Submitted:
09 August 2023
Posted:
10 August 2023
You are already at the latest version
Abstract
Keywords:
1. Introduction.
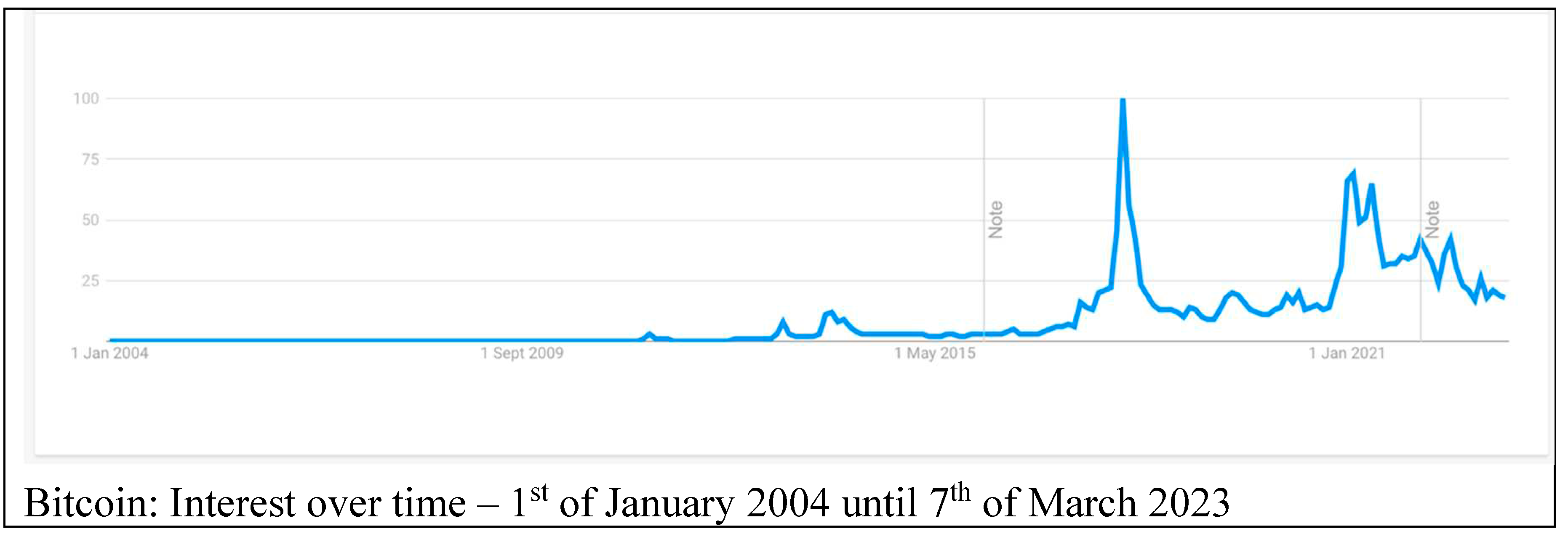
1.1. Historical context
1.2. Historical overview of Blockchain technologies
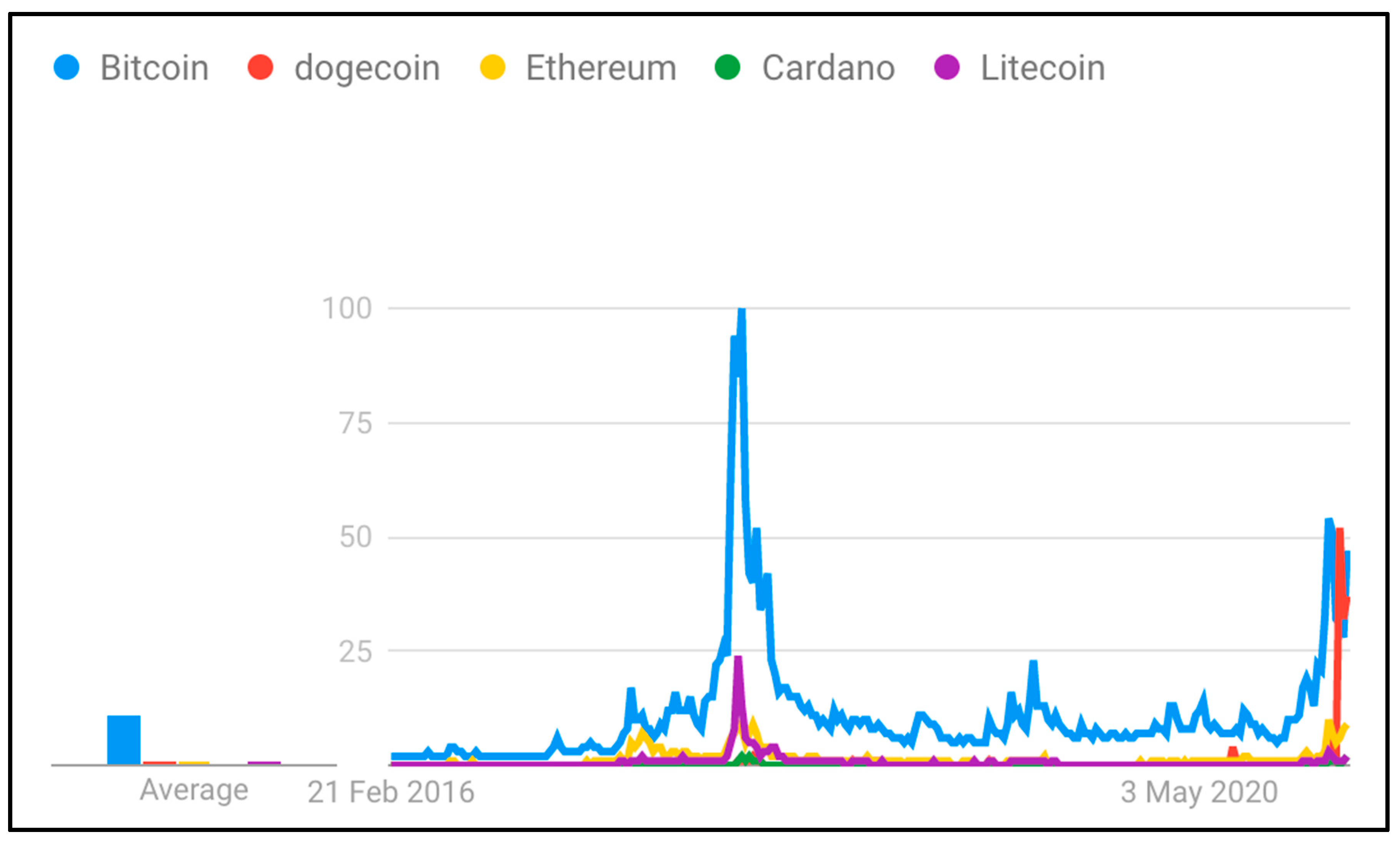
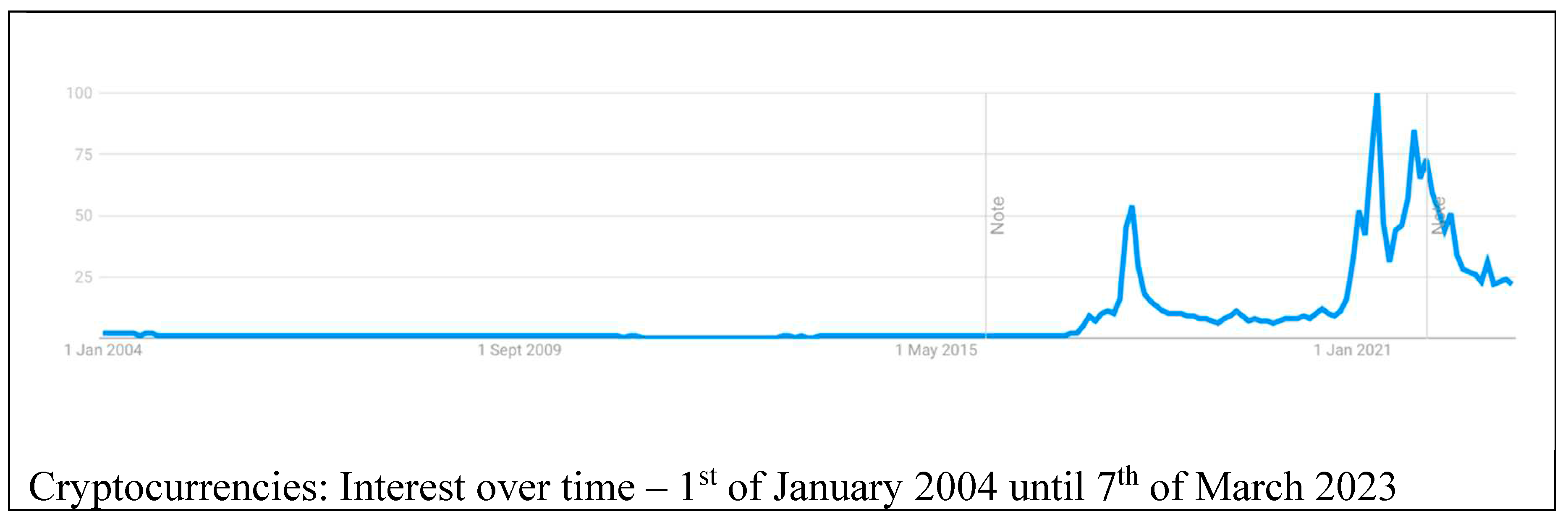
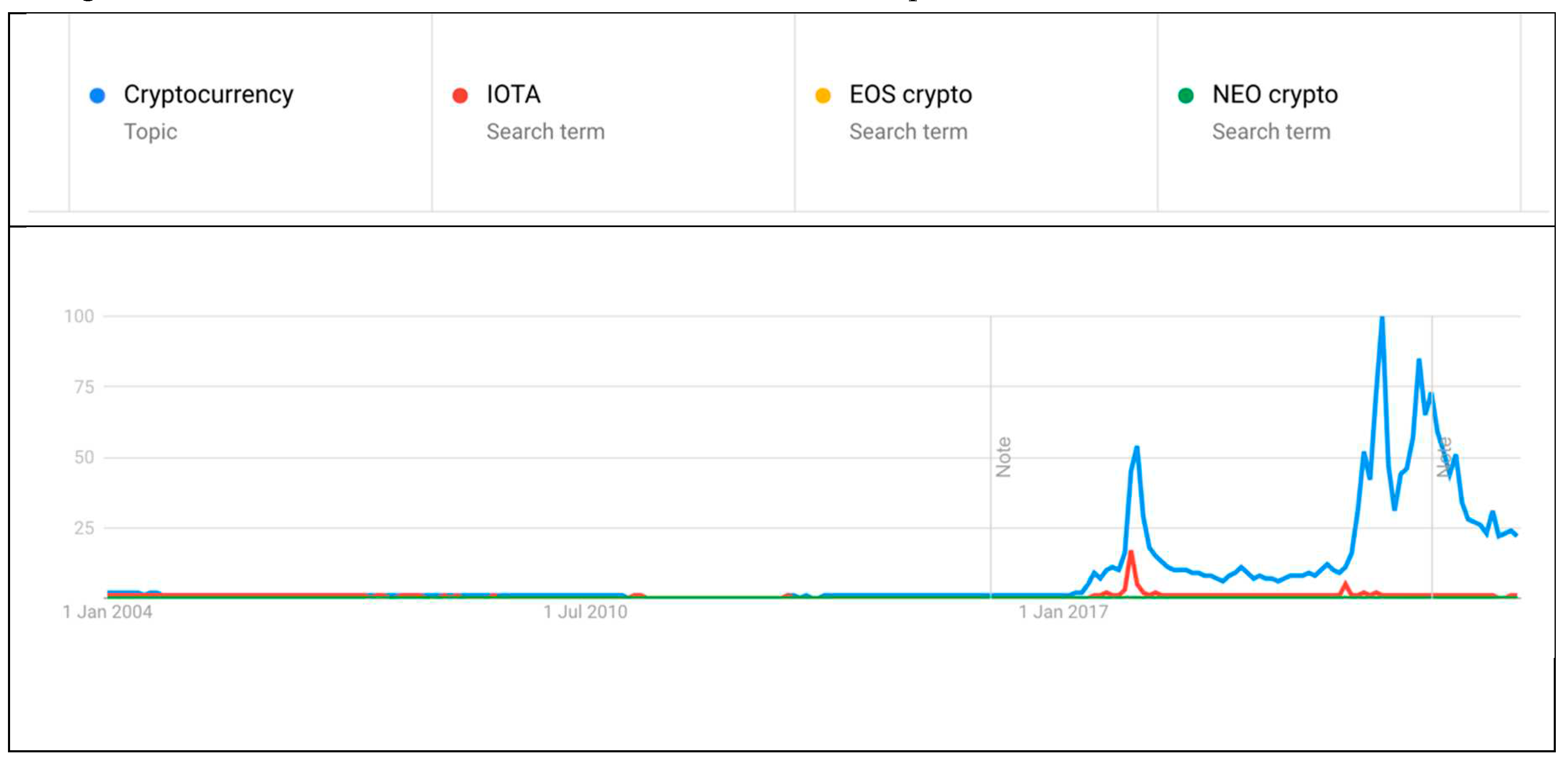
1.3. Brief History of Cryptocurrencies
1.4. Research questions and structure
- To assess the potential of blockchain technology as a catalyst for innovation in future iterations of the internet and Web3 and to determine whether it represents a cutting-edge technology or an outdated concept in the context of financial invention.
- To comprehensively analyse and evaluate the risks associated with cryptocurrencies, including but not limited to market volatility, security vulnerabilities, regulatory challenges, and potential illicit activities, to understand the risk landscape within financial innovation better.
- Investigating and identifying the intrinsic values derived from cryptocurrencies, considering their potential impact on financial systems, economic growth, financial inclusion, transaction efficiency, and transparency, thus contributing to understanding their value proposition within financial innovation.
- Conduct a thorough analysis of different blockchain projects and their underlying technologies to identify critical factors that contribute to their long-term viability and survival in the dynamic landscape of financial innovation, thereby providing insights into the sustainability of blockchain projects.
- To explore and identify blockchain projects that have the potential to further the development and advancement of already developed countries' financial systems, addressing specific areas such as efficiency, security, transparency, financial inclusion, and regulatory compliance, thus providing valuable insights into the role of blockchain in enhancing financial innovation in advanced economies.
- To examine and identify blockchain projects that can foster development and progress in developing countries, taking into consideration their unique challenges and needs, including financial inclusion, access to capital, remittances, land registries, supply chain management, and government services, thereby contributing to the understanding of how blockchain can drive financial innovation in developing economies.
- To critically evaluate the feasibility and implications of regulating cryptocurrencies and blockchain projects, including both national and international regulatory frameworks, to assess the potential benefits, challenges, and trade-offs associated with effective regulation in the context of financial innovation. This research objective seeks to contribute to the ongoing discourse on appropriate regulatory approaches for cryptocurrencies and blockchain technology.
