Submitted:
21 March 2024
Posted:
26 March 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Mutual exclusion: when a process accesses a resource, it is granted exclusive use of that resource in a non-sharable mode.
- Hold and wait: a process is holding at least one resource and is waiting for one or more additional resources that are currently being held by other processes.
- No preemption: a process cannot preempt or take away the resources held by another process.
- Circular wait: there exists a set [P0, P1, P2, …, P n] of waiting processes such that P0 is waiting for a resource which is held by P1, P1 is waiting for a resource which is held by P2, …, Pn-1 is waiting for a resource which is held by Pn, and Pn is waiting for a resource which is held by P0.
2. Related Work
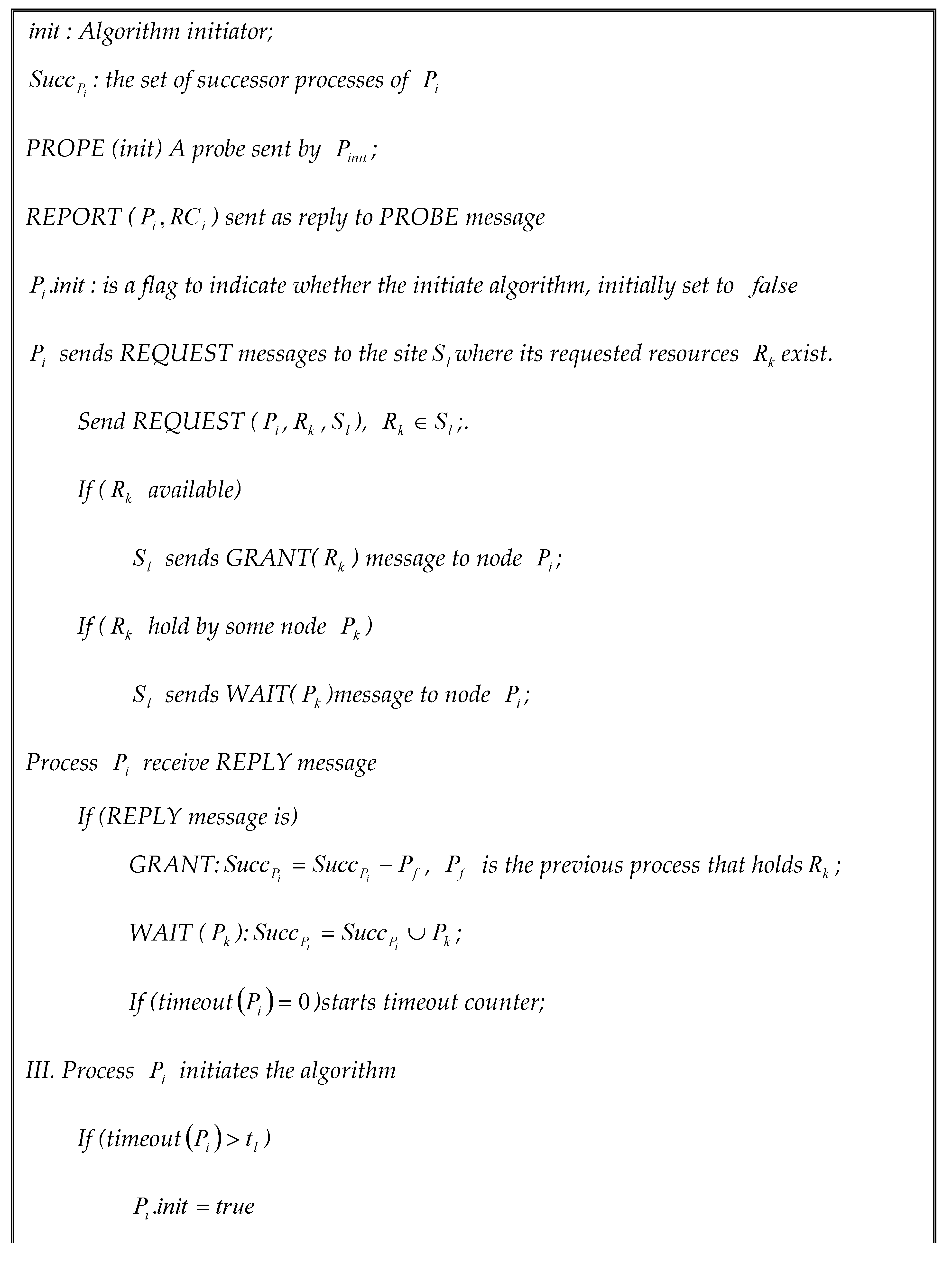
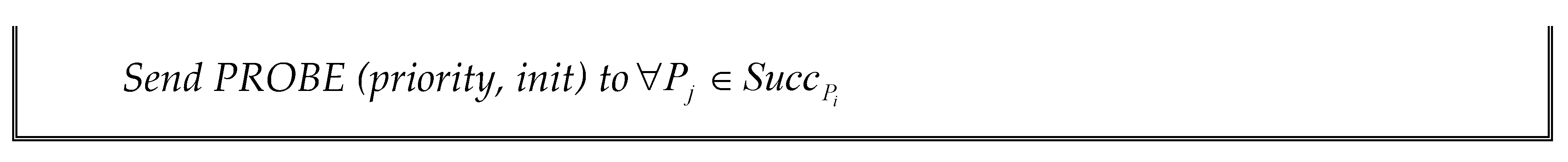
3. Proposed Deadlock Detection Algorithm
3.1. The Idea behind the Proposed Deadlock Detection Algorithm
- Local and global deadlock detection: local deadlocks have their effect on global transaction management; this approach combines both local and global deadlock detection. Also, it can detect several deadlock cycles per single instance execution.
- Latency: all deadlocks either local or global are detected within a short time.
- Simplicity: building a WFG to detect global deadlocks within two global transactions in two different sites is simpler than building a complete WFG and more suitable for distributed implementation, which will reduce the total number of exchanged messages used to detect global deadlocks. Also, using a global timeout to detect other existing global deadlocks of length more than two chooses the threshold value of global timeoutis a less critical problem.
