Submitted:
12 August 2024
Posted:
13 August 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Research Goal and Methods
- The computer collection method is used to gather pertinent literature and web sources listed in the literature list, serving the purpose of writing this paper.
- The inductive method was employed in this study to analyze specific individual cases and gather new information about the role and significance of honeypots.
- This paper employed a deductive approach to analyzing the comprehensive aspects of honeypots in cybersecurity. This method involves drawing conclusions based on assumed truths and suggestions.
- This paper employs analytical techniques to deconstruct intricate concepts, evaluations, and conclusions into their fundamental elements. Specifically, it applies these methods to analyze an individual honeypot solution according to predetermined criteria.
- The comparison method assesses the similarities and differences between the same or related facts. It allows for identifying standard features or distinctions when evaluating different honeypot solutions.
3. Honeypot Types
3.1. High-Interaction Honeypots
3.2. Low-Interaction Honeypots
3.3. Hybrid Honeypots
4. Honeypot Solutions and Comparison Criteria
- SSH honeypots – Kippo and Cowrite.
- HTTP honeypots – Glasstopf, Nodepot and Google Hack Honeypot.
- WordPress honeypots – Formidable Honeypot, Blackhole For Bad Bots, Wordpot.
- Database honeypots – ElasticHoney, HoneyMysql and MongoDB-HoneyProxy.
- Email honeypots – Honeymail, Mailoney, and SpamHAT.
