Submitted:
03 July 2024
Posted:
04 July 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Background
1.2. Research Questions
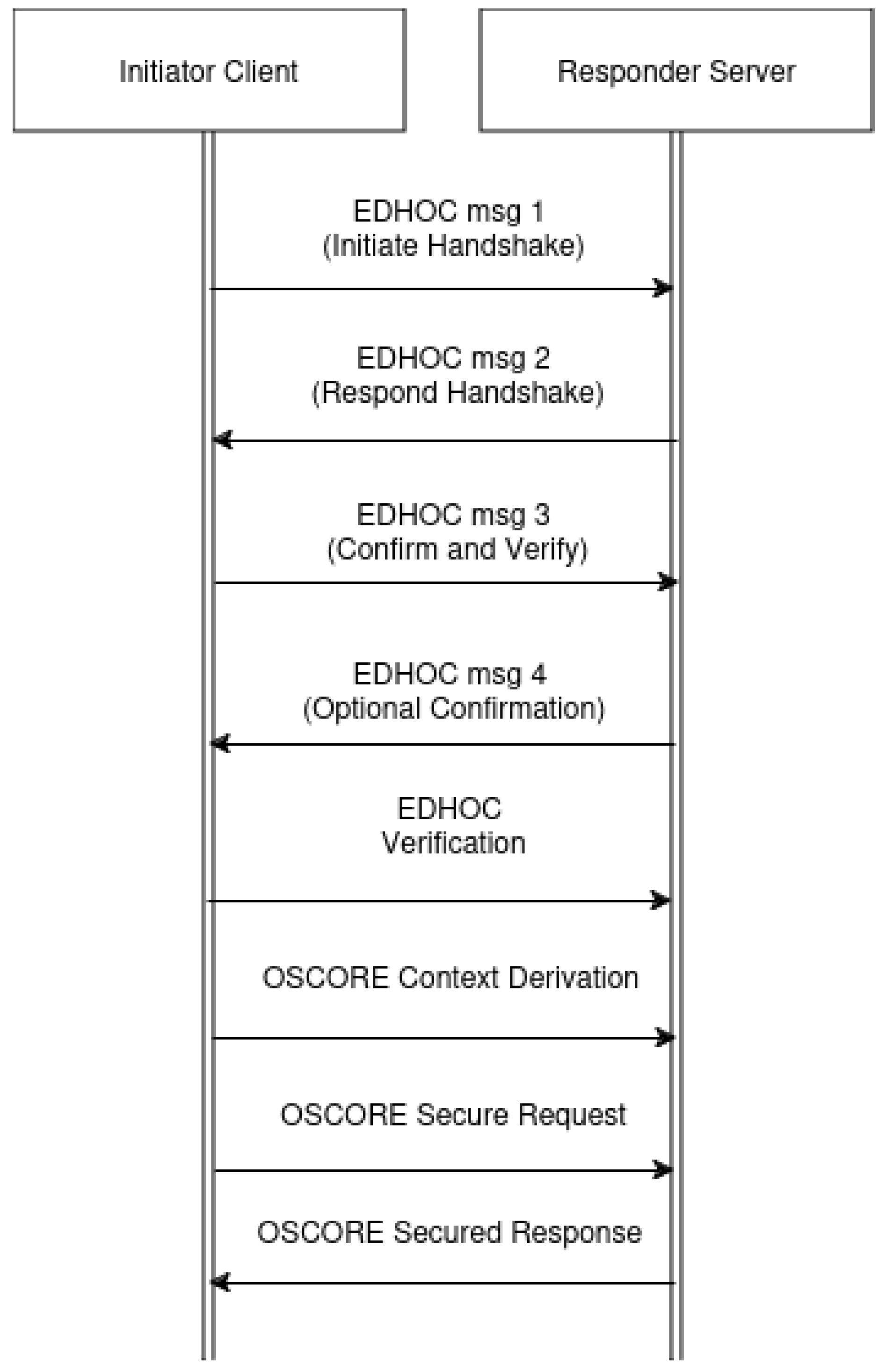
- How do different EDHOC methods of operation impact the security of a system utilizing the OSCORE protocol and its performance metrics, such as latency and memory requirements in IoT networks?
- How do hardware accelerators influence the computational overhead, energy consumption, and memory usage of IoT devices implementing OSCORE and EDHOC protocols, and what are the associated trade-offs?
- How does establishing a security context for OSCORE over DTLS compare in terms of computational overhead to incorporating the EDHOC protocol in the design?
