Submitted:
04 April 2024
Posted:
04 April 2024
You are already at the latest version
Abstract
Keywords:
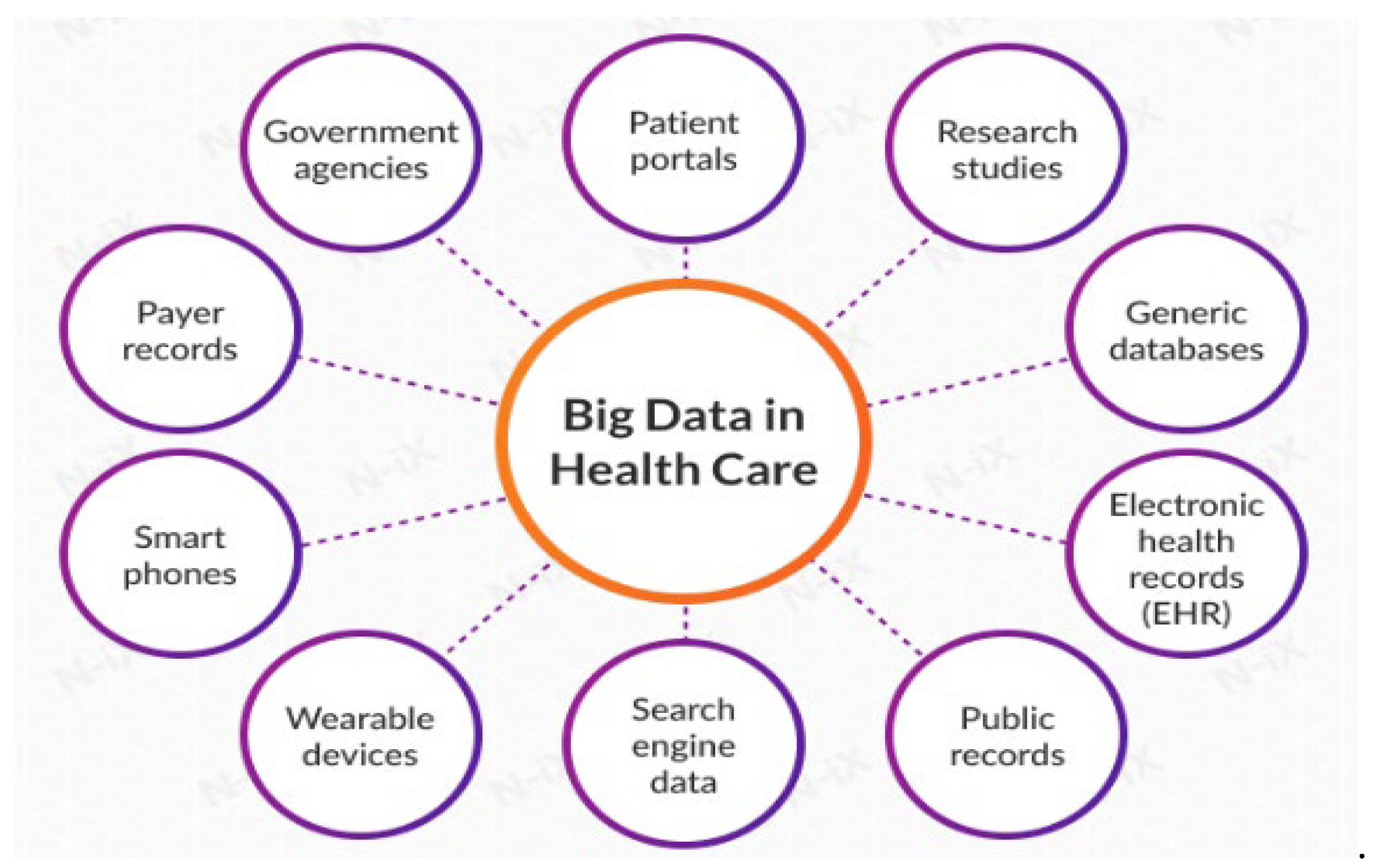
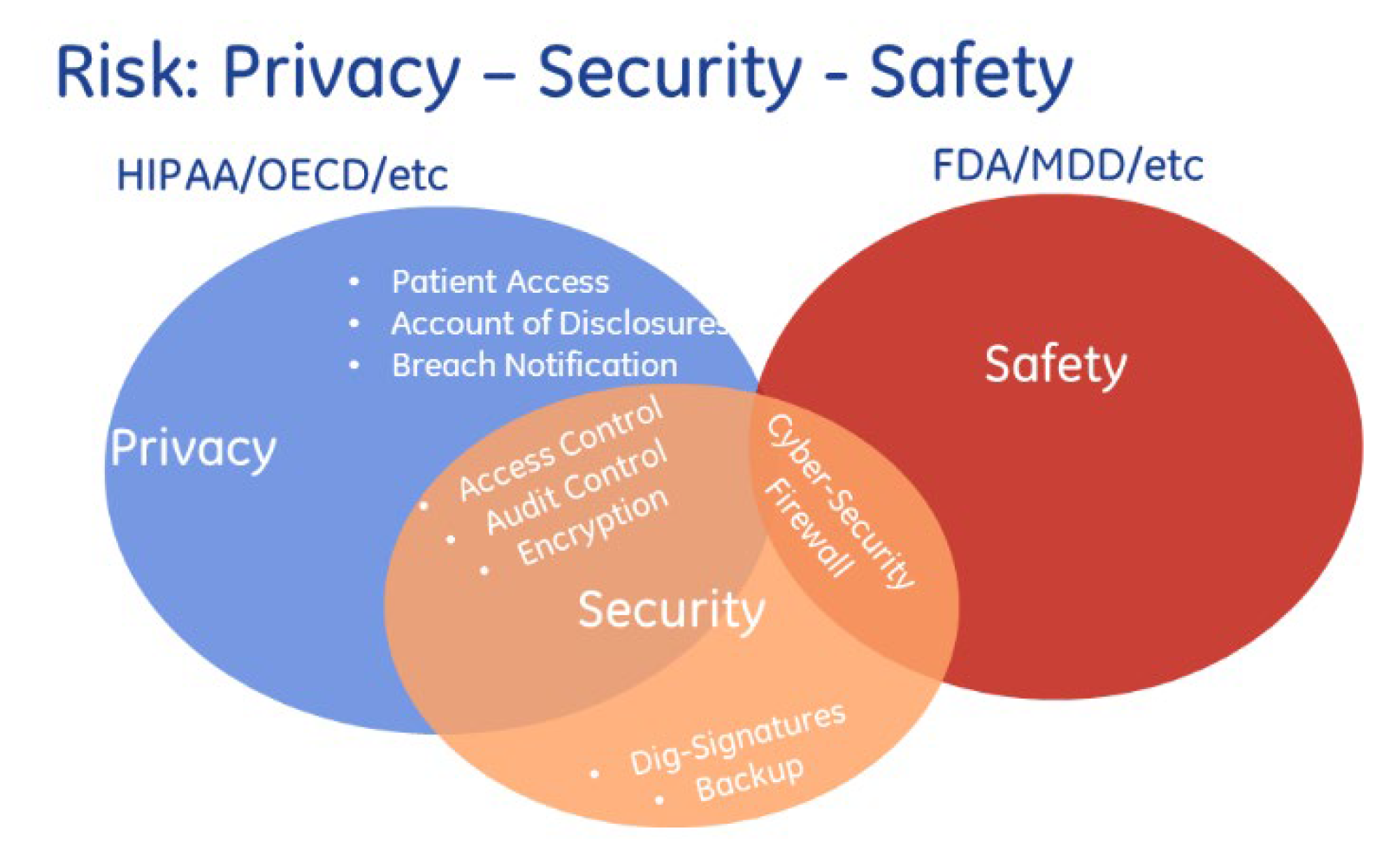
1. Introduction
2. Literature Review
3. Proposed Method
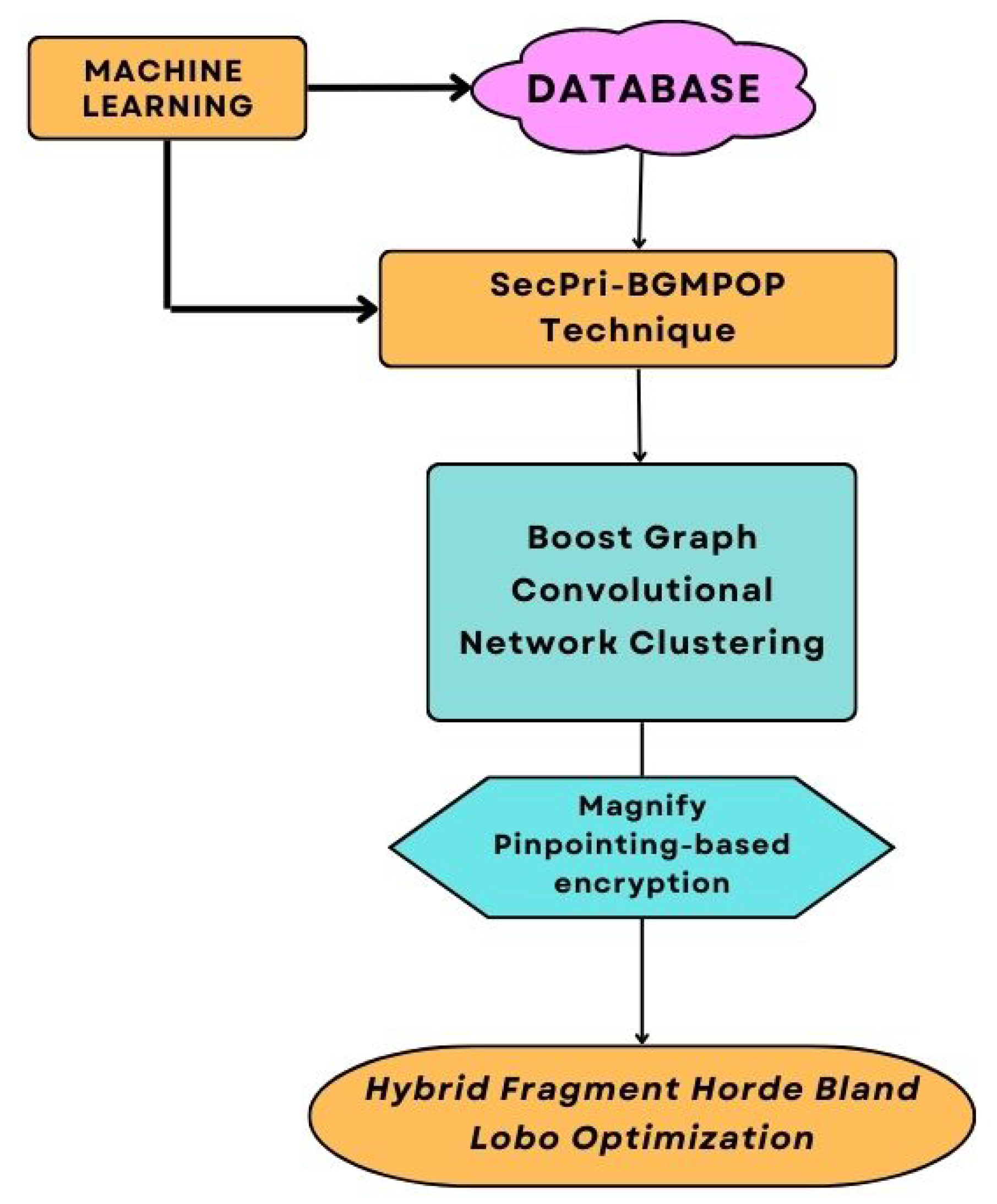
3.1. Graph Convolutional Network Clustering (GCNC)
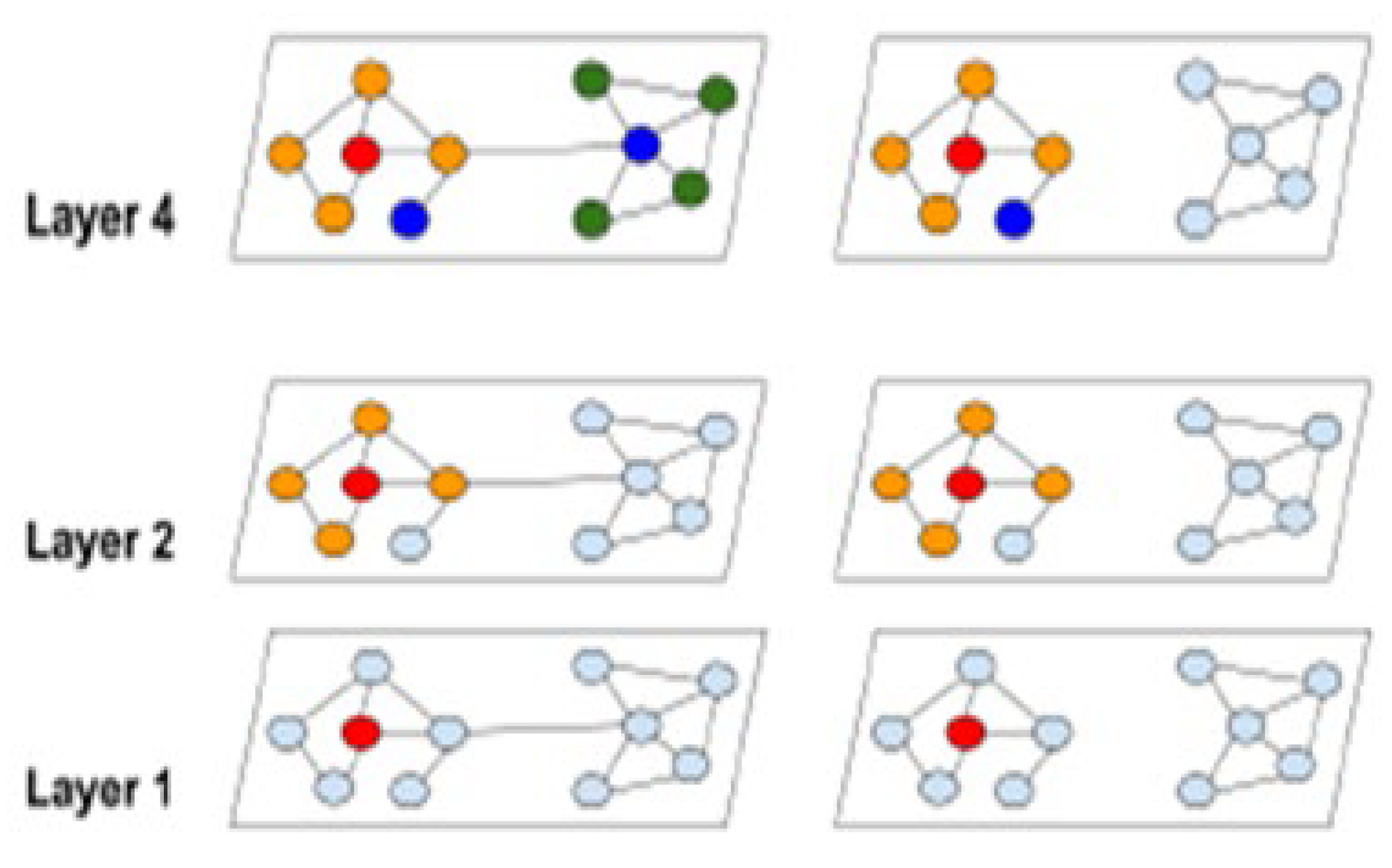
Boost Graph Convolutional Network Clustering (BGCNC)
- Certain links (the part in Eq. (2)) are eliminated from the graph after it has been partitioned. As a result, the performance can be impacted.
- Algorithms for graph clustering frequently group related nodes together. As a result, a cluster's distribution may deviate from the original data set, which could cause a skewed estimation of the complete gradient while doing SGD updates.