- IoT honeypots – HoneyThing.
- Other types are Dionaea, Honeypot-ftp, HoneyNTP, Thug, and Canarytokens.
5. Comparative Evaluation and Results Analysis
-
Selecting the type of honeypot - various types exist, each designed for distinct purposes. It is imperative to consider the kind most suits the organization's objectives. Several prevalent categories include:
- Low-interaction honeypots are emulators that mimic specific vulnerabilities or services, but their level of interaction is limited. They are simple to implement and maintain but provide limited information regarding the attackers;
- High-interaction honeypots imitate genuine systems and enable attackers to interact extensively. They collect comprehensive data but necessitate additional resources and maintenance;
- Virtualized Honeypots are implemented on virtual machines, which enables effortless deployment, isolation, and scalability;
- Manufacturing honeypots refers to natural systems or services that have been strengthened and closely observed. They can detect and prevent attacks on actual infrastructure while reducing the potential harm to operational systems.
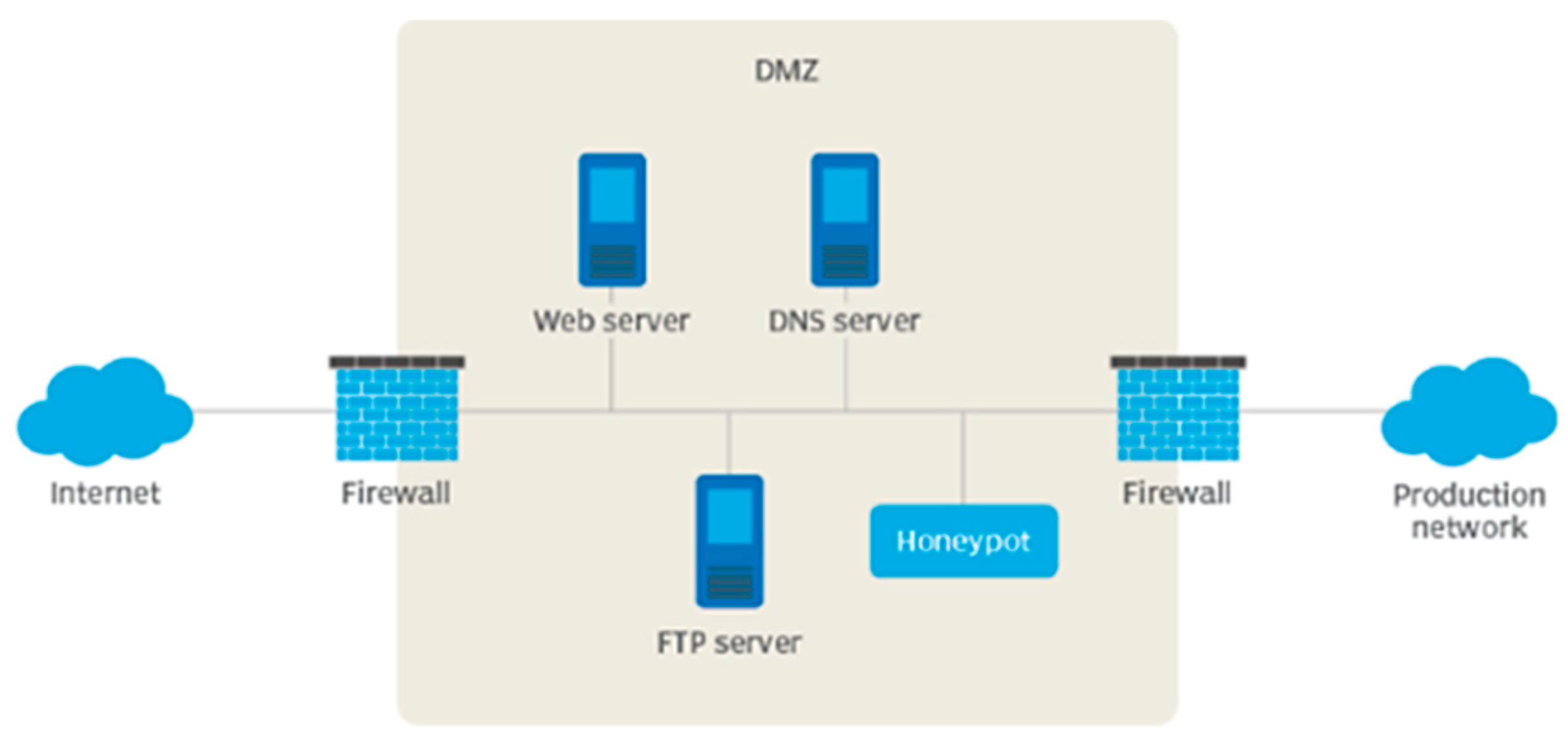
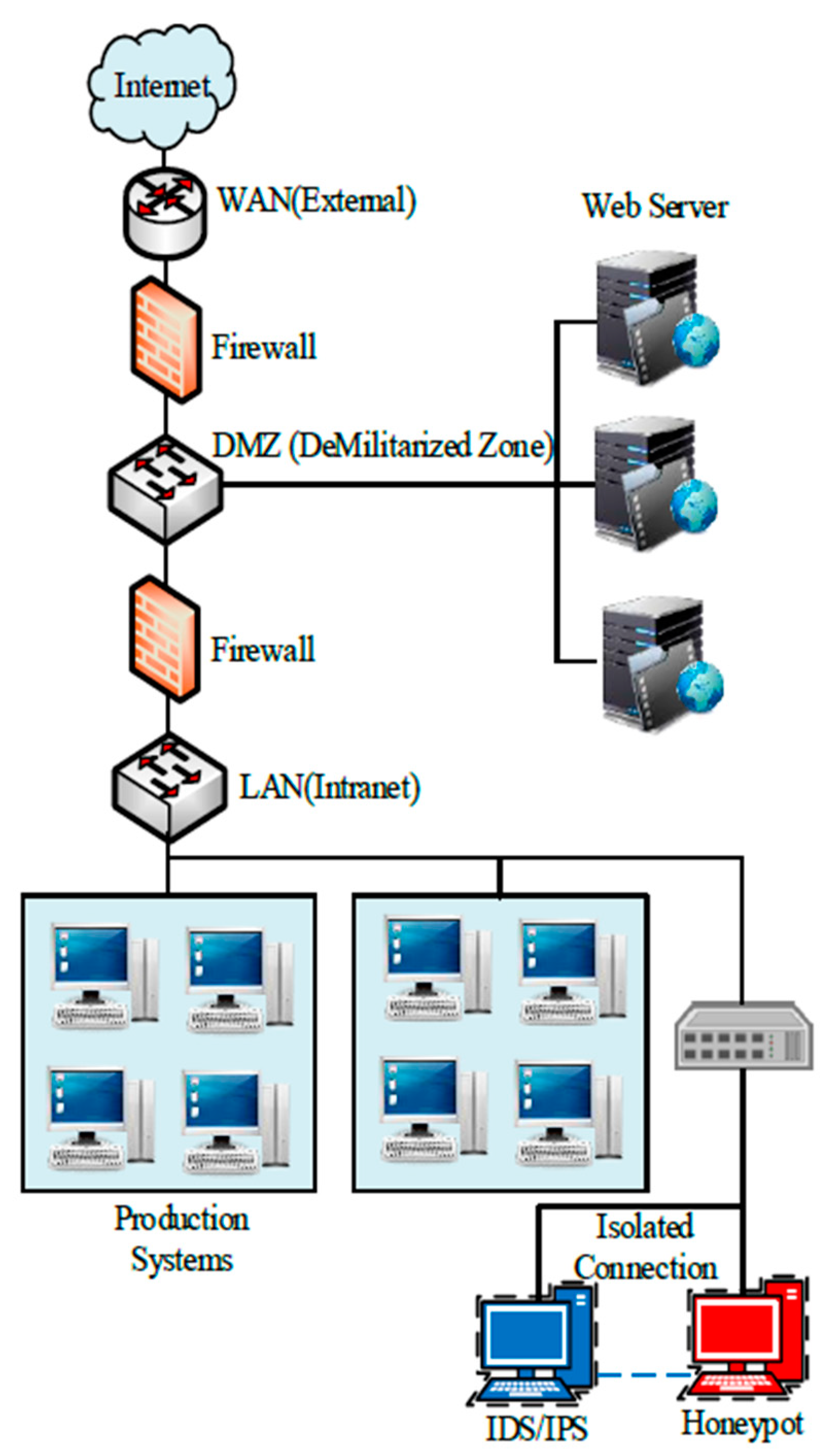
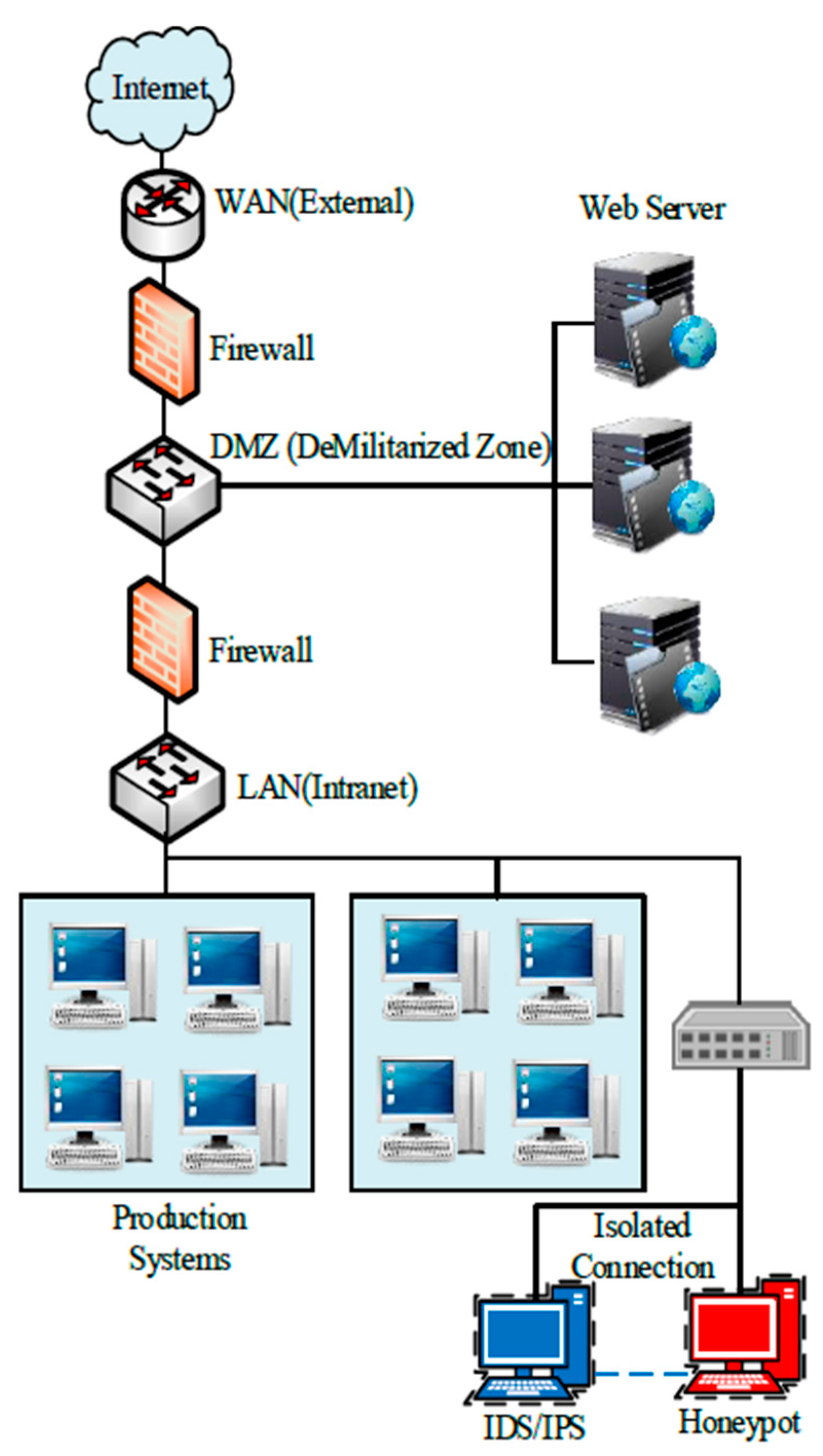
- Network placement – it is imperative to determine the specific location within the network infrastructure where the honeypot system will be deployed. The primary emphasis should be on positioning the honeypot near actual systems to replicate their presence or isolating it within a distinct network segment to minimize the likelihood of the honeypot being utilized as a starting point for launching attacks on other systems.
