Submitted:
23 July 2024
Posted:
25 July 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Overview of Blockchain Technology
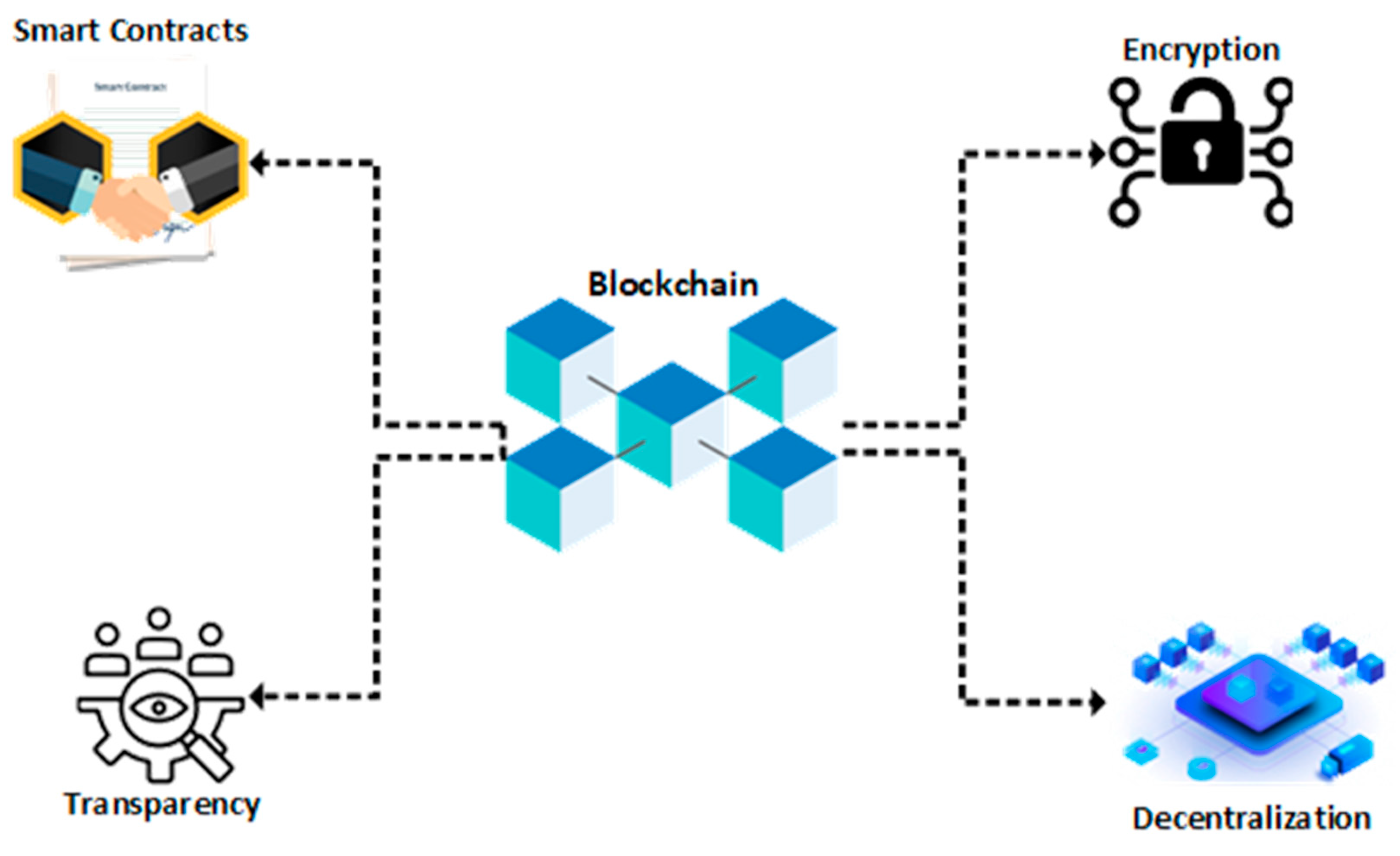
2.1. Blockchain Features
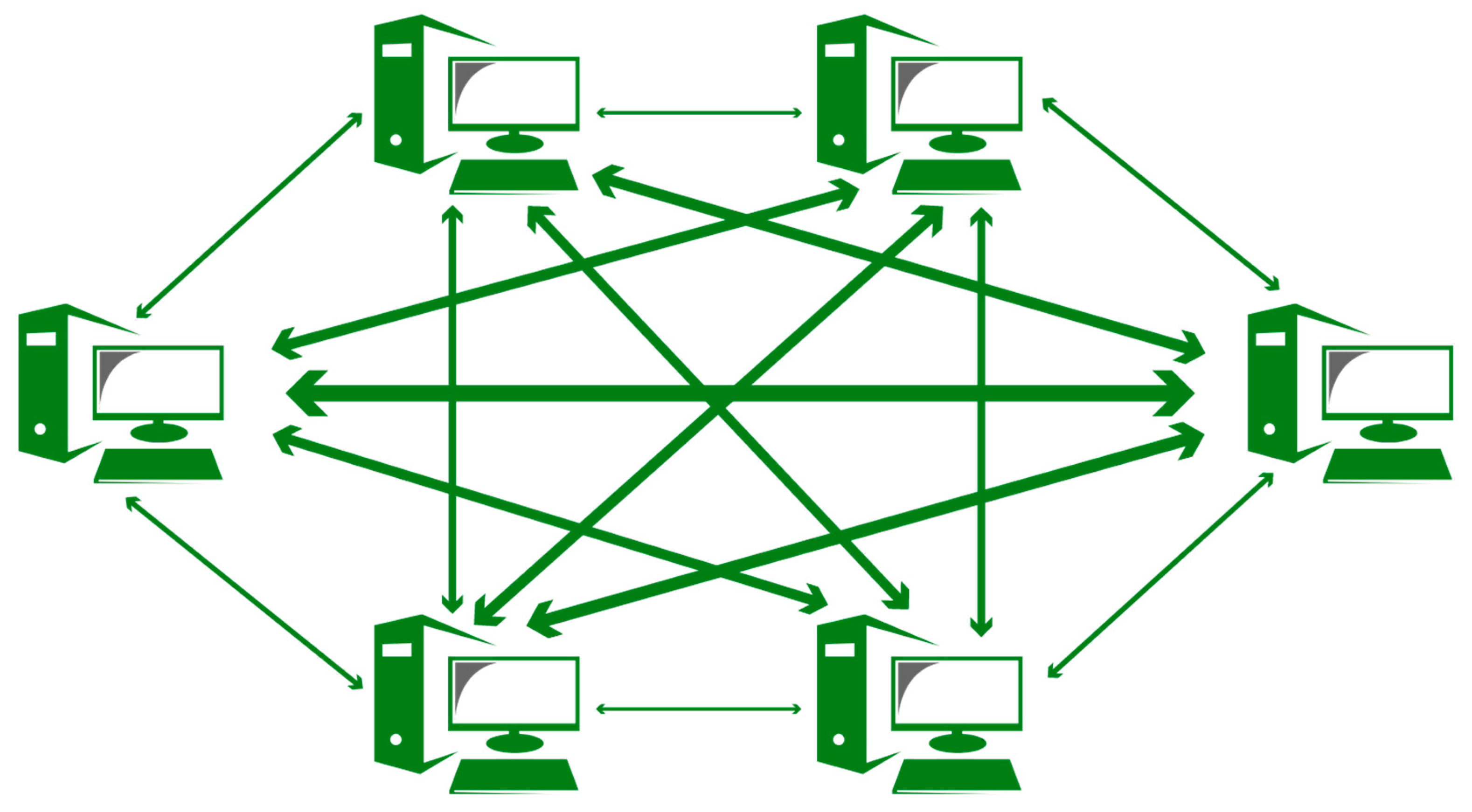
- Decentralization: In traditional centralized transaction systems, a third-party agency was always required in order to validate and authenticate each transaction being made between two parties. For example, a bank (central or commercial) would serve as a mediator in a every kind of transaction between two individuals. This would result in an overload to their central systems and servers. In blockchain, due to its utilization of consensus algorithms, third parties are no longer required to act as intermediaries, thereby giving blockchain its decentralized nature [3].
- Anonymity: Due to its decentralized nature, blockchain allows users to execute their transactions under entirely random generated addresses, since there is no centralized authority system to record, monitor and validate the authenticity of these addresses.
- Auditability (Transparency): In blockchain technology, a digital distributed ledger and a digital timestamp are used in order to record and validate each transaction. This means that whoever has access to any node in the network can trace and audit any previous record. In Bitcoin, for example, which is the first and most frequently used cryptocurrency, all transactions can be traced, thus making the data in the blockchain transparent and auditable [5].
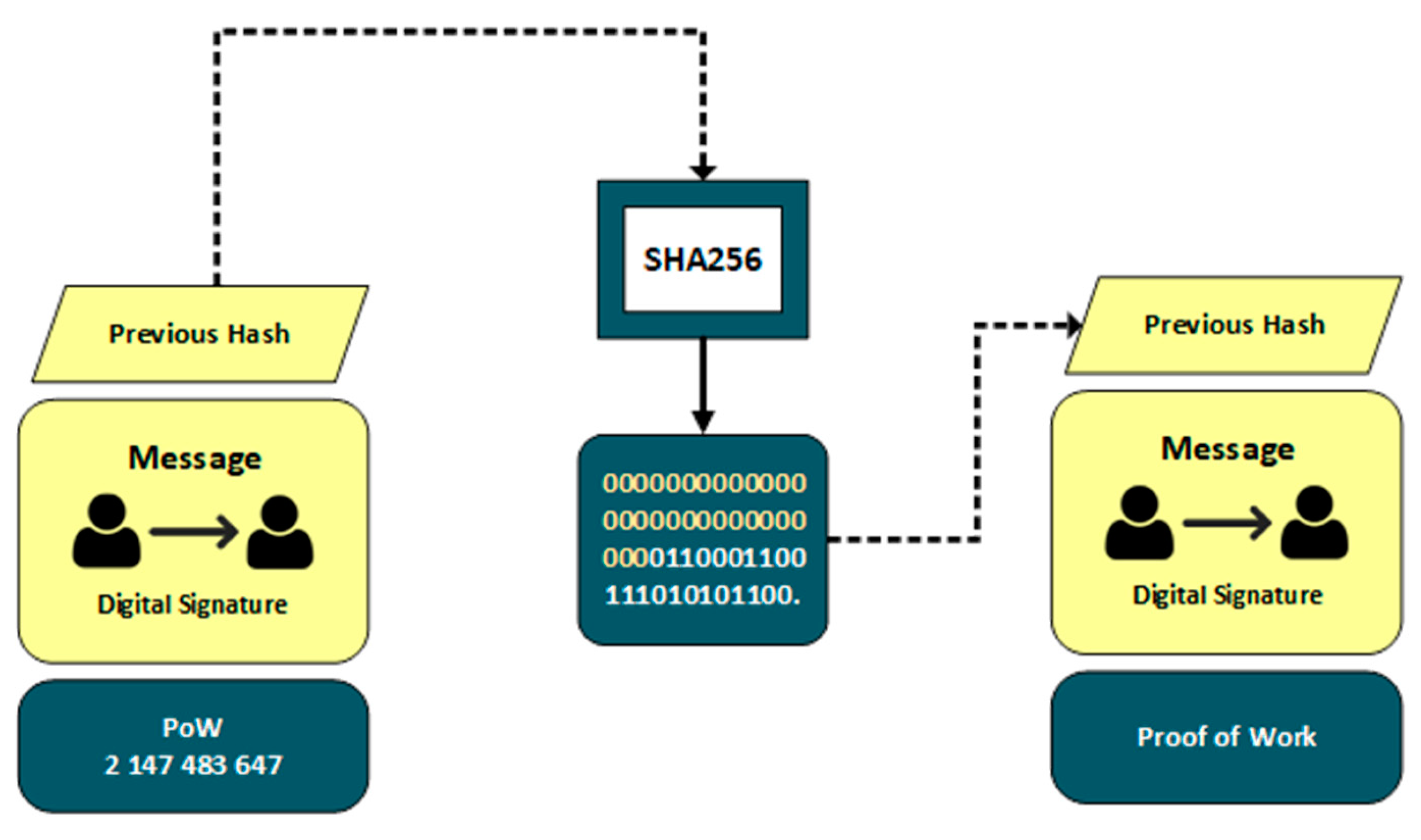
- Immutability (Persistency): Once a transaction has been recorded in the blockchain, it cannot be tampered with or deleted by any party. This is one of many aspects that makes blockchain networks secure and easily trusted. It works like this; each block in the blockchain contains a unique piece of code, called a hash, which works like a digital fingerprint. When a new block is created, this hash consists of all the information inside the block, including details of the transaction being made, the hash from previous blocks and a timestamp, among other information. If anyone attempts to change any information in the block, the hash (fingerprint) will also change, thus signaling that someone has tried to alter something in the blockchain.