| Algorithm 1:Boost Graph convolutional network clustering |
| Input: Graph A, Feature X, Label Y; Output: Node representation Partition graph nodes into clusters Randomly choose clusters, from V without replacement; From the subgraph with nodes and links Compute (loss on the subgraph ); Conduct adam update using gradient estimator Output: |
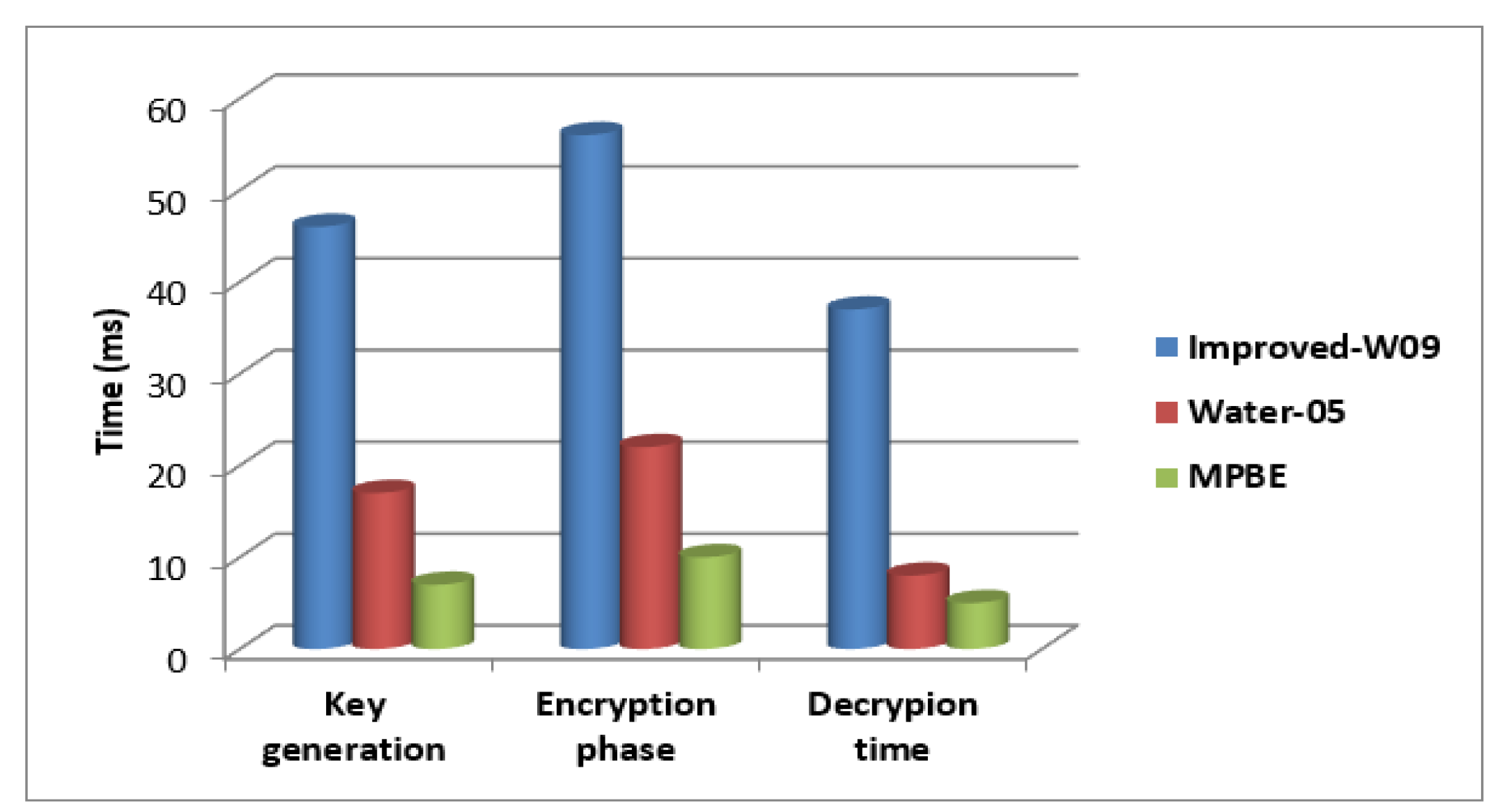
3.2. Magnify Pinpointing-Based Encryption(MPBE)
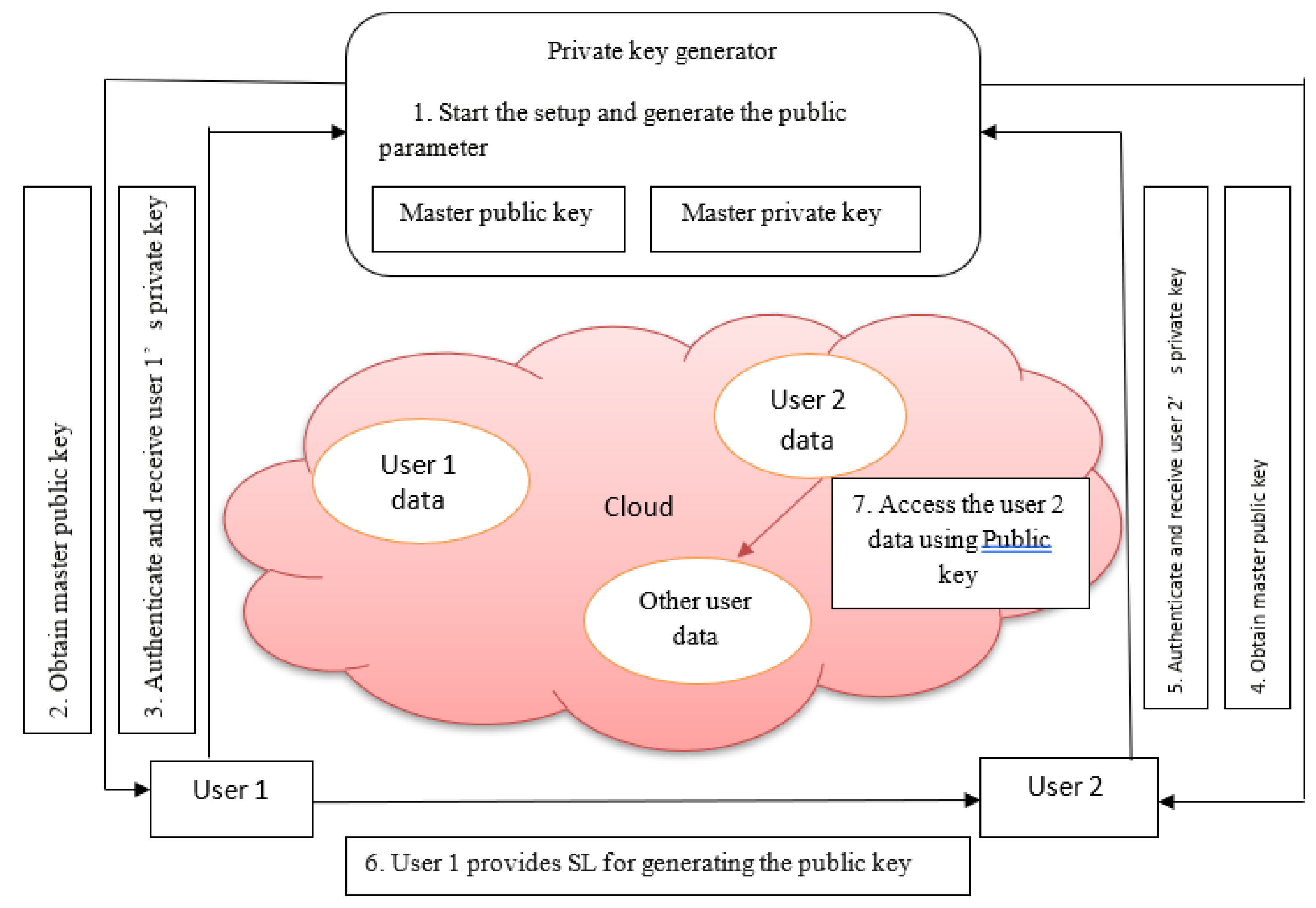
| 1. Private key generator (PKG) starts the setup process and decides the security parameters like the level of bits and type of curves. 2. Bob obtains the master public key from PKG. 3. Bob authenticates himself by issuing his identity to PKG and receives the private key for encrypting the data. 4. Similarly, Alice obtains the master public key from PKG. 5. Alice authenticates herself by issuing his identity to PKG and receives the private key for encrypting the data. 6. Bob sends his identity to Alice for generating