Submitted:
07 May 2023
Posted:
08 May 2023
You are already at the latest version
Abstract
Keywords:
1. Introduction
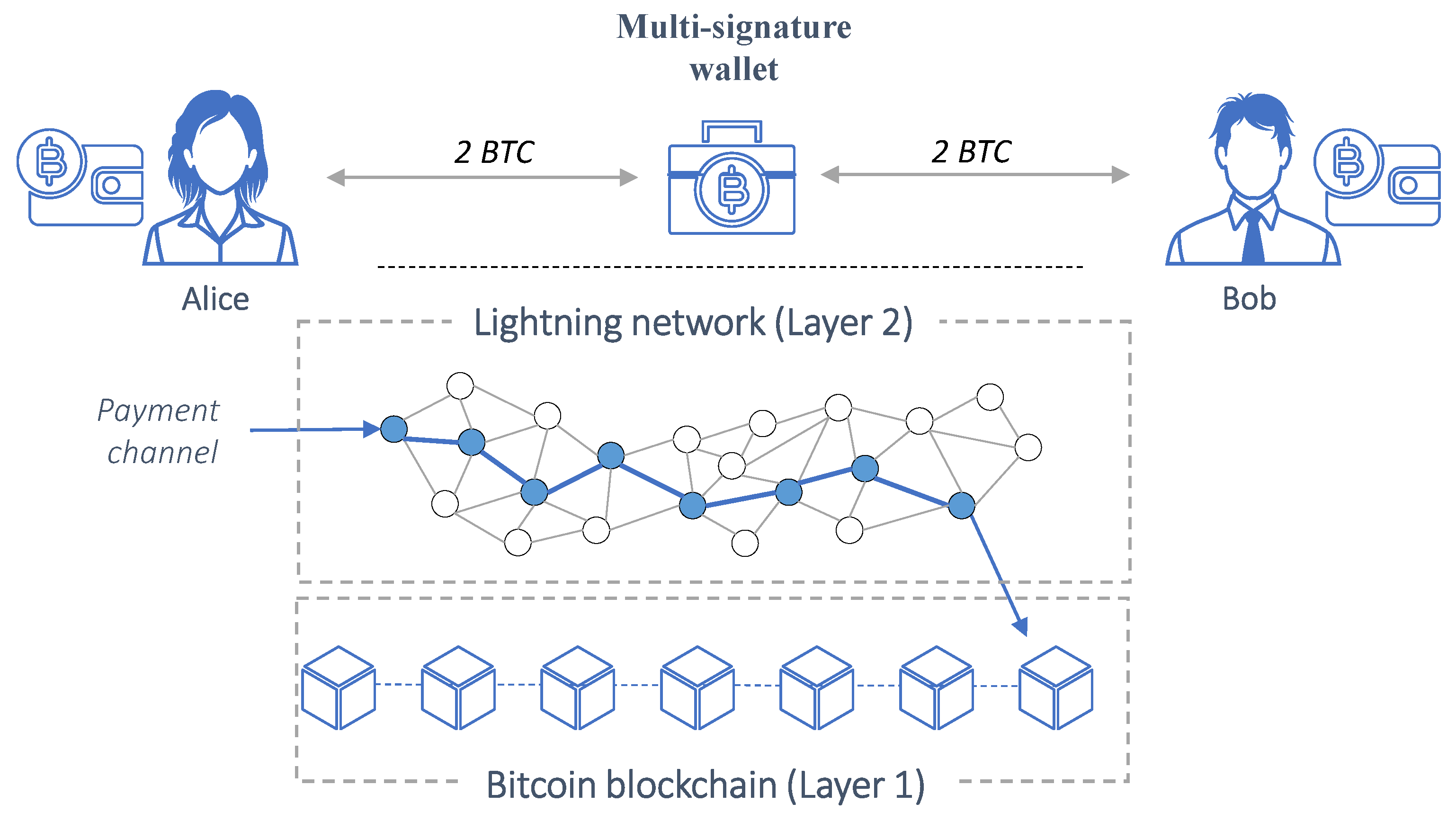
- Alice and Bob, both with bitcoin wallets, agree to create a channel between them. Alice funds the channel with a specific amount (e.g., 2 BTC). Currently, only one user can fund a channel, but developers aim to enable both parties to contribute.
- Both participants exchange public keys, which are required for BTC blockchain transactions.
- A new BTC address, a "2-of-2 multisig address," is created using their public keys. This special address type requires signatures from both participants to validate a transaction.
- Before the channel is built, a refund transaction is created to ensure Alice can retrieve her funds without trusting Bob. This transaction, signed by both parties, becomes valid once the Lightning channel is funded. It remains off-chain, shared only between Alice and Bob.
- After validating the refund transaction, the funding transaction takes place, with Alice depositing 2 BTC into the multisig address. The Lightning Channel is now open for further transactions, and Alice can reclaim her Bitcoins through the refund transaction, which can be executed by publishing it on the bitcoin blockchain.