- The choice of operating systems and services—The selection of the operating system and services that the honeypot system will imitate should be determined. To create a convincing honeypot, it is essential to replicate the systems being emulated closely. Verifying that the chosen systems and services possess well-documented vulnerabilities is imperative to attract attackers.
- Regularly updating and patching the honeypot system is necessary for effective vulnerability management and to ensure the presence of genuine vulnerabilities. This provides the honeypot's continued appeal to potential attackers and prevents it from becoming obsolete or easily recognizable.
- Robust monitoring and logging mechanisms are essential for recording all activities within the honeypot system, including network traffic, system logs, and user interactions. Observe deviant behavior and set up notifications for potential attacks or dubious actions.
- Deception techniques—Integrating deceptive strategies enhances the attractiveness of honeypots. This may involve presenting fabricated data or files, deploying honeytokens (counterfeit credentials or documents), or offering lure services designed to appear enticing to potential attackers. These factors enhance the likelihood of attackers contacting the honeypot and uncovering their techniques.
6. Best Practices and Recommendations
6.1. Honeypot Implementation Strategies
6.2. Security Assumptions and Mitigation Techniques
- The position of the honeypot is vital for its effectiveness. Strategically positioning honeypots within the network provides potential attackers with a target, as these honeypots appear to be legitimate services. The configuration should also consider the network environment where the attacker can establish a presence. Moreover, deploying honeypots on external or internal infrastructure will dictate the identified attacks' nature, frequency, and intensity. Outward-facing honeypots are vulnerable to regular scanning, deceptive botnet exploits, and practical attacks from various threat actors. This can amplify noise in logging signals, impeding distinguishing between genuine and targeted threats.
- Isolation—The honeypot must be segregated from the rest of the network and should not store confidential information. This reduces the likelihood of attackers using their access to honeypots to carry out further attacks across the network, using the honeypot as a starting point. Honeypot configurations should be designed to trap attackers and monitor their activities accurately and effectively.
- Tracking—The honeypot should be meticulously observed to collect data on the attacker's tactics, techniques, and procedures (TTPs) that can be incorporated into the network and security defenses. Mere implementation of a honeypot is insufficient. An essential task is to analyze honeypot logs to identify malicious activity, which serves to promptly notify the organization of possible attacks.
