Submitted:
04 February 2024
Posted:
05 February 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. 2D-CHSLM model
2.1. Definition of 2D-CHSLM
2.2. Performance evaluation of 2D-CHSLM
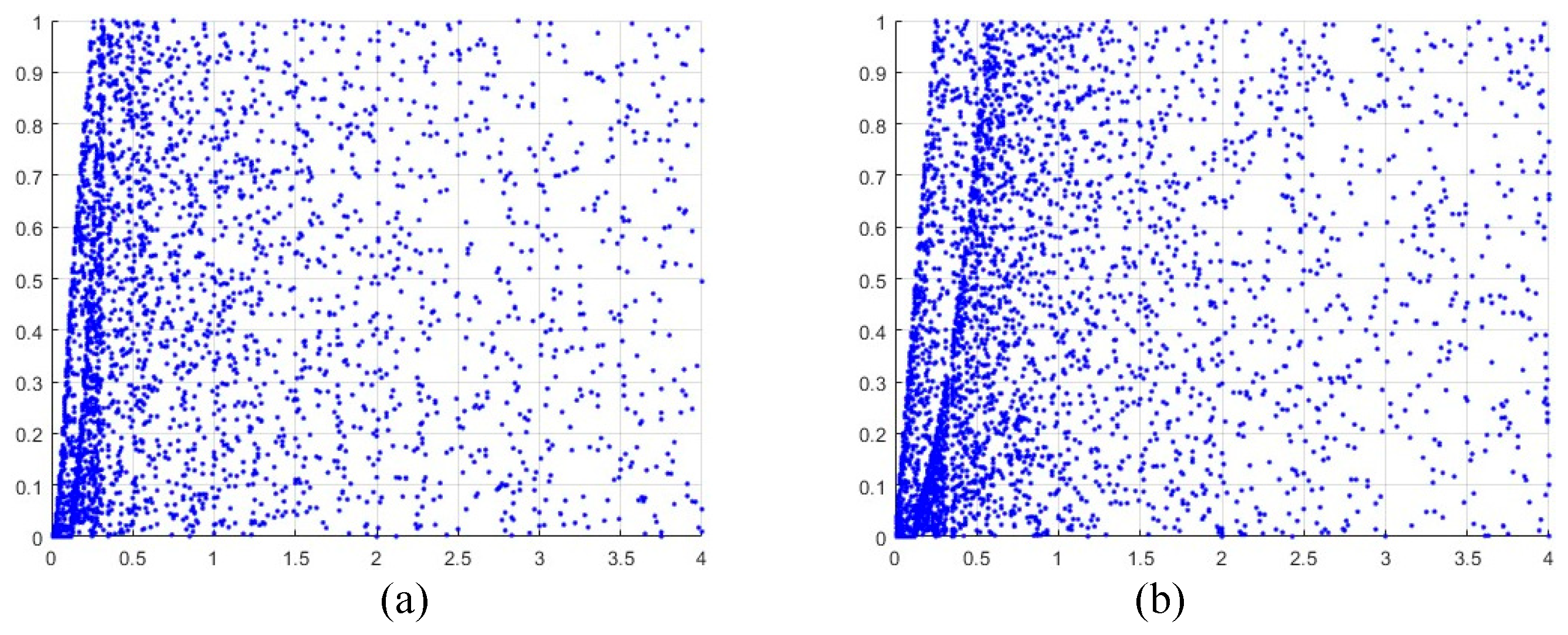
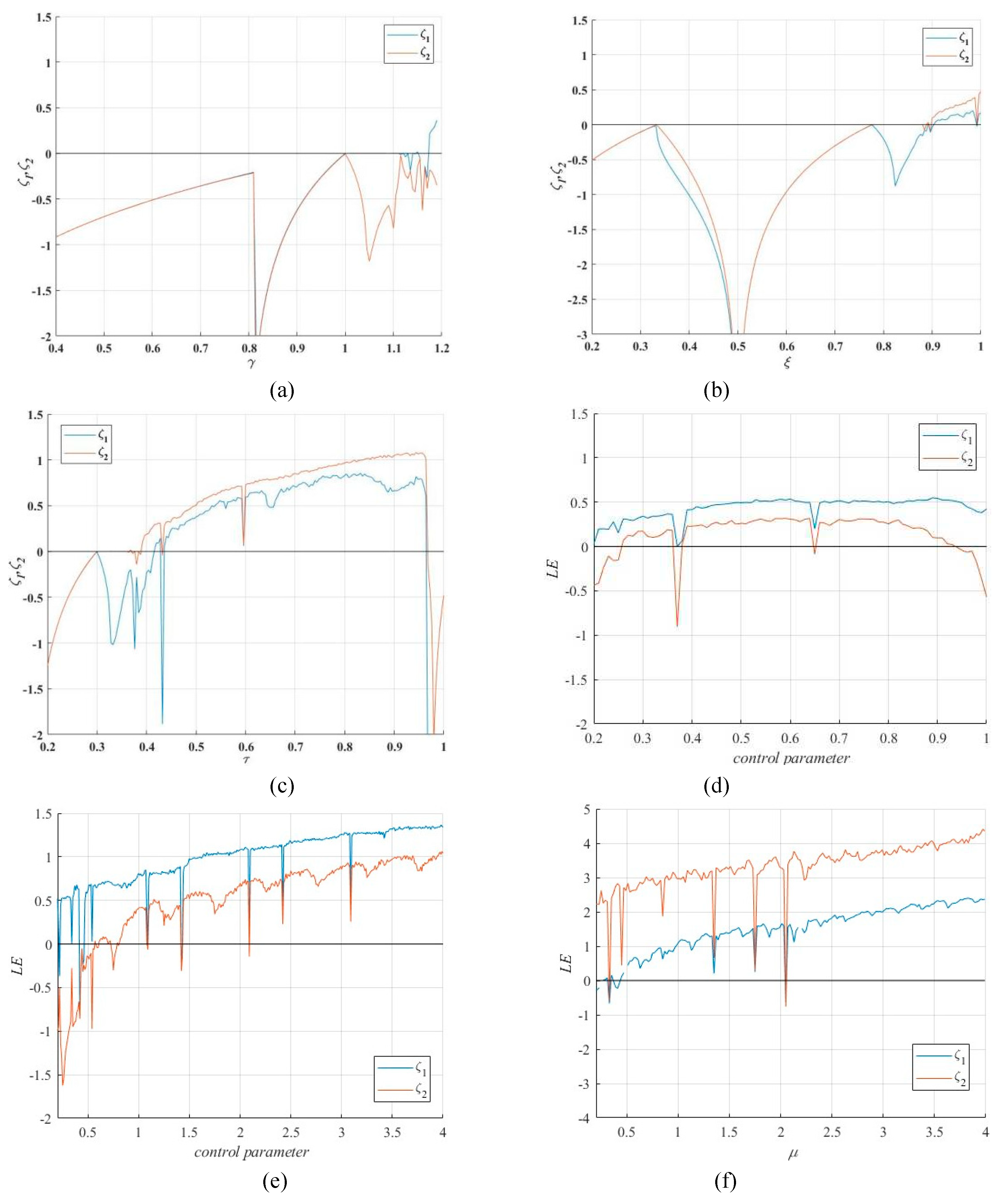
2.2.1. Bifurcation diagram
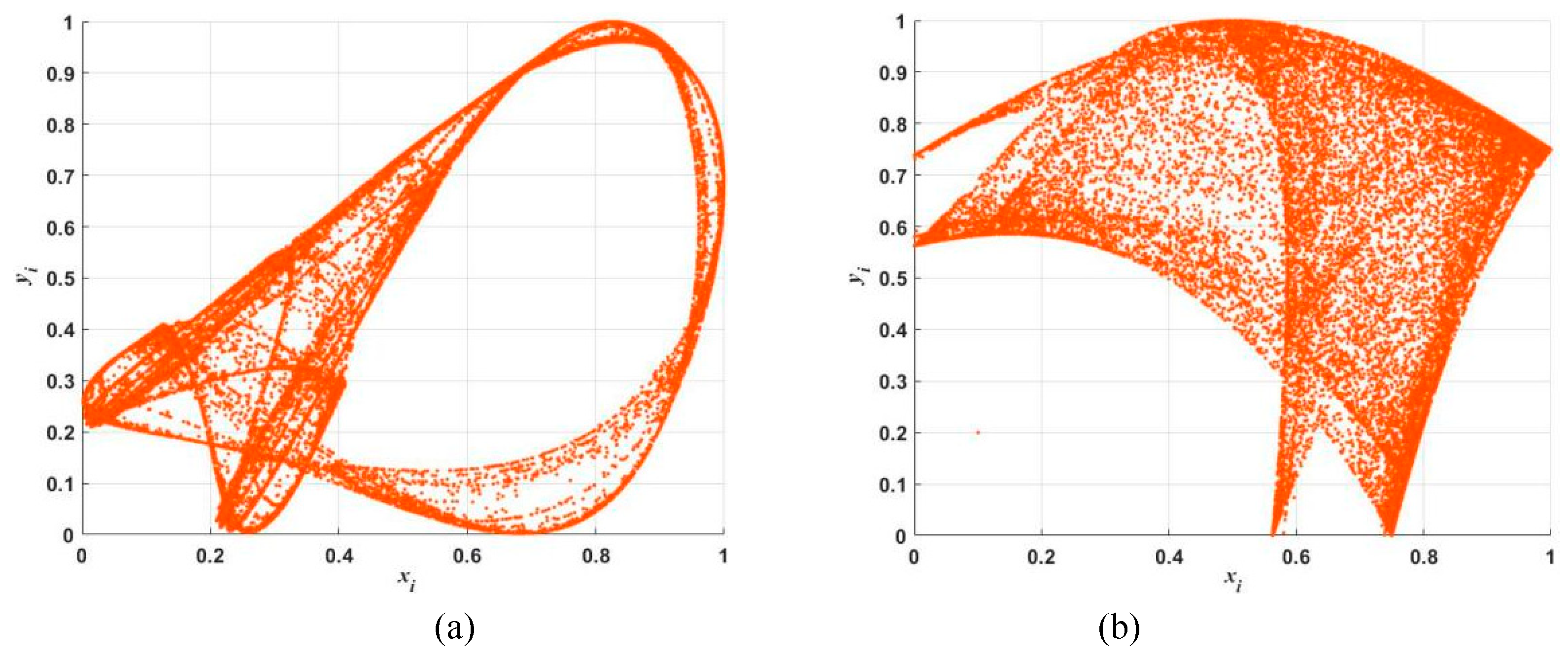
2.2.2. Chaos trajectory
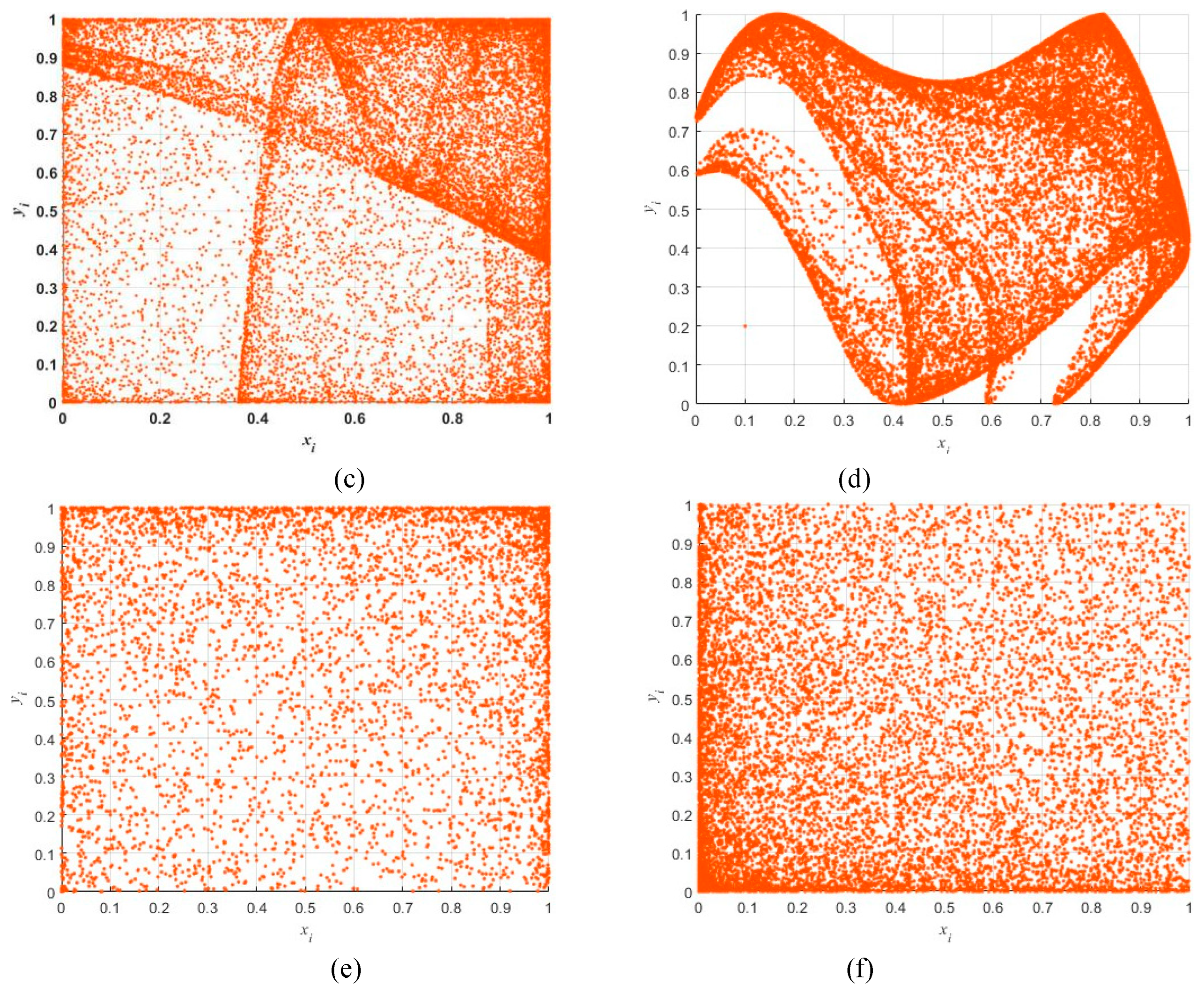
2.2.3. Lyapunov exponent
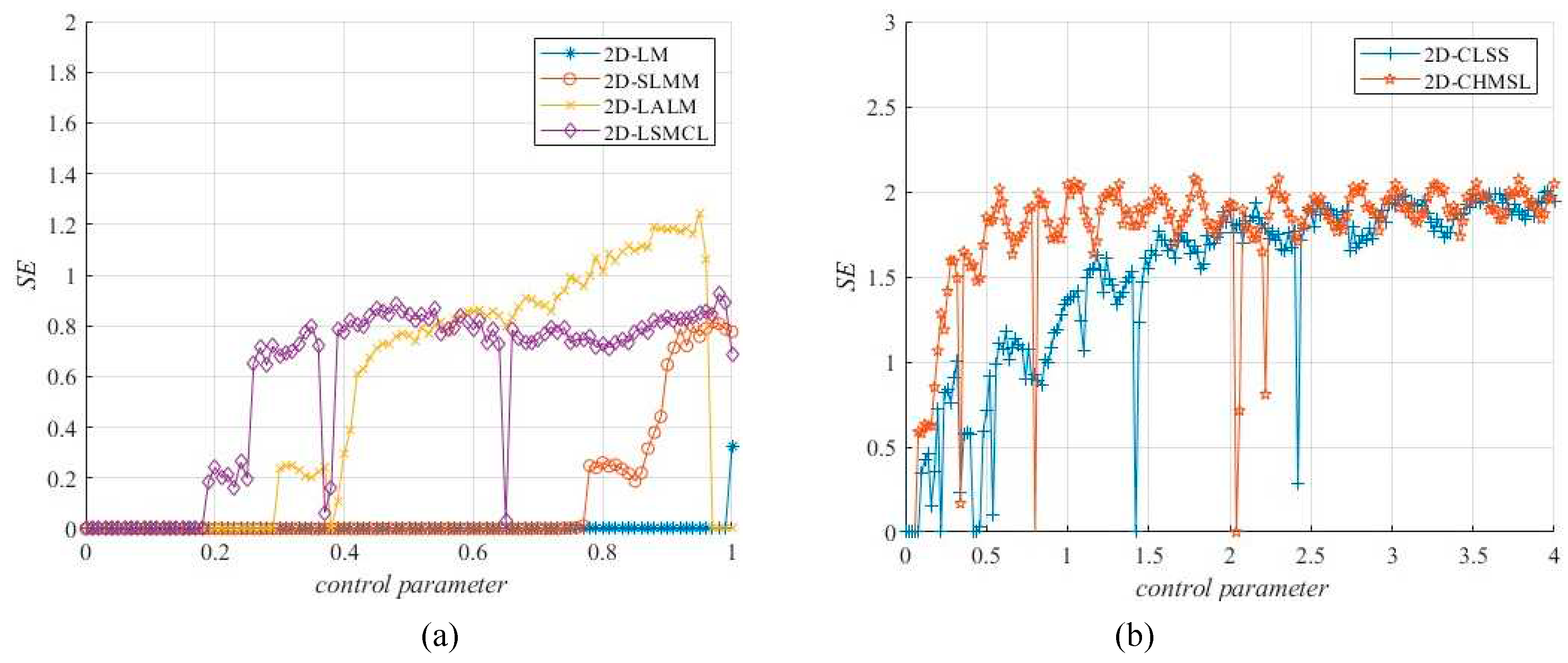
2.2.4. Sample entropy
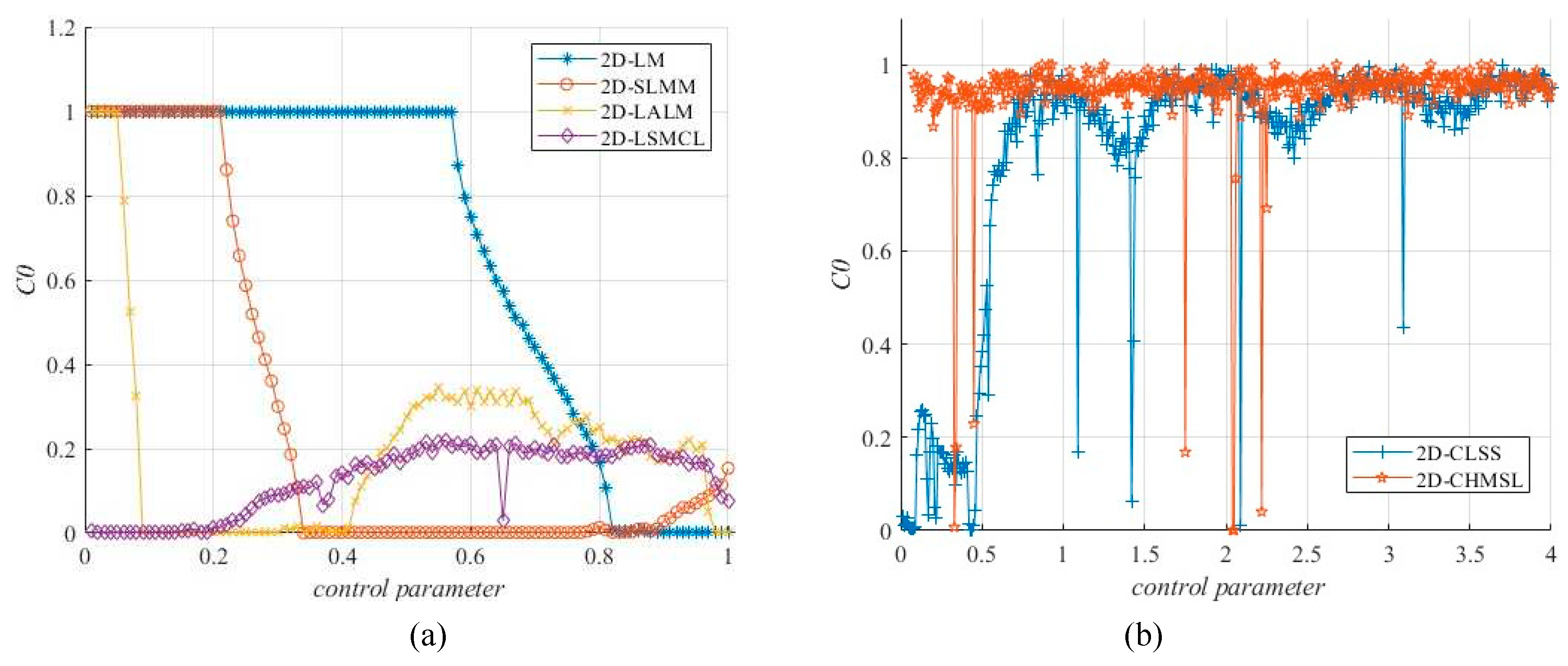
2.2.5. C0 complexity
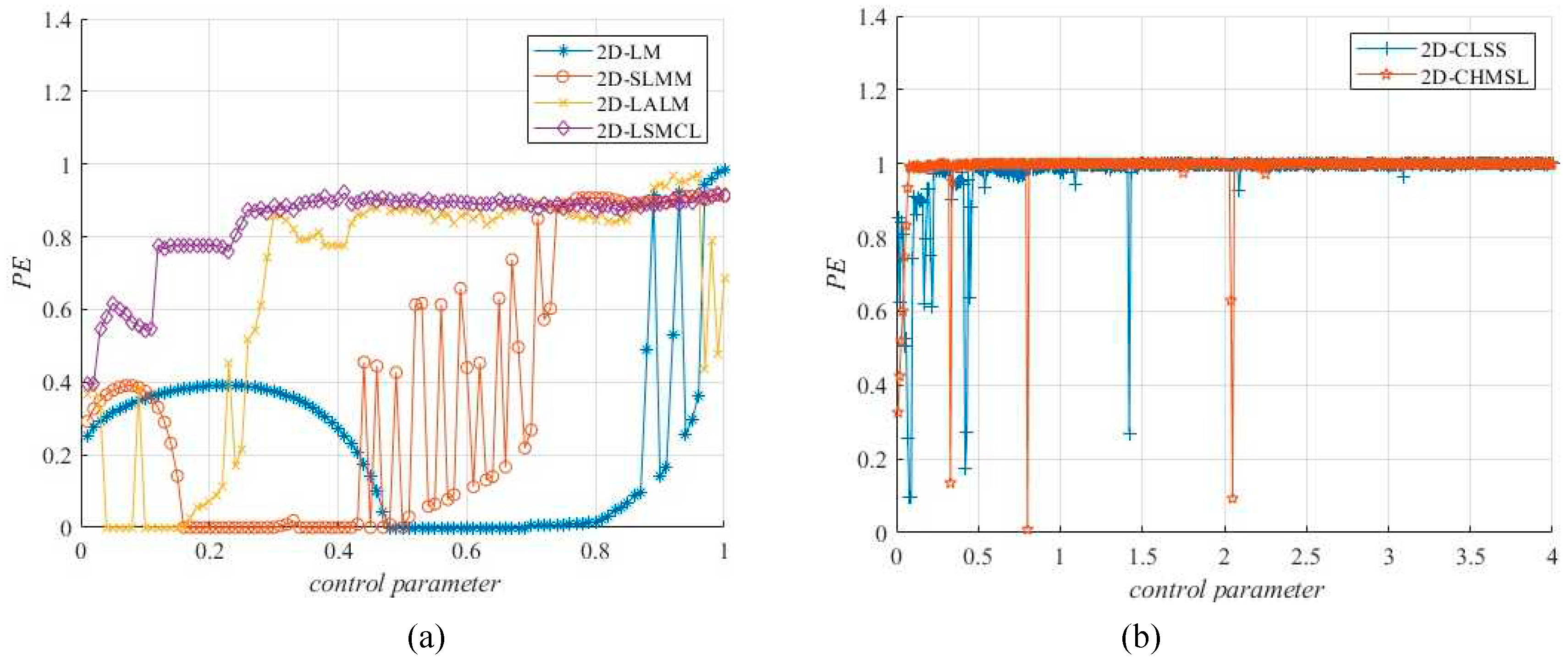
2.2.6. Permutation entropy
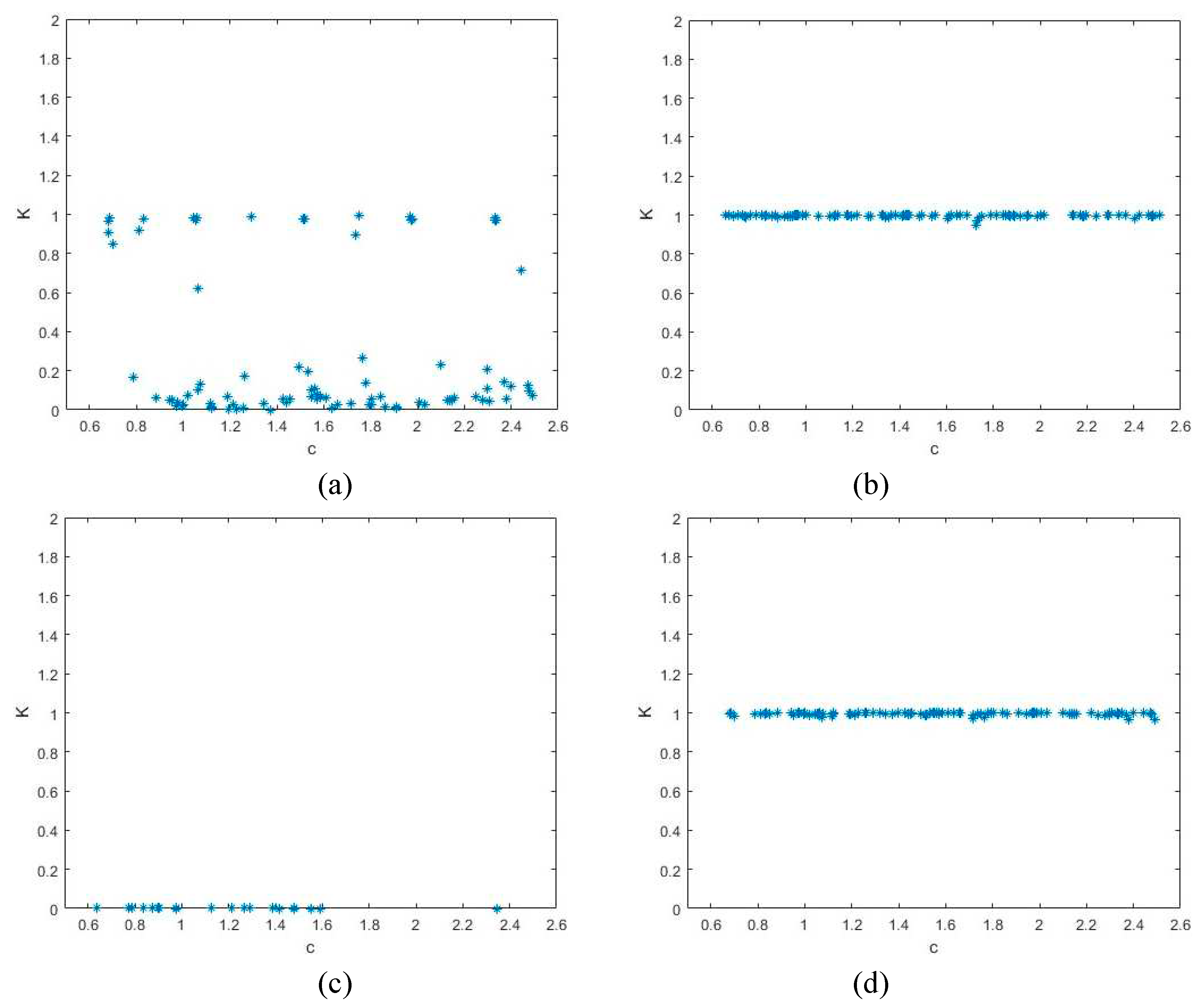
2.2.7. 0-1 Test
3. Related methods
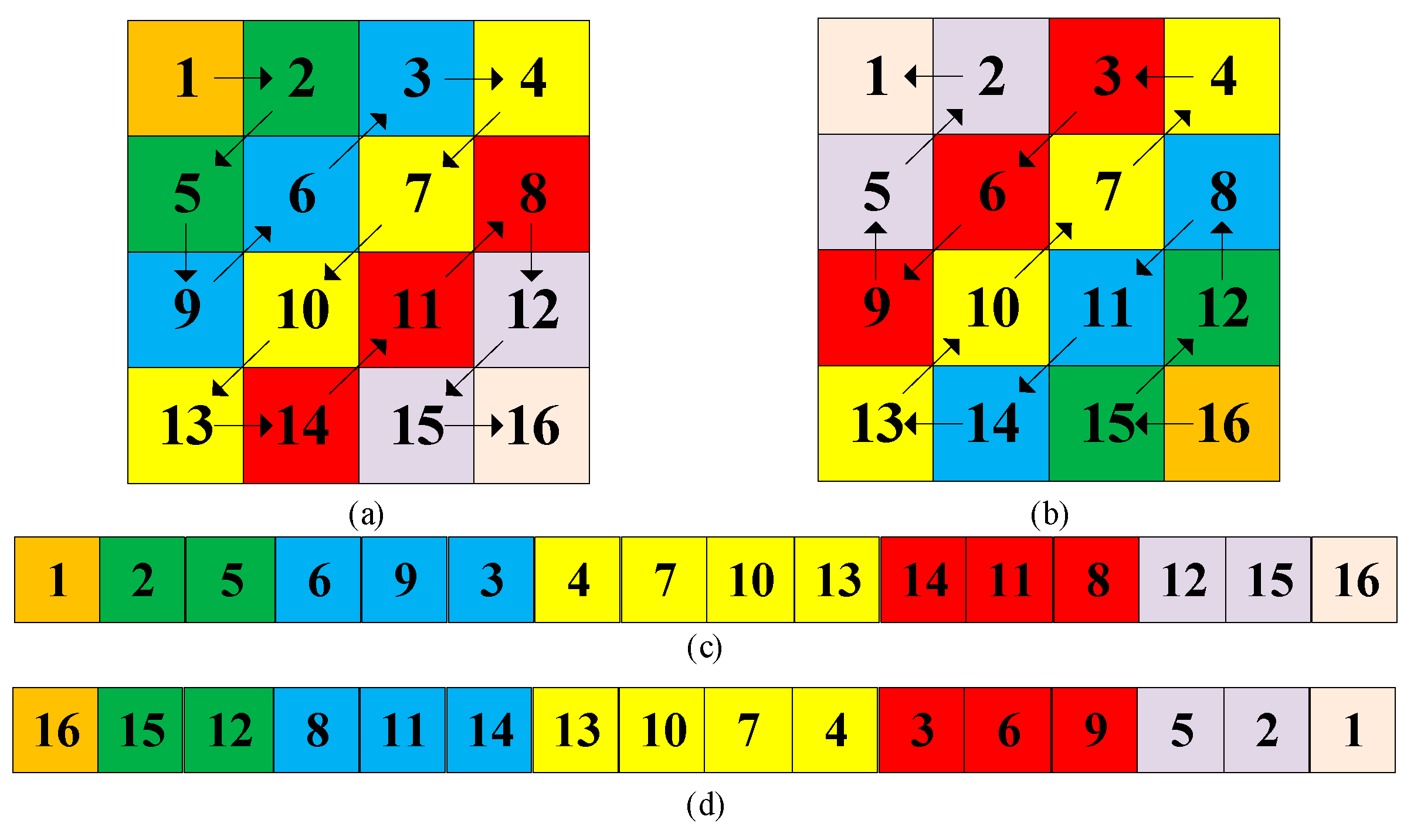
3.1. Zig-zag transform
3.2. Cross coupled pixels diffusion strategy
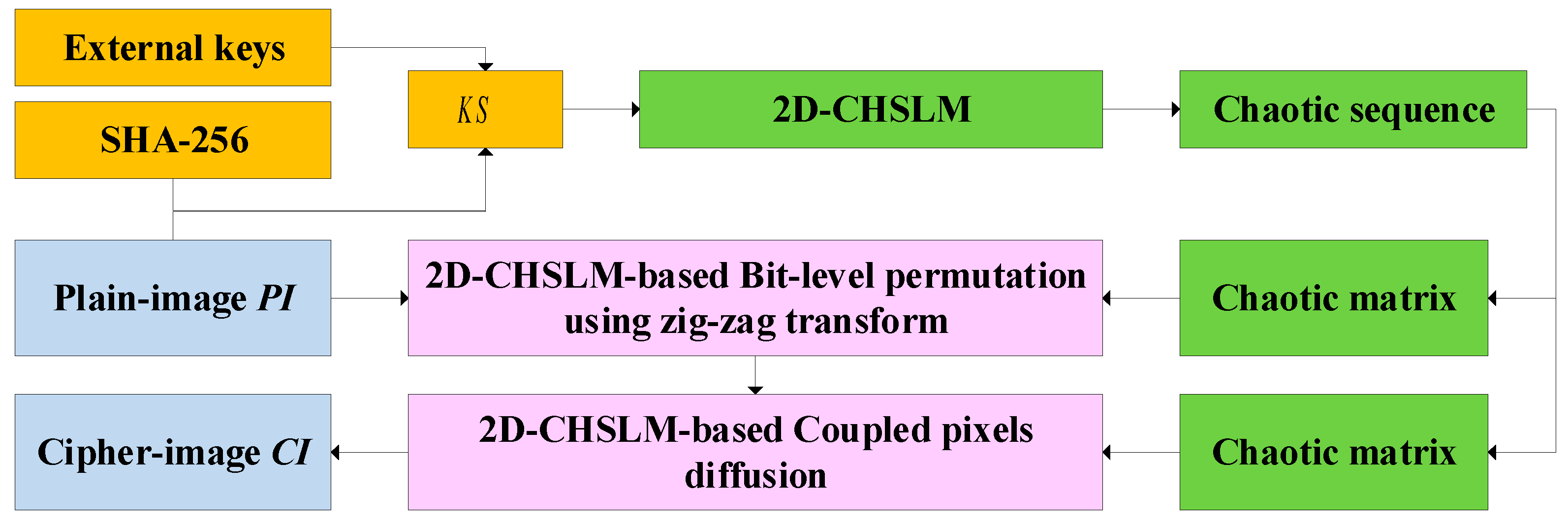
4. The bit-level IES based on 2D-CHSLM
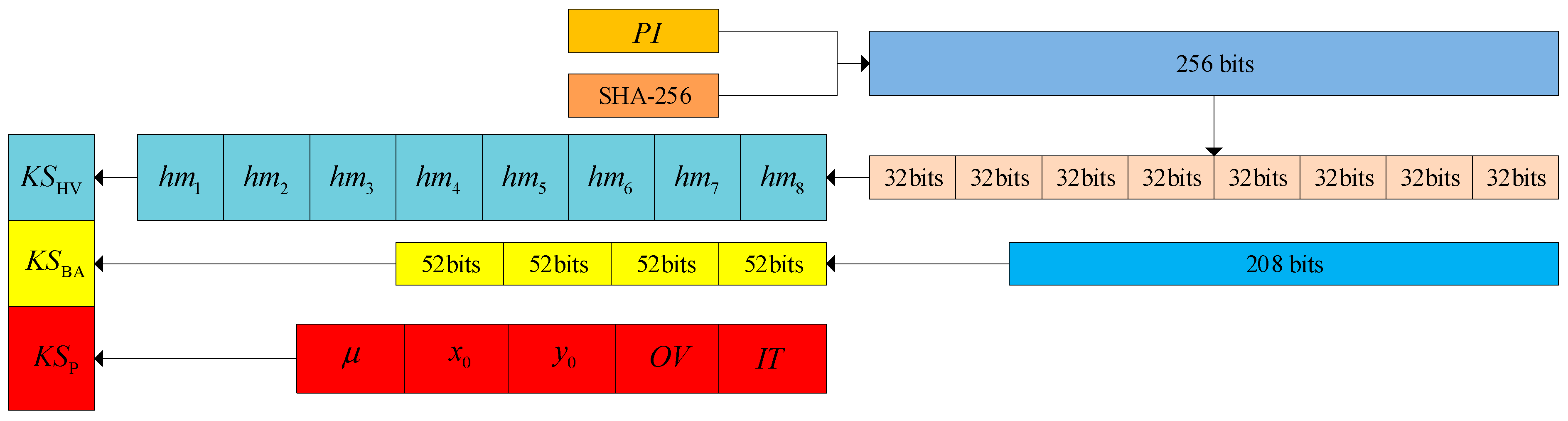
4.1. Initial state calculation
4.2. 2D-CHSLM-based bit-level permutation using zig-zag transform
4.3. 2D-CHSLM-based coupled pixel diffusion
5. Experimental results and security analyses
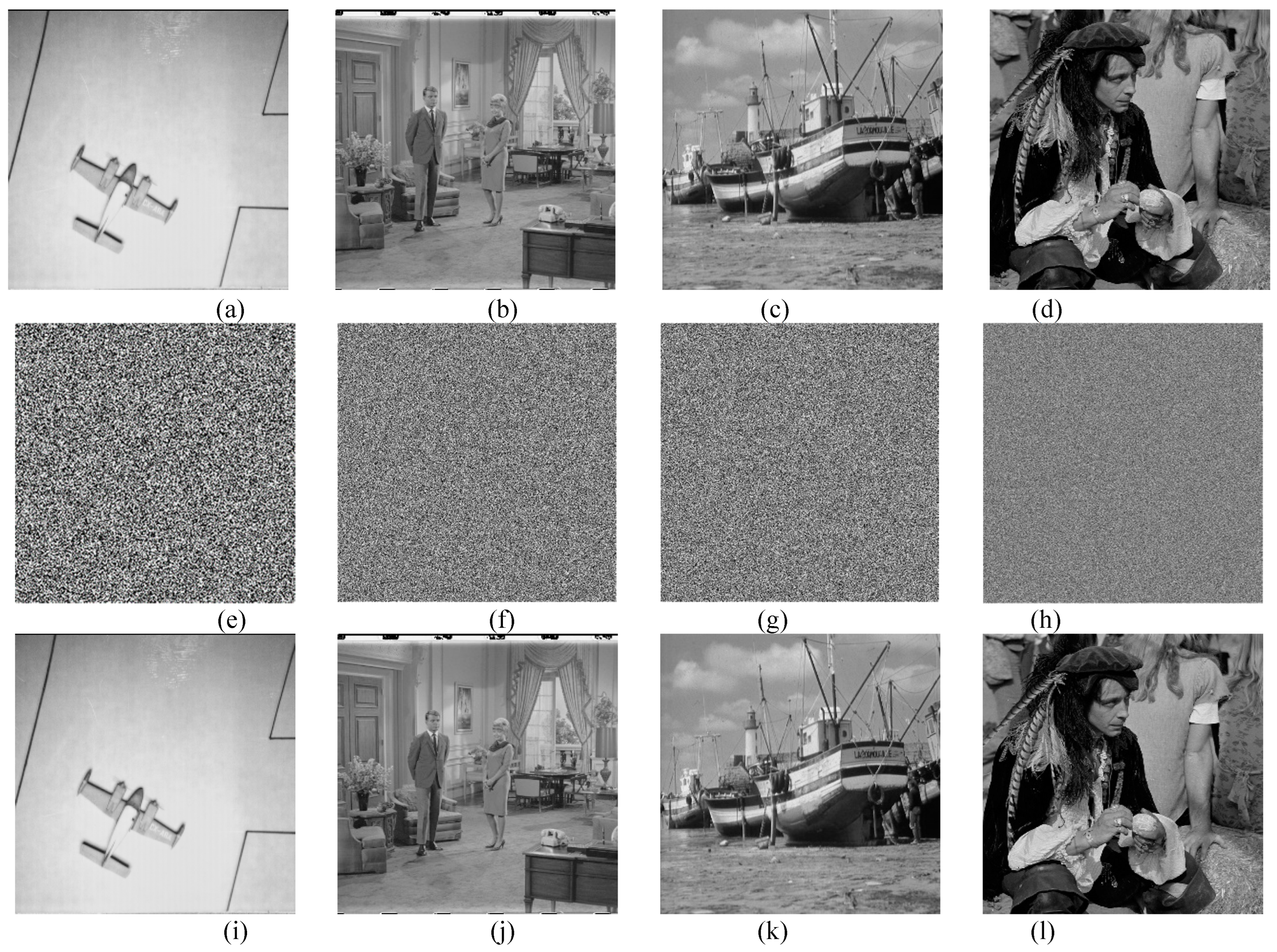
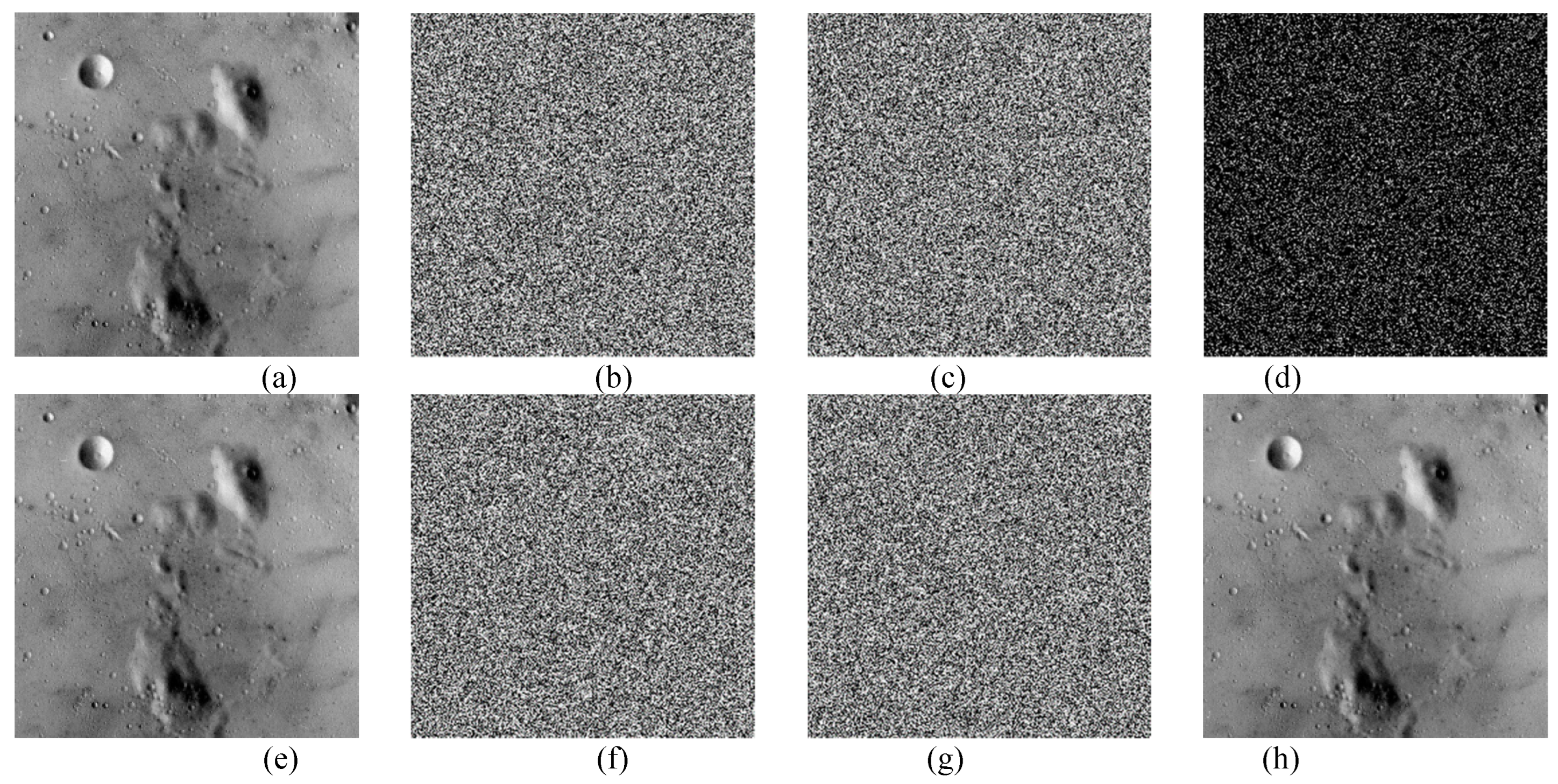
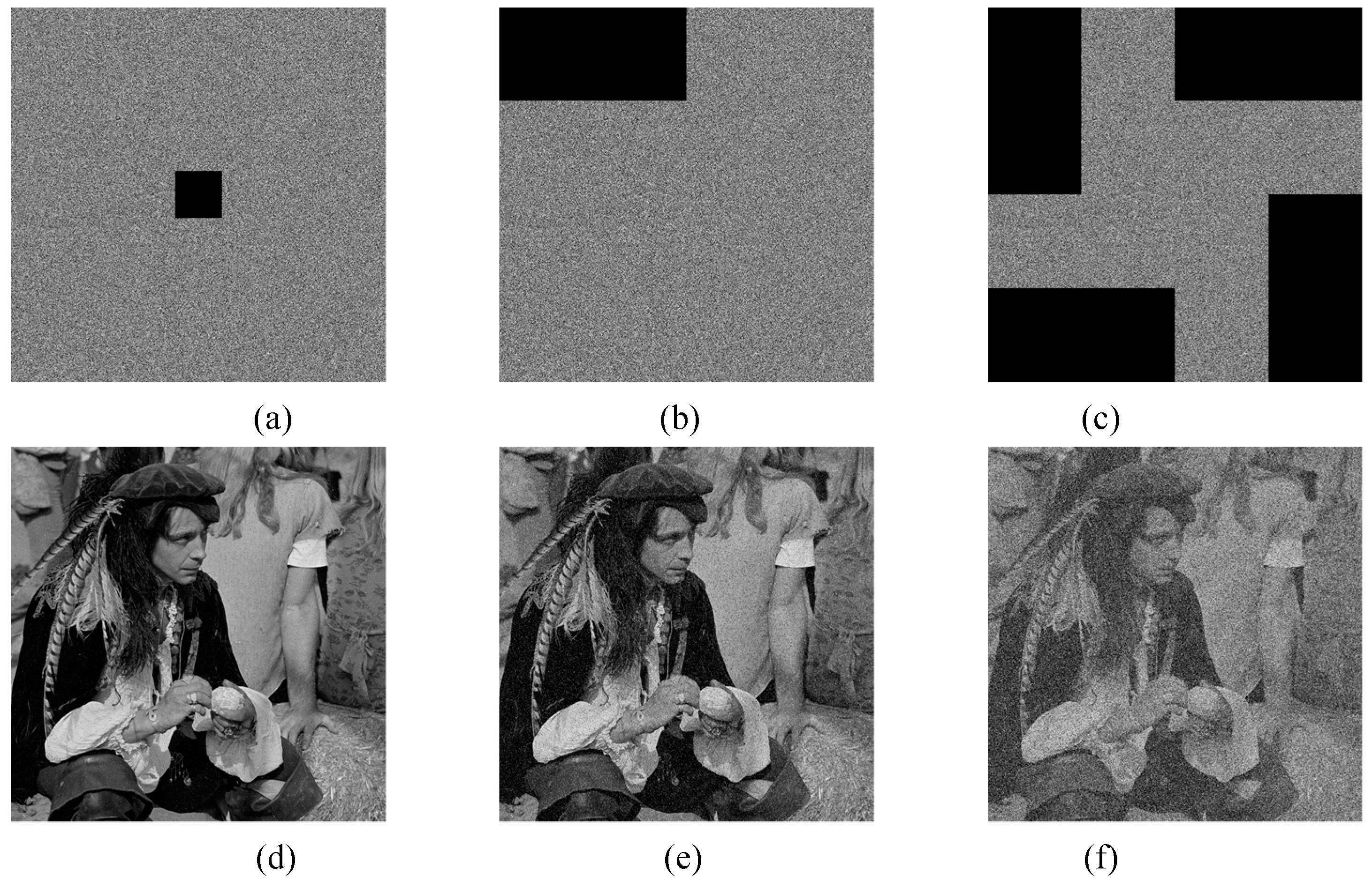
5.1. Visual analysis
5.2. Key space
5.3. Key sensitivity
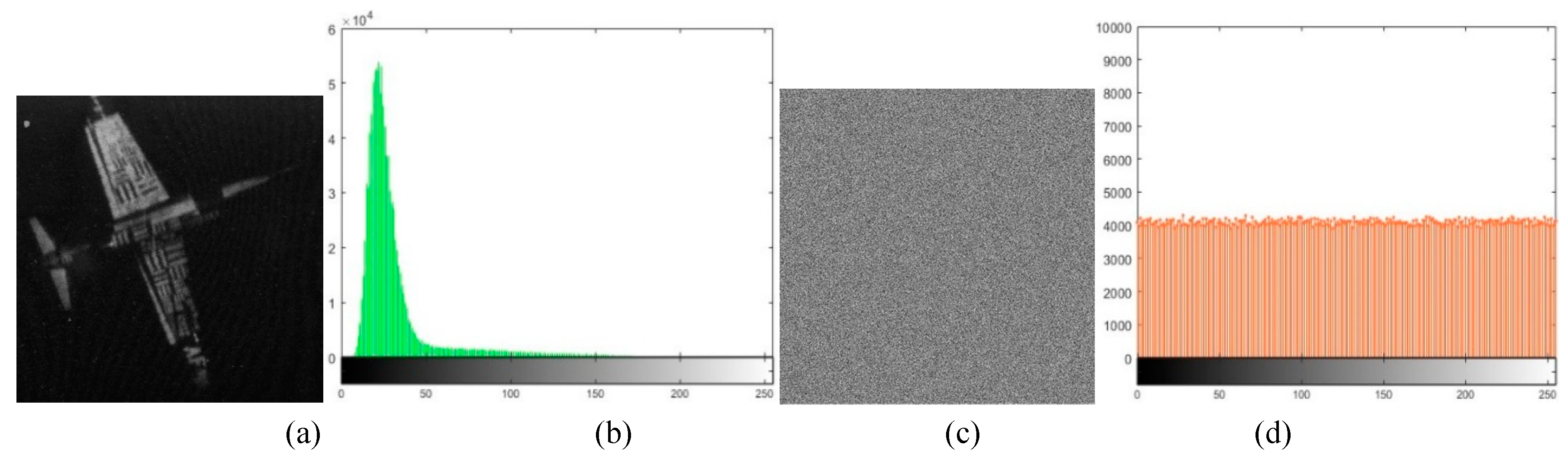
5.4. Histogram
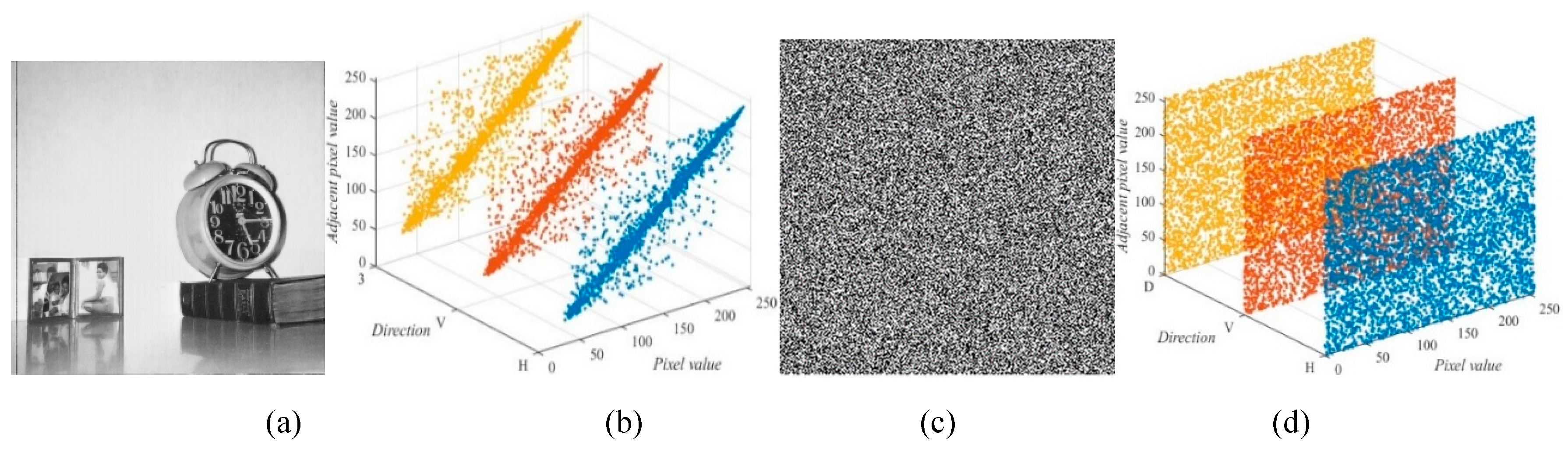
5.5. Correlation
5.6. Information entropy
5.7. Differential attack
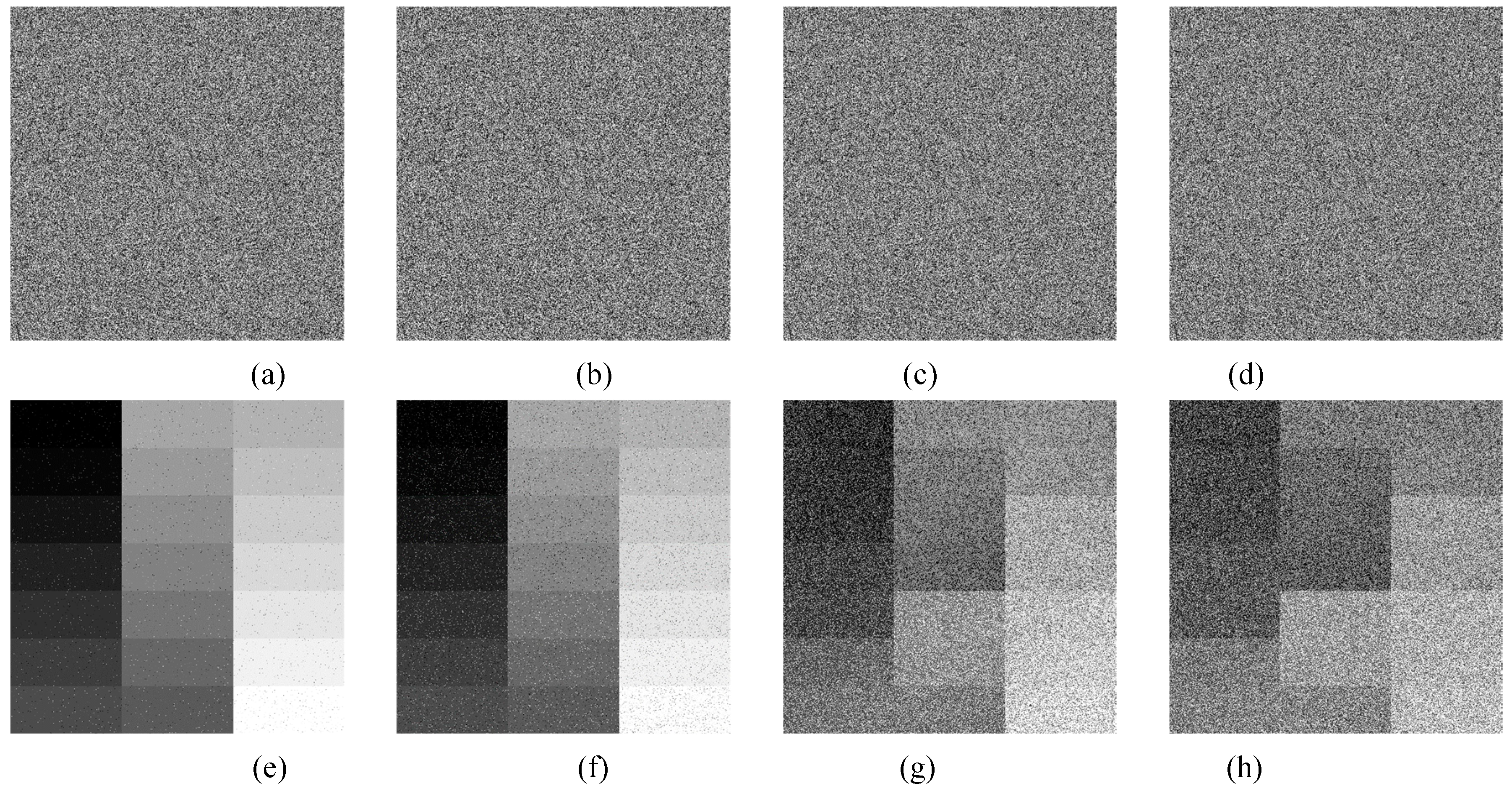
5.8. Noise and data loss attacks
5.8.1. Robust to noise attacks
5.8.2. Robust to data loss attacks
6. Conclusion
Acknowledgements
References
- Liu, H.; Liu, J.; Ma, C. Constructing dynamic strong S-Box using 3D chaotic map and application to image encryption. Multimed Tools Appl. 2023, 82, 23899–23914. [Google Scholar] [CrossRef]
- Xia, Z.; Wang, X.; Zhou, W.; Li, R.; Wang, C.; Zhang, C. Color medical image lossless watermarking using chaotic system and accurate quaternion polar harmonic transforms. Signal Process. 2019, 157, 108–118. [Google Scholar] [CrossRef]
- Wei, Z. Dynamical behaviors of a chaotic system with no equilibria. Phys Lett A 2011, 376, 102–108. [Google Scholar] [CrossRef]
- Peng, H.-H.; Xu, X.-M.; Yang, B.-C.; Yin, L.-Z. Implication of two-coupled differential Van der Pol duffing oscillator in weak signal detection. J Phys Soc Jpn 2016, 85, 044005. [Google Scholar] [CrossRef]
- Boriga, R.; Dascalescu, A.C.; Priescu, I. A new hyperchaotic map and its application in an image encryption scheme. Signal Process: Image Commun 2014, 29, 887–901. [Google Scholar] [CrossRef]