1.1. Motivation and contribution
- An exploration of the various technical characteristics of the LN as well as its main attributes with respect to network’s topology, performance, privacy and security, among others. By examining these aspects, businesses and the research community can gain insights into how the technical characteristics of the LN can give rise to a new global, monetary network.
- An exploration of applications and use cases of the LN across different industries, including retail, e-commerce, and remittance services, particularly emphasizing its low transaction costs, near-instant transaction speeds, and scalability. By examining these practical applications, businesses can gain insights into how the LN can be effectively utilized to address specific transaction-related challenges.
- Identification of potential challenges and limitations associated with the LN, such as liquidity constraints, privacy concerns, and technical complexities. This information will provide businesses and policymakers/researchers with a more comprehensive understanding of the LN and inform future research and development efforts.
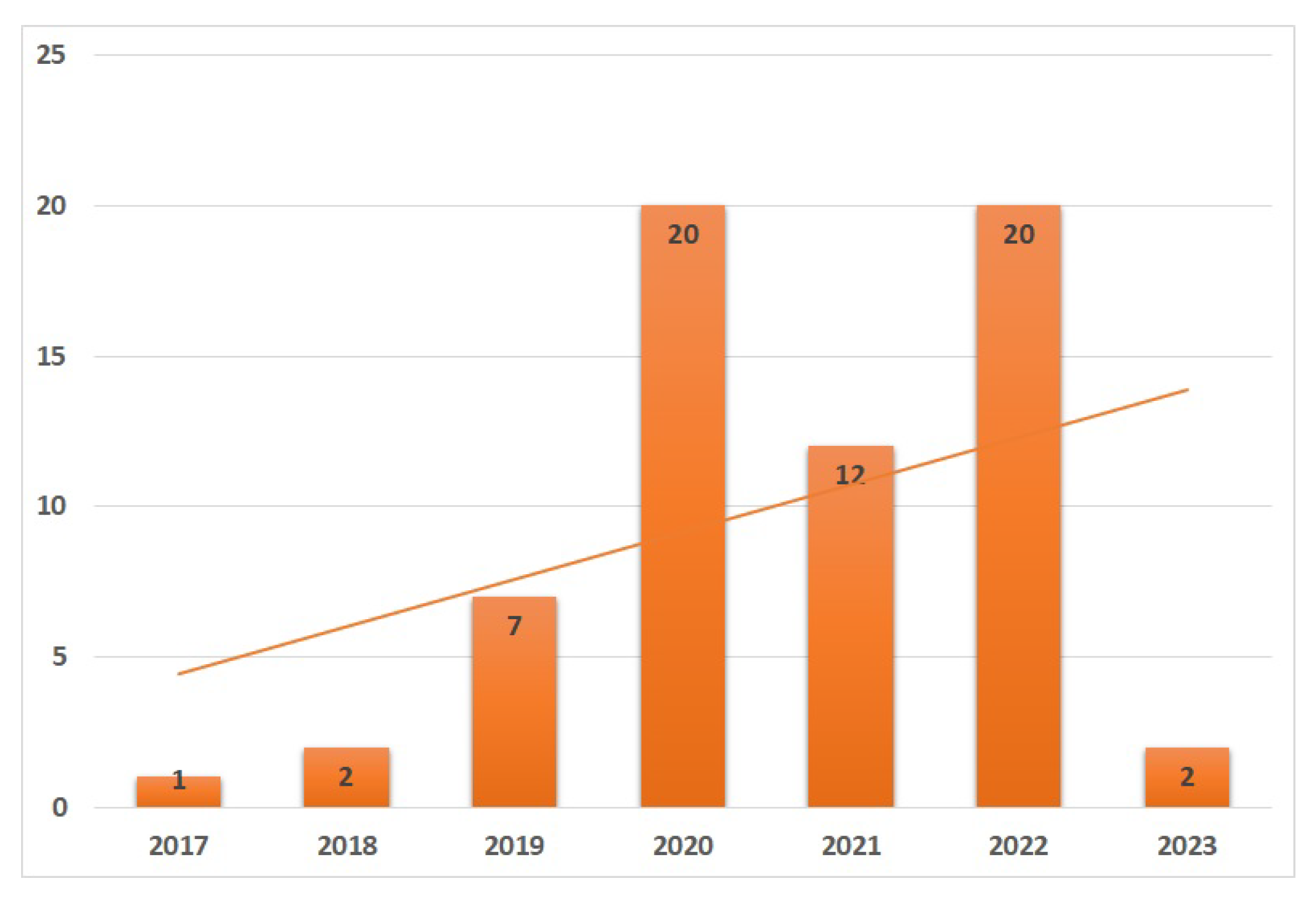
2. Methodology
2.1. Defining the scope of the review
2.2. Search strategy
2.3. Assessing the eligibility of the retrieved literature
2.4. Content Analysis
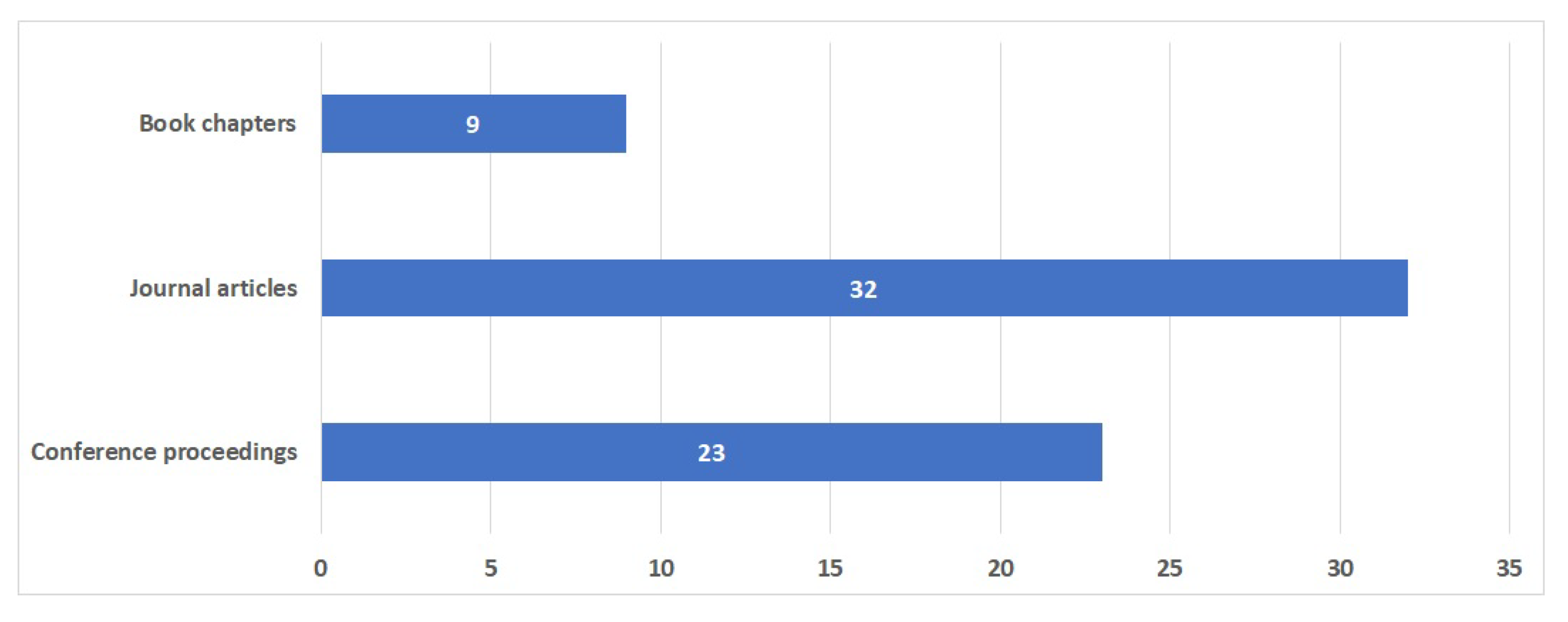
2.5. Synthesis and Reporting
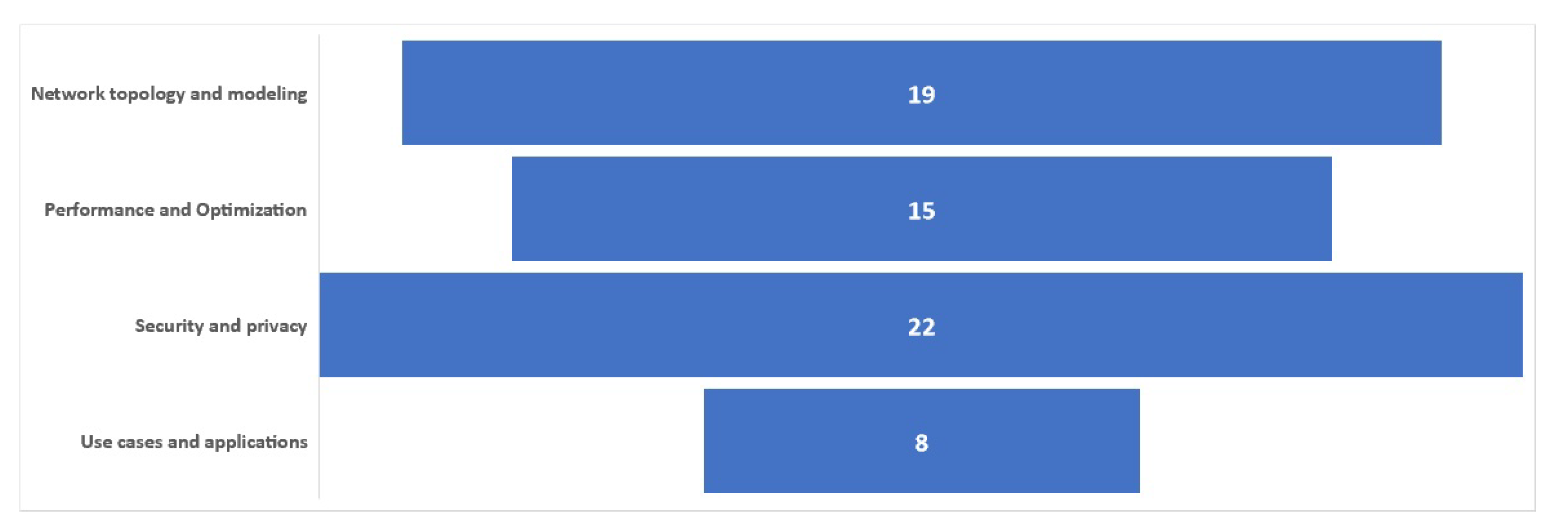
3. Literature review