- Management and maintenance—The honeypot should be overseen by proficient security personnel who can set it up, monitor it, and uphold it to guarantee its efficacy in detecting and responding to attacks. Furthermore, it is crucial to regularly update the honeypot to maintain its authenticity as a replica of genuine systems and applications, thus ensuring its appeal to potential attackers.
- Integration with complementary security measures – The honeypot should be seamlessly incorporated into existing security measures, including firewalls, intrusion detection systems, incident response plans, SIEMs, MDRs, and systems for managing detection alerts, investigation, and response. This guarantees that the honeypot enhances the network's security and boosts its worth by generating activity detections and alerts. Honeypots can be utilized to dynamically construct detections by leveraging information from attackers.
6.3. Integration with Existing Security Infrastructure
7. Future Work
- Progress in machine learning: Machine learning and artificial intelligence have been utilized to enhance the identification of attacks in honeypots. In the future, these advancements are expected to further progress, enabling more precise and automated detection of attacks.
- Enhanced automation is expected to impact the advancement of honeypots significantly. This will enable organizations to deploy honeypots more quickly and effectively, thereby improving their ability to analyze the data gathered by honeypots systematically.
- Honeypots are expected to be more effectively integrated with other security tools, such as intrusion detection and prevention systems, to enhance coordination and collaboration. By harnessing the attributes of different security devices, organizations can improve their ability to safeguard their systems against attacks.
- Cloud-based honeypots are expected to follow the trend of organizations migrating their infrastructure to the cloud. Cloud-based honeypots can distinguish between attacks on assets and attacks on cloud-based applications.
- Fraud technology, including honeypots, is a component of the broader field of cybersecurity. Fraud technology encompasses the dissemination of diversions or other deceptive methods employed to confuse attackers and create additional complications within the organization.
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Šimon M, Huraj L, Hrinkino D. Using a honeypot to improve student cybersecurity awareness. 2023 21st International Conference on Emerging eLearning Technologies and Applications (ICETA). 2023 Oct 26; [CrossRef]
- Nintsiou M, Grigoriou E, Karypidis PA, Saoulidis T, Fountoukidis E, Sarigiannidis P. Threat intelligence using digital twin honeypots in cybersecurity. 2023 IEEE International Conference on Cyber Security and Resilience (CSR). 2023 Jul 31; [CrossRef]
- Touch S, Colin J-N. Asguard: Adaptive self-guarded honeypot. Proceedings of the 17th International Conference on Web Information Systems and Technologies. 2021; [CrossRef]
- Subhan D, Lim C. Analyzing Adversary’s Attack on Ethereum Collected from Honeypots. 2023 11th International Conference on Information and Communication Technology (ICoICT). 2023:313-318. [CrossRef]
- Benedict, S. EA-pot: An explainable AI-assisted Blockchain Framework for honeypot IP predictions. Acta Cybernetica. 2022 Nov 22;26(2):149–73. [CrossRef]
- Valeros V, Rigaki M, García S. Attacker Profiling Through Analysis of Attack Patterns in Geographically Distributed Honeypots. arXiv. 2023. [CrossRef]
- Baykara M, Das R. SoftSwitch: a centralized honeypot-based security approach using software-defined switching for secure management of VLAN networks. Turk J Electr Eng Comput Sci. 2019;27:3309-3325. [CrossRef]
- Du C, Zhao S, Wang W. RRPOT: A Record and Replay Based Honeypot System. J Phys Conf Ser. 2021;1757:012183.Naik N, Shang C, Jenkins P, Shen Q. D-FRI-Honeypot: A Secure Sting Operation for Hacking the Hackers Using Dynamic Fuzzy Rule Interpolation. IEEE Trans Emerg Top Comput Intell. 2020;5:893-907. 10.1109/TETCI.2020.3023447. [CrossRef]
