Submitted:
25 May 2023
Posted:
26 May 2023
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background
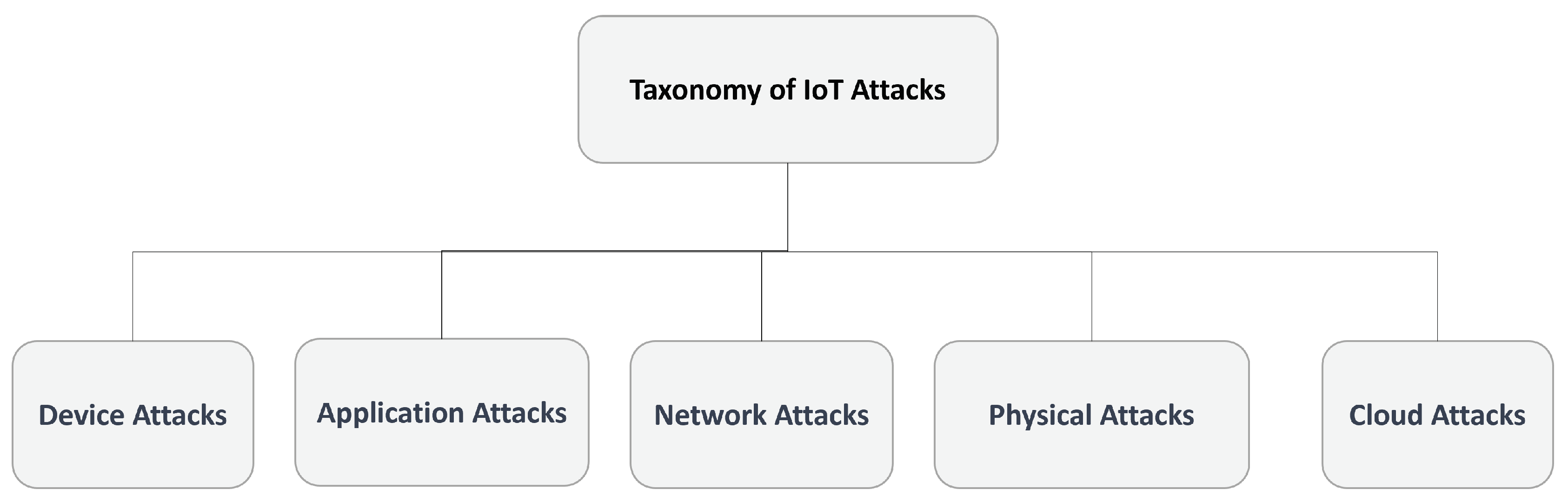
2.1. Taxonomy
2.1.1. Device Attacks in IoT
2.1.2. Application Attacks in IoT
2.1.3. Network Attacks in IoT
2.1.4. Physical Attacks in IoT
2.1.5. Cloud Attacks in IoT
3. Related Work
3.1. Clustering of Stakeholders
3.2. Feature Selection
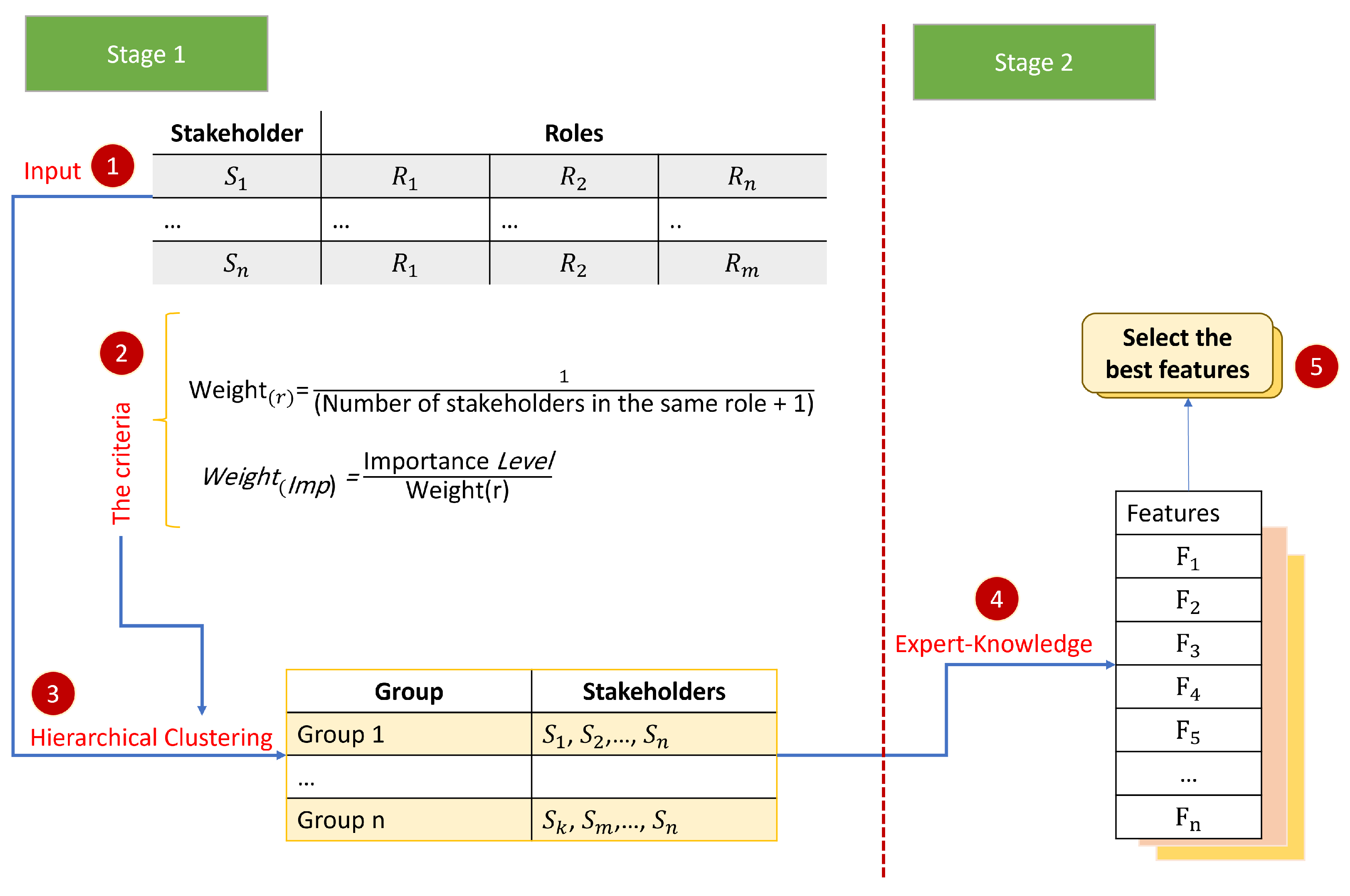
4. Methodology
4.1. The First Stage: Clustering Stakeholders
| Algorithm 1 The Ward method with weight(r) and weight(Imp) |
|
4.2. The Second Stage: Features Assignment
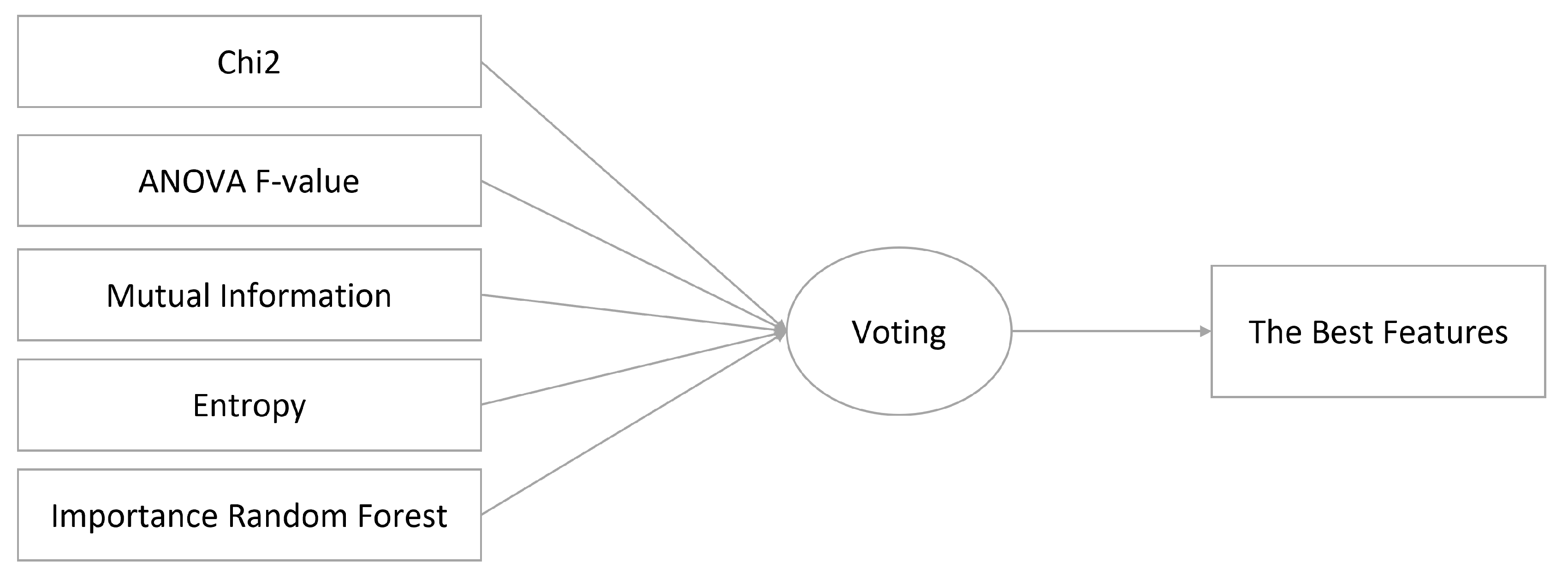
4.2.1. Chi-squared
4.2.2. ANOVA F-value
4.2.3. Mutual Information
4.2.4. Entropy
4.2.5. Importance Random Forest
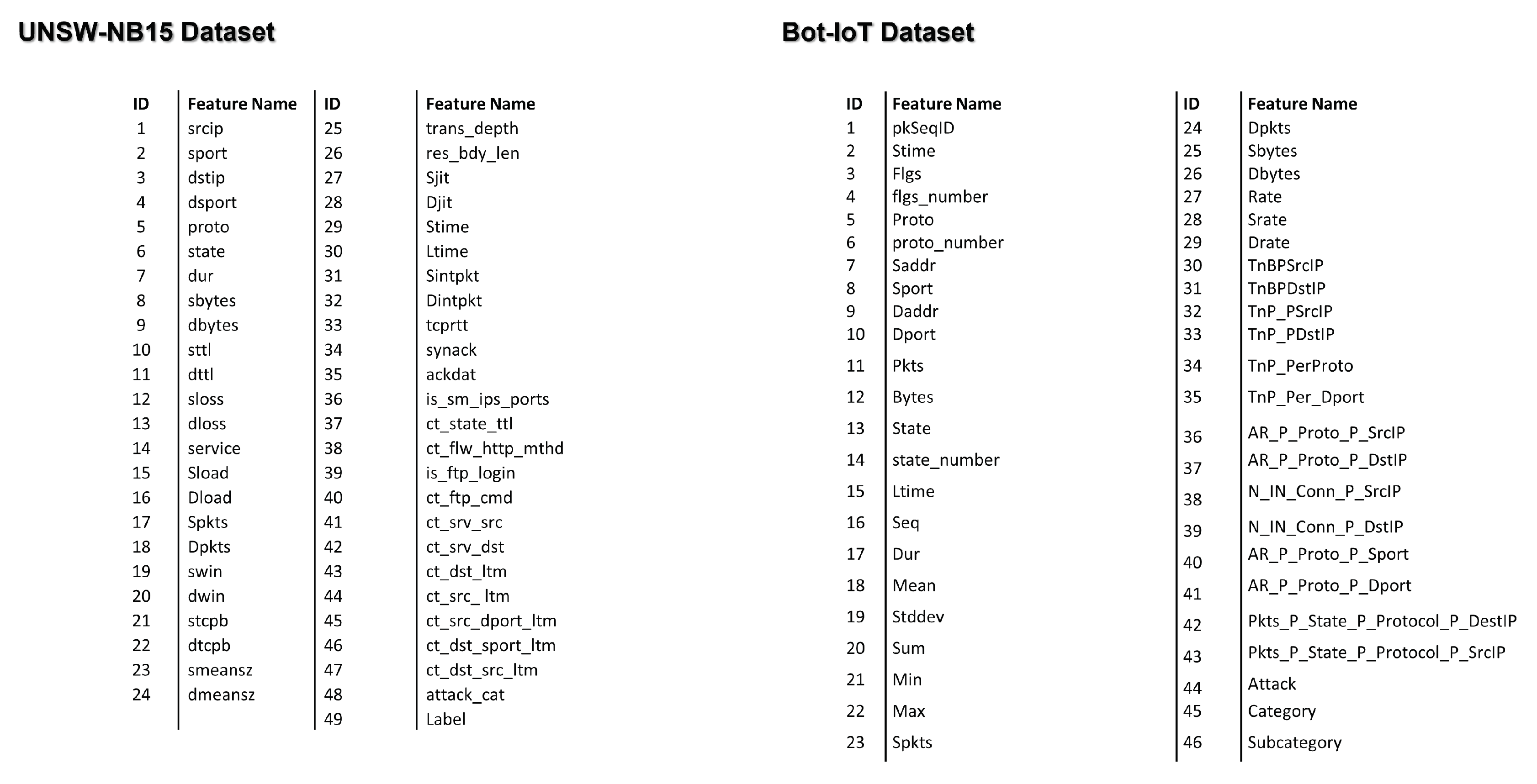
5. Case Study on Nine Stakeholders and Two Datasets
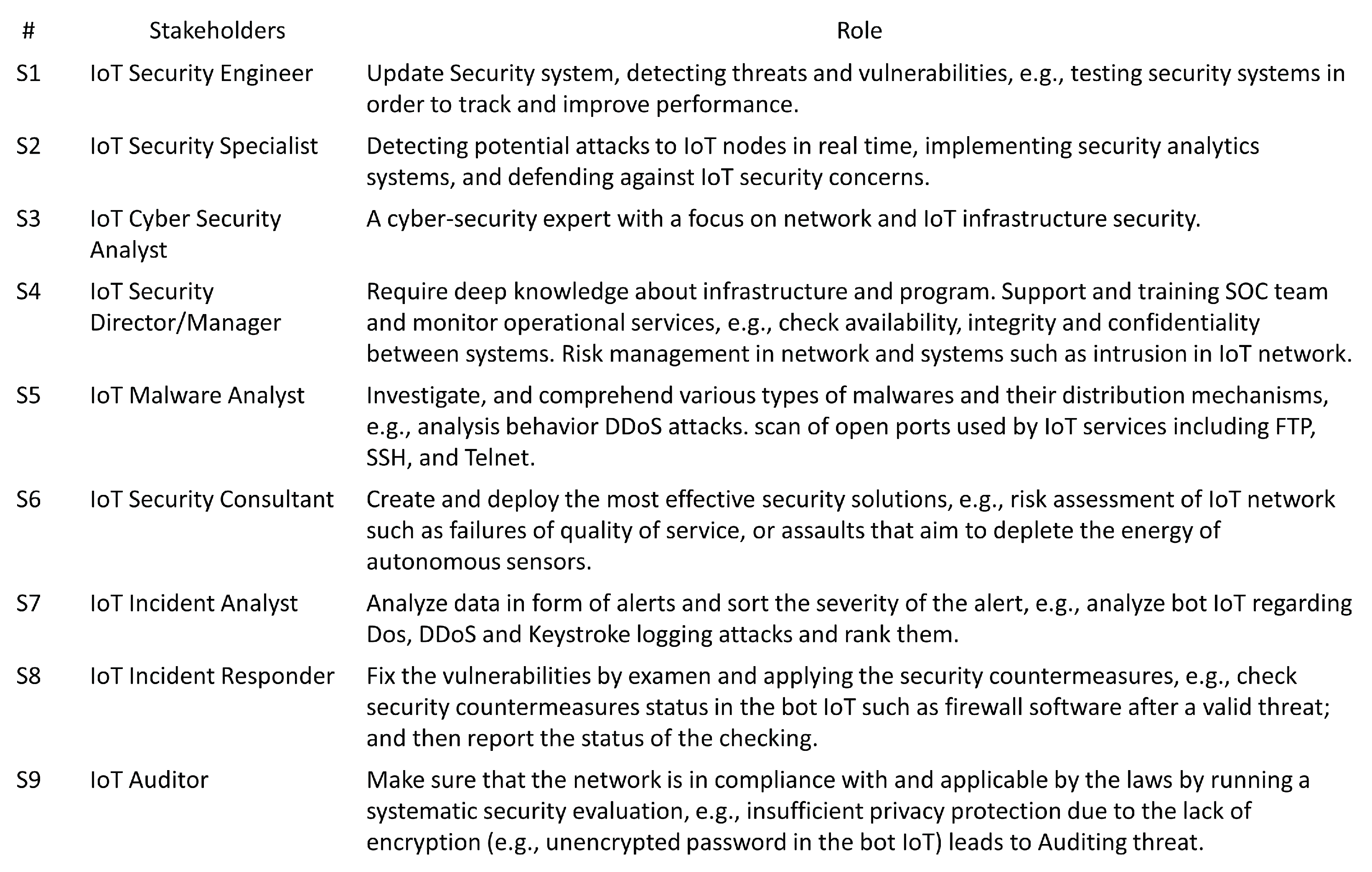
5.1. Step 1: Define Stakeholders and Their Roles
5.2. Step 2: Weights and Normalization
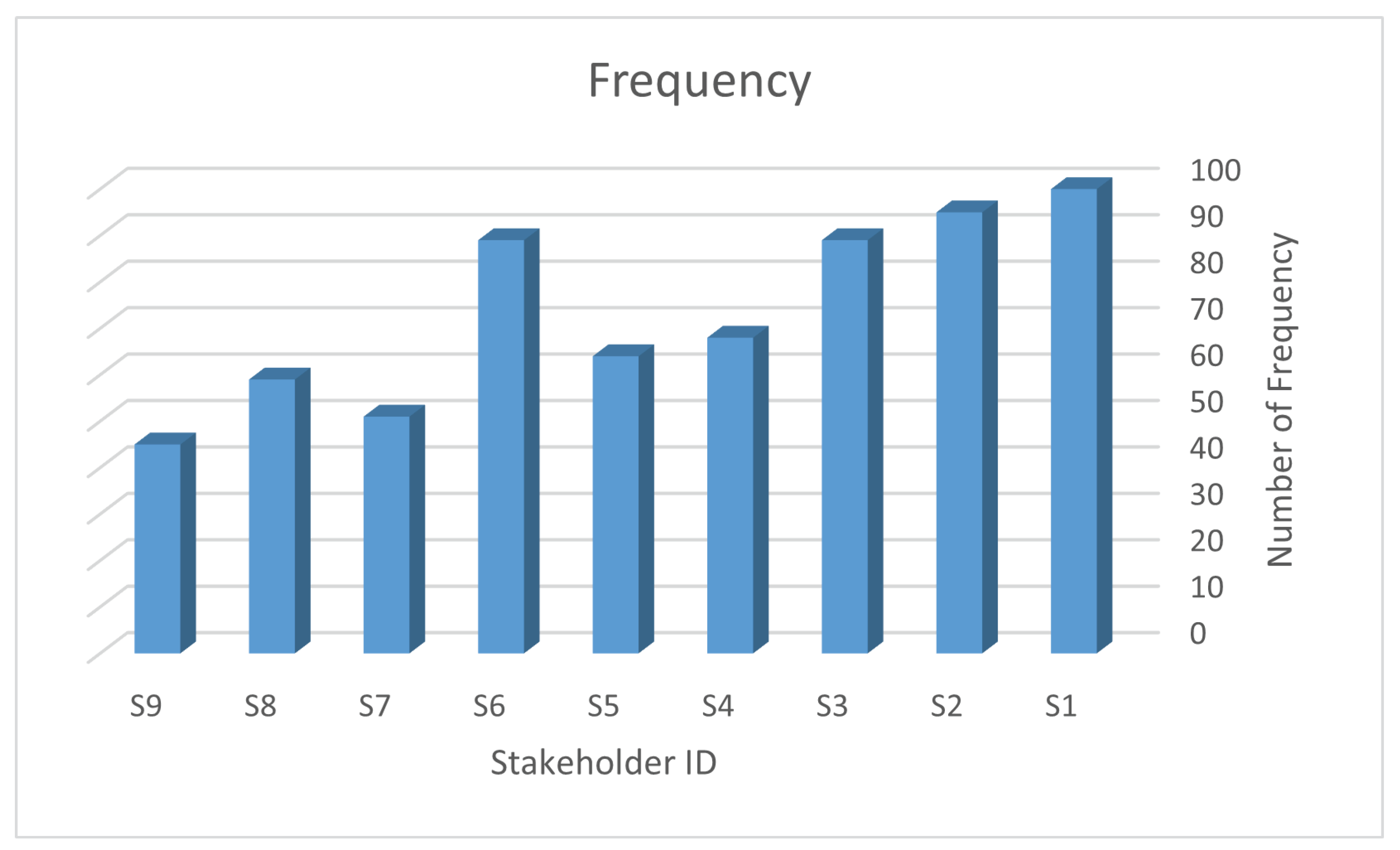
5.2.1. Weights of Roles
5.2.2. Weights of Importance
5.2.3. Normalizing Weights
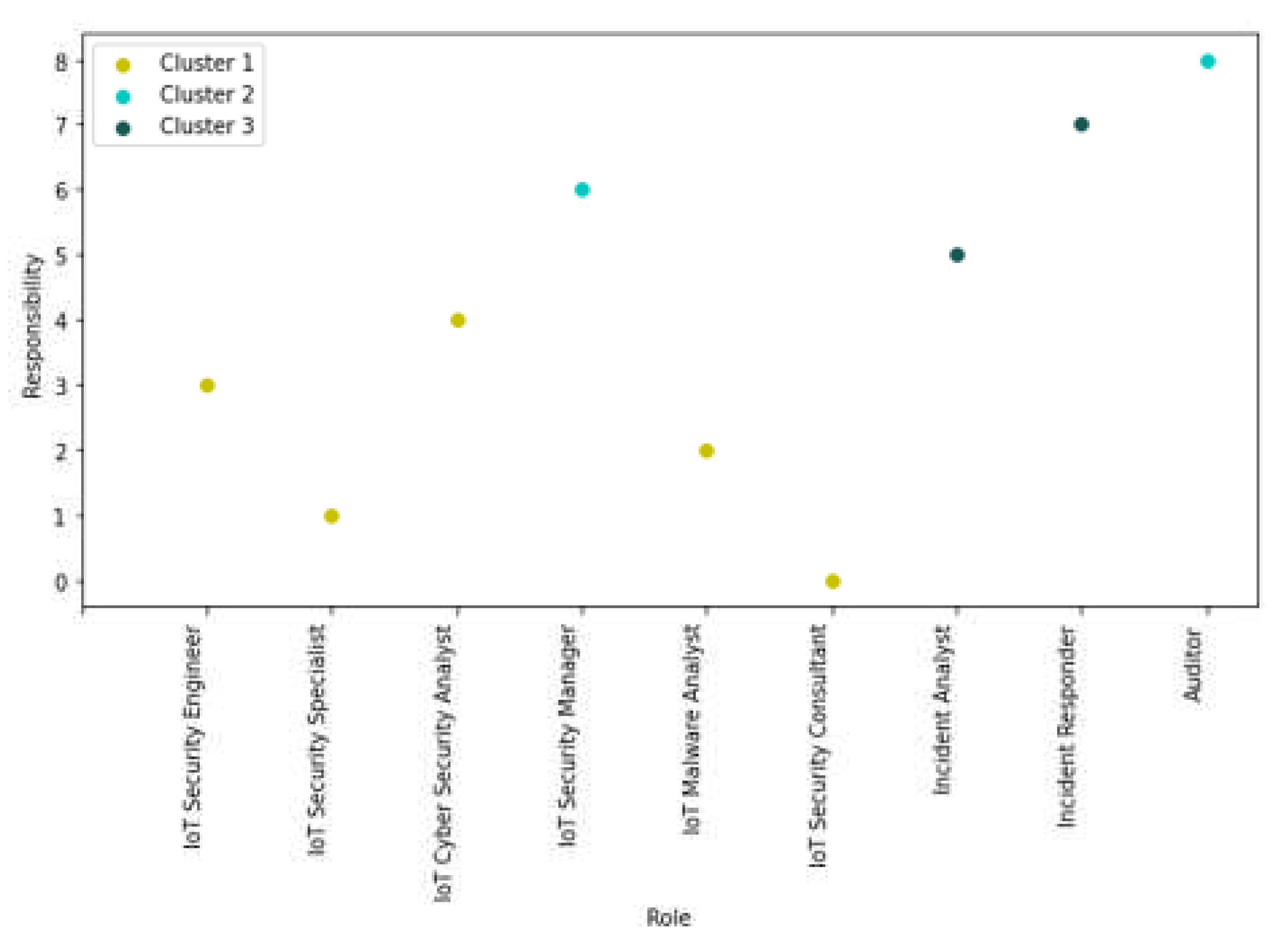
5.3. Step 3: Clustering of Stakeholders
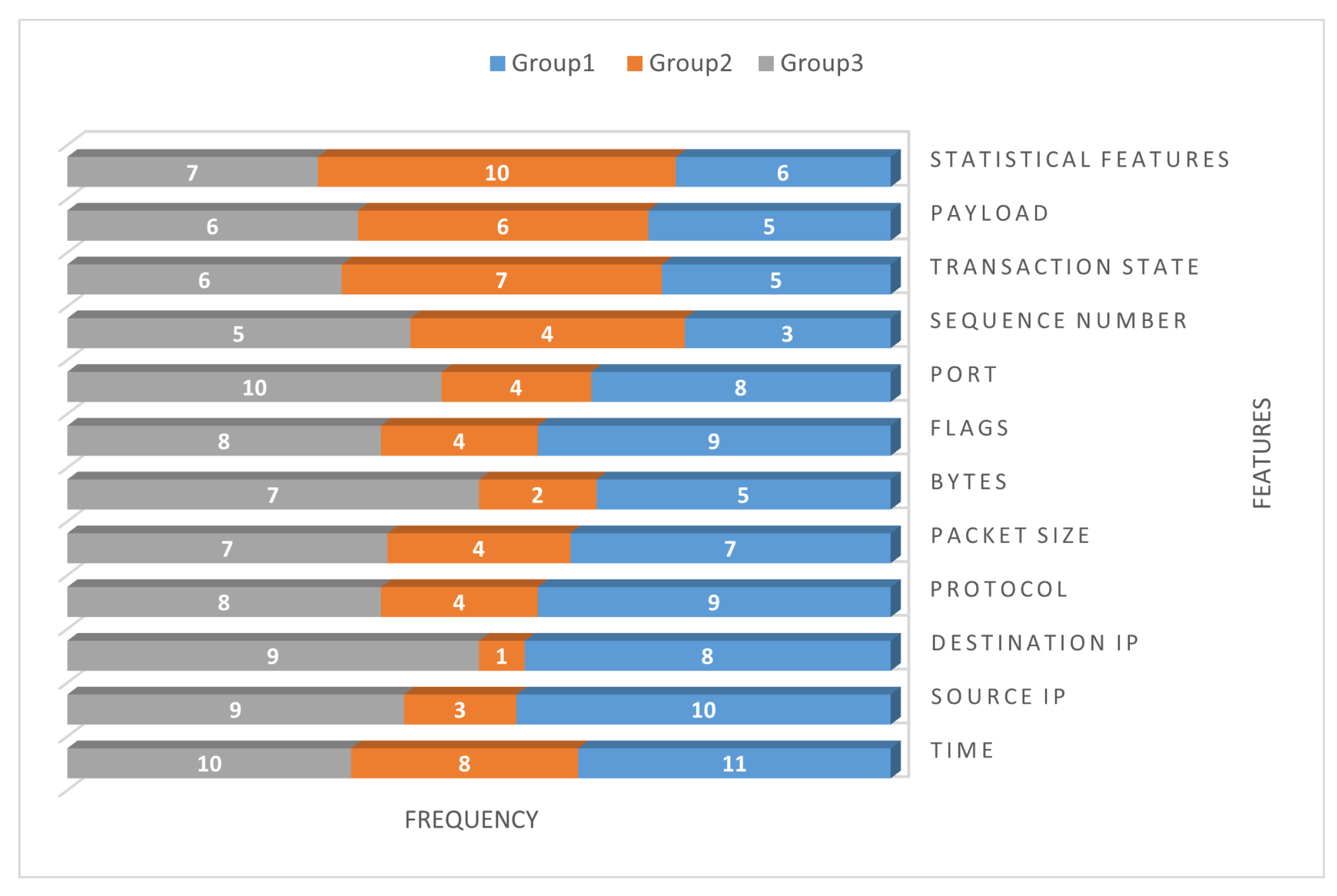
5.4. Step 4: Select the Relevant Features
5.5. Step 5: Select the Best Features from the Relevant Features
5.5.1. Five Models on Two Datasets
5.5.2. Votes to Select the Best Features
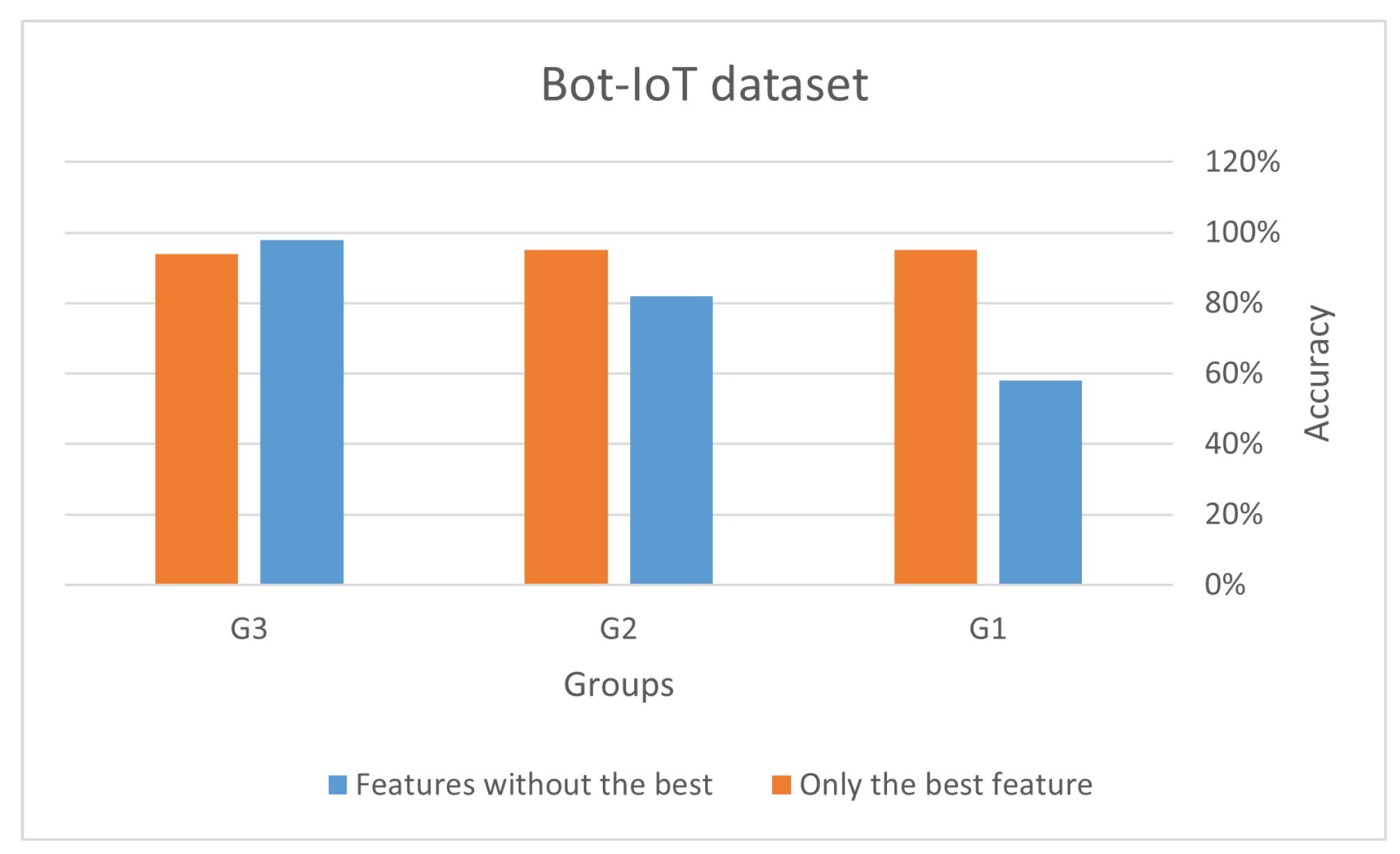
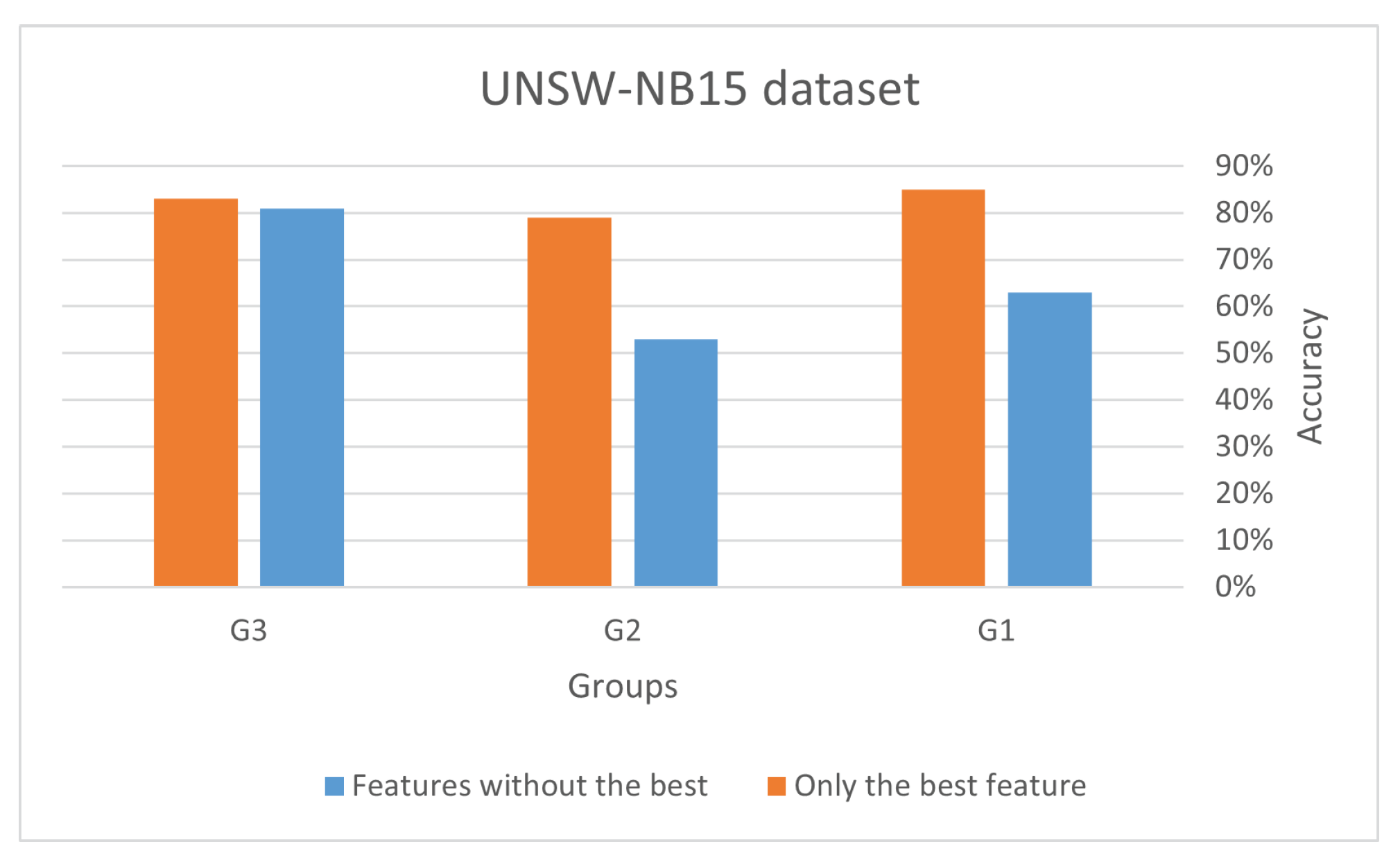
5.6. Validation of Results
6. Discussion
7. Conclusions
Funding
Institutional Review Board Statement
Informed Consent Statement
Conflicts of Interest
References
- Sobin, C. A survey on architecture, protocols and challenges in IoT. Wireless Personal Communications 2020, 112, 1383–1429. [Google Scholar] [CrossRef]