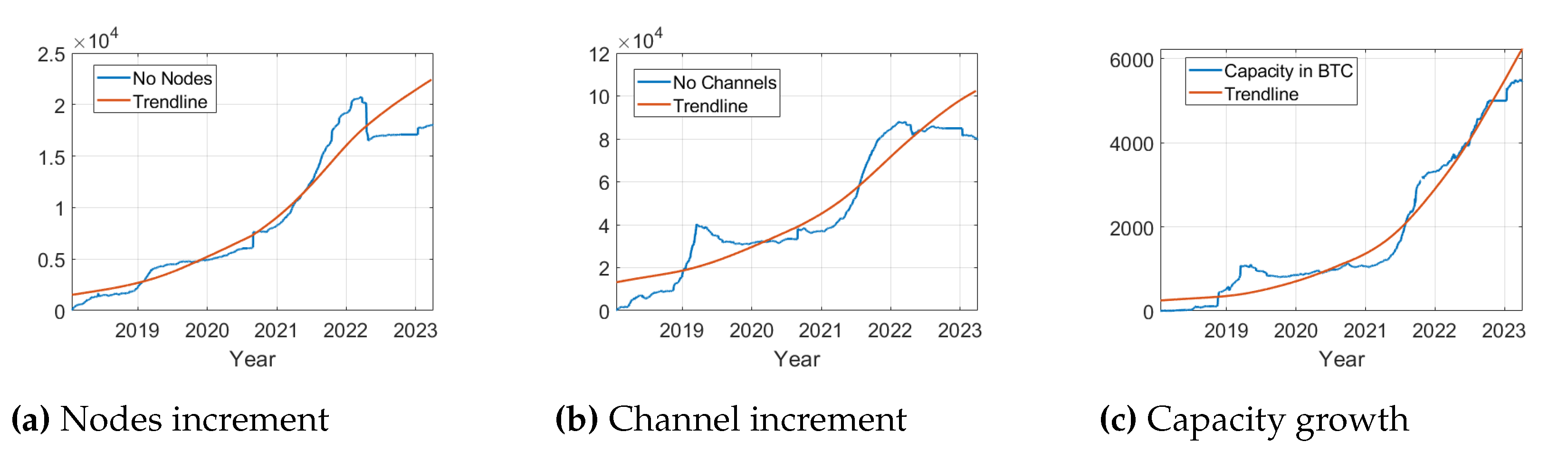
3.1. Network topology and modeling
3.2. Security and privacy
3.3. Performance and Optimization
3.4. Use cases and applications
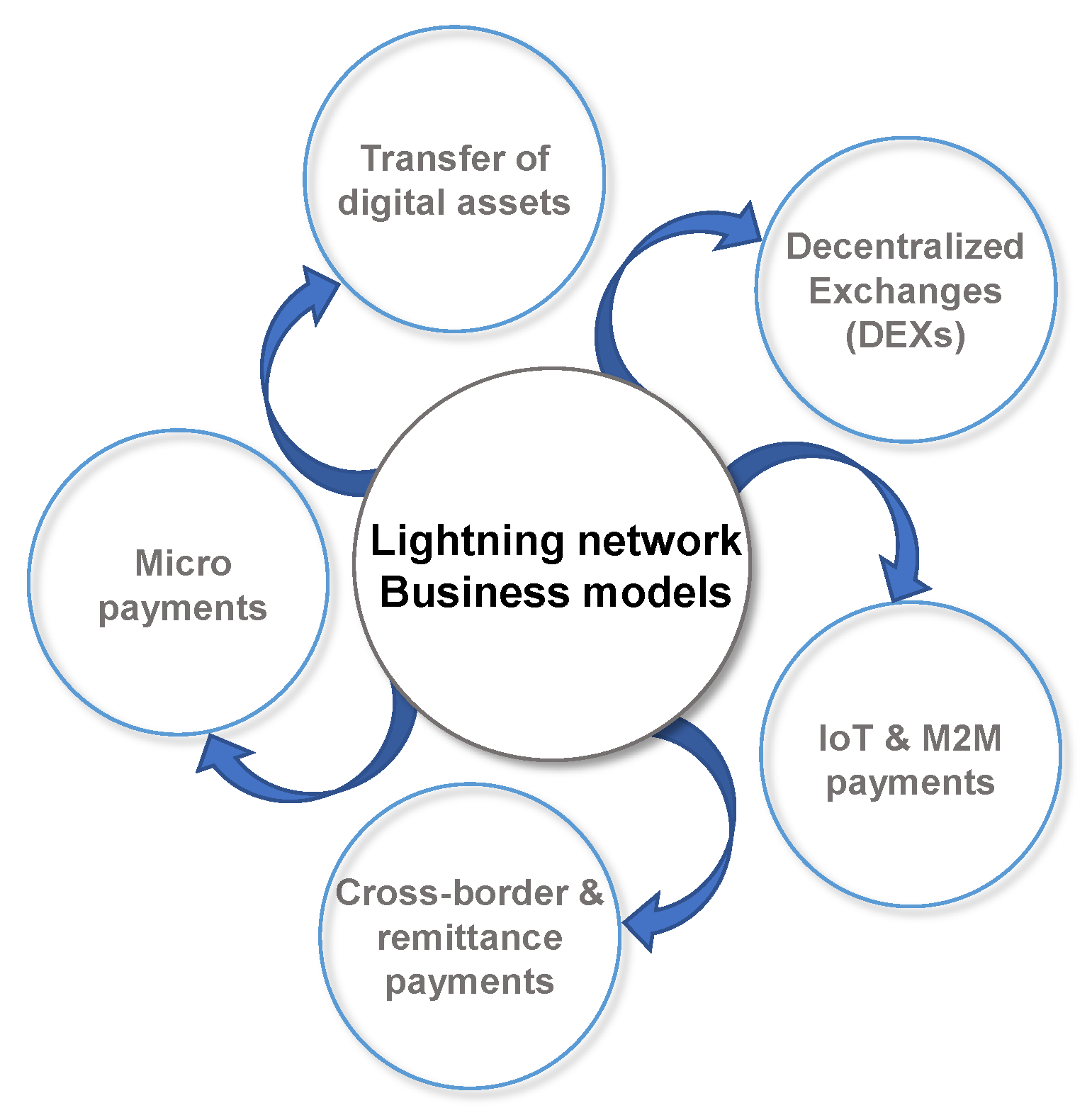
4. Business models empowered by the Lightning Network
4.1. Micropayments
4.2. Cross-border and remittance payments
4.3. IoT and Machine-to-Machine payments
4.4. Decentralized Exchanges
4.5. Transfers of digital assets
4.6. Lightning Network-related services
5. Discussion
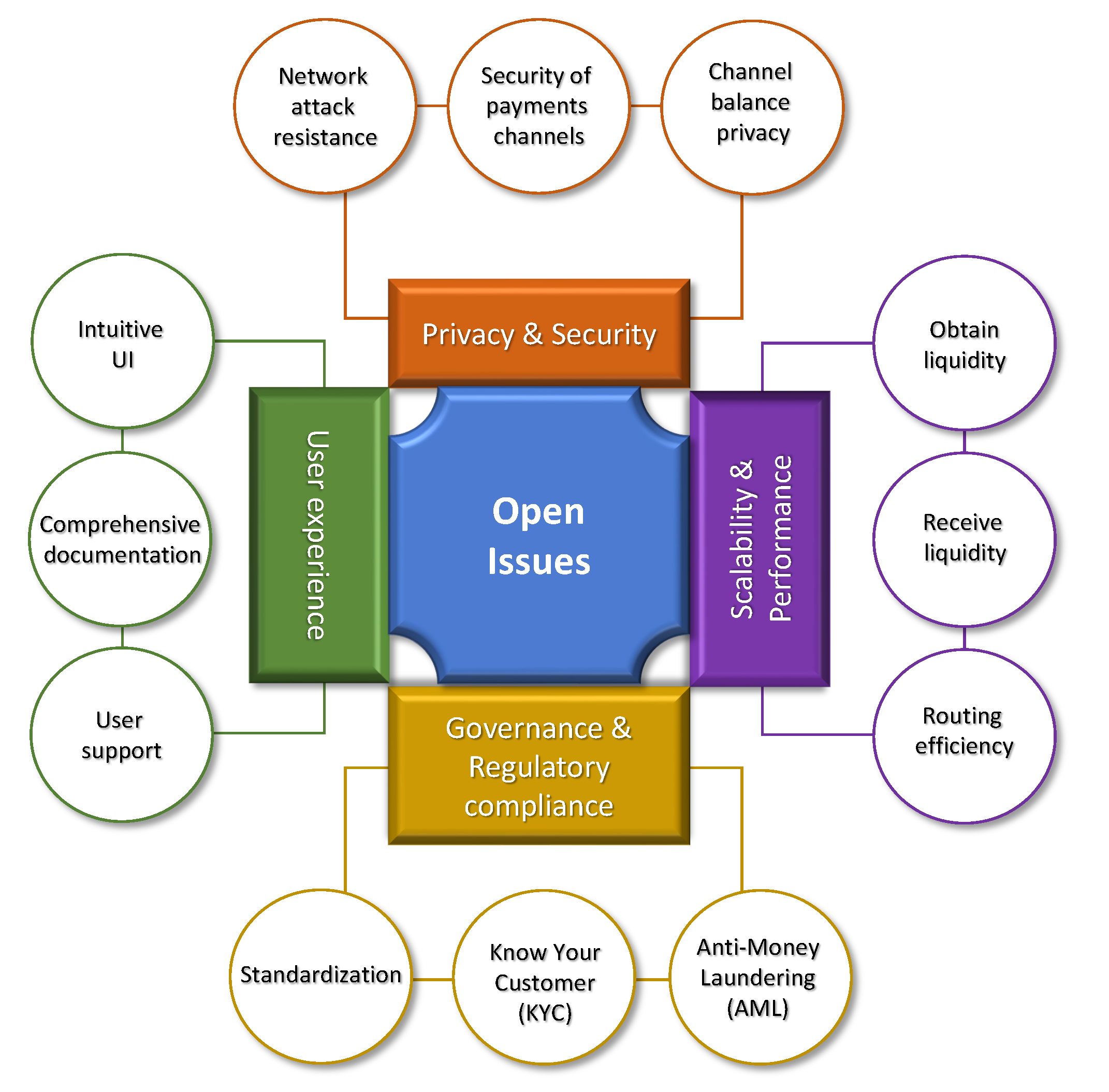
5.1. Open issues and adoption challenges
- Channel balance privacy: the risk of exposing channel balances during routing, which could reveal sensitive information about users’ funds. For example, the balance disclosure attack could reveal the balance of a channel by carrying out multiple non-finalized payments. The use of a multi-payment method, called Torrent, has been proposed by [43,59] as a mitigation strategy. Additionally, an attacker could obtain sensitive payment information by controlling just 2% of nodes, as presented in [48], by performing a wormhole attack. To decrease the exposure to this risk, users are suggested to open channels only with trusted parties.
- Security of payment channels: payment channels could be insecure, particularly in scenarios involving channel closure or uncooperative participants. For example, as mentioned in [12], an attacker could steal funds from nodes on the LN by causing