Submitted:
04 September 2024
Posted:
05 September 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Importance Of Cyber Security
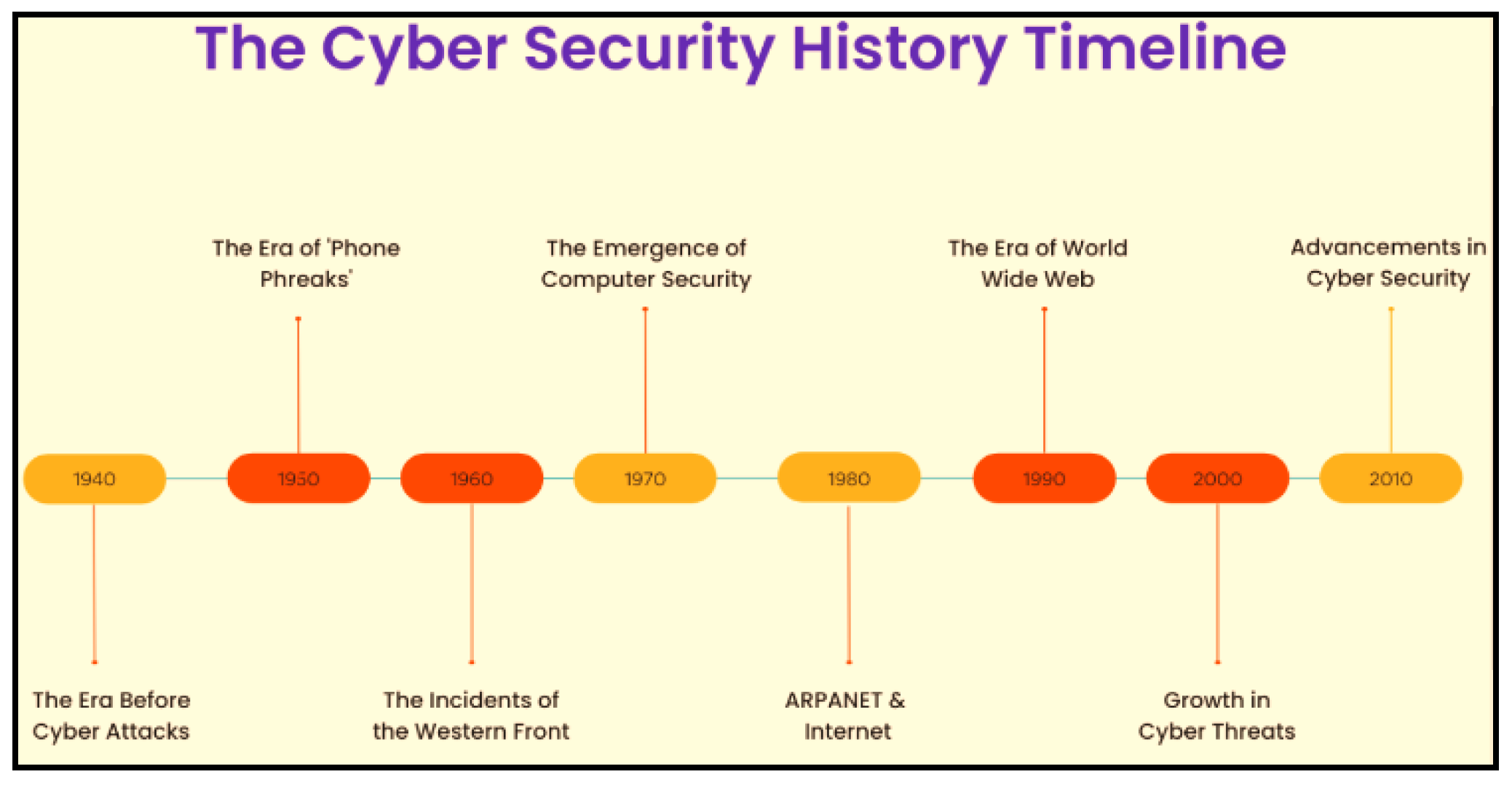
3. Evolution Of The Cyber Security Threat
Gen V Assaults
Ransomware
Supply Chain Assault
Malware
4. Cyber Attack Classification
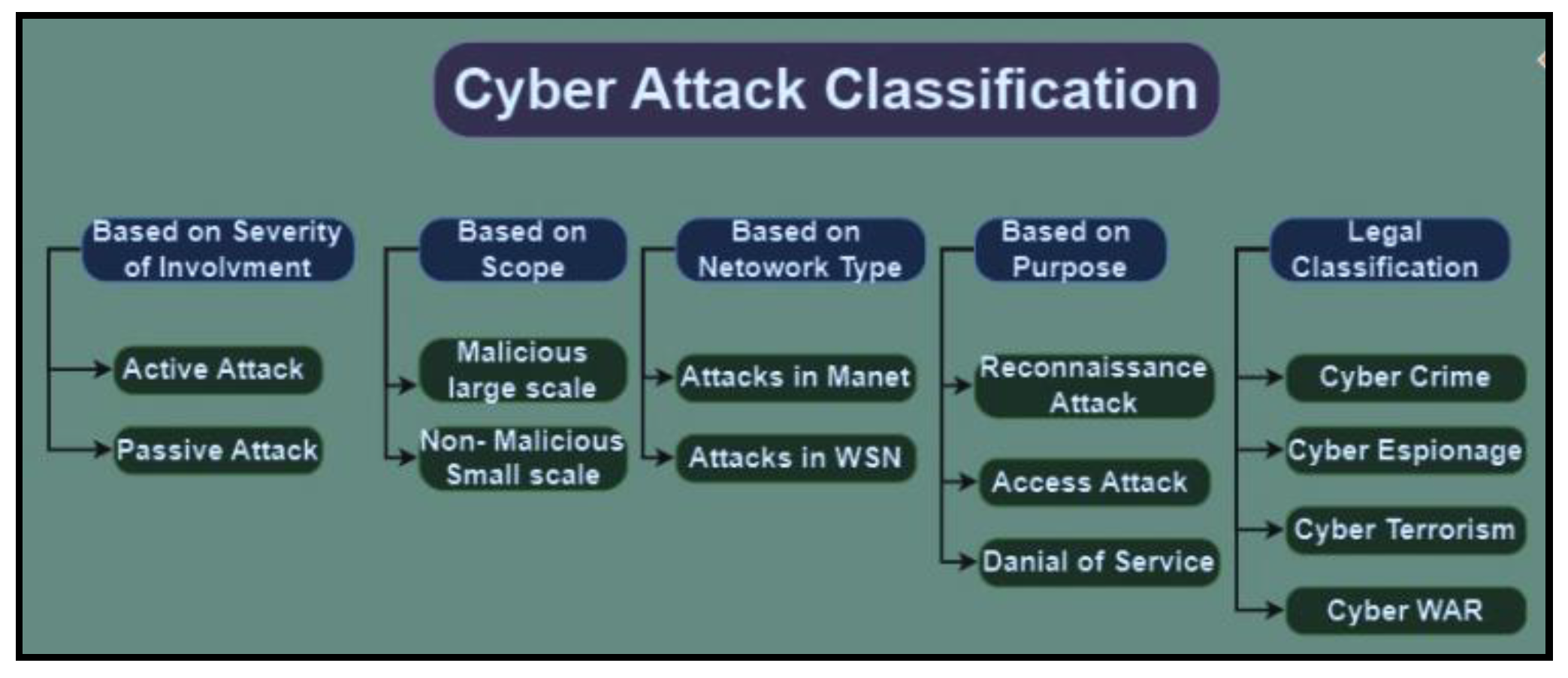
- (i)
- Passive Attack: The intruder is passively listening to the two parties’ conversation to play the data stored in the device by call hearing. In contrast, a breach may have been attempted even when the database was not accessed, unlike in an ongoing assault.
- (ii)
- Active attacks: they include the attacker causing packets to be sent unidirectionally or bidirectionally to other parties or obstructing data transit—an examination of research studies on cyberterrorism’s passive attacks. [6]
- (i)
- Moreover, classify cyberattacks according to their focus. There are two types of big-range malware: malicious and non-malicious.
- (ii)
- Dubious Broad Spectrum Attackers in this category aim to gain benefits for themselves or their organization or undermine the system’s effectiveness. Attacks that interfere with the intended device or disturb the social order include some Attacks that interfere with the target device or disturb the social order.