- Yao, X.; Farha, F.; Li, R.; Psychoula, I.; Chen, L.; Ning, H. Security and privacy issues of physical objects in the IoT: Challenges and opportunities. Digital Communications and Networks 2021, 7, 373–384. [Google Scholar] [CrossRef]
- Mohanta, B.K.; Jena, D.; Satapathy, U.; Patnaik, S. Survey on IoT security: Challenges and solution using machine learning, artificial intelligence and blockchain technology. Internet of Things 2020, 11, 100227. [Google Scholar] [CrossRef]
- Nock, O.; Starkey, J.; Angelopoulos, C.M. Addressing the security gap in IoT: towards an IoT cyber range. Sensors 2020, 20, 5439. [Google Scholar] [CrossRef]
- Ahmetoglu, S.; Che Cob, Z.; Ali, N. A systematic review of Internet of Things adoption in organizations: taxonomy, benefits, challenges and critical factors. Applied Sciences 2022, 12, 4117. [Google Scholar] [CrossRef]
- Ramson, S.J.; Vishnu, S.; Shanmugam, M. Applications of internet of things (iot)–an overview. In Proceedings of the 2020 5th international conference on devices, circuits and systems (ICDCS); IEEE, 2020; pp. 92–95. [Google Scholar]
- Tawalbeh, L.; Muheidat, F.; Tawalbeh, M.; Quwaider, M. IoT Privacy and security: Challenges and solutions. Applied Sciences 2020, 10, 4102. [Google Scholar] [CrossRef]
- Pal, S.; Hitchens, M.; Rabehaja, T.; Mukhopadhyay, S. Security requirements for the internet of things: A systematic approach. Sensors 2020, 20, 5897. [Google Scholar] [CrossRef] [PubMed]
- Sidhu, S.; Mohd, B.J.; Hayajneh, T. Hardware security in IoT devices with emphasis on hardware trojans. Journal of Sensor and Actuator Networks 2019, 8, 42. [Google Scholar] [CrossRef]
- Bansal, S.; Kumar, D. IoT ecosystem: A survey on devices, gateways, operating systems, middleware and communication. International Journal of Wireless Information Networks 2020, 27, 340–364. [Google Scholar] [CrossRef]