1.5. Crypto regulations
1.6. Structure and novelty of the research study
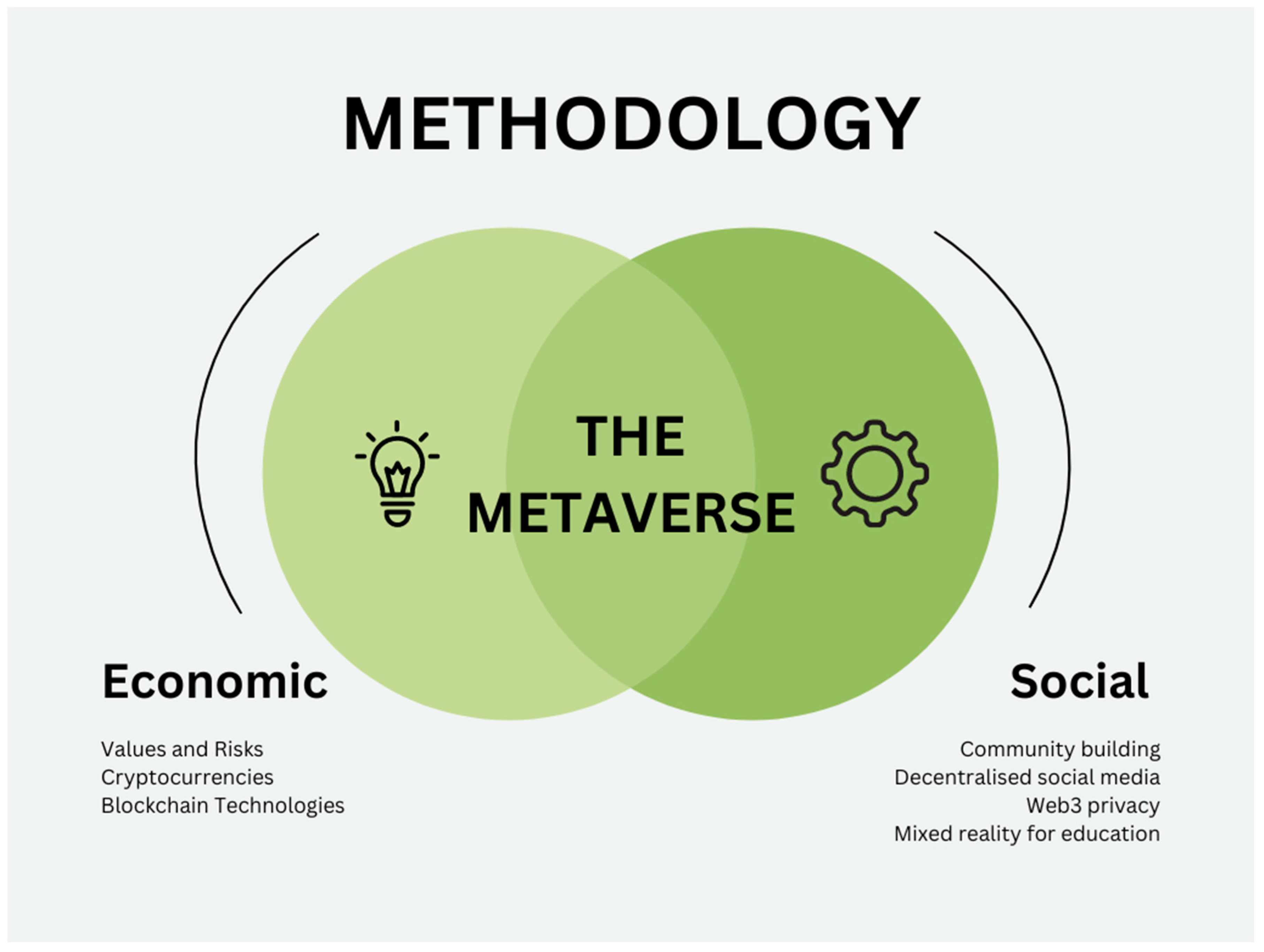
2. Methodology
2.1. Data sources
2.2. Contextualising this study with the existing body of literature
3. Academic literature review
4. Case Study Review: Case studies of existing Blockchain solutions.
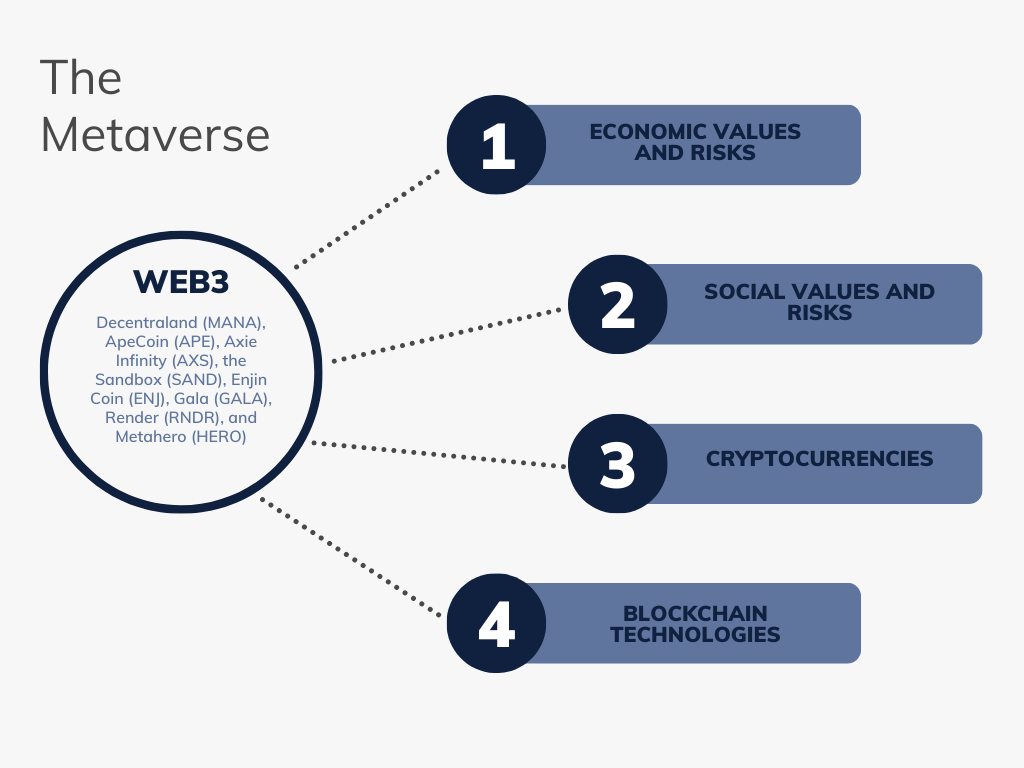
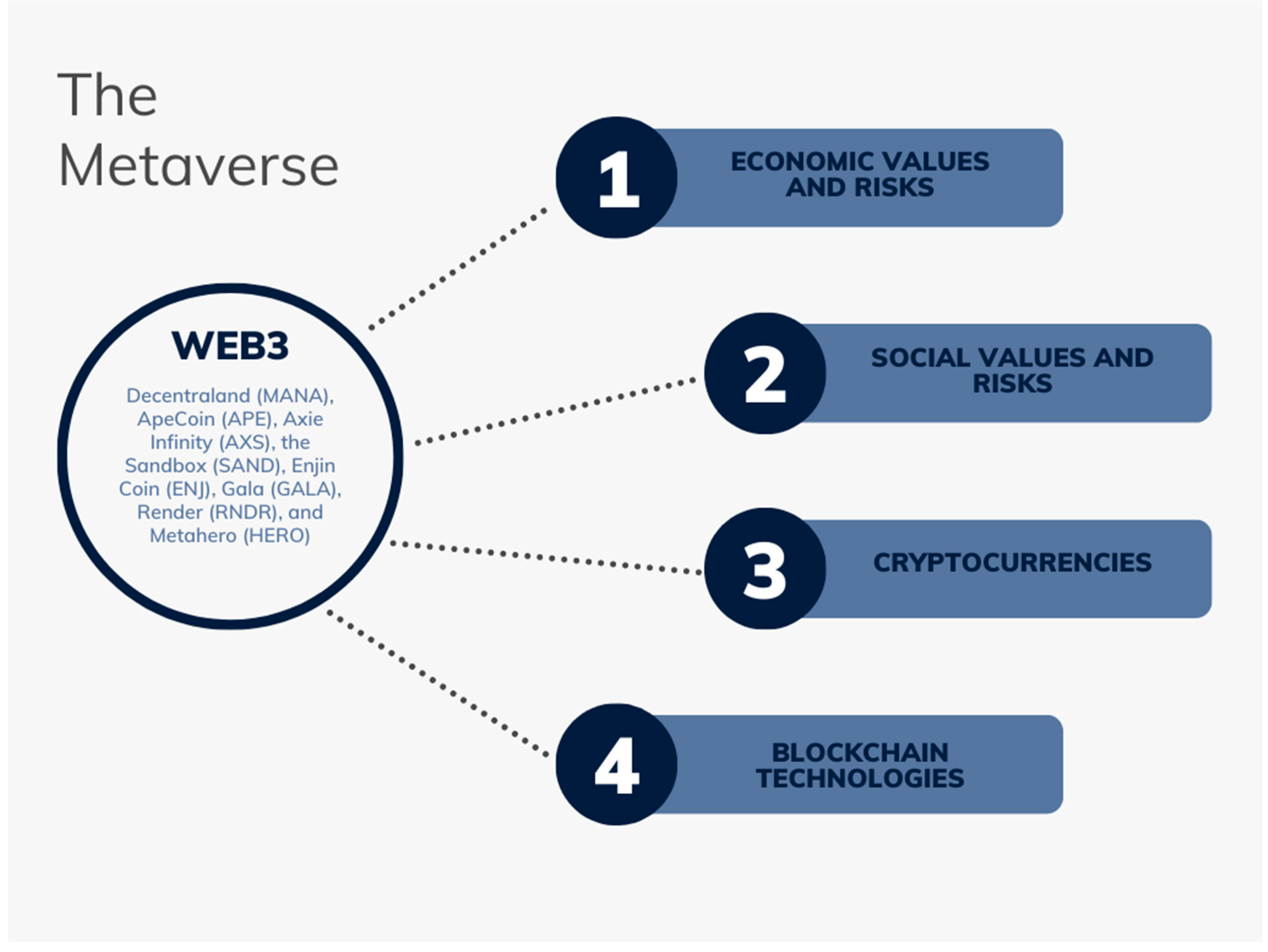
4.1. Blockchain 3.0 and Web 3.0
4.2. IoT-based Blockchain solutions
4.3. IoT for healthcare
4.4. Decentralised finance – DeFi
4.5. Centralised exchanges
4.6. Layer 1s and 2s, Non-Fungible Tokens (NFTs), and the Metaverses
| Blockchain/Protocol | Layer Type | Notable Tokens |
| Bitcoin | Layer 1 | - |
| Ethereum | Layer 1 | MANA, APE, AXS, SAND, ENJ, GALA, RNDR, HERO |
| Arbitrum | Layer 2 | - |
| Optimism | Layer 2 | - |
| Theta | Layer 1 | THETA (governance), TFUEL (utility) |
| Stacks | Layer 1 | STX |
4.7. Crypto Bridges and Oracles
4.8. Crypto Wallets
| Wallet Type | Examples |
| Safe Storage | Ledger, Trezor |
| Hot Wallet | Metamask, TrustWallet |
| Exchange Wallet | Coinbase Wallet |
5. Lessons to be learned from the past errors: the two Cases of FTX and Terra Luna
- The first is to create standards and regulations for cryptocurrencies because as of today (08 Jan 2023), we have 22,228 different cryptos (i.e., crypto projects) and 534 crypto exchanges, with a market cap of $824,468,428,103 and 24h trade volume of $16,374,071,351[139]. None of the trades are regulated in the UK, nor most other countries.
