Submitted:
04 June 2023
Posted:
05 June 2023
Read the latest preprint version here
Abstract
Keywords:
1. Introduction
- 1.
- We propose a novel LDP named IPLDP, which independently perturbs different items with different privacy budgets to achieve personalized privacy protection and utility improvement simultaneously.
- 2.
- We propose IPRR mechanism to provide equivalent protection for inputs and outputs simultaneously using the direct encoding method.
- 3.
- By calculating the and losses through the unbiased estimator of the gound-truth distribution under IPRR, we theoretically prove that our method has tighter upper bounds than that of existing direct encoding mechanisms.
- 4.
- We evaluate our IPRR on a synthetic and a real-world dataset with the comparison with the existing methods. The results demonstrate that our method has better performance than existing methods in data utility.
2. Related Work
3. Preliminaries
3.1. Problem Statement
3.2. Local Differential Privacy
3.3. Distribution Estimation Method
3.3.1. Empirical estimation method
3.4. Utility Evaluation Method
4. Item-Oriented Personalized LDP
4.1. Privacy Definition
- 1.
- for any and for any ,
- 2.
- for any and for any ,
4.2. Relationship with LDP
4.3. Comparison with MinID-LDP
5. Item-Oriented Personalized Mechanisms and Distribution Estimation
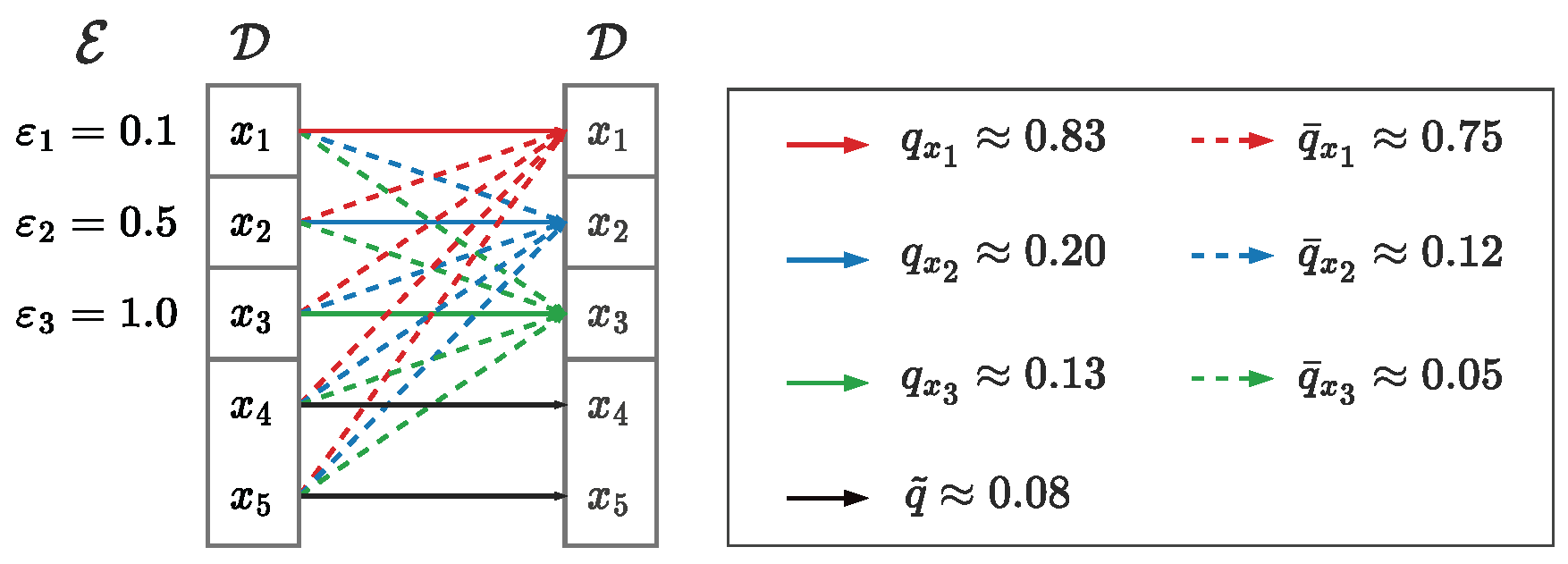
5.1. Item-Oriented Personalized Randomized Response
5.2. IPRR with Non-sensitive Items
5.3. Empirical Estimation under IPRR
6. Utility Analysis
7. Evaluation
7.1. Experimental Setup
7.1.1. Datasets
7.1.2. Metrics
7.1.3. Settings
7.2. Experimental Results
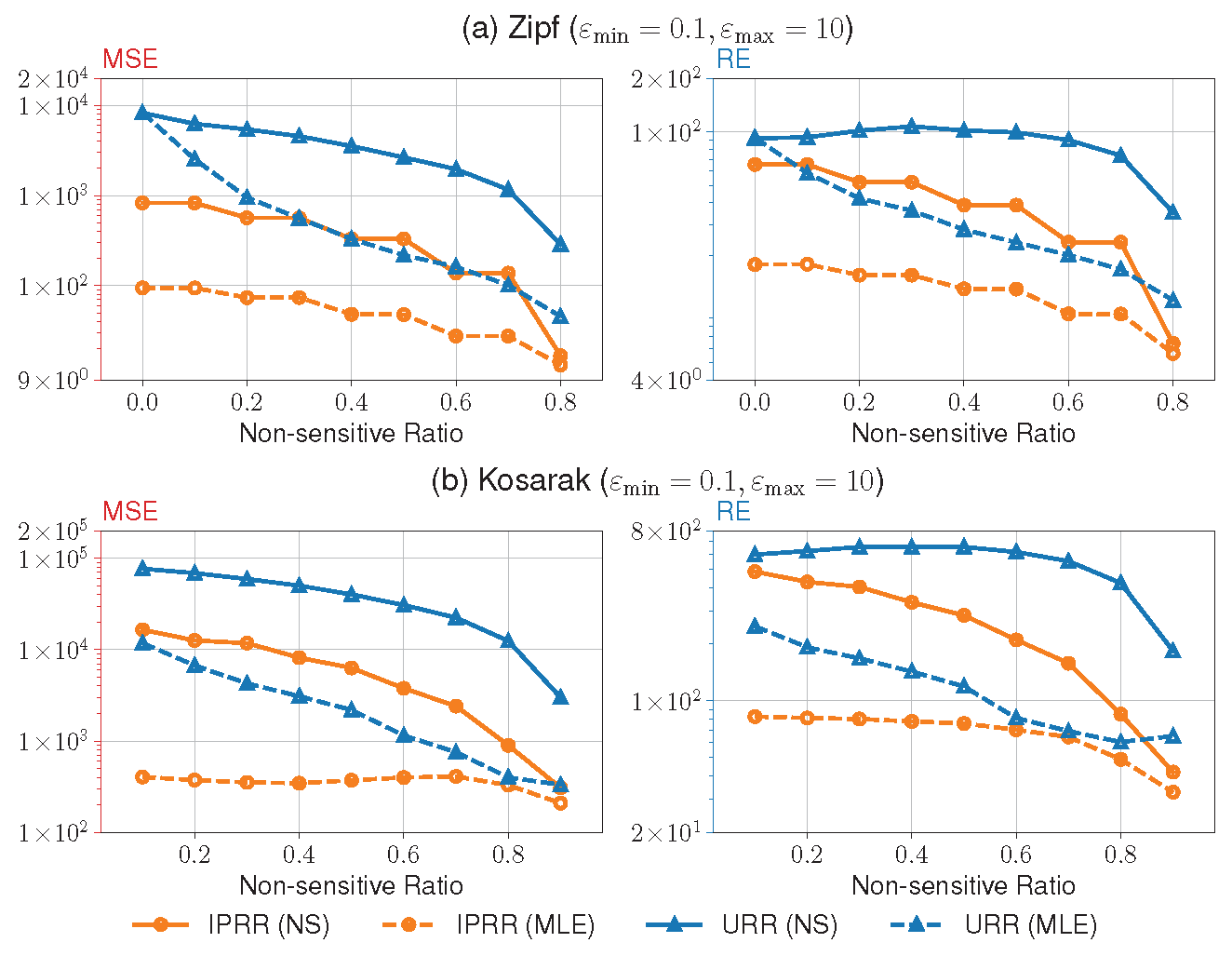
7.2.1. Utility under various privacy level groups
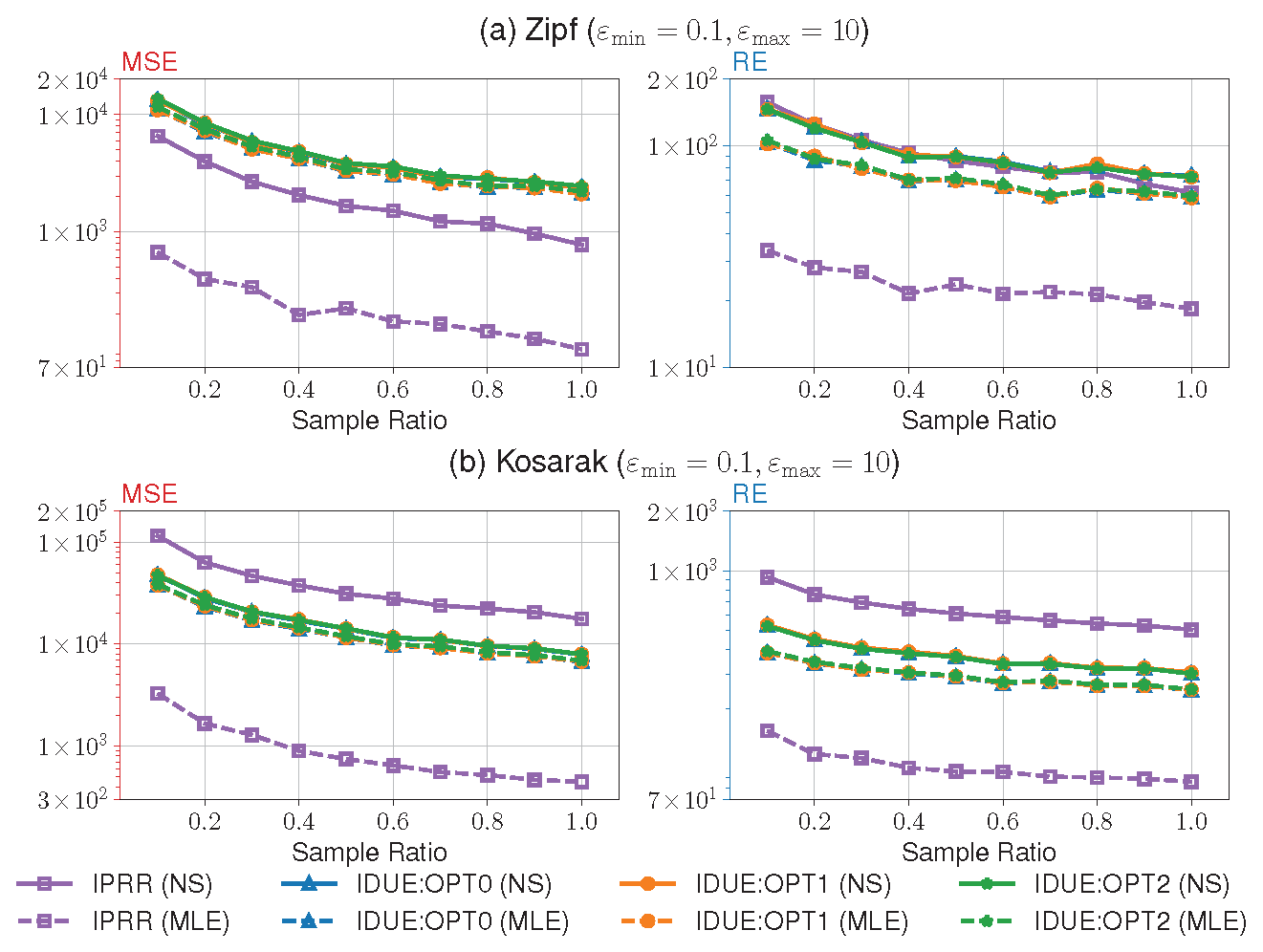
