Chain Management. In N. Jhanjhi & I. Shah (Eds.), Cybersecurity Measures for Logistics Industry Framework (pp. 248-304). IGI Global. [CrossRef]
- Sood, M.; Angra, P.; Verma, S.; Jhanjhi, N.Z. (2022). Efficient feature grouping for IDS using clustering algorithms in detecting known/unknown attacks. In Information security handbook (pp. 103-116). CRC Press.
- Sindiramutty, S.R. (2024) ‘Autonomous Threat Hunting: a future paradigm for AI-Driven Threat intelligence’. arXiv (Cornell University) [Preprint]. [CrossRef]
- Sindiramutty, S.R.; Tan, C.E.; Lau, S.P.; et al. (2024) ‘Explainable AI for cybersecurity’. in Advances in computational intelligence and robotics book series, pp. 31–97. [CrossRef]
- Sindiramutty, S.R.; Tan, C.E.; Tee, W.J.; et al. (2024) ‘Modern smart cities and open research challenges and issues of explainable artificial intelligence’. in Advances in computational intelligence and robotics book series, pp. 389–424. [CrossRef]
- Sindiramutty, S.R.; Tee, W.J.; et al. (2024) ‘Explainable AI in healthcare application’. in Advances in computational intelligence and robotics book series, pp. 123–176. [CrossRef]
- Singhal, V.; et al. ‘Artificial Intelligence Enabled Road Vehicle-Train Collision Risk Assessment Framework for Unmanned railway level crossings’. IEEE Access 2020, 8, 113790–113806. [Google Scholar] [CrossRef]
- Tatipatri, N.; Arun, S.L. (2024) ‘A Comprehensive Review on Cyber-attacks in Power Systems: Impact Analysis, Detection and Cyber security’. IEEE Access, p. 1. [CrossRef]
- Usman, T.M.; Saheed, Y.K.; Ignace, D.; Nsang, A. Diabetic retinopathy detection using principal component analysis multi-label feature extraction and classification, International Journal of Cognitive Computing in Engineering, Volume 4, 2023,Pages 78-88, ISSN 2666-3074. [CrossRef]
- Tung, L. (2020) Microsoft: How One EMOTET infection took out this organization’s entire network, ZDNET. Available at: https://www.zdnet.com/article/microsoft-how-one-emotet-infection-took-out-this-organizations-entire-network/.
- Uddin, R.; Kumar, S.A.P.; Chamola, V. ‘Denial of service attacks in edge computing layers: Taxonomy, vulnerabilities, threats and solutions’. Ad Hoc Networks 2024, 152, 103322. [Google Scholar] [CrossRef]
- Varshney, G.; et al. ‘Anti-phishing: A comprehensive perspective’. Expert Systems With Applications 2024, 238, 122199. [Google Scholar] [CrossRef]
- Vasani, V.; et al. ‘Comprehensive analysis of advanced techniques and vital tools for detecting malware intrusion’. Electronics 2023, 12, 4299. [Google Scholar] [CrossRef]
- Vijayalakshmi, B.; Ramar, K.; Jhanjhi, N.Z.; Verma, S.; Kaliappan, M.; Vijayalakshmi, K.; Ghosh, U. An attention-based deep learning model for traffic flow prediction using spatiotemporal features towards sustainable smart city. International Journal of Communication Systems 2021, 34, e4609. [Google Scholar] [CrossRef]
- Waheed, A.; et al. (2024) ‘Zero-Day Exploits in Cybersecurity: Case Studies and Countermeasure’. Preprints [Preprint]. [CrossRef]
- Wen, B.O.T.; et al. (2023) ‘Detecting cyber threats with a Graph-Based NIDPS’. in Advances in logistics, operations, and management science book series, pp. 36–74. [CrossRef]
- What is Ryuk Ransomware? A Detailed Breakdown (2024). https://www.sentinelone.com/cybersecurity-101/threat-intelligence/ryuk-ransomware/.
- van Wieren, H.D. (2019) “Signature-based DDoS attack mitigation: Automated Generating Rules for extended berkeley packet filter and express data path, Signature-Based DDoS Attack Mitigation: Automated Generating Rules for Extended Berkeley Packet Filter and.
- Wisser, W. (2020) Lockergoga ransomware: How to decrypt files and remove virus, MySpyBot. Available at: https://myspybot.com/lockergoga-ransomware/#preventiontips (Accessed: November 6, 2022).
- Yadav, R.S.; Likhar, P. (2024) ‘Firewall: A Vital Constituent of Network Security’. in Information Technology Security, pp. 47–67. [CrossRef]
- Zaman, *!!! REPLACE !!!*; Noor, *!!! REPLACE !!!*; Abdullah, A.B. Zaman; Noor; Abdullah, A.B. “Position responsive routing protocol (prrp)”. In 13th International Conference on Advanced Communication Technology (ICACT2011), pp. 644–648. IEEE, 2011.
- Zhou, Z.; et al. ‘A statistical approach to secure health care services from DDoS attacks during COVID-19 pandemic’. Neural Computing and Applications 2021, 36, 1–14. [Google Scholar] [CrossRef] [PubMed]
- Zou, Y.; Fan, W.; Ma, Z. (2024) ‘Unveiling Vulnerabilities in Bitcoin’s Misbehavior-Score Mechanism: Attack and Defense’. ACM Library. [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



