Since the work on hand is based on a combination of approaches originating from different domains, the aim of this section is to give an holistic overview of existing solutions regarding DPP-specific requirements, the feasibility of potential technologies for implementing a respective framework, as well as considering surfacing security considerations. This multi-disciplinary approach is furthermore observed in the context of the main objective in the EU regulations regarding DPPs, which is to promote the so-called
R-strategies, e.g., enabling the reuse, repair, refurbish, remanufacture and recycle of the regulated product classes [
6]. According to [
11] an implementation of such strategies which act as an replacement for current product End-of-Life (EoL) concepts, could save 80-90% of raw materials and energy consumption, leading to an estimated 25-30% decrease of product prices, which remains to be proven.
The concept of a DPP is also closely related to Digital Twin (DT)s, material passports and life-cycle record files. The key difference is that a DPP provides information whenever and on-demand, rather than just at the pre-defined end of a cycle [
11]. Although there are various approaches of implementing lifecycle-related data structures for considering cross-tenant tracking systems [
5], an common and EU-wide standard of defining DPPs is still to come. As the overall methodology of defining and applying DPP is still in a conceptual phase, technologies like BC and the Asset administration Shell (AAS) are widely applied [
11], but in no way required or . The common objective of all of these technologies is information modelling for multi-tenant ecosystems [
5]. Studies such as [
12] discuss the various whitepapers and living documents to provide a holistic and comprehensive view of current approaches and methodologies related to DPP.
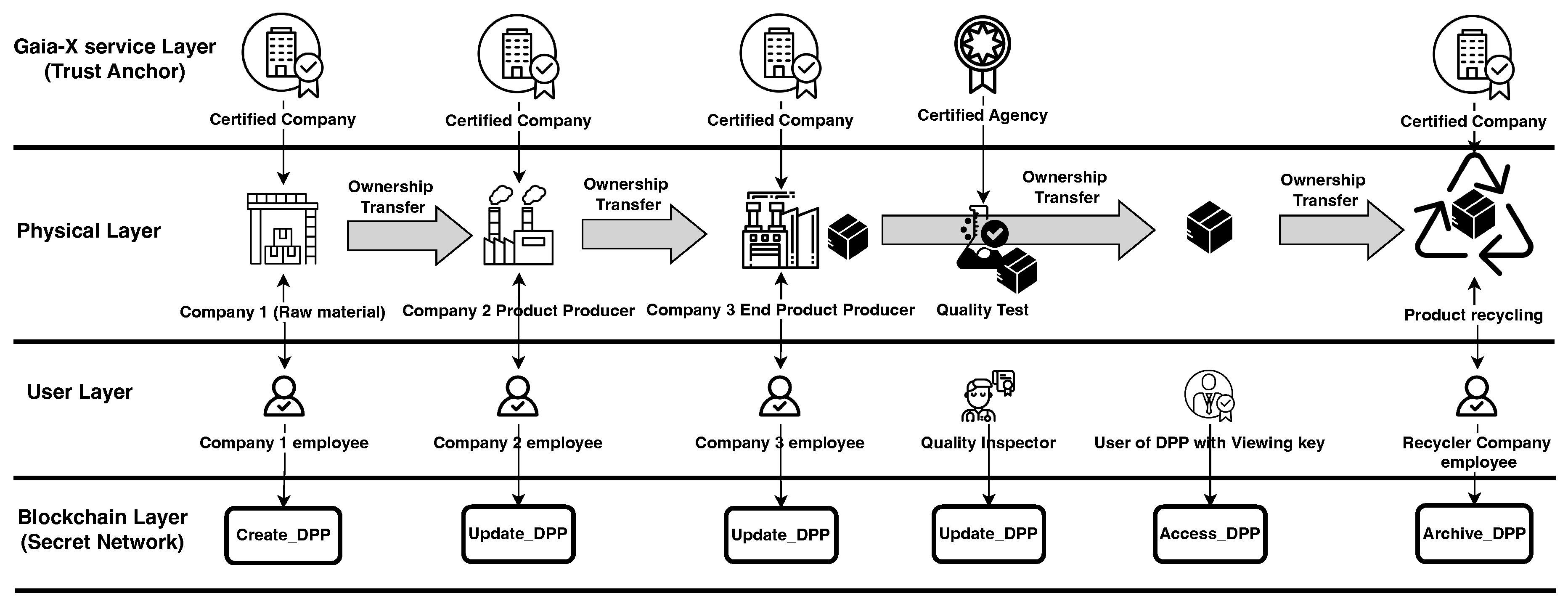
The Gaia-X project aims at creating future data platforms with focus on data privacy, as well as on the compliance of data-at-rest policies, e.g., the location in which data is stored [
7]. Even within an organization, the traditional exchange of data is not always standardized, e.g., there are often
information silos per business process or department, whereas the concept of data sovereignty aims at enforcing context-based usage constraints, definable by the respective data owners. By designing a trusted infrastructure ecosystem for standardizing service descriptions, management-capabilities and audition of federated services, a framework for managing and controlling the their overall compliance with regulations, on-boarding processes, certification, etc., is foreseen. On the other hand, the data ecosystem is focusing on securing the accountable processes with respect to a sovereign and certifiable data exchanges among different actors, utilizing the concept of data spaces which are implemented in the infrastructure services for providing or consuming information. Since the final technical service landscape of Gaia-X, and therefore the common requirements for participation, is still to be defined and standardized, there are many additional aspects to consider when designing DPP-enabling solutions in the context of the Gaia-X ecosystem. Although the work on hand is discussing a DPP-enabling framework for enabling such federated or cross-company scenarios in the broadest sense, a Gaia-X affiliation is not required at all. In addition, the approach in hand is solely utilizing BC technology for DPP-related operations, which in turn also contributes to decreasing the complexity of the overall system’s setup.