- The second is to ban all use of cryptocurrencies, including ownership and trading, but this is unlikely to be effective because most crypto projects are run from outside of the UK, and some (e.g., Bitcoin) are decentralised. Hence, even if a global task force could be created to track and trace cryptocurrency projects and exchanges, it would be ineffective against decentralised crypto and will only push trade and ownership into the dark economy. In addition, it is unlikely that the legal mechanisms can cope with persecuting all cryptocurrency projects and exchanges because, as we can see from the case of the XRP legal proceedings, just one point can take years to resolve. The US Government has proven that it can effectively ban crypto projects. In August 2022, the U.S. Treasury sanctioned the virtual currency mixer Tornado Cash [140]. The Tornado Cash DAO was shut down, and its lead developer Aleksey Pertsev was arrested, but what this translates to is that the mixer's code itself is banned for use, and it does not mean that the code has been disabled and cannot be used. It means that the Tornado Cash U.S. crypto customers are not allowed to use the mixer, at least not without permission from the U.S. Treasury. The mixer is blacklisted in the US because of its use in money laundering. However, the Tornado Cash app will continue to operate on the Ethereum blockchain exists. The critical point is that it is impossible to shut down such technology without shutting down the entire Blockchain. Since some Blockchains are decentralised, this will prove difficult, and even, if possible, many new Blockchains are constantly emerging. Hence, sanctioning and banning are unlikely to be valid for completely closing all operations.
- The third option is to create fully centralised Government run Blockchains, upon which open crypto projects and exchanges can be built. In this scenario, Governments could control the type of projects and impose regulations and standards upon the developers and the user community. In such fully centralised Blockchains, the government could allow the development of centralised and decentralised crypto exchanges and fund or encourage the development of CBDCs (Central Bank Digital Currencies) and regulated Stablecoins (cryptocurrency with a pegged value to another currency, commodity, or financial instrument). By enabling the development of a fully regulated Stablecoin, the UK Government would prevent one of the main risks for individual crypto savers: the collapse of another Stablecoin, which happened to the UST Algorithmic Stablecoin in 2022. Many of the current stablecoins are highly speculative, and at present most stablecoins are not audited or regulated – at least not in any meaningful way. Although Tether (USDT) has announced that it is preparing to be audited by a large accounting firm to prove the transparency of Tether, at present, USDT market reserves are not audited. As of today, Tether's market cap is $66,268,895,618. Around $11,106,992,770 of the cryptocurrency stablecoins traded in the last 24 hours alone. Tether (USDT) is just one of many stablecoins on the many current crypto exchanges. In the top 10 cryptocurrencies by market cap, apart from USDT, we also have the USDC (market cap of $43,922,152,193) and BUSD (market cap of $16,377,185,225).
- In contrast, in 11th place, we have DAI (market cap of $5,790,436,026). In the 41st place, we have USDP (market cap of $876,254,775). On the 43rd place is TUSD (market cap of $846,271,617), in the 52nd place is USDD (market cap of $707,743,989) and so on – data from the 8th of January 2023 [139]. From the above-listed stablecoins, USDC has reserves regularly attested but not audited. None of the stablecoins are audited. This creates a systemic risk for all cryptocurrencies, and regulating the stablecoins will not only prevent future loss of savings for individual users and savers (hodlers), but it would increase the confidence in the market. Combined with a regulated crypto exchange, it would provide security and quick exit for investors during times of volatility. In the final comment on CBDCs, we must point out that the view emerging from this article is not sympathetic to the values of society and economy from CBDCs. Although CBDCs would resolve many issues related to fluctuations in the price of all cryptocurrencies, the stablecoin solution could be a preferred version of a Blockchain-based currency, specifically, decentralised stablecoins. However, the collapse of UST – LUNA has exposed vulnerabilities in some of the decentralised algorithmic stablecoins. We need new solutions to address some of the vulnerabilities disclosed in 2022.
- The main lesson we must learn from FTX is that without taking regulatory action, corporate malfunction and malfeasance cases will continue to dominate the cryptocurrency ecosystems. Even if governments worldwide embrace the concept of complete monetary decentralisation (which seems highly unlikely), some crypto market elements still need to be regulated to ensure that self-governance is not replaced again with malfeasance. The collapse of FTX (which was considered one of the safest exchanges because of the public display of approval from various high-profile politicians), has proven that corporate malfeasance exists in cryptocurrencies on a much greater level than we are aware. To put this into perspective, if users start withdrawing large volumes from any of the above-listed stablecoins, it seems questionable if they will survive. That is not to say that the concept of stablecoins should be abandoned or that the currency should be pegged to gold and not to the USD. Stablecoins provide crucial services in the crypto markets, and USD is the most traded currency. The concept seems sound, but the regulations, standards and accountancy audits are missing.
6. Survey of Crypto use cases
- Borderless payments without any centralised entities acting as an intermediary,
- Decentralised finance for lending and borrowing, accessible to anyone and everyone that has an internet connection and knows how to use the specific blockchain–crypto project,
- Security and privacy of products (and services) as they move through different supply chains,
- Authenticity verification for products and services,
- Ensuring payments are processed somewhat in supply chains- with the use of smart contracts,
- Buying and owning digital assets, such as gaming and collectables, can be held as non-fungible tokens (NFTs).
- Crypto transactions can be designed to help with privacy and anonymity, creating added value for users that prefer to keep their finances private.
- Crypto can be used for crowdfunding, where new funds can be raised by issuing initial coin offerings (ICO) or token generation events (TGEs).
- Creatives can use crypto to monetise their work. For example, digital content creators can accept payments for premium content, opening a safer and cheaper environment for various artists, from dancers, tutors, and painters to fitness instructors, digital consultants and education providers.
- Charitable donations, crypto can be used as a fast and secure method for transferring wealth to people in need.
6.1. Evolution and Uncertainties of the Internet: From Web1 to Web3
6.2. The Buterin's trilemma
7. Discussion
7.1. The good
7.2. The bad
7.3. The ugly
8. Conclusion
8.1. Final comments
Funding
Acknowledgments
Abbreviations
| Bitcoin | the first decentralised blockchain. |
| Terra Luna | collapsed crypto project. |
| FTX | collapsed crypto exchange. |
| Solana (SOL) | crypto project that got affected by the FTX collapse. |
| Ethereum, Cardano, Dogecoin, Litecoin, Algorand, NEAR | crypto projects that remained popular with investors in the 2021 bull run. |
| IOTA, NEO, EOS | crypto projects that were popular in the previous bull runs, and are still present in the crypto market in 2023. |
| NEFD | new and emerging forms of data. |
| CBDCs | Central Bank Digital Currencies. |
| Tornado Cash DAO | crypto mixer that has been prohibited for use by the USA |
| UST Algorithmic Stablecoin | collapsed stablecoin. |
| USDT, USDC, DAI, BUSD, USDP, USDD, TUSD | Stablecoins still in existence in 2023 (as of 25th of January 2023). |
| NHS | National health Service. |
| Uniswap / SushiSwap | decentralised exchanges. |
| NFTs | non-fungible tokens. |
| ICO | initial coin offerings. |
| TGEs | token generation events. |
| ChatGPT | AI based chat designed to replace the Google search engine. |
| M-Pesa | SIM card payment from a mobile phone. |
| We Chat Pay | a QR Code payment. |
| KYC | know your customer. |
| 1 | |
| 2 | |
| 3 | |
| 4 | |
| 5 | |
| 6 | |
| 7 |
References
- S. Nakamoto, “Bitcoin: A peer-to-peer electronic cash system,” Decentralized Business Review, p. 21260, 2008.
- C. Dierksmeier and P. Seele, “Cryptocurrencies and Business Ethics,” Journal of Business Ethics, vol. 152, no. 1, pp. 1–14, Sep. 2018. [CrossRef]
- Mikhaylov, H. Dinçer, and S. Yüksel, “Analysis of financial development and open innovation oriented fintech potential for emerging economies using an integrated decision-making approach of MF-X-DMA and golden cut bipolar q-ROFSs,” Financial Innovation, vol. 9, no. 1, pp. 1–34, Dec. 2023. [CrossRef]
- Khan et al., “QoS-Ledger: Smart Contracts and Metaheuristic for Secure Quality-of-Service and Cost-Efficient Scheduling of Medical-Data Processing,” Electronics 2021, Vol. 10, Page 3083, vol. 10, no. 24, p. 3083, Dec. 2021. [CrossRef]
- M. C. Chang and D. Park, “How Can Blockchain Help People in the Event of Pandemics Such as the COVID-19?,” Journal of Medical Systems, vol. 44, no. 5. Springer, May 01, 2020. [CrossRef]
- Pranggono and A. Arabo, “COVID-19 pandemic cybersecurity issues,” Internet Technology Letters, vol. 4, no. 2, p. e247, Mar. 2021. [CrossRef]
- S. W. Ting, L. Carin, V. Dzau, and T. Y. Wong, “Digital technology and COVID-19,” Nature Medicine, Nature Research, pp. 1–3, Mar. 27, 2020. [CrossRef]
- Bouri, X. V. Vo, and T. Saeed, “Return equicorrelation in the cryptocurrency market: Analysis and determinants,” Financ Res Lett, vol. 38, p. 101497, Jan. 2021. [CrossRef]
- Y. Malhotra, “Advancing Cyber Risk Insurance Underwriting Model Risk Management beyond VaR to Pre-Empt and Prevent the Forthcoming Global Cyber Insurance Crisis.” Dec. 07, 2017. Accessed: Mar. 22, 2018. [Online]. Available: https://papers.ssrn.com/sol3/papers.cfm?abstract_id=3081492.