2. Related Work
2.1. Review of Existing Cybersecurity Solutions for IoT Networks
2.2. Existing Cybersecurity Solutions for IoT Networks
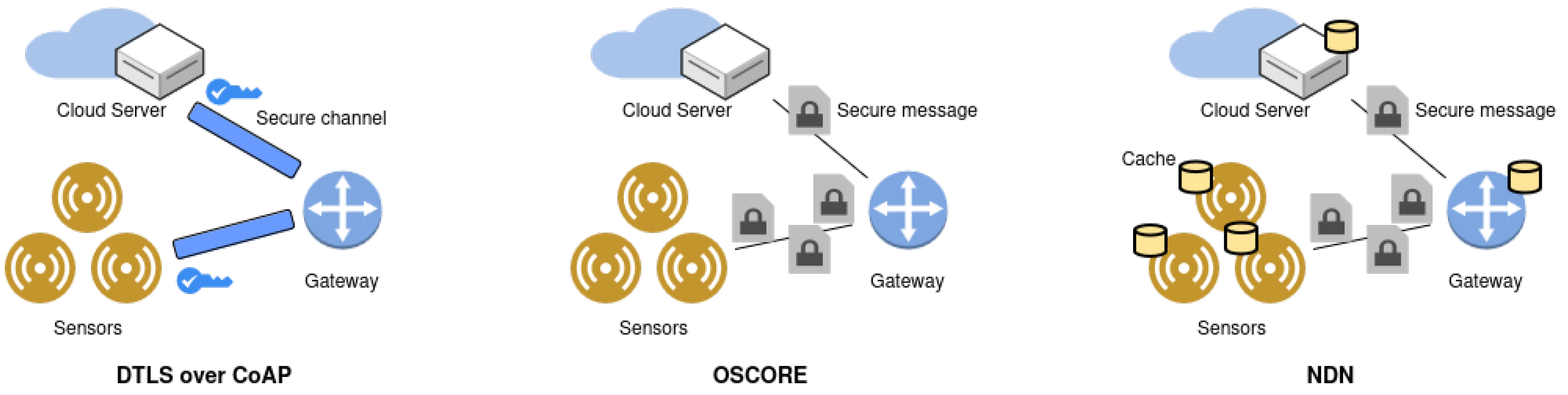
- Transport Layer Security (TLS) and Datagram TLS (DTLS): TLS and DTLS provide robust security for communications over the internet by ensuring data confidentiality, integrity, and authenticity. While TLS is designed for reliable transport like TCP, DTLS adapts it for use with unreliable transport like UDP. These protocols are widely used but can be too resource-intensive for many IoT devices [15].
- Internet Protocol Security (IPsec): IPsec is a suite of protocols that provide security at the IP layer, ensuring secure data transmission between devices. Although IPsec is highly effective, it is often too complex and heavyweight for constrained IoT environments [16].
- Message Queuing Telemetry Transport (MQTT) with SSL/TLS: MQTT is a lightweight messaging protocol designed for low-bandwidth, high-latency networks. When combined with SSL/TLS, it can offer secure communication. However, the overhead introduced by SSL/TLS can be significant for constrained devices [17].
- Lightweight Machine-to-Machine (LwM2M): LwM2M is a protocol developed by the Open Mobile Alliance (OMA) for managing IoT devices. It includes security features such as bootstrap from smartcard, PSK, and RPK. While it is more suitable for IoT environments, it may not fully address the needs of all applications, particularly those requiring end-to-end security [18].
2.3. Comparison of Various Lightweight Key Establishment Protocols
| Protocol | Security Level | Resource Consumption | Complexity | Latency |
|---|---|---|---|---|
| PANA | Medium | Low | Medium | Medium |
| IKEv2 with EAP | High | High | High | High |
| Zigbee APS | Medium | Low | Low | Low |
| CoAP with DTLS | High | Medium | Medium | High |
| OSCORE | High | Low | Low | Low |
| EDHOC | High | Low | Low | Low |
2.4. Limitations of Current Approaches and How OSCORE and EDHOC Address Them
2.4.1. Resource Consumption
- PANA: While it has low resource consumption, it relies on EAP methods, which can vary in complexity and resource requirements [19].
- IKEv2 with EAP: This protocol is highly secure but consumes significant computational and memory resources, which are often scarce in IoT devices [20].
- Zigbee APS: Although it has low resource consumption, its security mechanisms may not be robust enough for more demanding applications [21].
- CoAP with DTLS: DTLS adds significant overhead, affecting the performance of constrained devices [22].
2.4.2. Complexity
2.4.3. Latency
- IKEv2 with EAP and CoAP with DTLS: The time required to establish secure communication can introduce latency, which is critical in time-sensitive applications [24].
2.5. How OSCORE and EDHOC Address These Limitations
- Efficient Security: OSCORE secures the application data itself, making it resilient to attacks on intermediary nodes. This reduces the overhead associated with traditional transport-layer security [25].
- Low Resource Consumption: It uses COSE (CBOR Object Signing and Encryption) to provide confidentiality, integrity, and authenticity with minimal resource usage.
- Simplicity: OSCORE is simpler to implement and manage compared to traditional protocols like DTLS, making it more suitable for large-scale IoT deployments [26].
- Reduced Latency: EDHOC significantly reduces the number of round-trips needed for key establishment, minimizing latency [26].
- Flexibility: It supports various authentication methods, including PSK, RPK, and certificates, providing flexibility while maintaining strong security properties like forward secrecy.
