Submitted:
06 June 2023
Posted:
07 June 2023
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Data flow and Mutation Testing
2.1. Data Flow Testing
2.2. Higher-Order Mutation
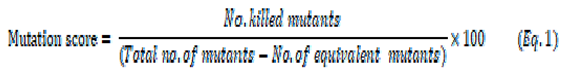
2.3. Relationship between testing criteria
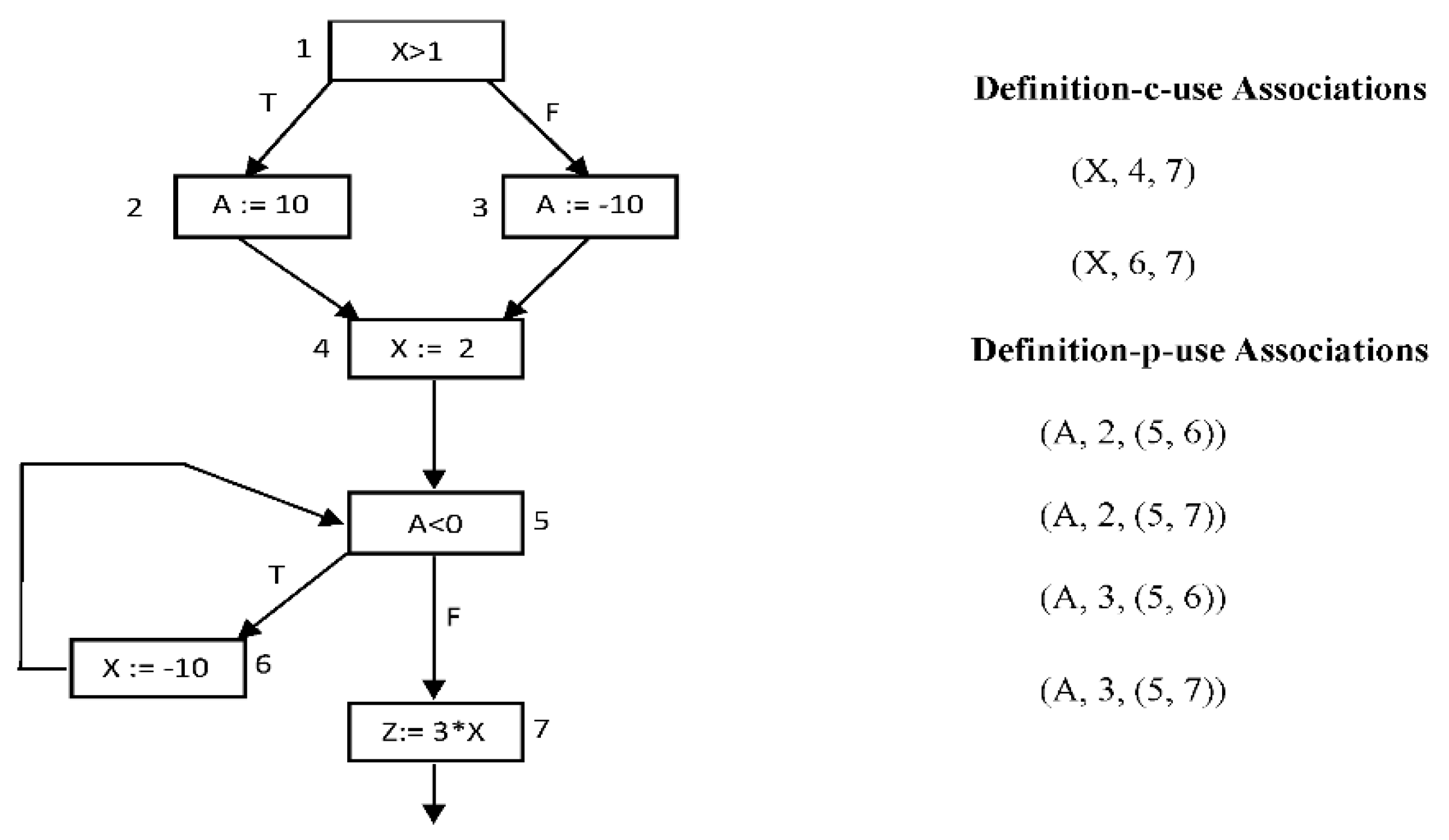
3. The Proposed Approach
3.1. Program analyzer module
- An Instrumented version (P’) of the given original program. The system instruments the assigned programs with software probes. During program execution, these probes cause the number of each traversed line to be recorded to keep track of the path traveled during the execution.
