Submitted:
04 September 2024
Posted:
04 September 2024
You are already at the latest version
Abstract
Keywords:
I. Introduction
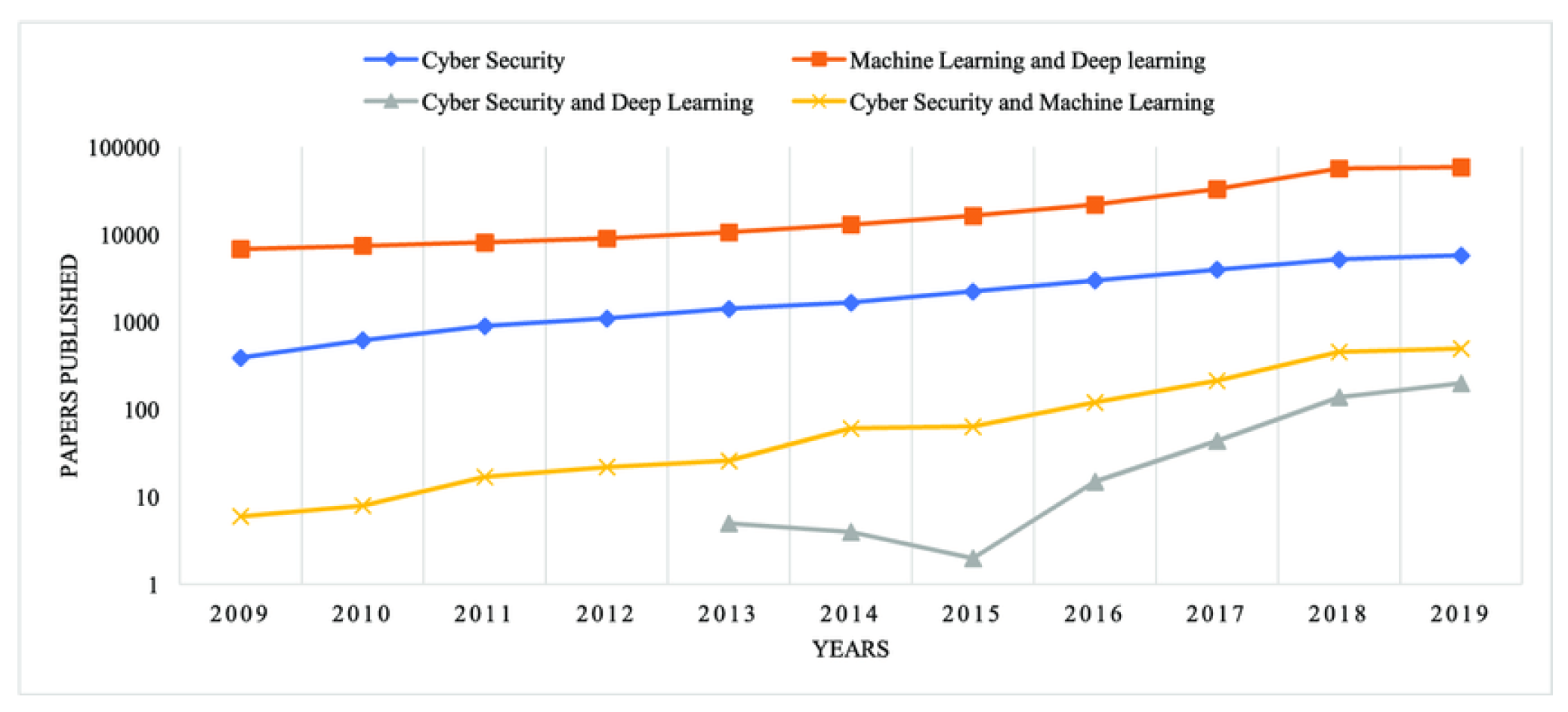
II. AI and Machine Learning in Cybersecurity: A Dynamic Force for Defense
A. Streamlined Security Operations
B. Proactive Threat Hunting
III. Zero-Trust Architectures: Redefining Network Security
A. Micro-Segmentation and Least Privilege Access
B. Continuous Monitoring and Identity Verification
C. Zero Trust Network Access (ZTNA) for the Cloud
IV. Integration of Cybersecurity and Business Strategy: A Collaborative Approach