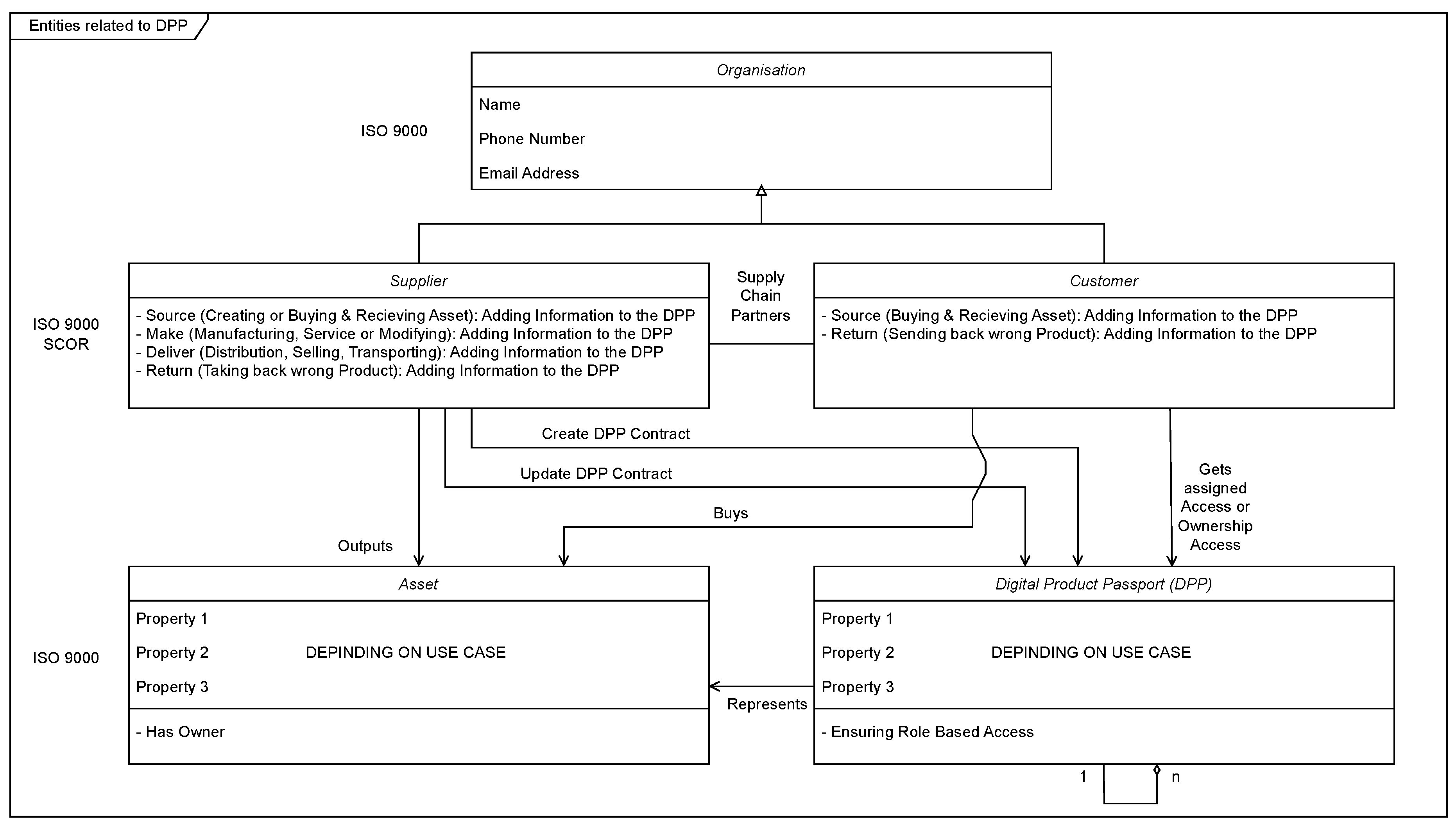
2.1. Implications of DPP for Manufacturing
As there is a variety of possible scenarios which may increase the motivation of manufacturers to take part in the Circular Economy (CE), a literature review of requirements on DPPs in [
11] resulted in four main-categories, e.g.,
product-, utilization-, value-chain-, & sustainability-information, and 21 sub-categories, showcasing how to potentially apply concepts in the machinery sector. Beginning with the mostly non-changeable
product information ranging from details of physical models to certifications of standards applied during the manufacturing process. Another sub-category concerns the
utilization information which is dynamically gathered and adjusted during the product life-cycle, e.g., different service-related data as for example energy consumption, as well as service manuals or information about spare parts. The data defined in the
value chain information increases transparency along stakeholders and enables a certain degree of automation when processing a DPP-enabled product with respect to the
R-strategies. When gathering
sustainability information with respect to a product, it may be an added value to apply DT technology for calculating and illustrating conclusion about the products sustainability e.g., ecological, social or circular events. Although the work on hand is considering many aspects of such an DPP design, the focus is on an approach of securing the overall DPP ecosystem and usage by presenting a BC-enabled concept.