- Ding, D.; Han, Q.L.; Ge, X.; Wang, J. Secure state estimation and control of cyber-physical systems: A survey. IEEE Transactions on Systems, Man, and Cybernetics: Systems 2020, 51, 176–190. [Google Scholar] [CrossRef]
- Farivar, F.; Haghighi, M.S.; Jolfaei, A.; Alazab, M. Artificial intelligence for detection, estimation, and compensation of malicious attacks in nonlinear cyber-physical systems and industrial IoT. IEEE transactions on industrial informatics 2019, 16, 2716–2725. [Google Scholar] [CrossRef]
- Xenofontos, C.; Zografopoulos, I.; Konstantinou, C.; Jolfaei, A.; Khan, M.K.; Choo, K.K.R. Consumer, commercial, and industrial iot (in) security: Attack taxonomy and case studies. IEEE Internet of Things Journal 2021, 9, 199–221. [Google Scholar] [CrossRef]
- Sadhu, P.K.; Yanambaka, V.P.; Abdelgawad, A. Internet of Things: Security and Solutions Survey. Sensors 2022, 22, 7433. [Google Scholar] [CrossRef]
- Shah, Y.; Sengupta, S. A survey on Classification of Cyber-attacks on IoT and IIoT devices. In Proceedings of the 2020 11th IEEE Annual Ubiquitous Computing, Electronics & Mobile Communication Conference (UEMCON); 2020; pp. 0406–0413. [Google Scholar] [CrossRef]
- Gaur, V.; Kumar, R. Analysis of machine learning classifiers for early detection of DDoS attacks on IoT devices. Arabian Journal for Science and Engineering 2022, 47, 1353–1374. [Google Scholar] [CrossRef]
- Gupta, R.; Phanden, R.K.; Sharma, S.; Srivastava, P.; Chaturvedi, P. Security in manufacturing systems in the age of industry 4.0: Pitfalls and possibilities. In Proceedings of the Advances in Industrial and Production Engineering: Select Proceedings of FLAME 2020.; Springer, 2021; pp. 105–113. [Google Scholar]