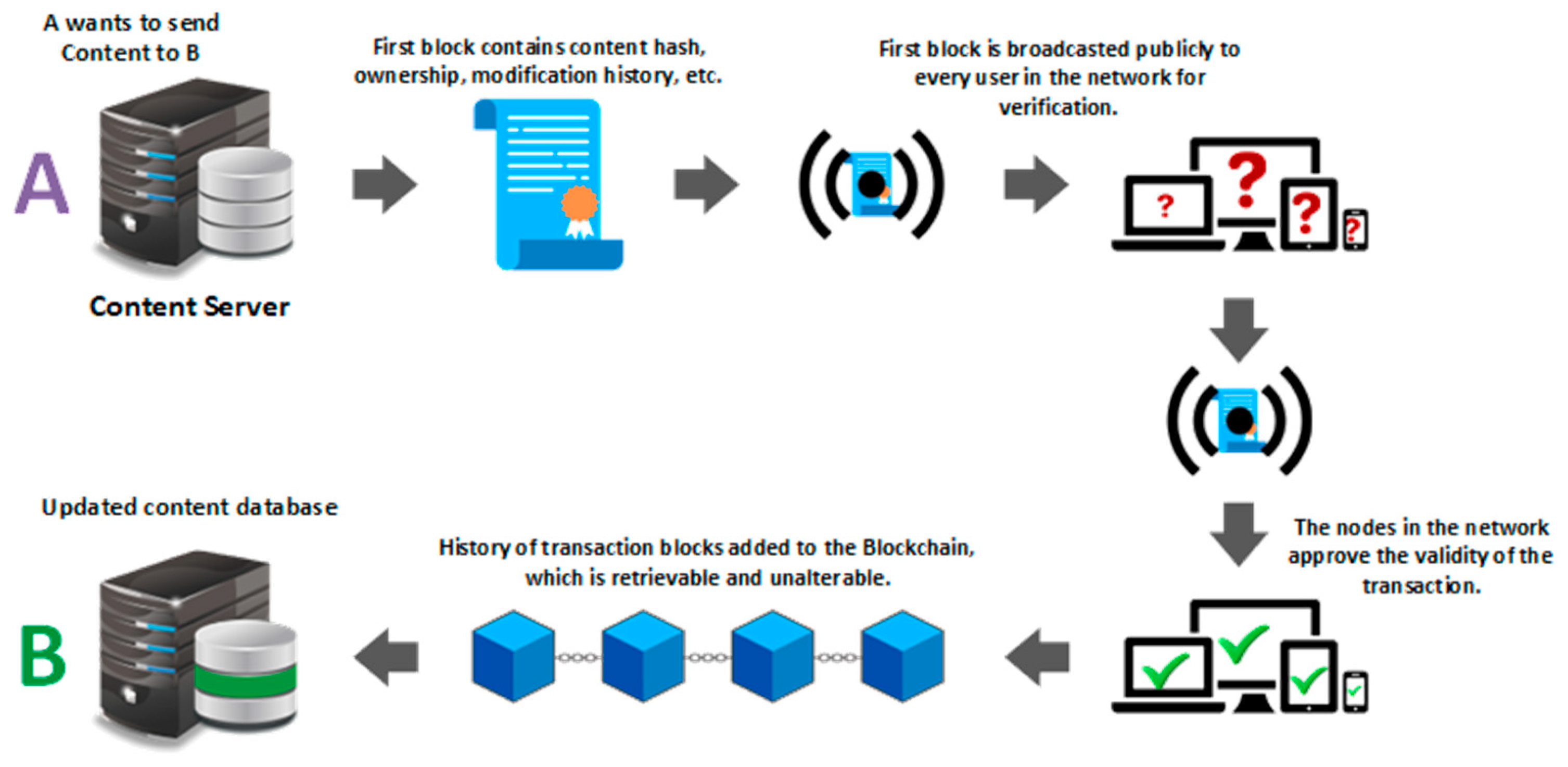
2.2. How Blockchain Technology Works
2.2.1. Consensus Algorithms
2.2.1.1. Proof of Work (PoW)
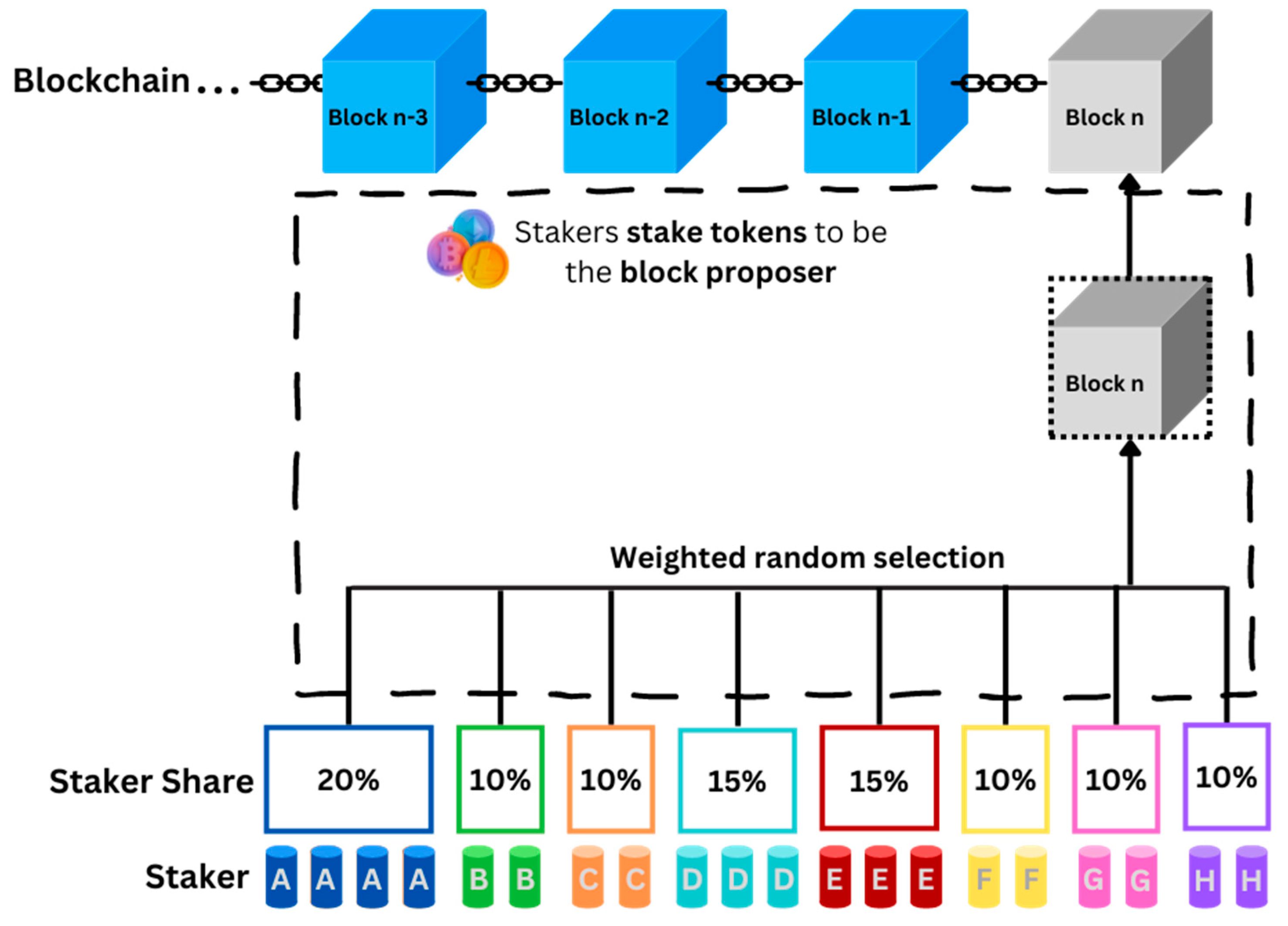
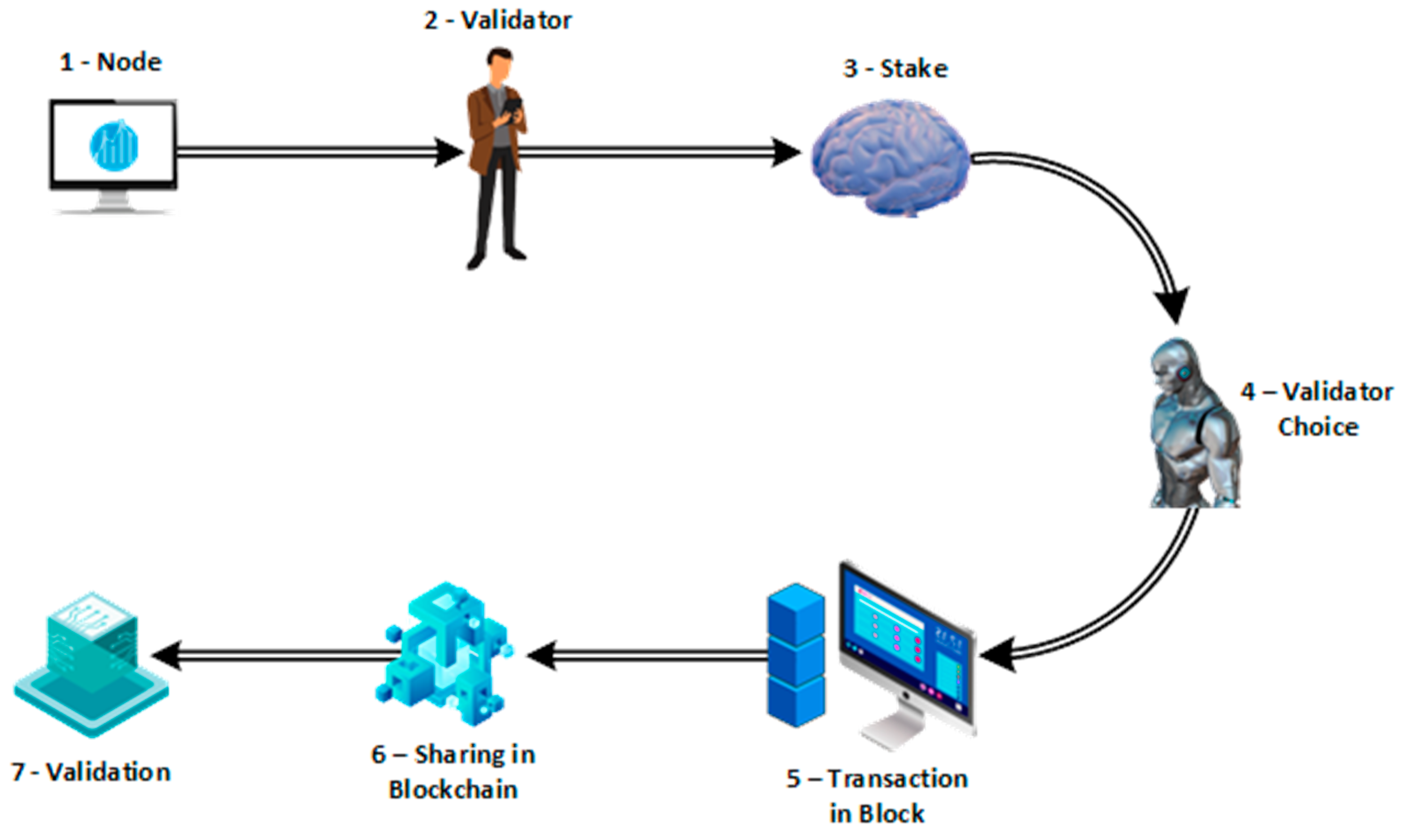
2.2.1.2. Proof of Stake (PoS)
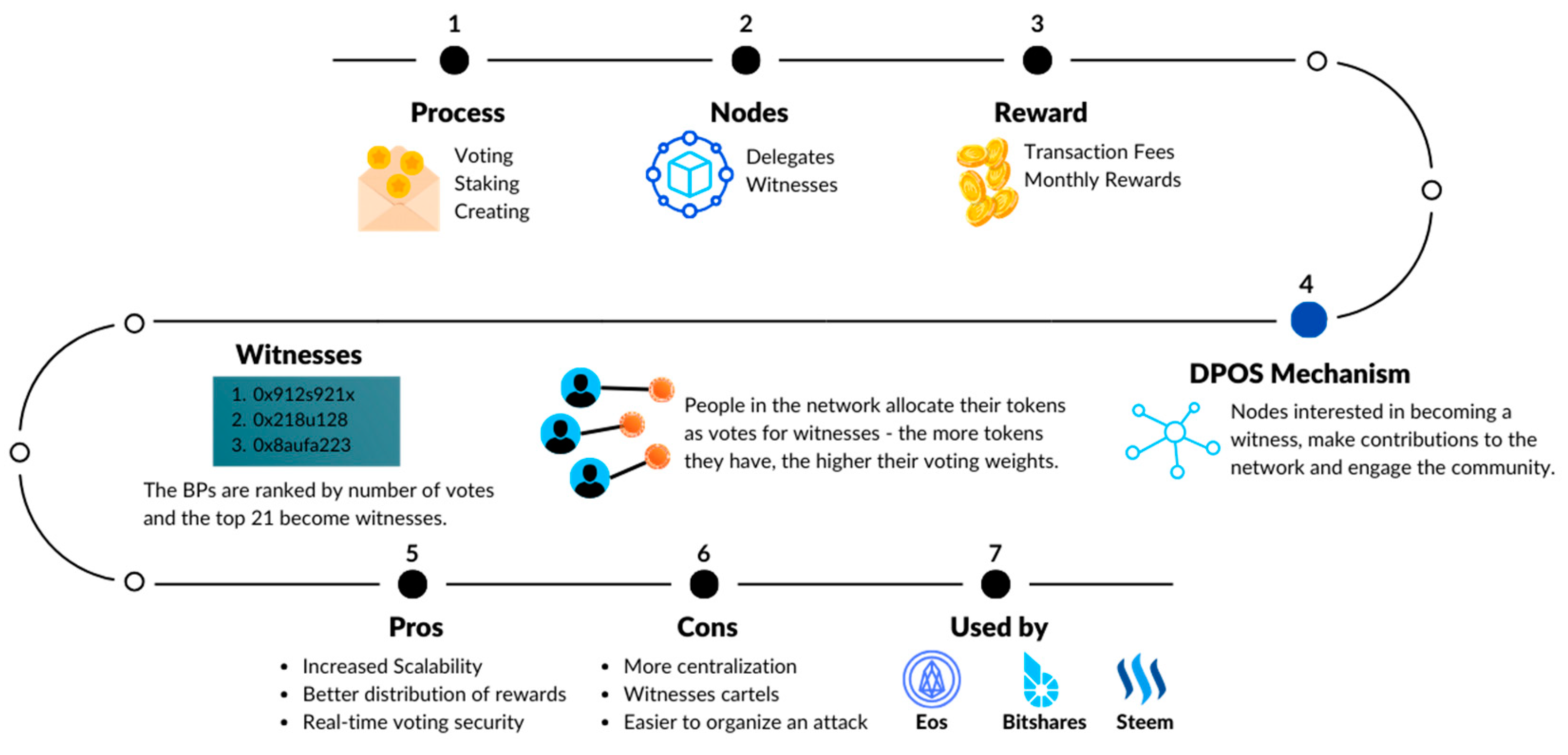
2.2.1.3. Delegated Proof of Stake (DPoS)
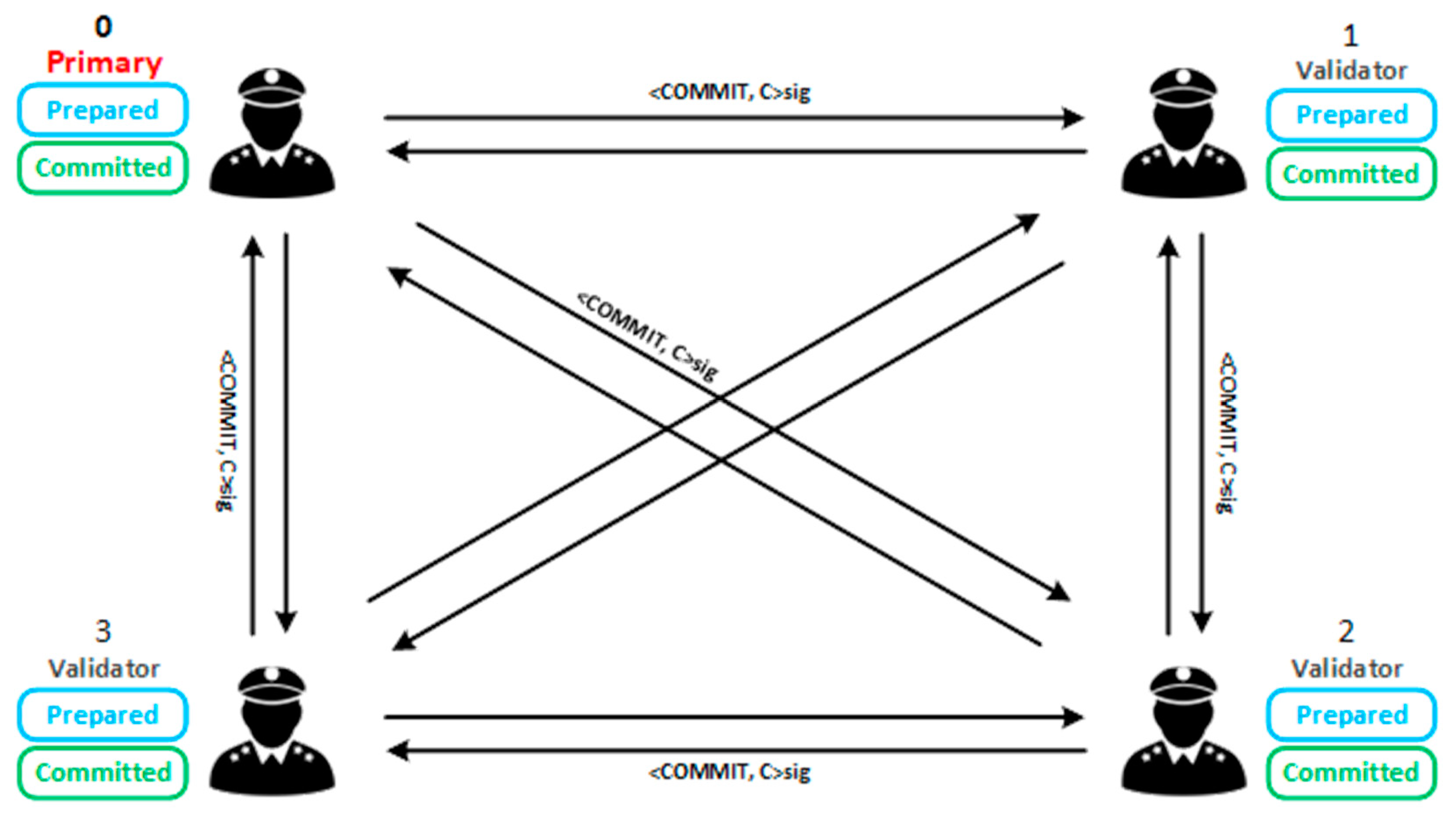
2.2.1.4. Practical Byzantine Fault Tolerance (PBFT)
2.2.1.5. Proof of Authority (PoA)
| Consensus Mechanism | Energy Consumption | Security | Scalability | Use Cases |
|---|---|---|---|---|
| Proof of Work (PoW) | High | High, but energy-intensive and vulnerable to 51% attacks | Limited by transaction throughput (e.g., Bitcoin ~7 transactions per second) | Bitcoin, Ethereum (transitioning away), Litecoin |
| Proof of Stake (PoS) | Low to Moderate | High, dependent on the amount of staked tokens | Better than PoW, but still faces challenges with network congestion | Ethereum 2.0, Cardano, Tezos |
| Delegated Proof of Stake (DPoS) | Low | High, but relies on a smaller number of validators | High scalability due to fewer validators needed for consensus | EOS, Tron, Steem |
| Byzantine Fault Tolerance (BFT) | Moderate | Very high, resilient to up to 1/3 of nodes failing or acting maliciously | High scalability with fast transaction finality | Hyperledger Fabric, Tendermint (used in Cosmos) |
| Proof of Authority (PoA) | Low | High, but depends on the trustworthiness of authorities | High scalability with quick consensus due to limited validators | VeChain, POA Network, Private blockchains |
3. Distributed Systems: Concepts and Challenges
3.1. Core Concepts of Distributed Systems
- Voting is a cooperative algorithm used by decentralized systems in order to make decisions collectively. In such a network, each node will place its vote on certain decisions like which version of a specific set of data is correct. The nodes (or computers) will communicate their “votes” with each other, based on a set of rules that each one has, subsequently making a decision based on the total number of votes the corresponding option gathered [7].
- Token Ring is another cooperative algorithm tasked with managing the network’s communication system. In this kind of network, all nodes are connected with each other in the shape of a ring. Within this ring of nodes, there is a digital token which moves around the network, to the node that wants to send a message. Without this token, a node cannot communicate with the other nodes in the network. Once a node has sent its message, it passes the token on to the next node in line to communicate [7].
