Submitted:
10 September 2024
Posted:
10 September 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Literature Review
2.1. Digital Twin in Cyber Security
2.2. Co-simulation and Human Behavior Modelling
2.3. Comparing Solutions in Digital Twin and IDS Research
2.4. The Gap in Literature: Integrating Digital Twins and IDS for Smart Cities
2.5. Conclusion of the Literature Review
3. Proposed Solution
3.1. Overview of the Proposed Framework
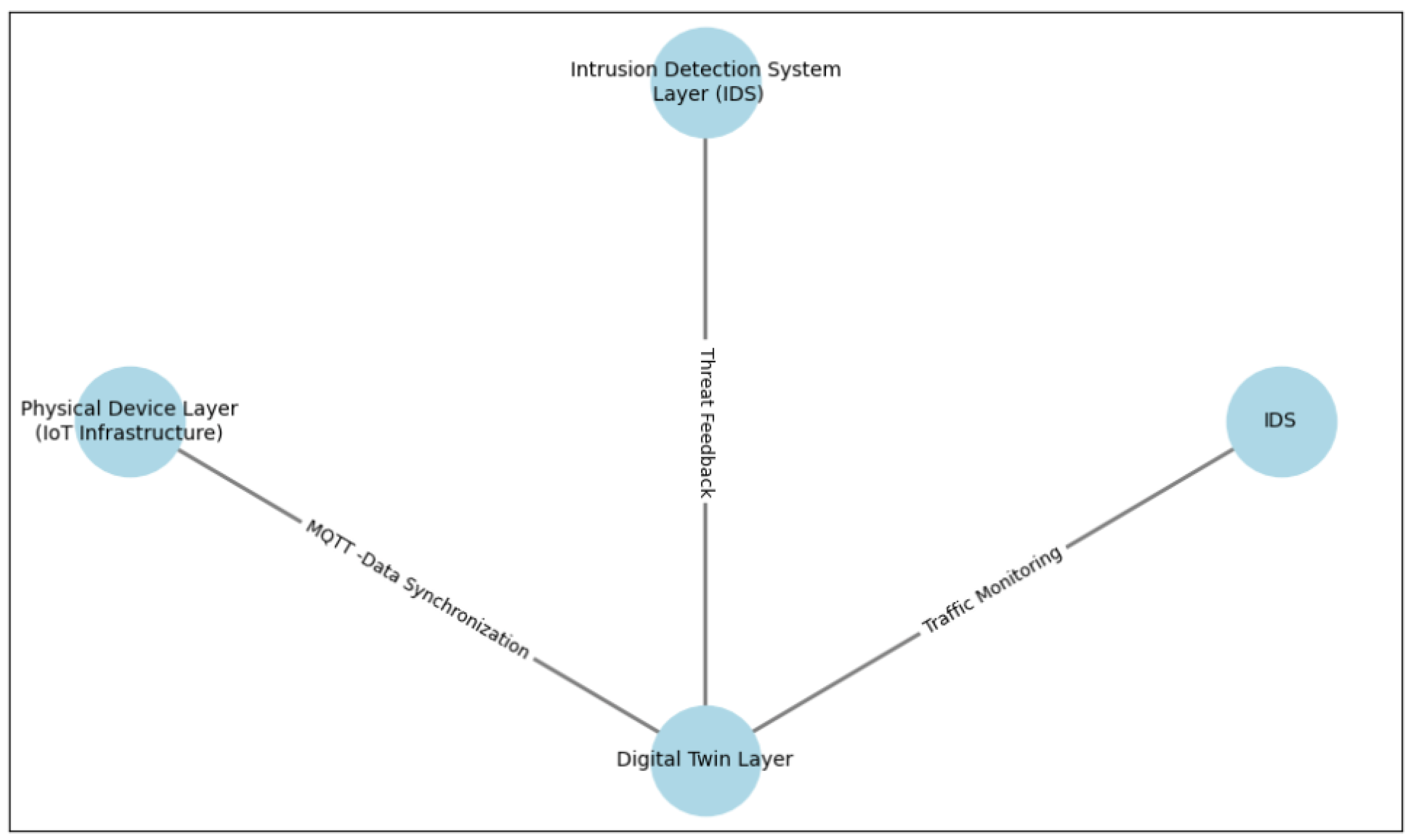
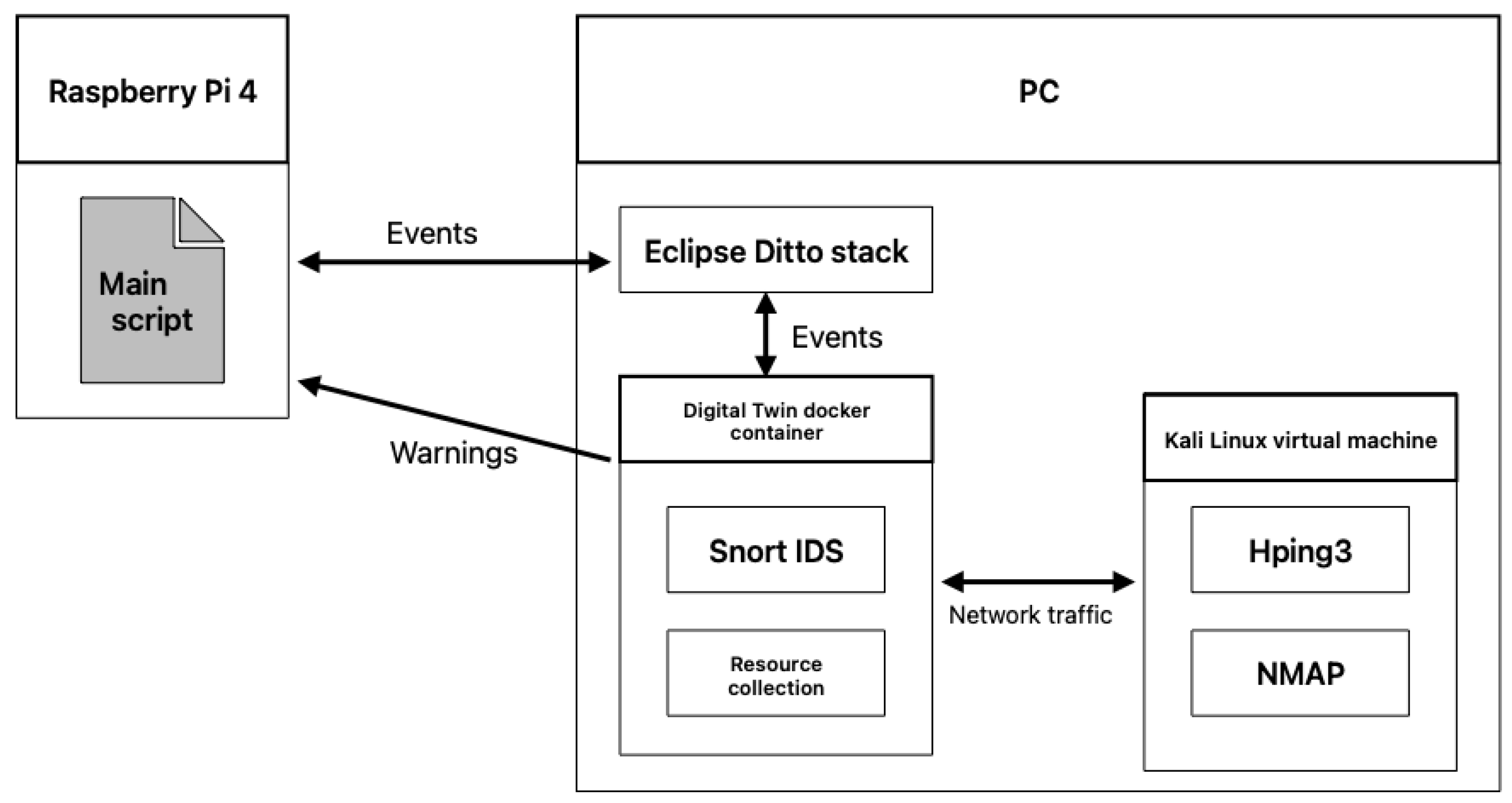
3.2. System Architecture
- Physical Device Layer (IoT Infrastructure): Represented by the physical smart city devices (e.g., sensors, cameras, actuators).
