Submitted:
12 July 2024
Posted:
15 July 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Research Motivation/Problem
- To comprehensively identify and discuss the vulnerabilities of the ADS-B system and explore potential exploitation scenarios.
- To assess and acknowledge the limitations of existing security solutions, emphasizing their inability to offer a complete defense to the ADS-B system and their lack of practical implementation in real-world scenarios (experimental phase).
- To evaluate existing security solutions from multiple perspectives, including cost-effectiveness, implementation difficulty, scalability, and coverage against potential attacks.
- To highlight the challenges and obstacles researchers face in developing holistic security solutions tailored to the unique complexities of the ADS-B system.
1.2. Research Objectives/Contributions
- To offer a comprehensive overview of the aviation system to enhance readers’ understanding of ADS-B technology and its security implications.
- To provide an in-depth analysis of ADS-B vulnerabilities, potential threats, and attack vectors, supported by illustrative diagrams, to facilitate a deeper understanding of security risks.
- To evaluate existing security solutions published till 2024 based on cost-effectiveness, scalability, implementation complexity, and coverage against diverse attack scenarios to inform decision making for security implementations.
- To identify security requirements and challenges in ADS-B systems and propose future research directions to address emerging threats and enhance system resilience.
1.3. Research Methodology
1.4. Paper Structure
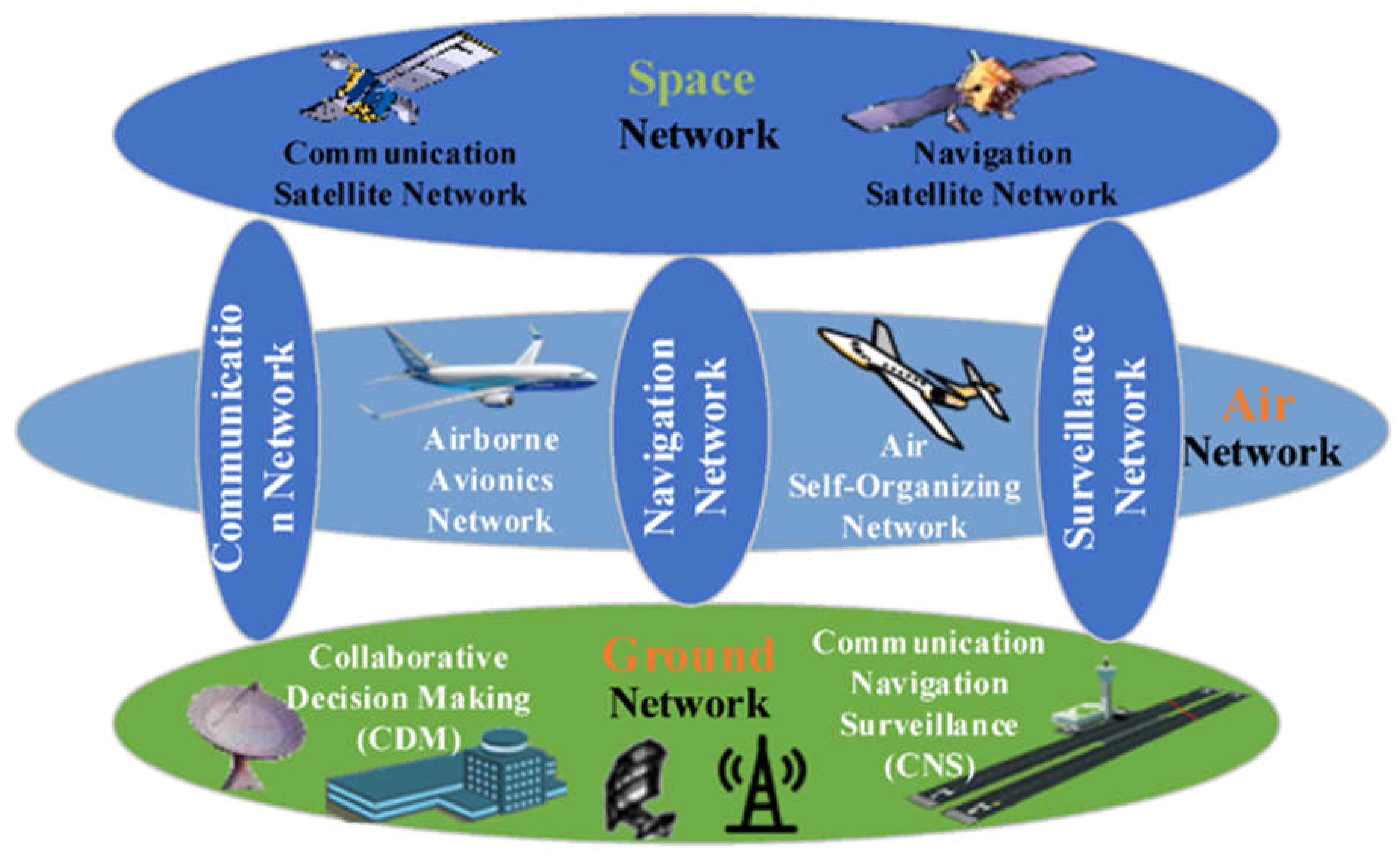
2. Overview of Aviation System
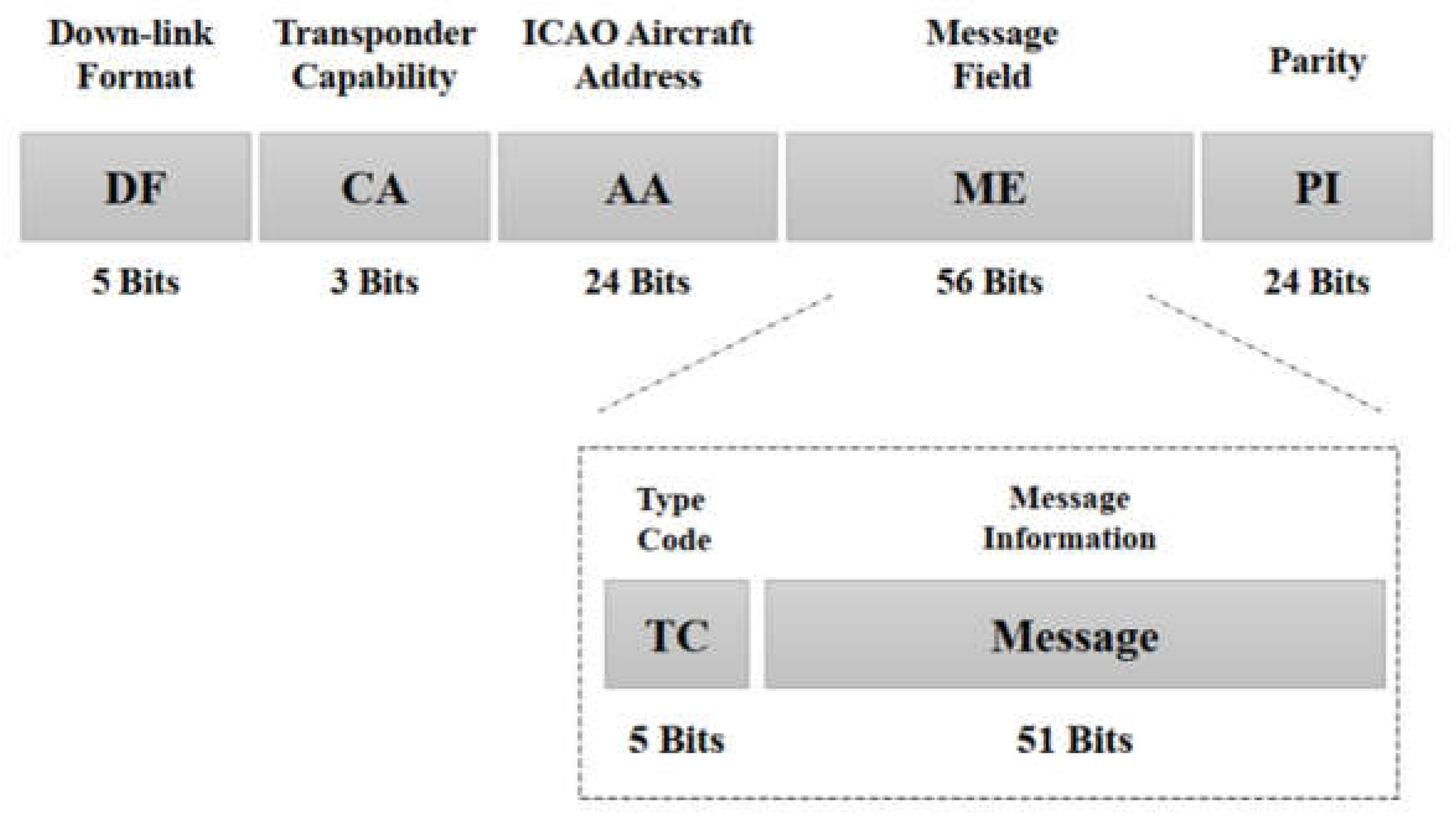
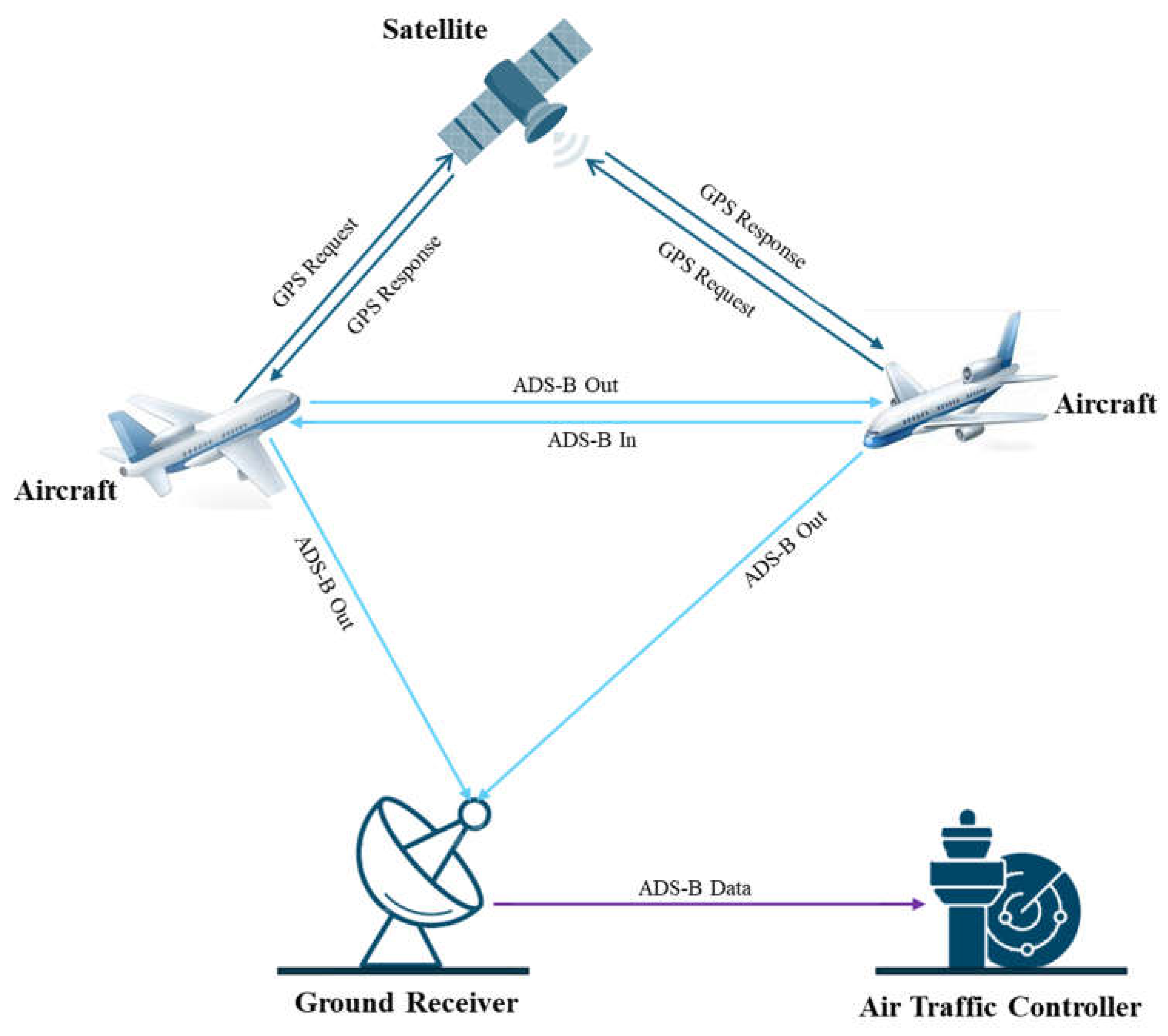
3. Overview of Automatic Dependent Surveillance–Broadcast (ADS-B)
4. Security Analysis of ADS-B