2.6. Literature Review
3. Methodology
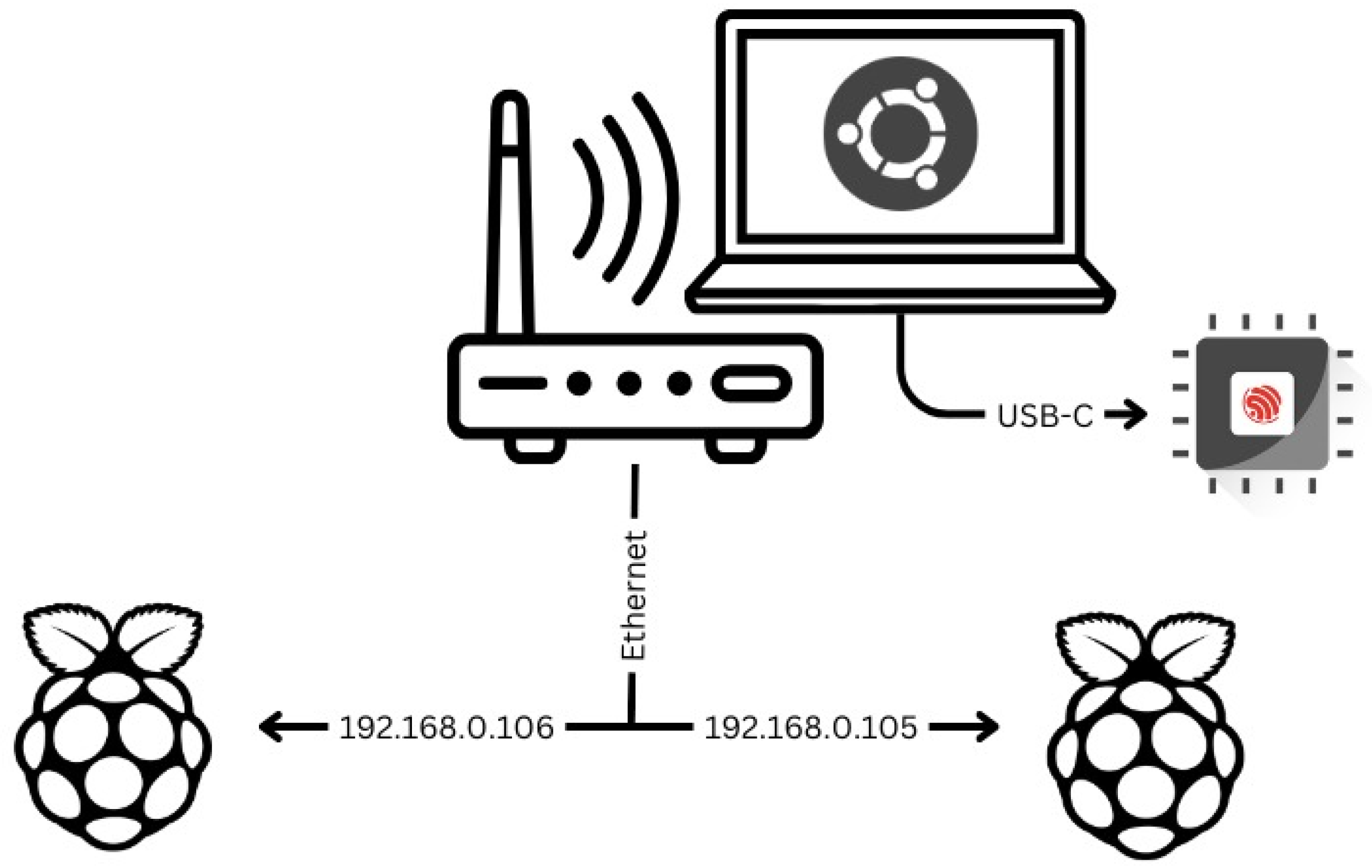
3.1. Hardware Setup
| Device | Flash Memory | SRAM |
| 2x Raspberry Pi 4B | 32GB | 4GB |
| ESP32-S | 4MB | 520KB |
| Thinkpad P15v | 500GB | 16GB |
| AVHzY USB-Meter C3 | / | / |
3.2. Software Setup
3.2.1. uOSCORE-uEDHOC Library
3.2.2. Libcoap Library
3.2.3. Edhoc and Libcoap Libraries
3.3. Research Metrics
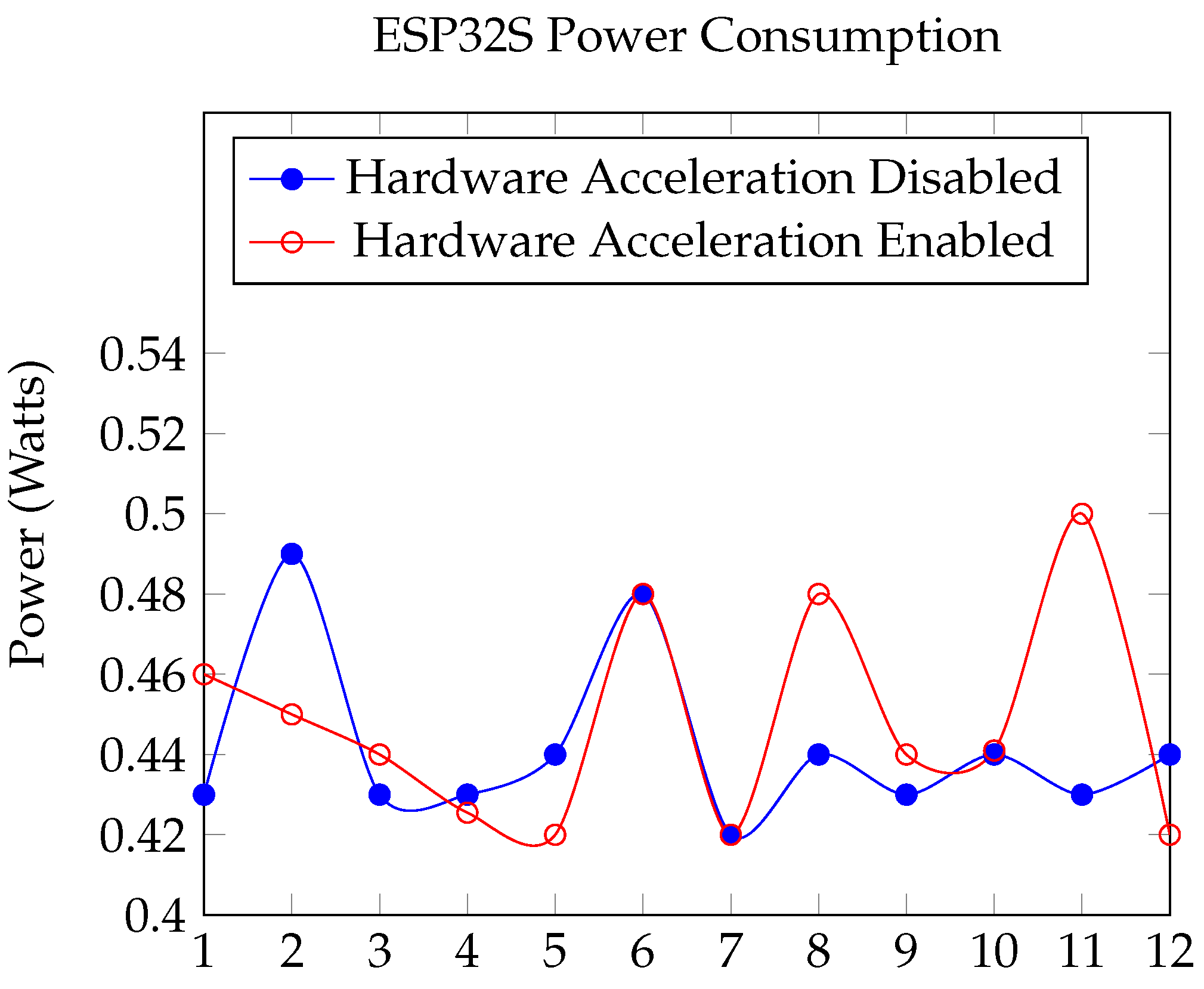
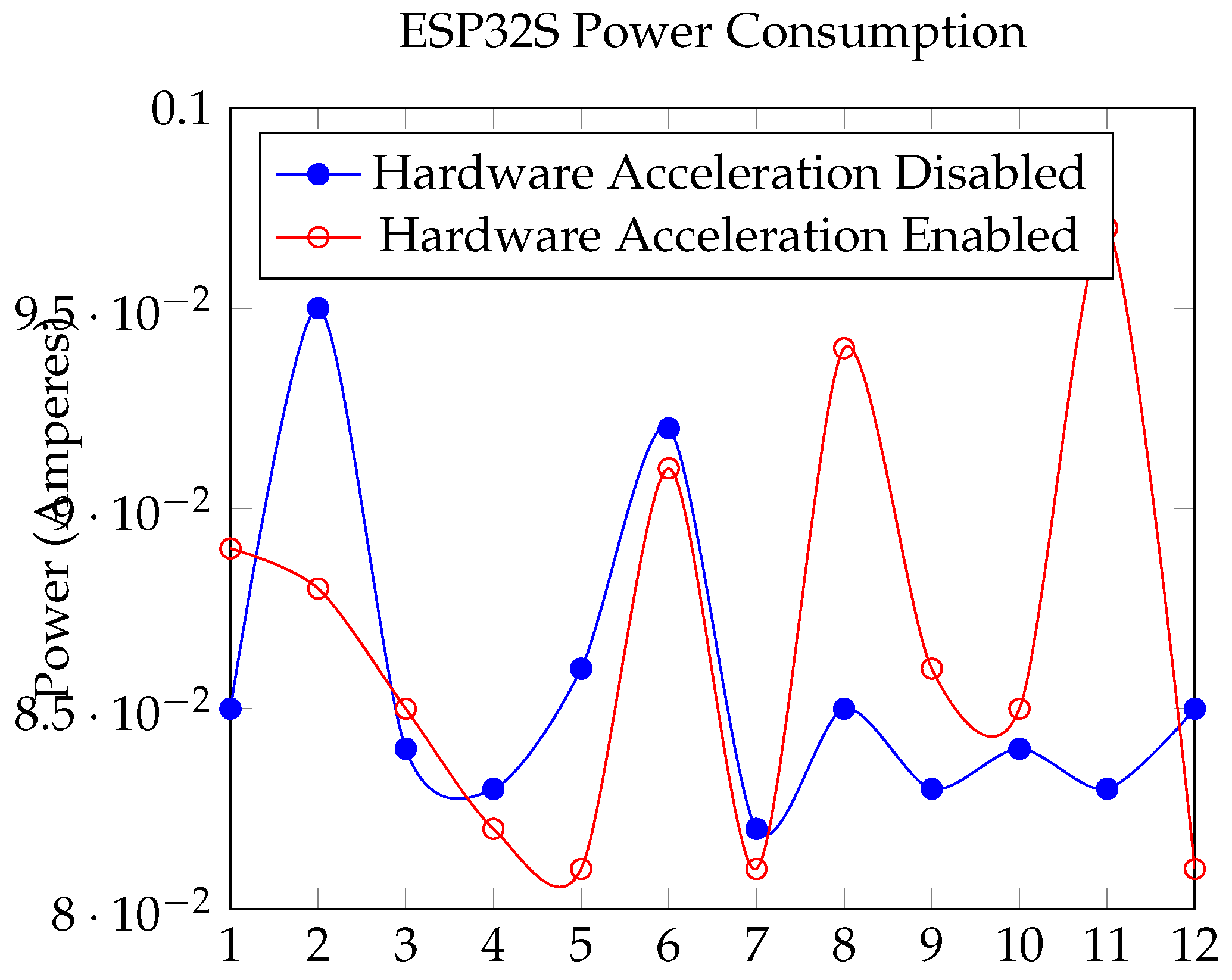
- Power Consumption: The electric current (Amperes) and electric power (Watts) consumed by the devices [29].
- Memory usage: the Flash or RAM requirements that need to be satisfied to use the protocols measured in bytes [31].
- Computation Time: The time that certain processes take to execute [42]; in this study, it is measured in milliseconds or seconds, depending on the experiment.
- Confidentiality: Ensuring no unauthorized individuals have access to the transmitted data [43].
- Integrity: The data has not been altered by an unauthorized individual [43].
- Authentication: The process of confirming the identity of a device or entity in the system [43].