- Market-based is the third cooperative algorithm of the list that is being employed in a decentralized distributed system. This algorithm works like a “trading marketplace”; nodes offer specific resources and ask for something else in return. For example, a node may offer processing power to another node in exchange for some storage space. These algorithms help a network allocate its resources in the most efficient way, taking into consideration each node’s demands and maximizing the network’s overall performance.
| Type | Description |
|---|---|
| Access | This kind of transparency hides from the end-user the data behind the system or the way this data is accessed. A prime example of this is ATMs. We do not see how they work but they do their job and we get our money. |
| Location | The location transparency hides from the user where a system’s resources (or services or files) are located but it can be accessed as if it were a user’s local system. |
| Concurrency | This type of transparency allows for multiple users to access resources all at the same time, without any of them interfering in the others’ work. One example of this transparency is the way colleagues can work on the same text document simultaneously, in real time. |
| Replication | Replication transparency makes sure to hide the replicated resources and data from the user and only show them one instance of the data they require. |
| Failure | This transparency hides from the user a system’s failure and recovery of its components. Every time a server crashes, a user’s request is automatically rerouted and executed by another server, without the user ever realizing the crash. |
| Migration | Migration transparency allows a system to transfer its resources and processes within the system, without the user ever noticing or being affected by it. |
| Performance | The system has the ability to reconfigure itself in order to improve its performance, again without the end-user ever noticing or being affected by this process. |
3.2. Challenges in Distributed Systems
| Type | Description |
|---|---|
| Preventive maintenance | This technique involves the regular maintenance of the entire system and all of its components in order to keep it robust and prevent its failure. |
| Predictive analysis | This technique is about analyzing patterns and behaviors of a system, as well as its overall performance, in order to identify potential issues that could cause system failure and address them properly. It works much like the process of weather forecasting. |
| Rejuvenation | This technique involves the frequent rebooting of a system, or parts of it, in order to clear any errors or bugs that may have accumulated in the system over a period of time. |
| Type | Description |
|---|---|
| Redundancy | This technique involves adding extra hardware or software that are not necessary for a system to work properly, but can be utilized in case of a failure, in order to provide a fallback solution. You can think of it as having a spare tyre in the car’s trunk, in case of a tyre burst. |