congestion on the Bitcoin blockchain and exploiting the use of time locks to route payments. In another example, presented in [90], malicious actors could disable channels by repeatedly sending small payments through them and holding onto the corresponding HTLCs, causing channels to become frozen.
- Network attack resistance: the network may not always be able to resist in potential attack vectors, such as denial-of-service or eclipse attacks. For example, as presented in [90], an attacker can isolate a victim node, shut down Lightning channels, and steal funds without the victim being aware. Research has also found that the scale-free network topology used in the LN, makes it resistant to random disruptions but vulnerable to targeted attacks on highly connected hub nodes [28,41]. This means that removing a small number of key nodes can lead to a significant decrease in the efficiency of the network, and in some cases, cause the network to break down into disconnected parts [30,34,36]. Note, also, that an attacker could obtain sensitive payment information by controlling just 2% of nodes, as presented in [48], by performing a wormhole attack. To decrease the exposure to this risk, users are suggested to open channels only with trusted parties.
5.2. Key findings and future research suggestions
- Scalability, interoperability, and performance: Research should focus on improving the LN’s scalability to handle a growing number of transactions while ensuring interoperability with other blockchain platforms and payment systems. This includes optimizing the network topology to enhance resilience against attacks, addressing performance challenges such as convergence delays and network imbalance, and designing incentive mechanisms to encourage a decentralized distribution of nodes and channels.
- Security and privacy: Future research should examine security risks and privacy concerns associated with the LN, developing methods to mitigate these issues while maintaining the network’s efficiency and speed. This includes creating advanced privacy solutions to counterbalance various attacks and examining the trade-offs between privacy, performance, and network security. Researchers should work on identifying and addressing security vulnerabilities in the LN and developing adaptive routing protocols that can dynamically respond to network changes, congestion, and potential attacks, in order to maintain high transaction throughput and low latency.
- Regulatory frameworks and market adoption: Investigating appropriate regulatory frameworks for successful LN implementation and adoption is crucial, addressing compliance, consumer protection, and taxation issues. Additionally, understanding factors that influence LN adoption across industries and exploring innovative financial services and products through the LN will help expand its applications. To understand the adoption of the LN, we can use game theory to model the behavior of various actors, such as bitcoin users, merchants, payment processors, and developers.
- Integration with IoT, M2M ecosystems, and existing systems: Studying potential LN use cases in the context of IoT and M2M ecosystems is essential, as well as examining technical requirements for integration. Additionally, research should focus on seamless integration of the LN with existing payment systems and explore tailored solutions for small and medium-sized enterprises to address their specific challenges and resource limitations.
- Economic, social impact, and impact assessment: Investigating the broader economic and social implications of widespread LN adoption, such as financial inclusion and global economic growth, is essential. Evaluating the impact of LN adoption on businesses and developing metrics to assess the effectiveness of LN integration and adoption efforts will help drive informed decision-making. Analyzing the potential implications of LN adoption for traditional financial institutions is important for understanding how they might need to adapt their business models and strategies to remain competitive in a blockchain-driven financial landscape.
- Education and awareness: Developing educational resources and initiatives to increase LN awareness among businesses, policymakers, and the general public is crucial for facilitating its adoption and integration into mainstream financial systems.