4. Results
4.1. RQ1
4.1.1. Power Consumption:
- P is the power in watts (W).
- V is the voltage in volts (V).
- I is the current in amperes (A).
4.1.2. Computation Time
| Type | EDHOC Method | Latency (sec) | IRAM (bytes) | DRAM (bytes) | FLASH (bytes) |
| Client request | Signature Keys | 0.154 | 46656 | 8756 | 147456 |
| Client request | Static DH Keys | 0.164 | 46656 | 8756 | 147456 |
| Server key derivation | Signature Keys | 0.038 | 46656 | 8752 | 147456 |
| Server key derivation | Static DH Keys | 0.044 | 46656 | 8752 | 147456 |
| Client authentication | CBOR certificate | 2.827 | 46656 | 8808 | 229376 |
| Server authentication | CBOR certificate | 2.791 | 46656 | 8808 | 229376 |
4.1.3. Memory Usage
4.1.4. Confidentiality
- Diffie-Hellman Static Keys: As DH keys provide a strong encryption mechanism that establishes communication over an insecure channel, even if attackers intercept a message, it will not be possible to decrypt the data. As the EDHOC suite uses the AES-CCM-16-64-128 algorithm, confidentiality is protected while keeping the protocols efficient in a constrained environment.
- Signature keys offer strong encryption, although they lack forward secrecy - the keys used to encrypt and decrypt information do not change, making the system vulnerable to retrospective attacks.
- Using PKI (Public Key Infrastructure), CBOR encoded X.509 certificates provide a strong level of confidentiality.
4.1.5. Integrity
4.1.6. Authentication
4.2. RQ2
- Resource-Efficient Protocol Design: The EDHOC protocol is specifically designed for minimal computational and message overhead, as many resource-constrained devices do not have the capacity to perform intense operations. The protocol employs elliptic curve cryptography, which requires less computational effort and is thus efficient even without hardware acceleration.