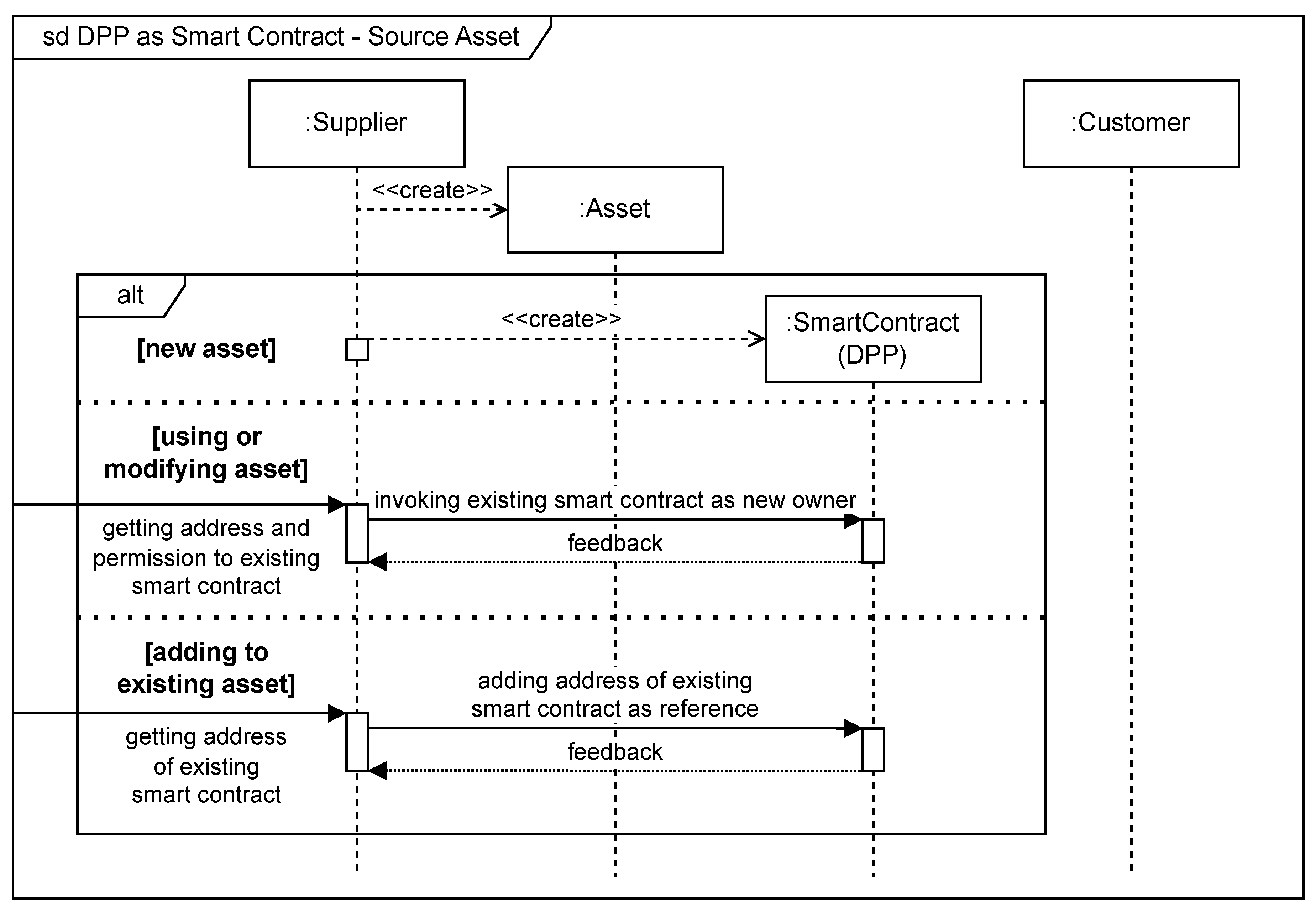
In [
13], an adaptable DPP-specific framework was proposed in an CE-enabling context, considering different technologies regarding the collection, curation, sharing, as well as leveraging of product-specific data. With respect to Internet of Things (IoT) and other
smart devices, the collection of data may be considered in an DT implementation, where efficient monitoring can be included, too. Another aspect to take notice of is the processing of personal data, as for example the consideration of biometric information provided by personal devices for authentication, as well as enabling Machine Learning (ML)-based approaches by interconnecting databases, the detection and collection of user-specific and identifying data respectively. Next to common techniques for the curation of data by, as for example reducing background-noise or applying filters, the format for sharing information between process or organizations must be considered, too. By now, there is also a wide utilization of the BC technology as configurable processing and maintenance mechanisms are provided while a combination with ’foreign’ technologies remains possible. With respect to approaches regarding
data leverage, the term ’Piggybacking’ is used for describing the utilization of business data in productive data pipelines for CE purposes. Although a concept of an adaptable and BC-enabled DPP system is presented in the work on hand, the overall focus is on the framework’s dynamism and accountability in the manufacturing domain, instead of solving user-specific privacy consideration.
In [
5], multiple approaches of implementing DPP-alike systems for different purposes and scenarios were analyzed. Therein, the intention of an DPP is considered as the consistent ’track-and-trace’ of information with respect to a product’s origin, composition, repair, dismantling options and EoL handling. In addition, such a implementation must be compatible across all involved actors. The considered DPP examples were also categorized according to their regulations, as for example the European Union (EU)
energy labeling framework where a product is extended with a product-identifying sticker on market introduction. This already implemented approach is shaped due to other politically driven impacts as for example the referencing of European Product Registry for Energy Labelling (EPREL) data, which is mandatory to register since 2021 for a variety of energy-related products on entering the market and where energy consumption and technical aspects can be requested on-demand during usage. In extreme cases, there are also obligations where information must be provided by suppliers of products containing substances of very high concern to the European Chemicals Agency (ECHA) [
5]. On the other hand, there are benefits of implementing DPP in a variety of scenarios, which is why there are some approaches of proving voluntary regulations. One of the most prominent is the material passport in building industry with focus on recycling materials when the product EoL is reached. There are other voluntary regulations, as in the case of the Cradel-to-Cradel (C2C) passport where a 3D-model depicts the kind of materials and their exact locations within large cargo-ships for recycling purposes when the boat’s EoL is reached. In addition to being capable of handling the depiction of each of such approach-specific DPP information, e.g., product type-specific decisions for
r-strategies, technical specifications like energy consumption, or location-specific material utilization, the generic architecture which is proposed in the work on hand also considers a variety of security mechanisms.
