Submitted:
01 January 2024
Posted:
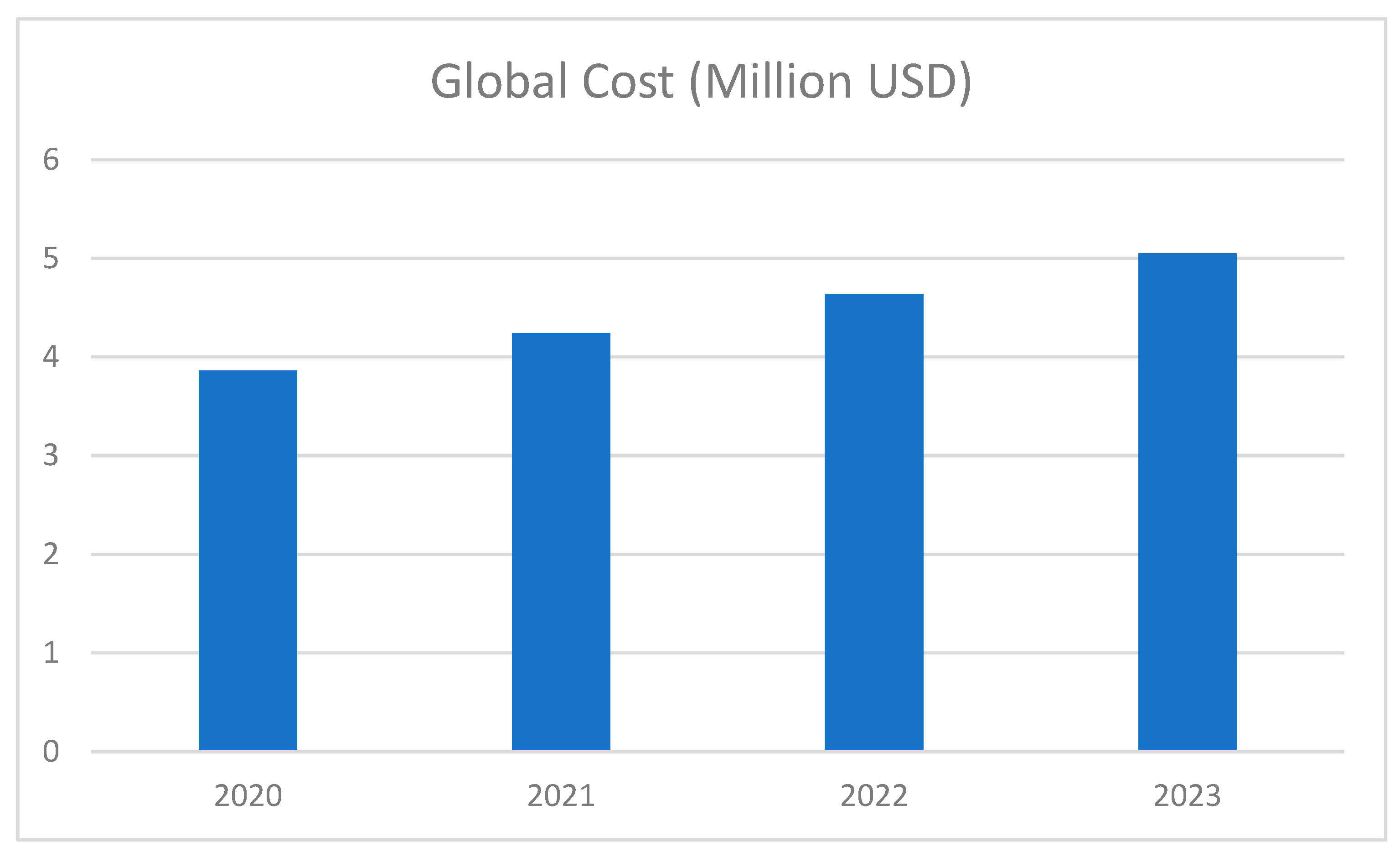
03 January 2024
You are already at the latest version
Abstract
Keywords:
Introduction:
1.0. Introduction
2.0. Literature Review
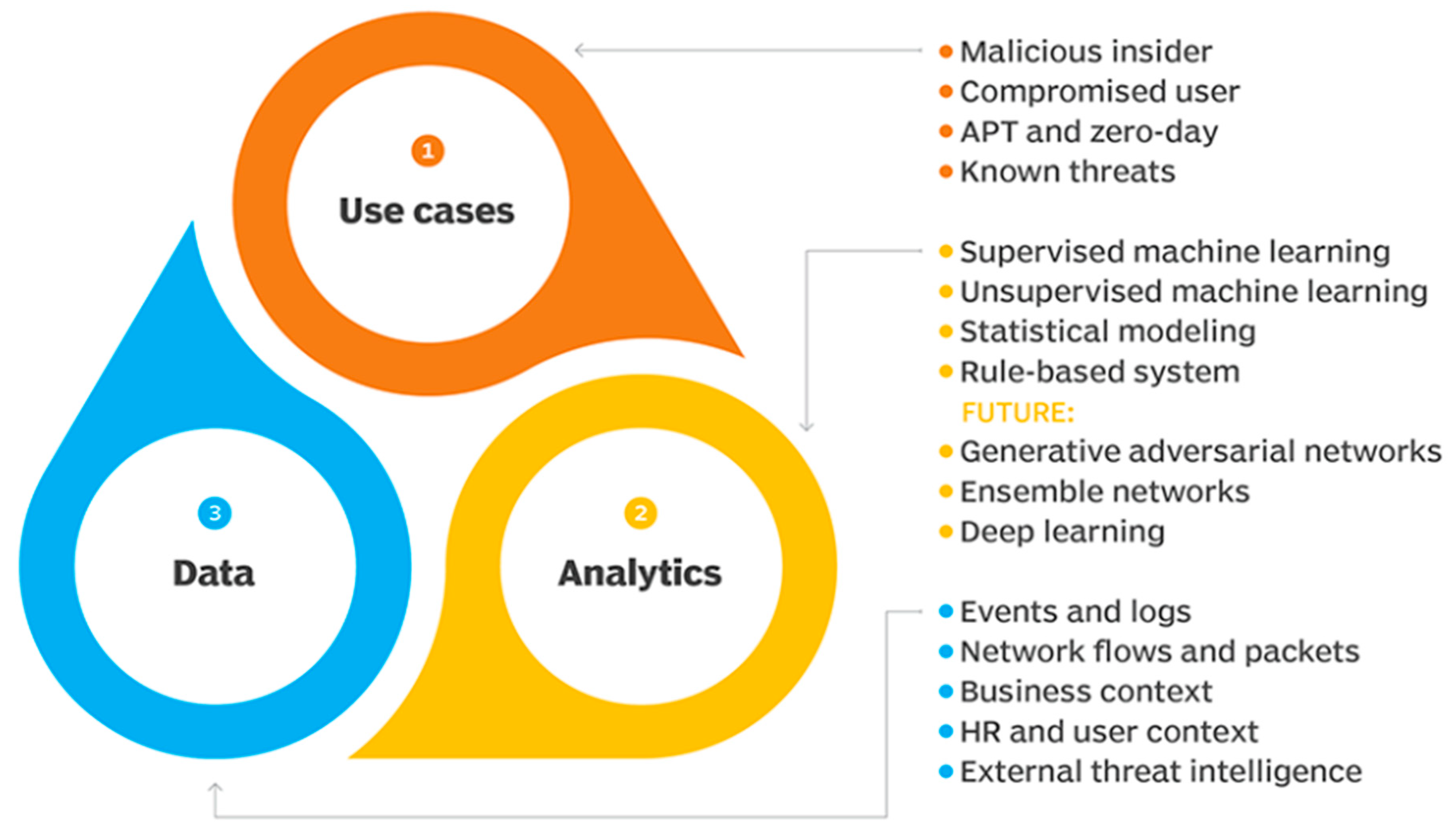
2.1. An Outline of Artificial intelligence and ML Approaches for Peculiarity Location in Network protection
2.2. Challenges and Solutions in Implementing AI-based Automated Response Systems for Cyber Threats
2.3. Issues with Scalability in AI-Powered Threat Recognition and Reaction Systems
3.0. AI-Driven Data Collection and Analysis
3.1. AL Libraries
3.2. Dataset Preparation and Correlation
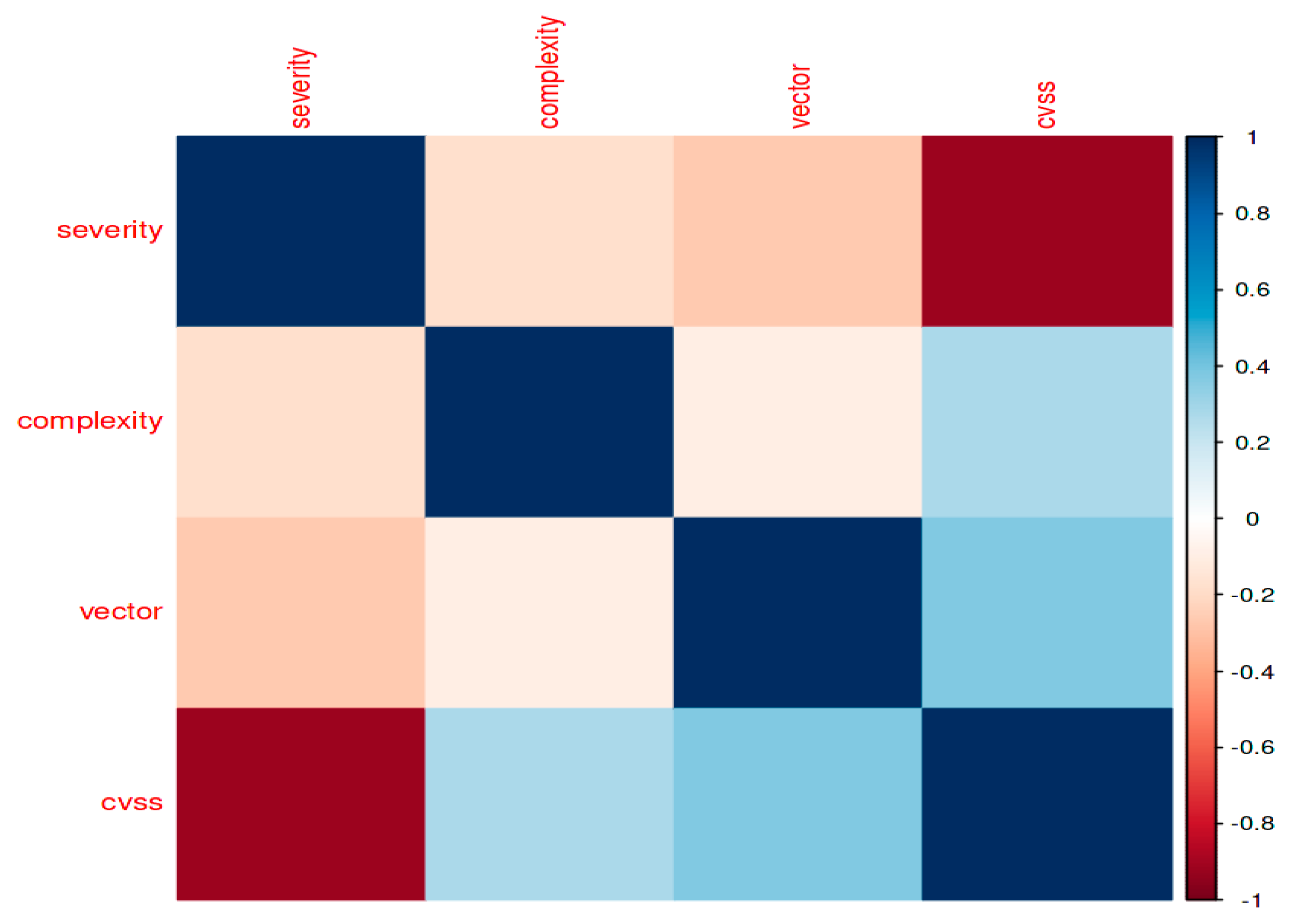
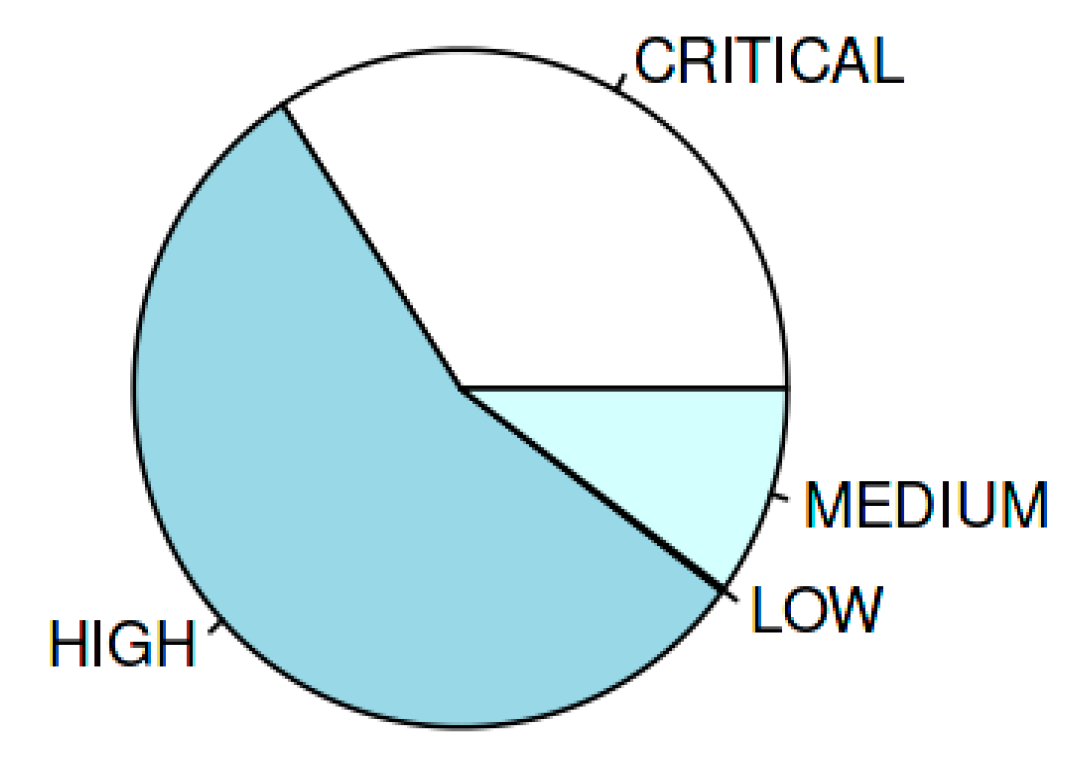
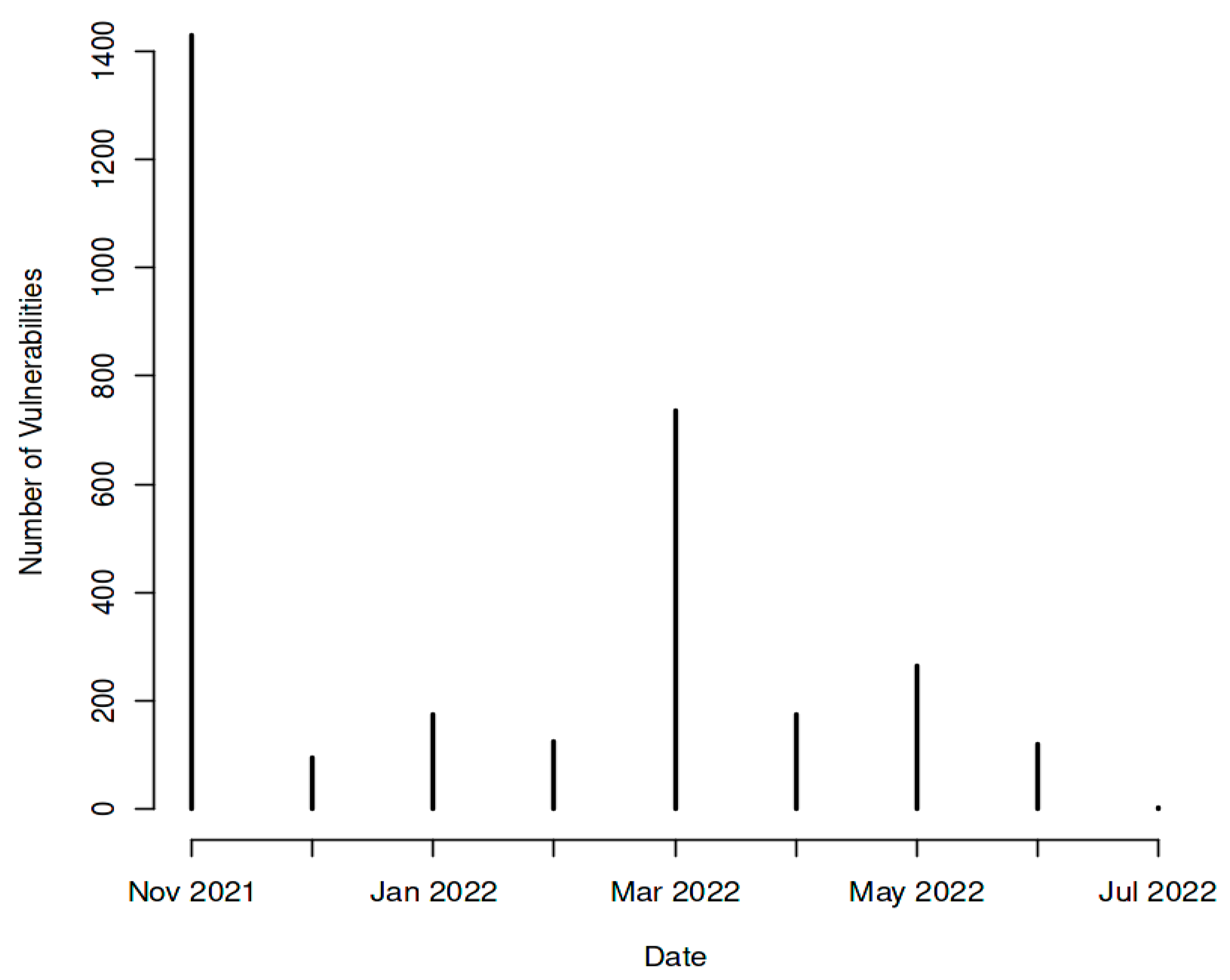
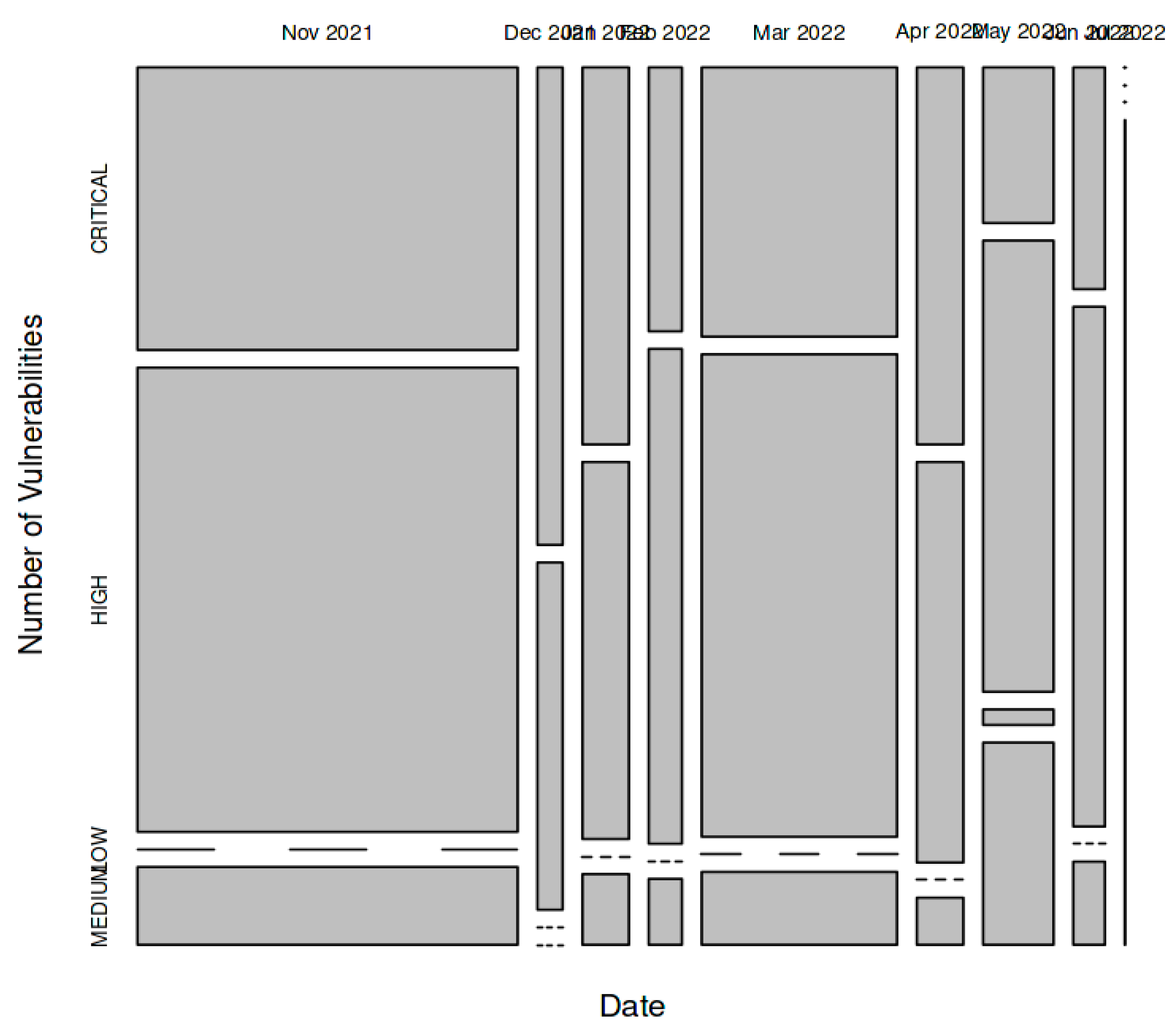
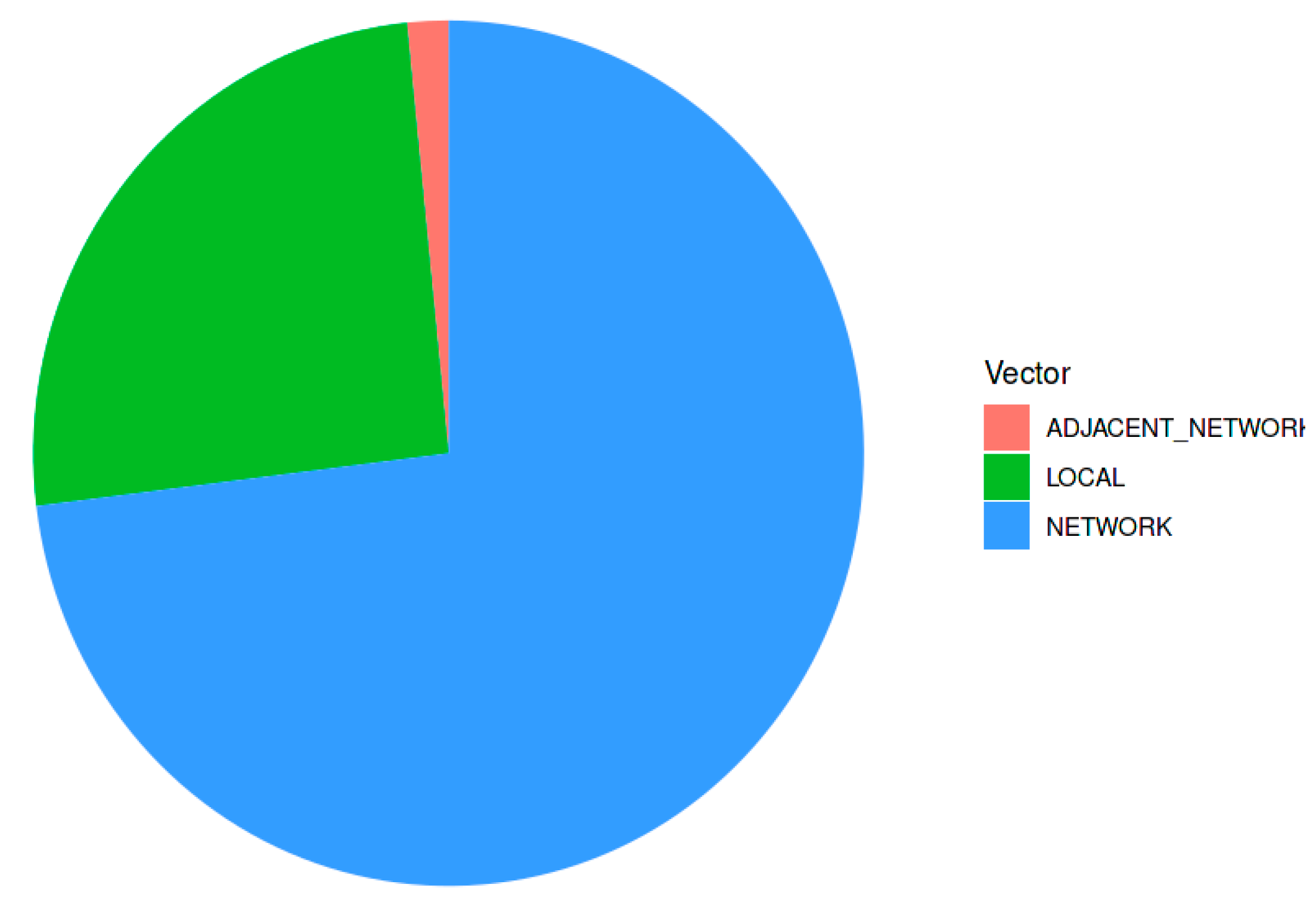
3.3. Examination of Image Trend and Number of Vulnerabilities
3.4. Effect on organizations
