Submitted:
10 March 2024
Posted:
11 March 2024
You are already at the latest version
Abstract
Keywords:
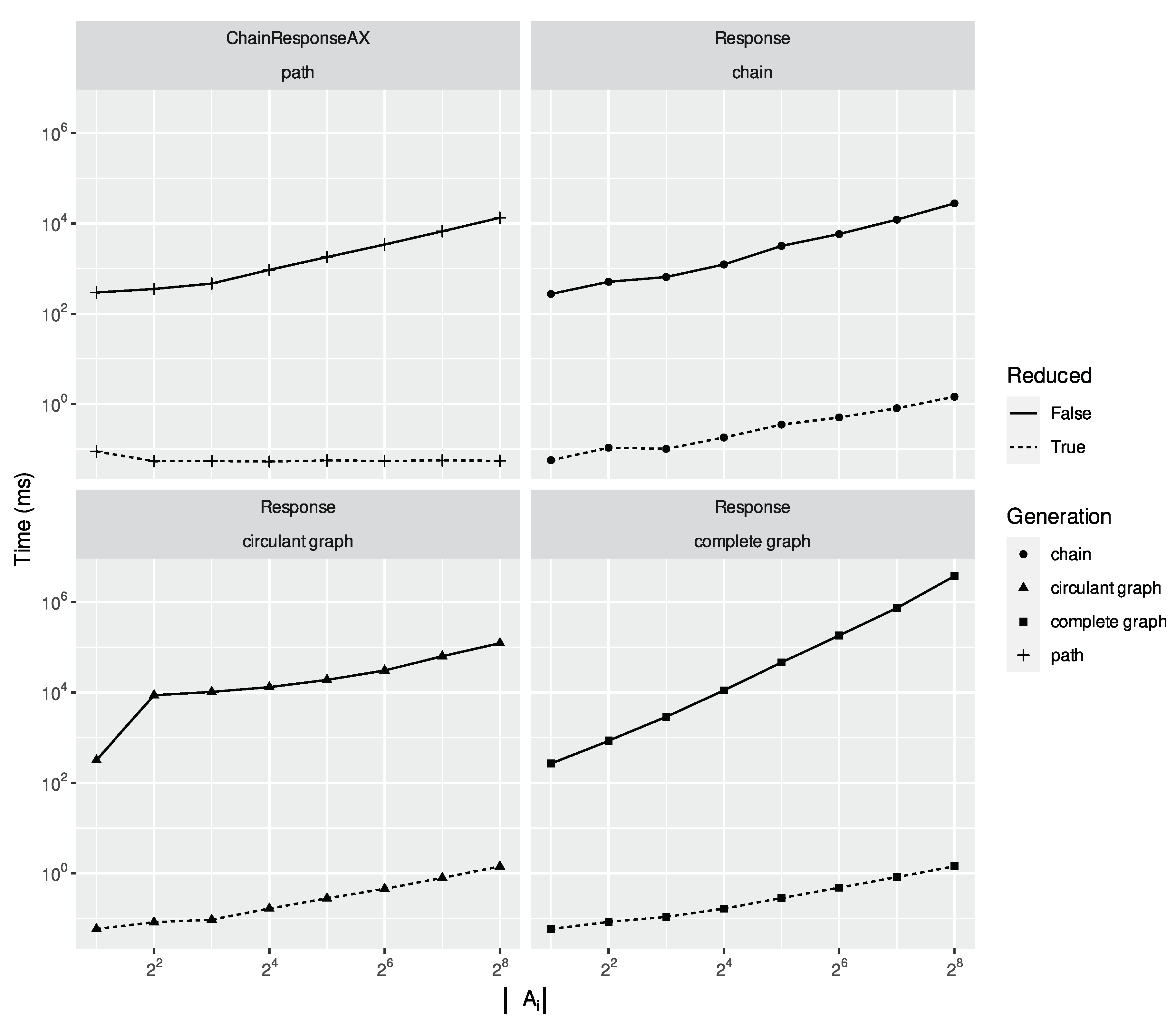
- Under temporal non-simultaneity, the time required for both running a verified temporal artificial intelligence task and computing is also smaller than the running time of running such tasks over (§5.2).
1. Brief Related Work
Formal Synthesis.
Formal Verification.
SAT-Solvers.
LTLf Modulo Theories
2. Preliminaries
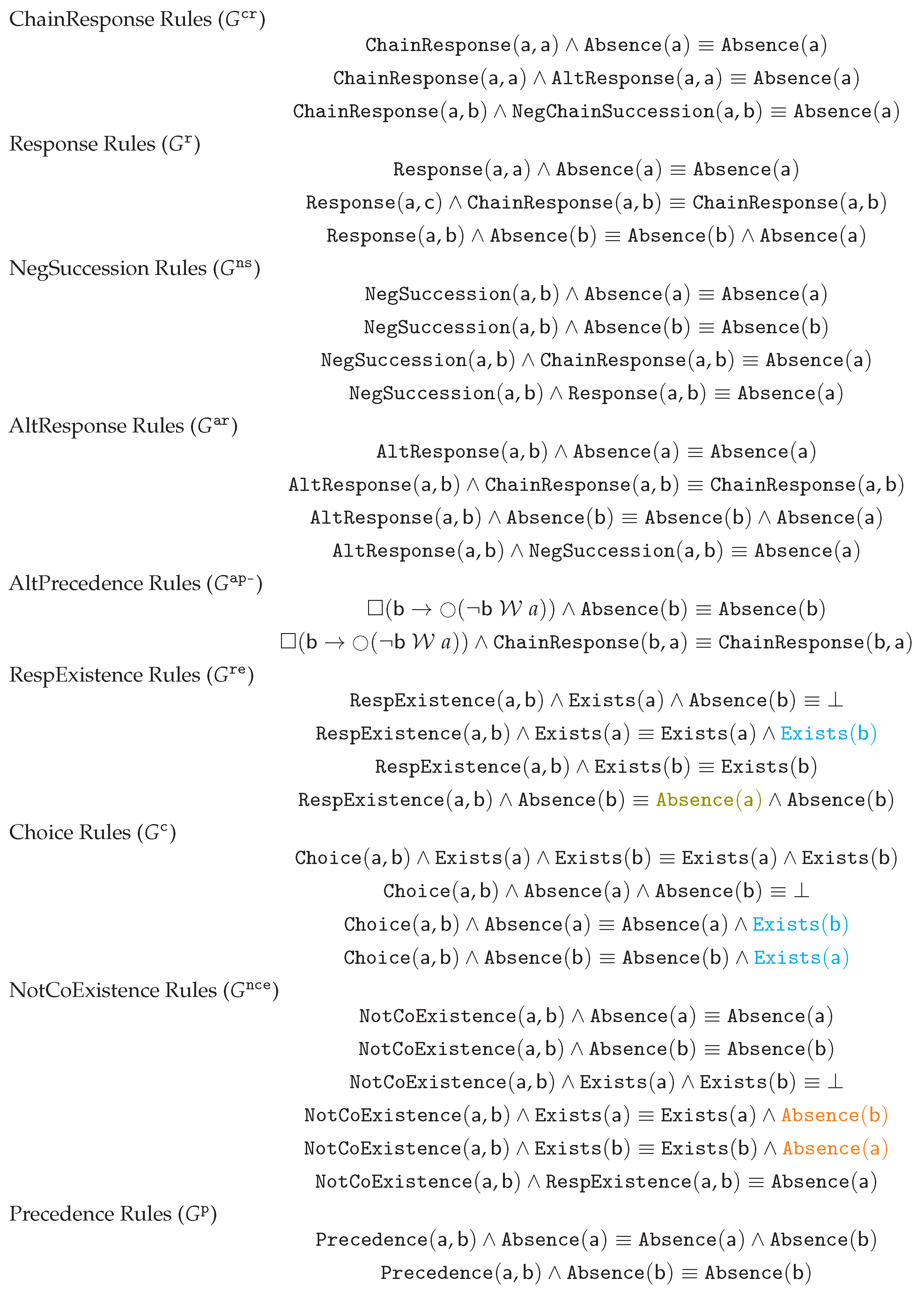
2.1. Rewriting Rules
2.2. Temporal Short-Circuit Rewriting
2.3. Temporal Non-Simultaneity
Rewriting Rules
Temporal Short-Circuit Rewriting
3. Reducer: Equational Rewriting
3.1. Algorithmic Subroutines
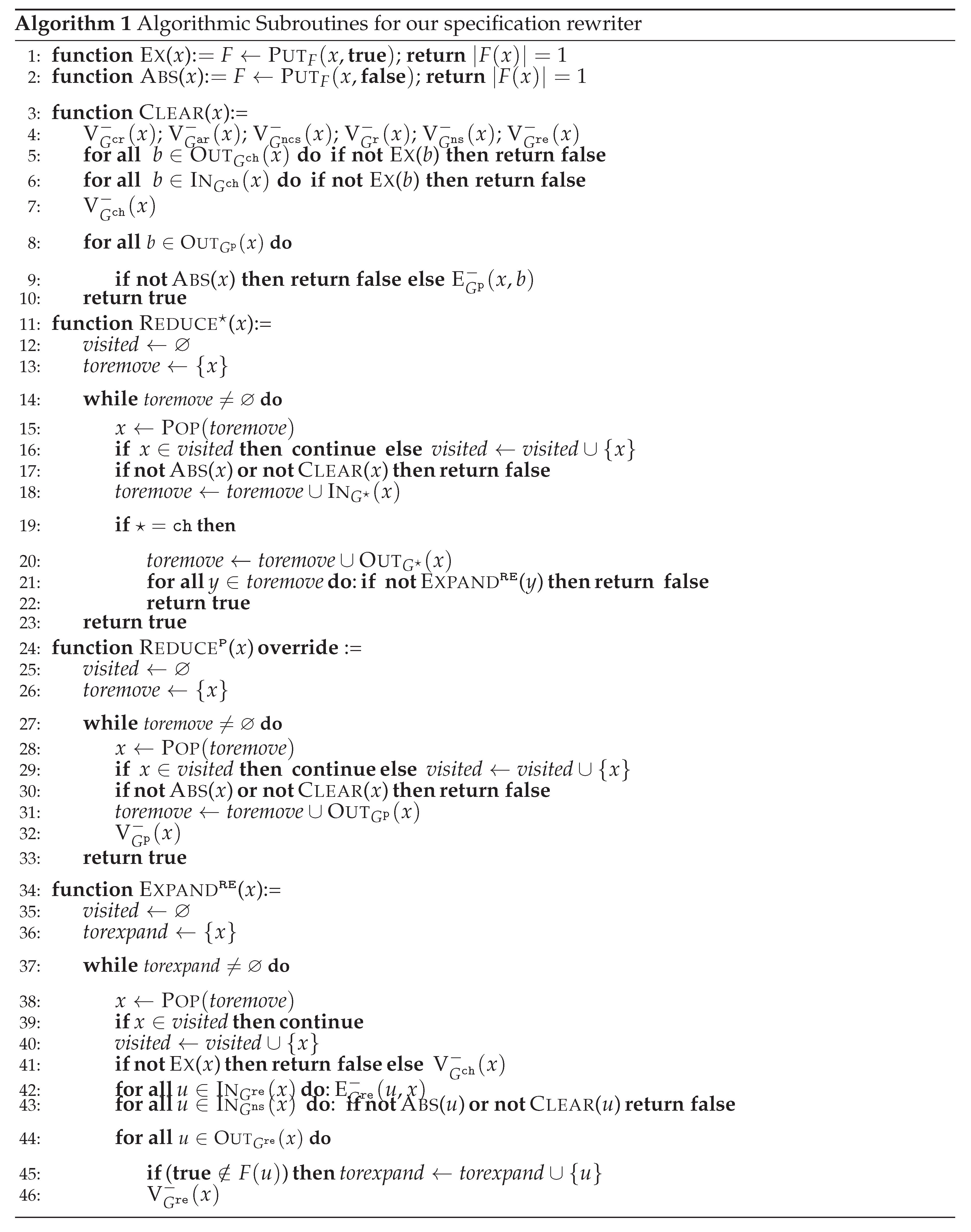
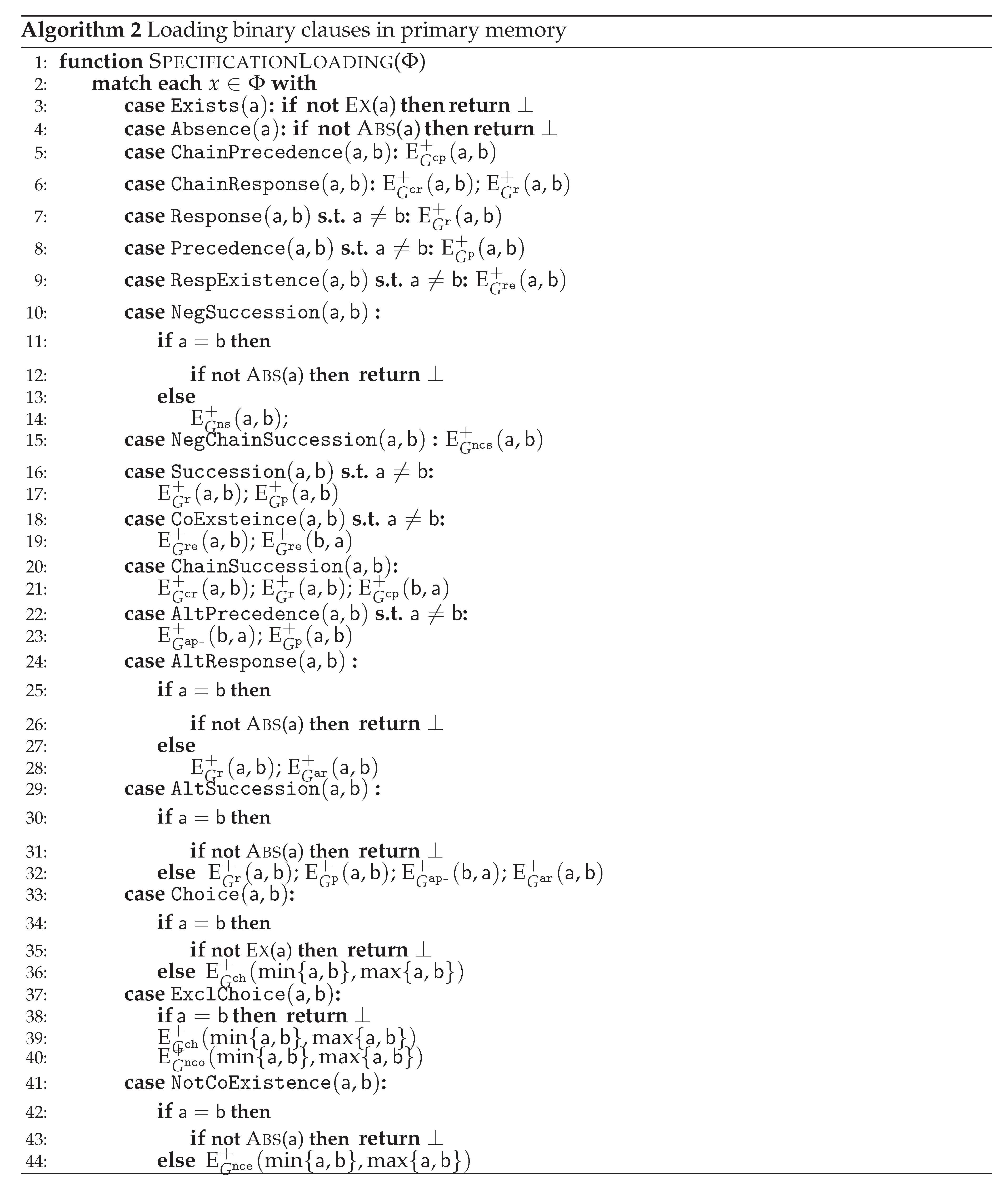
3.2. Specification Loading as Graphs
3.3. Applying Equational Rewriting
3.4. Applying Short-Circuit Rewriting
4. A PolyTime SAT-Solver for DECLAREd
5. Empirical Evaluation
- c=ChainResponse:
- c=Precedence:
- c=Response:
- c=RespExistence+Exists:
-
c=RespExistence+ExclChoice+Exists: ,
-
c=(Chain+Alt)Response: ,
- c=ChainResponseAX: .