- (iii)
- Mild-mannered Small-Scale These are threats that cause minimal damage to property, minimal impact to the target infrastructure, or minimal loss of recoverable data. It is executed by inexperienced assailants or staff members with inexperience [6]
- (i)
- Attacks on the MANET Numerous assaults exist in this range, such as the Black Hole Attack, the Byzantine Assault, and the Flood Rushing Research Studies.
- (ii)
- WSN-related attacks This kind consists of two assaults. Among them are: Attacks based on network layers as well as attacks about and unrelated to cryptography. The regional character of certain cyberattacks raises concerns about global security, and methodological and ideological approaches are examined in connection to these challenges. Data and research on cyber security throughout this phase point to a conceptual trend about the rise in cyberterrorism. Increased reliance on cyberspace yields different scores in the terror domain. This categorization of cyberattack and terrorism gives rise to a cyberwarfare phenomenon. [7]
- (i)
- Attack of Reconnaissance Results from system mapping studies were included for resources and locations that were not authorized. Examples of reconnaissance attacks are port scanning and packet sniffing.
- (ii)
- Attack on Access Without access privileges, an attacker can break into the system or take advantage of a vulnerability to get data. Examples of this kind of assault include phishing, social engineering, and man-in-the-middle attacks.
- (iii)
- DoS stands for denial of service, or slowing down or interrupting a system. Additionally, records can be corrupted or erased using this. [7]
- (i)
- Cybercrime An alternative way to put it is "use of IT to encourage the handling of unlawful behavior or offenses." Any act that includes, in the widest sense, the use of IT is referred to as computer crime. Within this category are worms, malware, and logical bombs. Cybercriminals, IT criminals, high-tech criminals, web-based criminals, and electronic criminals are also used interchangeably. 184 An analysis of Research Reports on Cyber Terror.
- (ii)
- Cyber-spying or cyber-espionage This community includes well-known programs like spyware and Trojan horses in addition to techniques for capturing target devices. Cyber theft or spying is the illegal use of instruments or methods and the gathering of important data from unapproved or secret sites. In particular, these exercises may be carried out by paid spies, hostile invaders, or coders.
- (iii)
- Cybercrime Another issue that has evolved in the twenty-first century is cyber terror. It has grown over time. These kinds of terrorist assaults are quite easy to carry off and inflict unimaginable harm. It is only a sensation of worry that is incredibly difficult to overcome. According to the FBI definition, cyber terror is any incident that has the potential to cause chaos by impairing essential infrastructure and organizational functions. Cyberwarfare or Cyberwar Cyber warfare is defined as state-performed infiltration activities intended to disrupt or damage the computer systems or networks of another state.
5. Current Trends in Cybersecurity Information Systems
- Cybersecurity Information Systems (CIS)
- Definition of CIS: Cybersecurity Information Systems encompass a range of technologies, processes, and practices designed to protect networks, systems, and data from cyber threats.
- Importance of CIS: With the increasing frequency and sophistication of cyber attacks, CIS plays a crucial role in safeguarding organizations’ digital assets and ensuring business continuity. [8]
- Components of CIS:
- Security Hardware: Includes firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), routers, switches, and other network devices designed to enforce security policies and protect against unauthorized access and malicious activities. [9]
- Security Software: Encompasses antivirus software, anti-malware solutions, encryption tools, vulnerability scanners, security information and event management (SIEM) systems, and other software applications used to detect, prevent, and respond to cyber threats. [10]
- Functions of CIS:
- Threat Detection: CIS continuously monitors networks, systems, and applications for signs of suspicious activity or potential security breaches. This involves analyzing network traffic, log files, and system behavior to identify indicators of compromise (IOCs) and security incidents.
- Threat Prevention: CIS employs various security controls and mechanisms to prevent cyber attacks and unauthorized access to digital assets. This includes implementing access controls, firewalls, intrusion detection/prevention systems, antivirus software, and encryption technologies.
- Security Awareness and Training: CIS educates users and employees about cybersecurity best practices, policies, and procedures to promote a culture of security awareness and compliance. This includes conducting security awareness training sessions, phishing simulations, and promoting good cyber hygiene practices. [11]
- Key Technologies in CIS:
- Blockchain: Blockchain technology is being leveraged in CIS for secure data storage, authentication, and tamper-proof transaction logging, enhancing data integrity and transparency.