- Eustis, A.G. The Mirai Botnet and the importance of IoT device security. In Proceedings of the 16th International Conference on Information Technology-New Generations (ITNG 2019); Springer, 2019; pp. 85–89. [Google Scholar]
- Rajendran, G.; Nivash, R.R.; Parthy, P.P.; Balamurugan, S. Modern security threats in the Internet of Things (IoT): Attacks and Countermeasures. In Proceedings of the 2019 International Carnahan Conference on Security Technology (ICCST); IEEE, 2019; pp. 1–6. [Google Scholar]
- Vishwakarma, R.; Jain, A.K. A survey of DDoS attacking techniques and defence mechanisms in the IoT network. Telecommunication systems 2020, 73, 3–25. [Google Scholar] [CrossRef]
- Chaudhary, P.; Gupta, B.B.; Singh, A. Securing heterogeneous embedded devices against XSS attack in intelligent IoT system. Computers & Security 2022, 118, 102710. [Google Scholar]
- Mullen, G.; Meany, L. Assessment of buffer overflow based attacks on an IoT operating system. In Proceedings of the 2019 Global IoT Summit (GIoTS). IEEE; 2019; pp. 1–6. [Google Scholar]
- Toutsop, O.; Harvey, P.; Kornegay, K. Monitoring and detection time optimization of man in the middle attacks using machine learning. In Proceedings of the 2020 IEEE Applied Imagery Pattern Recognition Workshop (AIPR); IEEE, 2020; pp. 1–7. [Google Scholar]
- Al-Hadhrami, Y.; Hussain, F.K. DDoS attacks in IoT networks: a comprehensive systematic literature review. World Wide Web 2021, 24, 971–1001. [Google Scholar] [CrossRef]
- Jović, M.; Tijan, E.; Aksentijević, S.; Čišić, D. An overview of security challenges of seaport IoT systems. In Proceedings of the 2019 42nd International Convention on Information and Communication Technology, Electronics and Microelectronics (MIPRO); IEEE, 2019; pp. 1349–1354. [Google Scholar]