- FAIR, “What is a Cyber Value-at-Risk Model?,” 2017. http://www.fairinstitute.org/blog/what-is-a-cyber-value-at-risk-model (accessed Dec. 25, 2017).
- P. Jorion, Value at risk: the new benchmark for controlling market risk. Irwin Professional Pub., 1997.
- Khorshidi and V. R. Ghezavati, “Application of mathematical modeling value-at-risk (VaR) to optimize decision making in distribution networks,” SN Appl Sci, vol. 1, no. 12, p. 1671, Dec. 2019. [CrossRef]
- J. Buith, “Cyber Value at Risk in the Netherlands,” 2016. Accessed: Apr. 03, 2017. [Online]. Available: https://www2.deloitte.com/content/dam/Deloitte/nl/Documents/financial-services/deloitte-nl-fsi-cyber-value-at-risk.pdf.
- T. Aspembitova, L. Feng, and L. Y. Chew, “Behavioral structure of users in cryptocurrency market,” PLoS One, vol. 16, no. 1, p. e0242600, Jan. 2021. [CrossRef]
- F. Breidbach and S. Tana, “Betting on Bitcoin: How social collectives shape cryptocurrency markets,” J Bus Res, vol. 122, pp. 311–320, Jan. 2021. [CrossRef]
- The Federal Reserve, “Central Bank Digital Currency (CBDC),” 2022. [Online]. Available: https://www.federalreserve.gov/central-bank-digital-currency.htm.
- T. Hansen and K. Delak, “Security Considerations for a Central Bank Digital Currency,” FEDS Notes, vol. 2022, no. 2970, Feb. 2022. [CrossRef]
- P. Cheng, “Decoding the rise of Central Bank Digital Currency in China: designs, problems, and prospects,” Journal of Banking Regulation 2022, pp. 1–15, Feb. 2022. [CrossRef]
- Y. Mikhaylov, “Development of Friedrich von Hayekʼs theory of private money and economic implications for digital currencies,” Terra Economicus, vol. 19, no. 1, pp. 53–62, 2021. [CrossRef]
- HMT, “UK sets out plans to regulate crypto and protect consumers - GOV.UK,” HM Treasury - Gov.UK, Feb. 01, 2023. https://www.gov.uk/government/news/uk-sets-out-plans-to-regulate-crypto-and-protect-consumers (accessed Mar. 05, 2023).
- K. M. Eisenhardt, “Building Theories from Case Study Research,” The Academy of Management Review, vol. 14, no. 4, p. 532, Oct. 1989. [CrossRef]
- R. K. Yin, Case study research: Design and methods, vol. 5. Sage, 2009.
- K. Charmaz, Constructing grounded theory : a practical guide through qualitative analysis. Sage Publications, 2006.
- G. Glaser and A. L. Strauss, The discovery of grounded theory : strategies for qualitative research. Abingdon, Oxford: Routledge, 1967.
- Christina. Goulding, Grounded theory : a practical guide for management, business and market researchers. SAGE, 2002.
- M. Xu, X. Chen, and G. Kou, “A systematic review of blockchain,” Financial Innovation, vol. 5, no. 1, pp. 1–14, Dec. 2019. [CrossRef]
- Fang et al., “Cryptocurrency trading: a comprehensive survey,” Financial Innovation, vol. 8, no. 1, pp. 1–59, Dec. 2022. [CrossRef]
- Sebastião and P. Godinho, “Forecasting and trading cryptocurrencies with machine learning under changing market conditions,” Financial Innovation, vol. 7, no. 1, pp. 1–30, Dec. 2021. [CrossRef]
- Zhang, G. Kou, and Y. Peng, “Soft consensus cost models for group decision making and economic interpretations,” Eur J Oper Res, vol. 277, no. 3, pp. 964–980, Sep. 2019. [CrossRef]
- G. Kou, Ö. Olgu Akdeniz, H. Dinçer, and S. Yüksel, “Fintech investments in European banks: a hybrid IT2 fuzzy multidimensional decision-making approach,” Financial Innovation, vol. 7, no. 1, pp. 1–28, Dec. 2021. [CrossRef]
- T. Li, G. Kou, Y. Peng, and P. S. Yu, “An Integrated Cluster Detection, Optimization, and Interpretation Approach for Financial Data,” IEEE Trans Cybern, vol. 52, no. 12, pp. 13848–13861, Dec. 2022. [CrossRef]
- G. Kou, X. Chao, Y. Peng, F. E. Alsaadi, and E. Herrera-Viedma, “Machine learning methods for systemic risk analysis in financial sectors,” Technological and Economic Development of Economy, vol. 25, no. 5, pp. 716–742, May 2019. [CrossRef]
- G. Kou, Y. Peng, and G. Wang, “Evaluation of clustering algorithms for financial risk analysis using MCDM methods,” Inf Sci (N Y), vol. 275, pp. 1–12, Aug. 2014. [CrossRef]
- M. Kumar, N. Nikhil, and R. Singh, “Decentralising finance using decentralised blockchain oracles,” 2020 International Conference for Emerging Technology, INCET 2020, Jun. 2020. [CrossRef]
- V. Sharma, V. Orindi, C. Hesse, J. Pattison, and S. Anderson, “Supporting local climate adaptation planning and implementation through local governance and decentralised finance provision,” https://doi.org/10.1080/09614524.2014.907240, vol. 24, no. 4, pp. 579–590, 2014. [CrossRef]
- M. Yu, F. S. Tsai, H. Jin, and H. Zhang, “Digital finance and renewable energy consumption: evidence from China,” Financial Innovation 2022 8:1, vol. 8, no. 1, pp. 1–19, May 2022. [CrossRef]
- Y. Chen, Y. Zhang, and B. Zhou, “Research on the risk of block chain technology in Internet finance supported by wireless network,” EURASIP J Wirel Commun Netw, vol. 2020, no. 1, pp. 1–11, Dec. 2020. [CrossRef]
- Z. Dong, F. Luo, and G. Liang, “Blockchain: a secure, decentralized, trusted cyber infrastructure solution for future energy systems,” Journal of Modern Power Systems and Clean Energy, vol. 6, no. 5, pp. 958–967, Sep. 2018. [CrossRef]
- P. Liu and P. Chu, “Renewables finance and investment: how to improve industry with private capital in China,” Journal of Modern Power Systems and Clean Energy, vol. 7, no. 6, pp. 1385–1398, Nov. 2019. [CrossRef]
- P. O’Brien and A. Pike, “‘The governance of local infrastructure funding and financing,’” Infrastructure Complexity 2015 2:1, vol. 2, no. 1, pp. 1–9, Jun. 2015. [CrossRef]
- G. Falchetta, B. Michoud, M. Hafner, and M. Rother, “Harnessing finance for a new era of decentralised electricity access: A review of private investment patterns and emerging business models,” Energy Res Soc Sci, vol. 90, p. 102587, Aug. 2022. [CrossRef]
- Y. Faqir-Rhazoui, J. Arroyo, and S. Hassan, “A comparative analysis of the platforms for decentralized autonomous organizations in the Ethereum blockchain,” Journal of Internet Services and Applications, vol. 12, no. 1, pp. 1–20, Dec. 2021. [CrossRef]
- V. Mohan, “Automated market makers and decentralized exchanges: a DeFi primer,” Financial Innovation, vol. 8, no. 1, pp. 1–48, Dec. 2022. [CrossRef]
- F. Fang et al., “Cryptocurrency trading: a comprehensive survey,” Financial Innovation, vol. 8, no. 1, pp. 1–59, Dec. 2022. [CrossRef]
- T. van der Linden and T. Shirazi, “Markets in crypto-assets regulation: Does it provide legal certainty and increase adoption of crypto-assets?,” Financial Innovation, vol. 9, no. 1, pp. 1–30, Dec. 2023. [CrossRef]
- Chu, S. Chan, and Y. Zhang, “An analysis of the return–volume relationship in decentralised finance (DeFi),” International Review of Economics & Finance, vol. 85, pp. 236–254, May 2023. [CrossRef]
- Yavin and A. Reardon, “What digital banks can learn from decentralised finance”.