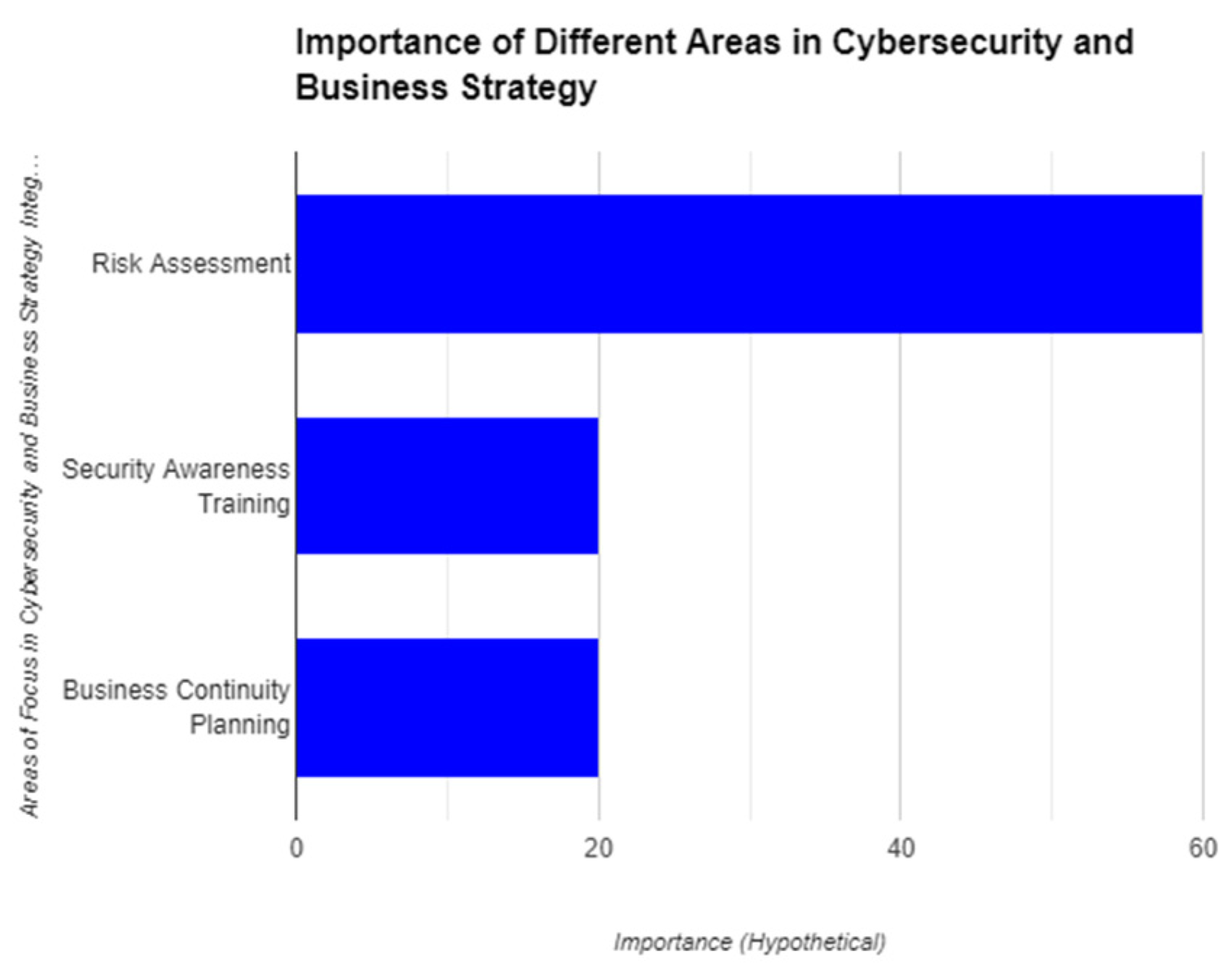
A. Risk Assessment and Alignment
B. Security Culture and Awareness
C. Business Continuity and Disaster Recovery Planning
V. Cyber Resilience: Building Bouncing Back Better
A. Proactive Threat Detection and Response
B. Incident Response Planning and Recovery
C. Business Continuity and Operational Resilience
VII. The Increasing Importance of Data Privacy: A Growing Concern in the Digital Age
A. The Rise of the Data Economy
B. Evolving Data Privacy Regulations
C. Heightened Awareness of Data Breaches
VIII. The Rise Zero-Trust Architectures: Redefining Network Security