7.2.2. Comparison with IDUE
8. Conclusion
Appendix A. Item-Oriented Personalized LDP
Appendix A.1. Proof of Theorem 1
Appendix A.2. Proof of Theorem 2
Appendix B. Utility Analysis
Appendix B.1. Proof of Theorem 3
Appendix B.2. Proof of Lemma 1
Appendix B.3. Proof of Lemma 2
Appendix B.4. Proof of Theorem 4
Appendix B.5. Proof of Theorem 5
Appendix B.6. Proof of Theorem 6
References
- Han, J. , Pei, J., Yin, Y.: Mining frequent patterns without candidate generation. In: SIGMOD Conference. pp. 1–12. 2000. [Google Scholar]
- Xu, J. , Zhang, Z., Xiao, X., Yang, Y., Yu, G.: Differentially private histogram publication. In: ICDE. pp. 32–43. 2012. [Google Scholar] [CrossRef]
- Wang, T. , Li, N., Jha, S.: Locally differentially private heavy hitter identification. IEEE Trans. Dependable Secur. Comput. 2021. [Google Scholar] [CrossRef]
- Dwork, C. : Differential privacy. In: ICALP (2). Lecture Notes in Computer Science, vol. 4052, pp. 1–12. 2006. [Google Scholar]
- Dwork, C. , McSherry, F., Nissim, K., Smith, A.D.: Calibrating noise to sensitivity in private data analysis. In: TCC. Lecture Notes in Computer Science, vol. 3876, pp. 265–284. 2006. [Google Scholar] [CrossRef]
- Bun, M. , Steinke, T.: Concentrated differential privacy: Simplifications, extensions, and lower bounds. In: TCC (B1). Lecture Notes in Computer Science, vol. 9985, pp. 2016. [Google Scholar] [CrossRef]
- Cuff, P. , Yu, L.: Differential privacy as a mutual information constraint. In: CCS. pp. 43–54. 2016. [Google Scholar] [CrossRef]
- Kifer, D. , Machanavajjhala, A.: Pufferfish: A framework for mathematical privacy definitions. ACM Trans. Database Syst. 3: 39(1), 3:1–3, 2014. [Google Scholar] [CrossRef]