- The static analysis reports contain information about the components of each program: classes, objects, statements, variables, and functions.
- The control flow graph for the tested program.
- The list of variables def-use pairs for the tested program.
3.2. Mutant generator module
3.3. Test data generator module
- Consider the population to be sets of test data (test suite). Each set of test data is represented by a binary string called chromosome.
- Find the sets of test data that represent the initial population. These sets can be randomly generated according to the format and type of data used by the program under test or it may be input to the GAs.
- Determine the fitness of each individual of the population, which is based on a fitness function that is problem dependent.
- Select two individuals that will be combined by some way to contribute to the next generation.
- Apply the crossover and mutation processes.
- The input to this phase includes:
- Instrumented version of the program to be tested.
- List of def-use paths to be covered.
- Number of program input variables.
- Domain and precision of input data.
- Population size.
- Maximum no. of generations.
- Probabilities of crossover and mutation.
- A dynamic analysis report that shows the traversed path(s) and list of covered and uncovered def-use pairs after executing the given program with the test cases generated by the GA.
- Set of test cases (du pairs cover) that cover the def-use paths of the given program, if possible. The GA may fail to find test cases to cover some of the specified def-use paths when they are infeasible (i.e., no test data can be found by the GA to cover them).
- Set of test cases (mutants cover) that cover the mutant.
4. The experiments and results
4.1. Subject programs
4.2. Mutant generator
4.3. GA parameters setup
- Apply the CREAM tool to generate 1st order mutants.
- Generate the 2nd-order mutants for each program by applying the CREAM tool on all 1st-order mutants.
- Eliminate the 2nd-order mutants that are stillborn, equivalent, or don't contain a def or use for any du-pairs.