4.1. ADS-B Vulnerabilities
“the FAA assessed the vulnerability risk associated with using ADSB broadcast messages to target air carrier aircraft in particular.” The current assessment includes Sensitive Security Information, subject to the regulations outlined in 49 CFR Parts 1 and 1520. Apart from that, the data it comprises is protected from being disclosed to the public. While the agency refrains from offering commentary on the study’s data, it can affirm, in response to the remarks expressed throughout this rulemaking procedure, that the application of ADS-B data does not augment the existing level of risk to an aircraft”.
4.2. ADS-B Vulnerability Exploits
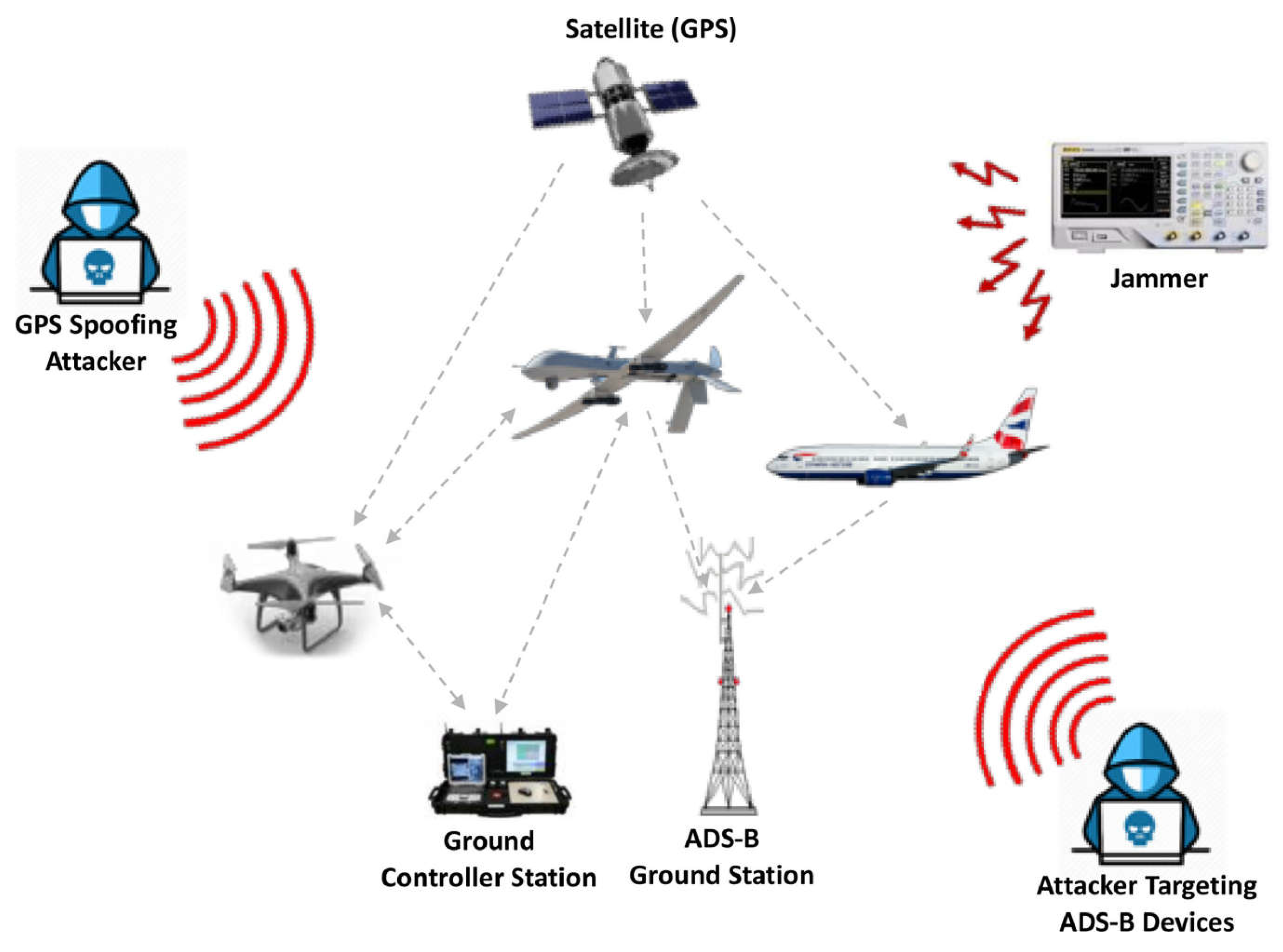
4.3. ADS-B Attacks
- Message Injection Attack: This is an attack in which an attacker sends nonlegitimate ADS-B messages to nearby Aircraft and ATC. These nonlegitimate messages deceive the system into believing that an aircraft is flying at a different altitude or location or on a different course than its original location. This attack can create a dangerous situation and confuse ATC and the pilots. Message injection attacks violate the authentication of the ADS-B protocol. In [49], the authors investigate the impact of message injection and spoofing attacks on ADS-B.
- Message Deletion Attack: This is an attack in which an attacker intercepts and deletes legitimate messages broadcast by other aircraft in the surroundings. From an ATC and aircraft point of view, ADS-B messages are critical because they provide real-time information about aircraft, such as the current altitude, speed, and other important information. An attacker can cause accidents or confusion by deleting ADS-B messages and hiding the aircraft’s status and location from ATC. Message deletion attacks violate the integrity of ADS-B protocol. In [50], the authors discuss two strategies for deleting a legitimate ADS-B message.