| Replication | This method involves the duplication of important data or components across different parts of a system so that every time a failure occurs, a copy can be deployed without interrupting the system’s main functions. |
| Checkpoints and Rollbacks | This technique works much like an operating system’s restore point feature; it saves a state of the system at certain points (known as checkpoints) that works well and, when a failure happens, the system will roll back to its last saved point, thus restarting its function from that specific checkpoint. |
| Failover | This last technique is about having an entire backup system that will start working automatically once the main system faces a failure or crashes entirely. The process has to happen so quickly that the user won’t notice any difference in the way the system works. Think of it as a backup power generator that starts working automatically once the main power system of a building goes out. |
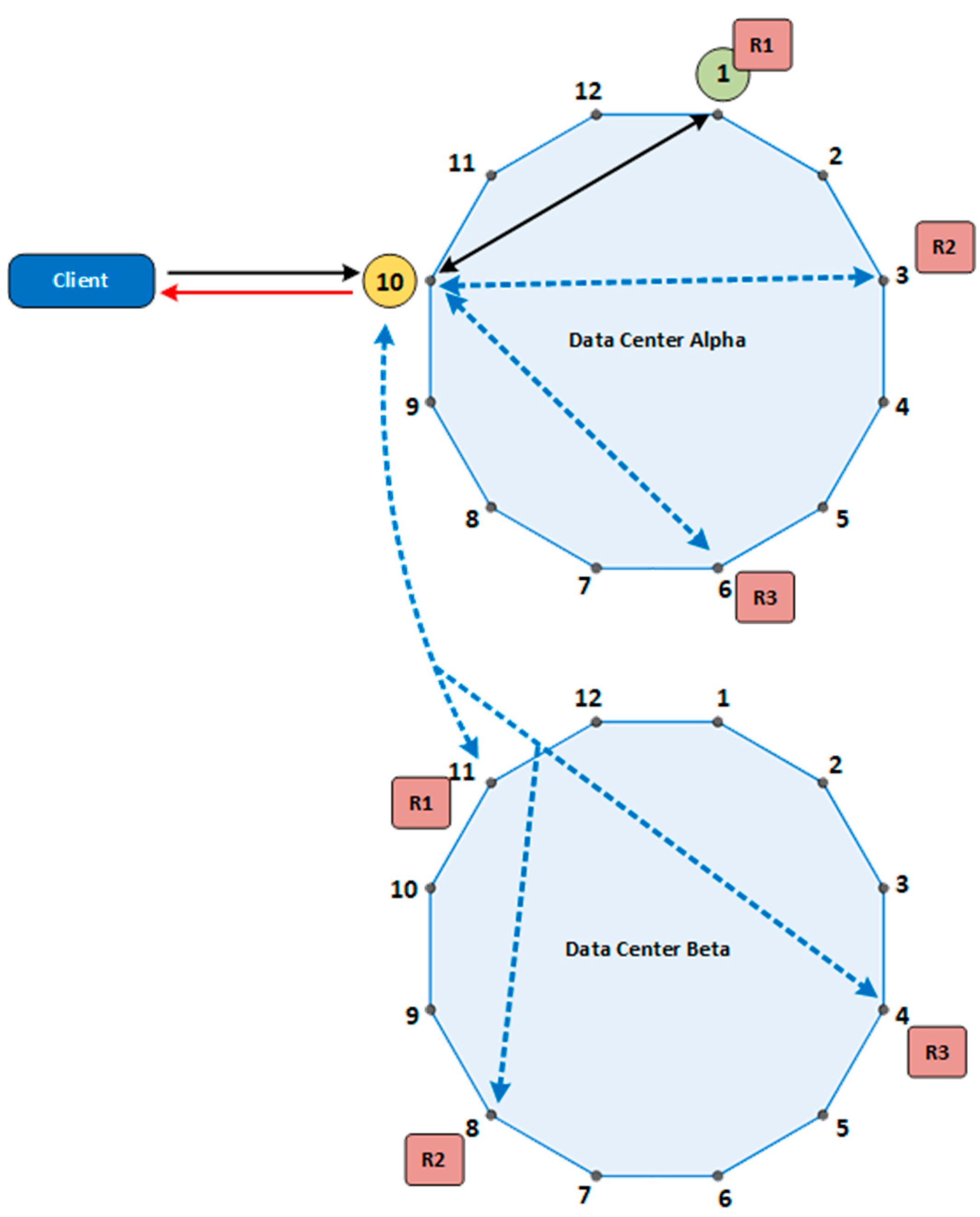
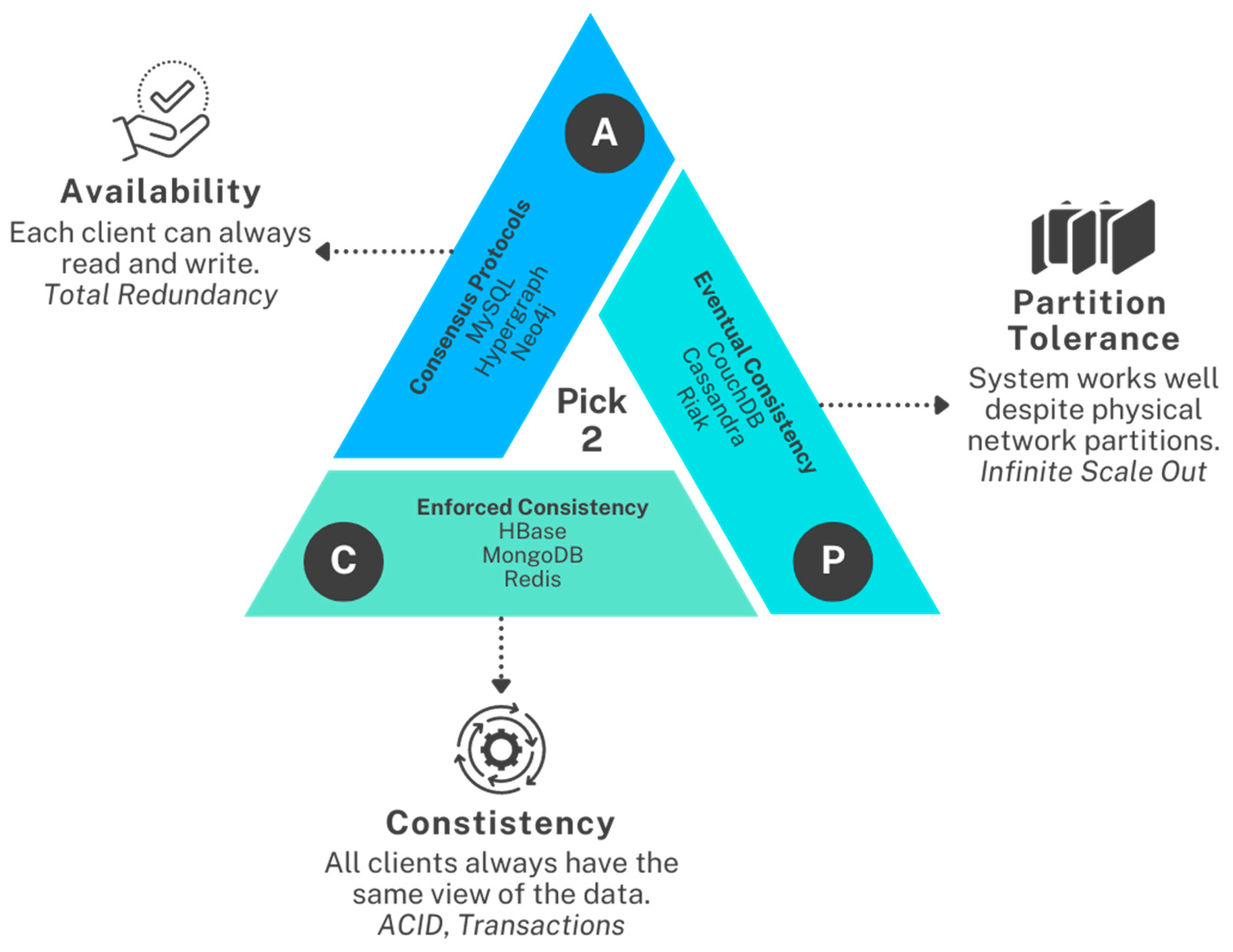
- Consistency (C): Every read from the system receives the most recent write or an error. In other words, all nodes see the same data at the same time.
- Availability (A): Every request (read or write) receives a non-error response, without the guarantee that it contains the most recent write.
- Partition Tolerance (P): The system continues to operate despite network partitions, where communication between some subsets of nodes is lost.
- CA (Consistency and Availability): These systems reject partitions, meaning they require a consistent network. If a partition occurs, the system must either sacrifice consistency or availability.
- CP (Consistency and Partition Tolerance): These systems remain consistent in the presence of network partitions but may not be available to all nodes.
- AP (Availability and Partition Tolerance): These systems remain available even when network partitions occur but may not guarantee consistency.
- ➢
- Databases like Cassandra and DynamoDB: Prioritize availability and partition tolerance (AP), allowing them to remain available during network partitions but possibly returning stale data.
- ➢
- Ø Systems like HBase and MongoDB: Often focus on consistency and partition tolerance (CP), ensuring data consistency across partitions at the cost of potential availability issues during network failures.
- ➢
- Ø Relational databases with distributed architectures: Tend to focus on consistency and availability (CA), often at the expense of partition tolerance, requiring a reliable network to function correctly.
4. The Intersection of Blockchain and Distributed Systems
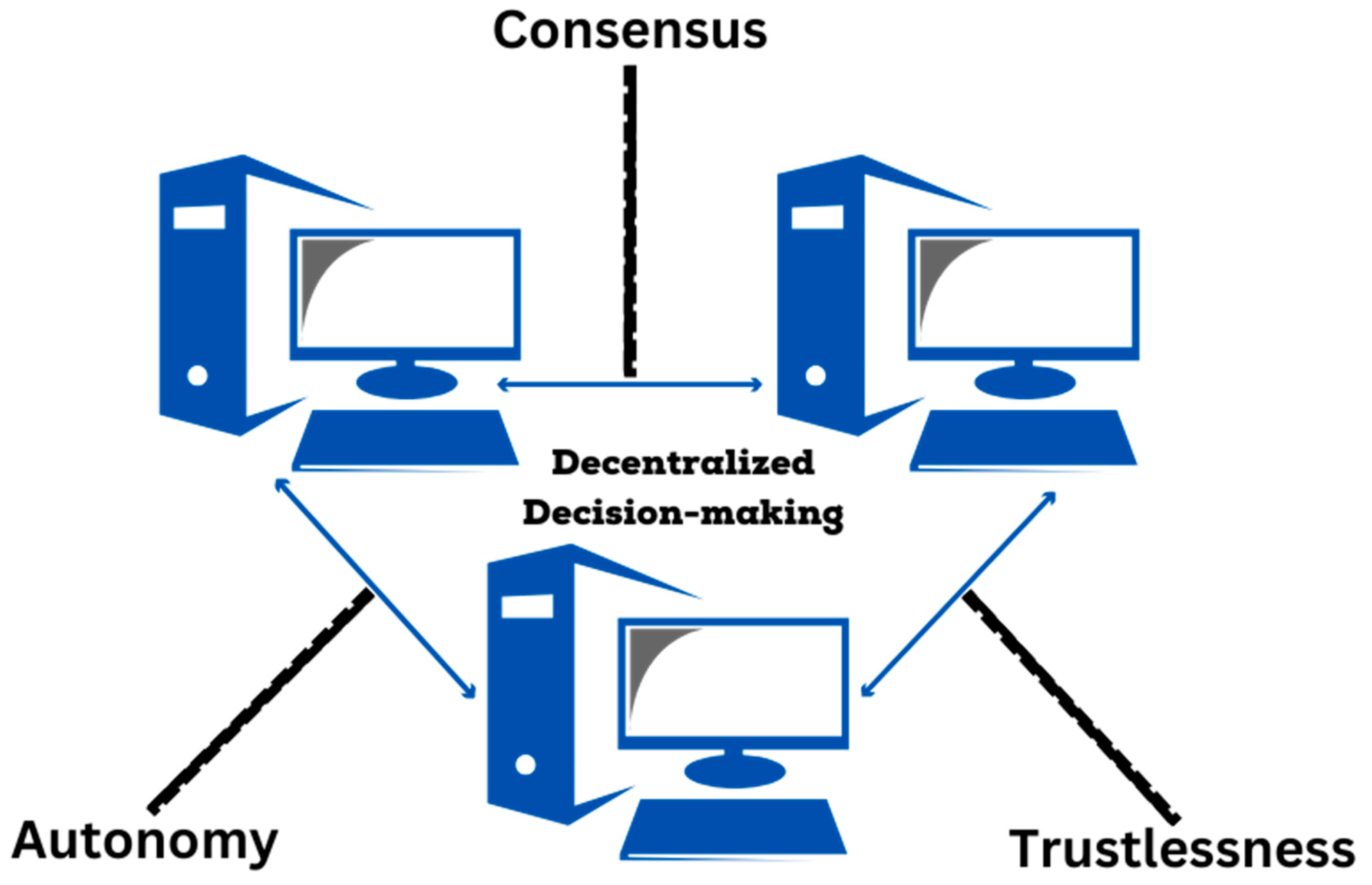
5. Decentralized Decision-Making