- Generate the def-uses pairs for each program.
- Eliminate the stillborn and the equivalent mutants from the 1st and 2nd-order mutants.
- Find the killable 2nd-order mutants that affect the du-pairs.
4.4. Comparison hypotheses
4.5. Experimental Results
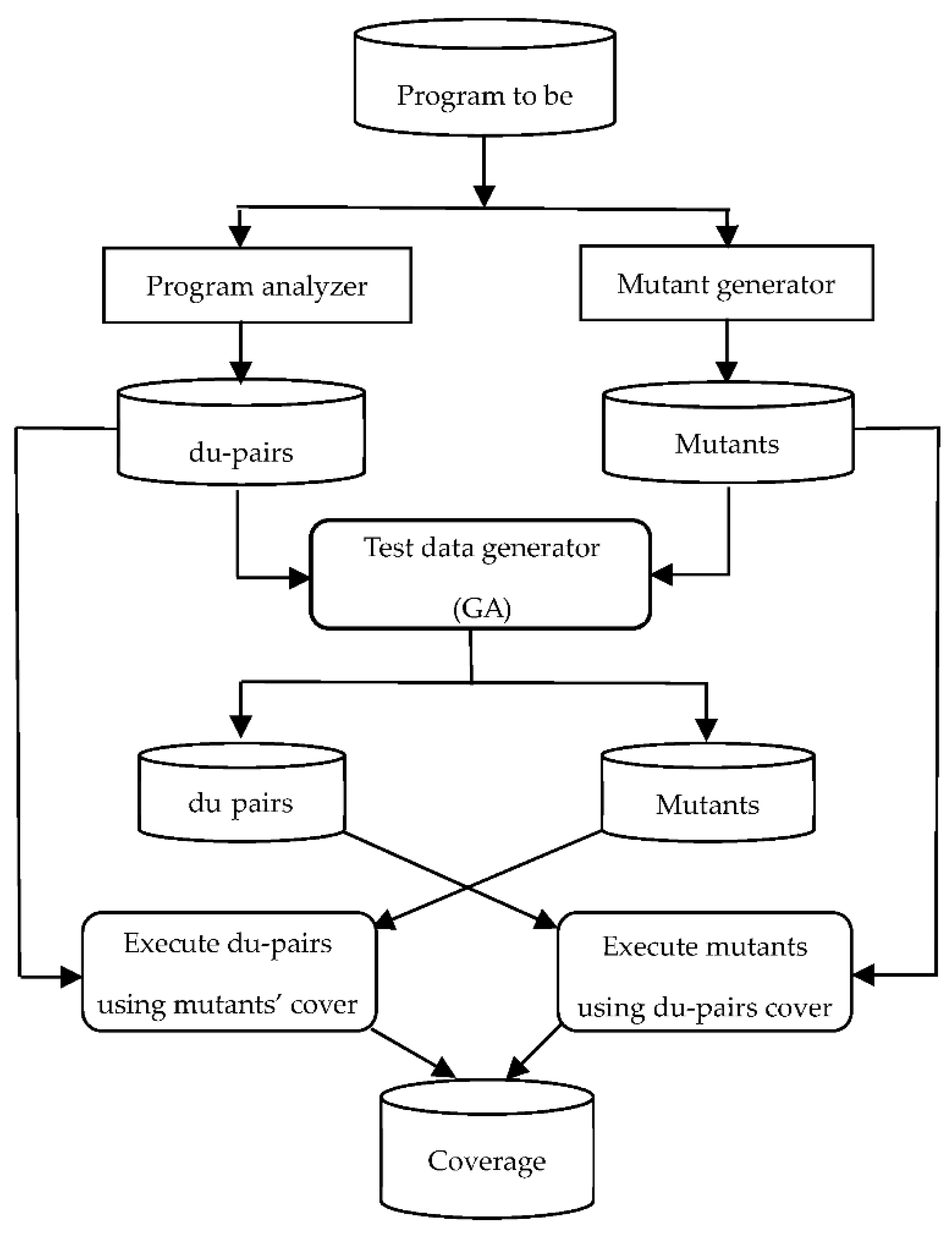
- i. Coverage cost
- 2.
- ii. Coverage adequacy
- 3.
- iii. Failure detection efficiency
5. Conclusion and Future work
Acknowledgments
References
- L. J. White, “Software testing and verification,” In Marshall C. Yovits, editor, Advances in Computers, vol. 26, pp. 335-390, 1987. [CrossRef]
- J. Offutt, J. Pan, K. Tewary and T. Zhang, “An Experimental Evaluation of Data Flow and Mutation Testing,” Journal of Software: Practice and Experience, vol. 26, p. 165–176, 1996.
- P. Mathur and W. E. Wong, “An empirical comparison of data flow and mutation-based adequacy criteria,” Software Testing, Verification, and Reliability, vol. 4, no. 1, pp. 9-31, 1994. [CrossRef]
- J. Offutt and J. M. Voas, “Subsumption of condition coverage techniques by mutation testing,” Technical Report ISSE-TR-96-01 Information and Software Systems Engineering George Mason University Tech. Rep., 1996.
- P. G. Frankl, S. N. Weiss and C. Hu, “All-uses vs. mutation testing: An experimental comparison of effectiveness,” Journal of Systems and Software, vol. 38, no. 3, pp. 235-253, 1997. [CrossRef]
- S. Kakarla, S. Momotaz and A. S. Namin, “An Evaluation of Mutation and Data-Flow Testing: A Meta-analysis,” in 2011 IEEE Fourth International Conference on Software Testing, Verification and Validation Workshops, Berlin, Germany, 2011. [CrossRef]
- I. Bluemke and K. Kulesza, “A Comparison of Dataflow and Mutation Testing of Java Methods,” in Zamojski, W., Kacprzyk, J., Mazurkiewicz, J., Sugier, J., Walkowiak, T. (eds) Dependable Computer Systems. Advances in Intelligent and Soft Computing, Berlin, Heidelberg., Springer, 2011.
- P. Mathur and W. E. Wong, “Comparing the fault detection effectiveness of mutation and data flow testing: An empirical study,” Software Quality Journal, vol. 4, pp. 69-83, 1994.