- Cloud Computing: Cloud-based security solutions offer scalability, flexibility, and cost-effectiveness for organizations seeking to protect their digital assets. This includes cloud-based firewalls, antivirus software, encryption services, and security-as-a-service (SECaaS) offerings.
- Internet of Things (IoT) Security: With the proliferation of IoT devices, securing interconnected devices and networks has become a critical component of CIS. This involves implementing security controls, encryption, and access management for IoT endpoints and gateways.
- Emerging Technologies Shaping CIS
- IoT Security: The proliferation of Internet of Things (IoT) devices introduces new security challenges, including device vulnerabilities, data privacy concerns, and network segmentation issues.
- Edge Computing: Edge computing brings processing power closer to IoT devices, enabling real-time data analysis and reducing latency, but also necessitating enhanced security measures to protect edge networks and devices. [12]
- Adoption of Blockchain Technology for Secure Data Management
- Blockchain Principles: Blockchain technology, known for its decentralized and immutable nature, is being leveraged in CIS to enhance data integrity, transparency, and security.
- Secure Data Storage: Blockchain-based solutions provide secure and tamper-proof data storage, reducing the risk of unauthorized access, data breaches, and data manipulation.
- Identity and Access Management: Blockchain facilitates decentralized identity and access management systems, enhancing authentication and authorization processes while reducing the reliance on centralized authorities. [13]
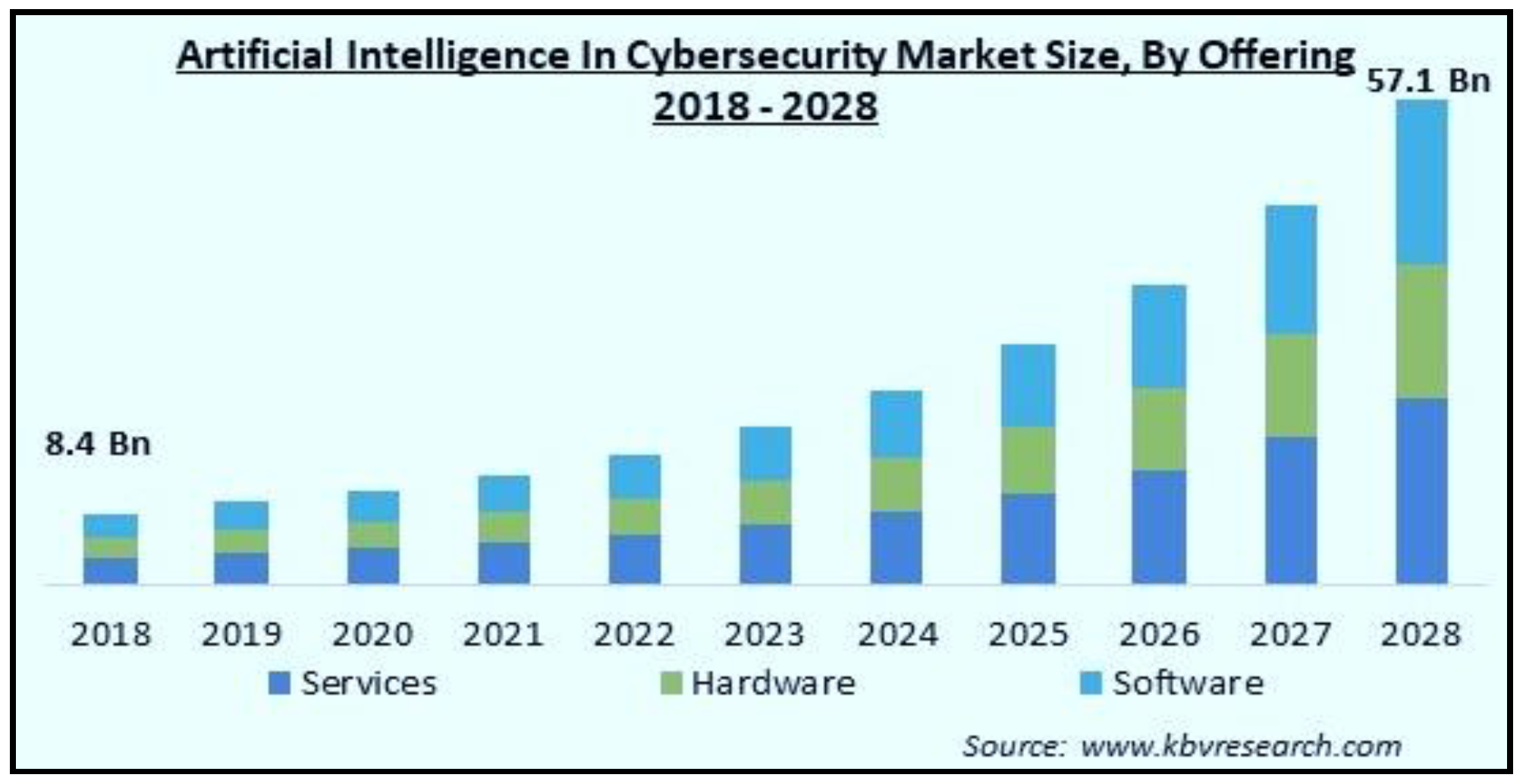
6. Integration of AI and Machine Learning
- Threat Detection: AI-powered cybersecurity solutions can detect and identify malicious activities, including malware, phishing attempts, and insider threats, by analyzing network traffic, user behavior, and system logs in real time.