- Optimized Library Implementation: The EDHOC library, edhoc,, available at Marco von Raumer’s GitLab repository, utilizes the mbedtls library for cryptographic operations. This library is optimized for performance, leveraging efficient algorithms and data structures to minimize computational load. The use of mbedtls_ecdh_calc_secret together with other optimized functions ensures that the performance of resource-constrained devices remains high even without them having dedicated hardware acceleration.
- Minimal Message Overhead: The protocol’s design minimizes the number of messages exchanged and their sizes, which reduces the time and computational resources required for each operation.
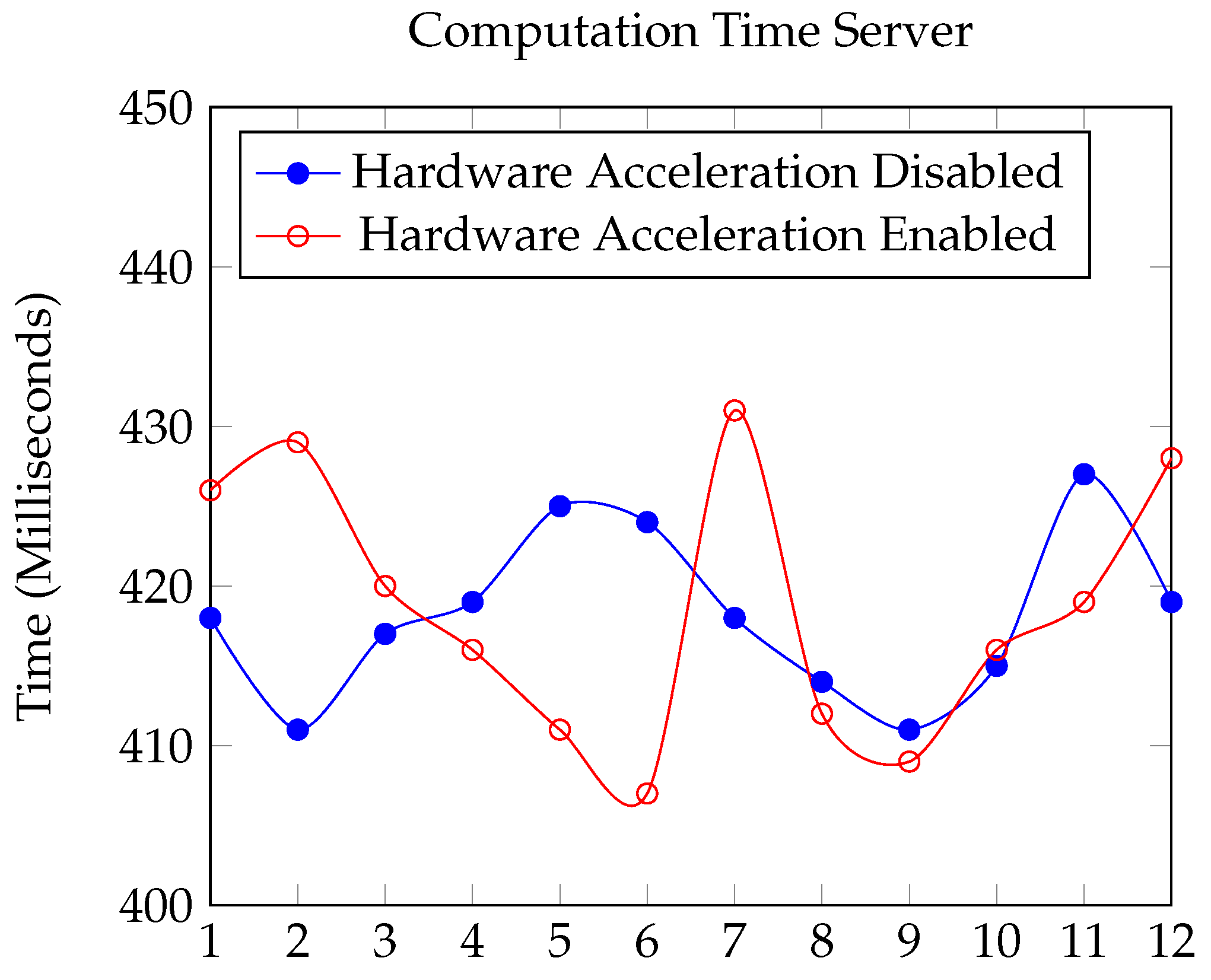
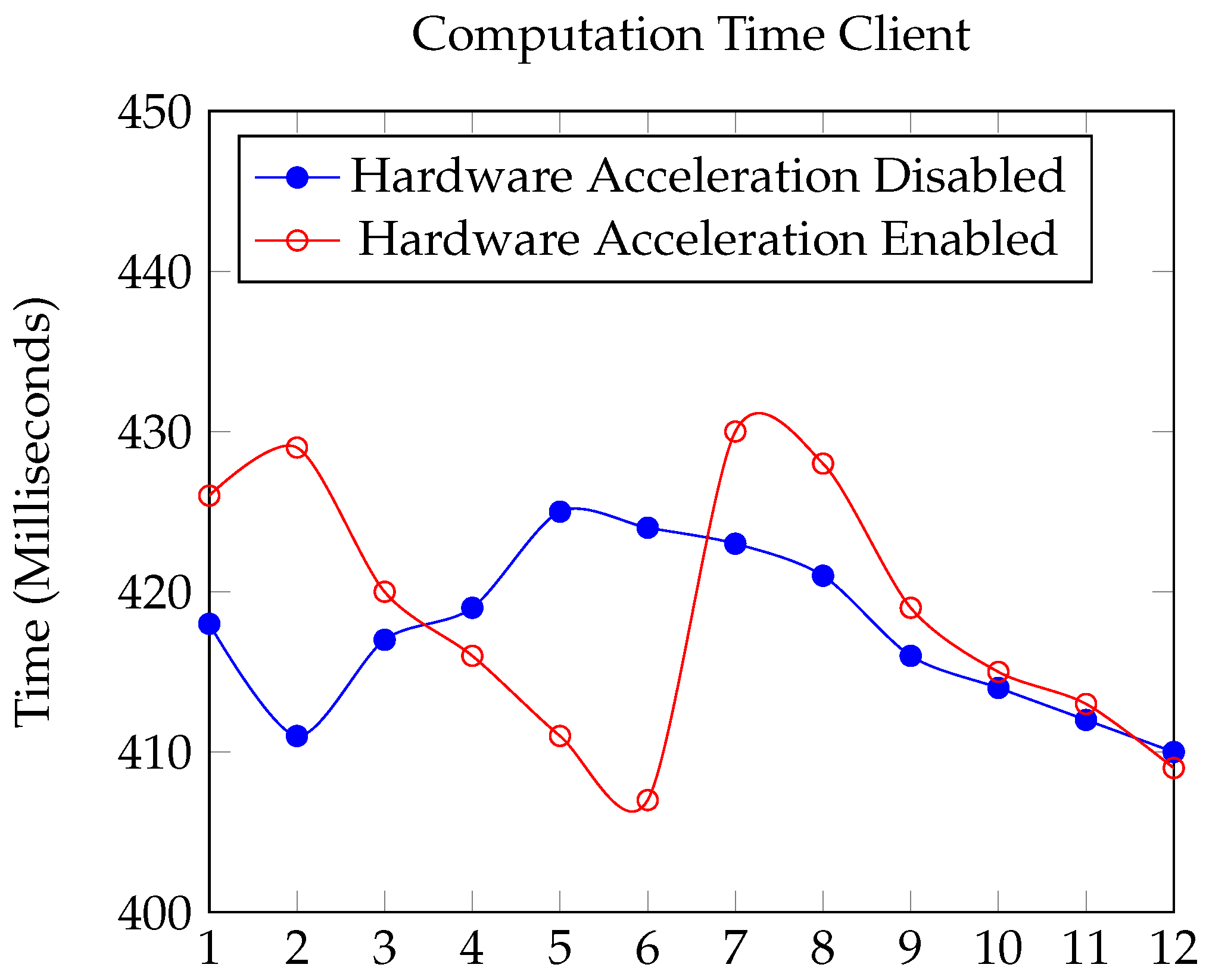
4.2.1. Computation Time:
- EDHOC Initialization (edhoc_init_context): Both configurations took nearly the same time ( 28 ms).
- Handling CoAP Message (edhoc_handle_coap_message): The average time with hardware acceleration enabled was slightly higher (98.33 ms) compared to when disabled (94.67 ms); however, such difference is negligible.
- OSCORE Context Creation (create_oscore_ctx): With hardware acceleration enabled, the average time was 54.75 ms, slightly more than the 52.8 ms without it.
4.2.2. Memory Usage:
| Mode | Flash Memory | Flash Memory (Compressed) |
| Server HWA | 785536 | 503872 |
| Server no HWA | 790608 | 508758 |
| Client HWA | 792624 | 508707 |
| Client no HWA | 797760 | 513425 |
4.2.3. Power Consumption:
4.3. RQ3
4.3.1. Power Consumption:
4.3.2. Computation time:
4.3.3. Memory Usage:
4.3.4. Confidentiality:
4.3.5. Integrity:
4.3.6. Authentication:
5. Discussion
5.1. Answering RQ1
5.2. Answering RQ2
5.3. Answering RQ3
6. Conclusions
6.1. Future Work
References
- Berte, D.R. Defining the IoT. Proceedings of the International Conference on Business Excellence 2018, 12, 118–128. [Google Scholar] [CrossRef]
- Fneish, Z.A.A.M.; El-Hajj, M.; Samrouth, K. Survey on iot multi-factor authentication protocols: A systematic literature review. 2023 11th International Symposium on Digital Forensics and Security (ISDFS). IEEE, 2023, pp. 1–7.