the public key related to Bob’s identity. Alice will use this key to decrypt the data authenticated by Bob. 7. Alice gets the Bob’s data from database and decrypts it for accessing. |
3.2.1. Initial Phase
3.2.2. Generation Phase
3.2.3. Encryption Phase
3.2.4. Decryption Phase
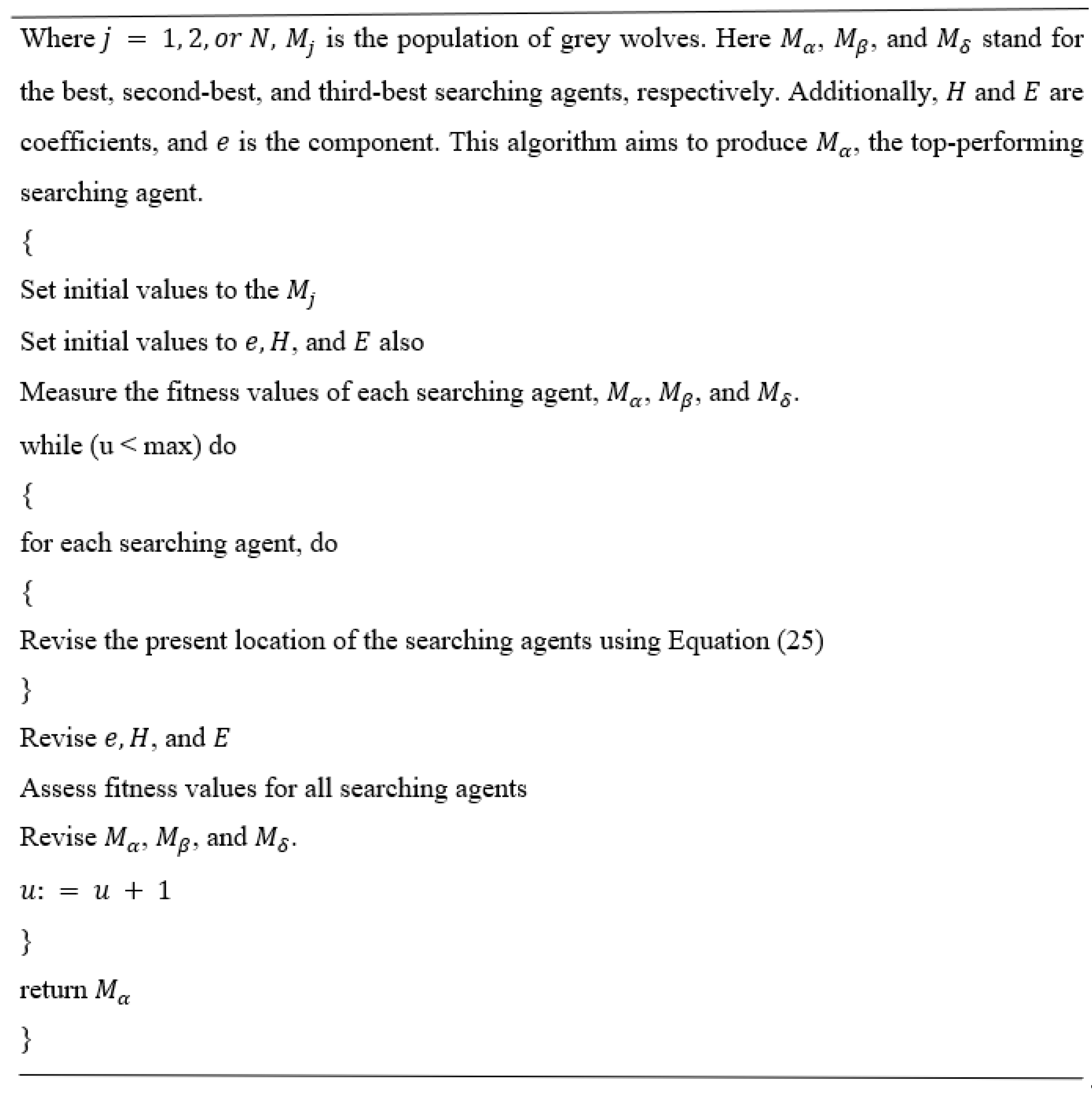
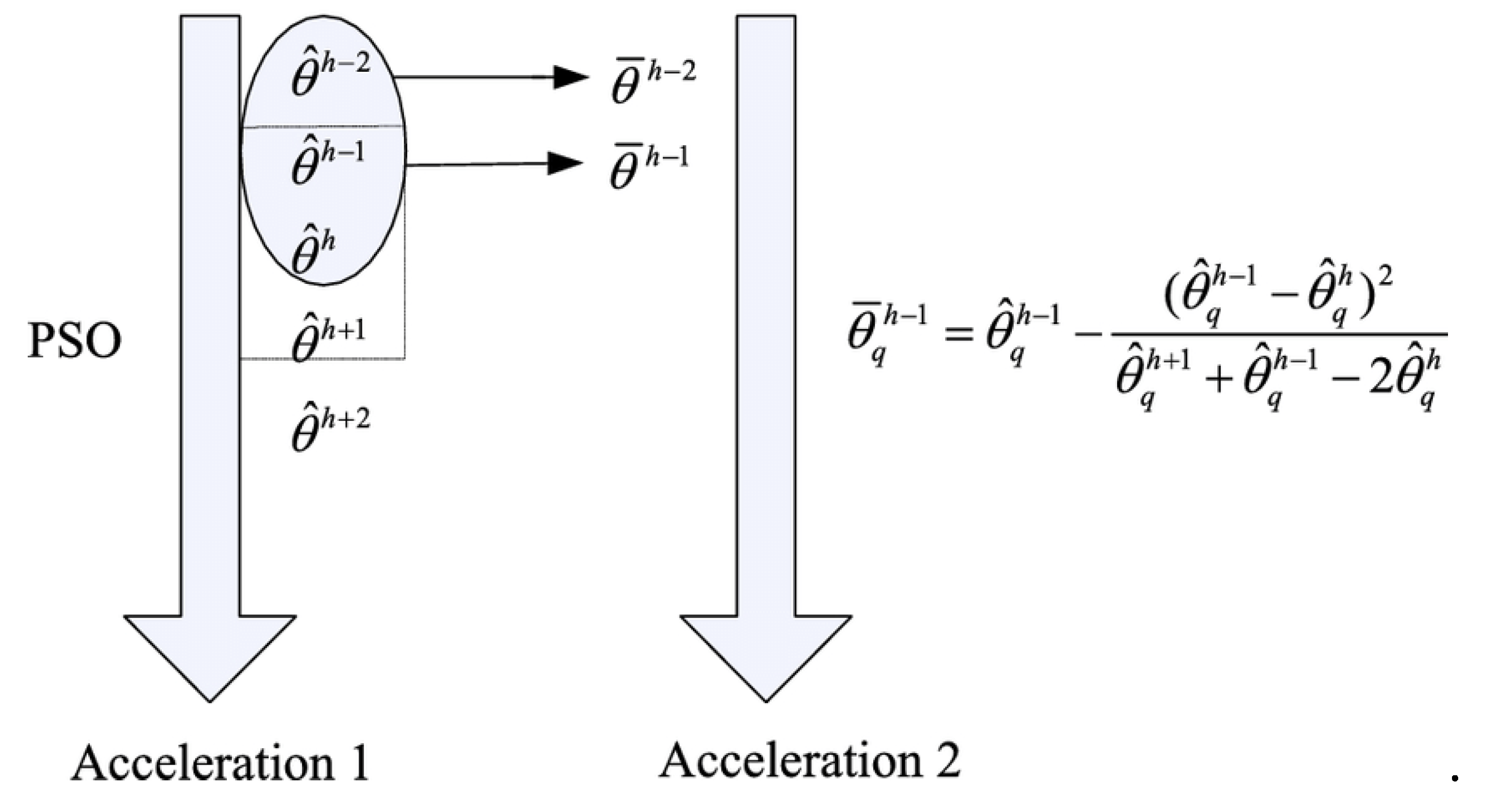
3.3. Hybrid Fragment Horde Bland lobo Optimization
3.3.1. Traditional PSO Algorithm
3.3.2. Traditional GWO Algorithm
3.3.2. Hybrid Fragment Horde Bland Lobo Optimization
4. Results and Discussion
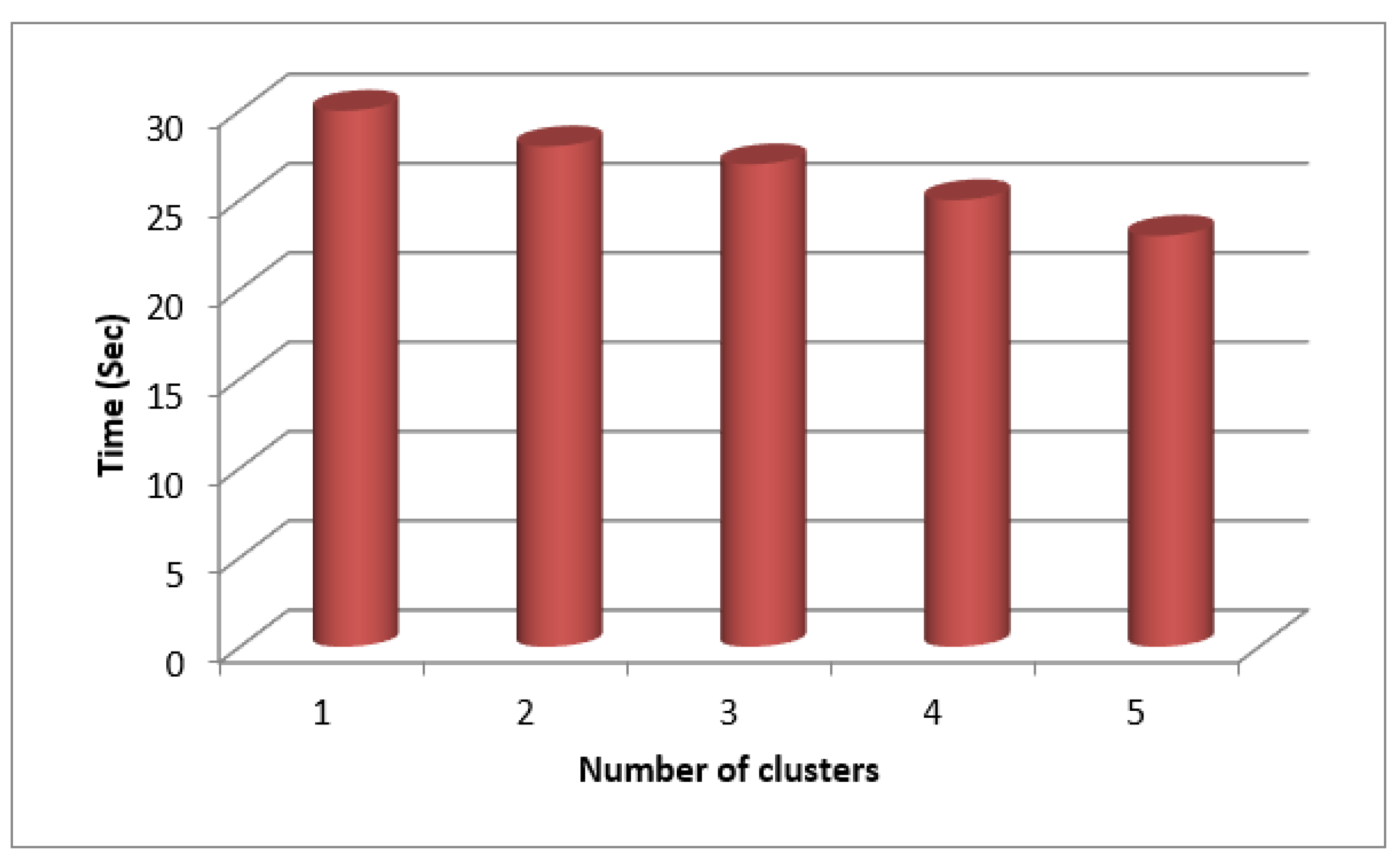
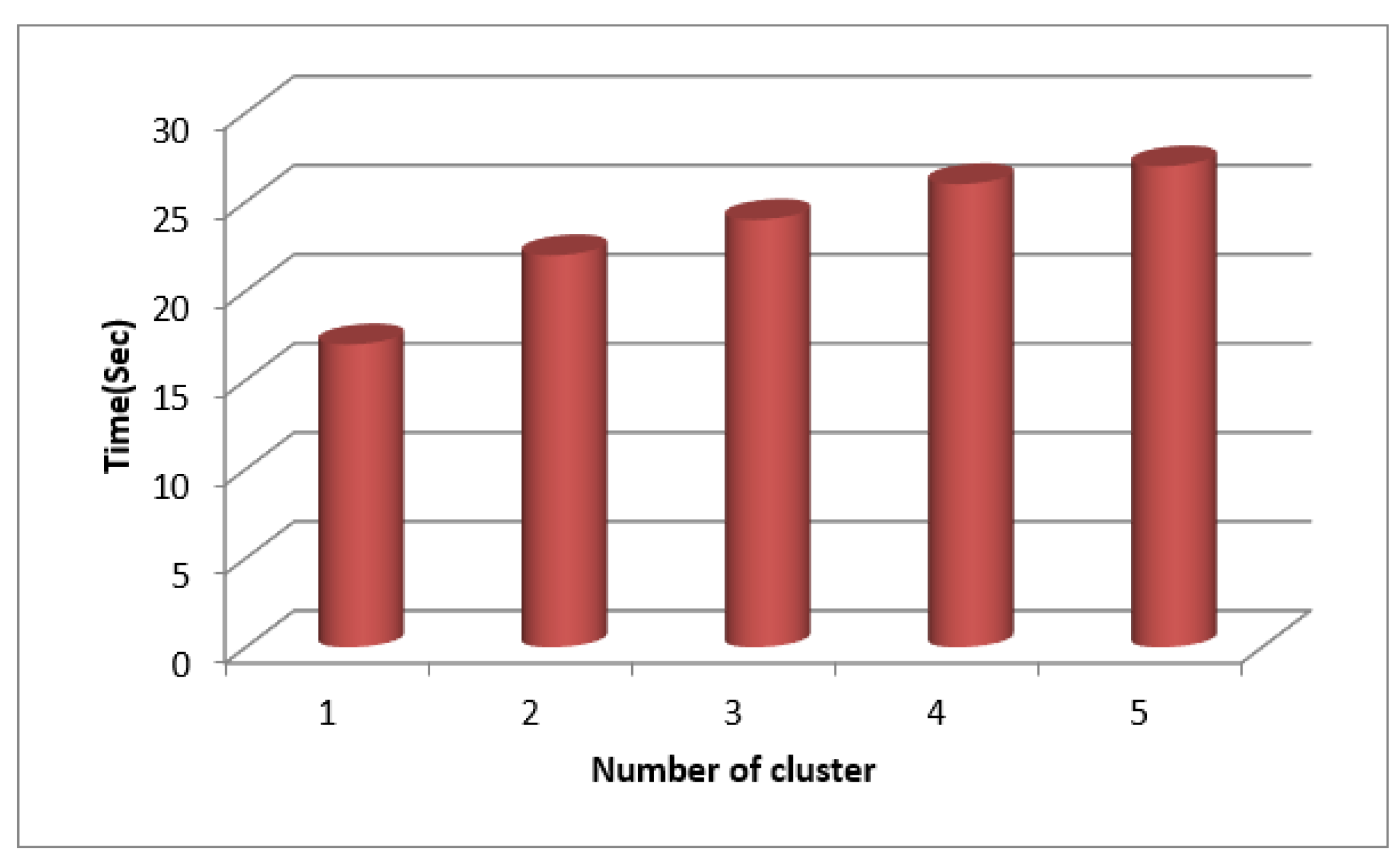
4.1. Running Time
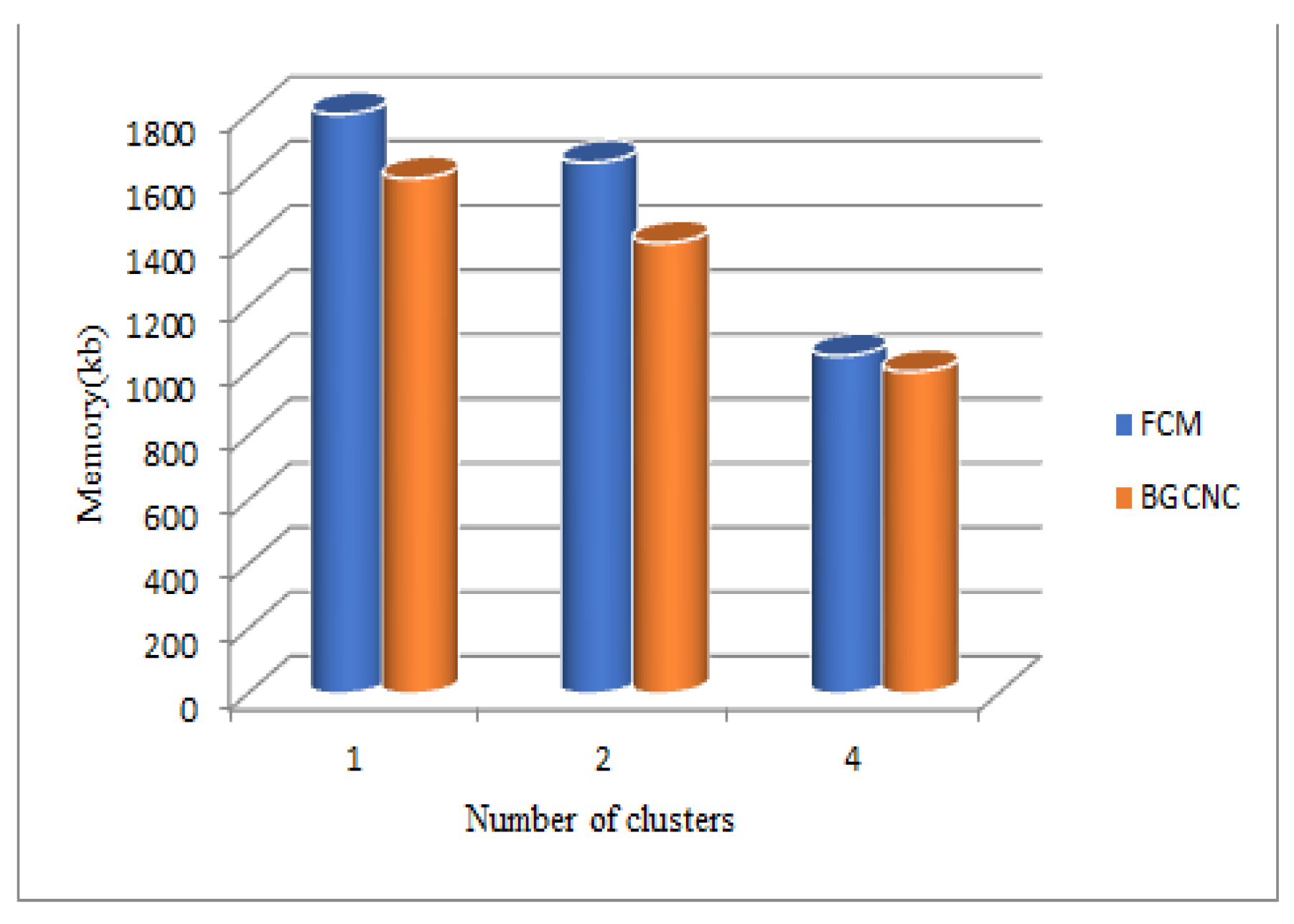
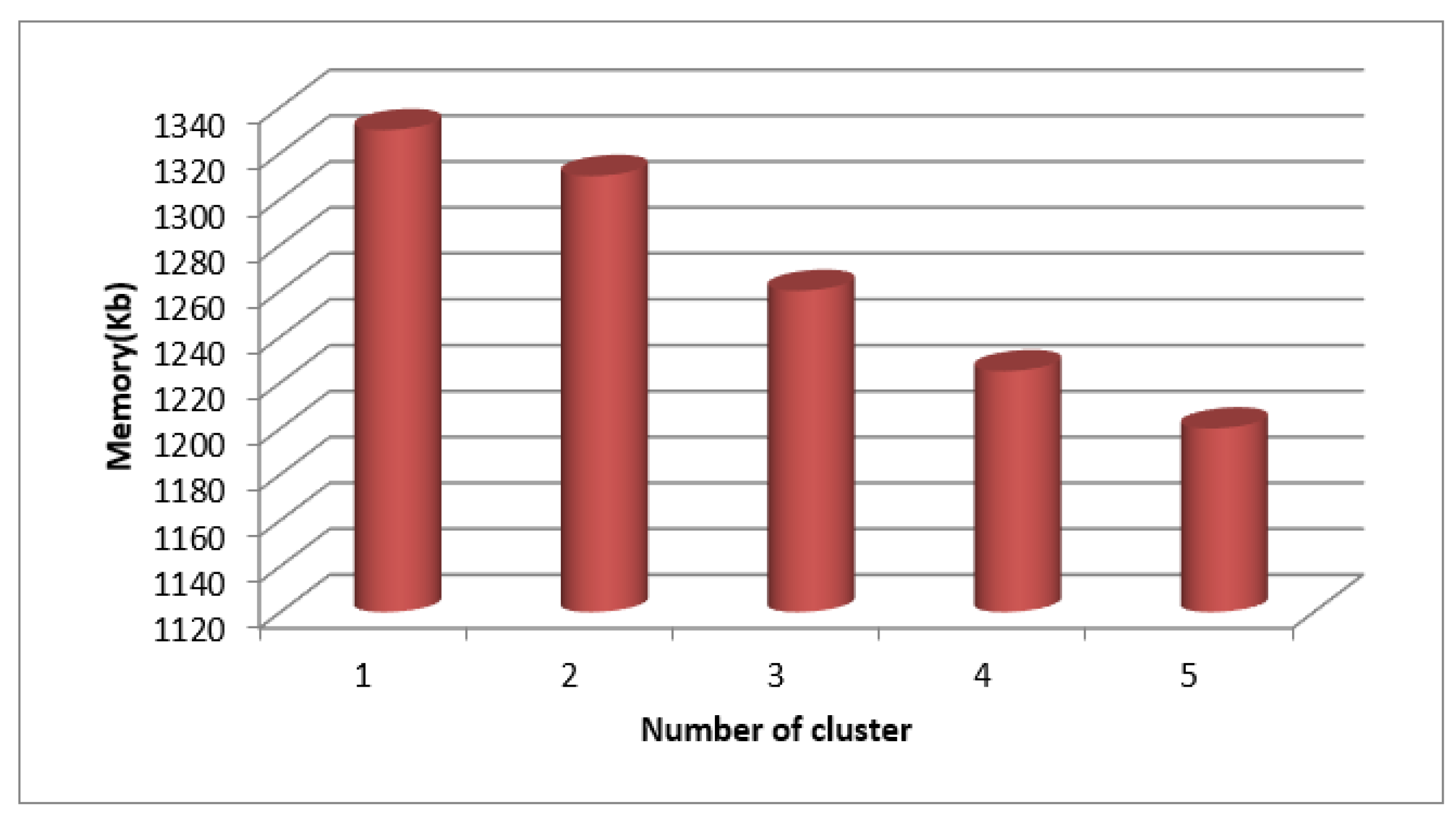
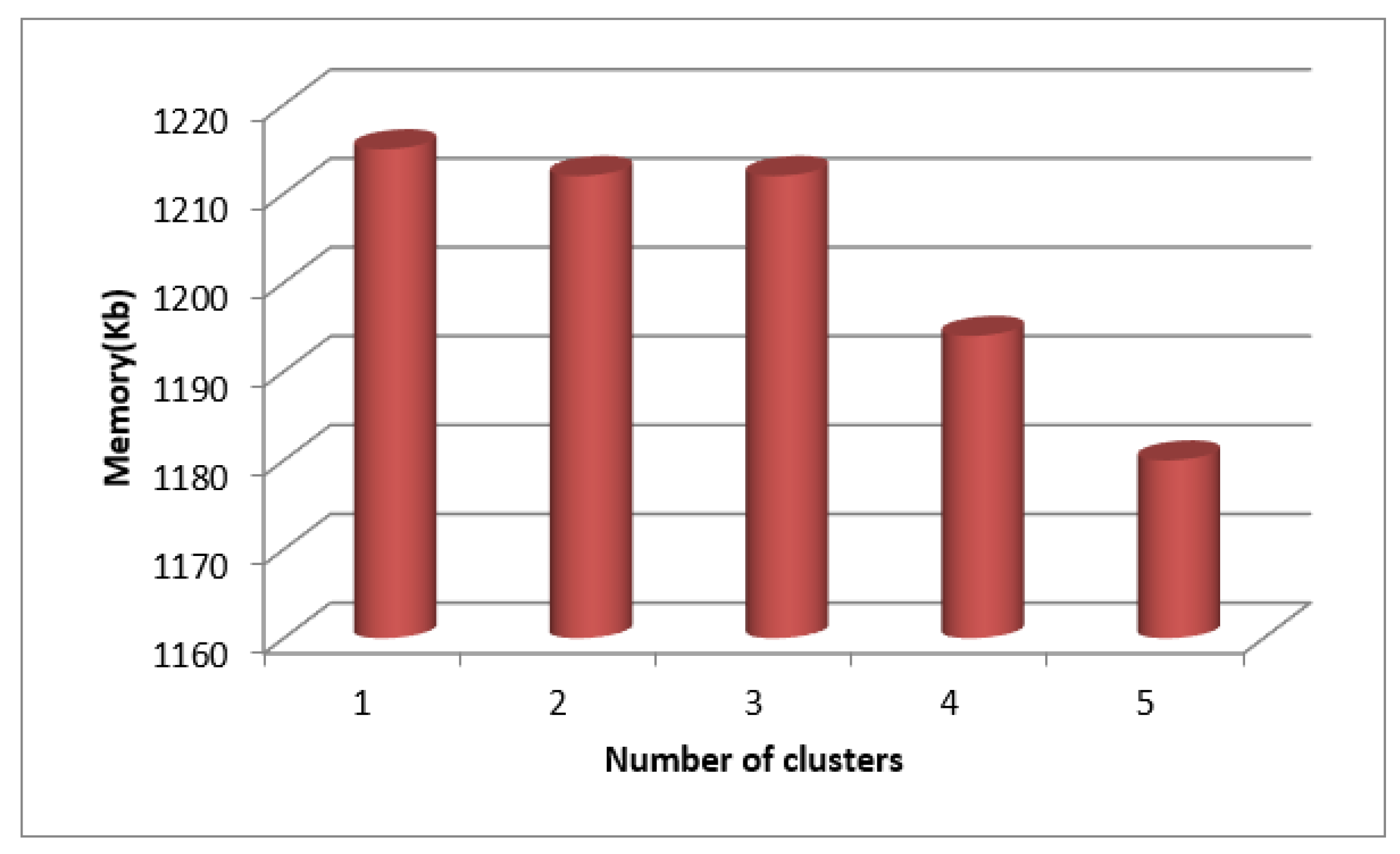
4.2. Memory Usage
4.3. Output measures
4.4. Performance Comparison
| Performance metrics | Proposed versus previous approaches | ||
|---|---|---|---|
| Sanitization method | SecPri-BGMPOP | ||
| Information loss | 0.07% | 0.024% | |