- Garagad, V.G.; Iyer, N.C.; Wali, H.G. Data integrity: a security threat for internet of things and cyber-physical systems. In Proceedings of the 2020 International Conference on Computational Performance Evaluation (ComPE); IEEE, 2020; pp. 244–249. [Google Scholar]
- Yang, X.; Shu, L.; Liu, Y.; Hancke, G.P.; Ferrag, M.A.; Huang, K. Physical security and safety of iot equipment: A survey of recent advances and opportunities. IEEE Transactions on Industrial Informatics 2022, 18, 4319–4330. [Google Scholar] [CrossRef]
- González-Granadillo, G.; González-Zarzosa, S.; Diaz, R. Security information and event management (SIEM): analysis, trends, and usage in critical infrastructures. Sensors 2021, 21, 4759. [Google Scholar] [CrossRef]
- Ahmad, W.; Rasool, A.; Javed, A.R.; Baker, T.; Jalil, Z. Cyber security in iot-based cloud computing: A comprehensive survey. Electronics 2022, 11, 16. [Google Scholar] [CrossRef]
- Saini, D.K.; Kumar, K.; Gupta, P. Security issues in IoT and cloud computing service models with suggested solutions. Security and Communication Networks 2022, 2022. [Google Scholar] [CrossRef]
- Pérez Vera, Y.; Bermudez Peña, A. Stakeholders Classification System Based on Clustering Techniques. In Proceedings of the Advances in Artificial Intelligence - IBERAMIA 2018; Simari, G.R., Fermé, E., Gutiérrez Segura, F., Rodríguez Melquiades, J.A., Eds.; Springer International Publishing: Cham, 2018; pp. 241–252. [Google Scholar]
- Zhong, H.; Liu, C. Career Path Clustering via Sequential Job Embedding and Mixture Markov Models. In Proceedings of the ICIS 2022 Proceedings; 2022; Vol. 5. [Google Scholar]