3.2. Proposed Algorithm Implementation
3.3. Global Process Manager Action
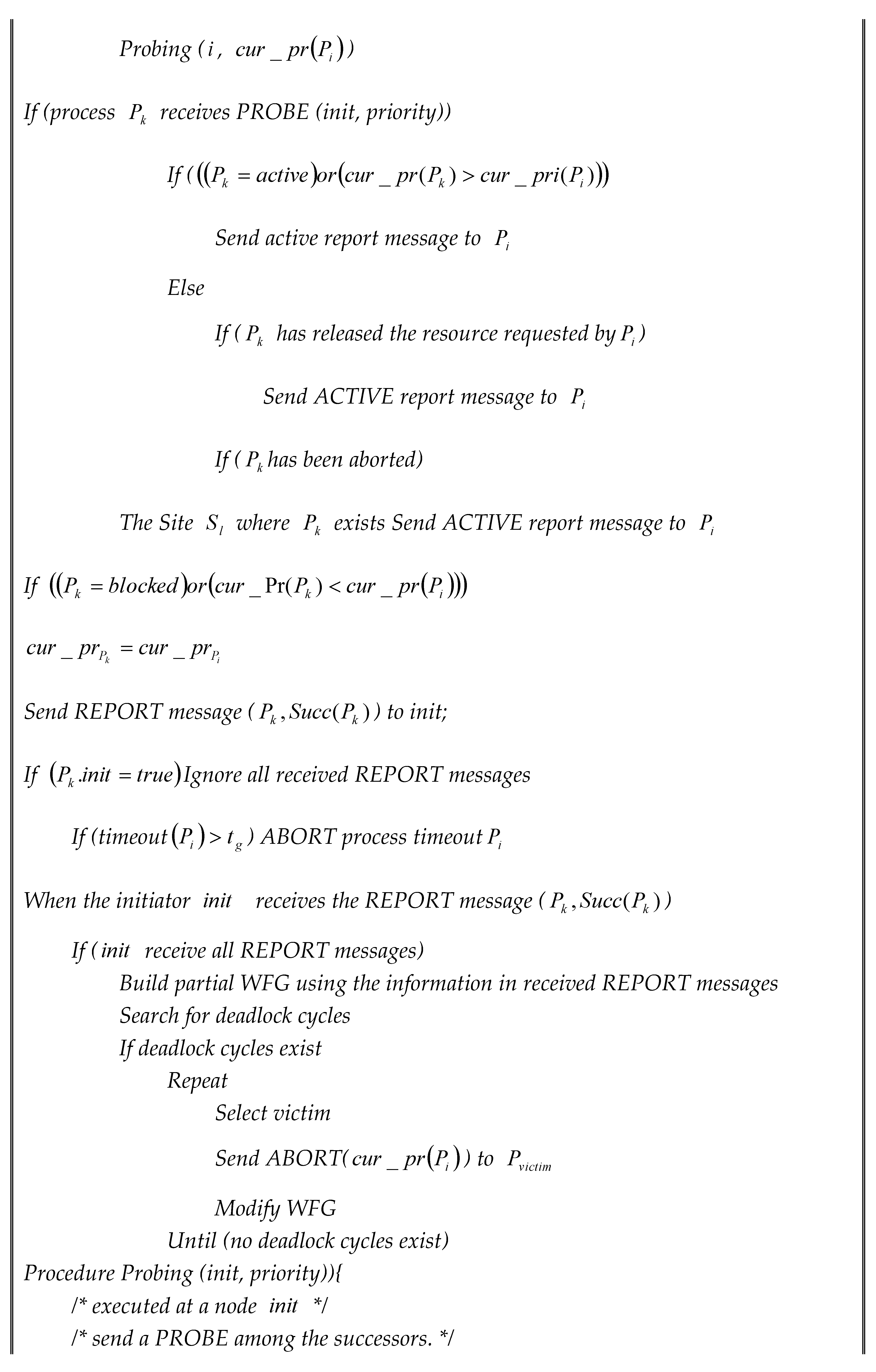
3.4. Detection Deadlock Cycles of Length Two
- Ignoring any abort messages that could be received from low-priority initiators. Process judge on the priority of abort message according to the priority of probed messages it received from other initiators by holding a variable this variable is updated only if the process receives a probe message from an initiator with higher priority than what it is stored invariable.
- Priority distribution is based on two things, time of initiation and process identifier. The old process has a higher priority than recent ones.
- Responding to the probed messages from low-priority initiators always implies that the probed process is active because the probed node assumes that the high initiator will resolve the deadlock cycle the probed process is involved in.
- Initiators with low priority will terminate the execution of their initiated algorithms upon receiving a probe message from high high-priority initiator. Terminating algorithm execution is done by ignoring all report messages that will be received from their successors.
- The initiation phase ends with receiving all report messages from initiator successors.
- Any process that receives a probe message must send a report message as a reply to it, the content of this report message depends on process status, initiator priority, and process priority.
- In case of sending a probe message to a process that is selected as a victim and killed by some other initiator. Then it’s the responsibility of the global process manager of that process to send the abort message indicating to the initiator that this process has been aborted before.
4. Discussion
- The process requests its resources in parallel, by submitting each request to the corresponding site.
- Each lock is a write lock. For the simplicity of the simulated model, no replication for resources is assumed.
- A transmission time is needed to send a request message to the other site, and a processing time for processing the acquired item. The transmission time is dependent on network topology. For fully connected network will be equal for all messages.
- The local processes have similar structures, but request resources from their sites, and spend all processing time on their sites. For simplicity, we assume that the requesting and acquiring time for local resources is negligible.
- If the requested resource is granted by some other process, then the requested site sends a wait-reply message to the requestor indicating the identifier of the process that holds the requested resource, the needed time for the wait-reply message is and the process identifier is added to the requestor successor set.