A. Micro-segmentation and Least Privilege Access
B. Continuous Monitoring and Identity Verification
C. Zero Trust Network Access (ZTNA) for the Cloud:
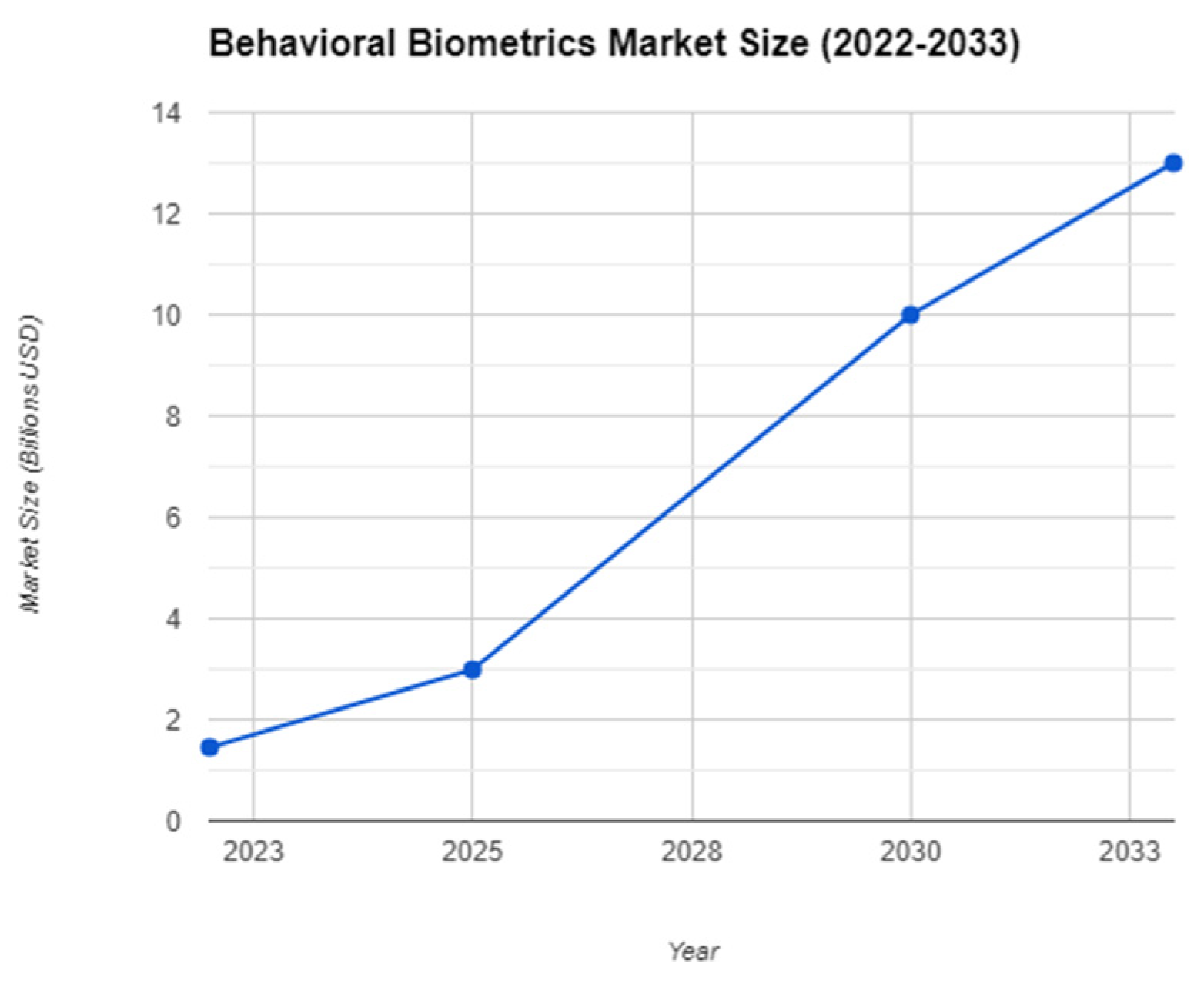
XI. Behavioral Biometrics
- Typing Dynamics: Analyzes how a user types, including typing speed, rhythm, pressure, and dwell time on keys.
- Mouse Dynamics: Analyzes how a user interacts with a mouse, including movement patterns, click speed, and scrolling behavior.
- Touch Dynamics: Analyzes how a user interacts with a touchscreen device, including swipe patterns, tap pressure, and dwell time on specific areas.