- Wang, M.; Wang, X.; Wang, C.; Zhou, S.; Xia, Z.; Li, Q. Color image encryption based on 2D enhanced hyperchaotic logistic-sine map and two-way Josephus traversing. Digit. Signal Process. 2023, 132, 103818. [Google Scholar] [CrossRef]
- Alsubaei, F.S.; Alneil, A.A.; Mohamed, A.; Hilal, A.M. Block-Scrambling-Based Encryption with Deep-Learning-Driven Remote Sensing Image Classification. Remote Sens. 2023, 15, 1022. [Google Scholar] [CrossRef]
- Hu, Y.; Nan, L. Image encryption algorithm based on 1D-SFACF with cross-cyclic shift and adaptive diffusion. Phys Scr. 2023, 98, 055209. [Google Scholar] [CrossRef]
- Yan, X.; Wang, X.; Xian, Y. Chaotic image encryption algorithm based on arithmetic sequence scrambling model and DNA encoding operation. Multimed Tools Appl. 2022, 80, 10949–10983. [Google Scholar] [CrossRef]
- Wang, M.; Wang, X.; Wang, C.; Xia, Z.; Zhou, S. Novel Image Compression-Then-Encryption Scheme Based on 2D Cross Coupled Map Lattice and Compressive Sensing. Multimed Tools Appl. 2023, 83, 1891–1917. [Google Scholar] [CrossRef]
- Wu, Y.; Yang, G.; Jin, H.; Noonan, J.P. Image encryption using the two-dimensional logistic chaotic map. J Electron Imaging. 2012, 21, 013014. [Google Scholar] [CrossRef]
- Hua, Z.; Zhou, Y.; Pun, C.M.; Chen, C. 2D Sine Logistic modulation map for image encryption. Inf Sci. 2014, 297, 80–94. [Google Scholar] [CrossRef]
- Sharma, M. Image encryption based on a new 2D logistic adjusted logistic map. Multimed. Tools Appl. 2020, 79, 355–374. [Google Scholar] [CrossRef]
- Zhu, H.; Zhao, Y.; Song, Y. 2D Logistic-Modulated-Sine-Coupling-Logistic Chaotic Map for Image Encryption. IEEE Access 2019, 7, 14081–14098. [Google Scholar] [CrossRef]
- Teng, L.; Wang, X.; Xian, Y. Image encryption algorithm based on 2D-CLSS hyperchaotic map using simultaneous permutation and diffusion. Inf Sci. 2022, 605, 71–85. [Google Scholar] [CrossRef]
- Matthews, R. On the derivation of a chaotic encryption algorithm. Cryptologia 1989, 13, 29–42. [Google Scholar] [CrossRef]
- Wang, M.; Wang, X.; Zhao, T.; Zhang, C.; Xia, Z.; Yao, N. Spatiotemporal chaos in improved Cross Coupled Map Lattice and its application in a bit-level image encryption scheme. Inf Sci. 2021, 544, 1–24. [Google Scholar] [CrossRef]
- Zhang, Z.; Tang, J.; Ni, H.; Huang, T. Image adaptive encryption algorithm using a novel 2D chaotic system. Nonlinear Dyn. 2023, 111, 10629–10652. [Google Scholar] [CrossRef]
- Zhou, S.; Zhao, Z.; Wang, X. Novel chaotic colour image cryptosystem with deep learning. Chaos Soliton Fract. 2022, 161, 112380. [Google Scholar] [CrossRef]