- Usability, user experience, and liquidity management: Research should focus on improving the LN’s usability and user experience, addressing onboarding, user interface, and user support. Enhancing the user experience by simplifying channel management and securing liquidity, as well as developing innovative solutions to address liquidity and channel capacity issues, will make LN adoption more accessible for businesses with varying technical expertise.
5.3. Limitations
6. Conclusions
Funding
Conflicts of Interest
References
- Khando, K.; Islam, M.S.; Gao, S. The Emerging Technologies of Digital Payments and Associated Challenges: A Systematic Literature Review. Future Internet 2023, 15. [Google Scholar] [CrossRef]
- Tang, Y.M.; Chau, K.Y.; Hong, L.; Ip, Y.K.; Yan, W. Financial innovation in digital payment with wechat towards electronic business success. Journal of Theoretical and Applied Electronic Commerce Research 2021, 16, 1844–1861. [Google Scholar] [CrossRef]
- Patil, P.P.; Dwivedi, Y.K.; Rana, N.P. Digital payments adoption: An analysis of literature. Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), 0595. [Google Scholar] [CrossRef]
- Chaveesuk, S.; Khalid, B.; Chaiyasoonthorn, W. Digital payment system innovations: A marketing perspective on intention and actual use in the retail sector. Innovative Marketing 2021, 17, 109–123. [Google Scholar] [CrossRef]
- Guo, Y.; Tong, J.; Feng, C. A measurement study of bitcoin lightning network. Proceedings - 2019 2nd IEEE International Conference on Blockchain, Blockchain 2019, 2019, pp. 202–211. [Google Scholar]
- Khan, N.; State, R. Lightning network: A comparative review of transaction fees and data analysis; Vol. 1010, 2020. Pages: 18.
- Teoh, B. Navigating the Blockchain Trilemma: A Supply Chain Dilemma. Advanced Structured Materials 2022, 166, 291–300. [Google Scholar] [CrossRef]
- Arcane Research. The State of Lightning Volume 2. Retrieved , 2023 from https://arcane.no/research/reports/the-state-of-lightning-volume-2. Technical report. 02 February.
- Zhao, Z.; Zhou, L.; Su, C. Systematic Research on Technology and Challenges of Lightning Network. 2021 IEEE Conference on Dependable and Secure Computing, DSC 2021, 2021.
- Poon, J.; Dryja, T. The bitcoin lightning network: Scalable off-chain instant payments, 2016.
- Azzolini, D.; Riguzzi, F. Probabilistic Logic Models for the Lightning Network. Cryptography 2022, 6. [Google Scholar] [CrossRef]
- Harris, J.; Zohar, A. Flood & Loot: A Systemic Attack on the Lightning Network. AFT 2020 - Proceedings of the 2nd ACM Conference on Advances in Financial Technologies, 2020; pp. 202–213. [Google Scholar]
- Miraz, M.; Donald, D. Lapps: Technological, legal and market potentials of blockchain lightning network applications. ACM International Conference Proceeding Series, 2019, pp. 185–189.
- Ibaba, A.; Abdulmalik, A.; Alhassan, A.B.; Sunusi, I.; Thomas, S. Rem9ja: Bitcoin Lightning Network Remittance Solution. 2021 1st International Conference on Multidisciplinary Engineering and Applied Science, ICMEAS 2021, 2021.
- Tan, C.; Chen, Y.; Ren, X.; Peng, C. A mobile energy trading scheme based on Lightning Network. Concurrency and Computation: Practice and Experience.
- Kumar, S.; Amin, R. Decentralized trade finance using blockchain and lightning network. SECURITY AND PRIVACY. [CrossRef]
- Klein, M.; Stummer, C. Feeless Micropayments as Drivers for New Business Models: Two Exemplary Application Cases. Frontiers in Blockchain 2021, 4. [Google Scholar] [CrossRef]
- Mercan, S.; Kurt, A.; Akkaya, K.; Erdin, E. Cryptocurrency Solutions to Enable Micropayments in Consumer IoT. IEEE Consumer Electronics Magazine 2022, 11, 97–103. [Google Scholar] [CrossRef]
- Kurt, A.; Mercana, S.; Erdin, E.; Akkaya, K. Enabling micro-payments on IoT devices using bitcoin lightning network. IEEE International Conference on Blockchain and Cryptocurrency, ICBC 2021, 2021.
- Robert, J.; Kubler, S.; Ghatpande, S. Enhanced Lightning Network (off-chain)-based micropayment in IoT ecosystems. Future Generation Computer Systems 2020, 112, 283–296. [Google Scholar] [CrossRef]
- Fang, Z.; Gai, K.; Zhu, L.; Xu, L. LNBFSM: A Food Safety Management System Using Blockchain and Lightning Network; Vol. 12454 LNCS, 2020. Pages: 34.