5.1. Key Principles of Decentralized Decision-Making
5.2. Game Theory and Decentralized Decision-Making
5.3. Decentralized Decision-Making Mechanisms
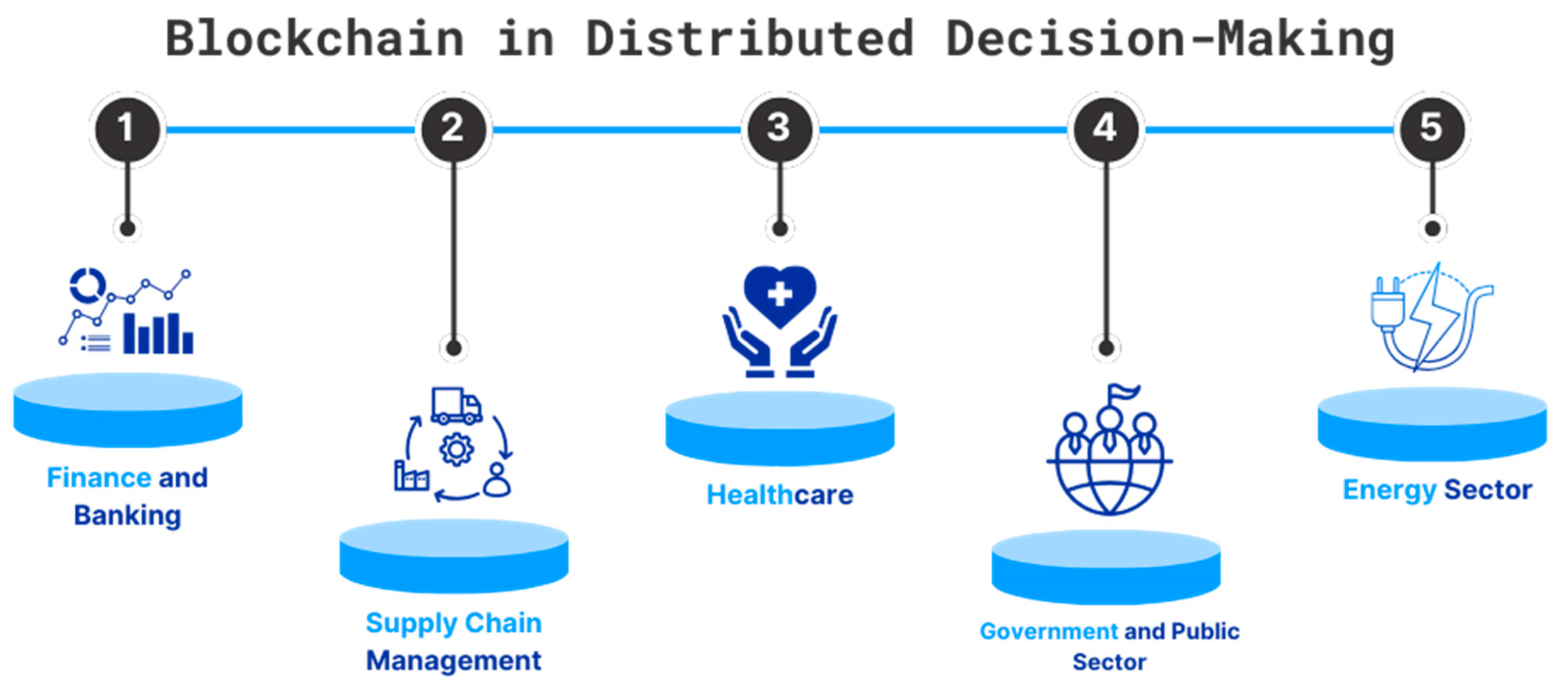
6. Applications of Blockchain in Distributed Decision-Making
6.1. Finance and Banking
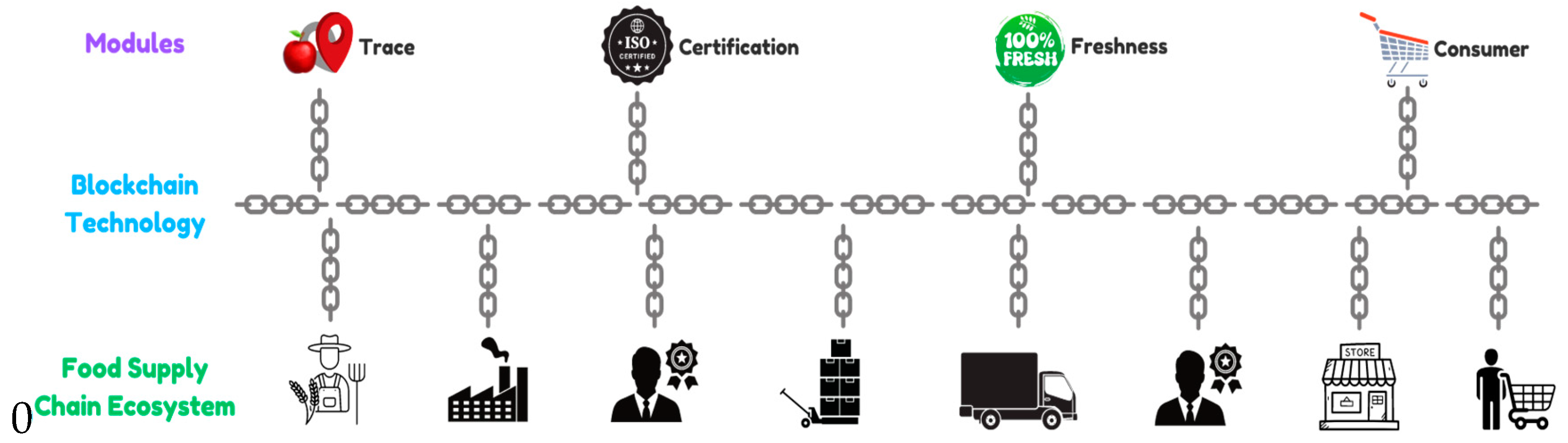
6.2. Supply Chain Management
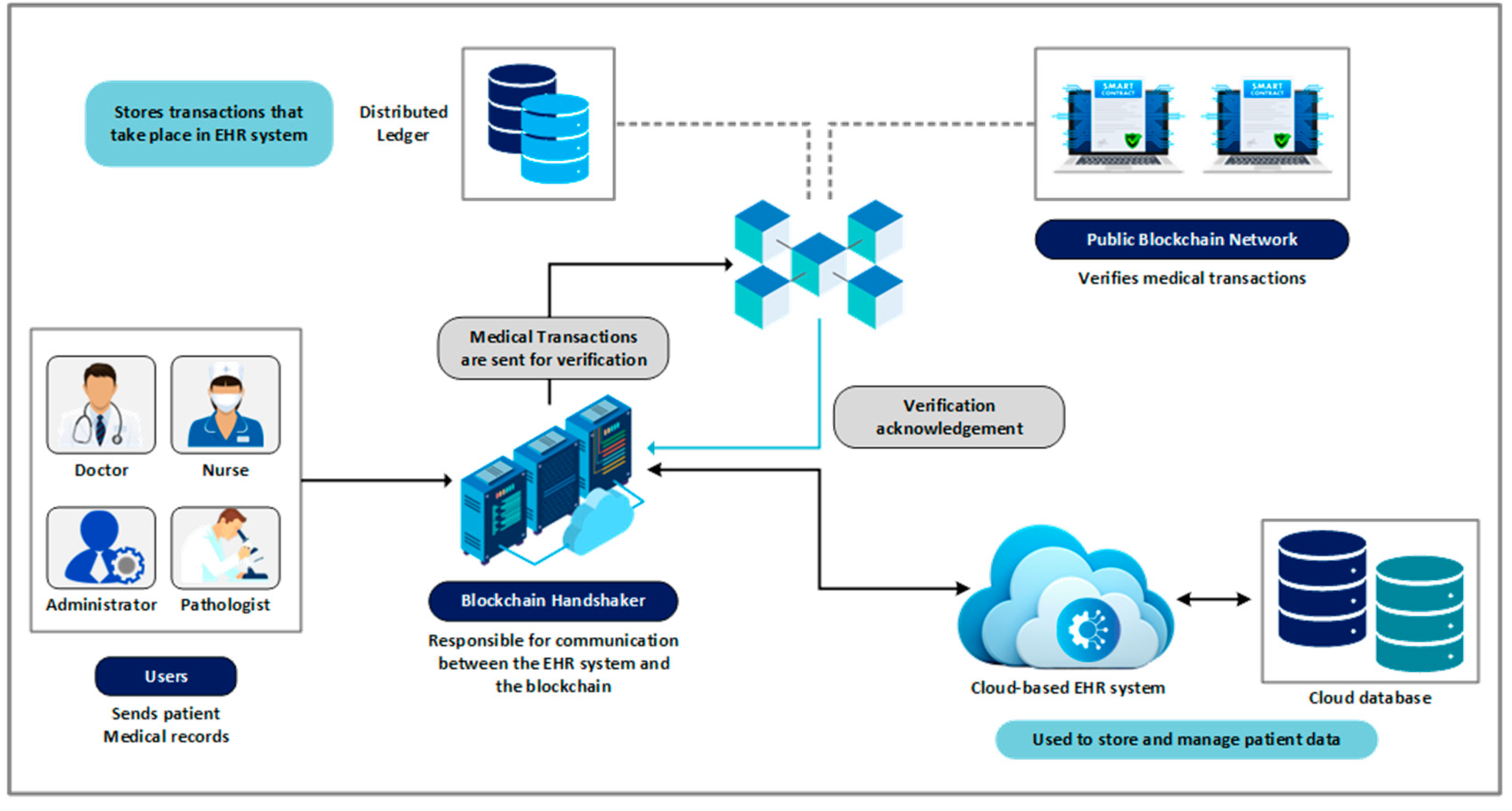
6.3. Healthcare
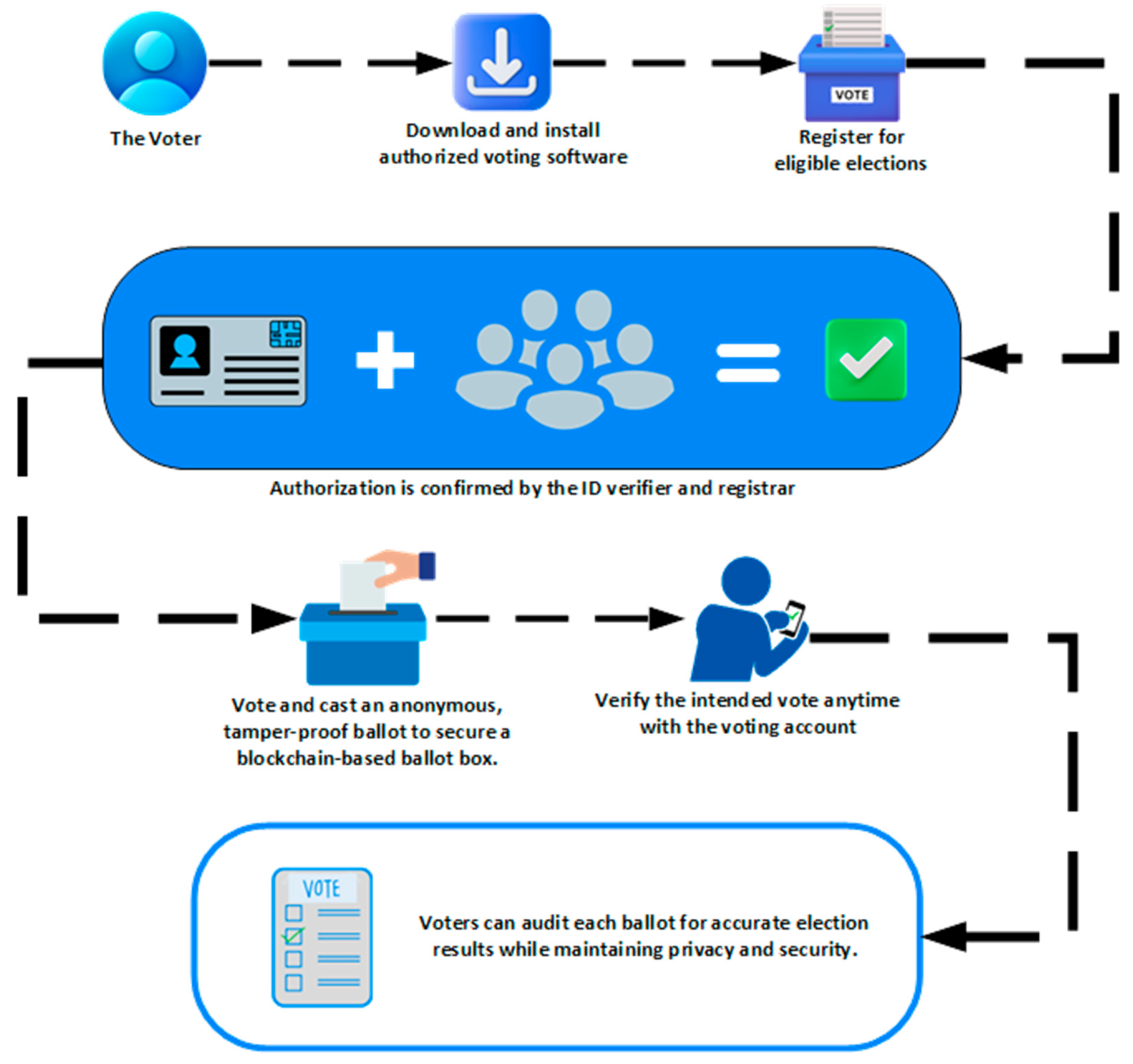
6.4. Government and Public Sector
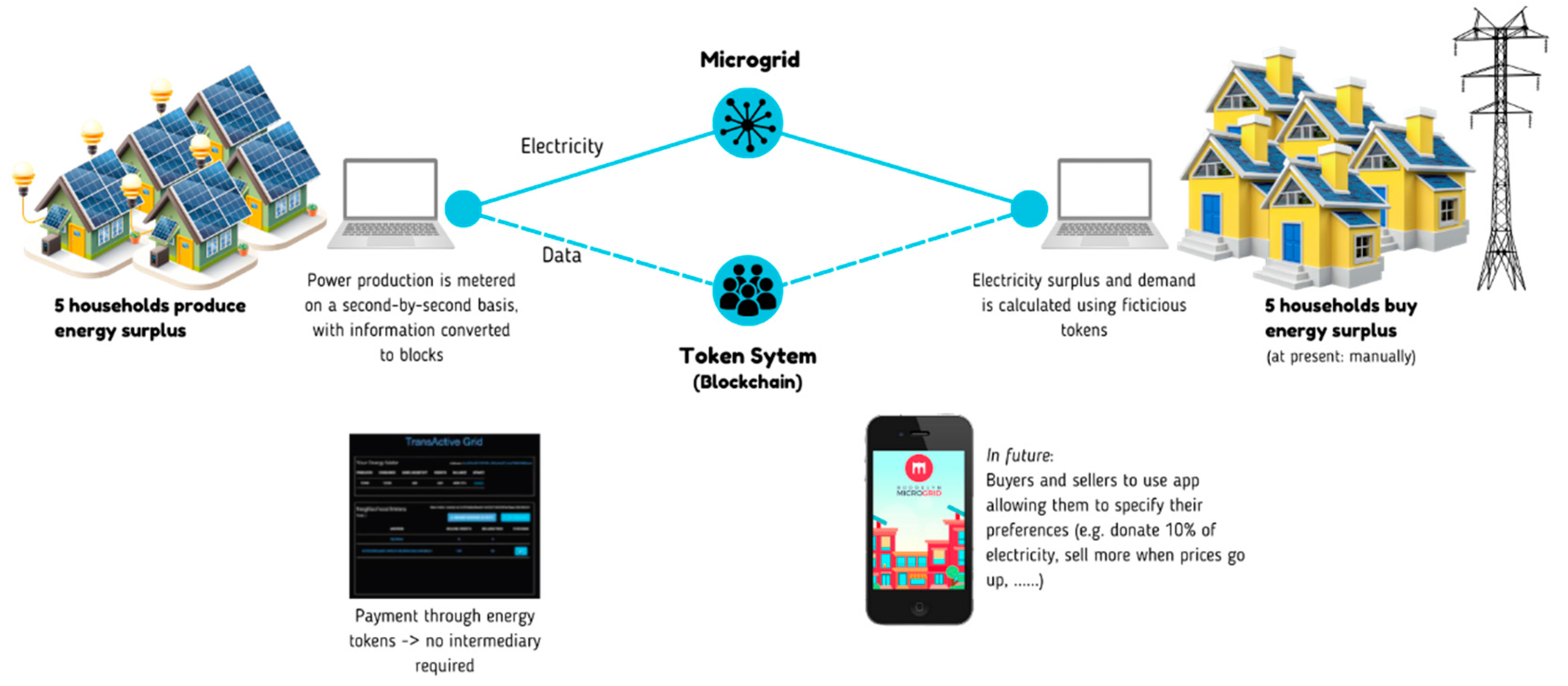
6.5. Energy Sector
6.6. Case Studies and Real-World Examples
7. Big Data and Blockchain in Decision-Making
7.1. Enabling Real-Time Data Processing and Decision-Making in Decentralized Systems
7.2. Facilitating Predictive Analytics and Automation
7.2.1. Predictive Analytics in Decentralized Systems
7.2.2. Enhancing Decision-Making with Predictive Analytics and Automation
8. Challenges and Potential Issues in Integrating Big Data and Blockchain for Decentralized Decision-Making
| Type | Summary |
|---|---|
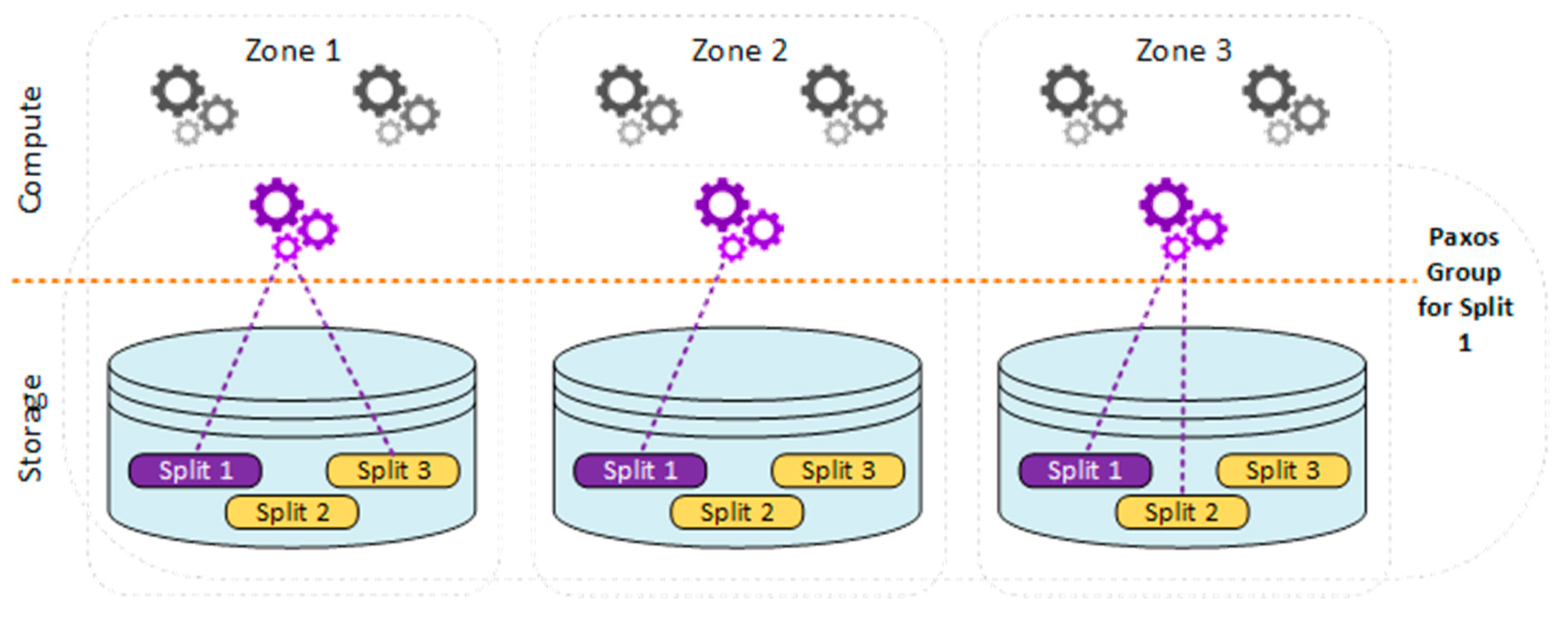
| Scalability and Performance | Integrating Big Data and blockchain faces scalability issues due to large datasets and high transaction volumes. Blockchain networks, particularly those using Proof of Work (PoW), have limited transaction throughput and high latency, which can slow down data processing. Solutions like sharding and layer-two protocols are being developed to improve scalability and performance. |
| Data Privacy and Security | Blockchain enhances data security but poses privacy concerns due to its transparency. Ensuring data confidentiality in sectors like healthcare and finance is challenging. Techniques like zero-knowledge proofs and homomorphic encryption are being explored to balance privacy and transparency. |
| Interoperability and Integration | Integrating blockchain with existing Big Data systems presents interoperability challenges, requiring seamless technical compatibility and alignment of data formats and protocols. Efforts are underway to develop standardized protocols and middleware solutions to facilitate integration and interoperability between blockchain networks and traditional systems. |
| Regulatory and Compliance Issues | The evolving regulatory landscape for blockchain and Big Data presents challenges in compliance with data protection laws. Blockchain's immutable nature conflicts with regulations requiring data modification or deletion. Hybrid blockchain models and regulatory sandboxes are being explored to ensure compliance while leveraging blockchain technology. |
| Cost and Resource Allocation | Implementing blockchain and Big Data solutions is costly, requiring significant investment in hardware, software, and skilled personnel. Energy consumption, particularly in PoW systems, is a major concern. Transitioning to energy-efficient consensus mechanisms and using cloud-based blockchain services can help manage costs and resources. |