- Lai, Q.; Liu, Y. A cross-channel color image encryption algorithm using two-dimensional hyperchaotic map. Expert Syst Appl. 2023, 223, 119923. [Google Scholar] [CrossRef]
- Peng, F.; Zhang, X.; Lin, Z.; Long, M. A tunable selective encryption scheme for H.265/HEVC based on chroma IPM and coefficient scrambling. IEEE Trans Circuits Syst Video Technol 2020, 30, 2765–2780. [Google Scholar] [CrossRef]
- Wu, Y.; Zhou, Y.; Saveriades, G.; Agaian, S.; Noonan, J.P.; Natarajan, P. Local Shannon entropy measure with statistical tests for image randomness. Inf Sci. 2022, 222, 323–342. [Google Scholar] [CrossRef]
- Tang, Z.; Song, J.; Zhang, X.; Sun, R. Multiple-image encryption with bit-plane decomposition and chaotic maps. Opt Lasers Eng. 2016, 80, 1–11. [Google Scholar] [CrossRef]
- Wang, M.; Wang, X.; Wang, C.; Xia, Z.; Zhao, H.; Gao, S.; Zhou, S.; Yao, N. Spatiotemporal chaos in cross coupled map lattice with dynamic coupling coefficient and its application in bit-level color image encryption. Chaos Soliton Fract. 2020, 139, 110028. [Google Scholar] [CrossRef]
- Wang, M.; Liu, H.; Zhao, M. Bit-level image encryption algorithm based on random-time S-Box substitution. Eur. Phys. J. Spec. Top. 2022, 231, 3225–3237. [Google Scholar] [CrossRef]
- Li, J.; Wang, J.; Di, X. Image encryption algorithm based on bit-level permutation and "Feistel-like network" diffusion. Multimed Tools Appl. 2022, 81, 44335–44362. [Google Scholar] [CrossRef]
- Devipriya, M.; Brindha, M. Image encryption using modified perfect shuffle-based bit level permutation and learning with errors based diffusion for IoT. Comput Electr Eng, 2022, 100, 107954. [Google Scholar]
- Luo, J.; Xu, X.; Ding, Y.; Yuan, Y.; Yang, B.; Sun, K.; Yin, L. Application of a memristor-based oscillator to weak signal detection. Eur. Phys. J. Plus, 2018, 133, 239. [Google Scholar] [CrossRef]
- ul Haq, T.; Shah, T. 4D mixed chaotic system and its application to RGB image encryption using substitution diffusion. J Inf Secur Appl, 2021, 61, 102931. [Google Scholar] [CrossRef]
- Wang, X.; Guan, N. 2D sine-logistic-tent-coupling map for image encryption. J. Ambient. Intell. Humaniz. Comput, 2022, 14, 13399–13419. [Google Scholar] [CrossRef]
- Wang, X.; Guan, N.; Yang, J. Image encryption algorithm with random scrambling based on one-dimensional logistic self-embedding chaotic map. Chaos Soliton Fract. 2021, 150, 111117. [Google Scholar] [CrossRef]
- Li, Y.; Li, C.; Liu, S.; Hua, Z.; Jiang, H. A 2-D conditional symmetric hyperchaotic map with complete control. Nonlinear Dyn. 2022, 109, 1155–1165. [Google Scholar] [CrossRef]