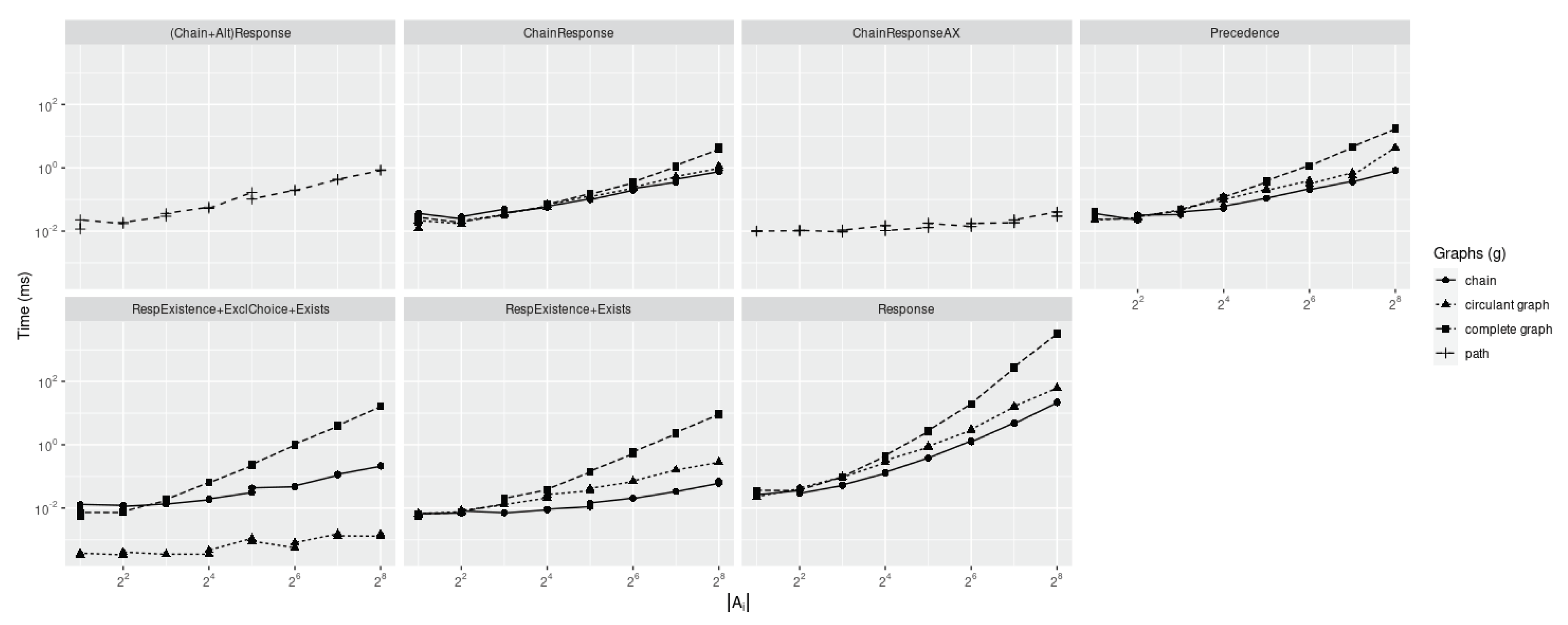
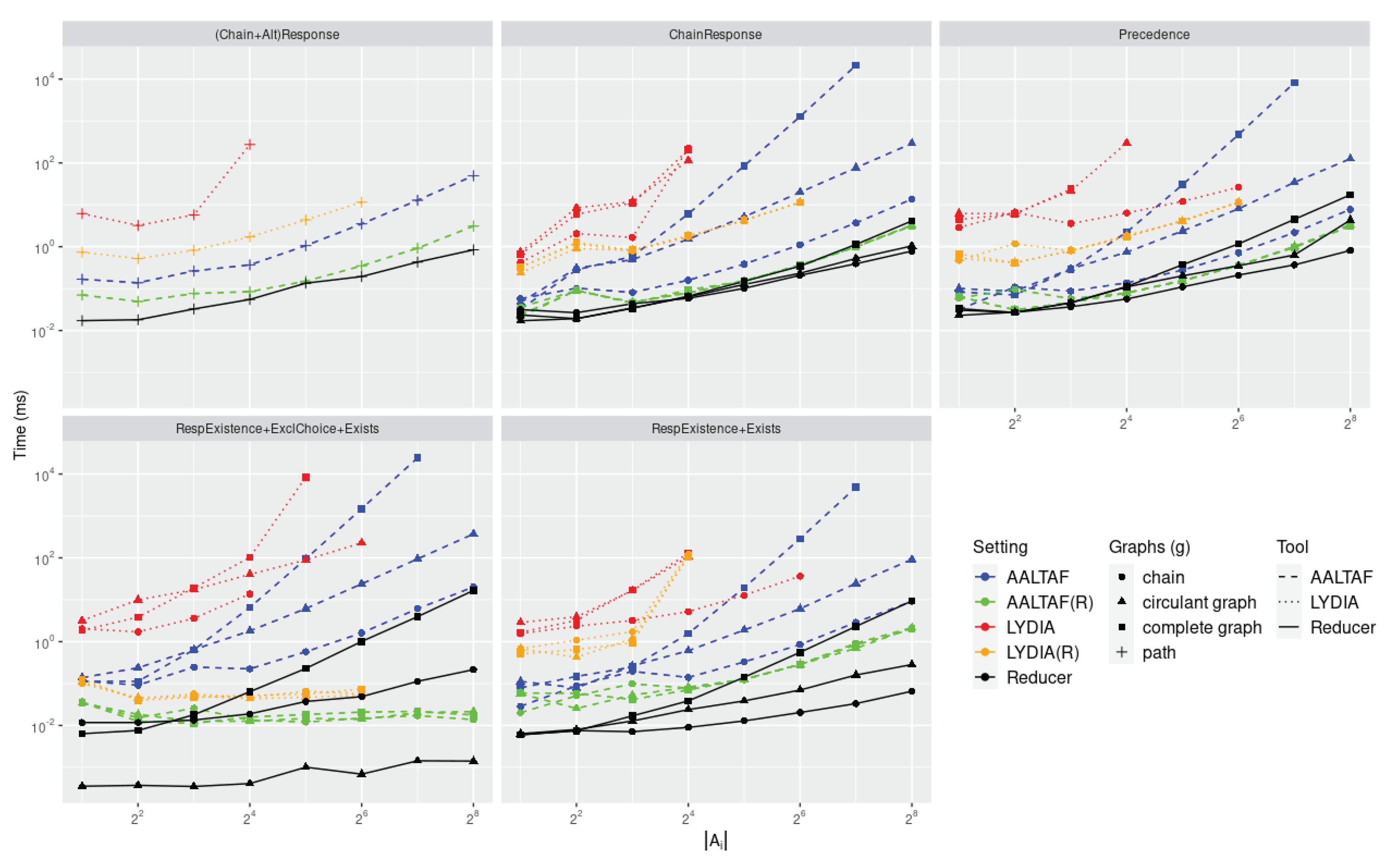
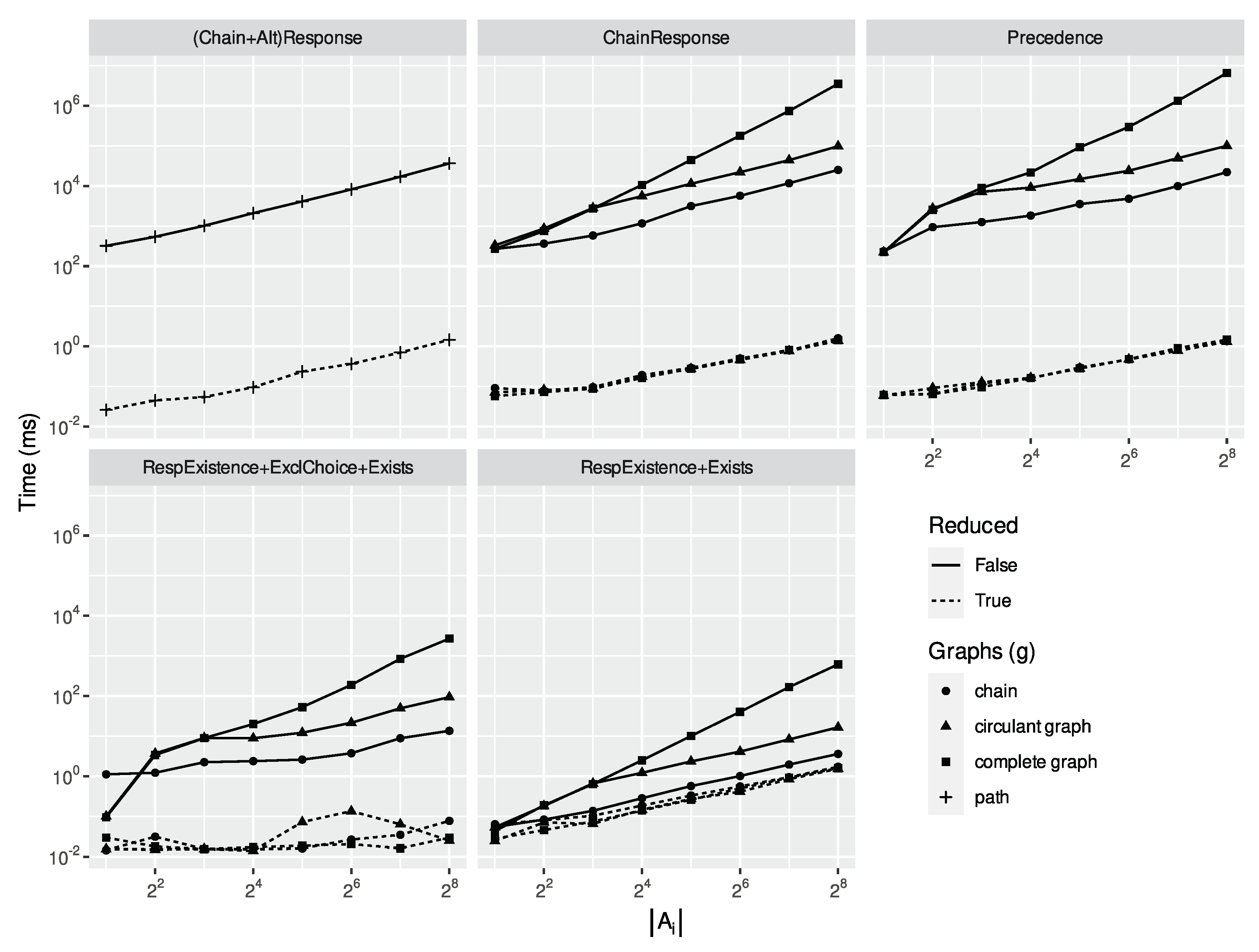
5.1. Rule Rewriting without Temporal Non-Simultaneity
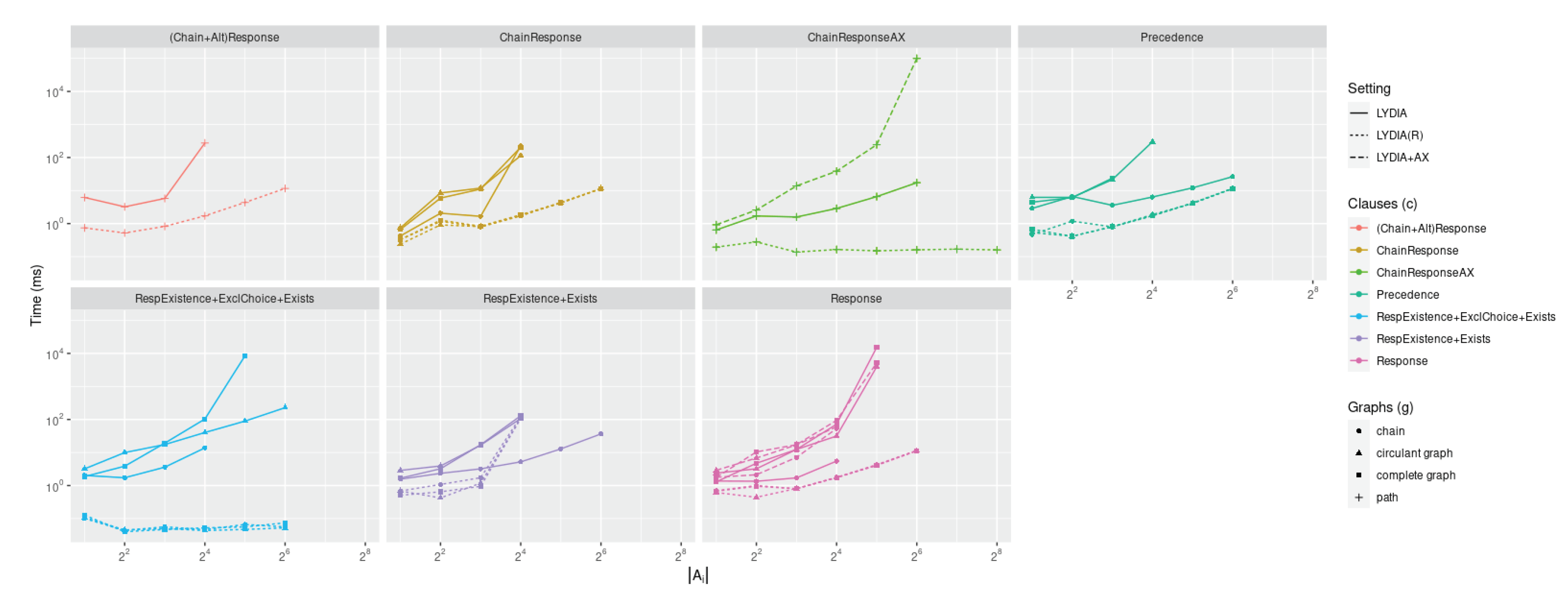
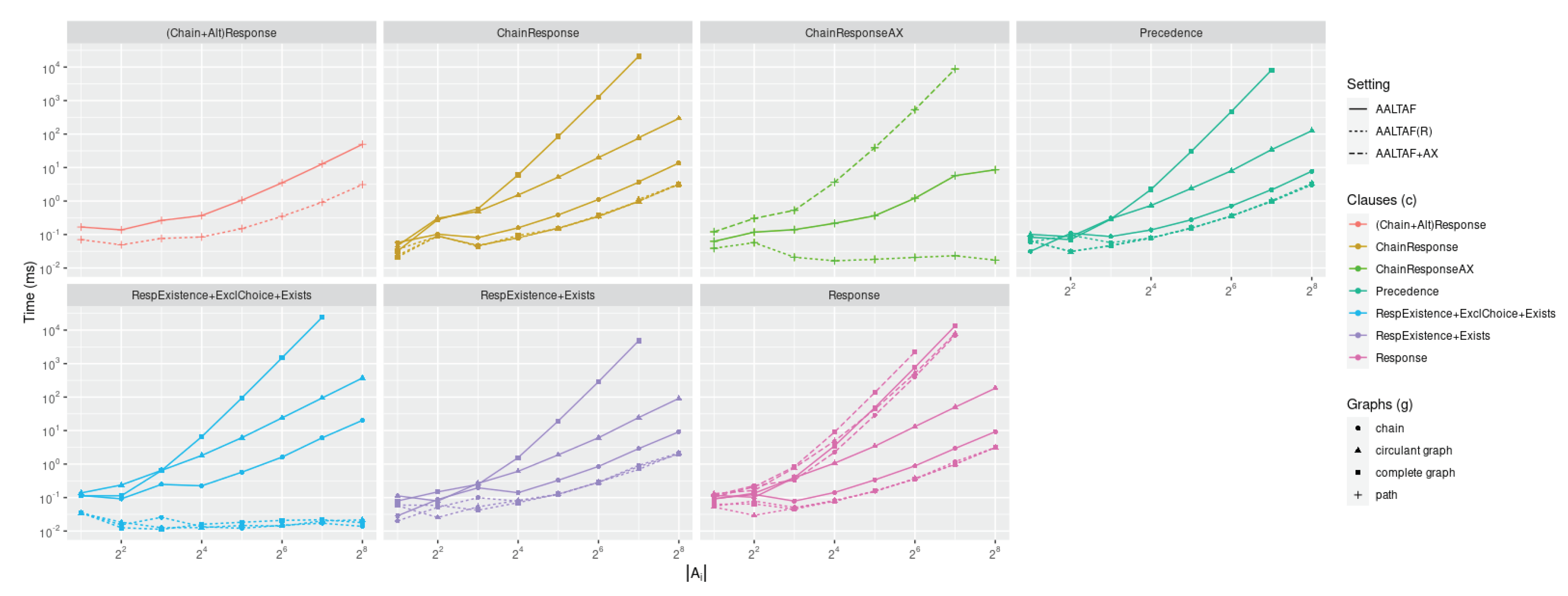
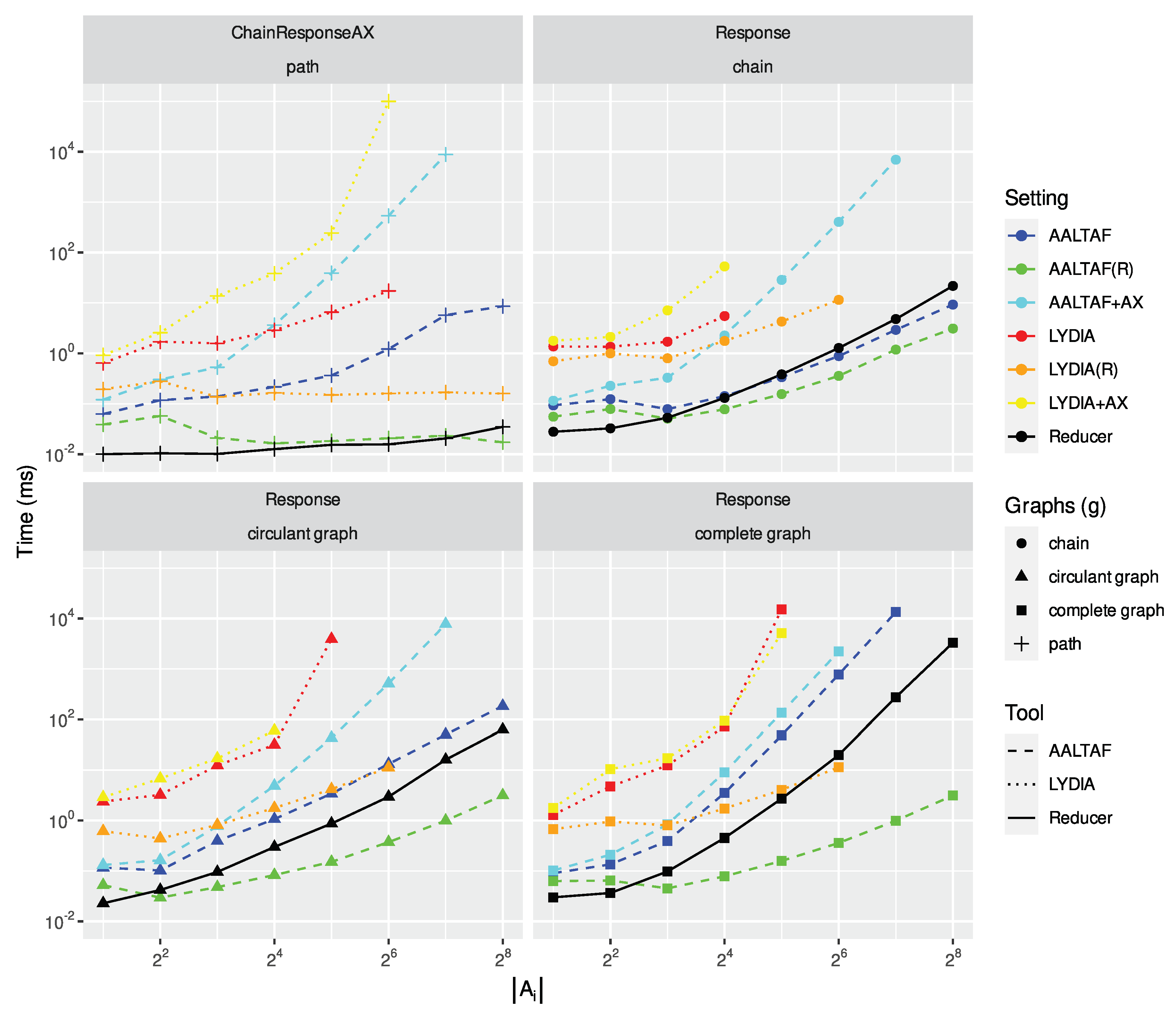
5.2. Rule Rewriting Requiring Temporal Non-Simultaneity
6. Conclusion and Future Works
Funding
Institutional Review Board Statement
Informed Consent Statement
Conflicts of Interest
Appendix A. Formal Definition
Appendix A.1. Graph Operations
Appendix A.2. Multimap Operations
Appendix B. Short-Circuit Rewriting: Time Complexity
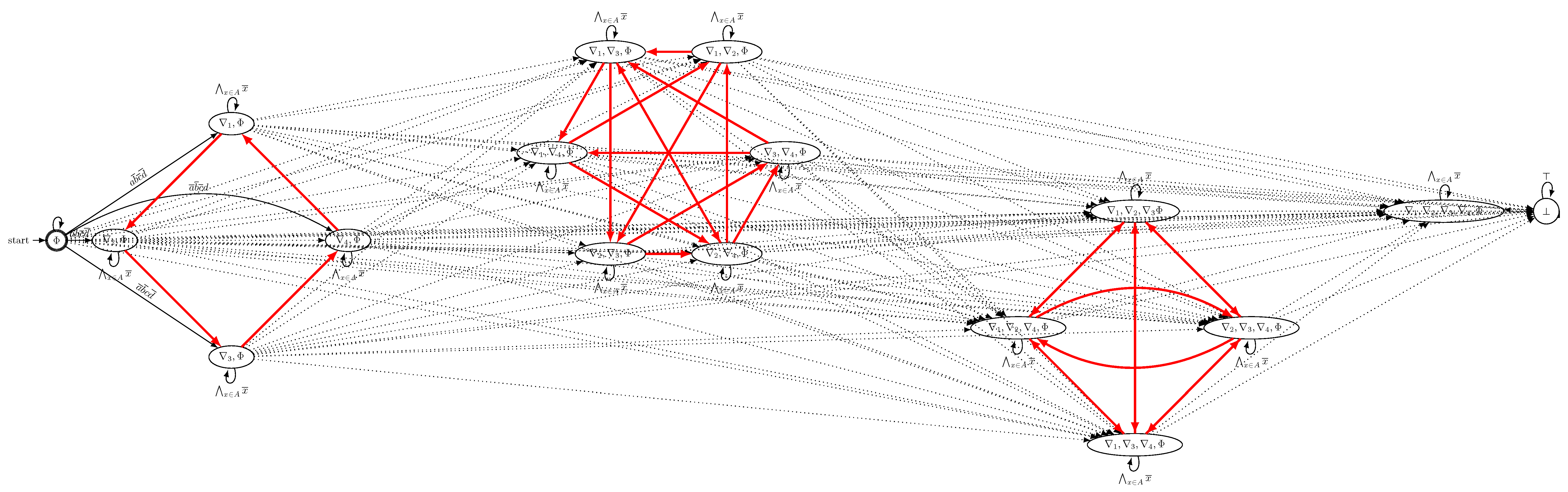
Appendix B.1. Automata-Based Strategy
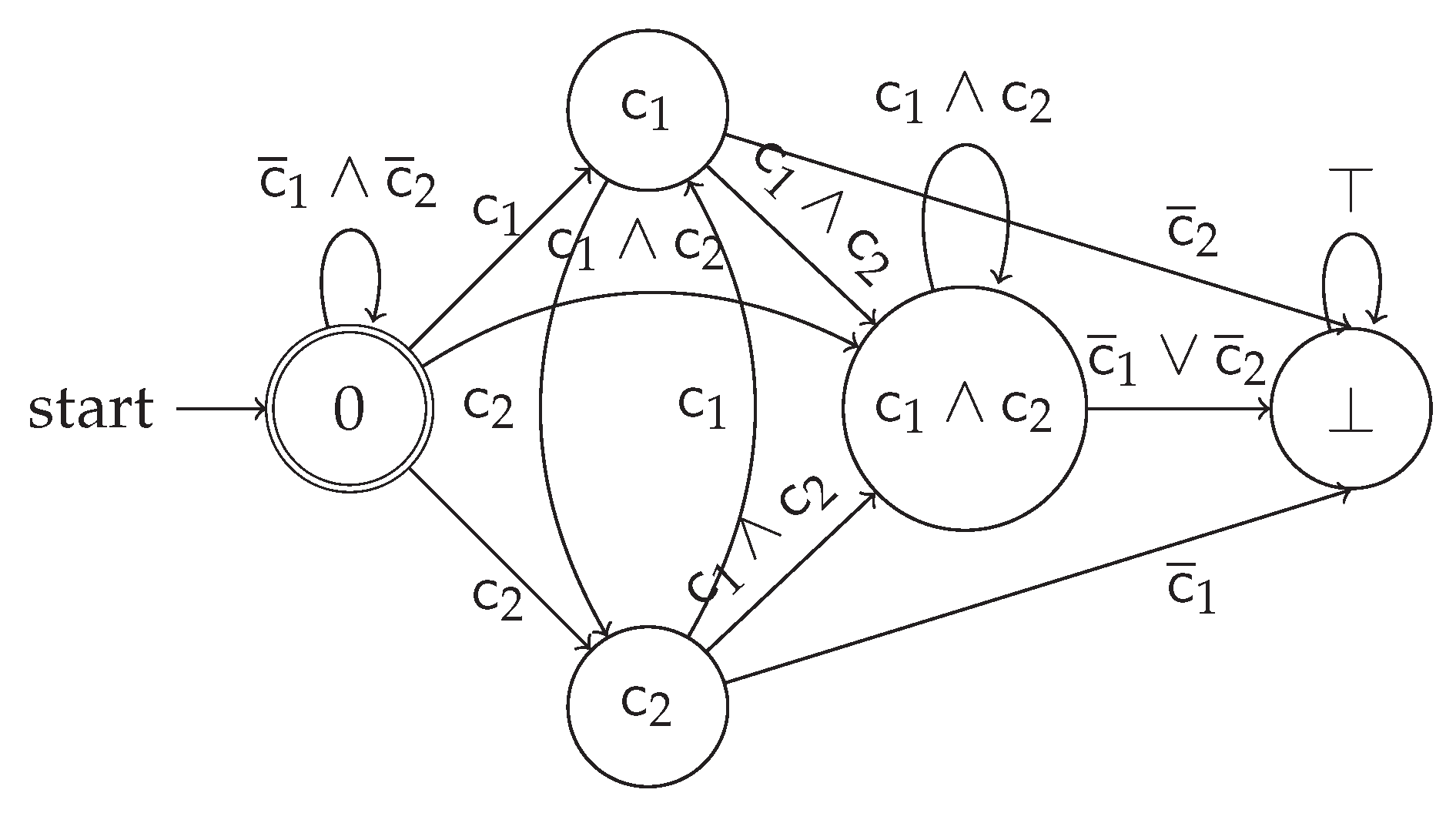
- an edge : this requires that, as soon as at least one of the activities in A is run, then we need to follow the requirements associated to the specification;
- an edge : this requires that, as soon as we miss one of the transition conditions requiring that each of the activities being true in S should then immediately move to the immediately following activities , we then violate the specification;