| Throughput | 3.5Mbps | 7Mbps | |
| 3.625Mbps | 7.16Mbps | ||
| Encryption time | 0.11s | 0.0086s | |
| Decryption time | 0.054s | 0.315s | |
| Efficiency | 46.87s | 58.130s | |
| HFHBLO | PSO | GWO | Attack |
|---|---|---|---|
| Better than | 0.26% | 0.23% | CCA |
| Superior to | 0.40% | 0.29% | CPA |
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Lv, Z.; Qiao, L. Analysis of healthcare big data. Future Gener. Comput. Syst. 2020, 109, 103-110. [CrossRef]
- Yang, Yang, Xianghan Zheng, Wenzhong Guo, Ximeng Liu, and Victor Chang. "Privacy-preserving smart IoT-based healthcare big data storage and self-adaptive access control system." Information Sciences 479 (2019): 567-592.
- Hathaliya, J.J.; Tanwar, S. An exhaustive survey on security and privacy issues in Healthcare 4.0. Comput. Commun. 2020, 153, 311-335. [CrossRef]
- Chang, Victor, Yen-Hung Kuo, and Muthu Ramachandran. "Cloud computing adoption framework: A security framework for business clouds." Future Generation Computer Systems 57 (2016): 24-41. [CrossRef]
- Premkamal, P.K.; Pasupuleti, S.K.; Alphonse, P. J. A. A new verifiable outsourced ciphertext-policy attribute based encryption for big data privacy and access control in cloud. J. Ambient Intell. Humaniz. Comput. 2019, 10, 2693-2707. [CrossRef]
- CHELLADURAI, M.U.; Pandian, S.; Ramasamy, K. A blockchain based patient centric electronic health record storage and integrity management for e-Health systems. Health Policy Technol. 2021, 10, 100513. [CrossRef]
- Ogu, E.C. Cybersecurity for eHealth: A simplified guide to practical cybersecurity for non-technical healthcare stakeholders & practitioners. Routledge, 2022.
- Razzaq, A. Blockchain-based secure data transmission for internet of underwater things. Clust. Comput. 2022, 1-20. [CrossRef]
- Liu, J.; Liu, Z.; Sun, C.; Zhuang, J. A data transmission approach based on ant colony optimization and threshold proxy re-encryption in wsns. J. Artifi. Intell. Technol. 2022, 2, 23-31.