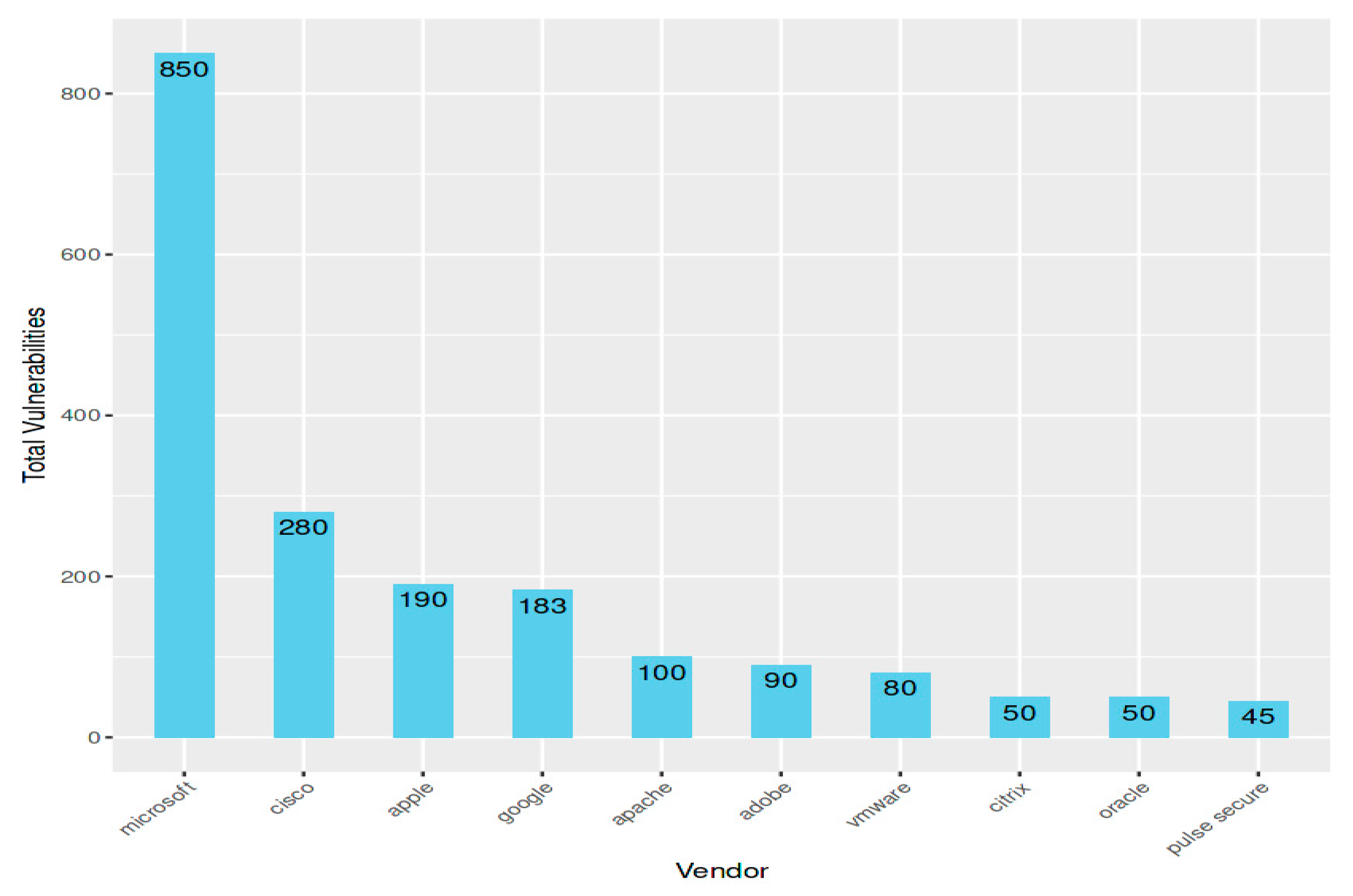
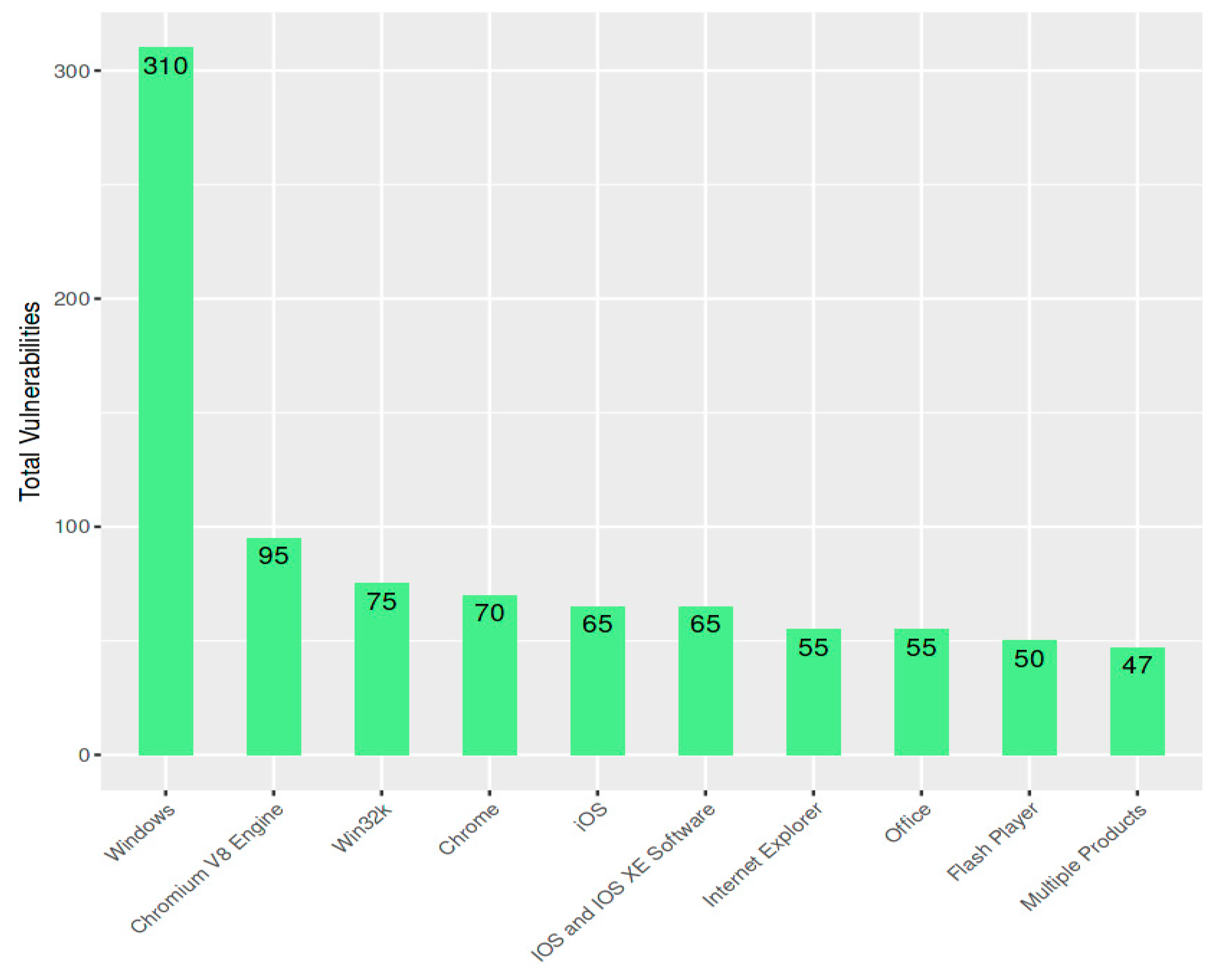
3.5. Top Ten Applications with highest number of vulnerabilities
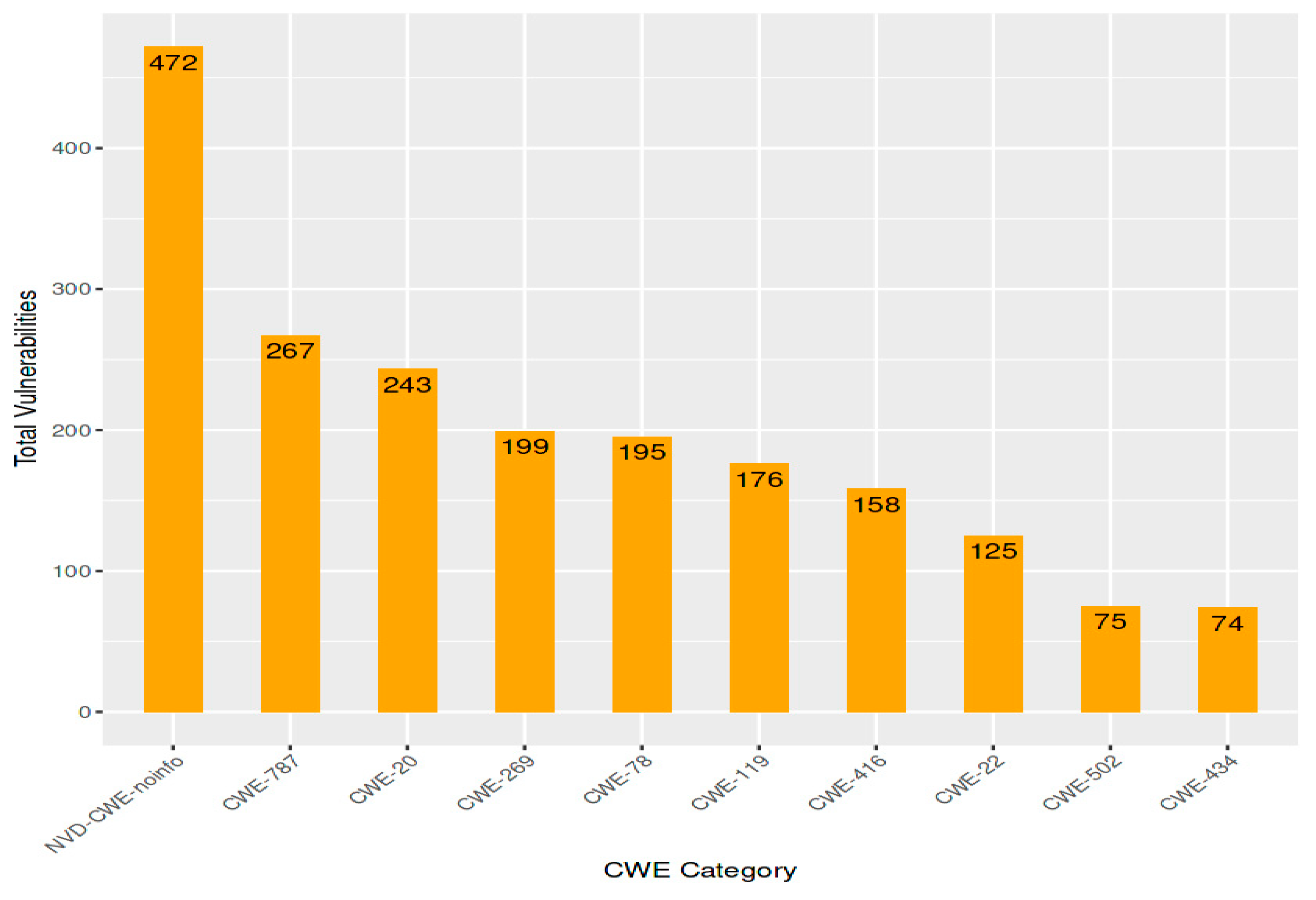
- CWE-119: Improper Input Validation
- CWE-78: Improper Neutralization of Special Elements used in Output
- CWE-20: Improper Authentication
- CWE-269: Improper Privilege Management
- CWE-787: Out-of-bounds Read
- CWE-416: Use of Hard-coded Credentials
- CWE-22: Path Traversal
- CWE-502: Deserialization of Untrusted Data
- CWE-200: Information Exposure
- CWE-400: Unrestricted Uploading of File with harmful File Type
| CWE Category | vulnerabilities |
|---|---|
| CWE-119 | Inadequate input validation can allow an attacker to insert SQL code into a database and steal data or perform other malicious tasks. |
| CWE-78 | Cross-site scripting attacks can be leveraged by improper neutralization of special elements used in output, giving an attacker the ability to steal session cookies. |