- Schuba M, Höfken H, Linzbach S. An ICS Honeynet for Detecting and Analyzing Cyberattacks in Industrial Plants. 2021 International Conference on Electrical, Computer and Energy Technologies (ICECET). 2021:1-6. [CrossRef]
- Nilă C, Preda M, Apostol I, Patriciu V. Reactive WiFi honeypot. 2021 13th International Conference on Electronics, Computers and Artificial Intelligence (ECAI). 2021:1-6. [CrossRef]
- Draghicescu D, Caranica A, Fratu O. Honeypot Technologies for Malware Detection and Analysis. Strategies XXI - Command and Staff College. 2021. [CrossRef]
- Sehgal R, Majithia N, Singh S, Sharma S, Mukhopadhyay S, Handa A. Honeypot Deployment Experience at IIT Kanpur. 2020:49-63. [CrossRef]
- Sladić M, Valeros V, Catania C, Garcia S. LLM in the Shell: Generative Honeypots. arXiv. 2023. [CrossRef]
- Subhan D, Lim C. Unveiling Attack Patterns: A Study of Adversary Behavior from Honeypot Data. 2023 IEEE International Conference on Cryptography, Informatics, and Cybersecurity (ICoCICs). 2023:178-183. [CrossRef]
- Florea R, Craus M. A Game-Theoretic Approach for Network Security Using Honeypots. Future Internet. 2022;14:362. [CrossRef]
- Mocanu F, Scripcariu L. Intrusion Detection Platform with Virtual Honeypots. 2023 International Symposium on Signals, Circuits and Systems (ISSCS). 2023:1-4. [CrossRef]
- Katakwar H, Aggarwal P, Dutt V. Modeling the effects of different honeypot proportions in a deception-based security game. Human Factors Cybersecurity. 2023. [CrossRef]
- Ziaie Tabari A, Ou X. A Multi-phased Multi-faceted IoT Honeypot Ecosystem. Proc 2020 ACM SIGSAC Conf Comput Commun Secur. 2020. [CrossRef]
- Osman M, Nadeem T, Hemida A, Kamhoua CA. Optimizing Honeypot Placement Strategies with Graph Neural Networks for Enhanced Resilience via Cyber Deception. Proc 2nd Graph Neural Netw Workshop. 2023. [CrossRef]
- European Network and Information Security Agency (ENISA). Proactive Detection of Security Incidents. 2012. Available from: https://www.enisa.europa.eu/publications/proactive-detection-of-security-incidents-II-honeypots/@@download/fullReport, accessed May 2024.
- Yang X, Yuan J, Yang H, Kong Y, Zhang H, Zhao J. A Highly Interactive Honeypot-Based Approach to Network Threat Management. 2023. Available from: https://www.mdpi.com/1999-5903/15/4/127, accessed November 2023.
- Baykara M, Das R. A Survey on Potential Applications of Honeypot Technology in Intrusion Detection Systems. 2015. Available from: https://www.researchgate.net/publication/290433369_A_Survey_on_Potential_Applications_of_Honeypot_Technology_in_Intrusion_Detection_Systems, accessed May 2024.
- Satheesh, V. The Evolution Of Honeypot Technologies And Future Directions. Available from: https://www.irjmets.com/uploadedfiles/paper/issue_5_may_2023/38648/final/fin_irjmets1683961611.pdf, accessed May 2024.
| Title 1 | Honeyd | Dionaea | Cowrie | Amun | Glasstopf | Kippo | Thug |
|---|---|---|---|---|---|---|---|
| Detection range | Multifunctional | Multifunctional | Specialized | Multifunctional | Specialized | Specialized | Multifunctional |
| Emulation accuracy | Acceptable | All right | All right | Acceptable | Excellent | All right | All right |
| Quality of collected data | Weak | Excellent | All right | All right | All right | All right | All right |
| Readability | Excellent | Excellent | All right | Excellent | All right | Acceptable | Acceptable |
| Scalability and performance | Excellent | All right | Acceptable | All right | Acceptable | Acceptable | Acceptable |
| Expandability | Excellent | Excellent | All right | Excellent | Excellent | Acceptable | All right |
| Embeddable | Acceptable | Excellent | Acceptable | All right | All right | Acceptable | All right |
| Complexity of setup and use | Acceptable | All right | All right | All right | All right | All right | All right |
| Maintenance requirements | All right | All right | Acceptable | All right | All right | All right | All right |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