In [
4], efforts for clarifying requirements on DPPs were undertaken with respect to the depiction of different lifecycle stages, performed operations and design decisions of an DPP structure, as well as it’s possible utilization. Next to common advice such as investigating co-contractors components and analyzing previously developed components, the assessment of the product’s replaceability in terms of material and components are basic practices when designing the data management within an DPP system. In [
6], a holistic analysis of requirements on DPP-enabling systems is presented. In general, a DPP is a unique document and may contain life-cycle data like the composition of a product, e.g., manufacturing processes, materials, phsyical- and chemical properties, Substances of Concern (SoC), etc., specific usage data as for example repairs or replaced components, as well as information and how to treat product components when their EoL is reached. With identifying different requirement categories fro DPPenabling systems, e.g., considerations regarding legal questions, functionality, security, interoperability, modifiability, accessibility, availability, as well as portability. Since many of the requirements apply to the approach in the work on hand, specific attention was payed to them during the architecture’s design decisions, e.g., the selection of the respective BC technology, as well as pre-defined interaction specifications.
In general, there are also many additional commonalities of the information which is contained in an DPP. As the digital nameplate [
14] sets the focus on static features like the manufacturer’s address, name, product name and type, serial & batch number and others, there are also references to CE certification possible. For example, in Germany it is required to state the electronic voltage, current and frequency range, connection types, as well as special power supply information physically on the product. On the other hand, specific product properties [