- A requestor that cannot grant all requested resources will initiate a deadlock detection algorithm after some timeout value.
- Initiation deadlock algorithm implies sending probe messages for all requestor’s successors. Each successor sends back a report message to the initiator. Report message carries process status and its successor set if it exists.
- After receiving all report messages, the initiator starts executing the deadlock algorithm to detect deadlock cycles by constructing a partial WFG based on the received information. Detecting cycles exhibits time units.
- If either a local or global deadlock is detected, one of the deadlocked processes is aborted and all locked resources by that process are released, and the aborted process is restarted after a time . If the waiting time for any process exceeds the global timeout value then this process is assumed deadlocked and it aborts itself.
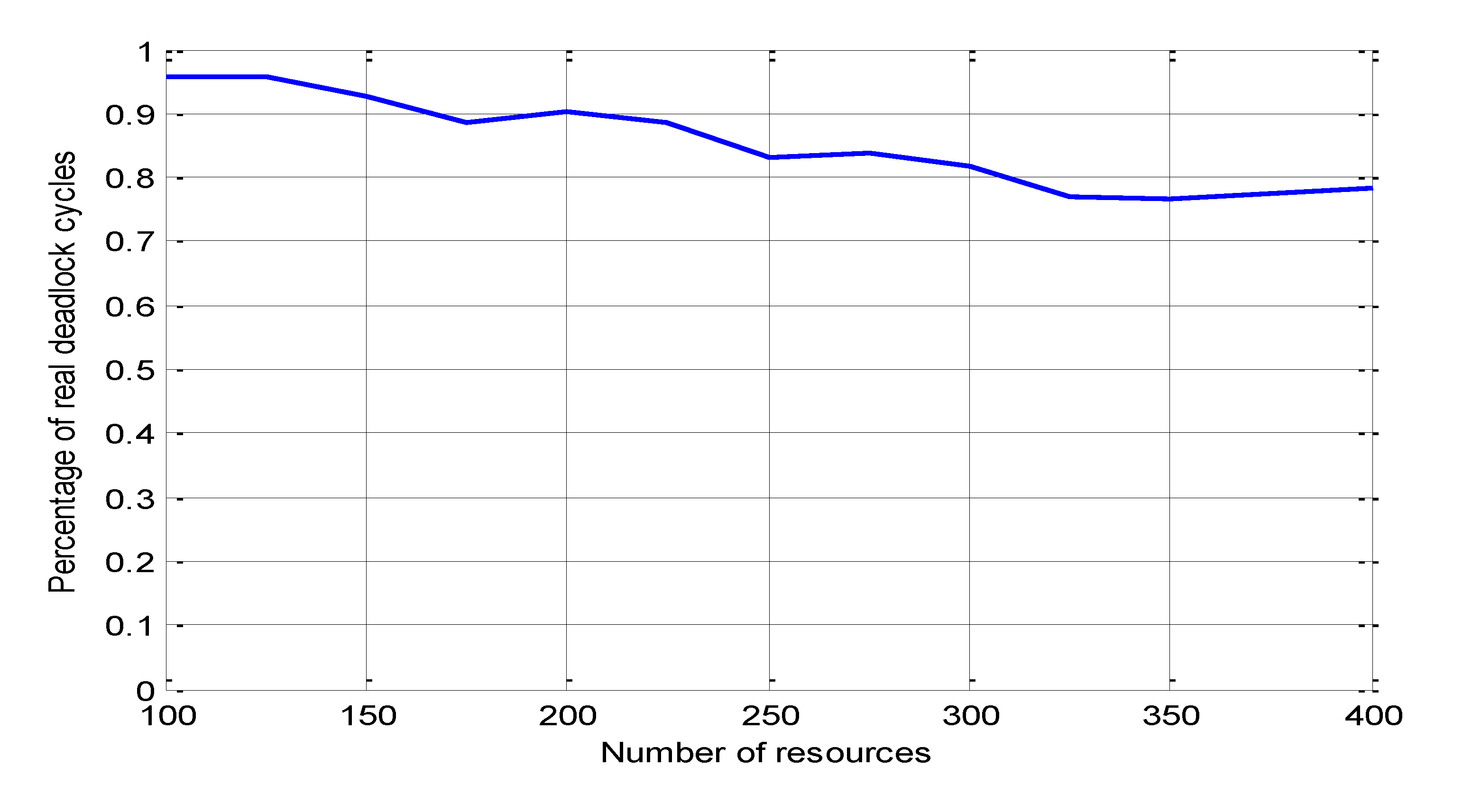
5. Performance Evaluation Metrics
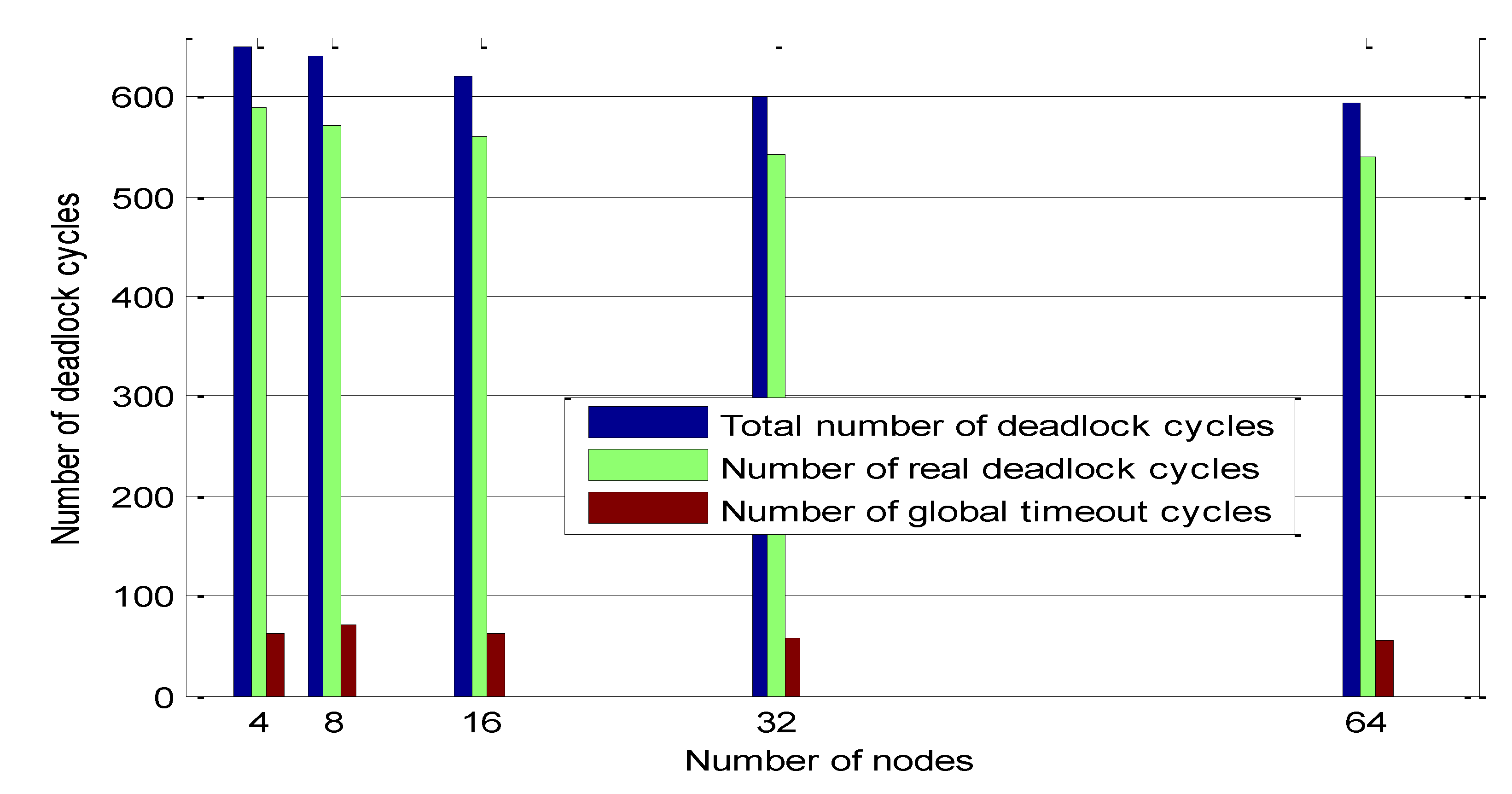
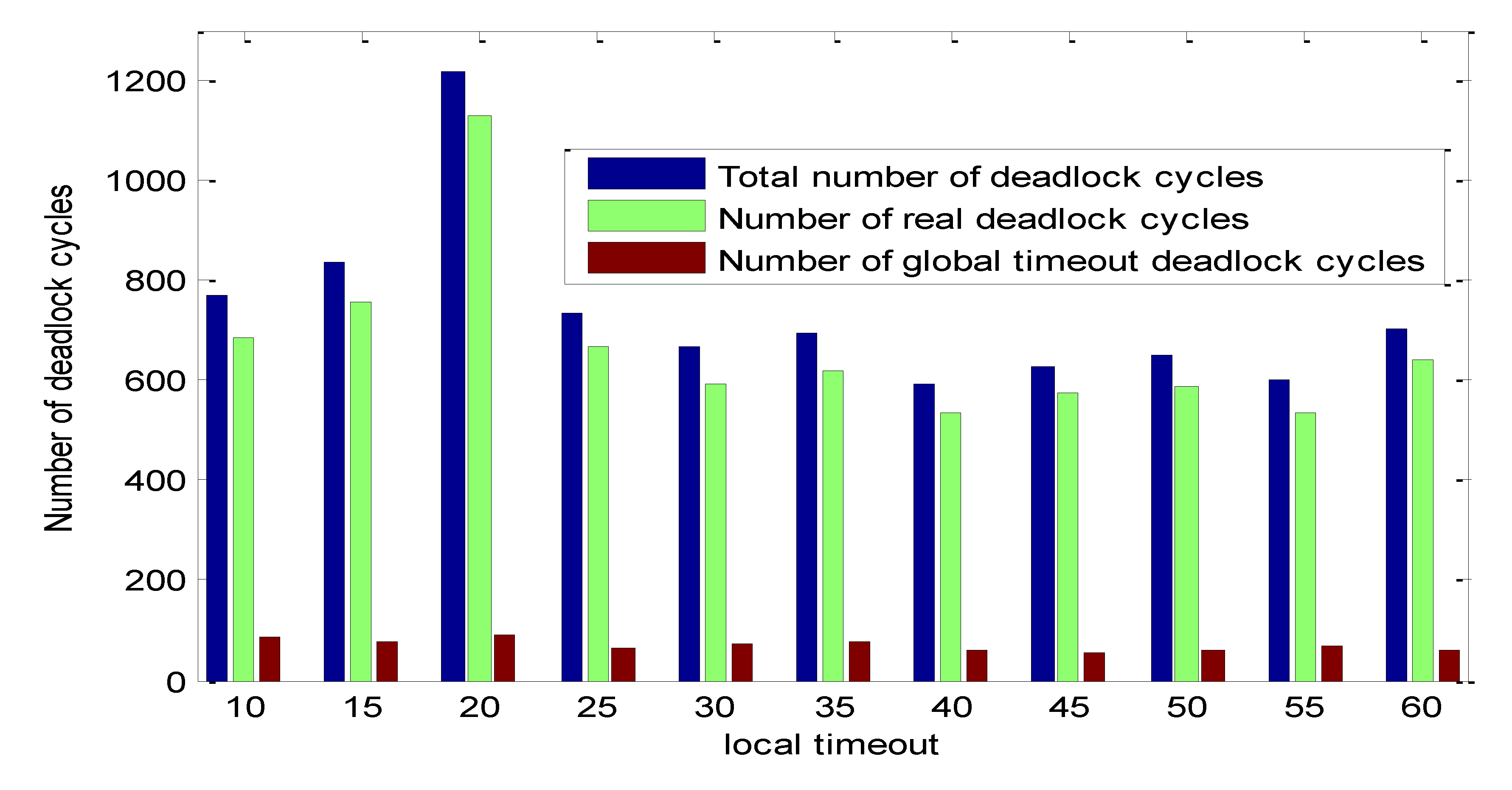
- Percentage of the real and global timeout deadlock cycles detected by the proposed algorithm to the total number of deadlock cycles
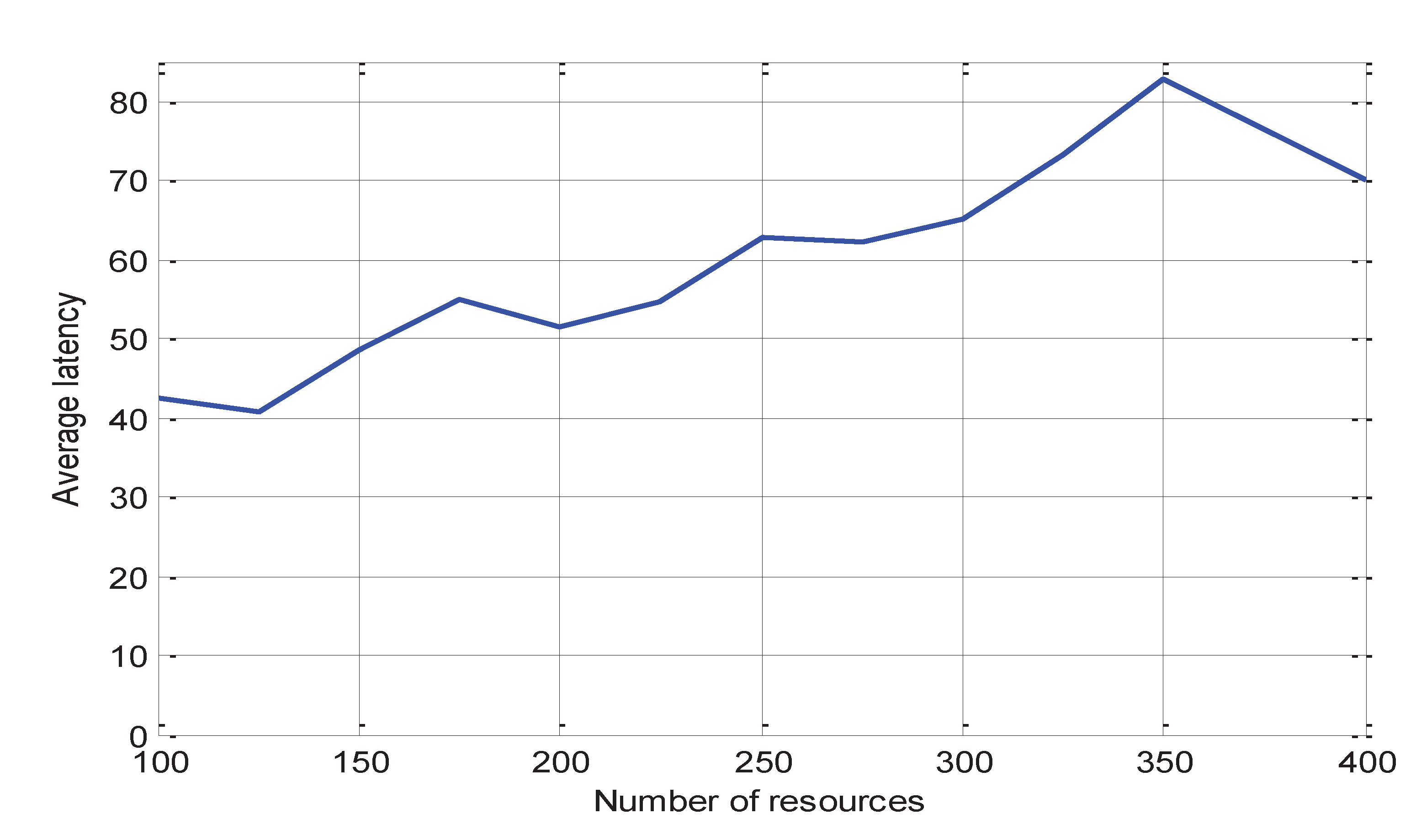