- G. C. Maia and J. Vieira dos Santos, “MiCA and DeFi (‘Proposal for a Regulation on Market in Crypto-Assets’ and ’Decentralised Finance’),” SSRN Electronic Journal, Jul. 2021. [CrossRef]
- M. Barrett, J. Marron, V. Yan Pillitteri, J. Boyens, G. Witte, and L. Feldman, “Draft NISTIR 8170, The Cybersecurity Framework: Implementation Guidance for Federal Agencies,” Maryland, 2017. Accessed: Mar. 08, 2018. [Online]. Available: https://csrc.nist.gov/CSRC/media/Publications/nistir/8170/draft/documents/nistir8170-draft.pdf.
- P. K. Ozili, “DECENTRALISED FINANCE AND CRYPTOCURRENCY ACTIVITY IN AFRICA,” Contemporary Studies in Economic and Financial Analysis, vol. 109A, pp. 3–11, 2022. [CrossRef]
- R. N. Marishane and R. J. Botha, “Empowering school-based management through decentralised financial control,” https://doi.org/10.1080/18146620408566272, vol. 1, no. 1, pp. 95–112, Jan. 2008. [CrossRef]
- C. Eikmanns, P. Mehrwald, P. G. Sandner, and I. M. Welpe, “Decentralised finance platform ecosystems: conceptualisation and outlook,” https://doi.org/10.1080/09537325.2022.2163886, 2023. [CrossRef]
- T. Miller, S. Cao, M. Foth, X. Boyen, and W. Powell, “An asset-backed decentralised finance instrument for food supply chains – A case study from the livestock export industry,” Comput Ind, vol. 147, p. 103863, May 2023. [CrossRef]
- M. Sumah, L. Baatiema, and S. Abimbola, “The impacts of decentralisation on health-related equity: A systematic review of the evidence,” Health Policy (New York), vol. 120, no. 10, pp. 1183–1192, Oct. 2016. [CrossRef]
- Makarov and A. Schoar, “Cryptocurrencies and Decentralised Finance (DeFi),” Bank for International Settlements, 2022, Accessed: Apr. 24, 2023. [Online]. Available: www.bis.org.
- S. K. Routray, M. K. Jha, L. Sharma, R. Nyamangoudar, A. Javali, and S. Sarkar, “Quantum cryptography for IoT: APerspective,” IEEE International Conference on IoT and its Applications, ICIOT 2017, Oct. 2017. [CrossRef]
- NIST, “Post-Quantum Cryptography PQC,” 2022. https://csrc.nist.gov/Projects/post-quantum-cryptography.
- NIST, “Post-Quantum Cryptography | CSRC | Competition for Post-Quantum Cryptography Standardisation,” 2022. Accessed: Mar. 16, 2023. [Online]. Available: https://csrc.nist.gov/projects/post-quantum-cryptography.
- H. Bennett and G. Brassard, “Quantum cryptography: Public key distribution and coin tossing,” in Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, New York, 1984, pp. 1–8. Accessed: Mar. 16, 2023. [Online]. Available: https://web.archive.org/web/20200130165639/http://researcher.watson.ibm.com/researcher/files/us-bennetc/BB84highest.pdf.
- Gyongyosi and S. Imre, “Secret Key Rate Adaption for Multicarrier Continuous-Variable Quantum Key Distribution,” SN Comput Sci, vol. 1, no. 1, pp. 1–17, Jan. 2020. [CrossRef]
- P. W. Shor, “Polynomial-Time Algorithms for Prime Factorization and Discrete Logarithms on a Quantum Computer,” SIAM Journal on Computing, vol. 26, no. 5, pp. 1484–1509, Oct. 1997. [CrossRef]
- NIST, “Post-Quantum Cryptography | CSRC | Selected Algorithms: Public-key Encryption and Key-establishment Algorithms,” 2022. Accessed: Mar. 16, 2023. [Online]. Available: https://csrc.nist.gov/Projects/post-quantum-cryptography/selected-algorithms-2022.
- B. Farahani, F. Firouzi, and K. Chakrabarty, “Healthcare IoT,” in Intelligent Internet of Things, Springer International Publishing, 2020, pp. 515–545. [CrossRef]
- Piya, Q. A. Au, S. Shrestha, A. Singh, and T. K. Mohd, “IoT in Health Care Industry: A Promising Prospect,” pp. 0466–0474, Jan. 2022. [CrossRef]
- Aldahiri, B. Alrashed, and W. Hussain, “Trends in Using IoT with Machine Learning in Health Prediction System,” Forecasting, vol. 3, no. 1, pp. 181–206, Mar. 2021. [CrossRef]
- R. Rastogi, P. Singhal, D. K. Chaturvedi, and M. Gupta, “Investigating Correlation of Tension-Type Headache and Diabetes: IoT Perspective in Health care,” Springer, Singapore, 2021, pp. 71–91. [CrossRef]
- Banerjee, C. Chakraborty, A. Kumar, and D. Biswas, “Emerging trends in IoT and big data analytics for biomedical and health care technologies,” in Handbook of Data Science Approaches for Biomedical Engineering, Elsevier, 2020, pp. 121–152. [CrossRef]
- K. Jayavel, V. Nagarajan, and G. Sharma, “An Analysis of IOT Test beds with Application in the Field of Medicine and Health Care,” Research J. Pharm. and Tech, vol. 10, no. 12, 2017. [CrossRef]
- J. L. Beavers, M. Faulks, and J. Marchang, “Hacking NHS Pacemakers: A Feasibility Study,” Proceedings of 12th International Conference on Global Security, Safety and Sustainability, ICGS3 2019, Apr. 2019. [CrossRef]
- X. Feng, M. Conrad, and K. Hussein, “NHS Big Data Intelligence on Blockchain Applications,” pp. 191–208, 2022. [CrossRef]
- NHS Digital, “Adult Psychiatric Morbidity Survey (APMS): Survey of Mental Health and Wellbeing, England, 2014 - NHS Digital,” England, Sep. 2016.
- U. D. Ani, J. D. McK. Watson, J. R. C. Nurse, A. Cook, and C. Maple, “A Review of Critical Infrastructure Protection Approaches: Improving Security through Responsiveness to the Dynamic Modelling Landscape,” in PETRAS/IET Conference Living in the Internet of Things: Cybersecurity of the IoT - 2019, Apr. 2019, pp. 1–16. Accessed: Sep. 03, 2019. [Online]. Available: http://arxiv.org/abs/1904.01551.
- S. Jalali, J. P. Kaiser, M. Siegel, and S. Madnick, “The Internet of Things Promises New Benefits and Risks: A Systematic Analysis of Adoption Dynamics of IoT Products,” IEEE Secur Priv, vol. 17, no. 2, pp. 39–48, Mar. 2019. [CrossRef]
- Crawford and J. Sherman, “Gaps in United States federal government IoT security and privacy policies,” Journal of Cyber Policy, vol. 3, no. 2, pp. 187–200, May 2018. [CrossRef]
- B. Russell and D. Van Duren, Practical internet of things security : a practical, indispensable security guide that will navigate you through the complex realm of securely building and deploying systems in our IoT-connected world. 2016. Accessed: Mar. 05, 2019. [Online]. Available: https://www.packtpub.com/hardware-and-creative/practical-internet-things-security.
- Roopak, G. Yun Tian, and J. Chambers, “Deep learning models for cyber security in IoT networks,” in 2019 IEEE 9th Annual Computing and Communication Workshop and Conference, CCWC 2019, Institute of Electrical and Electronics Engineers Inc., Mar. 2019, pp. 452–457. [CrossRef]
- S. Latvala, M. Sethi, and T. Aura, “Evaluation of Out-of-Band Channels for IoT Security,” SN Comput Sci, vol. 1, no. 1, pp. 1–17, Jan. 2020. [CrossRef]
- H. Abie and I. Balasingham, “Risk-Based Adaptive Security for Smart IoT in eHealth,” SeTTIT 2012, September 24-26, Oslo, Norway, 2012, Accessed: Mar. 24, 2018. [Online]. Available: https://pdfs.semanticscholar.org/c39d/04c6f3b84c77ad379d0358bfbe7148ad4fd2.pdf.
- Brass, L. Tanczer, M. Carr, M. Elsden, and J. Blackstock, “Standardising a Moving Target: The Development and Evolution of IoT Security Standards,” in Living in the Internet of Things: Cybersecurity of the IoT - 2018, Institution of Engineering and Technology, 2018, pp. 24 (9 pp.)-24 (9 pp.). [CrossRef]
- Ayad, A. Zamani, A. Schmeink, and G. Dartmann, “Design and Implementation of a Hybrid Anomaly Detection System for IoT,” in 2019 6th International Conference on Internet of Things: Systems, Management and Security, IOTSMS 2019, Institute of Electrical and Electronics Engineers Inc., Oct. 2019, pp. 87–92. [CrossRef]
- R. Ahmad and I. Alsmadi, “Machine learning approaches to IoT security: A systematic literature review,” Internet of Things, vol. 14, p. 100365, Jun. 2021. [CrossRef]
- Dubois, K. Hulthén, and A.-C. Pedersen, “Supply chains and interdependence: a theoretical analysis,” Journal of Purchasing and Supply management, vol. 10, no. 1, pp. 3–9, Jan. 2004. [CrossRef]
- T. Mentzer et al., “Defining supply chain management,” Wiley Online Library, 2001.