- El-Hajj, M.; Fadlallah, A.; Chamoun, M.; Serhrouchni, A. Secure PUF: Physically unclonable function based on arbiter with enhanced resistance against machine learning (ML) attacks. 2020.
- Khan, M.N.; Rao, A.; Camtepe, S. Lightweight cryptographic protocols for IoT-constrained devices: A survey. IEEE Internet of Things Journal 2020, 8, 4132–4156. [Google Scholar] [CrossRef]
- Haterd, R.v.d.; El-Hajj, M. Enhancing Privacy and Security in IoT Environments through Secure Multiparty Computation. Proceedings of International Conference on Intelligent Systems and New Applications 2024, 2, 64–69. [Google Scholar] [CrossRef]
- El-Hajj, M.; Beune, P. Decentralized zone-based PKI: A lightweight security framework for IoT ecosystems. Information (Basel) 2024, 15, 304. [Google Scholar] [CrossRef]
- Shelby, Z.; Hartke, K.; Bormann, C. The Constrained Application Protocol (CoAP). Internet Engineering Task Force (IETF), 2014.
- Selander, G.; Mattsson, J.; Palombini, F.; Seitz, L. RFC 8613: Object Security for Constrained RESTful Environments (OSCORE), 2019.
- Elhajj, M.; Jradi, H.; Chamoun, M.; Fadlallah, A. Lasii: Lightweight authentication scheme using iota in iot platforms. 2022 20th Mediterranean Communication and Computer Networking Conference (MedComNet). IEEE, 2022, pp. 74–83.
- Palombini, F.; Tiloca, M.; Höglund, R.; Hristozov, S.; Selander, G. Using Ephemeral Diffie-Hellman Over COSE (EDHOC) with the Constrained Application Protocol (CoAP) and Object Security for Constrained RESTful Environments (OSCORE). Internet-Draft draft-ietf-core-oscore-edhoc-11, Internet Engineering Task Force, 2024. Work in Progress.
- Cottier, B.; Pointcheval, D. Security Analysis of the EDHOC protocol. 2022; arXiv:cs.CR/2209.03599. [Google Scholar]
- Malwarebytes. What was the Mirai Botnet? Malwarebytes, 2023.
- Peccerillo, B.; Mannino, M.; Mondelli, A.; Bartolini, S. A survey on hardware accelerators: Taxonomy, trends, challenges, and perspectives. Journal of Systems Architecture 2022, 129, 102561. [Google Scholar] [CrossRef]
- El-Hajj, M.; Fadlallah, A.; Chamoun, M.; Serhrouchni, A. A survey of internet of things (IoT) authentication schemes. Sensors 2019, 19, 1141. [Google Scholar] [CrossRef] [PubMed]
- Fossati, T. RFC 7925: Transport Layer Security (TLS)/Datagram Transport Layer Security (DTLS) Profiles for the Internet of Things, 2016.
- Raza, S.; Duquennoy, S.; Höglund, J.; Roedig, U.; Voigt, T. Secure communication for the Internet of Things—a comparison of link-layer security and IPsec for 6LoWPAN. Security and Communication Networks 2014, 7, 2654–2668. [Google Scholar] [CrossRef]
- Paris, I.L.B.M.; Habaebi, M.H.; Zyoud, A.M. Implementation of SSL/TLS security with MQTT protocol in IoT environment. Wireless Personal Communications 2023, 132, 163–182. [Google Scholar] [CrossRef]
- Singh, D.; Singh, R.; Gupta, A.; Pawar, A.V. Message queue telemetry transport and lightweight machine-to-machine comparison based on performance efficiency under various scenarios. International Journal of Electrical and Computer Engineering 2022, 12, 6293. [Google Scholar] [CrossRef]
- Sanchez-Gomez, J.; Garcia-Carrillo, D.; Marin-Perez, R.; Skarmeta, A.F. Secure authentication and credential establishment in narrowband IoT and 5G. Sensors 2020, 20, 882. [Google Scholar] [CrossRef] [PubMed]
- Aboelfotoh, R.M.A. Quality of service and privacy in internet of things dedicated to healthcare. PhD thesis, Université d’Avignon; American university in Cairo, 2021.
- Gavra, V.; Pop, O.A.; Dobra, I. A Comprehensive Analysis: Evaluating Security Characteristics of Xbee Devices against Zigbee Protocol. Sensors 2023, 23, 8736. [Google Scholar] [CrossRef] [PubMed]
- Kumar, P.M.; Gandhi, U.D. Enhanced DTLS with CoAP-based authentication scheme for the internet of things in healthcare application. The Journal of Supercomputing 2020, 76, 3963–3983. [Google Scholar] [CrossRef]
- Pagliusi, P.S.; Mitchell, C.J. PANA/IKEv2: an Internet authentication protocol for heterogeneous access. International Workshop on Information Security Applications. Springer, 2003, pp. 135–149.
- Bhattacharjya, A.; Zhong, X.; Wang, J.; Li, X. CoAP—application layer connection-less lightweight protocol for the Internet of Things (IoT) and CoAP-IPSEC Security with DTLS Supporting CoAP. Digital twin technologies and smart cities, 2020, pp. 151–175.