- for each , we define a new edge if : we connect each of such states not only to the immediately following actions as per , but we also assume that further activation conditions must hold.

- (1)
- : if none of the clauses is activated, we trigger no activation condition leading into a target requirement to be met; we, therefore, persist on the same initial accepting state.
- (2)
- for each : when at least one activity label in activates one clause, we transit to a state representing the activation of the specific clause.
- (3)
-
for each : for remaining in the same state, we require that no other condition not appearing as shall be activated, otherwise, we will be transiting towards another state. Furthermore, we require that the activation of any for which both and appear in S should also require the activation of the activity as, otherwise, we will reduce the number of , thus ending into a state containing a subset of activated conditions: this is enforced by the construction of . Given this, we obtain the following formulation for F:Please observe that we do not require that should also hold, as the eventuality of the condition for the target condition does not strictly require that such condition must immediately hold in a subsequent step, so either the possibility of being still activated or its opposite are both considered.
- (4)
- with : we need to ensure that the conditions appearing only in are newly activated, while the ones being active in shall be kept active in ; given this, we obtain the following F:
- (5)
- with : this transition can only occur if, by attempting to consume with by executing an action , this leads to generating appearing in or, otherwise, we would have transited towards another state. This then provides a restriction of the states towards which we can transit and the states that can move backwards. F can be then defined as:
- (6)
- with : otherwise, we can transit with at the following conditions: for each , either or . If those conditions had not been met, given the previous considerations, it would not have been possible to transit exactly between these two states.
- (1)
- : Same as per the previous lemma.
- (2)