- Lin, B. , Kifer, D.: Information preservation in statistical privacy and bayesian estimation of unattributed histograms. In: SIGMOD Conference. pp. 677–688. 2013. [Google Scholar] [CrossRef]
- Chen, R. , Li, H., Qin, A.K., Kasiviswanathan, S.P., Jin, H.: Private spatial data aggregation in the local setting. In: ICDE. pp. 289–300. 2016. [Google Scholar] [CrossRef]
- Duchi, J.C. , Jordan, M.I., Wainwright, M.J.: Local privacy and statistical minimax rates. In: FOCS. pp. 429–438. 2013. [Google Scholar] [CrossRef]
- Wang, T. , Li, N., Jha, S.: Locally differentially private frequent itemset mining. In: IEEE Symposium on Security and Privacy. pp. 127–143. 2018. [Google Scholar] [CrossRef]
- Warner, S.L. : Randomized response: a survey technique for eliminating evasive answer bias. Publications of the American Statistical Association 60 ( 1965. [CrossRef]
- Kairouz, P. , Oh, S., Viswanath, P.: Extremal mechanisms for local differential privacy. In: NIPS. pp. 2879. [Google Scholar]
- Erlingsson, Ú. , Pihur, V., Korolova, A.: RAPPOR: randomized aggregatable privacy-preserving ordinal response. In: CCS. pp. 1054–1067. 2014. [Google Scholar] [CrossRef]
- Murakami, T. , Kawamoto, Y.: Utility-optimized local differential privacy mechanisms for distribution estimation. In: USENIX Security Symposium. pp. 1877–1894. 2019. [Google Scholar]
- Gu, X. , Li, M., Xiong, L., Cao, Y.: Providing input-discriminative protection for local differential privacy. In: ICDE. pp. 505–516. 2020. [Google Scholar] [CrossRef]
- Chatzikokolakis, K. , Andrés, M.E., Bordenabe, N.E., Palamidessi, C.: Broadening the scope of differential privacy using metrics. In: Privacy Enhancing Technologies. Lecture Notes in Computer Science, vol. 7981, pp. 82–102. 2013. [Google Scholar] [CrossRef]