- Gambo, I.P.; Taveter, K. Identifying and Resolving Conflicts in Requirements by Stakeholders: A Clustering Approach. In Proceedings of the 16th International Conference on Evaluation of Novel Approaches to Software Engineering (ENASE); 2021; pp. 158–169. [Google Scholar]
- Ali, S.; Hafeez, Y.; Asghar, S.; Nawaz, A.; Saeed, S. Aspect-based requirements mining technique to improve prioritisation process: multi-stakeholder perspective. IET Software 2020, 14, 482–492. [Google Scholar] [CrossRef]
- Piccialli, F.; Casolla, G.; Cuomo, S.; Giampaolo, F.; Di Cola, V.S. Decision making in IoT environment through unsupervised learning. IEEE Intelligent Systems 2019, 35, 27–35. [Google Scholar] [CrossRef]
- Shafiq, M.; Tian, Z.; Bashir, A.K.; Du, X.; Guizani, M. IoT malicious traffic identification using wrapper-based feature selection mechanisms. Computers & Security 2020, 94, 101863. [Google Scholar] [CrossRef]
- Nimbalkar, P.; Kshirsagar, D. Feature selection for intrusion detection system in Internet-of-Things (IoT). ICT Express 2021, 7, 177–181. [Google Scholar] [CrossRef]
- Guerra-Manzanares, A.; Bahsi, H.; Nõmm, S. Hybrid feature selection models for machine learning based botnet detection in IoT networks. In Proceedings of the 2019 International Conference on Cyberworlds (CW); IEEE, 2019; pp. 324–327. [Google Scholar]
- Abawajy, J.; Darem, A.; Alhashmi, A.A. Feature subset selection for malware detection in smart IoT platforms. Sensors 2021, 21, 1374. [Google Scholar] [CrossRef]
- Kalakoti, R.; Nõmm, S.; Bahsi, H. In-Depth Feature Selection for the Statistical Machine Learning-Based Botnet Detection in IoT Networks. IEEE Access 2022, 10, 94518–94535. [Google Scholar] [CrossRef]
- Ghosal, A.; Nandy, A.; Das, A.K.; Goswami, S.; Panday, M. A short review on different clustering techniques and their applications. Emerging Technology in Modelling and Graphics: Proceedings of IEM Graph 2018 2020, 69–83. [Google Scholar]