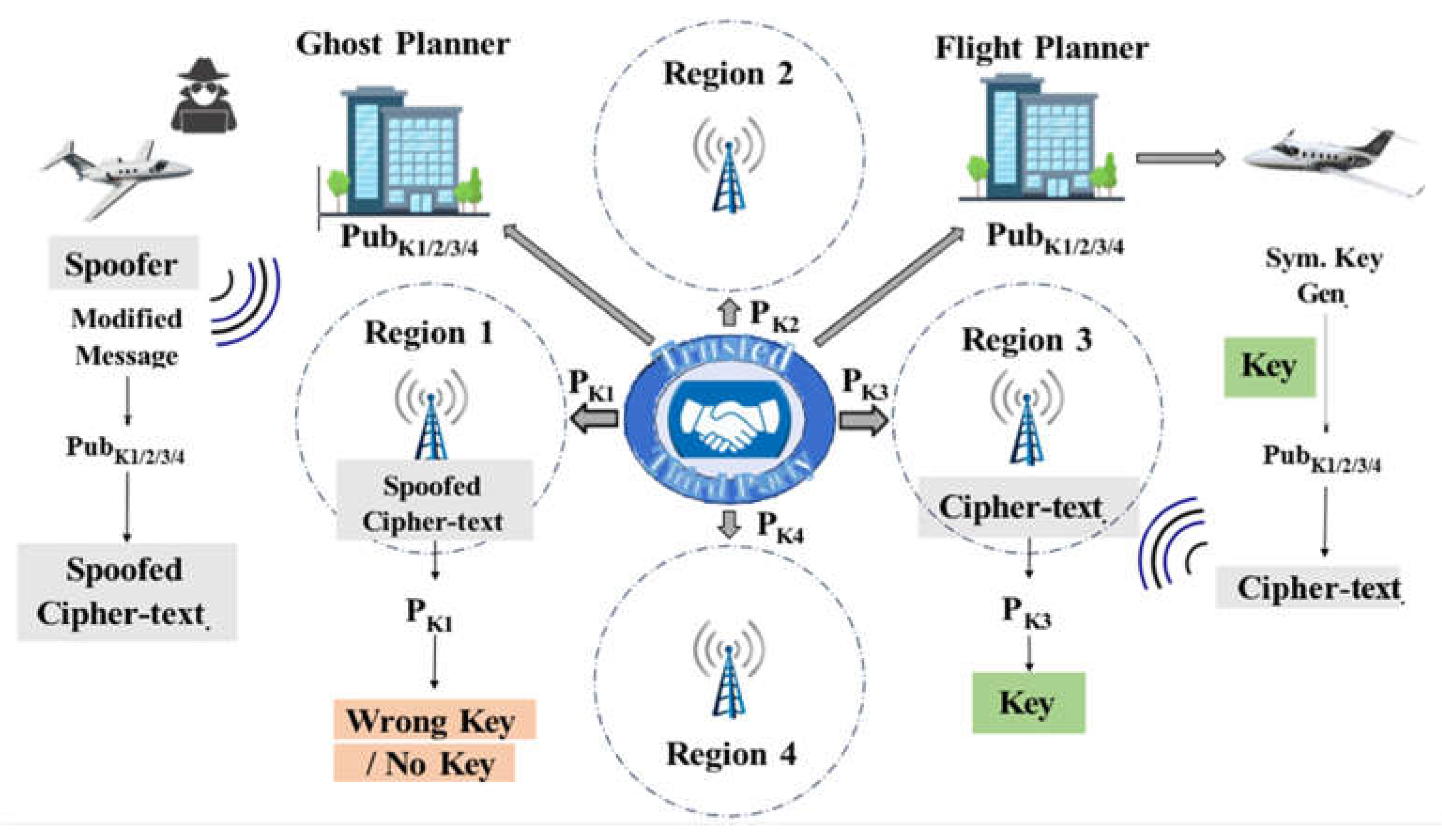
- Message Modification Attack: In a message modification attack, the attacker intercepts a legitimate broadcast message by violating ADS-B confidentiality and modifying different message values, such as the altitude, speed, etc. The modified message is transferred to ATC, making it difficult for ATC to track the aircraft’s updated location and status. Message modification attacks violate the integrity of the ADS-B protocol. In [51], the authors proposed a mechanism for injecting and verifying a modified message in the ATC system.
- Eavesdropping Attack: This is an attack in which an attacker intercepts and listens to legitimate messages broadcast by aircraft. These messages contain critical data related to aircraft, such as the altitude, position, etc. The intercept messages also provide sensitive information to the attacker, such as the flight status and path. In [52], the authors discuss and implement multiple methods of passive attacks, such as eavesdropping. Eavesdropping violates the confidentiality of ADS-B protocol.
- Jamming Attack: Transmitting similar high-power radio signals on a frequency identical to that used by aircraft for communication can prevent air traffic controllers from receiving legitimate ADS-B messages. This attack will disrupt communication between air traffic control and air, creating difficulties for pilots in receiving instructions from air traffic controllers. Message-jamming attacks violate the availability of ADS-B protocol. In [52], the authors discuss and implement multiple methods of active attacks, such as eavesdropping. Table 3 presents a summary of ADS-B attacks.
| Sr# | Attack | Sub-Attack | Attack Purpose | Attack Method |
|---|---|---|---|---|
| Eavesdropping | Reconnaissance attack | Obtaining aircraft information is also called aircraft reconnaissance. | Using an ADS-B receiver, the corresponding airspace data are obtained. | |
| Jamming | Denial of service, flooding attack | Jam ADS-B communicates for a certain amount of time in a specific airspace. | A high-frequency signal is transmitted on the targeted frequency band (1090ES). | |
| Message injection | Ghost injection | To mislead ATC in the targeted airspace, fake aircraft is injected. | Using a power-transmitting device generates and injects fake messages using relevant frequency. | |
| Message deletion | Aircraft disappearance | A target field or complete message is deleted. | At physical layers, bits are flipped in the ADS-B message. | |
| Message modification | Virtual trajectory modification | The content of the message is modified. | Message injection and deletion attack are combined. |
5. Security Analysis of Existing Solutions
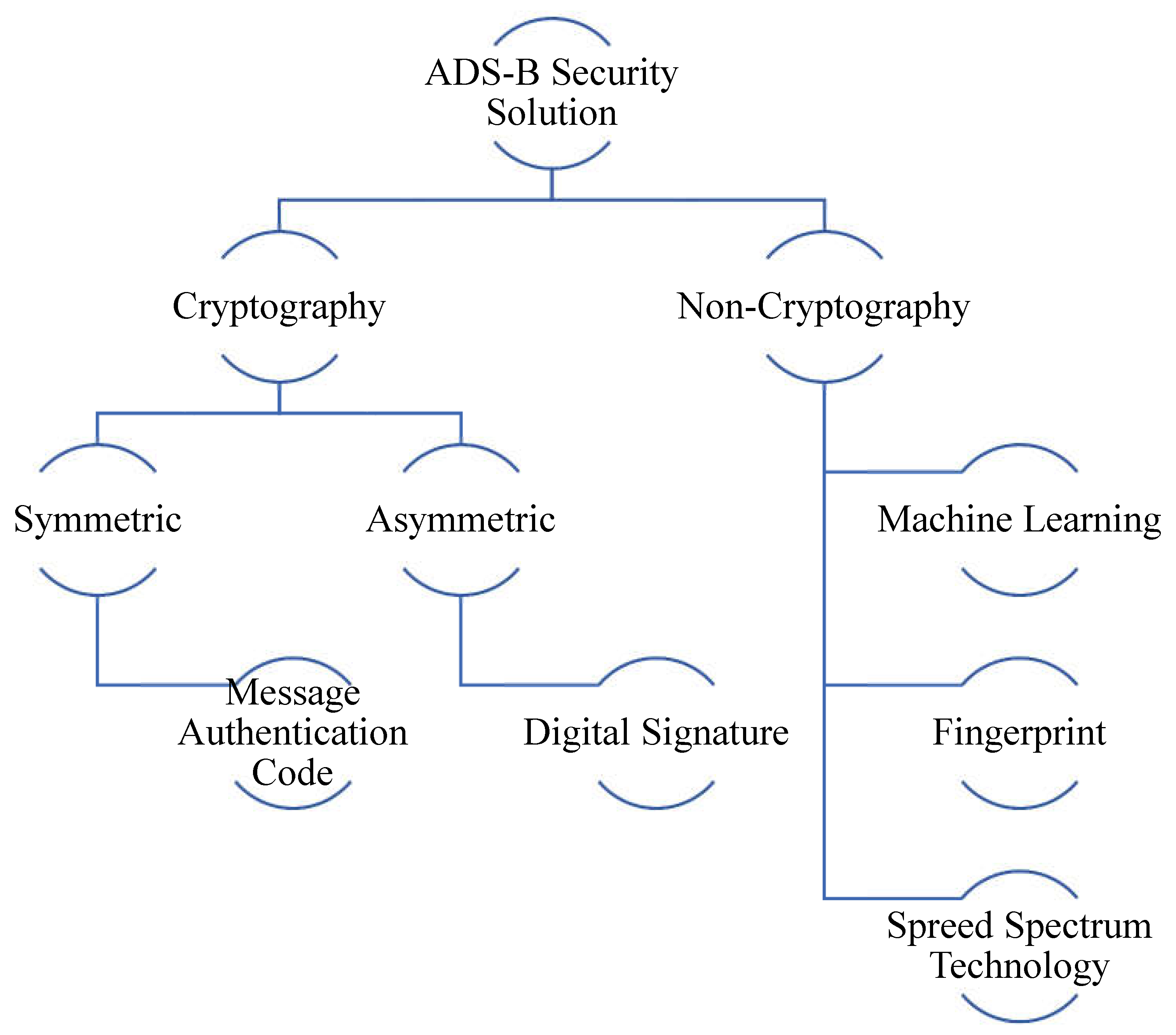
5.1. Cryptography Schemes
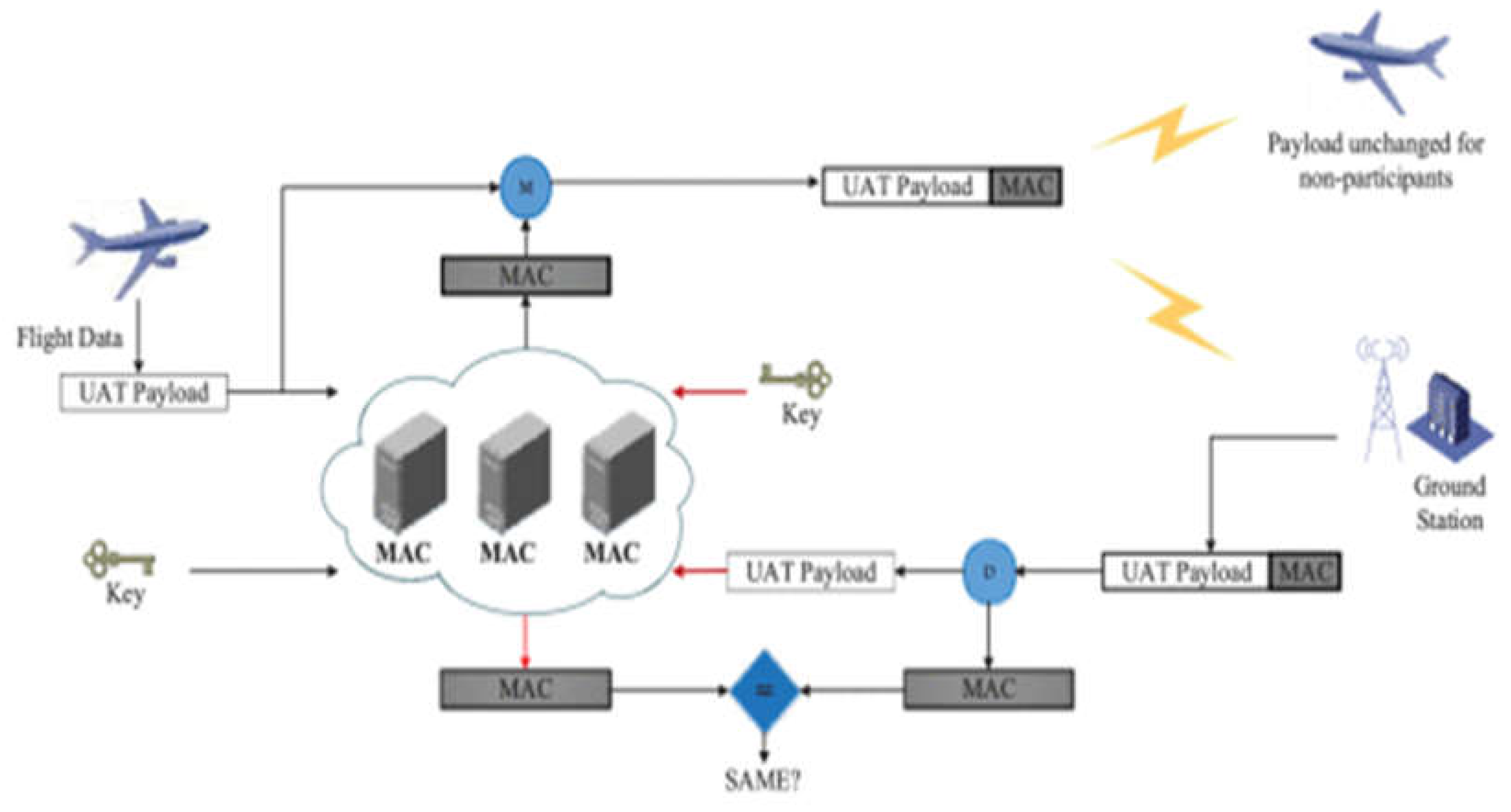
5.1.1. Symmetric Cryptography
5.1.1.1. Message Authentication Code (MAC)
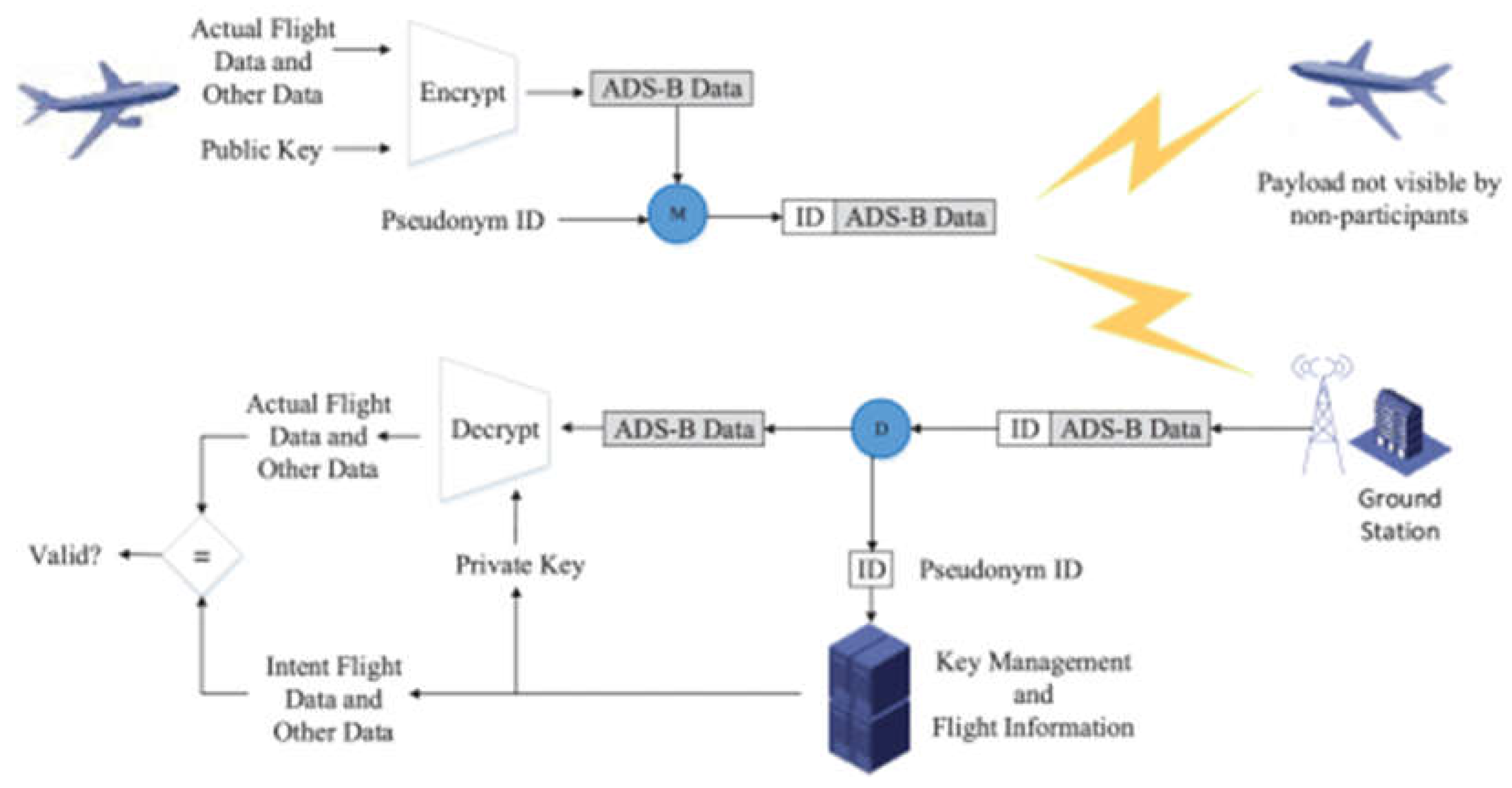
5.1.2. Asymmetric Cryptography
5.1.2.1. Digital Signature