- Liu, C. , Chakraborty, S., Mittal, P.: Dependence makes you vulnberable: Differential privacy under dependent tuples. In: NDSS. 2016. [Google Scholar]
- Yang, B. , Sato, I., Nakagawa, H.: Bayesian differential privacy on correlated data. In: SIGMOD Conference. pp. 747–762. 2015. [Google Scholar] [CrossRef]
- Mironov, I. : Rényi differential privacy. In: CSF. pp. 263–275. 2017. [Google Scholar] [CrossRef]
- Kawamoto, Y. , Murakami, T.: Differentially private obfuscation mechanisms for hiding probability distributions. CoRR abs/1812. 0093. [Google Scholar]
- Chen, Z. , Wang, J.: Ldp-fpminer: Fp-tree based frequent itemset mining with local differential privacy. CoRR abs/2209. 0133. [Google Scholar]
- Wang, N. , Xiao, X., Yang, Y., Hoang, T.D., Shin, H., Shin, J., Yu, G.: Privtrie: Effective frequent term discovery under local differential privacy. In: ICDE. pp. 821–832. 2018. [Google Scholar] [CrossRef]
- Bassily, R. , Smith, A.D.: Local, private, efficient protocols for succinct histograms. In: STOC. pp. 127–135. 2015. [Google Scholar] [CrossRef]
- Bassily, R. , Nissim, K., Stemmer, U., Thakurta, A.G.: Practical locally private heavy hitters. In: NIPS. pp. 2288. [Google Scholar]
- Lin, W. , Li, B., Wang, C.: Towards private learning on decentralized graphs with local differential privacy. IEEE Trans. Inf. Forensics Secur. 2936; 17. [Google Scholar] [CrossRef]
- Qin, Z. , Yu, T., Yang, Y., Khalil, I., Xiao, X., Ren, K.: Generating synthetic decentralized social graphs with local differential privacy. In: CCS. pp. 425–438. 2017. [Google Scholar] [CrossRef]
- Wei, C. , Ji, S., Liu, C., Chen, W., Wang, T.: Asgldp: Collecting and generating decentralized attributed graphs with local differential privacy. IEEE Trans. Inf. Forensics Secur. 3239; 15. [Google Scholar] [CrossRef]