- Hu, X.; Jiang, D.; Ahmad, M.; Tsafack, N.; Zhu, L.; Zheng, M. Novel 3-D hyperchaotic map with hidden attractor and its application in meaningful image encryption. Nonlinear Dyn. 2023, 111, 19487–19512. [Google Scholar] [CrossRef]
- Richman, J.; Moorman, J. Physiological time-series analysis using approximate entropy and sample entropy. American Journal of Physiology-Heart and Circulatory Physiology, 2000, 278, H2039–H2049. [Google Scholar] [CrossRef] [PubMed]
- Gao, X. Image encryption algorithm based on 2D hyperchaotic map. Opt. Laser Technol. 2021, 142, 107252. [Google Scholar] [CrossRef]
- Huo, D.; Zhu, Z.; Wei, L.; Han, C.; Zhou, X. A visually secure image encryption scheme based on compressive sensing. Opt. Commun. 2021, 492, 126976. [Google Scholar] [CrossRef]
- Mao, N.; Tong, X.; Zhang, M.; Wang, Z. Real-time image encryption algorithm based on combined chaotic map and optimized lifting wavelet transform. :J Real-Time Image Pr. 2023, 20, 35. [Google Scholar] [CrossRef]
- Cao, C.; Sun, K.; Liu, W. A novel bit-level image encryption algorithm based on 2D-LICM hyperchaotic map. Signal Process. 2018, 143, 122–133. [Google Scholar] [CrossRef]
- Parida, P.; Pradhan Pradhan, C.; Gao, X.; Roy, D.S.; Barik, R.K. Image encryption and authentication with elliptic curve cryptography and multidimensional chaotic maps. IEEE Access, 2021, 9, 76191–76204. [Google Scholar] [CrossRef]
- Wang, M.; Wang, X.; Zhang, Y.; Zhou, S.; Zhao, T.; Yao, N. A novel chaotic system and its application in a color image cryptosystem. Opt Lasers Eng. 2019, 121, 479–494. [Google Scholar] [CrossRef]
- Wang, X.; Chen, X.; Zhao, M. A new two-dimensional sine-coupled-logistic map and its application in image encryption. Multimed Tools Appl. 2023, 82, 35719–35755. [Google Scholar] [CrossRef]
- Wang, X.; Zhao, M. A new spatiotemporal chaos model and its application in bit-level image encryption. Multimed Tools Appl. 2023, 83, 10481–10502. [Google Scholar] [CrossRef]
- Liang, Q.; Zhu, C. A new one-dimensional chaotic map for image encryption scheme based on random DNA coding. Opt. Laser Technol. 2023, 160, 109033. [Google Scholar] [CrossRef]
- Wu, Y.; Noonan, J.P.; Agaian, S. NPCR and UACI randomness tests for image encryption. Cyber J. Multidiscipl. J. Sci. Technol. J. Sel. Areas Telecommun. 2011, 1, 31–38. [Google Scholar]
| Test image | Size | P-values | Decision (H=0 or 1) | ||
| 5.1.09 | 253.2188 | 0.1940 | 0 | Accepted | |
| 5.1.10 | 230.9609 | 0.7099 | 0 | Accepted | |
| 5.1.11 | 218.9922 | 0.6540 | 0 | Accepted | |
| 5.1.12 | 240.5078 | 0.3791 | 0 | Accepted | |
| 5.1.14 | 240.1172 | 0.1339 | 0 | Accepted | |