| CWE-20 | Unauthorized access to a system or application can be obtained by abusing improper authentication. |
| CWE-269 | An attacker may be able to carry out harmful activities on a system by elevating privileges through the use of improper privilege management. |
| CWE-787 | By using read to read data outside of the allocated memory buffer and breaking the limits, an attacker might be able to obtain private data. |
| CWE-416 | Passwords and other sensitive data can be stolen through the use of hard-coded credentials. |
| CWE-22 | An attacker may be able to obtain files outside of the intended directory by using path traversal, which gives them access to sensitive information. |
| CWE-502 | It is possible to use the deserialization of untrusted data to run arbitrary code on a computer. |
| CWE-200 | Information Exposure can be used to steal private information, including financial or consumer data. |
| CWE-400 | Malicious files could be uploaded to a system by an attacker, who could then use them to steal data or run arbitrary code. Due to this vulnerability, files containing risky file types can be uploaded without restriction. |
4.0. Conclusion
References
- Brakerski, Z., Gentry, C. and Vaikuntanathan, V., "(Leveled) Fully Homomorphic Encryption without Bootstrapping," ACM Trans. Comput. Theory, vol. 6, no. 3, pp. 1-36, 2014. [CrossRef]
- Ben Neria, M., Yacovzada, N.-S. and Ben-Gal, I., "A Risk-Scoring Feedback Model for Webpages and Web Users Based on Browsing Behavior," ACM Trans. Intell. Syst. Technol., vol. 8, no. 4, pp. 1-21, 2017. [CrossRef]
- Li, S., Da Xu, L., Zhao, S., "The internet of things: A survey," Inf. Syst. Front, vol. 17, p. 243–259, 2015. [CrossRef]