| Ref. | Cryptographic Technique | Research Contribution | Strengths | Challenges |
|---|---|---|---|---|
| [73] | Symmetric Cryptography |
The authors proposed a lightweight, highly compatible, and resource-constrained framework for ADS-B security. |
Symmetric cryptography-based solutions are suitable for bulk data, with less overhead, speed, and efficiency. | Challenges included data integrity, message authentication, key management, and exchange. |
| [74] |
Based on the modified AES algorithm, the authors proposed a framework to increase ADS-B message integrity and secure ADS-B messages. |
|||
| [75] | Using vector-homomorphic and FFX encryption, the authors proposed solutions for ADS-B message integrity and privacy. | |||
| [76] | The authors proposed using identity-based encryption (IBE) for key encryption and sharing and a hybrid technique with symmetric cryptography for data. | |||
| [77] | The authors proposed a technique to address the problems of key sharing and authentication. | |||
| [78] |
Asymmetric Cryptography |
The authors proposed a solution based on a hierarchical signature technique based on a certificate-less signature technique utilizing aggregate signatures to reduce the processing time using key validation and setup processes through various communication components. | Asymmetric cryptography-based solutions are suitable for ADS-B message integrity, privacy, cryptography key distribution, message confidentiality, and authentication. | Challenges included message overhead, increase in computational cost, performance, and key management. |
| [79] | The authors proposed a lightweight protocol based on symmetric and asymmetric encryption for ADS-B message confidentiality. In the proposed protocol, ATC manages the session data and the encryption keys, acting as TTP. | |||
| [80] | From the ADS-B security’s point of view, the authors discussed the suitability of the Elliptic Curve Digital Signature Algorithm (ECDSA) from the perspectives of signature length and standard constraints. | |||
| [81] | To protect ADS-B message confidentiality and authentication, the author proposed a holistic air protection (HAP) technique using an elliptical curve and certificate-based encryption. | |||
| [82] | Digital Signature | The authors presented an ADS-B message authentication technique based on a certificate-less signature. The proposed method is performance-efficient and does not need a certificate management authority. | Digital signatures provide integrity, authentication, and non-repudiation to ADS-B message data. | Challenges included complexity, interoperability, algorithm performance, and key management in an ample space. |
5.2. Non-Cryptography Schemes
5.2.1. Machine Learning-Based Security Solutions
5.2.2. Fingerprint
5.2.3. Spread Spectrum Technology
6. Security Requirements
- ▪
- Cryptography Elements—Despite the limited message size in standard ADS-B packets, the solution’s security level should not be compromised.