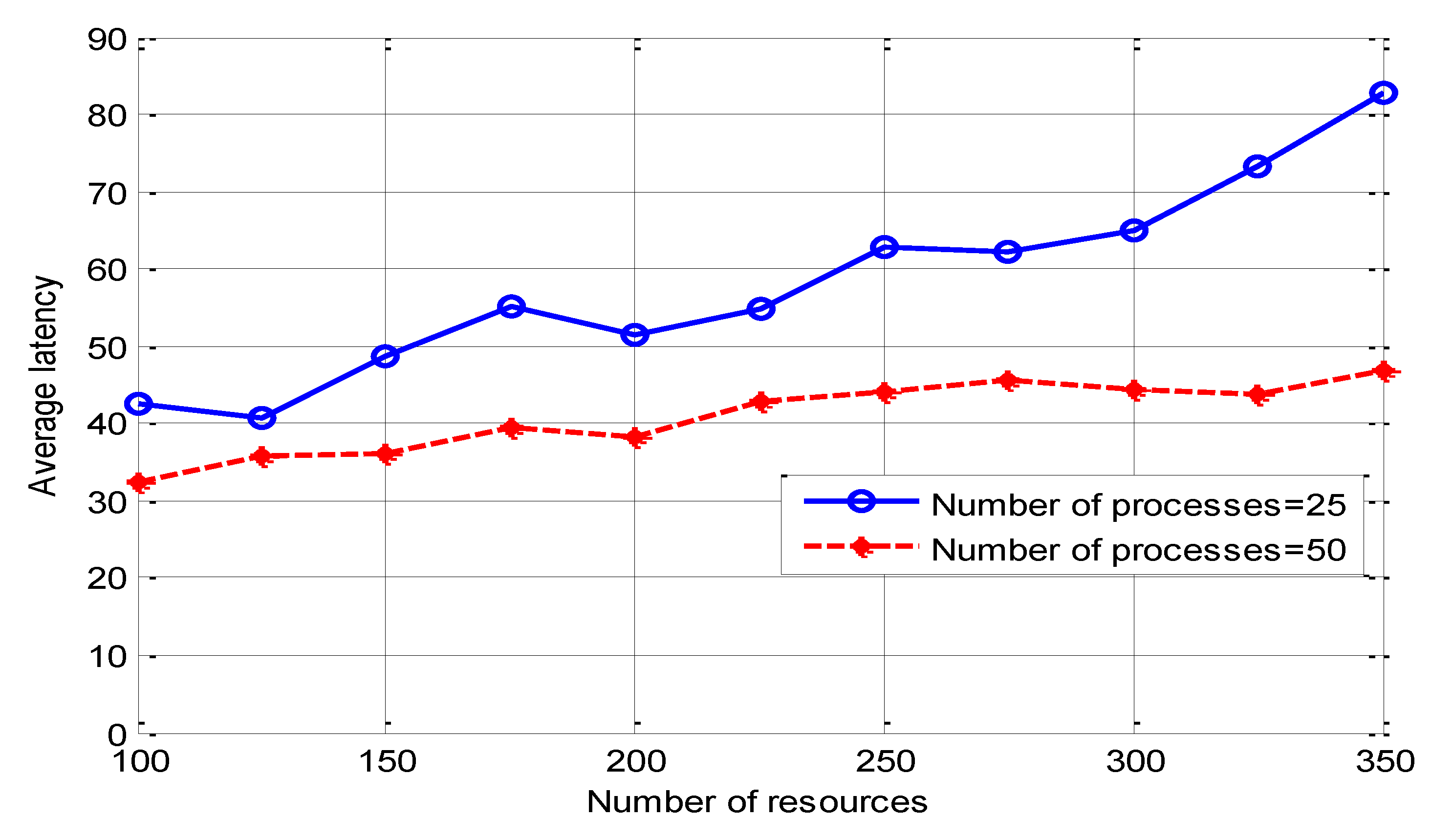
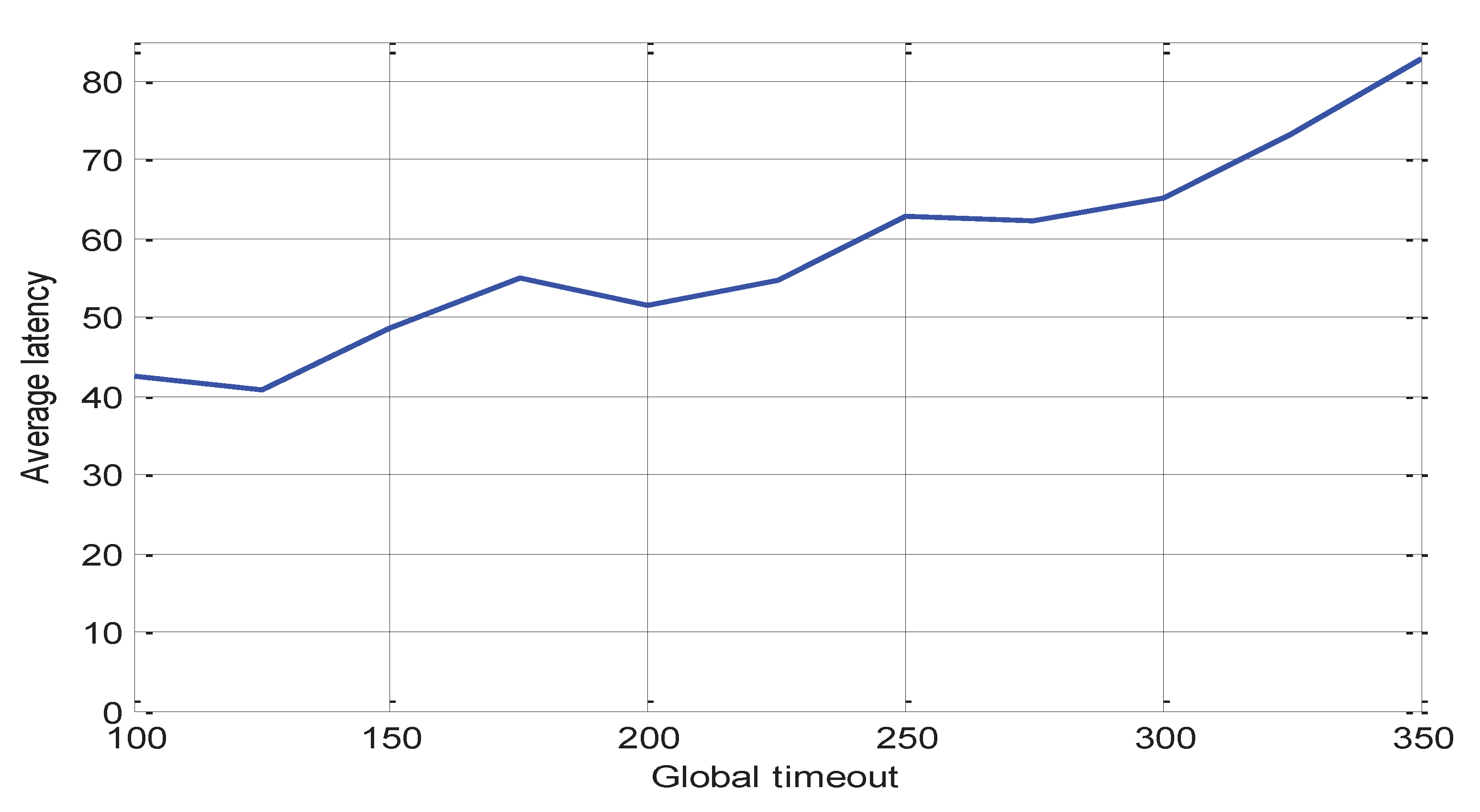
- Average deadlock latency; where deadlock latency is considered as the elapsed time from the instance of initiating the algorithm till the time of aborting the deadlocked process involved in the deadlock cycle. In the case of global time-out deadlocks, time latency is considered as the global timeout threshold value .