| 5.2.08 | 269.8145 | 0.7031 | 0 | Accepted | |
| 5.2.09 | 236.5098 | 0.2511 | 0 | Accepted | |
| 5.2.10 | 276.7363 | 0.4475 | 0 | Accepted | |
| 7.1.01 | 268.9434 | 0.5625 | 0 | Accepted | |
| 7.1.02 | 315.0625 | 0.2259 | 0 | Accepted | |
| 7.1.03 | 242.1719 | 0.0453 | 0 | Accepted | |
| 7.1.04 | 235.498 | 0.9711 | 0 | Accepted | |
| 7.1.05 | 292.6602 | 0.5090 | 0 | Accepted | |
| 7.1.06 | 237.9414 | 0.2222 | 0 | Accepted | |
| 7.1.07 | 311.0371 | 0.2414 | 0 | Accepted | |
| 7.1.08 | 225.7656 | 0.2992 | 0 | Accepted | |
| 7.1.09 | 302.6230 | 0.3242 | 0 | Accepted | |
| 7.1.10 | 225.2598 | 0.2378 | 0 | Accepted | |
| boat.512 | 267.3926 | 0.1914 | 0 | Accepted | |
| gray21.512 | 266.9336 | 0.2579 | 0 | Accepted | |
| 5.3.01 | 337.5430 | 0.0850 | 0 | Accepted | |
| 5.3.02 | 316.2832 | 0.3871 | 0 | Accepted | |
| 7.2.01 | 413.6880 | 0.1055 | 0 | Accepted |
| Test image | |||||
| 5.1.09 | 5441.8550 | 5485.7893 | 5485.2374 | 5448.9941 | 5432.9961 |
| 5.1.10 | 5447.6739 | 5493.1078 | 5457.2804 | 5456.3162 | 5447.6196 |
| 5.1.11 | 5496.4997 | 5449.3551 | 5460.8342 | 5472.1545 | 5493.2718 |
| 5.1.12 | 5458.7555 | 5453.2077 | 5466.7498 | 5480.9086 | 5460.4149 |
| 5.1.14 | 5459.1291 | 5442.7278 | 5477.9664 | 5457.8505 | 5459.0039 |
| 5.2.08 | 5459.5898 | 5459.0095 | 5457.9681 | 5454.6884 | 5459.5509 |
| 5.2.09 | 5452.3726 | 5449.8282 | 5466.6573 | 5458.529 | 5452.3228 |
| 5.2.10 | 5472.2117 | 5468.2702 | 5463.4145 | 5432.299 | 5472.0094 |
| 7.1.01 | 5474.1376 | 5460.8777 | 5475.4914 | 5462.9336 | 5474.935 |
| 7.1.02 | 5467.3954 | 5474.5296 | 5476.7792 | 5470.1655 | 5467.7073 |
| 7.1.03 | 5453.6022 | 5451.4377 | 5454.1955 | 5449.8652 | 5452.765 |
| 7.1.04 | 5474.5494 | 5459.1821 | 5446.8977 | 5456.0021 | 5472.9866 |
| 7.1.05 | 5462.1370 | 5446.5362 | 5460.1792 | 5460.415 | 5461.4496 |
| 7.1.06 | 5467.9458 | 5457.9691 | 5455.3284 | 5451.521 | 5467.192 |
| 7.1.07 | 5474.8764 | 5455.9308 | 5465.7357 | 5466.7098 | 5474.9154 |
| 7.1.08 | 5446.7922 | 5467.8586 | 5455.8798 | 5462.2921 | 5447.1123 |
| 7.1.09 | 5455.3019 | 5456.5913 | 5470.0106 | 5465.4739 | 5454.0027 |
| 7.1.10 | 5467.5594 | 5479.9682 | 5477.0743 | 5451.5287 | 5468.2064 |
| boat.512 | 5453.1570 | 5456.1997 | 5462.1926 | 5469.9872 | 5451.3742 |
| gray21.512 | 5448.9852 | 5448.5082 | 5455.3162 | 5459.1326 | 5448.9232 |
| 5.3.01 | 5463.5445 | 5461.2454 | 5461.4147 | 5458.3164 | 5463.4359 |
| 5.3.02 | 5469.0697 | 5462.018 | 5467.0965 | 5456.1629 | 5469.5559 |
| 7.2.01 | 5459.3065 | 5459.6969 | 5458.9651 | 5464.6389 | 5459.9138 |
| Test image | ||||
| 5.1.09 | 0.8 | 0.79 | 0.13 | 0.16 |
| 5.1.10 | 0.83 | 0.18 | 0.16 | 0,001 |