- for each : Same as per the previous lemma.
- (3)
- for each : As per previous observation, this is now changed to , as performing none of the states that are recorded in A is the only possible way not to transit into any other state.
- (4)
- with : Same as per previous lemma.
- (5)
- with . This type of transition never occurs similarly to lemr-1. Without any loss of generality, let us assume that and as in the previous lemma: allowing such transition would require to have an event abiding by for which either or . The only possible way to make this admissible is to make also (or ) move with a corresponding (or ) action; still, this would have contradicted the assumption that i and j are not moving, and therefore this action would either violate or , which is then impossible. Therefore, executing any of the activation conditions for being explicitly prohibited by the corresponding will just move the current source state of interest towards the sink falsehood state.
- (6)
- with : otherwise, as observed in the previous point, we can move towards a new state by either consuming a with leading to an , or by ensuring a with and for not violating an already-activated condition. Overall, we can observe that this leads to never transiting from a state containing more activation conditions towards one containing less than those, at any rate.
Appendix B.2. Proposed Methodology
Appendix C. Formal Verification Speedup
Appendix D. DECLAREd SAT
Appendix D.1. Correctness
Appendix D.2. Convergence in PolyTime(Φ d )
- Ex(x):
- This function takes note that the specification requires, at some point of the rewriting, that x shall exist anytime in a trace; this mainly updates a hashmap F and immediately returns a boolean value determining whether this is also associated to an absence, for which then F will be associated to two distinct values instead of one. Therefore, this trivially terminates in .
- Abs(x):
- This function is the exact dual of the previous one, as it predicates the absence of an event associated with an activity label x. Even in this case, this function always terminates in .
- Clear(x):
- This function calls only other functions for removing vertices and edges from a graph associated with a clause template, which functions are non-recursive and trivially terminating. Furthermore, this function only reduces the previously loaded and indexed information, except for the clauses associated with calls to Ex(x) and Abs(x), used to detect inconsistencies within the temporal specification. This is carried out in linear time over the size of the currently-loaded specification.
- Reduce(x) for :
- This function mainly describes an iterative backward DFS visit over a graph with using toremove as a stack by traversing all the edges in the graph backwards from x; we avoid in-definitively traversing loops in the graph by remembering which nodes were already visited and popped from the aforementioned stack (visited). This call jointly with Clear(x) ensures that no clause containing as an activity label will be returned in the resulting specification, as this function will remove all the vertices representing the activity label x. Henceforth, even this function does not generate new data jointly with A1. Overall, the algorithm is then guaranteed always to terminate in polynomial time over the size of the specification.