- ▪
- No Modifications in Hardware—The proposed security solution should require a simple software update without requiring hardware modifications in terms of maintenance and cost.
- ▪
- Packet Loss Events—Given the prevalent packet loss phenomena in the 1090ES frequency band, effective security solutions should demonstrate resilience against incomplete packet reception caused by obstacles and other factors.
- ▪
- Backward Compatibility—New security solutions should seamlessly integrate with existing systems, allowing aircraft that have yet to update their systems to continue operating.
- ▪
- Standard Compliance—Security solutions must align with the ADS-B protocol’s updated version to ensure message format and communication logic compliance.
- ▪
- Limited Message Overhead—Security techniques must introduce a minimal additional message overhead to avoid congestion on the 1090ES frequency band.
7. Challenges and Future Research Directions
- ▪
- Blockchain Integration: Blockchain, a composite system incorporating peer-to-peer (P2P) networks, smart contracts, consensus mechanisms, and cryptography, emerges as a promising solution for secure data sharing in an untrusted network. Blockchain is an exceptional public trust technique that applies to ADS-B protocol, using group certification techniques for ADS-B message integrity and authentication. Researchers should focus on blockchain’s usability in forthcoming research endeavors in ADS-B security. Pioneering work by the authors in [21] introduced blockchain technology for identity recognition by employing P2P technology for distributed data storage and authentication. This technique showcases high security, reliability, and scalability, offering identity authentication across different infrastructures [103]. Articles such as “Aviation Blockchain Infrastructure” (ABI) propose leveraging blockchain for effective, secure, and private communication between aircraft and authorized individuals [100].
- ▪
- Machine Learning Applications: Given the importance of abnormal data detection, particularly in a non-encrypted and open protocol like ADS-B, machine learning (ML) provides a compelling solution. In recent years, a surge in anomaly detection techniques based on ML has been witnessed, with deep learning gaining prominence in various domains. Deep learning and machine learning applications will play vital roles in anomaly detection in the ADS-B system. A time series algorithm can enhance detection efficacy by augmenting feature dimensions by leveraging the qualities of rapid ADS-B message updates with accurate time correlation and utilizing deep learning and machine learning models for detecting malicious ADS-B messages. This approach ensures compatibility with existing ADS-B protocols without additional sensors. Numerous articles, including the works of [101,102,103], illustrate using deep learning techniques or LSTM networks to enhance ADS-B system security.
- ▪
- Multi-layered Security Framework: The existing security solutions proposed by researchers failed to protect ADS-B from attack as they only provide a certain level of security. Researchers must design and test a security framework based on multi-layered security that can detect and defend ADS-B systems from different attacks.
- ▪
- High Attack Detection with Low False Alarm: Researchers face challenges in developing an attack detection method with low false alarms and high attack detection probabilities. The existing security solutions published by researchers have fundamental implementation limitations. To implement existing methods, researchers have to modify the infrastructure of the ADS-B system or the ADS-B message format. Most importantly, the developed solutions are not tested in a real-time environment, which will affect the method’s efficiency. The ADS-B system requires a security solution that overcomes the mentioned limitations.
8. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Wu, Z.; Shang, T.; Guo, A. Security issues in automatic dependent surveillance-broadcast (ADS-B): A survey. IEEE Access 2020, 8, 122147–122167. [CrossRef]
- Jacob, P.; Sirigina, R.P.; Madhukumar, A.S.; Prasad, V.A. Cognitive radio for aeronautical communications: A survey. IEEE Access 2016, 4, 3417–3443. [CrossRef]
- Sciancalepore, S.; Di Pietro, R. SOS: Standard-compliant and packet loss tolerant security framework for ADS-B communications. IEEE Trans. Dependable Secur. Comput. 2019, 18, 1681–1698. [CrossRef]
- Yang, C.; Mott, J.; Bullock, D.M. Leveraging aircraft transponder signals for measuring aircraft fleet mix at non-towered airports. Int. J. Aviat. Aeronaut. Aerosp. 2021, 8, 1. [CrossRef]
- Baek, J.; Hableel, E.; Byon, Y.-J.; Wong, D.S.; Jang, K.; Yeo, H. How to Protect ADS-B: Confidentiality Framework and Efficient Realization Based on Staged Identity-Based Encryption. IEEE Trans. Intell. Transp. Syst. 2017, 18, 690–700. [CrossRef]
- RTCA DO-282; Minimum Operational Performance Standards for Universal Access Transceiver (UAT) Automatic Dependent Surveillance Broadcast (ADS-B). RTCA: Washington, DC, USA, 2004.
- Martone, P.J.; Tucker, G.E. Candidate requirements for multilateration and ADS-B systems to serve as alternatives to secondary radar. In Proceedings of the 20th DASC. 20th Digital Avionics Systems Conference (Cat. No. 01CH37219), Daytona Beach, FL, USA, 14–18 October 2001; IEEE: New York, NY, USA; pp. 7C2-1. [CrossRef]
- Rekkas, C.; Rees, M. Towards ADS-B implementation in Europe. In Proceedings of the 2008 Tyrrhenian International Workshop on Digital Communications-Enhanced Surveillance of Aircraft and Vehicles, Capri, Italy, 3–5 September 2008; IEEE: New York, NY, USA, ; pp. 1–4. [CrossRef]
- Costin, A.; Francillon, A. Ghost in the Air (Traffic): On insecurity of ADS-B protocol and practical attacks on ADS-B devices. Black Hat USA 2012, 1, 1–12.
- Haines, B. “Hackers+ airplanes,” No good can come of this. Defcon 2012, 20, 26–29.
- Kelly, H. Researcher: New air traffic control system is hackable. CNN blog, July 26, 2012.
- Marks, P. Air Traffic System Vulnerable to Cyber Attack; Elsevier: Amsterdam, The Netherlands, 2011.
- Greenberg, A. Next-gen air traffic control vulnerable to hackers spoofing planes out of thin air. Forbes Mag. 2012, 10, 2014.
- Schäfer, M.; Lenders, V.; Martinovic, I. Experimental analysis of attacks on next generation air traffic communication. In Proceedings of theApplied Cryptography and Network Security: 11th International Conference, ACNS 2013, Banff, AB, Canada, 25–28 June 2013; Proceedings 11; Springer: Berlin/Heidelberg, Germany, 2013; pp. 253–271. [CrossRef]
- Dave, G.; Choudhary, G.; Sihag, V.; You, I.; Choo, K.-K.R. Cyber security challenges in aviation communication, navigation, and surveillance. Comput. Secur. 2022, 112, 102516. [CrossRef]
- Kraus, T.L. Celebrating a History of Excellence: The Federal Aviation Administration and Space Education Outreach Program; U.S. Department of Transportation, Federal Aviation Administration: Washington, DC, USA, 2011.
- Williams, G. (2009). GPS for the sky: A survey of automatic dependent surveillance-broadcast (ADS-B) and its implementation in the United States. J. Air L. & Com., 74, 473.
- Petrović, G. (2024). View on Regulations Concerning Communication, Navigation and Surveillance (CNS) Service in Civil Aviation. Air and Space Law, 49(2). [CrossRef]
- Kumari, A., Kumar, D., Sati, P., Kumar, S., Yadav, A. K., & Verma, A. S. (2024). Overview of Aviation Sector, Feedstock, and Supply Chain. In Biojet Fuel: Current Technology and Future Prospect (pp. 17-35). Singapore: Springer Nature Singapore. [CrossRef]
- Pennapareddy, S.; Natarajan, K. Securing ADS-B data transmissions using blockchain: A comprehensive survey and analysis. Aircr. Eng. Aerosp. Technol. 2023, 95, 452–463. [CrossRef]
- Habib, G., Sharma, S., Ibrahim, S., Ahmad, I., Qureshi, S., & Ishfaq, M. (2022). Blockchain technology: benefits, challenges, applications, and integration of blockchain technology with cloud computing. Future Internet, 14(11), 341. [CrossRef]
- Manesh, M.R.; Kaabouch, N. Analysis of vulnerabilities, attacks, countermeasures and overall risk of the Automatic Dependent Surveillance-Broadcast (ADS-B) system. Int. J. Crit. Infrastruct. Prot. 2017, 19, 16–31. [CrossRef]
- Strohmeier, M.; Lenders, V.; Martinovic, I. On the security of the automatic dependent surveillance-broadcast protocol. IEEE Commun. Surv. Tutor. 2015, 17, 1066–1087. [CrossRef]
- Strohmeier, M.; Schafer, M.; Lenders, V.; Martinovic, I. Realities and challenges of nextgen air traffic management: The case of ADS-B. IEEE Commun. Mag. 2014, 52, 111–118. [CrossRef]
- Strohmeier, M.; Lenders, V.; Martinovic, I. Security of ADS−B: State of the Art and Beyond; Department of Computer Science, University of Oxford: Oxford, UK, 2013.