15] like the geometric or physical model containing technical data and documentation, while an behavioral model is referencing configurations, operational data, simulation models or maintenance.
2.2. Impacting Approaches and Technologies
It is becoming obvious, that the concept of applying an DPP-alike methodology has originated out of an evolution of best practices and semi-standards over the last years. Next to the heavy utilization of AAS implementations with respect to dynamic inventory management, the concepts of DT and digital nameplates are closely related to DPPs.
Digital nameplate [
14] solves the problem of providing product-specific information which is directly located at a specific product and can be utilized by everyone, as they are usually applied in the form of an Quick Response (QR)-code printed on stickers, engraved metal plates or more technological solutions like Radio Frequency IDentification (RFID). A digital nameplate contains all labels which are required by law, as well as info regarding the life-cycle phases with the overall purposes of saving time and cost due to digital management, high availability and a standard-free depiction, while reducing the need for paper documentation and enhancing sustainability. With respect to a referenceable digitial identification, the concepts of Decentralized IDentifier (DID) are a promising technology for enabling DPP-based systems [
6], as they are represented by an specifically structured Universal Resource Identifier (URI) [
14]. Providing such verifiable credentials for a specific product will also contribute to CE scenarios while enabling cross-sectoral use-cases when participants settle upon such standardized formats. Another side-effect is the ability of providing a reference to the complete product documentation while enabling automation of information retrieval processes, their utilization in customer-specific applications, as well as the seamless communication of manufacturer and customer processes. When combining a digital nameplate system with Enterprise Resource Planning (ERP)-connectivity, error-free inventory-control is possible. When making heavy use of AAS, as proposed in [
14], all information about a product and how it is connected to processes in the company may be persisted within that technology, which is shielded by organization-internal web-apps referable by the QR codes. In the context of Gaia-X, concepts like the DID are playing a vital role for creating and identifying actors and services. Although they are not specifically considered in the work on hand, they are most likely implied when conformity with Gaia-X is a requirement. In general, the work on hand can easily be extended for utilization of physical enablers like QR codes burned into the product.
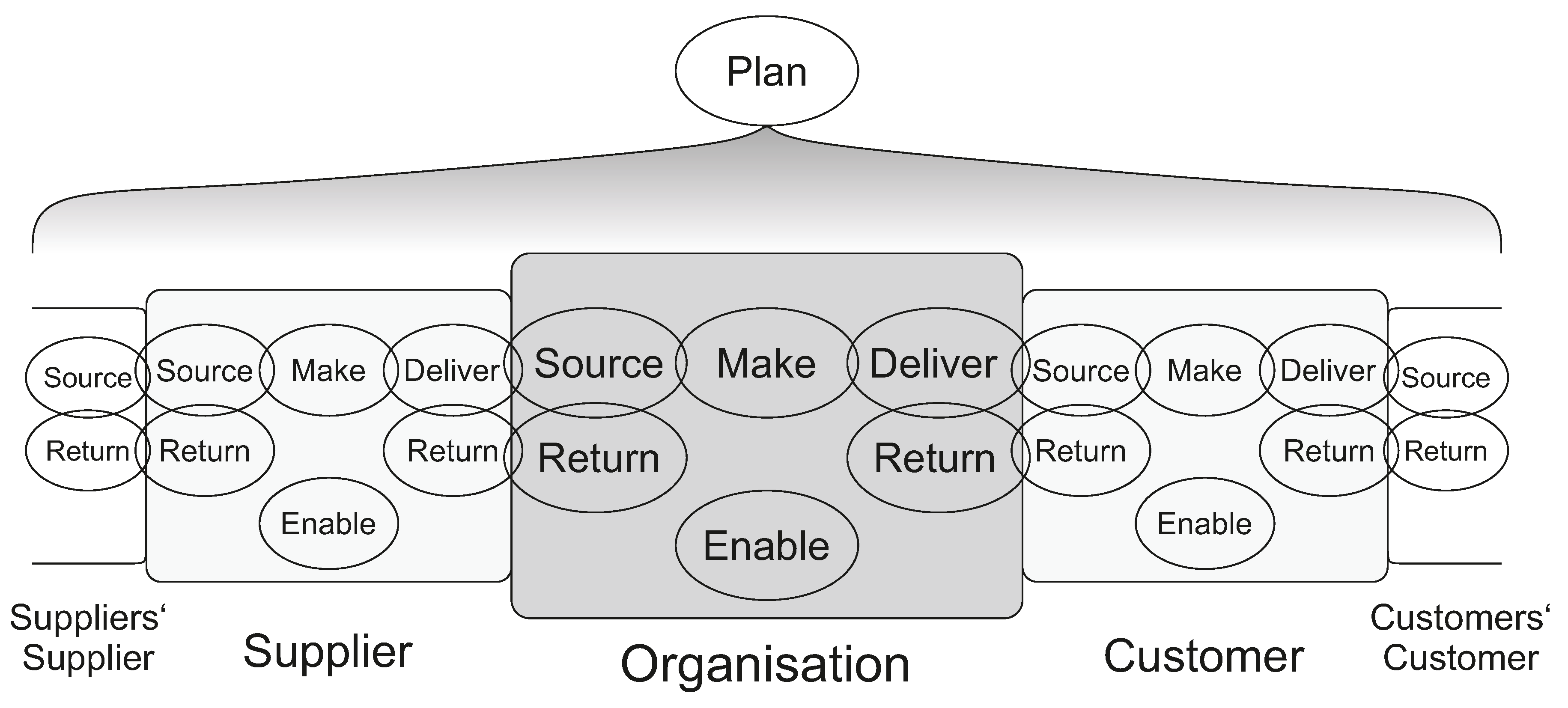
In current literature and projects with association to the manufacturing domain, the AAS is the database-type of choice [
5,
11,
15] and is sometimes called itself a DT implementation as all available product data can be placed there. The many opportunities and challenges of AAS implementations with respect to a holistic traceability for supply-chain management were discussed in [
16]. The end-to-end traceability of an object, e.g., service or product, is a vital instrument for validating the compliance of partners across the supply-chain, dynamic object-configurations or tackling disruptions . When for example applying the Reference Architectural Model for Industrie 4.0 (RAMI)4.0 model, differentAAS submodels can relate to different life-cycle stages of an unique asset. There are many opportunities of using AAS, as