- Ahmad, A.; Khan, S.S. Survey of state-of-the-art mixed data clustering algorithms. Ieee Access 2019, 7, 31883–31902. [Google Scholar] [CrossRef]
- Randriamihamison, N.; Vialaneix, N.; Neuvial, P. Applicability and interpretability of Ward’s hierarchical agglomerative clustering with or without contiguity constraints. Journal of Classification 2021, 38, 363–389. [Google Scholar] [CrossRef]
- Bu, J.; Liu, W.; Pan, Z.; Ling, K. Comparative study of hydrochemical classification based on different hierarchical cluster analysis methods. International journal of environmental research and public health 2020, 17, 9515. [Google Scholar] [CrossRef] [PubMed]
- Benabdellah, A.C.; Benghabrit, A.; Bouhaddou, I. A survey of clustering algorithms for an industrial context. Procedia computer science 2019, 148, 291–302. [Google Scholar] [CrossRef]
- Sikelis, K.; Tsekouras, G.E.; Kotis, K. Ontology-based feature selection: A survey. Future Internet 2021, 13, 158. [Google Scholar] [CrossRef]
- Kou, G.; Yang, P.; Peng, Y.; Xiao, F.; Chen, Y.; Alsaadi, F.E. Evaluation of feature selection methods for text classification with small datasets using multiple criteria decision-making methods. Applied Soft Computing 2020, 86, 105836. [Google Scholar] [CrossRef]
- Niu, D.; Wang, K.; Sun, L.; Wu, J.; Xu, X. Short-term photovoltaic power generation forecasting based on random forest feature selection and CEEMD: A case study. Applied soft computing 2020, 93, 106389. [Google Scholar] [CrossRef]
- UNSW. BoT-IoT dataset, 2019. Available online: https://research.unsw.edu.au/projects/bot-iot-dataset.
- UNSW. The UNSW-NB15 Dataset. Available online: https://research.unsw.edu.au/projects/unsw-nb15-dataset.