- McCallie, D.; Butts, J.; Mills, R. Security analysis of the ADS-B implementation in the next generation air transportation system. Int. J. Crit. Infrastruct. Prot. 2011, 4, 78–87. [CrossRef]
- Stastny, P.; Stoica, A.-M. Protecting aviation safety against cybersecurity threats. IOP Conf. Series Mater. Sci. Eng. 2022, 1226, 012025. [CrossRef]
- Lu, X.; Dong, R.; Wang, Q.; Zhang, L. Information Security Architecture Design for Cyber-Physical Integration System of Air Traffic Management. Electronics 2023, 12, 1665. [CrossRef]
- Paraschi, E.P.; Georgopoulos, A.; Papanikou, M. Safety and security implications of crisis-driven austerity HRM practices in commercial aviation: A structural equation modelling approach. Saf. Sci. 2022, 147, 105570. [CrossRef]
- Imran, M. A., Zennaro, M., Popoola, O. R., Chiaraviglio, L., Zhang, H., Manzoni, P., ... & Pietrosemoli, E. (2024). Exploring the Boundaries of Connected Systems: Communications for Hard-to-Reach Areas and Extreme Conditions. Proceedings of the IEEE. [CrossRef]
- Ukwandu, E.; Ben-Farah, M.A.; Hindy, H.; Bures, M.; Atkinson, R.; Tachtatzis, C.; Andonovic, I.; Bellekens, X. Cyber-Security Challenges in Aviation Industry: A Review of Current and Future Trends. Information 2022, 13, 146. [CrossRef]
- Tang, J.; Liu, G.; Pan, Q. Review on artificial intelligence techniques for improving representative air traffic management capability. J. Syst. Eng. Electron. 2022, 33, 1123–1134. [CrossRef]
- Rezo, Z.; Steiner, S.; Mihetec, T.; Čokorilo, O. Strategic planning and development of Air Traffic Management system in Europe: A capacity-based review. Transp. Res. Procedia 2023, 69, 5–12. [CrossRef]
- Mäurer, N.; Guggemos, T.; Ewert, T.; Gräupl, T.; Schmitt, C.; Grundner-Culemann, S. Security in Digital Aeronautical Communications A Comprehensive Gap Analysis. Int. J. Crit. Infrastruct. Prot. 2022, 38, 100549. [CrossRef]
- Valovage, E. Enhanced ADS-B Research. In Proceedings of the 2006 IEEE/AIAA 25TH Digital Avionics Systems Conference, Portland, OR, USA, 15–19 October 2006; pp. 1–7. [CrossRef]
- Boyen, X. A tapestry of identity-based encryption: Practical frameworks compared. Int. J. Appl. Cryptogr. 2008, 1, 3. [CrossRef]
- Chan-Tin, E.; Feldman, D.; Hopper, N.; Kim, Y. The frog-boiling attack: Limitations of anomaly detection for secure network coordinate systems. In Proceedings of the Security and Privacy in Communication Networks: 5th International ICST Conference, SecureComm 2009, Athens, Greece, 14–18 September 2009; Revised Selected Papers 5; Springer: Berlin/Heidelberg, Germany, 2009; pp. 448–458. [CrossRef]
- Finke, C.; Butts, J.; Mills, R.; Grimaila, M. Enhancing the security of aircraft surveillance in the next generation air traffic control system. Int. J. Crit. Infrastruct. Prot. 2013, 6, 3–11. [CrossRef]
- Phelps, B., Klinger-Neviska, Z., Mourning, C., & Braasch, M. (2024, April). Quantum in Aviation Security: ADS-B Protection with QKD. In 2024 Integrated Communications, Navigation and Surveillance Conference (ICNS) (pp. 1-8). IEEE. [CrossRef]
- Manesh, M.R.; Kaabouch, N. Cyber-attacks on unmanned aerial system networks: Detection, countermeasure, and future research directions. Comput. Secur. 2019, 85, 386–401. [CrossRef]
- FAA Reauthorization Act: Progress and Challenges Implementing Various Provisions of the 2012 Act. Available online: https://apps.dtic.mil/sti/citations/AD1102097 (accessed on 23 December 2023).
- Gorman, S.; Dreazen, Y.J.; Cole, A. Insurgents hack US drones. The Wall Street Journal, Dec. 17, December 2009. https://www.wsj.com/articles/SB126102247889095011.
- Katz, Y. IDF encrypting drones after Hezbollah accessed footage. Jerusalem Post, 2010. https://www.jpost.com/israel/idf-encrypting-drones-after-hizbullah-accessed-footage.
- Wood, A. (2024). After ADS-B launch, security concerns raised: AIN., September 14, 2006, Retrieved from https://www.ainonline.com/aviation-news/air-transport/2006-09-14/after-ads-b-launch-security-concerns-raised.
- Ganaie, N.A. India’s National Security: Issues and Challenges. Available online: https://books.google.com.pk/books?hl=en&lr=&id=adWmEAAAQBAJ&oi=fnd&pg=PA59&dq=NDTV,+A+phone+application+that+threatens+security,+Press+Trust+of+India,+New+Delhi,+India,+October+4,+2010.&ots=F5jZB7KOW6&sig=heSBl1Bmq6nbxSXXql1snctwwQc&redir_esc=y#v=onepage&q&f=false (accessed on 23 December 2023).
- Unnikrishnan, M., ITT Calls On AT&T For ADS-B Infrastructure, Network Centers. (2007). September 04, 2007, Retrieved from https://aviationweek.com/itt-calls-att-ads-b-infrastructure-network-centers.
- Spainhower, M.; Butts, J.; Guernsey, D.; Shenoi, S. Security analysis of RSVP-TE signaling in MPLS networks. Int. J. Crit. Infrastruct. Prot. 2008, 1, 68–74. [CrossRef]
- Fried, A., & Last, M. (2021). Facing airborne attacks on ADS-B data with autoencoders. Computers & Security, 109, 102405. [CrossRef]
- Manesh, M.R.; Mullins, M.; Foerster, K.; Kaabouch, N. A preliminary effort toward investigating the impacts of ADS-B message injection attack. In Proceedings of the in 2018 IEEE Aerospace Conference, Big Sky, MT, USA, 3–10 March 2018; IEEE: New York, NY, USA; 2018, pp. 1–6. [CrossRef]
- Mirzaei, K. F., Carvalho, B. P. de, & Pschorn, P. (2019). March 23, 2019, EasyChair Preprint no. 851, Security of ADS-B: Attack Scenarios. Retrieved from https://easychair.org/publications/preprint/DpM4.
- Shang, F.; Wang, B.; Yan, F.; Li, T. Multidevice false data injection attack models of ADS-B multilateration systems. Secur. Commun. Netw. 2019, 2019, 8936784. [CrossRef]
- Lubbe, H., Serfontein, R., & Coetzee, M. (2024, March). Assessing the Effectiveness of ADS-B Mitigations. In International Conference on Cyber Warfare and Security (Vol. 19, No. 1, pp. 535-544).
- Yang, H.; Li, H.; Shen, X.S. Modern Cryptography for ADS-B Systems. In Secure Automatic Dependent Surveillance-Broadcast Systems; Springer: Berlin/Heidelberg, Germany, 2022; pp. 19–59.
- Bavdekar, R.; Chopde, E.J.; Agrawal, A.; Bhatia, A.; Tiwari, K. Post Quantum Cryptography: A Review of Techniques, Challenges and Standardizations. In Proceedings of the International Conference on Information Networking, Bangkok, Thailand, 11–14 January 2023; pp. 146–151. [CrossRef]
- Jochum, L.R.J. Encripted Mode Select ADS-B for Tactical Military Situational Awareness. 2001. Available online: https://dspace.mit.edu/bitstream/handle/1721.1/86721/49223652-MIT.pdf;sequence=2 (accessed on 25 December 2023).
- Kožović, D. V., Đurđević, D. Ž., Dinulović, M. R., Milić, S., & Rašuo, B. P. (2023). Air traffic modernization and control: ADS-B system implementation update 2022: A review. FME Transactions, 51(1), 117-130. [CrossRef]
- Agbeyibor, R. Secure ADS-B: Towards Airborne Communications Security in the Federal Aviation Administration’s Next Generation Air Transportation System. Theses and Dissertations. 2014. Available online: https://scholar.afit.edu/etd/584 (accessed on 25 December 2023).
- Wesson, K.D.; Humphreys, T.E.; Evans, B.L. Can cryptography secure next generation air traffic surveillance? IEEE Security and Privacy Magazine, 20-Mar-2014., p. 1-8.