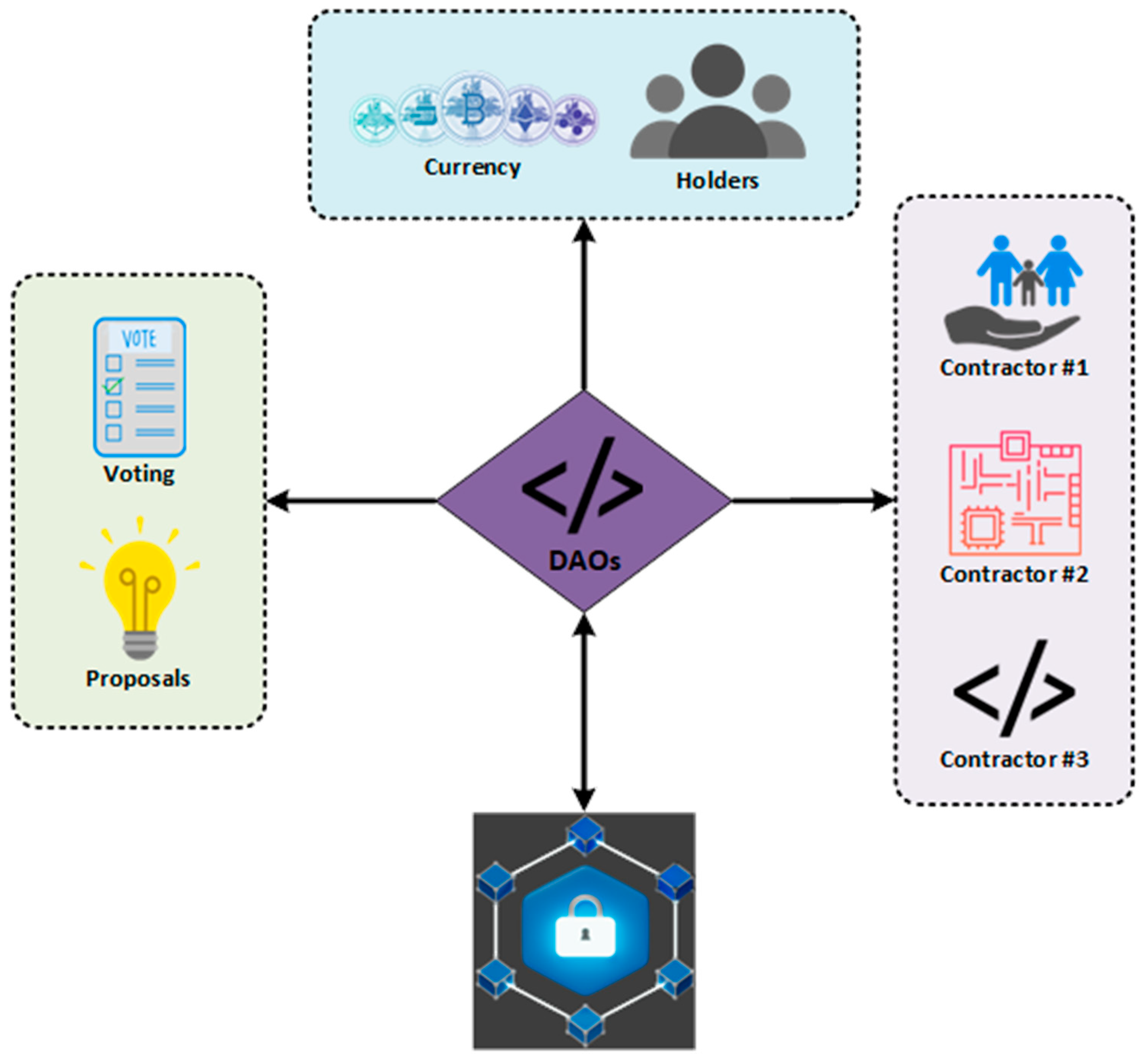
| Governance and Consensus | Effective governance and consensus mechanisms are crucial for decentralized decision-making. Ensuring inclusivity, transparency, and efficiency while preventing power concentration is challenging. Innovative governance models like decentralized autonomous organizations (DAOs) and research into consensus algorithms aim to improve decision-making processes and network stability. |
9. Future Directions and Emerging Trends
10. Conclusions
Author Contributions
Conflicts of Interest
References
- Schinckus, C. The good, the bad and the ugly: An overview of the sustainability of blockchain technology. Energy Res. Soc. Sci. 2020, 69, 101614. [Google Scholar] [CrossRef]
- Gad, A.G.; Mosa, D.T.; Abualigah, L.; Abohany, A.A. Emerging Trends in Blockchain Technology and Applications: A Review and Outlook. J. King Saud Univ. - Comput. Inf. Sci. 2022, 34, 6719–6742. [Google Scholar] [CrossRef]
- Zheng, Z. , Xie, S., Dai, H., Chen, X., & Wang, H. (2017, June). An overview of blockchain technology: Architecture, consensus, and future trends. In 2017 IEEE international congress on big data (BigData congress) (pp. 557-564). Ieee.
- Bhutta, M.N.M.; Khwaja, A.A.; Nadeem, A.; Ahmad, H.F.; Khan, M.K.; Hanif, M.A.; Song, H.; Alshamari, M.; Cao, Y. A Survey on Blockchain Technology: Evolution, Architecture and Security. IEEE Access 2021, 9, 61048–61073. [Google Scholar] [CrossRef]
- Guo, H.; Yu, X. A survey on blockchain technology and its security. Blockchain: Res. Appl. 2022, 3. [Google Scholar] [CrossRef]
- Andoni, M.; Robu, V.; Flynn, D.; Abram, S.; Geach, D.; Jenkins, D.; McCallum, P.; Peacock, A. Blockchain technology in the energy sector: A systematic review of challenges and opportunities. Renew. Sustain. Energy Rev. 2018, 100, 143–174. [Google Scholar] [CrossRef]
- Malek, S. , Mikic-Rakic, M., & Medvidovic, N. (2005, November). A decentralized redeployment algorithm for improving the availability of distributed systems. In International Working Conference on Component Deployment (pp. 99-114). Berlin, Heidelberg: Springer Berlin Heidelberg.
- Kuhlenkamp, J.; Klems, M.; Röss, O. Benchmarking scalability and elasticity of distributed database systems. Proc. Vldb Endow. 2014, 7, 1219–1230. [Google Scholar] [CrossRef]
- Creel, K.A. Transparency in Complex Computational Systems. Philos. Sci. 2020, 87, 568–589. [Google Scholar] [CrossRef]
- Ledmi, A. , Bendjenna, H., & Hemam, S. M. (2018, October). Fault tolerance in distributed systems: A survey. In 2018 3rd International Conference on Pattern Analysis and Intelligent Systems (PAIS) (pp. 1-5). IEEE.