- Reduce(x):
- we can draw similar considerations as the previous algorithm, as the main difference is merely in the direction of the graph visit: we are now traversing the edges forward instead than in reverse (, Line 56 also in fig:rewriting). Vertices from the are also explicitly covered in this function (L. 40), as this is not considered as part of Clear(x); this ensures that this function cannot be called with the same argument x.
- Expand(x):
-
Notwithstanding that this function is the dual of the previous, this works similarly: when a new Exists(x) DECLAREd clause is attempted to be generated, we ensure that this will not trigger another rewriting annihilating some RespExistence clauses (, Line 56). Similarly to the previous steps, we are not adding information in the graph that we are traversing, rather than removing those, thus ensuring to avoid unnecessary re-computations over the same activity label . Furthermore, we remove any occurrence of a Choice clause that might be trivialised by the existence of x (, Line 52) as well as checking whether the existence of x might lead to inconsistencies related to the required absence of the label expressed in the target condition at Line 54:Similarly to the other sub-routines, this function is gradually reducing the number of the clauses which are potentially rewritten in Exists/Absence: due to (A1), this procedure is also guaranteed to terminate.
- Reduce(x) for :
- This provides a restriction to the case inasmuch as the activity labels in toremove are not visited from the stack, rather than being used for calling Expand which, in turn, is also a terminating function. Overall, Reduce is always terminating independently from ★.
Appendix E. Detailed Benchmarks
References
- Bergami, G. Streamlining Temporal Formal Verification over Columnar Databases. Information 2024, 15. [Google Scholar] [CrossRef]
- Bergami, G.; Appleby, S.; Morgan, G. Quickening Data-Aware Conformance Checking through Temporal Algebras. Inf. 2023, 14, 173. [Google Scholar] [CrossRef]
- De Giacomo, G.; Favorito, M. Compositional Approach to Translate LTLf/LDLf into Deterministic Finite Automata. Proceedings of the International Conference on Automated Planning and Scheduling 2021, 31, 122–130. [Google Scholar] [CrossRef]
- Bergami, G.; Appleby, S.; Morgan, G. Specification Mining over Temporal Data. Computers 2023, 12. [Google Scholar] [CrossRef]
- Pnueli, A. The temporal logic of programs. In Proceedings of the 18th Annual Symposium on Foundations of Computer Science (sfcs 1977); 1977; pp. 46–57. [Google Scholar] [CrossRef]
- Giacomo, G.D.; Masellis, R.D.; Montali, M. Reasoning on LTL on Finite Traces: Insensitivity to Infiniteness. In Proceedings of the Proceedings of the Twenty-Eighth AAAI Conference on Artificial Intelligence, July 27 -31, 2014, Québec City, Québec, Canada; pp. 20141027–1033. [CrossRef]
- Pesić, M.; Schonenberg, H.; van der Aalst, W.M. DECLARE: Full Support for Loosely-Structured Processes. In Proceedings of the 11th IEEE International Enterprise Distributed Object Computing Conference (EDOC 2007); 2007; pp. 287–287. [Google Scholar]
- Xu, H.; Pang, J.; Yang, X.; Yu, J.; Li, X.; Zhao, D. Modeling clinical activities based on multi-perspective declarative process mining with openEHR’s characteristic. BMC Medical Informatics and Decision Making 2020, 20, 303. [Google Scholar] [CrossRef] [PubMed]
- Giacomo, G.D.; Maggi, F.M.; Marrella, A.; Patrizi, F. On the Disruptive Effectiveness of Automated Planning for LTLf-Based Trace Alignment. In Proceedings of the Proceedings of the Thirty-First AAAI Conference on Artificial Intelligence, February 4-9, 2017, San Francisco, California, USA; pp. 20173555–3561. [CrossRef]
- Bergami, G.; Maggi, F.M.; Marrella, A.; Montali, M. Aligning Data-Aware Declarative Process Models and Event Logs. In Proceedings of the Business Process Management; Polyvyanyy, A.; Wynn, M.T.; Van Looy, A.; Reichert, M., Eds., Cham; 2021; pp. 235–251. [Google Scholar]
- Huo, X.; Hao, K.; Chen, L.; song Tang, X.; Wang, T.; Cai, X. A dynamic soft sensor of industrial fuzzy time series with propositional linear temporal logic. Expert Systems with Applications 2022, 201, 117176. [Google Scholar] [CrossRef]
- Wang, C.; Wu, K.; Zhou, T.; Cai, Z. Time2State: An Unsupervised Framework for Inferring the Latent States in Time Series Data. Proc. ACM Manag. Data 2023, 1. [Google Scholar] [CrossRef]
- Yazi, A.F.; Çatak, F.Ö.; Gül, E. Classification of Methamorphic Malware with Deep Learning(LSTM). In Proceedings of the 27th Signal Processing and Communications Applications Conference, SIU 2019, Sivas, Turkey, April 24-26, 2019. IEEE, Sivas, Turkey, 24-26 April 2019; 2019; pp. 1–4. [Google Scholar]
- Catak, F.O.; Ahmed, J.; Sahinbas, K.; Khand, Z.H. Data augmentation based malware detection using convolutional neural networks. PeerJ Computer Science 2021, 7, e346. [Google Scholar] [CrossRef] [PubMed]
- Li, J.; Pu, G.; Zhang, Y.; Vardi, M.Y.; Rozier, K.Y. SAT-based explicit LTLf satisfiability checking. Artificial Intelligence 2020, 289, 103369. [Google Scholar] [CrossRef]
- Geatti, L.; Gianola, A.; Gigante, N.; Winkler, S. Decidable Fragments of LTLf Modulo Theories. In Proceedings of the ECAI; Gal, K.; et al.. 2023. [Google Scholar]
- Cormen, T.H.; Leiserson, C.E.; Rivest, R.L.; Stein, C. Introduction to Algorithms, 3rd Edition. MIT Press, 2009. [Google Scholar]
- Bergami, G. Fast Synthetic Data-Aware Log Generation for Temporal Declarative Models. In Proceedings of the Proceedings of the 6th Joint Workshop on Graph Data Management Experiences & Systems (GRADES) and Network Data Analytics (NDA), New York, NY, USA, 2023; GRADES & NDA ’23.
| 1 | |
| 2 | |
| 3 | |
| 4 | |
| 5 | An on-line tool is available here: http://ltlf2dfa.diag.uniroma1.it/
|
| 6 |
| Exemplifying clause () | LTLf Semantics () |
|---|---|
| Exists(A) | |
| Absence(A) | |
| Choice() | |
| NotCoExistence() | |
| ExlChoice() | |
| RespExistence() | |
| CoExistence() | |
| Precedence() | |
| Response() | |
| Succession() | |
| NegSuccession() | |
| ChainPrecedence() | |
| ChainResponse() | |
| ChainSuccession() | |
| AltResponse() | |
| NegChainSuccession() | |
| AltPrecedence() | |
| AltSuccession() |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