| 5.1.11 | 0.87 | 0.65 | 0.44 | 0.06 |
| 5.1.12 | 0.1 | 0.15 | 0.4 | 0.03 |
| 5.1.14 | 0.3 | 0.34 | 0.02 | 0.002 |
| 5.2.08 | 0.01 | 0.03 | 0.09 | 0.001 |
| 5.2.09 | 0.05 | 0.26 | 0.11 | 0.001 |
| 5.2.10 | 0.07 | 0.16 | 0.73 | 0.004 |
| 7.1.01 | 0.24 | 0.02 | 0.21 | 0.01 |
| 7.1.02 | 0.13 | 0.17 | 0.05 | 0.01 |
| 7.1.03 | 0.04 | 0.01 | 0.07 | 0.02 |
| 7.1.04 | 0.28 | 0.51 | 0.34 | 0.03 |
| 7.1.05 | 0.29 | 0.04 | 0.03 | 0.01 |
| 7.1.06 | 0.18 | 0.23 | 0.3 | 0.01 |
| 7.1.07 | 0.35 | 0.17 | 0.15 | 0.001 |
| 7.1.08 | 0.39 | 0.17 | 0.28 | 0.01 |
| 7.1.09 | 0.02 | 0.27 | 0.19 | 0.02 |
| 7.1.10 | 0.23 | 0.17 | 0.29 | 0.01 |
| boat.512 | 0.06 | 0.17 | 0.31 | 0.03 |
| gray21.512 | 0.01 | 0.12 | 0.19 | 0.001 |
| 5.3.01 | 0.04 | 0.04 | 0.1 | 0.002 |
| 5.3.02 | 0.13 | 0.04 | 0.24 | 0.01 |
| 7.2.01 | 0.01 | 0.01 | 0.1 | 0.01 |
| Mean | 0.24 | 0.20 | 0.21 | 0.02 |
| Test image | 2D-CHSLM-IES | Ref. [41] | |||||||
| Plain-image | Cipher-image | Cipher-image | |||||||
| H | V | D | H | V | D | H | V | D | |
| 5.1.09 | 0.9094 | 0.9053 | 0.8989 | 0.003 | -0.0029 | -0.0017 | 0.0162 | -0.0139 | 0.0025 |
| 5.1.10 | 0.8242 | 0.8047 | 0.7928 | 0.0012 | -0.0034 | 0.0016 | -0.0258 | 0.0041 | 0.0009 |
| 5.1.11 | 0.8898 | 0.8512 | 0.9212 | 0.001 | 0.0029 | 0.0019 | -0.0016 | -0.0012 | 0.0141 |
| 5.1.12 | 0.9485 | 0.9498 | 0.9308 | 0.0031 | -0.0033 | -0.0018 | -0.0114 | -0.0097 | 0.0034 |
| 5.1.13 | 0.7512 | 0.7549 | 0.7874 | 0.0042 | 0.0048 | 0.0015 | 0.0070 | 0.0100 | -0.0097 |
| 5.1.14 | 0.8583 | 0.8597 | 0.856 | -0.0012 | 0.0011 | -0.004 | -0.0176 | -0.0054 | -0.0196 |
| 5.2.08 | 0.8387 | 0.8374 | 0.8813 | -0.0012 | -0.0032 | -0.002 | -0.0028 | 0.0046 | 0.0124 |
| 5.2.09 | 0.7839 | 0.8213 | 0.817 | -0.001 | -0.0016 | 0.0031 | -0.0172 | -0.0091 | -0.0178 |
| 5.2.10 | 0.8824 | 0.9038 | 0.901 | -0.0028 | -0.0011 | 0.0036 | -0.0190 | 0.0005 | -0.0050 |
| 7.1.01 | 0.8975 | 0.9038 | 0.9128 | -0.0024 | -0.0024 | 0.0023 | 0.0195 | -0.0070 | -0.0165 |
| 7.1.02 | 0.9038 | 0.897 | 0.8766 | -0.0025 | 0.0026 | -0.0047 | 0.0291 | -0.0176 | -0.0080 |
| 7.1.03 | 0.8924 | 0.8931 | 0.8983 | -0.0016 | 0.003 | -0.0019 | -0.0293 | -0.0091 | 0.0086 |
| 7.1.04 | 0.9607 | 0.9529 | 0.9543 | 0.0015 | -0.0022 | -0.0018 | -0.0005 | 0.0026 | 0.0030 |
| 7.1.05 | 0.8827 | 0.8932 | 0.8949 | -0.0013 | 0.0032 | -0.0007 | -0.0126 | 0.0044 | 0.0004 |
| 7.1.06 | 0.8787 | 0.8772 | 0.8743 | 0.0037 | 0.0017 | -0.003 | 0.0161 | 0.0110 | 0.0032 |
| 7.1.07 | 0.8436 | 0.8454 | 0.8444 | -0.0001 | -0.0029 | -0.0028 | 0.0017 | -0.0194 | -0.0076 |
| 7.1.08 | 0.9208 | 0.9114 | 0.9276 | 0.0023 | -0.0041 | -0.0035 | 0.0006 | -0.0142 | 0.00002 |