- Zheng and L. A. Albert, “A Robust Approach for Mitigating Risks in Cyber Supply Chains,” Risk Analysis, vol. 39, no. 9, pp. 2076–2092, Sep. 2019. [CrossRef]
- T. Qu, G. Q. Huang, V.-D. Cung, and F. Mangione, “Optimal configuration of assembly supply chains using analytical target cascading,” Int J Prod Res, vol. 48, no. 23, pp. 6883–6907, Dec. 2010. [CrossRef]
- Sukati, A. B. Hamid, R. Baharun, and R. M. Yusoff, “The study of supply chain management strategy and practices on supply chain performance,” Procedia-Social and Behavioral Sciences, vol. 40, pp. 225–233, 2012.
- Dotoli, M. P. Fanti *, C. Meloni, and M. C. Zhou, “A multi-level approach for network design of integrated supply chains,” Int J Prod Res, vol. 43, no. 20, pp. 4267–4287, Oct. 2005. [CrossRef]
- V. Manthou, M. Vlachopoulou, and D. Folinas, “Virtual e-Chain (VeC) model for supply chain collaboration,” Int J Prod Econ, vol. 87, no. 3, pp. 241–250, 2004.
- R. Cigolini, M. Cozzi, and M. Perona, “A new framework for supply chain management,” International Journal of Operations & Production Management, vol. 24, no. 1, pp. 7–41, Jan. 2004. [CrossRef]
- R. Shaw, V. Takanti, T. Zullo, M. Director, and E. Llc, “Best Practices in Cyber Supply Chain Risk Management Boeing and Exostar Cyber Security Supply Chain Risk Management Interviews,” 2017. Accessed: Mar. 08, 2018. [Online]. Available: https://www.nist.gov/sites/default/files/documents/itl/csd/NIST_USRP-Boeing-Exostar-Case-Study.pdf.
- H. Fatorachian and H. Kazemi, “Impact of Industry 4.0 on supply chain performance,” Production Planning and Control, vol. 32, no. 1, pp. 63–81, 2021. [CrossRef]
- B. M. Beamon, “Environmental and sustainability ethics in supply chain management,” Sci Eng Ethics, vol. 11, no. 2, pp. 221–234, Jun. 2005. [CrossRef]
- S. Boyson and T. Corsi, “Building A Cyber Supply Chain Assurance Reference Model,” 2009. Accessed: Aug. 03, 2017. [Online]. Available: https://pdfs.semanticscholar.org/2757/9fc90accd57e0e5e4f402e33f0598841bafb.pdf.
- S.-H. Liao, D.-C. Hu, and L.-W. Ding, “Assessing the influence of supply chain collaboration value innovation, supply chain capability and competitive advantage in Taiwan’s networking communication industry,” Int J Prod Econ, vol. 191, pp. 143–153, Sep. 2017. [CrossRef]
- R. Azzi, R. K. Chamoun, and M. Sokhn, “The power of a blockchain-based supply chain,” Comput Ind Eng, vol. 135, pp. 582–592, Sep. 2019. [CrossRef]
- Jayaram and K.-C. Tan, “Supply chain integration with third-party logistics providers,” Int J Prod Econ, vol. 125, no. 2, pp. 262–271, 2010.
- D. Sachdev, “Enabling data democracy in supply chain using blockchain and IoT,” Journal of Management (JOM), vol. 6, no. 1, pp. 66–83, 2019, Accessed: Apr. 21, 2020. [Online]. Available: http://www.iaeme.com/JOM/index.asp66http://www.iaeme.com/JOM/issues.asp?JType=JOM&VType=6&IType=1http://www.iaeme.com/JOM/issues.asp?JType=JOM&VType=6&IType=1.
- Ben-Daya, E. Hassini, and Z. Bahroun, Internet of things and supply chain management: a literature review, vol. 57, no. 15–16. Taylor and Francis Ltd., 2019, pp. 4719–4742. [CrossRef]
- B. Yen, A. Farhoomand, and P. Ng, “Constructing an e-Supply Chain at Eastman Chemical Company,” Journal of Information Technology, vol. 19, no. 2, pp. 93–107, Jun. 2004. [CrossRef]
- C. Martínez-Olvera, D. Shunk, C. Martinez-Olvera, and D. Shunk, “Comprehensive framework for the development of a supply chain strategy,” Int J Prod Res, vol. 44, no. 21, pp. 4511–4528, Nov. 2006. [CrossRef]
- C. C. Bozarth, D. P. Warsing, B. B. Flynn, and E. J. Flynn, “The impact of supply chain complexity on manufacturing plant performance,” Journal of Operations Management, vol. 27, no. 1, pp. 78–93, 2009.
- Frohlich and R. Westbrook, “Arcs of Integration: An International Study of Supply Chain Strategies,” 2001.
- Chowdhury, S. K. Paul, S. Kaisar, and M. A. Moktadir, “COVID-19 pandemic related supply chain studies: A systematic review,” Transp Res E Logist Transp Rev, vol. 148, p. 102271, Apr. 2021. [CrossRef]
- X. F. Shao, W. Liu, Y. Li, H. R. Chaudhry, and X. G. Yue, “Multistage implementation framework for smart supply chain management under industry 4.0,” Technol Forecast Soc Change, vol. 162, p. 120354, Jan. 2021. [CrossRef]
- Bär, Z. N. L. Herbert-Hansen, and W. Khalid, “Considering Industry 4.0 aspects in the supply chain for an SME,” Production Engineering, vol. 12, no. 6, pp. 747–758, Dec. 2018. [CrossRef]
- Leng and X. Chen, “A genetic algorithm approach for TOC-based supply chain coordination,” Applied Mathematics and Information Sciences, vol. 6, no. 3, pp. 767–774, 2012.
- Heckmann, T. Comes, and S. Nickel, “A critical review on supply chain risk-Definition, measure and modeling,” Omega (Westport), vol. 52, pp. 119–132, 2015. [CrossRef]
- R. Cigolini, M. Cozzi, and M. Perona, “A new framework for supply chain management: conceptual model and empirical test,” International Journal of Operations & Production Management, vol. 24, no. 1, pp. 7–41, 2004.
- T. J. Strader, F.-R. Lin, and M. J. Shaw, “Business-to-business electronic commerce and convergent assembly supply chain management,” Journal of Information Technology, vol. 14, no. 4, pp. 361–373, Dec. 1999. [CrossRef]
- J. Schnetzler, A. Sennheiser, and P. Schönsleben, “A decomposition-based approach for the development of a supply chain strategy,” Int J Prod Econ, vol. 105, no. 1, pp. 21–42, Jan. 2007. [CrossRef]
- Sakka, P.-A. Millet, and V. Botta-Genoulaz, “An ontological approach for strategic alignment: a supply chain operations reference case study,” Int J Comput Integr Manuf, vol. 24, no. 11, pp. 1022–1037, 2011.
- T. Lu, X. Guo, B. Xu, L. Zhao, Y. Peng, and H. Yang, “Next Big Thing in Big Data: The Security of the ICT Supply Chain,” in 2013 International Conference on Social Computing, IEEE, Sep. 2013, pp. 1066–1073. [CrossRef]
- W. Jackson, “Code, Cars, and Congress: A Time for Cyber Supply Chain Management (1 of 3),” Sonatype, 2014. https://blog.sonatype.com/2014/12/cyber-supply-chain-management-part1/ (accessed Jan. 02, 2023).
- K. Dutta and S. Mitra, “Application of Agricultural Drones and IoT to Understand Food Supply Chain During Post COVID-19,” in Agricultural Informatics, Wiley, 2021, pp. 67–87. [CrossRef]
- R. G. G. Caiado, L. F. Scavarda, L. O. Gavião, P. Ivson, D. L. de M. Nascimento, and J. A. Garza-Reyes, “A fuzzy rule-based industry 4.0 maturity model for operations and supply chain management,” Int J Prod Econ, vol. 231, p. 107883, Jan. 2021. [CrossRef]
- D. Ivanov, “An adaptive framework for aligning (re)planning decisions on supply chain strategy, design, tactics, and operations,” Int J Prod Res, vol. 48, no. 13, pp. 3999–4017, Jul. 2010. [CrossRef]
- R. Royce, “H.R.5793 - 113th Congress (2013-2014): Cyber Supply Chain Management and Transparency Act of 2014,” Congress.Gov, 2014. http://www.congress.gov/ (accessed Jan. 02, 2023).