- Sun, N., Zhang, J., Rimba, P., Gao, S., Zhang, L.Y., Xiang, Y. , "Data-driven cybersecurity incident prediction," A survey. IEEE Commun. Surv. Tutor, vol. 21, p. 1744–1772, 2018. [CrossRef]
- McIntosh, T., Jang-Jaccard, J., Watters, P., Susnjak, T, "The inadequacy of entropy-based ransomware detection," Springer, pp. 181-189, 12–15 December 2019. [CrossRef]
- Alazab, M., Venkatraman, S., Watters, P., Alazab, M., "Zero-day malware detection based on supervised learning algorithms of API call signatures," In Proceedings of the Ninth Australasian Data Mining Conference (AusDM’11), Ballarat, Australia, 1–2 December 2011.
- Shaw, A, "Data breach: From notification to prevention using PCI DSS," Colum. JL Soc. Probs., vol. 517, no. 43, 2009.
- Gupta, B.B., Tewari, A., Jain, A.K., Agrawal, D.P., "Fighting against phishing attacks: State of the art and future challenges," Neural Comput. Appl., vol. 28, p. 3629, 2017. [CrossRef]
- Geer, D., Jardine, E., Leverett, E. , "On market concentration and cybersecurity risk.," J. Cyber Policy, vol. 5, pp. 9-29, 2020. [CrossRef]