- Almalki, L.S.; Alnahdi, A.K.; Albalawi, T.F. The Roles of Stakeholders in Internet of Things: A Theoretical Framework. In Proceedings of the 2023 1st International Conference on Advanced Innovations in Smart Cities (ICAISC); 2023; pp. 1–6. [Google Scholar] [CrossRef]
- Venkatesh, B.; Anuradha, J. A review of feature selection and its methods. Cybernetics and information technologies 2019, 19, 3–26. [Google Scholar] [CrossRef]
| 1 | 1 | 1 | 0 | 1 | 1 | 0 | 0 | 0 | |
| 1 | 1 | 1 | 0 | 1 | 1 | 0 | 0 | 0 | |
| 1 | 1 | 1 | 0 | 1 | 1 | 0 | 0 | 0 | |
| 0 | 0 | 0 | 1 | 0 | 0 | 0 | 0 | 0 | |
| 1 | 1 | 1 | 0 | 1 | 1 | 0 | 0 | 0 | |
| 1 | 1 | 1 | 0 | 1 | 1 | 0 | 0 | 0 | |
| 0 | 0 | 0 | 0 | 0 | 0 | 1 | 1 | 1 | |
| 0 | 0 | 0 | 0 | 0 | 0 | 1 | 1 | 1 | |
| 0 | 0 | 0 | 0 | 0 | 0 | 1 | 1 | 1 |
| Stakeholders | ||
|---|---|---|
| S1 | ||
| S2 | ||
| S3 | ||
| S4 | ||
| S5 | ||
| S6 | ||
| S7 | ||
| S8 | 2 | |
| S9 |
| Stakeholders | ||
|---|---|---|
| S1 | ||
| S2 | ||
| S3 | ||
| S4 | ||
| S5 | ||
| S6 | ||
| S7 | ||
| S8 | ||
| S9 |
| Group | Method | Feature ID | Accuracy | Precision | Recall | F1 Score | Time |
|---|---|---|---|---|---|---|---|
| Group 1 | chi2 | [2, 15, 18, 19, 22] | 0.9318 | 1 | 0.8637 | 0.8966 | 72.1125 |
| f_classif | [2, 15, 18, 19, 22] | 0.9318 | 1 | 0.8637 | 0.8966 | 74.0828 | |
| mutual_ info | [2, 36,37, 40, 41] | 0.9318 | 1 | 0.8637 | 0.8966 | 795.7370 | |
| entropy | [2, 15, 14, 27, 17, 36, 37, 40, 41,11, 12, 18, 19, 20, 21, 22] | 0.9318 | 1 | 0.8637 | 0.8966 | 252.578 | |
| importance_ RF | [2, 15, 19, 22] | 0.9318 | 1 | 0.8637 | 0.8966 | 1128.947 | |
| Group 2 | chi2 | [2, 15, 18, 19, 22] | 0.9318 | 1 | 0.8637 | 0.8966 | 72.1125 |
| f_classif | [2, 15, 18, 19, 22] | 0.9318 | 1 | 0.8637 | 0.8966 | 74.0828 | |
| mutual_ info | [2, 36,37, 40, 41] | 0.9318 | 1 | 0.8637 | 0.8966 | 795.737 | |
| entropy | [2, 15, 14, 27, 17, 36, 37, 40, 41, 11, 12, 18, 19, 20, 21, 22] | 0.9318 | 1 | 0.8637 | 0.8966 | 252.578 | |
| importance_ RF | [2, 15, 19, 22] | 0.9318 | 1 | 0.8637 | 0.8966 | 1128.947 | |
| Group 3 | chi2 | [2, 15, 34, 19, 22] | 0.9319 | 1.0000 | 0.8637 | 0.8966 | 94.2569 |
| f_classif | [2, 15, 34, 19, 22] | 0.9319 | 1.0000 | 0.8637 | 0.8966 | 98.0719 | |
| mutual_ info | [42, 33, 34, 30, 31] | 0.8752 | 0.8003 | 0.9999 | 0.8890 | 1280.683 | |
| entropy | [2, 15, 43 42, 6, 23, 24, 28, 29, 32, 33, 34, 35, 4, 25, 26, 30, 31,18, 19,20, 21, 22] | 0.9299 | 0.9960 | 0.8637 | 0.8946 | 348.2347 | |
| importance_ RF | [2, 15, 43, 42, 33, 19] | 0.9318 | 1.0000 | 0.8637 | 0.8966 | 804.577 |
| Group | Method | Feature ID | Accuracy | Precision | Recall | F1 Score | Time |
|---|---|---|---|---|---|---|---|
| Group 1 | chi2 | [36, 19, 20, 10, 31] | 0.8047 | 0.7865 | 0.8648 | 0.8183 | 17.6258 |
| f_classif | [36, 6, 19, 20, 10] | 0.7702 | 0.7845 | 0.7963 | 0.7685 | 23.7648 | |
| mutual_ info | [10, 11, 31, 32, 34] | 0.7889 | 0.7733 | 0.8541 | 0.8043 | 166.4645 | |
| entropy | [36, 6, 14, 19, 20, 40, 10, 11, 31, 32, 33, 34, 35, 27, 28] | 0.8426 | 0.8312 | 0.8884 | 0.8513 | 74.7406 | |
| importance_ RF | [6, 10, 11, 31, 32, 34] | 0.7867 | 0.7733 | 0.8491 | 0.8016 | 207.4284 | |
| Group 2 | chi2 | [10, 11, 31, 7, 24] | 0.7911 | 0.7707 | 0.8643 | 0.8086 | 16.0989 |
| f_classif | [10, 31, 34, 28, 24] | 0.7888 | 0.7709 | 0.8590 | 0.8056 | 22.0848 | |
| mutual_ info | [10, 11, 7, 23, 24] | 0.7900 | 0.7706 | 0.8625 | 0.8073 | 136.3324 | |
| entropy | [10, 11, 31, 32, 33, 34, 35, 27, 28, 5, 7, 23, 24] | 0.7885 | 0.7747 | 0.8501 | 0.8032 | 79.4134 | |
| importance_ RF | [10, 11, 23, 24] | 0.7899 | 0.7706 | 0.8624 | 0.8072 | 240.6583 | |
| Group 3 | chi2 | [10, 19, 20, 36, 24] | 0.8051 | 0.7865 | 0.8657 | 0.8189 | 24.1376 |
| f_classif | [10, 19, 20, 6, 24] | 0.8012 | 0.7846 | 0.8590 | 0.8146 | 18.6429 | |
| mutual_ info | [10, 11, 8, 9, 23] | 0.7900 | 0.7708 | 0.8626 | 0.8074 | 225.8134 | |
| entropy | [10, 11, 31, 32, 33, 34, 35, 27, 28, 14, 19, 20, 40, 17, 18, 8, 9, 6, 36, 23, 24] | 0.8544 | 0.8447 | 0.8926 | 0.8612 | 98.0131 | |
| importance_ RF | [10, 11, 34, 18, 8, 9, 23, 24] | 0.7890 | 0.7732 | 0.8552 | 0.8049 | 238.2793 |
| Dataset | Group | Votes | Total | ||
|---|---|---|---|---|---|
| V5 | V4 | V3 | |||
| Bot_IoT | G1 | [2,34] | [15] | [42,23,32,33,35] | 8 |
| G2 | [2] | [15,19,22] | [18] | 5 | |
| G3 | N/A | [2,15,19,34] | [22,33,42] | 7 | |
| UNSW-NB15 | G1 | [10 | [31] | [36,6,19,20,11,32,34] | 9 |
| G2 | [10,24] | [11] | [31,7,23] | 6 | |
| G3 | [10] | [24] | [20,11,23,9,8,19] | 8 | |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).