- Digital Twin Layer: The Digital Twin mirrors the physical device and interacts with the physical layer in real-time. It collects data, simulates device behavior, and provides insights on performance.
- Intrusion Detection System Layer (IDS): The IDS monitors the network traffic of the Digital Twin and physical devices, identifying potential threats like unauthorized access or suspicious patterns.
- These components are interconnected through communication protocols like MQTT, ensuring seamless synchronization between the physical device and its twin. The data collected by the IDS is analyzed in conjunction with the Digital Twin’s simulation to provide a comprehensive view of potential vulnerabilities.
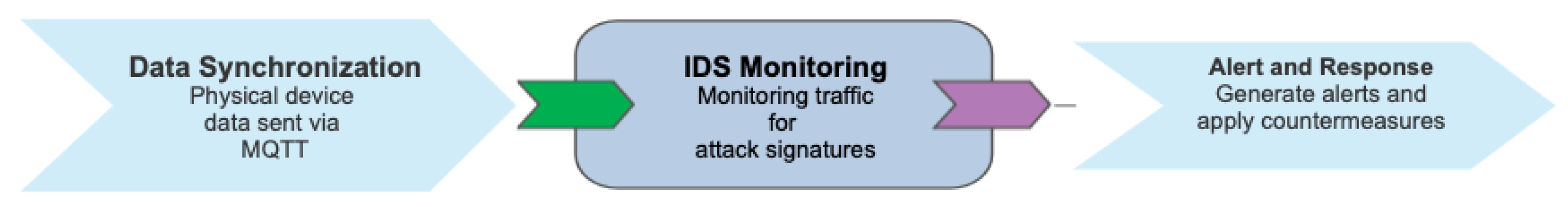
3.3. Attack Detection Workflow
- Data Synchronization: The physical device continuously sends data to the Digital Twin via MQTT. The Digital Twin simulates the device’s behavior and checks for anomalies based on historical data.
- IDS Monitoring: The IDS monitors network traffic and checks for known attack signatures (e.g., ICMP Flood, TCP Flood) or abnormal traffic patterns.
- Alert and Response: When an attack is detected, the IDS generates alerts, which are logged for analysis. Based on predefined security policies, automatic countermeasures can be taken, such as blocking suspicious traffic or isolating the affected device.
3.4. Hardware and Software Setup
3.4.1. Hardware Setup
- PC: A desktop computer running Eclipse Ditto (Digital Twin platform), a Digital Twin Docker container, and a Kali Linux virtual machine.
- Raspberry Pi (Pi): This device represents the physical IoT device within the smart city infrastructure.
- Kali Linux VM: A virtual machine used to perform penetration testing and launch cyberattacks (e.g., ICMP, TCP, HTTP floods, NMAP scans) against the Digital Twin to evaluate its resilience.
3.4.2. Software Setup
- Eclipse Ditto: A platform for creating Digital Twins. It is deployed in a Docker container for easy configuration and scalability.
- MQTT Protocol: Facilitates real-time communication between the physical device and the Digital Twin.
- Snort: A lightweight IDS that monitors network traffic and detects suspicious behavior.
- Python Scripts: Custom scripts for creating, managing, and synchronizing Digital Twins, as well as monitoring resource usage (CPU, memory, network) during attacks. All scripts can be found on the Gitlab repository 1
3.5. Use Cases and Attack Scenarios
- ICMP Flood: Overloads the device’s network with excessive ICMP requests.
- TCP Flood: Targets the TCP handshake process, leading to denial-of-service.
- HTTP Flood: Attacks the web server hosted on the IoT device or its Digital Twin.
- NMAP Scans: Scans for open ports and network vulnerabilities.
- The impact of each attack on the CPU and memory usage of the Docker container running the Digital Twin will be monitored, and the effectiveness of Snort in detecting these attacks will be analyzed.
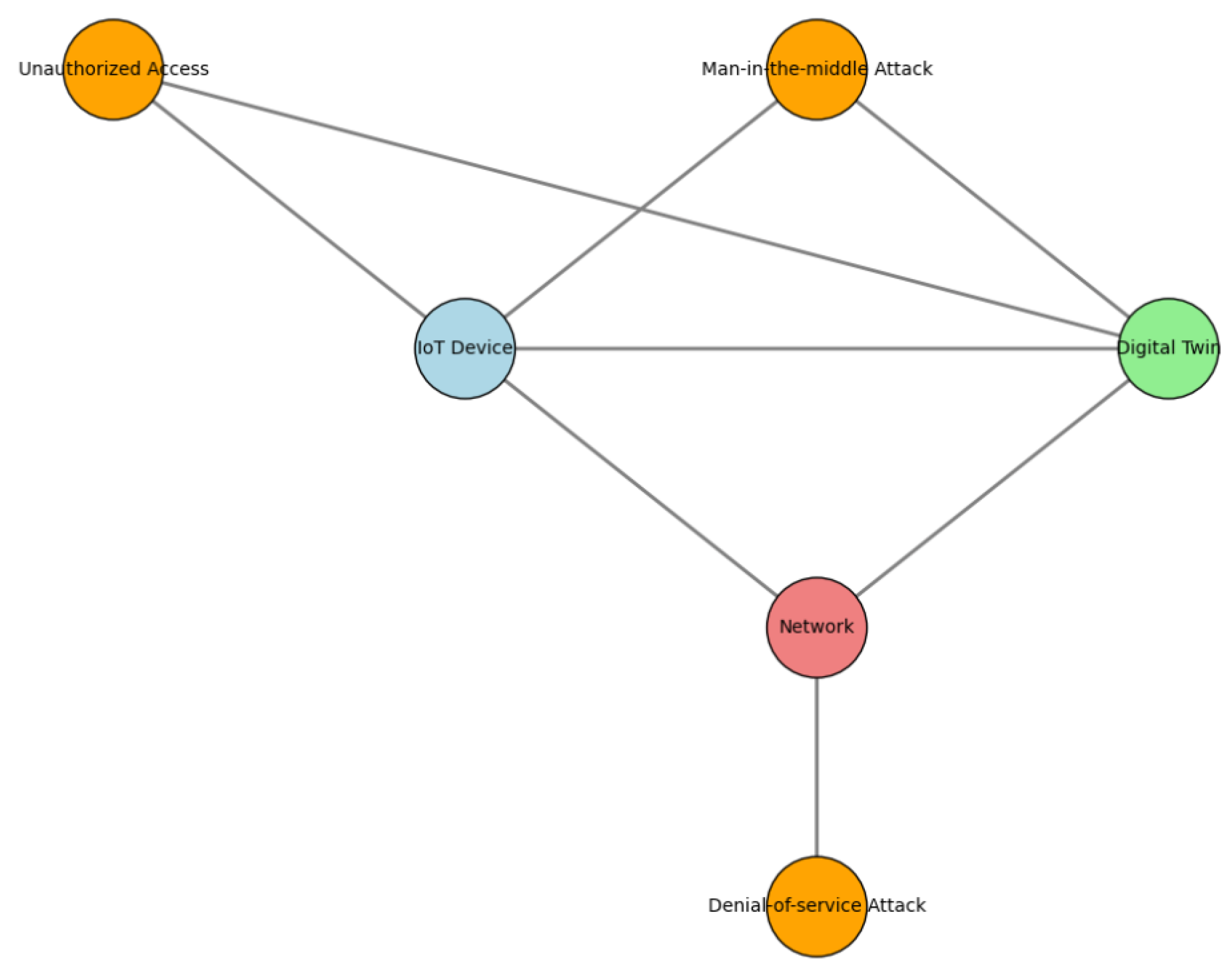
3.6. Threat Modeling and Security Analysis
- Man-in-the-middle attacks: Interception of communications between the Digital Twin and the physical device.