- Gait Analysis: Analyzes a user's walking pattern, often used in conjunction with other forms of biometrics for high-security applications.
- Cognitive Biometrics: Analyzes a user's cognitive responses during interaction, such as reaction time to stimuli or patterns in mouse movement during decision-making tasks.
- Voice Recognition: Analyzes the unique characteristics of a user's voice, including pitch, tone, accent, and speech patterns, to authenticate their identity in voice-based interactions.
- Signature Dynamics: Analyzes the individual nuances in a user's signature, including pen pressure, stroke order, and overall handwriting style, to verify their identity in digital signature applications.
- Facial Dynamics: Analyzes subtle facial movements and expressions, such as micro-expressions and blinking patterns, to authenticate users in facial recognition systems and detect spoofing attempts.
X. Conclusion
References
- “Cyber Security Defense Policies: A Proposed Guidelines for Organization’s Cyber Security Practices”, International Journal of Advanced Computer Science and Applications. https://thesai.org/Publications/ViewPaper?Volume=11&Issue=8&Code=IJACSA&SerialNo=17.
- A. S. Writer, “10 Ai ML in IT security trends to look out for in 2024,” AiThority, https://aithority.com/machine-learning/10-ai-ml-in-it-security-trends-to-look-out-for-in-2024 (accessed Apr. 22, 2024).
- “Using Darktrace for threat hunting: Darktrace Blog,” RSS, https://darktrace.com/blog/using-darktrace-for-threat-hunting (accessed Apr. 22, 2024).
- “Zero trust,” Palo Alto Networks, https://www.paloaltonetworks.com/zero-trust (accessed Apr. 22, 2024).
- “SSE & SASE | Converge Networking and Security”, Apr. 21, 2024. https://www.cloudflare.com/zero-trust/ (accessed Apr. 21, 2024).
- “Council Post: Why Cybersecurity Should Be Part Of Any Business Strategy”, Nov. 21, 2022. https://www.forbes.com/sites/forbestechcouncil/2022/11/21/why-cybersecurity-should-be-part-of-any-business-strategy/ (accessed Apr. 21, 2024).
- “The Competitive Edge: How Cybersecurity Integration Drives Business Success”. https://mackjacksonjr.medium.com/the-competitive-edge-how-cybersecurity-integration-drives-business-success-38d64d128484 (accessed Apr. 21, 2024).
- “cyber resiliency - Glossary | CSRC”, Apr. 21, 2024. https://csrc.nist.gov/glossary/term/cyber_resiliency (accessed Apr. 21, 2024).
- “What is Cyber Resilience?”, Apr. 21, 2024. https://blogs.opentext.com/cyber-resilience-definition/ (accessed Apr. 21, 2024).
- “What is Cyber Resilience?”. https://www.ibm.com/topics/cyber-resilience (accessed Apr. 21, 2024).
- “Deepfake”, Apr. 21, 2024. https://en.wikipedia.org/w/index.php?title=Deepfake&oldid=1219846632 (accessed Apr. 21, 2024).
- “Deep fakes | Synthesis AI | AI and machine learning”, Apr. 21, 2024. https://feedmagazine.tv/features/synthesia-ai/ (accessed Apr. 21, 2024).
- “EU turns to Big Tech to help deep fake-proof election”, Apr. 21, 2024. https://www.politico.eu/article/eu-big-tech-help-deepfake-proof-election-2024/ (accessed Apr. 21, 2024).
- “Markets & data”, Apr. 21, 2024. https://www.economist.com/markets-data (accessed Apr. 21, 2024).
- “General Data Protection Regulation (GDPR) Compliance Guidelines”, Apr. 21, 2024. https://gdpr.eu/ (accessed Apr. 21, 2024).
- “Help Center”. https://www.idtheftcenter.org/help-center/ (accessed Apr. 21, 2024).
- “Zero Trust”. https://www.paloaltonetworks.com/zero-trust (accessed Apr. 21, 2024).
- “Zero Trust Network Access (ZTNA)”. https://www.zscaler.com/capabilities/zero-trust-network-access (accessed Apr. 21, 2024).
- [PDF] A survey on machine learning techniques for cyber security in the last decade | semantic scholar, https://www.semanticscholar.org/paper/A-Survey-on-Machine-Learning-Techniques-for-Cyber-Shaukat-Luo/4c30d041c137948aa75e40912f14558234bf1ce2 (accessed Apr. 23, 2024).
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).