| 7.1.09 | 0.9187 | 0.9135 | 0.9073 | 0.0039 | -0.0029 | -0.0036 | -0.0047 | 0.0149 | 0.0089 |
| 7.1.10 | 0.9192 | 0.9423 | 0.9437 | 0.0047 | 0.0048 | 0.0035 | 0.0051 | -0.0109 | 0.0144 |
| boat.512 | 0.9257 | 0.9405 | 0.9276 | 0.0035 | 0.0008 | -0.0048 | -0.0045 | -0.0011 | -0.0113 |
| gray21.512 | 0.999 | 0.994 | 0.9974 | 0.0011 | 0.0012 | 0.0042 | -0.0086 | -0.0145 | 0.0068 |
| ruler.512 | 0.0425 | -0.0708 | -0.0811 | -0.0014 | 0.0025 | -0.0025 | -0.0035 | -0.0085 | 0.0165 |
| 5.3.01 | 0.9665 | 0.9625 | 0.9694 | -0.0022 | 0.0035 | -0.0037 | -0.0057 | -0.0069 | 0.0040 |
| 5.3.02 | 0.8712 | 0.8444 | 0.8557 | 0.0027 | -0.0004 | -0.0035 | -0.0137 | 0.0007 | 0.0091 |
| 7.2.01 | 0.9398 | 0.9562 | 0.9486 | 0.0024 | 0.0012 | 0.0026 | -0.0032 | 0.0032 | 0.0047 |
| Test image | Plain-image | Cipher-image | |||
| Ref. [41] | Ref. [42] | Ref. [43] | 2D-CHSLM-IES | ||
| 5.1.09 | 6.7057 | 7.996950 | 7.9973 | 7.9972 | 7.9972 |
| 5.1.10 | 1.5483 | 7.997474 | 7.9973 | 7.9977 | 7.9975 |
| 5.1.11 | 7.3424 | 7.997126 | 7.9968 | 7.9971 | 7.9976 |
| 5.1.12 | 7.2010 | 7.997025 | 7.9975 | 7.9972 | 7.9973 |
| 5.1.13 | 6.9940 | 7.996947 | 7.9975 | 7.9970 | 7.9972 |
| 5.1.14 | 5.7056 | 7.997028 | 7.9973 | 7.9970 | 7.9973 |
| 5.2.08 | 6.0274 | 7.999341 | 7.9993 | 7.9993 | 7.9993 |
| 5.2.09 | 4.0045 | 7.999300 | 7.9992 | 7.9991 | 7.9993 |
| 5.2.10 | 5.4957 | 7.999381 | 7.9993 | 7.9991 | 7.9992 |
| 7.1.01 | 6.1074 | 7.999235 | 7.9993 | 7.9993 | 7.9993 |
| 7.1.02 | 6.5632 | 7.999330 | 7.9993 | 7.9994 | 7.9991 |
| 7.1.03 | 6.6953 | 7.999262 | 7.9993 | 7.9993 | 7.9993 |
| 7.1.04 | 5.9916 | 7.999299 | 7.9993 | 7.9994 | 7.9994 |
| 7.1.05 | 5.0534 | 7.999333 | 7.9994 | 7.9992 | 7.9992 |
| 7.1.06 | 6.1898 | 7.999267 | 7.9992 | 7.9993 | 7.9993 |
| 7.1.07 | 5.9088 | 7.999211 | 7.9994 | 7.9993 | 7.9991 |
| 7.1.08 | 7.1914 | 7.999171 | - | 7.9993 | 7.9994 |
| 7.1.09 | 4.3923 | 7.999268 | - | 7.9993 | 7.9992 |
| 7.1.10 | 0.5000 | 7.999337 | - | 7.9992 | 7.9994 |
| boat.512 | 7.5237 | 7.999179 | 7.9993 | 7.9993 | 7.9993 |
| gray21.512 | 6.8303 | 7.999454 | 7.9993 | 7.9994 | 7.9993 |
| ruler.512 | 5.6415 | 7.999270 | 7.9993 | 7.9992 | 7.9991 |
| 5.3.01 | 6.7057 | 7.999829 | 7.9998 | 7.9998 | 7.9998 |
| 5.3.02 | 1.5483 | 7.999851 | 7.9998 | 7.9998 | 7.9998 |
| 7.2.01 | 7.3424 | 7.999821 | 7.9998 | 7.9998 | 7.9997 |
| Mean of | 6.0116 | 7.997091 | 7.9973 | 7.9972 | 7.9974 |
| Mean of | 5.6263 | 7.999290 | 7.9993 | 7.9993 | 7.9993 |
| Mean of | 6.6652 | 7.999834 | 7.9998 | 7.9998 | 7.9998 |
| , | Critical values () | ||
| 99.5693 | 99.5893 | 99.5994 | |
| 33.2824 | 33.3730 | 33.4182 | |
| 33.6447 | 33.5541 | 33.5088 | |