- Denial-of-service attacks: Flooding the network to disrupt the Digital Twin’s real-time functionality.
- Unauthorized access: Attempts to exploit vulnerabilities in the IoT devices or Digital Twins.
3.6.1. Formal Analysis of Threats
- Description: This attack targets the communication between the IoT device and the Digital Twin, potentially intercepting and altering data.
- Impact: Data manipulation or unauthorized control of devices can occur, leading to compromised system integrity.
- Countermeasure: Implement encrypted communication channels (e.g., TLS/SSL) and strong mutual authentication to mitigate this threat.
- Description: Attackers flood the network with excessive traffic, overwhelming system resources.
- Impact: Disruptions in real-time functionalities of the Digital Twin and delays in processing critical data.
- Countermeasure: Utilize rate-limiting, traffic filtering mechanisms, and an Intrusion Detection System (IDS) to detect and mitigate abnormal traffic patterns.
- Description: Exploiting vulnerabilities in IoT devices or the Digital Twin to gain unauthorized access.
- Impact: Potential system manipulation, sensitive data theft, or malicious activities.
- Countermeasure: Implement strong access control mechanisms, multi-factor authentication, and regular patching of vulnerabilities.
4. Results
4.1. CPU, Memory, and Network Utilization
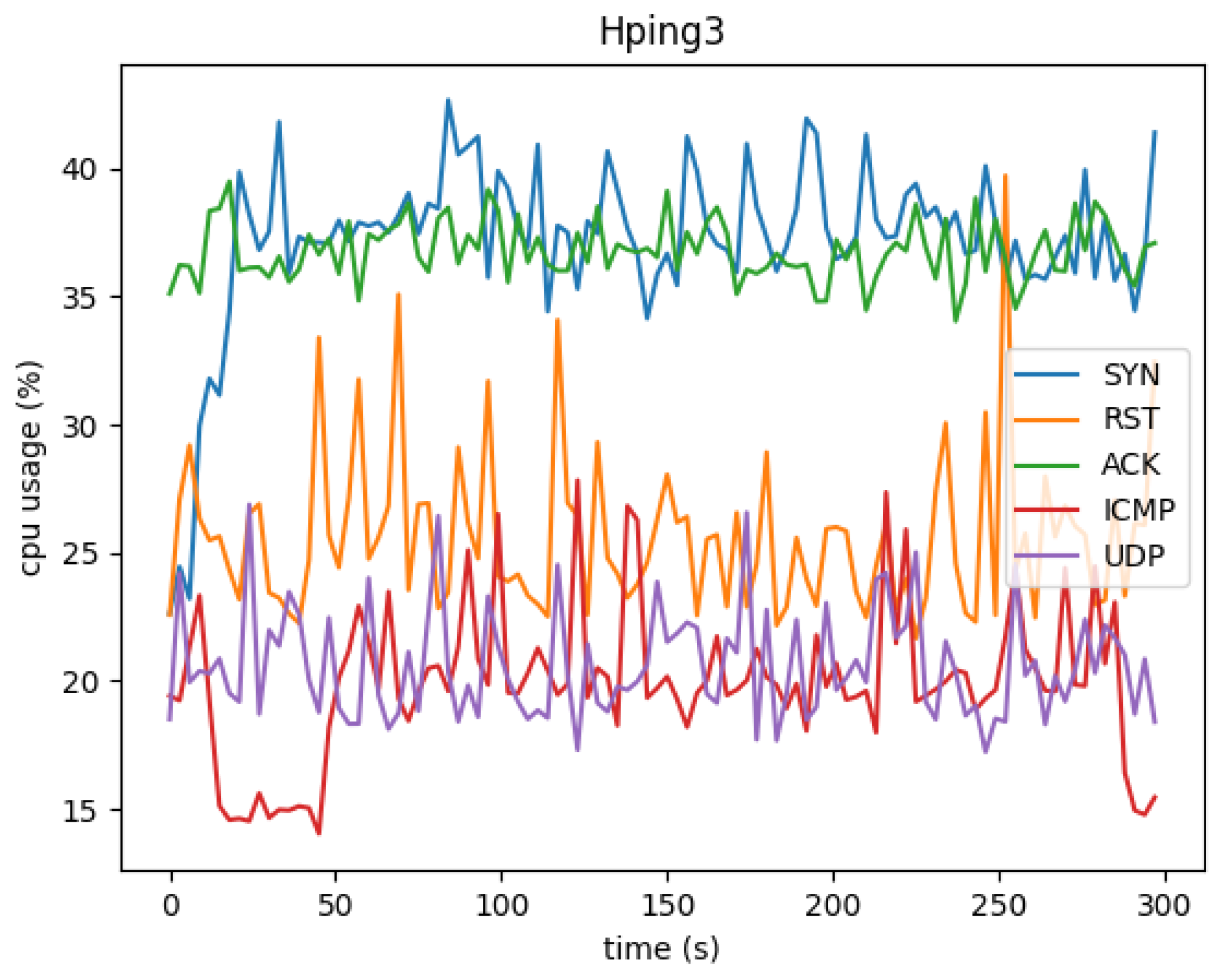
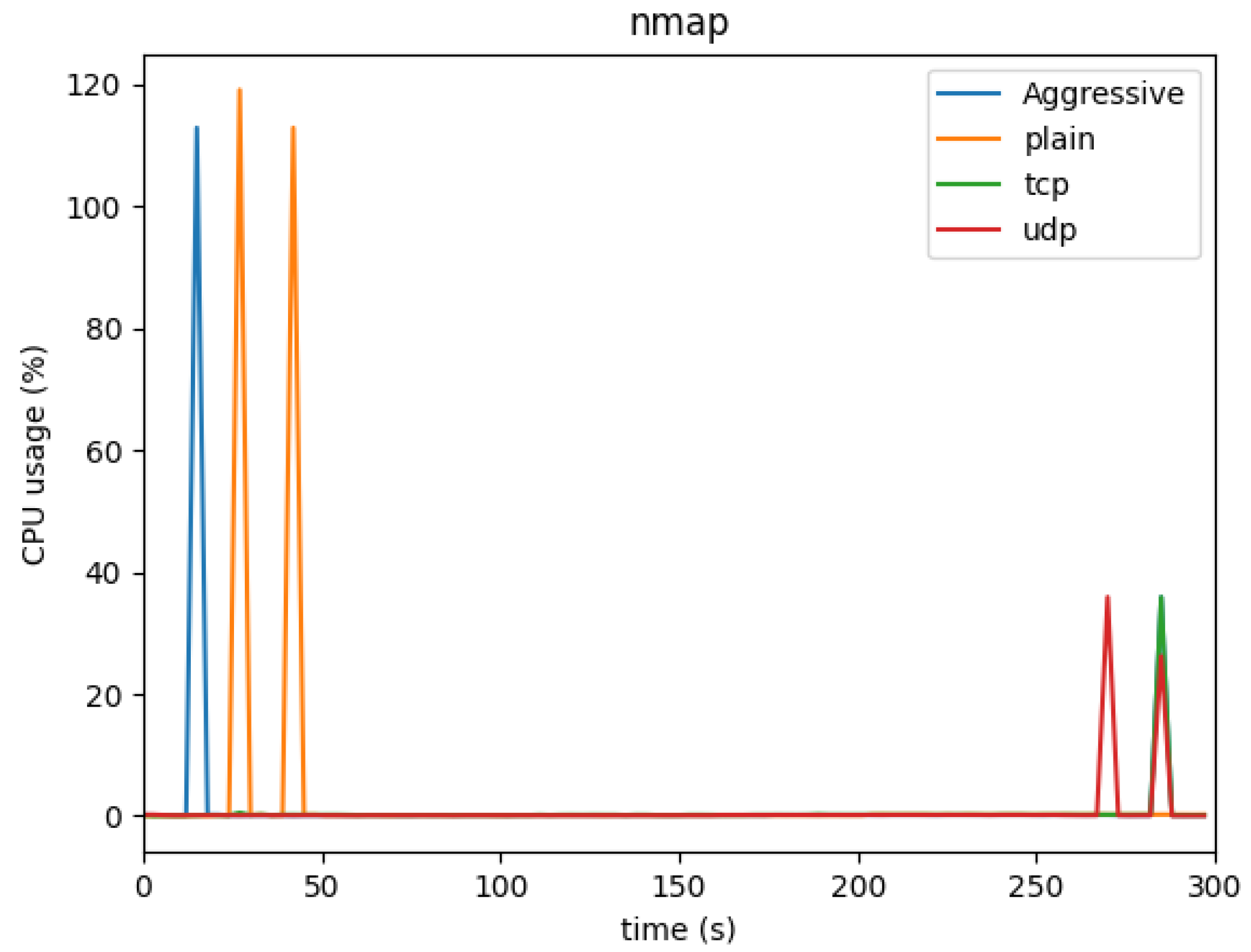
4.1.1. CPU Usage
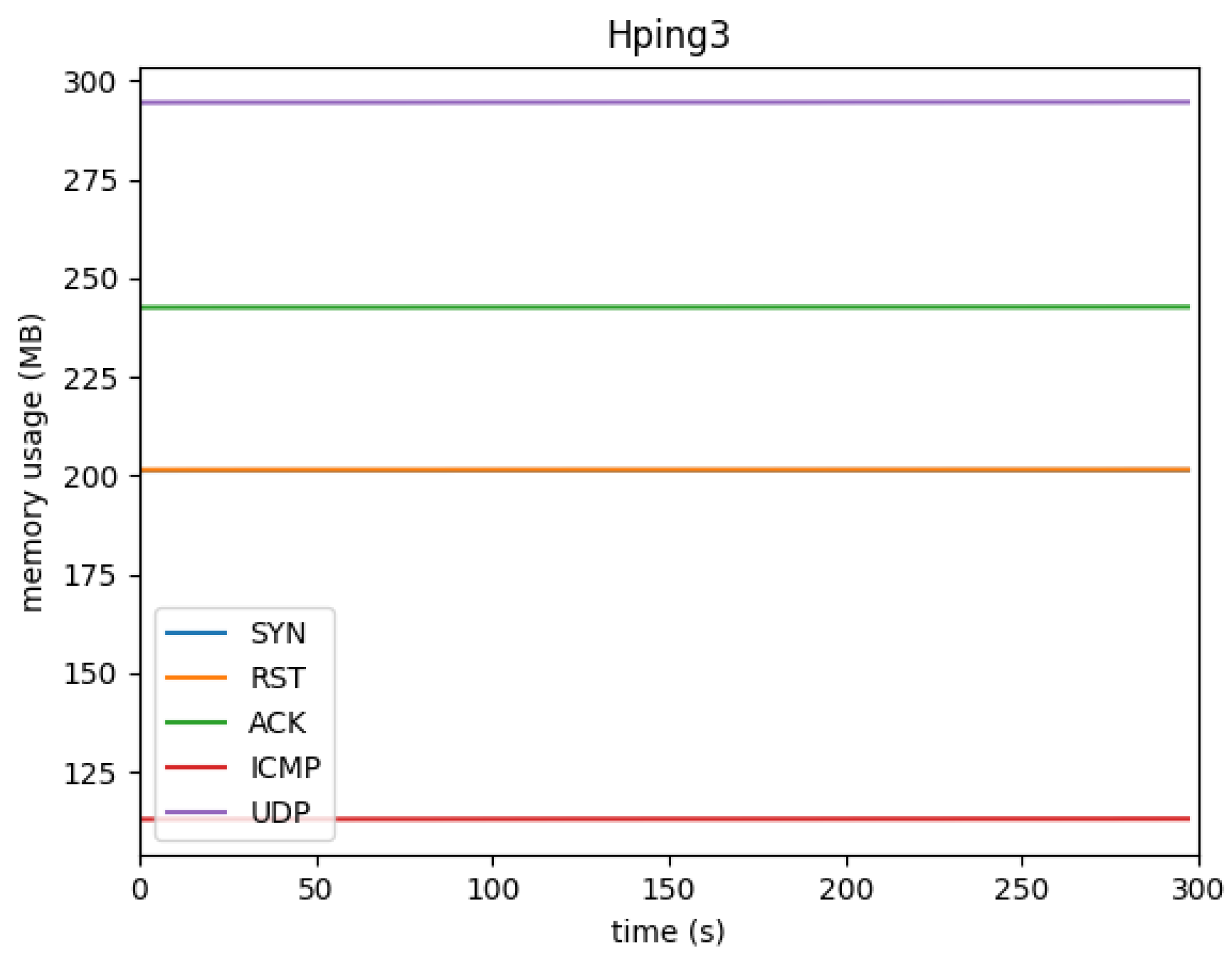
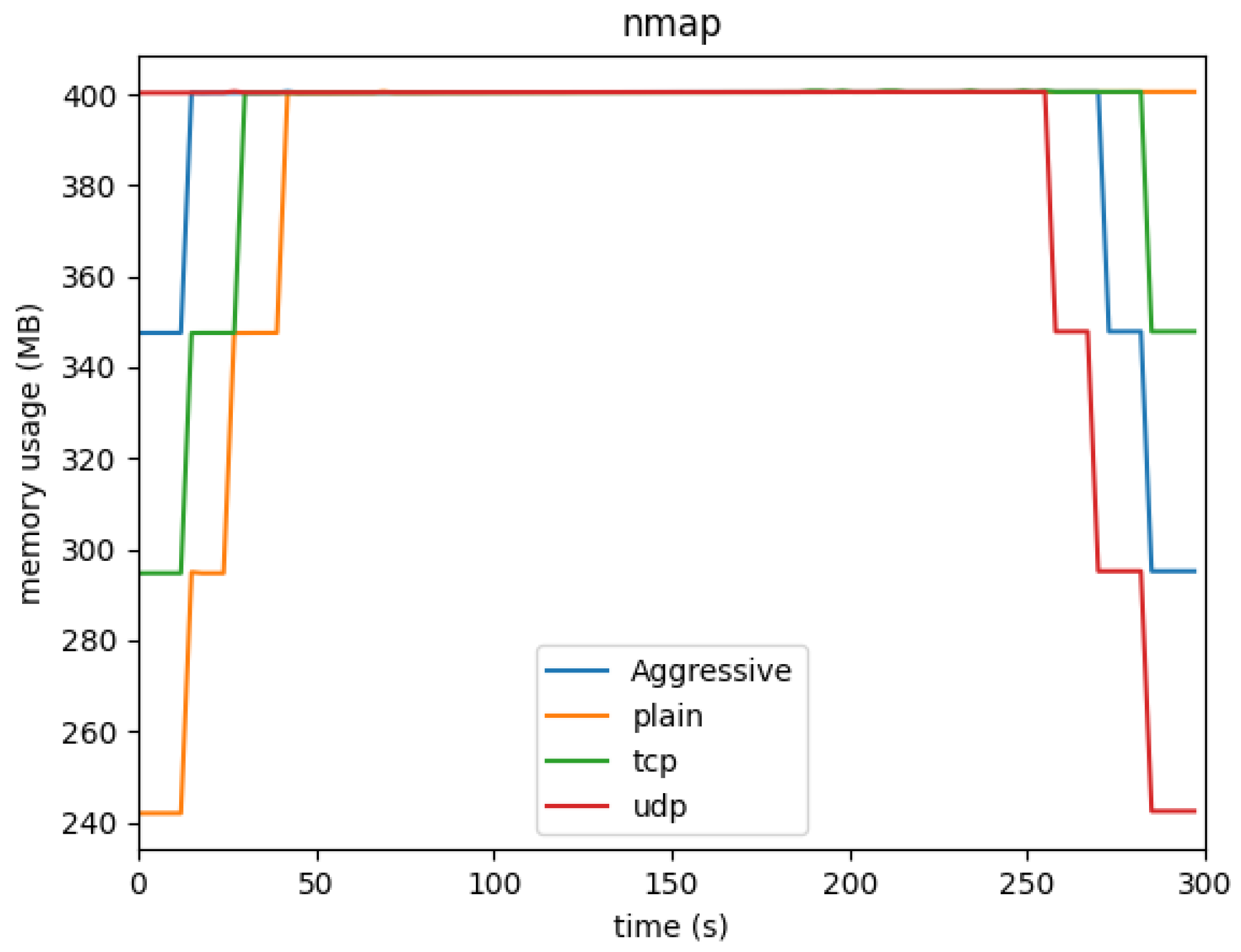