- Nanthini, N. , Vidhyasri, R., & Anand, V. V. (2024, April). Fault Tolerance Using AutoScaling in Amazon Web Services. In 2024 International Conference on Computing and Data Science (ICCDS) (pp. 1-6). IEEE.
- Ahmed, J.; Karpenko, A.; Tarasyuk, O.; Gorbenko, A.; Sheikh-Akbari, A. Consistency issue and related trade-offs in distributed replicated systems and databases: a review. Radioelectron. Comput. Syst. 2023, 171–179. [Google Scholar] [CrossRef]
- Hogade, N.S.; Pasricha, S.; Siegel, H.J. Energy and Network Aware Workload Management for Geographically Distributed Data Centers. IEEE Trans. Sustain. Comput. 2022, 7, 400–413. [Google Scholar] [CrossRef]
- Lee, E. A. , Bateni, S., Lin, S., Lohstroh, M., & Menard, C. (2021). Quantifying and generalizing the CAP theorem. arXiv:2109.07771.
- Skorykh, O. (2022). Migration of NoSQL (Cassandra) to relational database (Postgres) on high demanded distributed system (Doctoral dissertation, Hochschule für Angewandte Wissenschaften Hamburg).
- Adoni, H.W.Y.; Nahhal, T.; Krichen, M.; Aghezzaf, B.; Elbyed, A. A survey of current challenges in partitioning and processing of graph-structured data in parallel and distributed systems. Distrib. Parallel Databases 2019, 38, 495–530. [Google Scholar] [CrossRef]
- Brewer, E.A. Towards robust distributed systems (abstract). PODC00: ACM Symposium on Principles of Distributed Computing. LOCATION OF CONFERENCE, United StatesDATE OF CONFERENCE; p. 7.
- Khoshaba, O. , Grechaninov, V., Molodetska, T., Lopushanskyi, A., & Zavertailo, K. (2022, November). Study of the Workspace Model in Distributed Structures Using CAP Theorem. In International scientific-practical conference (pp. 229-242). Cham: Springer Nature Switzerland.
- Singh, S.; Hosen, A.S.M.S.; Yoon, B. Blockchain Security Attacks, Challenges, and Solutions for the Future Distributed IoT Network. IEEE Access 2021, 9, 13938–13959. [Google Scholar] [CrossRef]
- Yao, Q.; Wang, Q.; Zhang, X.; Fei, J. Dynamic Access Control and Authorization System based on Zero-trust architecture. CCRIS 2020: 2020 International Conference on Control, Robotics and Intelligent System. LOCATION OF CONFERENCE, ChinaDATE OF CONFERENCE;
- Daswani, N. , Elbayadi, M., Daswani, N., & Elbayadi, M. (2021). The Equifax Breach. Big Breaches: Cybersecurity Lessons for Everyone, 75-95.
- Huang, H.; Lin, J.; Zheng, B.; Zheng, Z.; Bian, J. When Blockchain Meets Distributed File Systems: An Overview, Challenges, and Open Issues. IEEE Access 2020, 8, 50574–50586. [Google Scholar] [CrossRef]
- B. Rawat, D. B. Rawat, D., Chaudhary, V., & Doku, R. (2020). Blockchain technology: Emerging applications and use cases for secure and trustworthy smart systems. Journal of Cybersecurity and Privacy, 1(1), 4-18.
- Panwar, A.; Bhatnagar, V. Distributed Ledger Technology (DLT): The Beginning of a Technological Revolution for Blockchain. 2020 2nd International Conference on Data, Engineering and Applications (IDEA). LOCATION OF CONFERENCE, IndiaDATE OF CONFERENCE; pp. 1–5.
- Zhou, S.; Li, K.; Xiao, L.; Cai, J.; Liang, W.; Castiglione, A. A Systematic Review of Consensus Mechanisms in Blockchain. Mathematics 2023, 11, 2248. [Google Scholar] [CrossRef]
- Esmat, A.; de Vos, M.; Ghiassi-Farrokhfal, Y.; Palensky, P.; Epema, D. A novel decentralized platform for peer-to-peer energy trading market with blockchain technology. Appl. Energy 2020, 282, 116123. [Google Scholar] [CrossRef]
- Cherupally, S.R.; Boga, S.; Podili, P.; Kataoka, K. Lightweight and Scalable DAG based distributed ledger for verifying IoT data integrity. 2021 International Conference on Information Networking (ICOIN). LOCATION OF CONFERENCE, South KoreaDATE OF CONFERENCE; pp. 267–272.
- Zhao, W. From Traditional Fault Tolerance to Blockchain; Wiley: Hoboken, NJ, United States, 2021. [Google Scholar]
- Tikhomirov, S. , Moreno-Sanchez, P., & Maffei, M. (2020, September). A quantitative analysis of security, anonymity and scalability for the lightning network. In 2020 IEEE European Symposium on Security and Privacy Workshops (EuroS&PW) (pp. 387-396). IEEE.
- Krichen, M.; Ammi, M.; Mihoub, A.; Almutiq, M. Blockchain for Modern Applications: A Survey. Sensors 2022, 22, 5274. [Google Scholar] [CrossRef]
- Mueller-Bloch, C.; Andersen, J.V.; Spasovski, J.; Hahn, J. Understanding decentralization of decision-making power in proof-of-stake blockchains: an agent-based simulation approach. Eur. J. Inf. Syst. 2022, 1–20. [Google Scholar] [CrossRef]
- Singh, A.; Kumar, G.; Saha, R.; Conti, M.; Alazab, M.; Thomas, R. A survey and taxonomy of consensus protocols for blockchains. J. Syst. Arch. 2022, 127. [Google Scholar] [CrossRef]
- Cornito, C.M. Striking a Balance between Centralized and Decentralized Decision Making: A School-Based Management Practice for Optimum Performance. Int. J. Soc. Educ. Sci. 2021, 3, 656–669. [Google Scholar] [CrossRef]
- Truong, N.; Lee, G.M.; Sun, K.; Guitton, F.; Guo, Y. A blockchain-based trust system for decentralised applications: When trustless needs trust. Futur. Gener. Comput. Syst. 2021, 124, 68–79. [Google Scholar] [CrossRef]
- Dong, J.; Song, C.; Liu, S.; Yin, H.; Zheng, H.; Li, Y. Decentralized peer-to-peer energy trading strategy in energy blockchain environment: A game-theoretic approach. Appl. Energy 2022, 325. [Google Scholar] [CrossRef]
- Zhang, J.; Wu, M. Cooperation Mechanism in Blockchain by Evolutionary Game Theory. Complexity 2021, 2021, 1–9. [Google Scholar] [CrossRef]
- Kiayias, A. , & Zindros, D. (2020). Proof-of-work sidechains. In Financial Cryptography and Data Security: FC 2019 International Workshops, VOTING and WTSC, St. Kitts, St. Kitts and Nevis, –22, 2019, Revised Selected Papers 23 (pp. 21-34). Springer International Publishing. 18 February.
- Saleh, F. Blockchain without Waste: Proof-of-Stake. Rev. Financial Stud. 2020, 34, 1156–1190. [Google Scholar] [CrossRef]
- Saad, S.M.S.; Radzi, R.Z.R.M. Comparative Review of the Blockchain Consensus Algorithm Between Proof of Stake (POS) and Delegated Proof of Stake (DPOS). Int. J. Innov. Comput. 2020, 10. [Google Scholar] [CrossRef]
- Huang, J. , He, D., Obaidat, M. S., Vijayakumar, P., Luo, M., & Choo, K. K. R. (2021). The application of the blockchain technology in voting systems: A review. ACM Computing Surveys (CSUR), 54(3), 1-28.
- Khan, S.N.; Loukil, F.; Ghedira-Guegan, C.; Benkhelifa, E.; Bani-Hani, A. Blockchain smart contracts: Applications, challenges, and future trends. Peer-to-Peer Netw. Appl. 2021, 14, 2901–2925. [Google Scholar] [CrossRef]
- El Faqir, Y., Arroyo, J., & Hassan, S. (2020, August). An overview of decentralized autonomous organizations on the blockchain. In Proceedings of the 16th international symposium on open collaboration (pp. 1-8). [CrossRef].
- Taş, R.; Tanrıöver, Ö.Ö. A Systematic Review of Challenges and Opportunities of Blockchain for E-Voting. Symmetry 2020, 12, 1328. [Google Scholar] [CrossRef]
- Jafar, U.; Ab Aziz, M.J.; Shukur, Z. Blockchain for Electronic Voting System—Review and Open Research Challenges. Sensors 2021, 21, 5874. [Google Scholar] [CrossRef]
- Aufiero, S. , Ibba, G., Bartolucci, S., Destefanis, G., Neykova, R., & Ortu, M. (2024). Dapps ecosystems: Mapping the network structure of smart contract interactions. arXiv:2401.01991.
- Vacca, A.; Di Sorbo, A.; Visaggio, C.A.; Canfora, G. A systematic literature review of blockchain and smart contract development: Techniques, tools, and open challenges. J. Syst. Softw. 2020, 174, 110891. [Google Scholar] [CrossRef]
- Hauck, R. Blockchain, Smart Contracts and Intellectual Property. Using distributed ledger technology to protect, license and enforce intellectual property rights. Leg. Issues Digit. Age 2021, 1, 17–41. [Google Scholar] [CrossRef]
- Carvalho, A. Bringing transparency and trustworthiness to loot boxes with blockchain and smart contracts. Decis. Support Syst. 2021, 144, 113508. [Google Scholar] [CrossRef]
- Khatoon, A. A Blockchain-Based Smart Contract System for Healthcare Management. Electronics 2020, 9, 94. [Google Scholar] [CrossRef]
- Sookhak, M.; Jabbarpour, M.R.; Safa, N.S.; Yu, F.R. Blockchain and smart contract for access control in healthcare: A survey, issues and challenges, and open issues. J. Netw. Comput. Appl. 2020, 178, 102950. [Google Scholar] [CrossRef]
- Appel, I.; Grennan, J. Control of Decentralized Autonomous Organizations. AEA Pap. Proc. 2023, 113, 182–185. [Google Scholar] [CrossRef]
- Liu, L.; Zhou, S.; Huang, H.; Zheng, Z. From Technology to Society: An Overview of Blockchain-Based DAO. IEEE Open J. Comput. Soc. 2021, 2, 204–215. [Google Scholar] [CrossRef]
- Bellavitis, C.; Fisch, C.; Momtaz, P.P. The rise of decentralized autonomous organizations (DAOs): a first empirical glimpse. Ventur. Cap. 2022, 25, 187–203. [Google Scholar] [CrossRef]
- Liang, X., Lin, Y., Fu, H., Zhu, L., & Li, X. (2022). Rscfed: Random sampling consensus federated semi-supervised learning. In Proceedings of the IEEE/CVF conference on computer vision and pattern recognition (pp. 10154-10163).
- Hou, D.; Zhang, J.; Man, K.L.; Ma, J.; Peng, Z. A Systematic Literature Review of Blockchain-based Federated Learning: Architectures, Applications and Issues. 2021 2nd Information Communication Technologies Conference (ICTC). LOCATION OF CONFERENCE, ChinaDATE OF CONFERENCE; pp. 302–307.
- De Filippi, P. , & Lavayssière, X. (2020). Blockchain technology: Toward a decentralized governance of digital platforms?. The Great Awakening: New Modes of Life amidst Capitalist Ruins, 185-222.
- Zwitter, A.; Hazenberg, J. Decentralized Network Governance: Blockchain Technology and the Future of Regulation. Front. Blockchain 2020, 3. [Google Scholar] [CrossRef]
- Singh, S. , Wable, S., & Kharose, P. (2021). A review of e-Voting system based on blockchain technology. International Journal of New Practices in Management and Engineering, 10(04), 09-13.