| Test image | ||||||||
| Ref. [41] | Ref. [42] | Ref. [43] | 2D-CHSLM-IES | Ref. [41] | Ref. [42] | Ref. [43] | 2D-CHSLM-IES | |
| 5.1.09 | 99.6002 | 99.6323 | 99.6094 | 99.6109 | 33.4831 | 33.4561 | 33.4817 | 33.4330 |
| 5.1.10 | 99.6170 | 99.6124 | 99.6185 | 99.6140 | 33.5384 | 33.5674 | 33.4672 | 33.4606 |
| 5.1.11 | 99.6292 | 99.6078 | 99.6048 | 99.6185 | 33.5100 | 33.4934 | 33.4216 | 33.4543 |
| 5.1.12 | 99.6109 | 99.6185 | 99.6094 | 99.6231 | 33.3905 | 33.4669 | 33.4362 | 33.5017 |
| 5.1.13 | 99.6307 | 99.5956 | 99.6109 | 99.6124 | 33.4601 | 33.4151 | 33.4393 | 33.4913 |
| 5.1.14 | 99.5911 | 99.6292 | 99.6002 | 99.6353 | 33.4052 | 33.4585 | 33.4646 | 33.4260 |
| 5.2.08 | 99.5972 | 99.6193 | 99.6109 | 99.6265 | 33.4380 | 33.4772 | 33.4865 | 33.4330 |
| 5.2.09 | 99.6265 | 99.6178 | 99.6090 | 99.6098 | 33.5115 | 33.4369 | 33.4788 | 33.4977 |
| 5.2.10 | 99.6216 | 99.6323 | 99.6086 | 99.6059 | 33.5257 | 33.4081 | 33.5094 | 33.4794 |
| 7.1.01 | 99.6098 | 99.6204 | 99.6071 | 99.6040 | 33.4190 | 33.4324 | 33.4632 | 33.4694 |
| 7.1.02 | 99.6189 | 99.6101 | 99.6094 | 99.6212 | 33.5257 | 33.4435 | 33.4572 | 33.4410 |
| 7.1.03 | 99.6273 | 99.5975 | 99.6098 | 99.6151 | 33.5024 | 33.4653 | 33.4241 | 33.4801 |
| 7.1.04 | 99.5979 | 99.6113 | 99.6117 | 99.6014 | 33.4243 | 33.4360 | 33.4671 | 33.4845 |
| 7.1.05 | 99.6120 | 99.6159 | 99.6105 | 99.6109 | 33.4230 | 33.4468 | 33.4469 | 33.4939 |
| 7.1.06 | 99.6056 | 99.6162 | 99.6117 | 99.6124 | 33.4550 | 33.4857 | 33.4557 | 33.4338 |
| 7.1.07 | 99.6029 | 99.6086 | 99.6101 | 99.6170 | 33.4514 | 33.4385 | 33.4847 | 33.4455 |
| 7.1.08 | 99.5998 | - | 99.6162 | 99.6105 | 33.4468 | - | 33.4796 | 33.4877 |
| 7.1.09 | 99.6220 | - | 99.6071 | 99.6334 | 33.4605 | - | 33.4256 | 33.4918 |
| 7.1.10 | 99.6254 | - | 99.6109 | 99.6044 | 33.4698 | - | 33.4636 | 33.5007 |
| boat.512 | 99.6120 | 99.6078 | 99.6033 | 99.6151 | 33.4356 | 33.4853 | 33.4305 | 33.4436 |
| gray21.512 | 99.6025 | 99.6227 | 99.6094 | 99.6216 | 33.4369 | 33.4007 | 33.4916 | 33.4577 |
| ruler.512 | 99.5983 | 99.6216 | 99.6098 | 99.6033 | 33.4237 | 33.4343 | 33.5110 | 33.4847 |
| 5.3.01 | 99.6127 | 99.6024 | 99.6094 | 99.61 | 33.4455 | 33.4902 | 33.4775 | 33.4914 |
| 5.3.02 | 99.6151 | 99.6009 | 99.6076 | 99.6081 | 33.4942 | 33.4440 | 33.4646 | 33.4433 |
| 7.2.01 | 99.6058 | 99.6059 | 99.6033 | 99.6043 | 33.4597 | 33.4598 | 33.4697 | 33.4309 |
| Pass/All | 25/25 | 22/22 | 25/25 | 25/25 | 25/25 | 22/22 | 25/25 | 25/25 |
| Mean | 99.611696 | 99.6139 | 99.6092 | 99.6140 | 33.461440 | 33.4565 | 33.4639 | 33.4663 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