4.1.2. Memory Usage
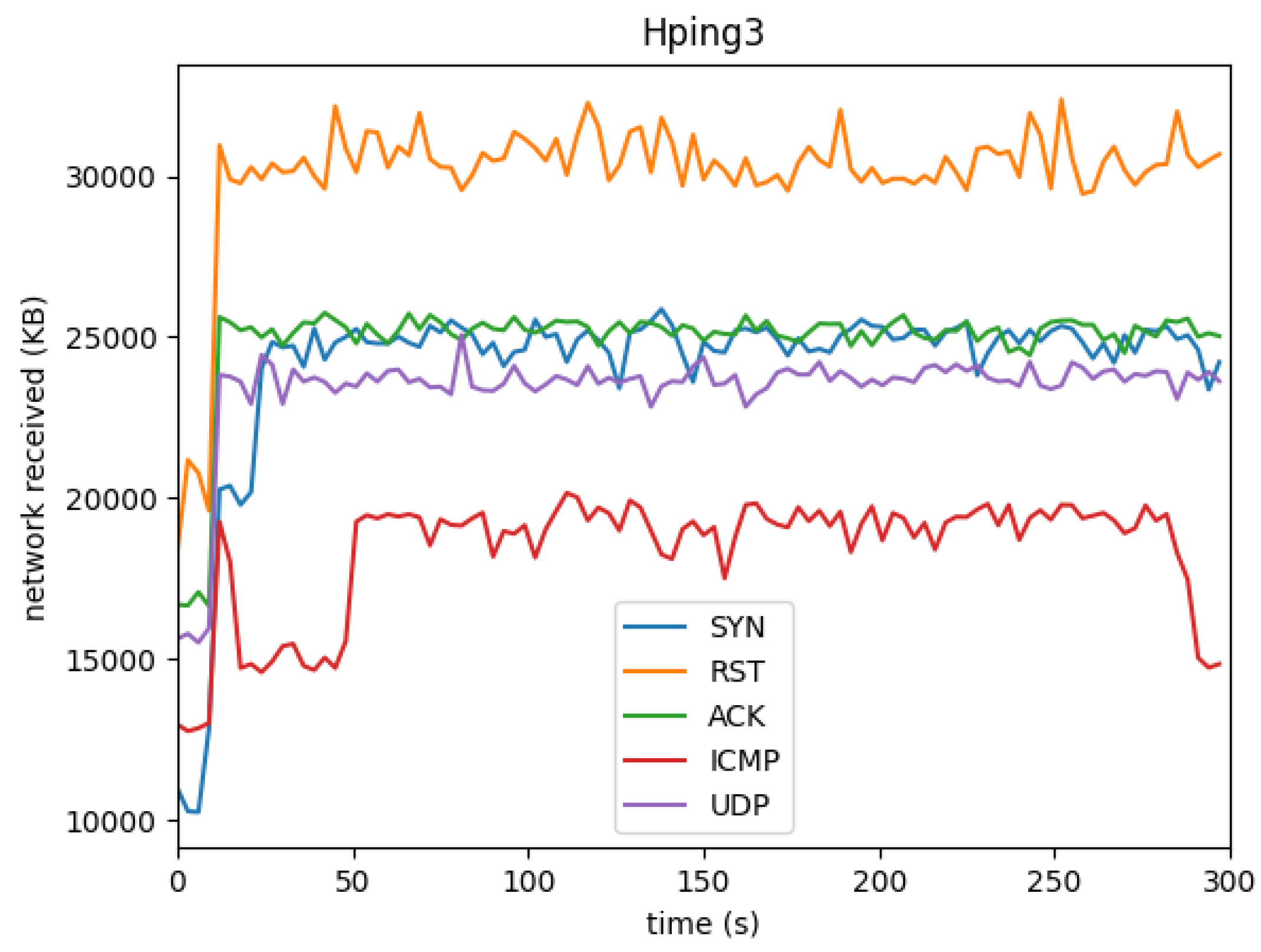
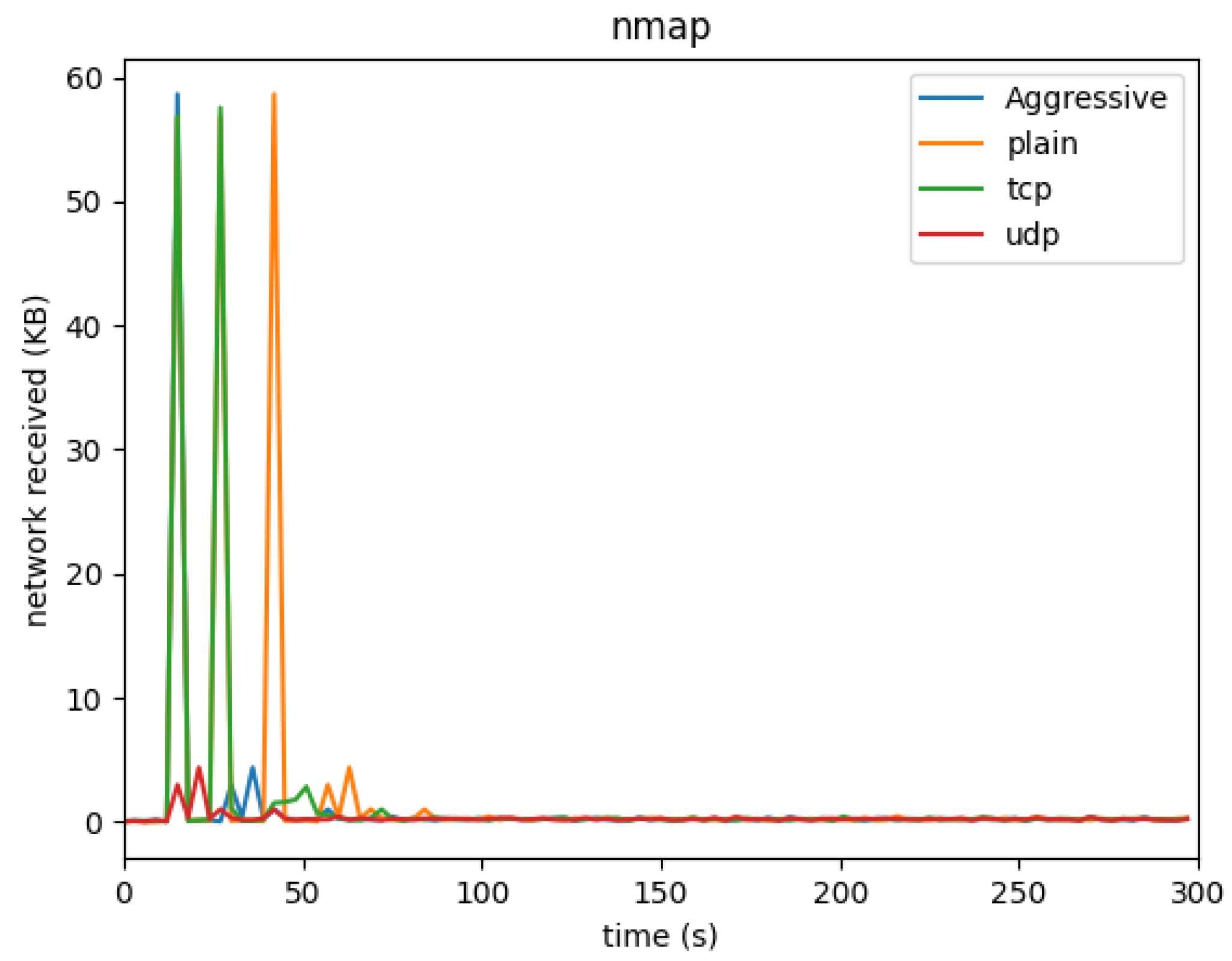
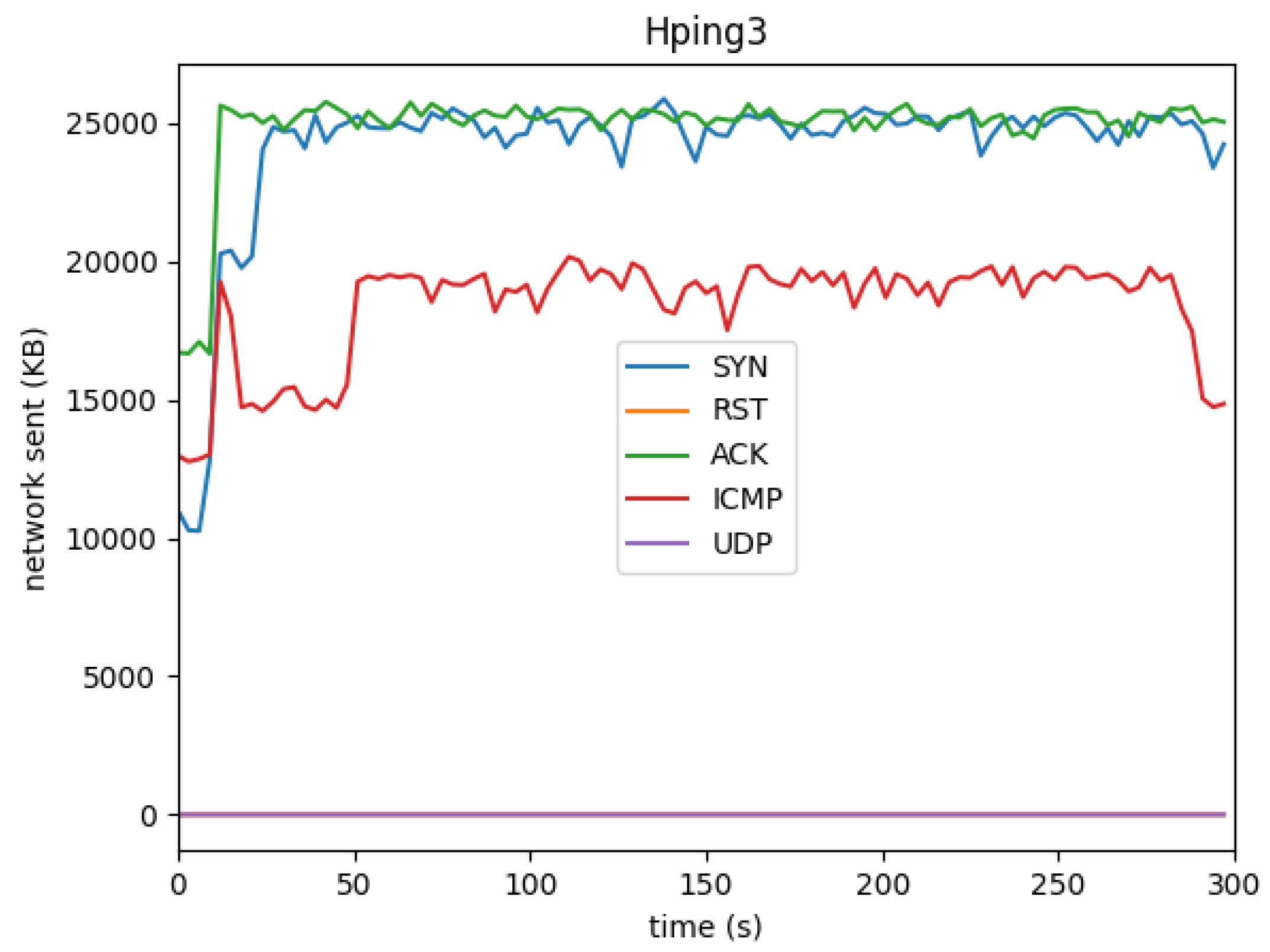
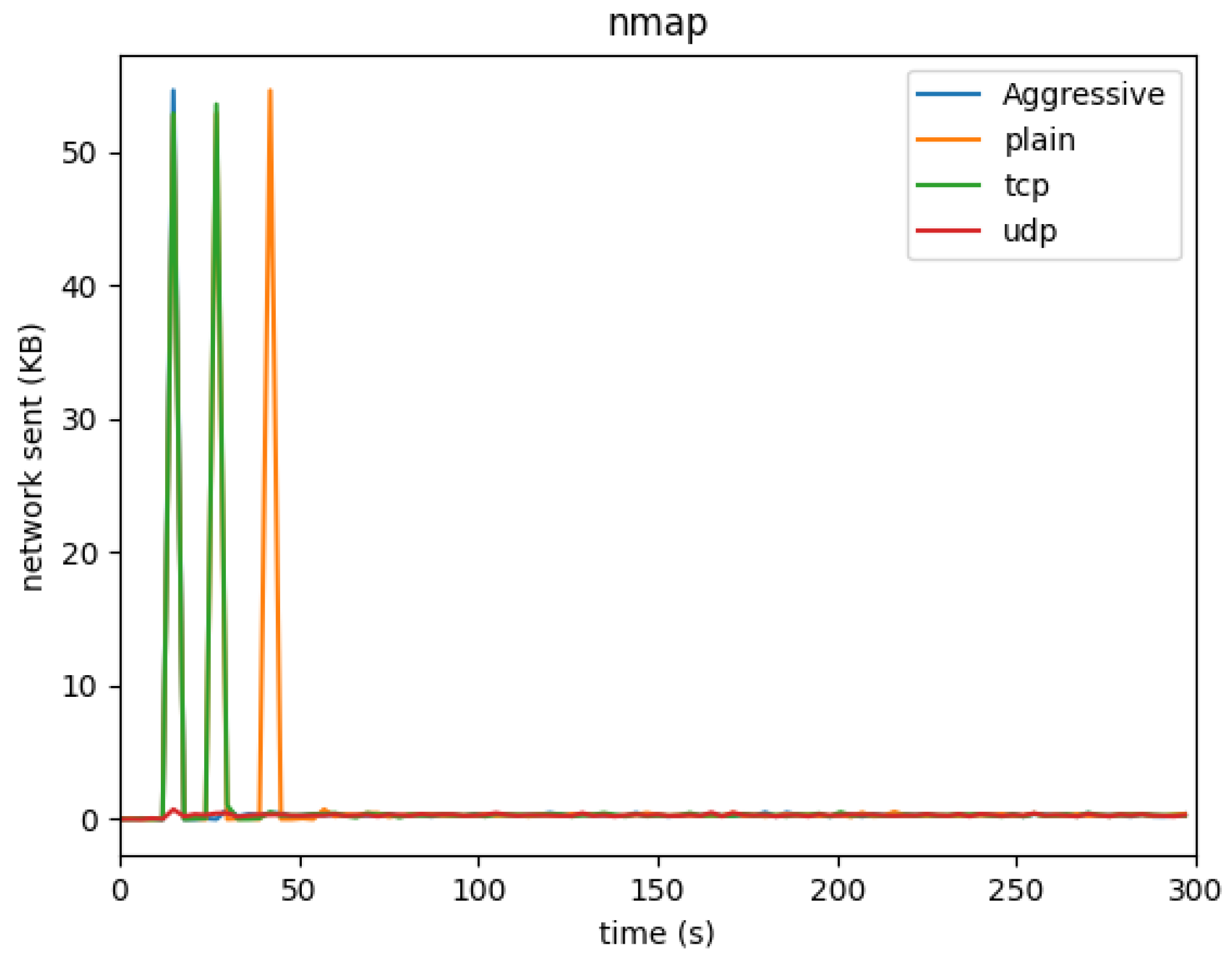
4.1.3. Network Usage
4.2. Attack Detection
5. Discussion
5.1. CPU Usage Insights
5.2. Memory Usage Insights
5.3. Network Traffic Insights
5.4. Snort’s Detection Capabilities
5.5. Novelty of the Work
- Resource Monitoring in Real-Time Attacks: Our work uniquely combines resource monitoring (CPU, memory, and network) with IDS alert generation, providing a comprehensive view of how attacks impact both system performance and security. Existing research often focuses on either system performance or IDS detection separately, but our approach integrates both, offering deeper insights into the trade-offs between security and performance.
- Identifying Vulnerabilities Under Different Attack Types: The results showcase how different types of attacks (flooding, reconnaissance, and stealthy scans) affect system resources in distinct ways. For example, while SYN and ACK floods consume more CPU, NMAP attacks place a heavier load on memory. These nuanced findings are valuable for designing systems that can better withstand a variety of attack types by understanding their specific impacts on system resources.
- Enhanced Detection with Digital Twin Coupling: y coupling the Digital Twin with Snort, we were able to simulate real-world attacks and monitor the behavior of a cyber-physical system in real-time. This provides a unique vantage point for security testing, enabling