- K. Tewary and M. J. Harrold, “Fault modeling using the program dependence graph,” in the Fifth International Symposium on Software Reliability Engineering, Monterey CA, 1994. [CrossRef]
- V. Aho, R. Sethi and J. D. Ullman, Compilers, Principles, Techniques, and Tools, Massachusetts: Addison-Wesley Publishing Company, 1986.
- P. G. Frankl and E. J. Weyuker, “An applicable family of data flow testing criteria,” IEEE Transactions on Software Engineering, vol. 14, no. 10, pp. 1483-1498, 1988. [CrossRef]
- Y. Jia and M. Harman, “Higher order mutation testing,” Information and Software Technology, vol. 51, no. 10, p. 1379–1393, 2009. [CrossRef]
- S. Ghiduk, M. R. Girgis and M. H. Shehata, “Higher-order mutation testing: a systematic literature review,” Computer Science Review Journal, vol. 25, p. 9–48, 2017. [CrossRef]
- R. A. DeMillo, R. J. Lipton and F. G. Sayward, “Hints on test data selection: Help for the practicing programmer,” Computer, vol. 11, no. 4, p. 4–41, 1978. [CrossRef]
- R. G. Hamlet, “Testing programs with the aid of a compiler,” IEEE Transactions on Software Engineering, vol. 3, no. 4, p. 279–290, 1977. [CrossRef]
- E. J. Weyuker, S. N. Weiss and R. G. Hamlet, “Comparison of program testing strategies,” in the Fourth Symposium on Software Testing, Analysis, and Verifcation, Victoria, British Columbia, Canada, 1991.
- Z. Michalewicz, Genetic algorithms + Data Structures = Evolution Programs, vol. 3rd, Springer, 1998.
- M. Harman, Y. Jia and B. Langdon, “Strong higher order mutation-based test data generation,” in the 8th European Software Engineering Conference and the ACM SIGSOFT Symposium on the Foundations of Software Engineering (ESEC/FSE ’11), 2011. [CrossRef]
- X. Dang, D. Gong, X. Yao, T. Tian and H. Liu, “Enhancement of Mutation Testing via Fuzzy Clustering and Multi-population Genetic Algorithm,” IEEE Transactions on Software Engineering, 2021. [CrossRef]
- A. Derezi´nska and A. Szustek, “CREAM- A system for object-oriented mutation of C# programs,” Warsaw University of Technology, Warszawa, Poland, 2007.
- Derezi´nska, “Advanced mutation operators applicable in C# programs,” Warsaw University of Technology, Warszawa, Poland, 2005.