- R. Perez-Franco, “A methodology to capture, evaluate and reformulate a firm’s supply chain strategy as a conceptual system.” Massachusetts Institute of Technology, 2010.
- Nikolopoulos, S. Punia, A. Schäfers, C. Tsinopoulos, and C. Vasilakis, “Forecasting and planning during a pandemic: COVID-19 growth rates, supply chain disruptions, and governmental decisions,” Eur J Oper Res, vol. 290, no. 1, pp. 99–115, Apr. 2021. [CrossRef]
- Pramatari, T. Evgeniou, and G. Doukidis, “Implementation of collaborative e-supply-chain initiatives: an initial challenging and final success case from grocery retailing,” Journal of Information Technology, vol. 24, no. 3, pp. 269–281, Sep. 2009. [CrossRef]
- D. Prajogo and J. Olhager, “Supply chain integration and performance: The effects of long-term relationships, information technology and sharing, and logistics integration,” Int J Prod Econ, vol. 135, no. 1, pp. 514–522, 2012.
- S. K. Vickery, J. Jayaram, C. Droge, and R. Calantone, “The effects of an integrative supply chain strategy on customer service and financial performance: an analysis of direct versus indirect relationships,” Journal of operations management, vol. 21, no. 5, pp. 523–539, 2003.
- Moore et al., “Scudo: A Proposal for Resolving Software Supply Chain Insecurities in Vehicles The second in a series of whitepapers on emerging and critical issues in automotive cybersecurity”.
- NTIA, “SBOM at a Glance,” NTIA Multistakeholder Process on Software Component Transparency | ntia.gov/sbom, 2021. https://tiny.cc/SPDX (accessed Jan. 02, 2023).
- J. Wiesner, “CSAF, Not SBOM, Is The Solution,” S4x22 - BSI, 2022. https://www.youtube.com/watch?v=fKlW9vOs7X4&t=504s (accessed Jan. 02, 2023).
- J. S. Meyers, “Are SBOMs Any Good? Preliminary Measurement of the Quality of Open Source Project SBOMs,” Chainguard, 2022. https://www.chainguard.dev/unchained/are-sboms-any-good-preliminary-measurement-of-the-quality-of-open-source-project-sboms (accessed Jan. 02, 2023).
- T. Alrich, “Hmm…It seems SBOMs might become big one of these days…,” Blog, 2022. https://tomalrichblog.blogspot.com/2022/04/hmmit-seems-sboms-might-become-big-one.html (accessed Jan. 02, 2023).
- P. on S. C. T.-S. and F. W. G. NTIA, “Survey of Existing SBOM Formats and Standards-Version 2021 Survey of Existing SBOM Formats and Standards Credit: Photo by Patrick Tomasso on Unsplash NTIA Multistakeholder Process on Software Component Transparency Standards and Formats Working Group,” 2021. Accessed: Dec. 24, 2022. [Online]. Available: https://www.ntia.gov/files/ntia/publications/sbom_formats_survey-version-2021.pdf.
- T. Alrich, “Real-time VEX,” Blog, Sep. 07, 2022. https://tomalrichblog.blogspot.com/2022/09/real-time-vex.html (accessed Jan. 02, 2023).
- S. Springett, “Vulnerability and Exploitability Transparency - VDR & VEX | OWASP Foundation,” OWASP, Feb. 2023. https://owasp.org/blog/2023/02/07/vdr-vex-comparison (accessed Apr. 24, 2023).
- VEX, “Vulnerability Exploitability eXchange (VEX) – Use Cases,” 2022. https://www.cisa.gov/sbom. (accessed Jan. 02, 2023).
- Ishmaev, “The Ethical Limits of Blockchain-Enabled Markets for Private IoT Data,” Philos Technol, pp. 1–22, Jun. 2019. [CrossRef]
- Chanson, A. Bogner, D. Bilgeri, E. Fleisch, and F. Wortmann, “Blockchain for the IoT: Privacy-preserving protection of sensor data,” J Assoc Inf Syst, vol. 20, no. 9, pp. 1271–1307, Sep. 2019. [CrossRef]
- Mozumder, M. M. Sheeraz, A. Athar, S. Aich, and H.-C. Kim, “Overview: Technology Roadmap of the Future Trend of Metaverse based on IoT, Blockchain, AI Technique, and Medical Domain Metaverse Activity,” in International Conference on Advanced Communication Technology (ICACT), Institute of Electrical and Electronics Engineers (IEEE), Mar. 2022, pp. 256–261. [CrossRef]
- V. Chamola, V. Hassija, V. Gupta, and M. Guizani, “A Comprehensive Review of the COVID-19 Pandemic and the Role of IoT, Drones, AI, Blockchain, and 5G in Managing its Impact,” IEEE Access, vol. 8, pp. 90225–90265, 2020. [CrossRef]
- Javaid, M. Zahid, I. Ali, R. J. U. H. Khan, Z. Noshad, and N. Javaid, “Reputation System for IoT Data Monetization Using Blockchain,” in Lecture Notes in Networks and Systems, Springer, 2020, pp. 173–184. [CrossRef]
- D. D. Nguyen and M. I. Ali, “Enabling On-demand decentralized IoT collectability marketplace using blockchain and crowdsensing,” in Global IoT Summit, GIoTS 2019 - Proceedings, Institute of Electrical and Electronics Engineers Inc., Jun. 2019. [CrossRef]
- S. Bajoudah, C. Dong, and P. Missier, “Toward a decentralized, trust-less marketplace for brokered IoT data trading using blockchain,” in Proceedings - 2019 2nd IEEE International Conference on Blockchain, Blockchain 2019, Institute of Electrical and Electronics Engineers Inc., Jul. 2019, pp. 339–346. [CrossRef]
- CoinMarketCap, “Cryptocurrency Prices, Charts And Market Capitalizations | CoinMarketCap.” https://coinmarketcap.com/ (accessed Jan. 08, 2023).
- OFAC, “U.S. Treasury Sanctions Notorious Virtual Currency Mixer Tornado Cash ,” U.S. Department of the Treasury, Aug. 08, 2022. https://home.treasury.gov/news/press-releases/jy0916 (accessed Jan. 08, 2023).
- F. Mogavero, I. Visconti, A. Vitaletti, and M. Zecchini, “The Blockchain Quadrilemma: When Also Computational Effectiveness Matters,” Proc IEEE Symp Comput Commun, vol. 2021-September, 2021. [CrossRef]
- Altarawneh, T. Herschberg, S. Medury, F. Kandah, and A. Skjellum, “Buterin’s Scalability Trilemma viewed through a State-change-based Classification for Common Consensus Algorithms,” 2020 10th Annual Computing and Communication Workshop and Conference, CCWC 2020, pp. 727–736, Jan. 2020. [CrossRef]
- Wang, “Rethinking the Rule and Role of Law in Decentralized Finance,” Proceedings - 2022 IEEE 24th Conference on Business Informatics, CBI 2022, vol. 2, pp. 118–125, 2022. [CrossRef]
- J. Kim, J. S. Hong, H. C. Hwang, S. M. Kim, and D. H. Han, “Comparison of Psychological Status and Investment Style Between Bitcoin Investors and Share Investors,” Front Psychol, vol. 11, p. 3230, Nov. 2020. [CrossRef]
- Johnson et al., “Cryptocurrency trading and its associations with gambling and mental health: A scoping review,” Addictive Behaviors, vol. 136, p. 107504, Jan. 2023. [CrossRef]
- Delfabbro, D. L. King, and J. Williams, “The psychology of cryptocurrency trading: Risk and protective factors,” J Behav Addict, vol. 10, no. 2, p. 201, Jun. 2021. [CrossRef]
- M. Sun and D. Smagalla, “Cryptocurrency-Based Crime Hit a Record $14 Billion in 2021 - WSJ,” The Wall Street Journal, 2022. Accessed: Mar. 08, 2023. [Online]. Available: https://www.wsj.com/articles/cryptocurrency-based-crime-hit-a-record-14-billion-in-2021-11641500073.
| Note about the author: |
 |
| Dr Petar Radanliev began his career as a penetration tester for the military and the defence industry. Subsequently, he transitioned to cyber risk management in the finance sector. After a decade in defence and finance, he re-joined the academic realm, obtaining his Ph.D., MSc, and BA (Hons) from the University of Wales. Before joining Oxford, Petar undertook postdoctoral research projects at Imperial College London, the University of Cambridge, MIT, and the University of North Carolina. He held positions as a Prince of Wales Innovation Scholar at the University of Wales and as a Fulbright Scholar at both MIT and the University of North Carolina. His research areas encompass Artificial Intelligence, Generative Pre-trained Transformers (GPT), Cybersecurity, Blockchain Technologies, Cryptocurrencies, and the Internet of Things. Recent research specialisations include the Software Bill of Materials (SBOM) and the Vulnerability Exploitability Exchange (VEX). |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