- Jorgensen, Z. , Yu, T., Cormode, G.: Conservative or liberal? personalized differential privacy. In: ICDE. pp. 1023–1034. 2015. [Google Scholar] [CrossRef]
- Nie, Y. , Yang, W., Huang, L., Xie, X., Zhao, Z., Wang, S.: A utility-optimized framework for personalized private histogram estimation. IEEE Trans. Knowl. Data Eng. 2019. [Google Scholar] [CrossRef]
- Alaggan, M. , Gambs, S., Kermarrec, A.: Heterogeneous differential privacy. J. Priv. 2016. [Google Scholar]
- Kotsogiannis, I. , Doudalis, S., Haney, S., Machanavajjhala, A., Mehrotra, S.: One-sided differential privacy. In: ICDE. pp. 493–504. 2020. [Google Scholar] [CrossRef]
- Kairouz, P. , Bonawitz, K.A., Ramage, D.: Discrete distribution estimation under local privacy. In: ICML. JMLR Workshop and Conference Proceedings, vol. 48, pp. 2436–2444. JMLR. 2016. [Google Scholar]
- Wang, T. , Lopuhaä-Zwakenberg, M., Li, Z., Skoric, B., Li, N.: Locally differentially private frequency estimation with consistency. In: NDSS. 2020. [Google Scholar] [CrossRef]
- Abstracts of Papers. The Annals of Mathematical Statistics 20(4), 620 – 624 (1949). 10. 1214. [CrossRef]
- Mangat, N.S. : An improved randomized response strategy. Journal of the Royal Statistical Society. Series B (Methodological) 56(1), 93–95 (1994), http://www.jstor. 2346. [Google Scholar]
- Wang, T. , Xu, M., Ding, B., Zhou, J., Hong, C., Huang, Z., Li, N., Jha, S.: Improving utility and security of the shuffler-based differential privacy. Proc. VLDB Endow. 3545. [Google Scholar] [CrossRef]
- Wang, Z. , Zhu, Y., Wang, D., Han, Z.: Fedfpm: A unified federated analytics framework for collaborative frequent pattern mining. In: INFOCOM. pp. 61–70. 2022. [Google Scholar] [CrossRef]
- "kosarak dataset", http://fimi.uantwerpen.