- Behavioural Analysis: To create baselines and identify variations that can point to suspicious or unusual activities, AI systems can examine user and entity behavior. This strategy assists in locating advanced persistent threats (APTs) and insider threats that elude conventional signature-based detection techniques.
- Automated Response: AI enables automated response capabilities, allowing cybersecurity systems to take immediate action to mitigate security threats, such as quarantining infected devices, blocking suspicious IP addresses, or triggering alerts for further investigation.
Spoofing
Manipulation
Denial of Service
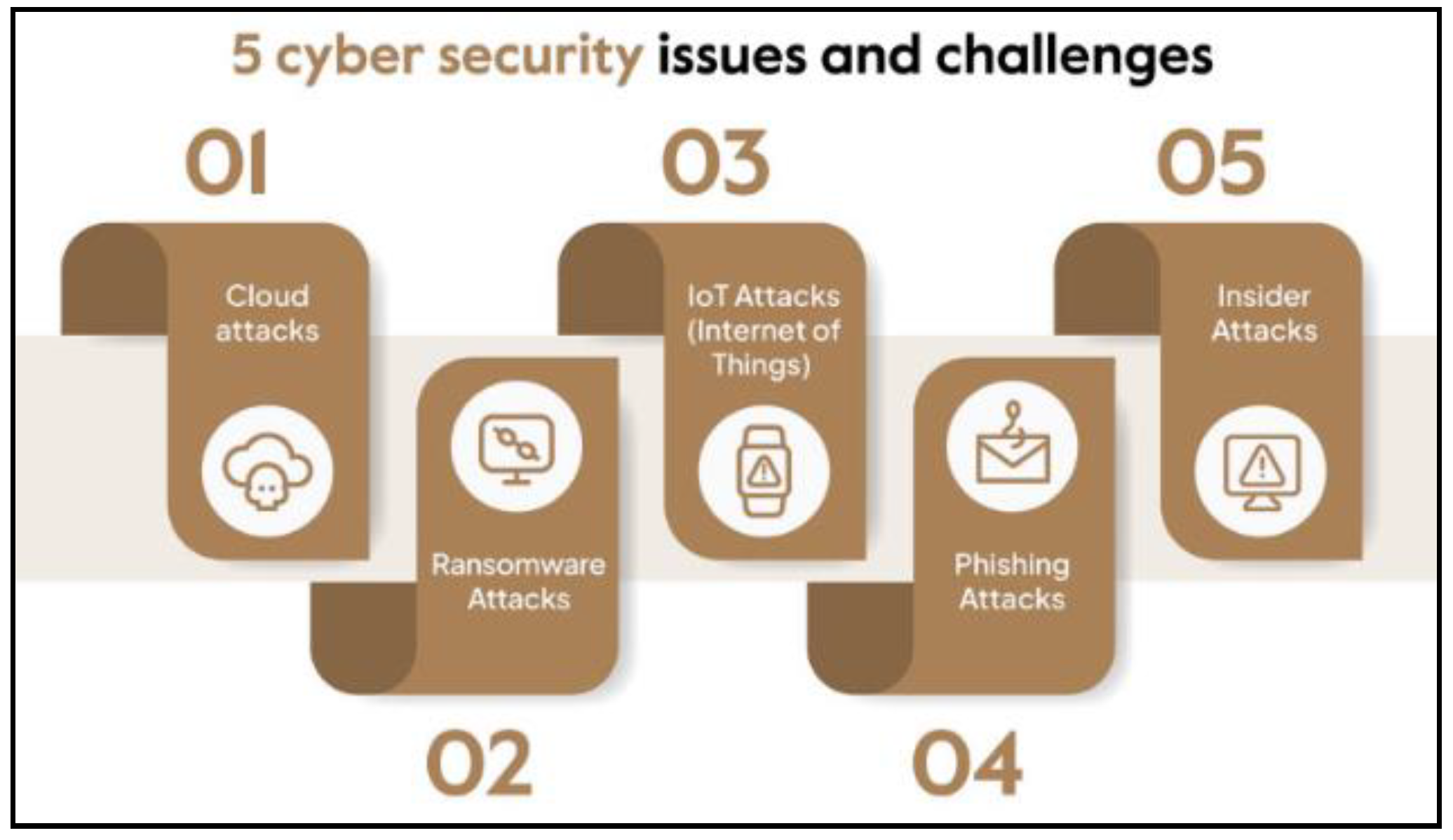
7. Challenges and Opportunities
8. Conclusion
Key Findings:
Regulatory Landscape and Compliance Challenges:
Implications And Future Directions:
Enhanced Collaboration And Information Sharing:
References
- Diwan and T. Dhar, "An investigation and analysis of cyber security information systems: latest trends and future suggestion,". Information Technology in Industry 2021, 2, 477–492.
- G. N. G. J. R. Reddy, "A study of cyber security challenges and its emerging trends on latest technologies,". arXiv 2014, arXiv:1402.1842.
- R. B. e. a. Kshiteesh, "A review on challenges and latest trends on cyber security using text cryptography," In Proceedings of the 3rd International Conference on Integrated Intelligent Computing Communication & Security (ICIIC 2021), 2021.
- T. Fadziso, "Evolution of the cyber security threat: an overview of the scale of cyber threat,". Digitalization & Sustainability Review 2023, 3, 1–12.
- N. Kaja, "Artificial intelligence and cybersecurity: Building an automotive cybersecurity framework using machine learning algorithms," Doctoral dissertation, 2019.