- Derezi´nska, “Quality assessment of mutation operators dedicated for C# programs,” in the 6th International Conference on Quality Software (QSIC’06), Beijing, China, 2006. [CrossRef]
| Original version |
Mutated version | ||
|---|---|---|---|
| 1st Order | Higher Order Mutant | ||
| 2nd Order | 3rd Order | ||
|
double n, m double d=n*m double d= n/m |
double n, m double d=n+m double d= n/m |
double n, m double d=n+m double d= n-m |
double n, m double d=n+m double d= n-m++ |
| Title | Description | Scale |
|---|---|---|
| Triangle | find the type of triangle according to its sides’ lengths. | 52 LOC |
| Sort | arrange a group of items | 40 LOC |
| Stack | using push method to enter a group of elements and using pop method to delete element from stack. | 51 LOC |
| Reversed | returns the array after inverting the elements | 44 LOC |
| Clock | return the time in hours, minutes and seconds | 63 LOC |
| Quotient | return the quotient and the remainder of the division between two numbers | 43 LOC |
| Product | find the summation, multiplication and subtraction of three numbers. | 54 LOC |
| Area | find the areas of any circle, triangle or rectangle. | 59 LOC |
| Dist | calling variables with more than one object and printing their dependent values with each call | 52 LOC |
| Middle | find the middle value of three numbers. | 42 LOC |
| Tested Program | all 1st order | killable 1st order | all 2nd order | killable 2nd order | du-based killable 2nd order |
du-pairs |
|---|---|---|---|---|---|---|
| Triangle | 163 | 146 | 30799 | 23799 | 2459 | 102 |
| Sort | 120 | 104 | 15960 | 11547 | 2333 | 95 |
| Stack | 70 | 57 | 5146 | 3507 | 354 | 68 |
| Reversed | 98 | 78 | 10444 | 6620 | 956 | 77 |
| Clock | 78 | 74 | 7638 | 7036 | 109 | 64 |
| Quotient | 156 | 140 | 27184 | 21338 | 2597 | 89 |
| Product | 117 | 101 | 17018 | 12321 | 759 | 71 |
| Area | 112 | 88 | 15555 | 8656 | 405 | 64 |
| Dist | 83 | 73 | 9207 | 6774 | 274 | 64 |
| Middle | 74 | 70 | 6876 | 5458 | 319 | 70 |
| Total | 1071 | 931 | 145827 | 107056 | 10565 | 764 |
| Tested Program | Cover size of 2nd order mutants |
Cover size of all du-pairs |
|---|---|---|
| Triangle | 71.3 | 21.3 |
| Sort | 18.3 | 6.7 |