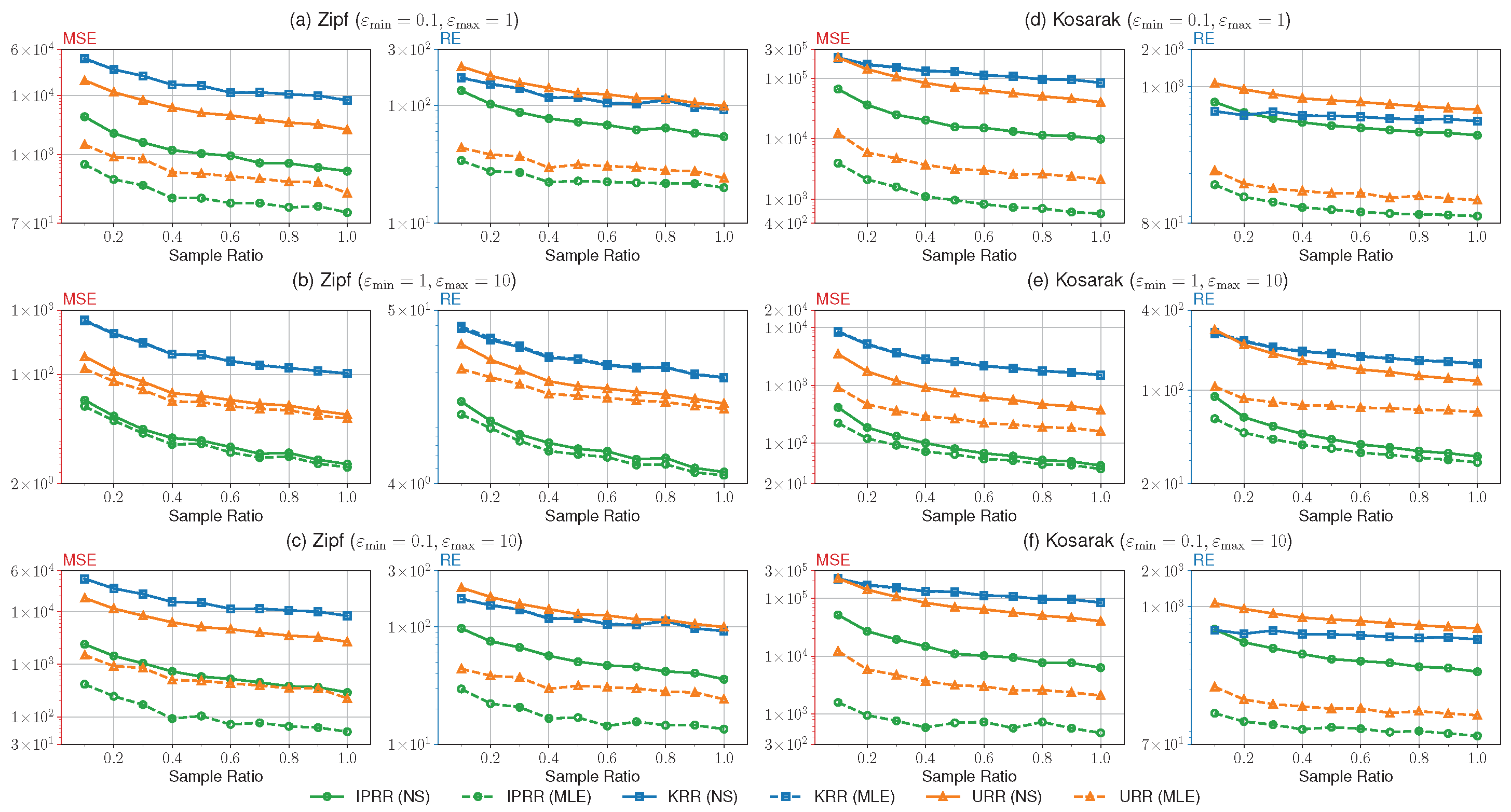
| Datasets | # Users | # Items |
|---|---|---|
| Zipf | 100000 | 20 |
| Kosarak [40] | 646510 | 100 |
| # | Mechanisms to Compare |
|||||
|---|---|---|---|---|---|---|
| 1 | KRR,URR | 0.1 | 1 | 4 | 0.5 | 0.2-1.0 |
| 2 | KRR,URR | 1 | 10 | 4 | 0.5 | 0.2-1.0 |
| 3 | KRR,URR | 0.1 | 10 | 4 | 0.5 | 0.2-1.0 |
| 4 | URR | 0.1 | 10 | 4 | 0.0-0.8 * 0.1-0.9 ** |
1.0 |
| 5 | IDUE | 0.1 | 10 | 4 | 0 | 0.1-1.0 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