- K. M. C. S. D. a. E. S. Rajasekharaiah, "Cyber security challenges and its emerging trends on latest technologies,". IOP Conference Series: Materials Science and Engineering 2020, 981.
- S. K. M. M. K. &. F. Y. Takemoto, "Trends in Cybersecurity and Latest Countermeasures,". Hitachi Review 2014, 63, 264.
- S. M. Tisdale, "Cybersecurity: Challenges from a Systems, Complexity, Knowledge Management and Business Intelligence Perspective," . Issues in Information Systems 2015, 16, 3.
- G. C. A. D. A. P. Wilshusen, "Cybersecurity: Continued efforts are needed to protect information systems from evolving threats,". United States Government Accountability Office, 2009.
- H. S. Alqahtani, "Latest Trends and Future Directions of Cyber Security Information Systems,". Journal of Information Engineering and Applications 2016, 6, 11.
- A.M. Y. M. a. K. M. N. W. Sandar, "Fundamental areas of cyber security on the latest technology,". International Journal of Trend in Scientific Research and Development 2019, 3.
- M. Himmat, "The Current Trends, Techniques, and Challenges of Cybersecurity,". European Journal of Information Technologies and Computer Science 2023, 3, 1–5.
- A. M. K. S. S. &. C. S. R. Tonge, "Cyber security: challenges for society-literature review," . IOSR Journal of Computer Engineering 2013, 2, 67–75.
- E. A. Fischer, "Cybersecurity issues and challenges: In brief,". 2014.
- D. Ghelani, "Cyber security, cyber threats, implications and future perspectives: A Review," Authorea Preprints, 2022.
- J. a. K. R. R. Kaur, "The recent trends in cyber security: A review,". Journal of King Saud University-Computer and Information Sciences 2022, 38, 5766–5781.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