- Wang, T.; Ke, H.; Zheng, X.; Wang, K.; Sangaiah, A.K.; Liu, A. Big data cleaning based on mobile edge computing in industrial sensor-cloud. IEEE Trans. Industr. Inform. 2019, 16, 1321-1329. [CrossRef]
- Hosseinioun, P.; Kheirabadi, M.; Tabbakh, S.R.K.; Ghaemi. R. A new energy-aware tasks scheduling approach in fog computing using hybrid meta-heuristic algorithm. J. Parallel Distrib. Comput. 2020, 143, 88-96. [CrossRef]
- Shukla, D.K.; Ali, S.; Trivedi, M.C. Energy Aware Scheduling of Tasks in Cloud environment. Turk. Online J. Qual. Inq. 2021, 12.
- Papageorgiou, P. A Novel Framework for Maritime Security Assessments and Its Applications on the Shipping Industry. Cyber Security Examples. PhD diss., Liverpool John Moores University (United Kingdom), 2022.
- Miyachi, K.; Mackey, T.K. hOCBS: A privacy-preserving blockchain framework for healthcare data leveraging an on-chain and off-chain system design. Inf. Process. Manag. 2021, 58, 102535. [CrossRef]
- Pramanik, P.K.D.; Pal, S.; Mukhopadhyay, M. Healthcare big data: A comprehensive overview. Research anthology on big data analytics, architectures, and applications, 2022, 119-147.
- Riaz, S.; Khan, A.H.; Muhammad Haroon, Sadia Latif, and Sana Bhatti. "Big data security and privacy: Current challenges and future research perspective in cloud environment. In 2020 International Conference on Information Management and Technology (ICIMTech), 2020, pp. 977-982.
- Sauber, A.M.; El-Kafrawy, P.M.; Shawish, A.F.; Amin, M.A.; Hagag, I.M. A New Secure Model for Data Protection over Cloud Computing. Comput. Intell. Neurosci. 2021, 1-11. [CrossRef]
- Samaraweera, G.D.; Chang, J.M. Security and privacy implications on database systems in Big Data era: A survey. IEEE Trans. Knowl. Data Eng. 2019, 33, 239-258. [CrossRef]
- Amanullah, M.A.; Habeeb, R.A.A..; Nasaruddin, F.H.; Gani, A.; Ahmed, E.; Nainar, A.S.M.; Akim, NM.; Imran, M. Deep learning and big data technologies for IoT security. Comput. Commun. 2020, 151, 495-517. [CrossRef]
- Rai, M.; Mandoria, H. A study on cyber crimes cyber criminals and major security breaches. Int. Res. J. Eng. Technol. 2019, 6, 1-8.
- Lv, Z., Wang, L., Guan, Z., Wu, J., Du, X., Zhao, H., Guizani, M. An optimizing and differentially private clustering algorithm for mixed data in SDN-based smart grid. IEEE access, 2019, 7, 45773-45782. [CrossRef]
- Shanmugapriya, E., Kavitha, R. Medical big data analysis: preserving security and privacy with hybrid cloud technology. Soft Comput. 2019, 23, 2585-2596. [CrossRef]
- Tian, Y., Wang, Z., Xiong, J., Ma, J. A blockchain-based secure key management scheme with trustworthiness in DWSNs. IEEE Transactions Indus. Inform. 2020, 16, 6193-6202. [CrossRef]
- Chen, J., Ramanathan, L., Alazab, M. Holistic big data integrated artificial intelligent modeling to improve privacy and security in data management of smart cities. Microprocess. Microsyst. 2021, 81, 103722. [CrossRef]