for example standardized data interfaces which enables participation across product-specific systems, as well as machine-readable data for improving automated processing steps during specific lifecycle stages. On the other hand, challenges like data non-sovereignity, inconsitences on exchange between different AAS instances, lack of consistent (global) asset identification and many others remain due to non-existing standards. In [
15], a mapping between DT and AAS models is considered for implementing a virtual industrial IoT simulation system. Therein, the AAS is enabling the interoperability of an systems which spreads across companies through standardized digital representation of industrial application assets. In a way, the AAS is considered as DT-embodiment of industrial applications, e.g., exploiting concepts like object encapsulating, information integration, data interaction, re-/configuration, decision support, also enabling scenarios as for example digital nameplates. Although the work on hand does not specifically make use of an AAS, the BC technology is considered in the work on hand as trust anchor, enabling global identification of assets, while conformity with Gaia-X addresses a sovereign data exchange between organizations.
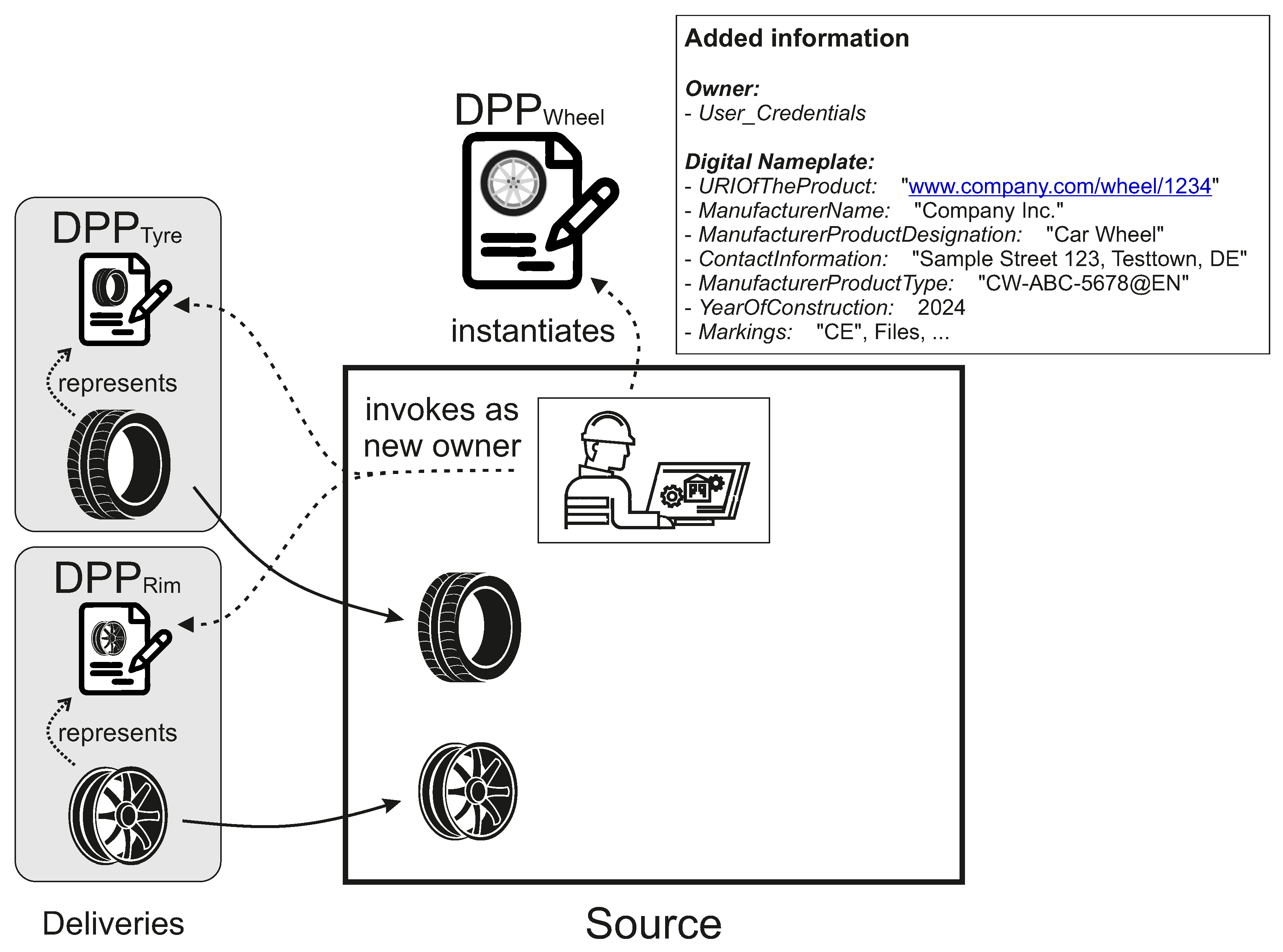
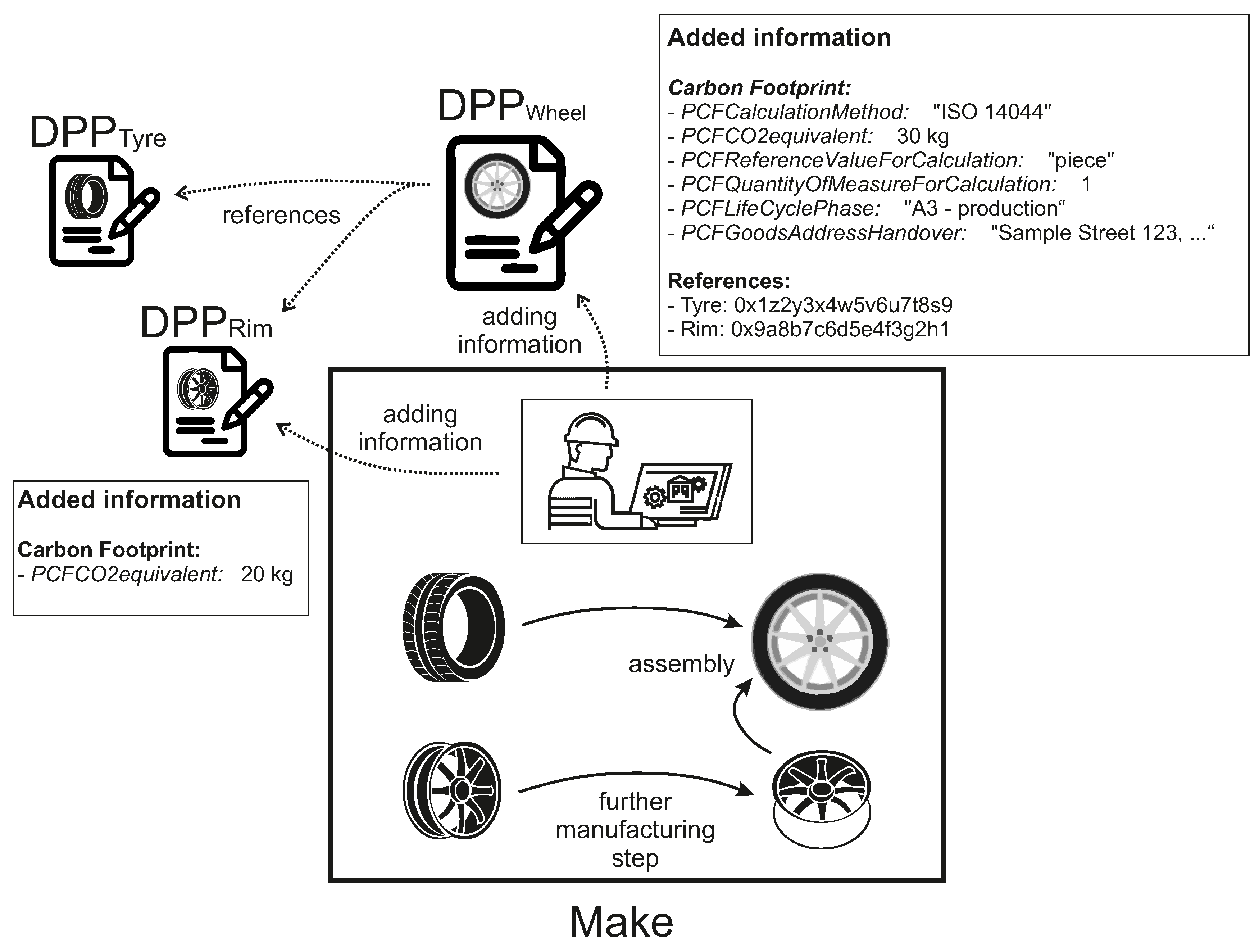
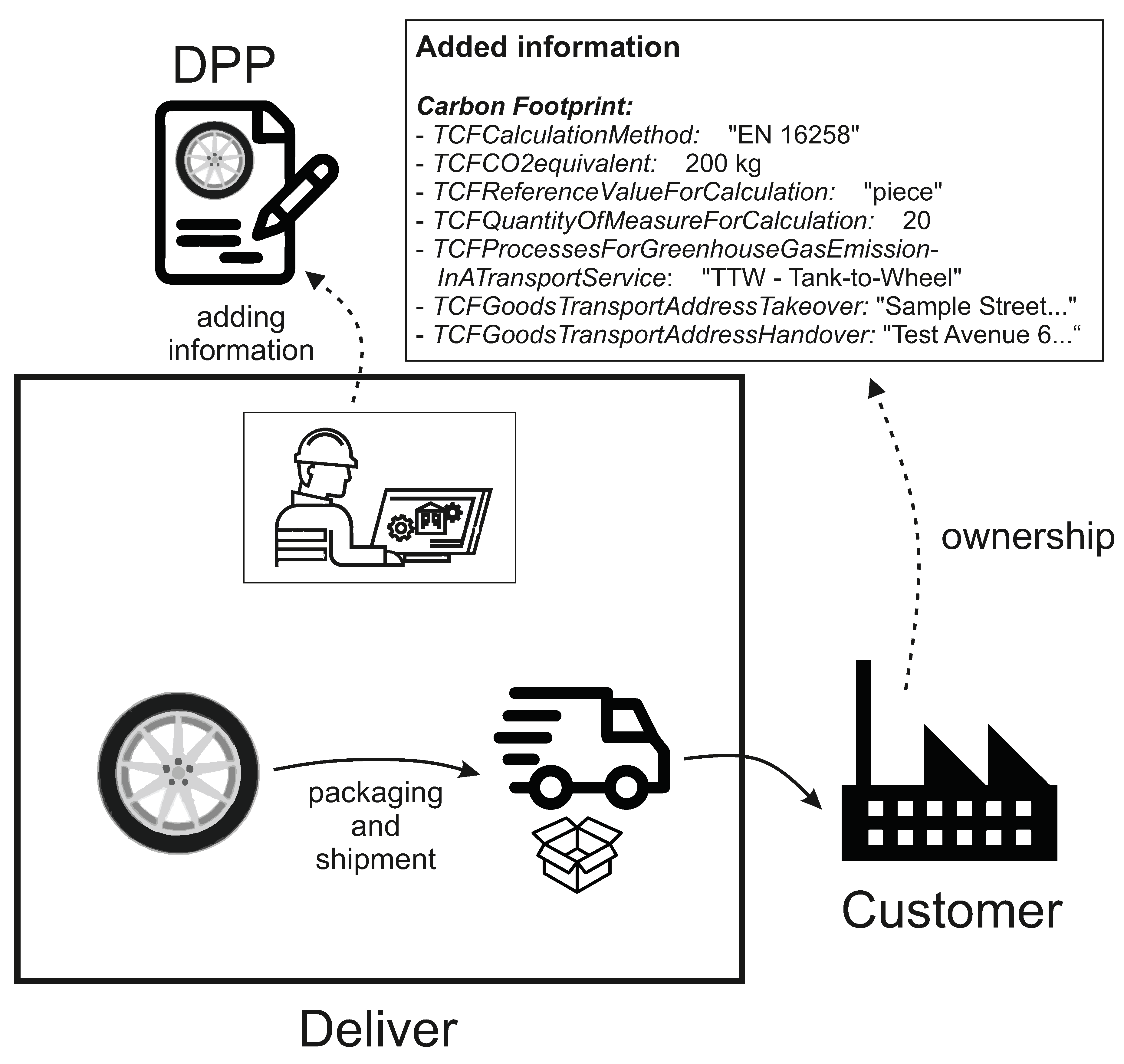
2.3. Use-Case: Carbon Footprint in Manufacturing
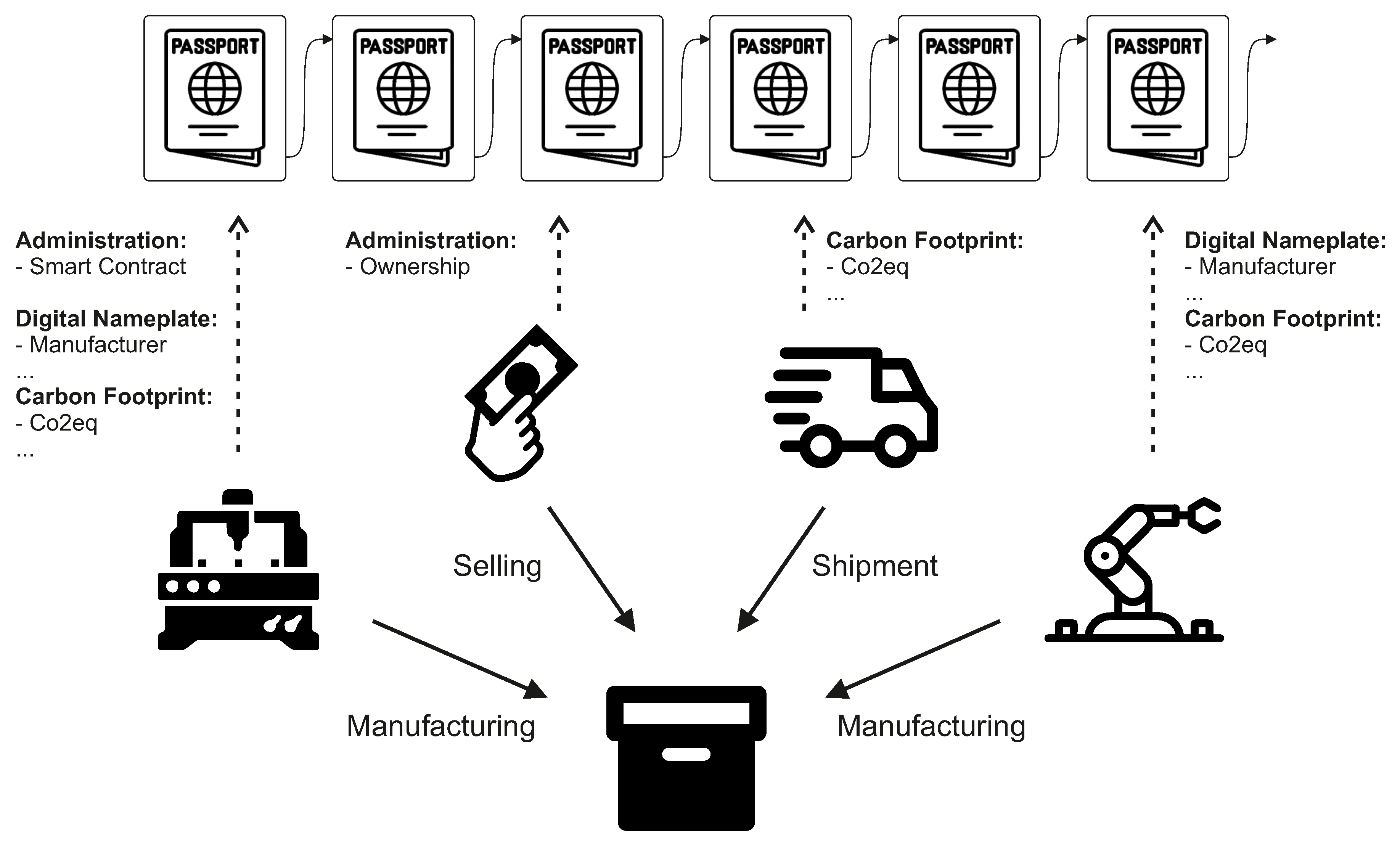
Since the work on hand is discussing the proposed architecture with respect to the use-case of carbon footprints within DPPs in
Section 5, this section is paying special attention to existing work in this domain. By specifically considering and overviewing the information from the digital nameplate required by [
17] and integrating them into the DPP [
18], a more holistic view on this realistic scenario can be gained.