a more realistic and accurate assessment of system vulnerabilities compared to purely virtual environments. Our methodology allows researchers to assess how physical devices would react to cyberattacks, which is not typically possible in traditional IDS research.
6. Conclusion
6.1. Successes and Key Insights
- Detection of Flood Attacks: The IDS successfully detected the Hping3 SYN, ACK, RST, ICMP, and UDP flood attacks, consistently generating 102 alerts for most flood types. This demonstrates that Snort, when correctly configured, can accurately detect high-volume, sustained attack traffic targeting the Digital Twin. This verification is crucial for enhancing the security of IoT devices and cyber-physical systems that rely on digital twinning for simulation and monitoring purposes. Additionally, the ability of the IDS to respond in real-time provides an essential layer of defense in operational environments.
- Challenges with NMAP Scan Detection: One of the notable challenges was the detection of NMAP reconnaissance scans. Despite NMAP’s ability to rapidly gather information about the target device, Snort was unable to trigger a significant number of alerts, especially for the UDP-based NMAP scan. This finding underscores the necessity of improving IDS configurations to detect stealthy scans, which often precede more significant attacks. Future research must delve deeper into fine-tuning IDS rules or incorporating machine learning techniques to better detect these reconnaissance efforts.
- System Resource Usage: Our study also revealed valuable insights into the impact of these attacks on system resources. While SYN and ACK floods caused higher CPU utilization, NMAP scans spiked CPU usage briefly but left an unexpectedly high memory footprint that persisted well after the scan ended. This indicates that certain types of attacks, particularly short-duration scans, can still leave lingering effects on system performance, which may be leveraged by attackers for sustained degradation or system exhaustion. Future work can focus on mitigating these side effects, ensuring that systems recover their resources efficiently post-attack.
- Digital Twin-IDS Integration: The coupling of the Digital Twin with Snort proved to be a significant innovation, enabling the simulation of realistic attack scenarios and the monitoring of system behavior in real-time. This integration represents a valuable tool for cybersecurity testing and defense in the IoT domain. By twinning physical devices, administrators can observe potential vulnerabilities, gauge the impact of different attack types, and adjust their defenses accordingly.
6.2. Novelty and Contribution of the Work
6.3. Future Directions
- Real-World Validation: The next logical step is to verify the results of this research in a real-world scenario, where the Digital Twin is not just a software abstraction but is connected to a physical device with actual, operational functionality. This will help determine the feasibility and reliability of the proposed approach in dynamic environments, such as manufacturing systems, smart grids, or autonomous vehicles.
- Automated Defense Mechanisms: Another promising direction for future work is to explore the possibility of automating defensive actions based on the IDS alerts generated in the Digital Twin. For example, if an attack is detected in the virtual model, automated responses could be triggered to defend the physical device, such as blocking malicious IP addresses, throttling network traffic, or initiating failover procedures. The effectiveness and security implications of such automated responses would need careful consideration and testing.
- Extending Attack Scenarios: While this research focused on Hping3 flood attacks and NMAP scans, it is important to broaden the scope to include more complex attack vectors such as ARP spoofing, SSH brute-force attacks, man-in-the-middle (MITM) attacks, and other sophisticated threats. By extending the range of attack simulations, the Digital Twin-IDS framework can be tested against a more diverse set of threats, thereby enhancing its robustness and generalizability to different network environments.
- Optimizing IDS Performance: Finally, optimizing the configuration of Snort (or other IDS systems) to improve its detection capabilities, especially for stealthy attacks like NMAP scans, remains a critical area for future research. Additionally, integrating more advanced machine learning or anomaly detection algorithms could significantly boost the IDS’s ability to detect zero-day attacks or previously unknown vulnerabilities in the Digital Twin or physical device.