- Buecker, A., Borrett, M., Lorenz, C., Powers, C., "Introducing the IBM Security Framework and IBM Security Blueprint to Realize Business-Driven Security," International Technical Support Organization: Riyadh, 2010.
- Fischer, E.A, "Cybersecurity Issues and Challenges: In Brief; Library of Congress," 2014.
- Chernenko, E., Demidov, O., Lukyanov, F. , "Increasing International Cooperation in Cybersecurity and Adapting Cyber Norms," Council on Foreign Relations.
- Papastergiou, S., Mouratidis, H., Kalogeraki, E.M., "Cyber security incident handling, warning and response system for the european critical information infrastructures (cybersane).," In Proceedings of the International Conference on Engineering Applications of Neural Networks, Crete, Greece, 24–26 May 2019; Springer: Berlin/Heidelberg, p. 476–487, 2019.
- Nicholas Jeffrey, Qing Tan and José R. Villar, "A Review of Anomaly Detection Strategies to Detect Threats to Cyber-Physical Systems," Electronics, vol. 12, p. 3283, July 2023. [CrossRef]
- Jiang, M., Zhang, Q. and Kong, J., , "Multiformer-based hybrid learning with outlier re-assignment for unsupervised person re-identification," International Journal of Machine Learning and Cybernetics, pp. 1-18, 2023. [CrossRef]
- Li, S.; Da Xu, L.; Zhao, S. , "The internet of things: A survey.," Inf. Syst. Front. , vol. 17, p. 243–259, 2015. [CrossRef]
- Sun, N.; Zhang, J.; Rimba, P.; Gao, S.; Zhang, L.Y.; Xiang, Y. , "Data-driven cybersecurity incident prediction: A survey.," IEEE Commun. Surv. Tutor, vol. 21, p. 1744–1772, 2018. [CrossRef]
- McIntosh, T.; Jang-Jaccard, J.; Watters, P.; Susnjak, T, "The inadequacy of entropy-based ransomware detection," in In Proceedings of the International Conference on Neural Information Processing, , Sydney, Australia, 2019.