- Patel, R.; Migliavacca, M.; Oriani, M.E. Blockchain in banking and finance: A bibliometric review. Res. Int. Bus. Finance 2022, 62. [Google Scholar] [CrossRef]
- Ullah, N.; Al-Rahmi, W.M.; Alfarraj, O.; Alalwan, N.; Alzahrani, A.I.; Ramayah, T.; Kumar, V. Hybridizing cost saving with trust for blockchain technology adoption by financial institutions. Telematics Informatics Rep. 2022, 6. [Google Scholar] [CrossRef]
- Tsao, Y.-C.; Vu, T.-L. A decentralized microgrid considering blockchain adoption and credit risk. J. Oper. Res. Soc. 2021, 73, 2116–2128. [Google Scholar] [CrossRef]
- Dashkevich, N.; Counsell, S.; Destefanis, G. Blockchain Application for Central Banks: A Systematic Mapping Study. IEEE Access 2020, 8, 139918–139952. [Google Scholar] [CrossRef]
- Queiroz, M.M.; Telles, R.; Bonilla, S.H. Blockchain and supply chain management integration: a systematic review of the literature. Supply Chain Manag. Int. J. 2019, 25, 241–254. [Google Scholar] [CrossRef]
- Moosavi, J.; Naeni, L.M.; Fathollahi-Fard, A.M.; Fiore, U. Blockchain in supply chain management: A review, bibliometric, and network analysis. Environ. Sci. Pollut. Res. 2021, 1–15. [Google Scholar] [CrossRef]
- Sunny, J.; Undralla, N.; Pillai, V.M. Supply chain transparency through blockchain-based traceability: An overview with demonstration. Comput. Ind. Eng. 2020, 150, 106895. [Google Scholar] [CrossRef]
- Bader, L.; Pennekamp, J.; Matzutt, R.; Hedderich, D.; Kowalski, M.; Lücken, V.; Wehrle, K. Blockchain-based privacy preservation for supply chains supporting lightweight multi-hop information accountability. Inf. Process. Manag. 2021, 58. [Google Scholar] [CrossRef]
- Haleem, A.; Javaid, M.; Singh, R.P.; Suman, R.; Rab, S. Blockchain technology applications in healthcare: An overview. Int. J. Intell. Networks 2021, 2, 130–139. [Google Scholar] [CrossRef]
- Attaran, M. Blockchain technology in healthcare: Challenges and opportunities. Int. J. Heal. Manag. 2020, 15, 70–83. [Google Scholar] [CrossRef]
- Mann, S.P.; Savulescu, J.; Ravaud, P.; Benchoufi, M. Blockchain, consent and prosent for medical research. J. Med Ethic- 2020, 47, 244–250. [Google Scholar] [CrossRef]
- Odeh, A.; Keshta, I.; Abu Al-Haija, Q. Analysis of Blockchain in the Healthcare Sector: Application and Issues. Symmetry 2022, 14, 1760. [Google Scholar] [CrossRef]
- Datta, A. (2021). Blockchain enabled digital government and public sector services: A survey. Blockchain and the Public Sector: Theories, Reforms, and Case Studies, 175-195.
- Cagigas, D.; Clifton, J.; Diaz-Fuentes, D.; Fernandez-Gutierrez, M. Blockchain for Public Services: A Systematic Literature Review. IEEE Access 2021, 9, 13904–13921. [Google Scholar] [CrossRef]
- Soner, S.; Litoriya, R.; Pandey, P. Exploring Blockchain and Smart Contract Technology for Reliable and Secure Land Registration and Record Management. Wirel. Pers. Commun. 2021, 121, 2495–2509. [Google Scholar] [CrossRef]
- Wang, Q.; Su, M. Integrating blockchain technology into the energy sector — from theory of blockchain to research and application of energy blockchain. Comput. Sci. Rev. 2020, 37, 100275. [Google Scholar] [CrossRef]
- Kumar, N.M.; Chand, A.A.; Malvoni, M.; Prasad, K.A.; Mamun, K.A.; Islam, F.; Chopra, S.S. Distributed energy resources and the application of AI, IoT, and blockchain in smart grids. Energies 2020, 13, 5739. [Google Scholar] [CrossRef]
- Mengidis, N. , Tsikrika, T., Vrochidis, S., & Kompatsiaris, I. (2021). Cybersecurity in next generation energy grids: Challenges and opportunities for blockchain and Ai technologies. Digital Transformation, Cyber Security and Resilience of Modern Societies, 299-314.
- Rane, S. B. , & Narvel, Y. A. M. (2022). Data-driven decision making with Blockchain-IoT integrated architecture: a project resource management agility perspective of industry 4.0. International Journal of System Assurance Engineering and Management, 13(2), 1005-1023.
- Deepa, N.; Pham, Q.-V.; Nguyen, D.C.; Bhattacharya, S.; Prabadevi, B.; Gadekallu, T.R.; Maddikunta, P.K.R.; Fang, F.; Pathirana, P.N. A survey on blockchain for big data: Approaches, opportunities, and future directions. Futur. Gener. Comput. Syst. 2022, 131, 209–226. [Google Scholar] [CrossRef]
- Theodorakopoulos, L.; Theodoropoulou, A.; Stamatiou, Y. A State-of-the-Art Review in Big Data Management Engineering: Real-Life Case Studies, Challenges, and Future Research Directions. Eng 2024, 5, 1266–1297. [Google Scholar] [CrossRef]
- Giannaros, A.; Karras, A.; Theodorakopoulos, L.; Karras, C.; Kranias, P.; Schizas, N.; Kalogeratos, G.; Tsolis, D. Autonomous Vehicles: Sophisticated Attacks, Safety Issues, Challenges, Open Topics, Blockchain, and Future Directions. J. Cybersecur. Priv. 2023, 3, 493–543. [Google Scholar] [CrossRef]
- Rahim, R. , Patan, R., Manikandan, R., & Kumar, S. R. (2020). Introduction to blockchain and big data. In Blockchain, Big Data and Machine Learning (pp. 1-23). CRC Press.
- Sundarakani, B.; Ajaykumar, A.; Gunasekaran, A. Big data driven supply chain design and applications for blockchain: An action research using case study approach. Omega 2021, 102, 102452. [Google Scholar] [CrossRef]
- Bhuiyan, M. Z. A., Zaman, A., Wang, T., Wang, G., Tao, H., & Hassan, M. M. (2018, May). Blockchain and big data to transform the healthcare. In Proceedings of the international conference on data processing and applications (pp. 62-68).
- Li, J.; Herdem, M.S.; Nathwani, J.; Wen, J.Z. Methods and applications for Artificial Intelligence, Big Data, Internet of Things, and Blockchain in smart energy management. Energy AI 2023, 11. [Google Scholar] [CrossRef]
- Antonopoulou, H.; Theodorakopoulos, L.; Halkiopoulos, C.; Mamalougkou, V. Utilizing Machine Learning to Reassess the Predictability of Bank Stocks. Emerg. Sci. J. 2023, 7, 724–732. [Google Scholar] [CrossRef]
- Kuo, T. T. , & Ohno-Machado, L. (2018). Modelchain: Decentralized privacy-preserving healthcare predictive modeling framework on private blockchain networks. arXiv:1802.01746.
- Rubio, M. A., Tarazona, G. M., & Contreras, L. (2018). Big data and blockchain basis for operating a new archetype of supply chain. In Data Mining and Big Data: Third International Conference, DMBD 2018, Shanghai, China, June 17–22, 2018, Proceedings 3 (pp. 659-669). Springer International Publishing.
- Paramesha, M. , Rane, N., & Rane, J. (2024). Big data analytics, artificial intelligence, machine learning, internet of things, and blockchain for enhanced business intelligence. Available at SSRN 4855856.
- Karafiloski, E. , & Mishev, A. (2017, July). Blockchain solutions for big data challenges: A literature review. In IEEE EUROCON 2017-17th International Conference on Smart Technologies (pp. 763-768). IEEE.
- Guo, L.; Xie, H.; Li, Y. Data encryption based blockchain and privacy preserving mechanisms towards big data. J. Vis. Commun. Image Represent. 2019, 70, 102741. [Google Scholar] [CrossRef]
- Karras, A.; Giannaros, A.; Theodorakopoulos, L.; Krimpas, G.A.; Kalogeratos, G.; Karras, C.; Sioutas, S. FLIBD: A Federated Learning-Based IoT Big Data Management Approach for Privacy-Preserving over Apache Spark with FATE. Electronics 2023, 12, 4633. [Google Scholar] [CrossRef]
- Wibowo, S. , & Sandikapura, T. (2019, November). Improving data security, interoperability, and veracity using blockchain for one data governance, case study of local tax big data. In 2019 International Conference on ICT for Smart Society (ICISS) (Vol. 7, pp. 1-6). IEEE.
- Ahsan, A. , & Shabbir, A. (2021). Blockchain and Big Data: Exploring Convergence for Privacy, Security and Accountability. Sage Science Review of Educational Technology, 4(2), 53-68.
- Alza Jr, G. (2021). Blockchain & CCPA. Santa Clara High Tech. LJ, 37, 231.
- Xu, C.; Wang, K.; Li, P.; Guo, S.; Luo, J.; Ye, B.; Guo, M. Making Big Data Open in Edges: A Resource-Efficient Blockchain-Based Approach. IEEE Trans. Parallel Distrib. Syst. 2018, 30, 870–882. [Google Scholar] [CrossRef]
- Fahlevi, M.; Moeljadi; Aisjah, S.; Djazuli, A. Corporate Governance in the Digital Age: A Comprehensive Review of Blockchain, AI, and Big Data Impacts, Opportunities, and Challenges. E3S Web Conf. 2023, 448. [Google Scholar] [CrossRef]
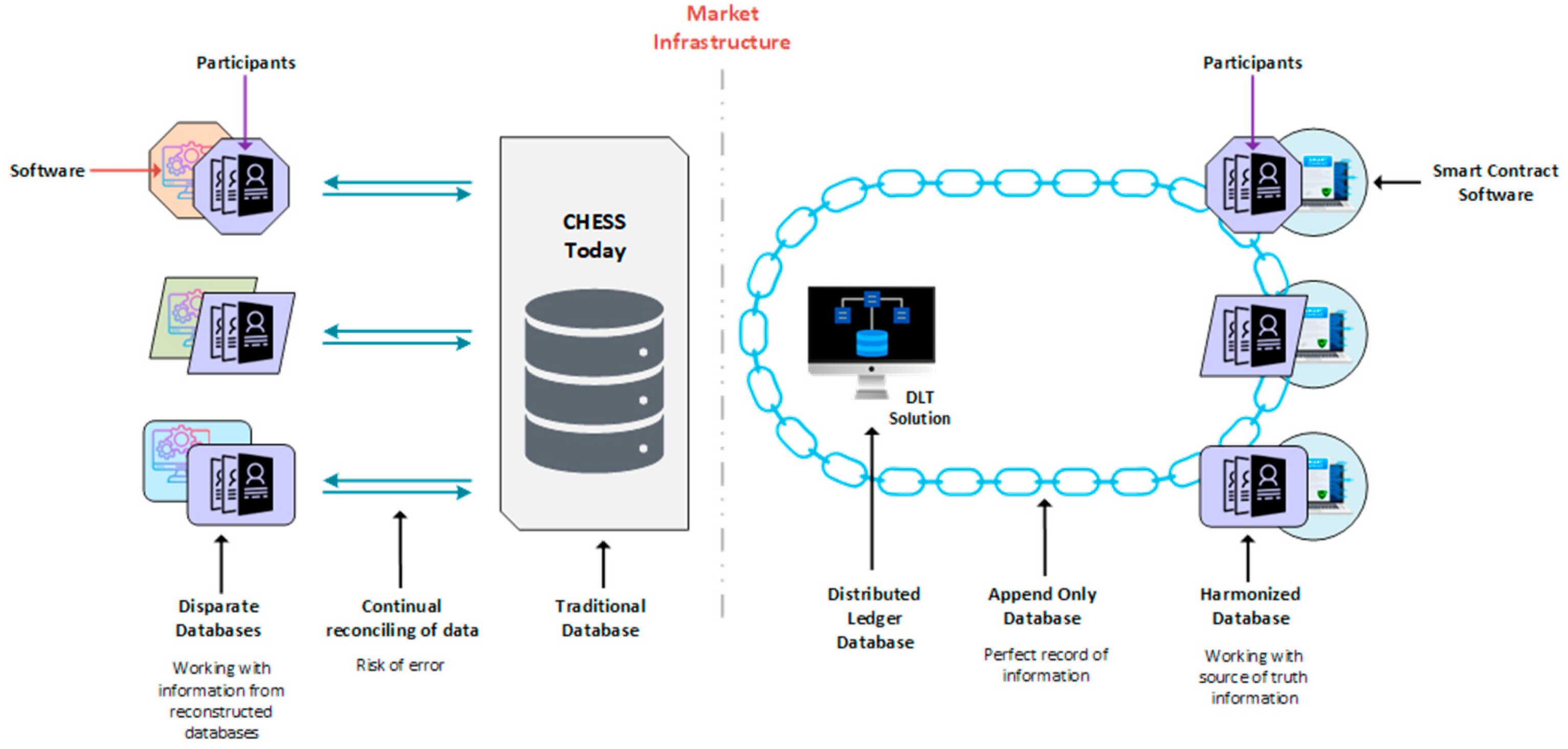
| Dimension | Traditional Systems | Blockchain-Integrated Systems |
|---|---|---|
| Data Integrity | Relies on centralized databases; prone to tampering or corruption if the central authority is compromised. | Ensures data integrity with an immutable ledger; data cannot be altered once recorded, reducing the risk of tampering. |
| Transparency | Limited transparency; data access is often restricted and requires trust in the central authority. | High transparency; all participants can view the entire transaction history, enhancing trust and accountability. |
| Fault Tolerance | Managed through central controllers with replication and redundancy strategies; still vulnerable to systemic failures. | Decentralized architecture enhances fault tolerance; each node maintains a complete copy of the ledger, ensuring continuity despite individual node failures. |
| Scalability | Centralized databases can become bottlenecks; scaling up often increases complexity and cost. | Scalability remains challenging, but emerging solutions like sharding and layer-two protocols (e.g., Lightning Network) are improving transaction throughput. |
| Security | Centralized control is vulnerable to attacks targeting the central authority, leading to potential data breaches. | Enhanced security through cryptographic techniques and decentralized consensus; eliminates single points of failure, making the system more resilient to attacks. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