- Zhang, S.; Li, H.; Dai, Y.; Li, J.; He, M.; Lu, R. Verifiable Outsourcing Computation for Matrix Multiplication With Improved Efficiency and Applicability. IEEE Internet Things J. 2018, 5, 5076–5088. [CrossRef]
- Li, H.; Yang, Y.; Dai, Y.; Yu, S.; Xiang, Y.; Bai, J. Achieving Secure and Efficient Dynamic Searchable Symmetric Encryption over Medical Cloud Data. IEEE Trans. Cloud Comput. 2020, 8, 484–494. [CrossRef]
- Feng, Z.; Pan, W.; Wang, Y. A data authentication solution of ADS-B system based on X. 509 certificate. In Proceedings of the 27th International Congress of the Aeronautical Sciences, ICAS, Nice, France, 19–24 September 2010; pp. 1–6.
- Gentry, C.; Silverberg, A. Hierarchical ID-based cryptography. In Proceedings of the Advances in Cryptology—ASIACRYPT 2002: 8th International Conference on the Theory and Application of Cryptology and Information Security Queenstown, New Zealand, 1–5 December 2002; Springer: Berlin/Heidelberg, Germany, 2002; Volume 2501, pp. 548–566. [CrossRef]
- Chow, S.S.M.; Hui, L.C.K.; Yiu, S.M.; Chow, K.P. Secure hierarchical identity based signature and its application. In Proceedings of the Information and Communications Security: 6th International Conference, ICICS 2004, Malaga, Spain, 27–29 October 2004; Springer: Berlin/Heidelberg, Germany, 2004; Volume 3269, pp. 480–494. [CrossRef]
- Cook, E. ADS-B, friend or foe: ADS-B message authentication for NextGen aircraft. In Proceedings of the 2015 IEEE 17th International Conference on High Performance Computing and Communications, 2015 IEEE 7th International Symposium on Cyberspace Safety and Security, and 2015 IEEE 12th International Conference on Embedded Software and Systems, New York, NY, USA, 24–26 August 2015; IEEE: New York, NY, USA, 2015; pp. 1256–1261. [CrossRef]
- Sher, B., Ahmad, M., Mansoor, K., Bangash, Y. A., Iqbal, W., & Mussiraliyeva, S. (2024). Lightweight secure authentication protocol for automatic dependent surveillance broadcast system. Cluster Computing, 1-16. [CrossRef]
- Pan, W.J.; Feng, Z.L.; Wang, Y. ADS-B data authentication based on ECC and X. 509 certificate. J. Electron. Sci. Technol. 2012, 10, 51–55. [CrossRef]
- Baek, J.; Byon, Y.J.; Hableel, E.; Al-Qutayri, M. An authentication framework for Automatic Dependent Surveillance-Broadcast based on online/offline identity-based signature. In Proceedings of the 2013 8th International Conference on P2P, Parallel, Grid, Cloud and Internet Computing, 3PGCIC 2013, Compiegne, France, 28–30 October 2013; pp. 358–363. [CrossRef]
- Yang, H.; Huang, R.; Wang, X.; Deng, J.; Chen, R. EBAA: An efficient broadcast authentication scheme for ADS-B communication based on IBS-MR. Chin. J. Aeronaut. 2014, 27, 688–696. [CrossRef]
- Markani, J.H.; Amrhar, A.; Gagné, J.-M.; Landry, R.J. Security establishment in ADS-B by format-preserving encryption and blockchain schemes. Appl. Sci. 2023, 13, 3105. [CrossRef]
- EBSCOhost|100818950| An Efficient Broadcast Authentication Scheme with Batch Verification for ADS-B Messages. Available online: https://web.s.ebscohost.com/abstract?direct=true&profile=ehost&scope=site&authtype=crawler&jrnl=19767277&AN=100818950&h=TvZ4Ne1ukku%2fhD0aeo%2b%2f09%2fGkYyBFZcpHy%2bND%2bDGPvpWm%2fD1kjjgBLTouRjqDOR1%2fC04tSdBXQ07dlSl6WYGjA%3d%3d&crl=c&resultNs=AdminWebAuth&resultLocal=ErrCrlNotAuth&crlhashurl=login.aspx%3fdirect%3dtrue%26profile%3dehost%26scope%3dsite%26authtype%3dcrawler%26jrnl%3d19767277%26AN%3d100818950 (accessed on 26 December 2023).
- Yang, A.; Tan, X.; Baek, J.; Wong, D.S. A new ADS-B authentication framework based on efficient hierarchical identity-based signature with batch verification. IEEE Trans. Serv. Comput. 2015, 10, 165–175. [CrossRef]
- Chen, X., He, D., Peng, C., Luo, M., & Huang, X. (2024). A Secure and Effective Hierarchical Identity-based Signature Scheme for ADS-B Systems. IEEE Transactions on Aerospace and Electronic Systems. [CrossRef]
- Yang, H., Zhou, Q., Yao, M., Lu, R., Li, H., & Zhang, X. (2018). A practical and compatible cryptographic solution to ADS-B security. IEEE Internet of Things Journal, 6(2), 3322-3334. [CrossRef]
- Pennapareddy, S., Srinivasan, R., & K, N. (2024). A method to mitigate cyber exploits on automatic dependent surveillance-broadcast (ADS-B) data transmissions. Aircraft Engineering and Aerospace Technology, 7 May 2024. [CrossRef]
- Yang, H.; Yao, M.; Xu, Z.; Liu, B. LHCSAS: A Lightweight and Highly-Compatible Solution for ADS-B Security. In Proceedings of the 2017 IEEE Global Communications Conference, GLOBECOM 2017—Proceedings, Singapore, 4–8 December 2017; Volume 2018; pp. 1–7. [CrossRef]
- Yang, H.; Li, H.; Shen, X.S. Secure Automatic Dependent Surveillance-Broadcast Systems; Springer: Berlin/Heidelberg, Germany, 2022. [CrossRef]
- Boneh, D.; Franklin, M. Identity-Based Encryption from the Weil Pairing. SIAM J. Comput. 2003, 32, 586–615. [CrossRef]
- Yi, P.; Li, J.; Zhang, Y.; Chen, Y. Efficient Hierarchical Signature Scheme with Batch Verification Function Suitable for ADS-B System. IEEE Trans. Aerosp. Electron. Syst. 2023, 59, 1292–1299. [CrossRef]
- Asari, A.; Alagheband, M.R.; Bayat, M.; Asaar, M.R. A new provable hierarchical anonymous certificateless authentication protocol with aggregate verification in ADS-B systems. Comput. Networks 2021, 185, 107599. [CrossRef]
- He, D.; Kumar, N.; Choo, K.-K.R.; Wu, W. Efficient hierarchical identity-based signature with batch verification for automatic dependent surveillance-broadcast system. IEEE Trans. Inf. Forensics Secur. 2017, 12, 454–464. [CrossRef]
- Burfeind, B.; Mills, R.; Nykl, S.; Betances, J.A.; Sielski, C. Confidential ADS-B. In Proceedings of the IEEE Aerospace Conference Proceedings, Big Sky, MT, USA, 2–9 March 2019; Volume 2019. [CrossRef]
- Braeken, A. Holistic Air Protection Scheme of ADS-B Communication. IEEE Access 2019, 7, 65251–65262. [CrossRef]
- Manesh, M.R.; Velashani, M.S.; Ghribi, E.; Kaabouch, N. Performance comparison of machine learning algorithms in detecting jamming attacks on ADS-B devices. In Proceedings of the 2019 IEEE International Conference on Electro Information Technology (EIT), Brookings, SD, USA, 20–22 May 2019; IEEE: New York, NY, USA, 2019; pp. 200–206. [CrossRef]
- Kacem, T.; Kaya, A.; Keceli, A.S.; Catal, C.; Wijsekera, D.; Costa, P. ADS-B Attack Classification using Machine Learning Techniques. In Proceedings of the 2021 IEEE Intelligent Vehicles Symposium Workshops (IV Workshops), Nagoya, Japan, 11–17 July 2021; IEEE: New York, NY, USA, 2021; pp. 7–12. [CrossRef]
- Yang, H.; Li, H.; Shen, X.S. Complete ADS-B Security Solution. In Secure Automatic Dependent Surveillance-Broadcast Systems; Springer: Berlin/Heidelberg, Germany, 2022; pp. 117–141.