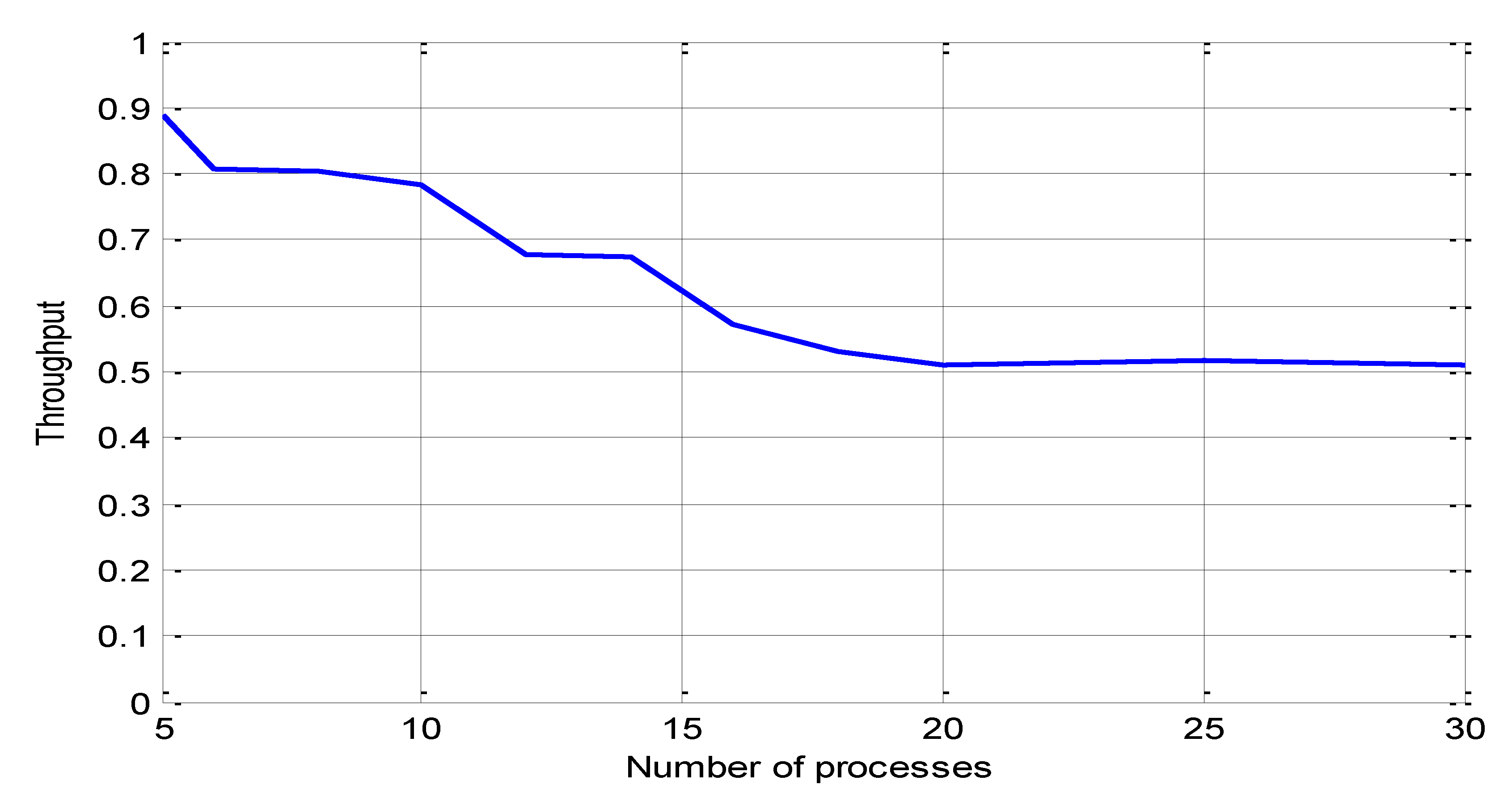
- Throughput is the expected number of committed transactions to the total number of transactions submitted to the system.