- Alazab, M.; Venkatraman, S.; Watters, P.; Alazab, M., "Zero-day malware detection based on supervised learning algorithms of API call signatures," in In Proceedings of the Ninth Australasian Data Mining Conference (AusDM’11), Ballarat, Australia, 2019.
- Shaw, A., "Data breach: From notification to prevention using PCI DSS. Colum," JL Soc. Probs. , vol. 43, p. 517, 2009.
- Gupta, B.B.; Tewari, A.; Jain, A.K.; Agrawal, D.P. , "Fighting against phishing attacks: State of the art and future challenges," Neural Comput. Appl. , vol. 28, p. 3629–3654, 2017. [CrossRef]
- Geer, D.; Jardine, E.; Leverett, E. , "On market concentration and cybersecurity risk," J. Cyber Policy , vol. 5, p. 9–29, 2020. [CrossRef]
- Buecker, A.; Borrett, M.; Lorenz, C.; Powers, C, "Introducing the IBM Security Framework and IBM Security Blueprint to Realize Business-Driven Security," International Technical Support Organization, 2010.
- Fischer, E.A, "Cybersecurity Issues and Challenges: In Brief," Library of Congress, 2014.
- Chernenko, E., Demidov, O., Lukyanov, F, "Increasing International Cooperation in Cybersecurity and Adapting Cyber Norms," Council on Foreign Relations, 2018.
- Papastergiou, S.; Mouratidis, H.; Kalogeraki, E.M., "Cyber security incident handling, warning and response system for the european critical information infrastructures (cybersane)," in In Proceedings of the International Conference on Engineering Applications of Neural Networks, Berlin/Heidelberg, Germany, 2019.
- O’Connell, M.E. , "Cyber security without cyber war," J. Confl. Secur. Law, vol. 17, p. 187–209, 2012. [CrossRef]
- Tolle, K.M.; Tansley, D.S.W.; Hey, A.J, "The fourth paradigm: Data-intensive scientific discovery," Proc. IEEE, 2011. [CrossRef]
- "Cost of Cyber Attacks vs. Cost of Cybersecurity in 2021|Sumo Logic," 2021. [Online]. Available: www.sumologic.com/blog/costof-cyber-attacks-vs-cost-of-cyber-security-in-2021/.
- Anwar, S.; Mohamad Zain, J.; Zolkipli, M.F.; Inayat, Z.; Khan, S.; Anthony, B.; Chang, V., "From intrusion detection to an intrusion response system: fundamentals, requirements, and future directions," Algorithms, vol. 10, no. 39, 2017. [CrossRef]
- Saxe, J.; Sanders, H, "Attack Detection and Attribution," Malware Data Science, 2018.
- Randall Smith, "Multi-Community Cyber Defense (MCCD)," 2002.
- Robert E. Mahan; Jerry D. Fluckiger; Samuel L. Clements; Cody W. Tews; John R. Burnette; Craig A. Goranson; Harold Kirkham, "Secure Data Transfer Guidance for Industrial Control and SCADA Systems," 2011.
- William J Buchanan, "Introduction to Security and Network Forensics," 2011.
- Christian M. Lesjak; Daniel M. Hein; Johannes Winter, "Hardware-security Technologies for Industrial IoT: TrustZone and Security Controller," in IECON 2015 - 41ST ANNUAL CONFERENCE OF THE IEEE INDUSTRIAL, 2015.
- Prageeth Gunathilaka; Daisuke Mashima; Binbin Chen, "SoftGrid: A Software-based Smart Grid Testbed for Evaluating Substation Cybersecurity Solutions," 2016.
- Teemu Väisänen, "Categorization of Cyber Security Deception Events for Measuring The Severity Level of Advanced Targeted Breaches," in PROCEEDINGS OF THE 11TH EUROPEAN CONFERENCE ON SOFTWARE, 2017.
- Hao Yi Ong; Mykel J. Kochenderfer, "Markov Decision Process-Based Distributed Conflict Resolution for Drone Air Traffic Management," JOURNAL OF GUIDANCE CONTROL AND DYNAMICS, 2017. [CrossRef]
- Jeffrey Wermann; Armando Walter Colombo; Agnes Pechmann; Maximilian Zarte, "Using an Interdisciplinary Demonstration Platform for Teaching Industry 4.0," PROCEDIA MANUFACTURING, 2019. [CrossRef]
- Peter Sullivan, "Network anomaly detection: The essential antimalware tool," 2023.
- Katie Terrell Hanna, "Brute- force attack".
- Erin Sullivan, "Data Loss," 2023.
- Peter Loshin, "user behavior analytics (UBA)," Tech Target.
- Quadrant, M., , "Magic quadrant for security information and event management," Magic Quadrant, 2016.
- Forrester Research, "The Forrester Wave™: Security Threat Intelligence Services," 2022.
- IDC, "Demand Driven by the Need for Security Automation to Address Growing Complexity and Scale of Threats," Worldwide Security Orchestration, Automation, and Response (SOAR) Software Market Shares, 2022.
- Moncada-Torres, A., van Maaren, M.C., Hendriks, M.P., Siesling, S. and Geleijnse, G, "Explainable machine learning can outperform Cox regression predictions and provide insights in breast cancer survival," Scientific reports, vol. 11, no. 1, p. 6968, 2021. [CrossRef]
- Najafabadi, M.M., Villanustre, F., Khoshgoftaar, T.M., Seliya, N., Wald, R. and Muharemagic, E., , "Deep learning applications and challenges in big data analytics," Journal of big data, vol. 2, no. 1, pp. 1-21, 2015. [CrossRef]
- Pandey, S., Srivastava, A.K. and Amidan, B.G., , "A real time event detection, classification and localization using synchrophasor data.," IEEE Transactions on Power Systems, vol. 35, no. 6, pp. 4421-4431, 2020. [CrossRef]
- Meng, Z., Xu, H., Chen, M., Xu, Y., Zhao, Y. and Qiao, C.,, "Learning-driven decentralized machine learning in resource-constrained wireless edge computing.," in In IEEE INFOCOM 2021-IEEE Conference on Computer Communications, 2021.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