- Khan, S.; Thorn, J.; Wahlgren, A.; Gurtov, A. Intrusion detection in automatic dependent surveillance-broadcast (ADS-B) with machine learning. In Proceedings of the 2021 IEEE/AIAA 40th Digital Avionics Systems Conference (DASC), San Antonio, TX, USA, 3–7 October 2021; IEEE: New York, NY, USA, 2021; pp. 1–10. [CrossRef]
- Mink, D.M.; McDonald, J.; Bagui, S.; Glisson, W.B.; Shropshire, J.; Benton, R.; Russ, S. Near-Real-Time IDS for the U.S. FAA’s NextGen ADS-B. Big Data Cogn. Comput. 2021, 5, 27. [CrossRef]
- Karam, R.; Salomon, M.; Couturier, R. A comparative study of deep learning architectures for detection of anomalous ADS-B messages. In Proceedings of the 2020 7th International Conference on Control, Decision and Information Technologies (CoDIT), Prague, Czech Republic, 29 June 2020–2 July 2020; IEEE: New York, NY, USA, 2020; pp. 241–246. [CrossRef]
- Wang, J.; Zou, Y.; Ding, J. ADS-B spoofing attack detection method based on LSTM. EURASIP J. Wirel. Commun. Netw. 2020, 2020, 1–12. [CrossRef]
- Karam, R.; Salomon, M.; Couturier, R. Supervised ADS-B Anomaly Detection Using a False Data Generator. In Proceedings of the 2022 2nd International Conference on Computer, Control and Robotics (ICCCR), Shanghai, China, 18–20 March 2022; IEEE: New York, NY, USA, 2022; pp. 218–223. [CrossRef]
- Guo, X.; Zhu, C.; Yang, J.; Xiao, Y. An Anomaly Detection Model for ADS-B Systems Based on Improved GAN and LSTM Networks. In Proceedings of the 2021 IEEE 21st International Conference on Communication Technology (ICCT), Tianjin, China, 13–16 October 2021; IEEE: New York, NY, USA, 2021; pp. 802–809. [CrossRef]
- Joseph, N.S.; Banerjee, C.; Pasiliao, E.; Mukherjee, T. FlightSense: A spoofer detection and aircraft identification system using raw ADS-B data. In Proceedings of the 2020 IEEE International Conference on Big Data (Big Data), Atlanta, GA, USA, 10–13 December 2020; IEEE: New York, NY, USA, 2020; pp. 3885–3894. [CrossRef]
- Ying, X.; Mazer, J.; Bernieri, G.; Conti, M.; Bushnell, L.; Poovendran, R. Detecting ADS-B spoofing attacks using deep neural networks. In Proceedings of the 2019 IEEE Conference on Communications and Network Security (CNS), Washington, DC, USA, 10–12 June 2019; IEEE: New York, NY, USA, 2019; pp. 187–195. [CrossRef]
- Habler, E.; Shabtai, A. Using LSTM encoder-decoder algorithm for detecting anomalous ADS-B messages. Comput. Secur. 2018, 78, 155–173. [CrossRef]
- Danev, B.; Zanetti, D.; Capkun, S. On physical-layer identification of wireless devices. ACM Comput. Surv. 2012, 45, 1–29. [CrossRef]
- Zeng, K.; Govindan, K.; Mohapatra, P. Non-cryptographic authentication and identification in wireless networks [security and privacy in emerging wireless networks]. IEEE Wirel. Commun. 2010, 17, 56–62. [CrossRef]
- Liu, Y.; Ning, P.; Dai, H.; Liu, A. Randomized differential DSSS: Jamming-resistant wireless broadcast communication. In Proceedings of the 2010 Proceedings IEEE INFOCOM, San Diego, CA, USA, 14–19 March 2010; IEEE: New York, NY, USA, 2010; pp. 1–9. [CrossRef]
- Pöpper, C.; Strasser, M.; Capkun, S. Jamming-resistant broadcast communication without shared keys. In Proceedings of theUSENIX Security Symposium, Montreal, QC, Canada, 10–14 August 2009; pp. 231–248.
- Strasser, M.; Popper, C.; Capkun, S.; Cagalj, M. Jamming-resistant key establishment using uncoordinated frequency hopping. In Proceedings of the 2008 IEEE Symposium on Security and Privacy (sp 2008), Oakland, CA, USA, 18–22 May 2008; IEEE: New York, NY, USA, 2008, pp. 64–78. [CrossRef]
- Reisman, R.J., “Air traffic management blockchain infrastructure for security, authentication, and privacy. In Proceedings of the AIAA Scitech 2019 Forum, San Diego, CA, USA, 7–11 January 2019. [CrossRef]
- Kakimoto, K., Immaru, T., Ikeda, M., & Barolli, L. (2024, April). A Filtering Method for Machine Learning Utilization of ADS-B Data. In International Conference on Advanced Information Networking and Applications (pp. 251-260). Cham: Springer Nature Switzerland. [CrossRef]
- Akerman, S.; Habler, E.; Shabtai, A. VizADS-B: Analyzing Sequences of ADS-B Images Using Explainable Convolutional LSTM Encoder-Decoder to Detect Cyber Attacks. arXiv 2019, arXiv:1906.07921. https://arxiv.org/abs/1906.07921v1.
- Chen, S.; Zheng, S.; Yang, L.; Yang, X. Deep Learning for Large-Scale Real-World ACARS and ADS-B Radio Signal Classification. IEEE Access 2019, 7, 89256–89264. [CrossRef]
| Ref. and Year | Aviation System | Security Analysis | Existing Security Solution | Security Requirements | Future Research Direction | ||
|---|---|---|---|---|---|---|---|
| Cryptography | Non-Cryptography | ML/DL | |||||
| [1] 2023 |
✕ | ✓ | ✓ | ✓ | ✓ | ✕ | ✕ |
| [2] 2022 |
✓ | ✓ | ✓ | ✕ | ✕ | ✓ | ✕ |
| [3] 2020 |
✕ | ✓ | ✓ | ✓ | ✕ | ✓ | ✓ |
| [4] 2017 |
✓ | ✓ | ✓ | ✓ | ✕ | ✕ | ✓ |
| [5] 2015 |
✕ | ✓ | ✓ | ✓ | ✕ | ✓ | ✓ |
| [6] 2014 |
✓ | ✓ | ✕ | ✕ | ✕ | ✕ | ✓ |
| [7] 2013 |
✕ | ✓ | ✓ | ✓ | ✕ | ✕ | ✕ |
| [8] 2011 |
✓ | ✓ | ✕ | ✕ | ✕ | ✓ | ✕ |
| Proposed Survey | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| Abbreviation | Description | Abbreviation | Description |
|---|---|---|---|
| ADS-B | Automatic Dependent Surveillance-Broadcast | ICT | Information and Communications Technology |
| NextGen | Next Generation | ATC | Air Traffic Control |
| FAA | Federal Aviation Administration | RF | Radio Frequency |
| ACAS | Automatic Collision Avoidance System | RTC | Radio Technical Committee |
| CPDLC | Controller–Pilot Data Link Communications | VHF | Very High-Frequency |
| HF | High-Frequency | DL | Deep Learning |
| ILS | Instrument Landing System | ICAO | International Civil Aviation Organization |
| PSR | Primary Surveillance Radar | SSR | Secondary Surveillance Radar |
| ATM | Air Traffic Management | DSCN | Digital Satellite Communication Networks |
| NIST | National Institute of Standards and Technology | MPLS | Multiprotocol Labeled Switching |
| CA | Certification Authority | MAC | Message Authentication Code |
| ECDSA | Elliptic Curve Digital Signature Algorithm | IBE | Identity-Based Encryption |
| HAP | Holistic Air Protection | LSTM | Short-Term Long Memory |
| CNN | Conventional Neural Network | P2P | Peer-to-Peer |
| Threat | Impact on System |
|---|---|
| Interception | Protocol-insignificant but perhaps useful for malicious tracking. |
| Data Manipulation | Message integrity is compromised, leading to misleading or omitted collision avoidance alerts, confusion, and incorrect controller actions; safety hazard. |
| Identity Spoofing | The integrity of the message is undermined by fraudulent tracks utilized for deceiving air traffic control; risk to safety. |
| Ghost Flights | False flight information is transmitted with the intention of perplexing controllers or overloading receiver processing capacity, compromising its dependability; prudence for safety. |
| Disappearance of Original Flight |
This is accomplished by replaying the aircraft’s previous flight data before its presence in the coverage area, thus preventing disseminating the most recent flight information. |
| Year and Ref. | Dataset Description | ML Models | Accuracy |
|---|---|---|---|
| 2019 [83] | Simulated (the authors did not mention the details of the dataset and number of messages used in the experiments) | LR | 65.6% |
| SVM | 67.3% | ||
| KNN | 74.6% | ||
| ANN | 81% | ||
| DT | 74.2% | ||
| 2021 [84] | Flightradar24 (the authors used a dataset containing messages of 1 flight from Lisbon to Paris) | SVM | 91% |
| DT | 92% | ||
| RF | 90% | ||
| 2019 [85] | Simulated (the author did not mention the number of legitimate and nonlegitimate messages) | DNN | 96.66% |
| 2021 [86] | OpenSky (the dataset containing 26,000) | LR | 52.10% |
| NB | 82.10% | ||
| K-NN | 99.57% | ||
| 2021 [87] | OpenSky (dataset with 20,000 messages, 10,000 legitimate and 10,000 nonlegitimate) | SVM | 80% |
| 2020 [88] | OpenSky (the author did not mention the number of legitimate and nonlegitimate messages) | LSTM | 91.59% |
| 2020 [89] | Simulated (detecting spoofing attack, authors did not mention the details of the dataset) | LSTM | 93% |
| 2022 [90] | OpenSky (20 randomly chosen flights were downloaded from the OpenSky Network) | LSTM | 98% |
| 2021 [91] | Flightradar24 (the authors did not mention the details of the dataset) | LSTM with GAN | 97% |
| 2020 [92] | Simulated (18,675 messages were collected for experiments) | GAN | 98.87% |
| CNN | 99% |
| Category | Compatibility | Scalability | Difficulty | Cost |
|---|---|---|---|---|
| Symmetric Cryptography | Key management and sharing | Medium | High | High |
| Asymmetric Cryptography | Key generation, sharing, and storing | Medium | High | High |
| Message Authentication Code (MAC) | Key management and changing message format | Medium | Low | Low |
| Machine Learning | Need to add software | High | Low | Low |
| Spread Spectrum | Changing the system and adding hardware | Medium | High | High |
| Fingerprinting | Adding hardware, but there is no need to modify the system | Medium | Medium | High |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