- Iqbal, S.; Kiah, M.L.M.; Zaidan, A.A.; Zaidan, B.B.; Albahri, O.S.; Albahri, A.S.; Alsalem, M. A. Real-time-based E-health systems: Design and implementation of a lightweight key management protocol for securing sensitive information of patients. Health Technol. 2019, 9, 93-111. [CrossRef]
- Elhoseny, M.; Haseeb, K.; Shah, A.A.; Ahmad, I.; Jan, Z.; Alghamdi, M.I. IoT solution for AI-enabled PRIVACY-PREServing with big data transferring: an application for healthcare using blockchain. Energies 2021. 14, 5364. [CrossRef]
- Ramachandra, M.N.; Rao, M.S.; Lai, W.C.; Parameshachari, B.D.; Babu, J.A.; Hemalatha, K.L. An Efficient and Secure Big Data Storage in Cloud Environment by Using Triple Data Encryption Standard. Big Data Cogn. Comput. 2022, 6, 101. [CrossRef]
- Gehlot, A.; Misra, N. Privacy and Security Enabling for Healthcare Data using Lightweight Deep learning with Cryptography. In 2022 IEEE 2nd Mysore Sub Section International Conference (MysuruCon), 2022, pp. 1-6.
- Mehbodniya, A.; Neware, R.; Vyas, S.; Kumar, M.R.; Ngulube, P.; Ray, S. Blockchain and IPFS integrated framework in bilevel fog-cloud network for security and privacy of IoMT devices. Comput. Math. Methods Med. 2021. [CrossRef]
- Refaee, E.; Parveen, S.; Begum, K.M.J.; Parveen, F.; Raja, M.C.; Gupta, S.K.; Krishnan, S. Secure and scalable healthcare data transmission in IoT based on optimized routing protocols for mobile computing applications. Wirel. Commun. Mob. Comput. 2022. [CrossRef]
- Senel, F.A.; Gökçe, F.; Yüksel, A.S.; Yi ˘ git, T. A novel hybrid PSO–GWO algorithm for optimization problems. Eng. Comput. 2018, 1359–1373.
- Zolghadr-Asli, B.; Bozorg-Haddad, O.; Chu, X. Crow Search Algorithm (CSA). In Advanced Optimization by Nature-Inspired Algorithms. Studies in Computational Intelligence; Bozorg-Haddad, O., Ed.; Springer: Singapore, 2018; Volume 720.
- Alphonsa, M.M.A.; Amudhavalli, P. Genetically modified glowworm swarm optimization based privacy preservation in cloud computing for healthcare sector. Evol. Intell. 2018, 11, 101–116. [CrossRef]
- Kavitha C; Anita X. Task failure resilience technique for improving the performance of MapReduce in Hadoop. Etri Journal 2020, 42, 748 -760. [CrossRef]
- C. Kavitha; S. R. Srividhya; Wen-Cheng Lai; Vinodhini Mani. IMapC: Inner MAPping Combiner to Enhance the Performance of MapReduce in Hadoop. Electronics 2022, 11, 1599 . [CrossRef]
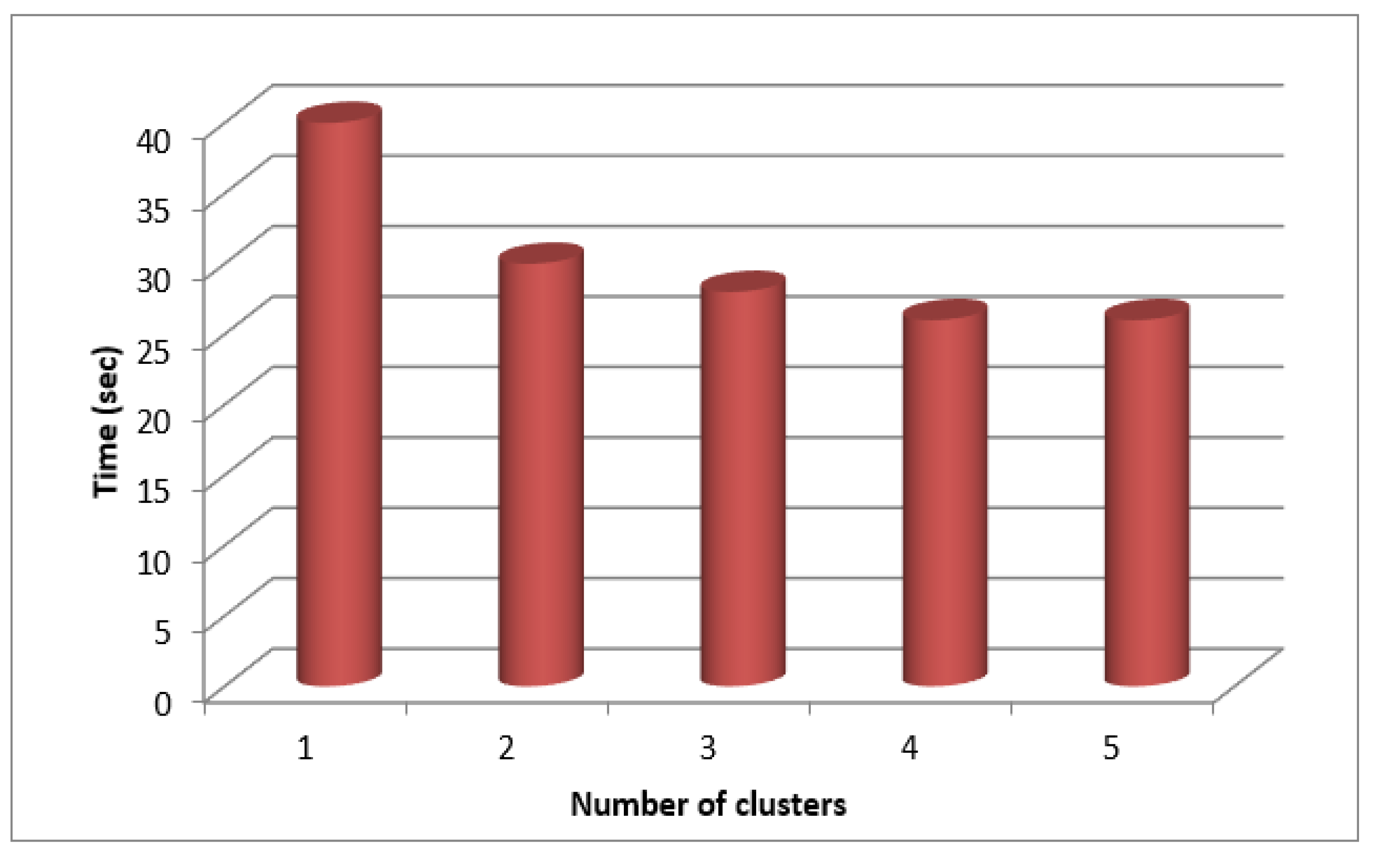
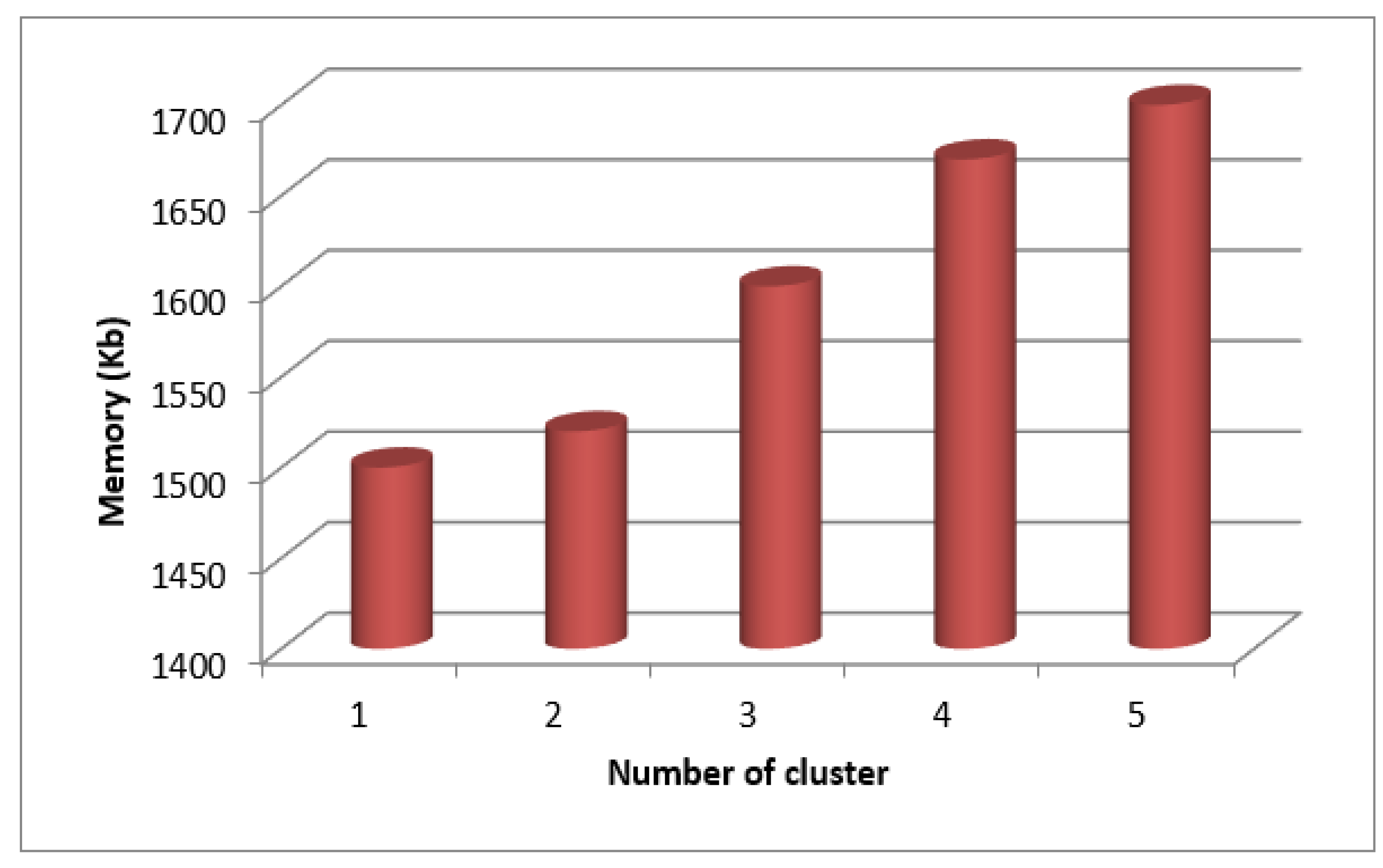
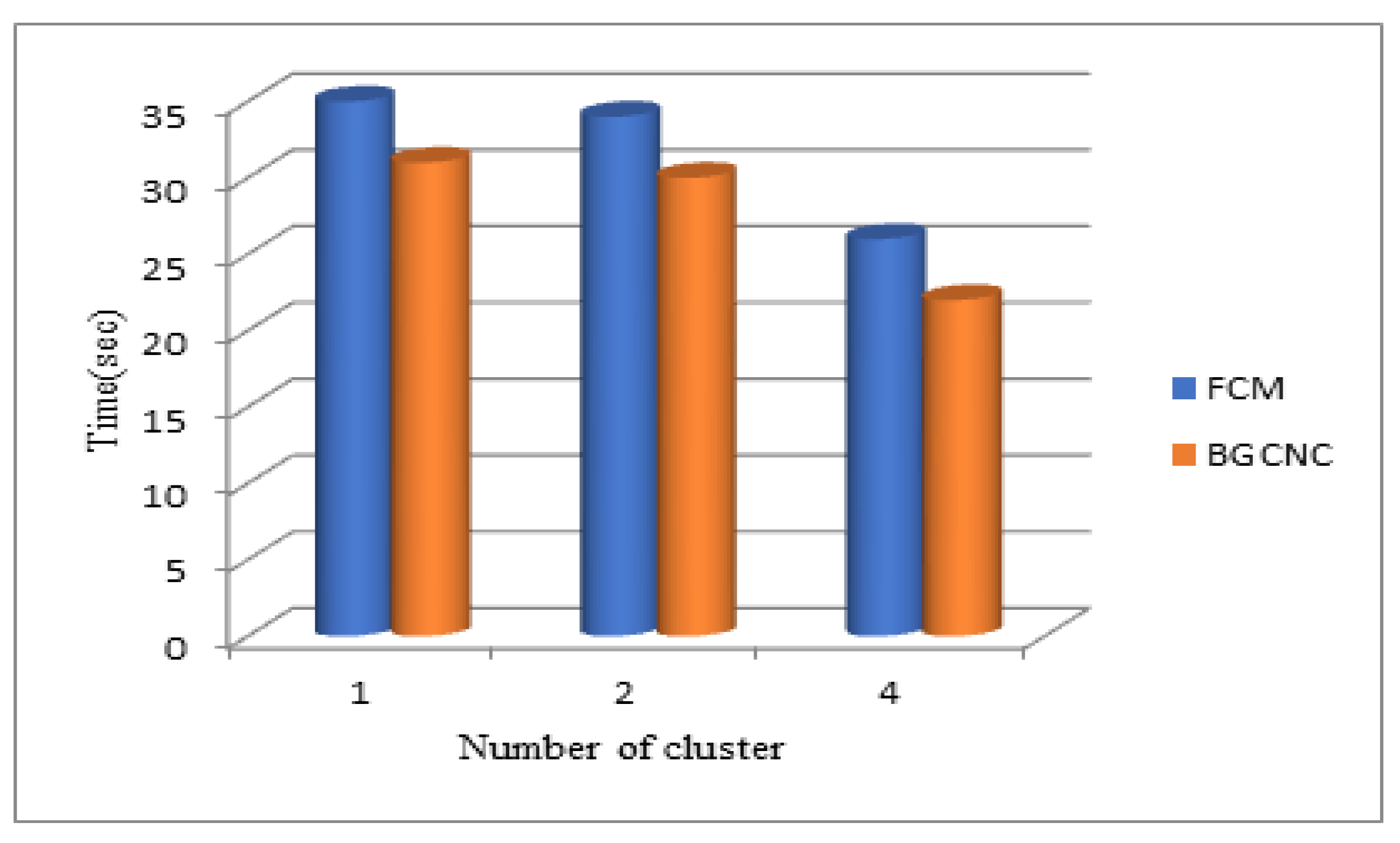
| Number of clusters | Time(sec) | Memory(KB) |
|---|---|---|
| 1 | 31.569 | 1520 |
| 2 | 30.638 | 1613 |
| 4 | 30.456 | 1663 |
| Number of clusters | Time(sec) | Memory(KB) |
|---|---|---|
| 1 | 29.55 | 1325 |
| 2 | 27.55 | 1265 |
| 4 | 26.45 | 1232 |
| Number of clusters | Time(sec) | Memory(KB) |
|---|---|---|
| 1 | 22.37 | 1216 |
| 2 | 24.45 | 1216 |
| 4 | 25.64 | 1199 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