- In conclusion, the coupling of an Intrusion Detection System with a Digital Twin offers a novel and promising approach to enhancing the cybersecurity of physical devices. Our results demonstrate that this integration can effectively detect common network attacks, provide real-time performance monitoring, and offer new insights into how different attack types impact system resources. The flexibility and potential of this approach make it a valuable tool for both security researchers and practitioners working to safeguard cyber-physical systems in today’s increasingly connected world. As cyber threats continue to evolve, so too must the defensive techniques employed, and this research lays the groundwork for future advancements in this critical area.
Funding
Conflicts of Interest
Abbreviations
| IoT | Internet of Things |
| AI | Artificial Intelligence |
| DT | Digital Twin |
| IDS | ntrusion Detection System |
| NMAP | Network Mapper |
| TCP | Transmission Contorl Protocol |
| ICMP | Internet Control Message Protocol |
| MQTT | Message Queuing Telemetry Transport |
| HTTP | Hypertext Transfer Protocol |
| CPU | Central Processing Unit |
References
- Verhulsdonck, G.; Weible, J.L.; Helser, S.; Hajduk, N. Smart cities, playable cities, and cybersecurity: A systematic review. International Journal of Human–Computer Interaction 2023, 39, 378–390. [CrossRef]
- Allam, Z.; Dhunny, Z.A. On big data, artificial intelligence and smart cities. Cities 2019, 89, 80–91. [CrossRef]
- El-Hajj, M.; Fadlallah, A.; Chamoun, M.; Serhrouchni, A. A survey of internet of things (IoT) authentication schemes. Sensors 2019, 19, 1141. [CrossRef]
- Appio, F.P.; Lima, M.; Paroutis, S. Understanding Smart Cities: Innovation ecosystems, technological advancements, and societal challenges. Technological Forecasting and Social Change 2019, 142, 1–14. [CrossRef]
- Silva, B.N.; Khan, M.; Han, K. Towards sustainable smart cities: A review of trends, architectures, components, and open challenges in smart cities. Sustainable cities and society 2018, 38, 697–713. [CrossRef]
- Itäpelto, T. Digital Twin Enhanced Critical Infrastructure Life Cycle Security. 2023 IEEE Smart World Congress (SWC). IEEE, 2023, pp. 1–3.
- van der Wal, E.W.; El-Hajj, M. Securing networks of iot devices with digital twins and automated adversary emulation. 2022 26th International Computer Science and Engineering Conference (ICSEC). IEEE, 2022, pp. 241–246. [CrossRef]
- El-Hajj, M.; Fadlallah, A.; Chamoun, M.; Serhrouchni, A. Secure PUF: Physically unclonable function based on arbiter with enhanced resistance against machine learning (ML) attacks. 2020.
- Garalov, T.; Elhajj, M. Enhancing IoT Security: Design and Evaluation of a Raspberry Pi-Based Intrusion Detection System. 2023 International Symposium on Networks, Computers and Communications (ISNCC). IEEE, 2023, pp. 1–7. [CrossRef]
- El-Hajj, M.; Itäpelto, T.; Gebremariam, T. Systematic literature review: Digital twins’ role in enhancing security for Industry 4.0 applications. Security and Privacy, p. e396. [CrossRef]
- Eckhart, M.; Ekelhart, A. Towards Security-Aware Virtual Environments for Digital Twins. Proceedings of the 4th ACM Workshop on Cyber-Physical System Security; Association for Computing Machinery: New York, NY, USA, 2018; CPSS ’18, p. 61–72. [CrossRef]
- El-hajj, M.; Hahn, F. Security Aspects of Digital Twins in IoT. 9th International Conference on Information Systems Security and Privacy, ICISSP 2023, 2023. [CrossRef]
- El-Hajj, M.; Gebremariam, T.H. Enhancing Resilience in Digital Twins: ASCON-Based Security Solutions for Industry 4.0. Network 2024, 4, 260–294. [CrossRef]
- Suhail, S.; Hussain, R.; Jurdak, R.; Oracevic, A.; Salah, K.; Hong, C.S.; Matulevičius, R. Blockchain-based digital twins: research trends, issues, and future challenges. ACM Computing Surveys (CSUR) 2022, 54, 1–34. [CrossRef]
- Empl, P.; Hager, H.; Pernul, G. Digital Twins for IoT Security Management. IFIP Annual Conference on Data and Applications Security and Privacy. Springer, 2023, pp. 141–149. [CrossRef]
- Damjanovic-Behrendt, V. A digital twin-based privacy enhancement mechanism for the automotive industry. 2018 International Conference on Intelligent Systems (IS). IEEE, 2018, pp. 272–279. [CrossRef]
- Bécue, A.; Maia, E.; Feeken, L.; Borchers, P.; Praça, I. A new concept of digital twin supporting optimization and resilience of factories of the future. Applied Sciences 2020, 10, 4482. [CrossRef]
- Sellitto, G.P.; Aranha, H.; Masi, M.; Pavleska, T. Enabling a zero trust architecture in smart grids through a digital twin. Dependable Computing-EDCC 2021 Workshops: DREAMS, DSOGRI, SERENE 2021, Munich, Germany, September 13, 2021, Proceedings 17. Springer, 2021, pp. 73–81. [CrossRef]
| Research name | Cyber security use of DT | Solution | Real-time Capability | IDS Integration | Pros and Cons |
| Suhail et al. (2022) [14] | monitoring, analyzing | secure communication layer | No | No | Simple, secure communication but lacks real-time protection |
| Empl and Pernul (2023) [15] | monitoring, analyzing, predicting | security analytics model | Yes | No | Predictive but lacks direct IoT security |
| Eckhart and Ekelhart (2018) [11] | monitoring | framework | No | No | Comprehensive but manual implementation needed |
| Damjanovic-Behrendt (2018) [16] | privacy enhancement | development tool for privacy | No | No | Strong privacy mechanisms but lacks focus on cyber attacks |
| Bécue et al. (2020) [17] | monitoring, simulating | co-simulation methodology | Yes | No | Simulates behavior but lacks IDS support |
| Sellitto et al. (2021) [18] | analyzing, testing, modelling | methodology for threat modelling | Yes | No | Detailed simulations but lacks real-time integration |
| Device | Purpose | Description |
| PC | Host for DT and IDS | Running Eclipse Ditto, Docker container, and IDS |
| Raspberry Pi | Physical IoT device | Simulates smart city infrastructure device |
| Kali Linux VM | Attack simulation | Performs attacks (ICMP, TCP, HTTP floods, etc.) |
| Software | Purpose | Platform |
| Eclipse Ditto | Digital Twin management and simulation | Docker |
| Snort | Intrusion detection and alert generation | Linux |
| Python Scripts | Synchronizing DT, logging data, initiating attacks | PC, Raspberry Pi |
| MQTT | Real-time communication | Linux |
| Attack Type | CPU Usage Increase (%) | Memory Usage Increase (%) | Detection Rate |
| ICMP Flood | 25% | 30% | 100% |
| TCP Flood | 15% | 20% | 95% |
| HTTP Flood | 35% | 40% | 85% |
| NMAP Scan | 5% | 10% | 100% |
| Attack executed | Number of alerts fired by Snort |
|---|---|
| Hping3 ACK | 102 |
| Hping3 SYN | 102 |
| Hping3 RST | 102 |
| Hping3 ICMP | 204 |
| Hping3 UDP | 102 |
| Nmap | 2 |
| Nmap aggressive | 1 |
| Nmap TCP | 1 |
| Nmap UDP | 0 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