- Gunnarsson, M.; Brorsson, J.; Palombini, F.; Seitz, L.; Tiloca, M. Evaluating the performance of the OSCORE security protocol in constrained IoT environments. Internet of Things 2021, 13, 100333. [Google Scholar] [CrossRef]
- Hristozov, S.; Huber, M.; Xu, L.; Fietz, J.; Liess, M.; Sigl, G. The cost of OSCORE and EDHOC for constrained devices. Proceedings of the Eleventh ACM Conference on Data and Application Security and Privacy, 2021, pp. 245–250.
- Jacomme, C.; Klein, E.; Kremer, S.; Racouchot, M. A comprehensive, formal and automated analysis of the {EDHOC} protocol. 32nd USENIX Security Symposium (USENIX Security 23), 2023, pp. 5881–5898.
- Fraile, L.P.; Fournaris, A.; Koulamas, C. Design and performance evaluation of an embedded EDHOC module. 2021 10th Mediterranean Conference on Embedded Computing (MECO). IEEE, 2021, pp. 1–6.
- Singh, S.; Sharma, P.; Moon, S.; others. Advanced lightweight encryption algorithms for IoT devices: survey, challenges and solutions. Journal of Ambient Intelligence and Humanized Computing 2024, 15, 1625–1642. [Google Scholar] [CrossRef]
- Levä, T.; Mazhelis, O.; Suomi, H. Comparing the cost-efficiency of CoAP and HTTP in Web of Things applications. Decision Support Systems 2014, 63, 23–38, 1. Business Applications ofWeb of Things 2. Social Media Use in Decision Making. [Google Scholar] [CrossRef]
- Gunnarsson, M.; Brorsson, J.; Palombini, F.; Seitz, L.; Tiloca, M. Evaluating the performance of the OSCORE security protocol in constrained IoT environments. Internet of Things 2021, 13, 100333. [Google Scholar] [CrossRef]
- Bruni, A.; Sahl Jørgensen, T.; Grønbech Petersen, T.; Schürmann, C. Formal Verification of Ephemeral Diffie-Hellman Over COSE (EDHOC). Security Standardisation Research; Cremers, C., Lehmann, A., Eds.; Springer International Publishing: Cham, 2018; pp. 21–36. [Google Scholar]
- Fedrecheski, G.; Vučinić, M.; Watteyne, T. Performance Comparison of EDHOC and DTLS 1.3 in Internet-of-Things Environments. IEEE Wireless Communications and Networking Conference;, 2024.
- Höglund, R.; Tiloca, M.; Selander, G.; Mattsson, J.P.; Vučinić, M.; Watteyne, T. Secure Communication for the IoT: EDHOC and (Group) OSCORE Protocols. IEEE Access 2024, 12, 49865–49877. [Google Scholar] [CrossRef]
- Kim, J.; Duguma, D.G.; Lee, S.; Kim, B.; Lim, J.; You, I. Scrutinizing the Vulnerability of Ephemeral Diffie–Hellman over COSE (EDHOC) for IoT Environment Using Formal Approaches. Mobile Information Systems 2021, 2021, 1–18. [Google Scholar] [CrossRef]
- Keoh, S.L.; Kumar, S.S.; Tschofenig, H. Securing the Internet of Things: A Standardization Perspective. IEEE Internet of Things Journal, 2014. [CrossRef]
- Selander, G.; Mattsson, J.P.; Palombini, F. Ephemeral Diffie-Hellman Over COSE (EDHOC). Internet Requests for Comments, 2024. [CrossRef]
- Hristozov, S.; Huber, M.; Xu, L.; Fietz, J.; Liess, M.; Sigl, G. The Cost of OSCORE and EDHOC for Constrained Devices. Proceedings of the Eleventh ACM Conference on Data and Application Security and Privacy; CODASPY ’21; Association for Computing Machinery: New York, NY, USA, 2021; pp. 245–250. [Google Scholar] [CrossRef]
- Santos, T.P.; Chaves, R.; Homsirikamol, E.; Rogawski, M.; Adamo, O. Efficient Implementation of Lightweight Cryptographic Algorithms for Securing IoT Devices. Cryptology ePrint Archive, Report 2021/058, 2021.
- Zhang, Z.; Yu, Y.; Zhang, H.; Newberry, E.; Mastorakis, S.; Li, Y.; Afanasyev, A.; Zhang, L. An Overview of Security Support in Named Data Networking. IEEE Communications Magazine 2018, 56, 62–68. [Google Scholar] [CrossRef]
- Gündogan, C.; Amsüss, C.; Schmidt, T.C.; Wählisch, M. IoT Content Object Security with OSCORE and NDN: A First Experimental Comparison. Proc. of 19th IFIP Networking Conference; IEEE Press: Piscataway, NJ, USA, 2020; pp. 19–27. [Google Scholar]
- Harris-Birtill, D.; Harris-Birtill, R. , Chapter 12 Understanding Computation Time: A Critical Discussion of Time as a Computational Performance Metric; Brill: Leiden, The Netherlands, 2021; pp. 220–248. [Google Scholar] [CrossRef]
- Stallings, W.; Brown, L. Computer Security: Principles and Practice; 2007.
- Kothmayr, T.; Schmitt, C.; Hu, W.; Brünig, M.; Carle, G. DTLS based security and two-way authentication for the Internet of Things. Ad Hoc Networks 2013, 11, 2710–2723. [Google Scholar] [CrossRef]
- Kwon, H.; Park, J.; Kang, N. Challenges in Deploying CoAP Over DTLS in Resource Constrained Environments. Information Security Applications; Kim, H.w., Choi, D., Eds.; Springer International Publishing: Cham, 2016; pp. 269–280. [Google Scholar]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