| Stack | 49.3 | 21.0 |
| Reversed | 34.7 | 15.3 |
| Clock | 101.3 | 32.7 |
| Quotient | 34.3 | 16.3 |
| Product | 79.7 | 21.3 |
| Area | 89.3 | 30.7 |
| Dist | 80.7 | 24.7 |
| Middle | 32.3 | 12.7 |
| Average | 59.1 | 20.3 |
| 2nd-order mutant | du-pairs | ||
|---|---|---|---|
| Mean | 59.13 | 20.27 | |
| Variance | 824.4 | 62.96 | |
| P(T<=t) two-tail | 2.77E-04 | ||
| Tested Program | Suite1 | Suite2 | Suite3 | Average |
|---|---|---|---|---|
| Triangle | 98% | 100% | 98% | 98.7% |
| Sort | 96% | 96% | 96% | 95.6% |
| Stack | 89% | 100% | 89% | 92.6% |
| Reversed | 100% | 100% | 100% | 100% |
| Clock | 100% | 100% | 100% | 100% |
| Quotient | 100% | 100% | 100% | 100% |
| Product | 100% | 100% | 100% | 100% |
| Area | 100% | 100% | 100% | 100% |
| Dist | 100% | 100% | 100% | 100% |
| Middle | 100% | 100% | 100% | 100% |
| Average | 98.3% | 99.6% | 98.3% | 98.7% |
| Tested Program | Suite1 | Suite2 | Suite3 | Average |
|---|---|---|---|---|
| Triangle | 80% | 82% | 80% | 81% |
| Sort | 85% | 85% | 85% | 85% |
| Stack | 89% | 85% | 85% | 86% |
| Reversed | 75% | 80% | 75% | 77% |
| Clock | 80% | 80% | 80% | 80% |
| Quotient | 70% | 73% | 70% | 71% |
| Product | 78% | 80% | 75% | 78% |
| Area | 80% | 83% | 88% | 84% |
| Dist | 79% | 90% | 79% | 83% |
| Middle | 85% | 85% | 85% | 85% |
| Average | 80.1% | 82.3% | 80.2% | 80.9% |
| 2nd-order mutant | du-pairs | ||
|---|---|---|---|
| Mean | 98.7% | 80.9% | |
| Variance | 0.1% | 0.2% | |
| P(T<=t) two-tail | 1.11E-05 | ||
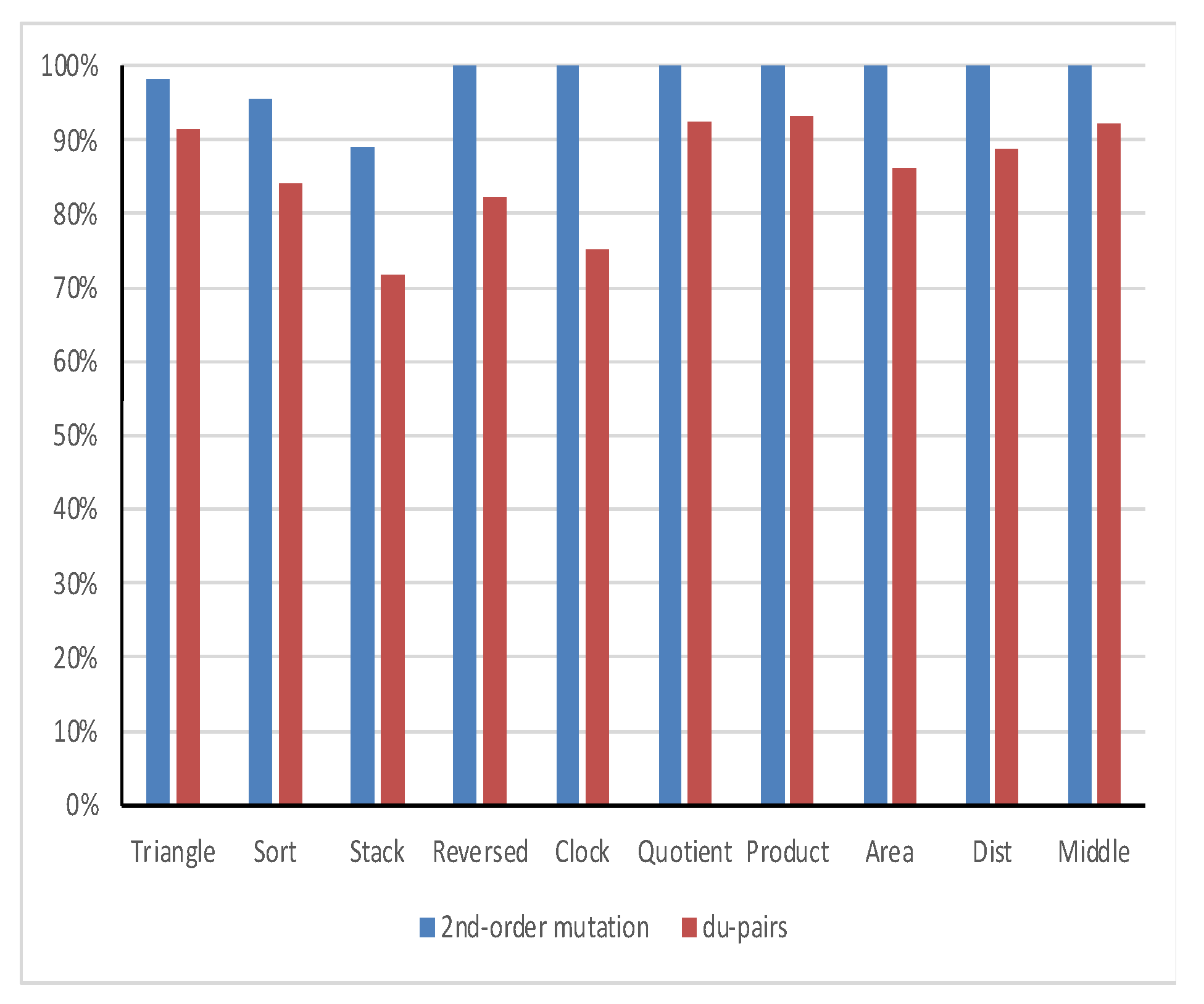
| Tested Program | No. of faults | failure detection efficiency | |
|---|---|---|---|
| 2nd-order mutation | du-pairs | ||
| Triangle | 2459 | 98% | 91% |
| Sort | 2333 | 96% | 84% |
| Stack | 354 | 89% | 72% |
| Reversed | 956 | 100% | 82% |
| Clock | 109 | 100% | 75% |
| Quotient | 2597 | 100% | 92% |
| Product | 759 | 100% | 93% |
| Area | 405 | 100% | 86% |
| Dist | 274 | 100% | 89% |
| Middle | 319 | 100% | 92% |
| Total = 10565 | Average = 98% | Average = 86% | |
| 2nd-order mutant | du-pairs | ||
|---|---|---|---|
| Mean | 98.3% | 85.7% | |
| Variance | 0.1% | 0.6% | |
| P(T<=t) two-tail | 9.195E-05 | ||
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