In [
19], a scenario specifying the likely content of DPPs in industrial application is presented. Therefore, two main components are presented, a
digital nameplate with administrational information of the product and manufacturer, as well as a
carbon footprint with information about
-equivalents that have accumulated during the production and the transport of the asset. While the digital nameplate fulfils import regulations, e.g. the CE mark, the carbon footprint provides information on the sustainability of the product, which is in line with the objectives of the European Green Deal regulations. The basis for the specific content of these two components are standardised information collections, such as [
18], which specifies an information model for the content required for a digital nameplate industrial machines products. The standardisation and digitization of nameplates can simplify the collaboration within supply chains by increasing the scope of product information, leading to enhanced interoperability between participants across the supply chain. The content must comply with existing international conventions and standards for nameplates and regulations such as the EU Machine Directive [
17]. The digital nameplate contains general information about the product, the manufacturer, as well as the regulations fulfilled. Therefore, the information from the digital nameplate required by [
17] were primarily integrated into the DPP [
18], as depicted in the following enumeration:
URIOfTheProduct: The product needs to be unambiguously identifiable using a globally URI.
ManufacturerName: The legally valid designation of the natural or judicial person directly responsible for the design, production, packaging and labeling of a product with respect to bringing it into circulation.
ManufacturerProductDesignation: Brief product description (e.g. "industrial robot").
ContactInformation: Contact to the manufacturer or an authorised service provider.
ManufacturerProductType: Characteristic of different products in a product family or special variants, e.g., an International Registration Data Identifier (IRDI) reference to a product class using [
20].
YearOfConstruction: The year in which the asset was completed.
Markings: Collection of product markings and all label-specific information, e.g., the "CE" mark including the date of issue and the label file.
A standard for the required content for a carbon footprint, as it is also utilized in the work on hand, is presented in [
21]. Therein, the carbon footprint is calculated from the sum of the emissions from the production of an asset and its transport. For this, the
-equivalents and the calculation method must be specified. Due to the different calculation methods used for the Product Carbon Footprint (PCF) and the Transprt Carbon Footprint (TCF), the two aspects contain different information, which is documented. According to [
21], the information used for the carbon footprint of the production of an asset can be summarized as follows:
ProductCarbonFootprintCalculationMethod: This describes a standard or a method for determining the greenhouse gas emissions of a product (from a list of various standards for calculation).
ProductCarbonFootprintCO2equivalent: This summarizes all greenhouse gas emissions of a product according to the quantification requirements of standard (e.g. 17.2 kg).
ProductCarbonFootprintReferenceValueForCalculation: This describes the quantity unit of the product to which the PCF information on the CO2 footprint refers to (e.g. per piece).
ProductCarbonFootprintQuantityOfMeasureForCalculation: This describes the quantity of the product to which the PCF information on the CO2 footprint refers to (e.g. 5 pieces).
ProductCarbonFootprintGoodsAddressHandover: This indicates the place of hand-over of the goods.
ProductCarbonFootprintLifeCyclePhase: Here the life cycle stages of the product according to the quantification requirements of the standard to which the PCF carbon footprint statement refers to is categorised (e.g. raw material supply).
In order to assess the carbon footprint of the asset’s transportation, the following information is collected in addition to the equivalents of points 1-5 from the PCF [
21]:
TransportCarbonFootprintProcess: Processes in a transport service to determine the sum of all direct or indirect greenhouse gas emissions from fuel supply and vehicle operation (e.g. Tank-to-Wheel).
TransportCarbonFootprintGoodsTransportAddressTakeover: This indicates the place of receipt of the goods.
2.4. Security Considerations
There are many existing frameworks and approaches with varying technology stacks and security requirements which are able to fulfill the core-requirements on a DPP system. In [
22], a threat analysis of a framework for the rapid implementation of cross-company scenarios was carried out with respect to BC-enabled use-cases in the manufacturing domain. Therein, a central management platform was considered as communication mechanism for decoupling different shopfloors or tenants and dynamically compiling and configuring different constellations of predefined containers from the ecosystem’s repository. By analysing the framework’s dataflows and assessing observed threats to the overall infrastructure, staff, as well as the business side of an organization, a high-level view of the system’s security considerations was presented. Although there are many commonalities of the overall system with the work on hand, there are major differences in the requirements on a DPP-enabling application, as well as the technical differences in managing the ecosystem. In [
23], a holistic enumeration and analysis of many major security incidents in the industrial sector is given while considering details of the adversarial tactics which were applied to the exploited vulnerabilities. When assessing systems where digital actions are based on physical resources or conversely, or humans are included in-the-loop, additional attention must be payed to security as not only is the attack vector is increasing, safety of personnel and the environment must be considered, too. Although this remains true for a DPP system in the manufacturing sector as the one discussed in the work on hand, only the digital security is considered since the physical environment, where the operational technology is executed, is almost always dependent on the use-case.
Whenever multi-tenant systems like the ones required to fulfill the concept of DPPs are designed, the trustworthiness and management of digital identities comes into play. Since such a problem formulation is also part of the BC paradigm in general, this choice of technology may offer an elegant solution for solving applications within the federated system. In [
24], many of the aforementioned aspects are considered in a review on digital wallets and cloud service identity management. With comparing self-sovereign identity to centralized, user-centric, federated and service-based identity management to different security requirements, e.g., assumptions about storage security, effectiveness of management, sharing- and storing-security, as well as their aggregation, the management of future ecosystems is depicted. Although the work on hand is not considering the assessment of a service’s criticality regarding it’s management of identities, the participation in the framework presented in the work on hand requires a type of digital wallet in the broadest sense, anyhow.