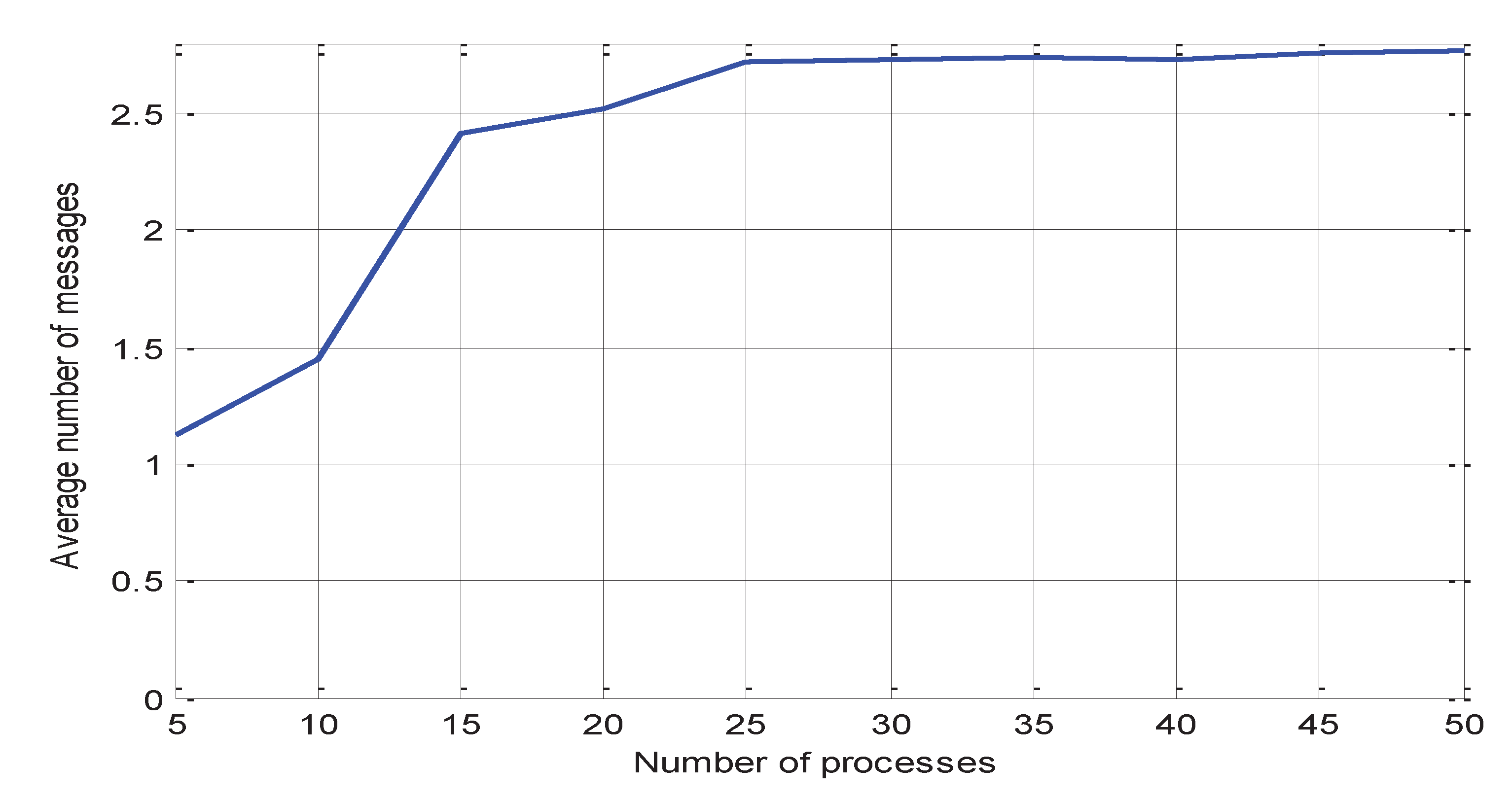
- Average number of deadlock detection messages
5.1. Algorithm Correctness
5.2. Throughput
5.3. Average Latency
5.4. Average Number of Deadlock Detection Messages
6. Conclusions and Future Work
Acknowledgments
Conflicts of Interest
References
- Soojung Lee, “Fast, Centralized Detection and Resolution of Distributed Deadlocks in the Generalized Model.”, “IEEE Trans on Software Engineering”, Vol. 30, no. 9, pp. 561-573. September 2004.
- Roberto Baldoni and Sivlio Salza, “Deadlock Detection in Multidatabase Systems: A Performance Analysis”, “Distributed System Engineering” vol. 4, pp. 244-252, 1997.
- D. Z. Badal, “The distributed deadlock detection algorithm.”, “ACM Trans. Computer Systems”, Vol. no. 4, pp. 320–337, November 1986.
- Gray, J., Homan, P., Obermarck, R., Korth, H.: A Straw Man Analysis of Probability of Waiting and Deadlock. IBM Research Report RJ 3066, San Jose, 1981.
- Jinho Ahn, “Adaptive Sender-based Message Logging and Checkpointing Protocol for Large-Scale Distributed Systems” January 2022, Journal of Korean Institute of Information Technology 20(1):41-48. [CrossRef]
- Houssem Mansouri, Al-Sakib Khan Pathan, “A Communication-Induced Checkpointing Algorithm for Consistent-Transaction in Distributed Database Systems”, Security in Computing and Communications (pp.21-32), 2021. [CrossRef]
- Masoomeh Ghodrati, Ali Harounabadi, “Provide a New Mapping for Deadlock Detection and Resolution Modeling of Distributed Database to Colored Petri Net”, June 2014, International Journal of Computer Applications 95(5):1-7. [CrossRef]
- Hisao Kameda, Jie Li, Chonggun Kim, Yongbing Zhang, “Optimal Load Balancing in Distributed Computer Systems, 2012.
- Shigang Chen, Yibei Ling, “Stochastic Analysis of Distributed Deadlock Scheduling.”, PODC’05, July 17-20, 2005 Las Vegas, Nevada, USA.
- M. van Steen and A.S. Tanenbaum, Distributed Systems, 3rd ed., distributed-systems.net, 2020.
- Maarten van Steen, Andrew S. Tanenbaum, “A brief introduction to distributed systems”, 2016, https://d-nb.info/1113645695/34.
- David Ola, “Deadlock Detection and Resolution in Distributed Database System”, 2015.
- Marwan H. Hassan, Saad Darwish, Saleh M. Elkaffas, “An Efficient Deadlock Handling Model Based on Neutrosophic Logic: Case Study on Real-Time Healthcare Database Systems”, January 2022, IEEE Access 10(6):1-1. [CrossRef]
- Wei Lu, Stephen Yong, Liqiang Wang, Weiwei Xing, “A Novel Concurrent Generalized Deadlock Detection Algorithm in Distributed Systems” November 2015. [CrossRef]
| Parameter | Mean Value | Description |
| 30 | Processing time for each acquired resource | |
| 20 | communication time of a message | |
| 1.5 | Time to execute the routine corresponding to a deadlock detection message | |
| 20-60 | Timeout threshold for initiating the algorithm | |
| 100-200 | Global timeout value | |
| 100 | Execution time of a process before making a resource request. | |
| Random | Restart time for the aborted process. | |
| 100-350 | Total number of resources | |
| 4-64 | Total number of nodes | |
| 25-50 | Total number of processes |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