- Furley, P.; Goldschmied, N. Systematic vs. Narrative Reviews in Sport and Exercise Psychology: Is Either Approach Superior to the Other? Frontiers in Psychology 2021, 12. [Google Scholar] [CrossRef]
- Greenhalgh, T.; Thorne, S.; Malterud, K. Time to challenge the spurious hierarchy of systematic over narrative reviews? European Journal of Clinical Investigation 2018, 48. [Google Scholar] [CrossRef] [PubMed]
- Green, B.; Johnson, C.; Adams, A. Writing narrative literature reviews for peer-reviewed journals: Secrets of the trade. Journal of Sports Chiropractic and Rehabilitation 2001, 15, 5–17. [Google Scholar] [CrossRef] [PubMed]
- Wong, G.; Greenhalgh, T.; Westhorp, G.; Buckingham, J.; Pawson, R. RAMESES publication standards: Meta-narrative reviews. BMC Medicine 2013, 11. [Google Scholar] [CrossRef]
- Denyer, D.; Tranfield, D. Producing a systematic review. 2009.
- Chen, Y.J.; Zhu, X.T.; Yu, Y.R.; Cheng, Z.Y. Empirical Analysis of Lightning Network: Topology, Evolution, and Fees. Ruan Jian Xue Bao/Journal of Software 2022, 33, 3858–3873. [Google Scholar] [CrossRef]
- Lee, S.; Kim, H. On the robustness of Lightning Network in Bitcoin. Pervasive and Mobile Computing 2020, 61. [Google Scholar] [CrossRef]
- Chiam, E. Hands-on guide to bitcoin layer-2 lightning network node setup; 2021. D: Publication Title: Blockchain And Smart Contracts. [CrossRef]
- Lin, J.H.; Primicerio, K.; Squartini, T.; Decker, C.; Tessone, C. Lightning network: A second path towards centralisation of the Bitcoin economy. New Journal of Physics 2020, 22. [Google Scholar] [CrossRef]
- Bartolucci, S.; Caccioli, F.; Vivo, P. A percolation model for the emergence of the Bitcoin Lightning Network. Scientific Reports 2020, 10. [Google Scholar] [CrossRef]
- Wu, J.; Jiang, S. Local Pooling of Connected Supernodes in Lightning Networks for Blockchains. Proceedings - 2020 IEEE International Conference on Blockchain, Blockchain 2020, 2020, pp. 421–427. [Google Scholar]
- Azzolini, D.; Riguzzi, F.; Bellodi, E.; Lamma, E. A Probabilistic Logic Model of Lightning Network; Vol. 444 LNBIP, 2022. Pages: 333.
- Lisi, A.; Di Francesco Maesa, D.; Mori, P.; Ricci, L. Lightnings over rose bouquets: An analysis of the topology of the Bitcoin Lightning Network. Proceedings - 2021 IEEE 45th Annual Computers, Software, and Applications Conference, COMPSAC 2021, 2021, pp. 324–331. [Google Scholar]
- Wang, Z.; Zhang, R.; Sun, Y.; Ding, H.; Lv, Q. Can Lightning Network’s Autopilot Function Use BA Model as the Underlying Network? Frontiers in Physics 2022, 9. [Google Scholar] [CrossRef]
- Martinazzi, S.; Flori, A. The evolving topology of the Lightning Network: Centralization, efficiency, robustness, synchronization, and anonymity. PLoS ONE 2020, 15. [Google Scholar] [CrossRef] [PubMed]
- Azzolini, D.; Bellodi, E.; Brancaleoni, A.; Riguzzi, F.; Lamma, E. Modeling bitcoin lightning network by logic programming (extended abstract). Electronic Proceedings in Theoretical Computer Science, EPTCS, 2020, Vol. 325.
- Zabka, P.; Foerster, K.T.; Schmid, S.; Decker, C. Empirical evaluation of nodes and channels of the lightning network. Pervasive and Mobile Computing 2022, 83. [Google Scholar] [CrossRef]
- Lin, J.H.; Marchese, E.; Tessone, C.; Squartini, T. The weighted Bitcoin Lightning Network. Chaos, Solitons and Fractals 2022, 164. [Google Scholar] [CrossRef]
- Camilo, G.; Rebello, G.; De Souza, L.; Potop-Butucaru, M.; Amorim, M.; Campista, M.; Costa, L. Topological Evolution Analysis of Payment Channels in the Lightning Network. 2022 IEEE Latin-American Conference on Communications, LATINCOM 2022, 2022. [CrossRef]
- Seres, I.; Gulyás, L.; Nagy, D.; Burcsi, P. Topological Analysis of Bitcoin’s Lightning Network. Springer Proceedings in Business and Economics, 2020, pp. 1–12.
- Zabka, P.; Foerster, K.T.; Decker, C.; Schmid, S. Short Paper: A Centrality Analysis of the Lightning Network 2022. 1 2022, 3411 LNCS, 374–385. [Google Scholar] [CrossRef]
- Herrera-Joancomartí, J.; Navarro-Arribas, G.; Ranchal-Pedrosa, A.; Pérez-Solà, C.; Garcia-Alfaro, J. On the difficulty of hiding the balance of lightning network channels. AsiaCCS 2019 - Proceedings of the 2019 ACM Asia Conference on Computer and Communications Security, 2019, pp. 602–612.
- Rohrer, E.; Malliaris, J.; Tschorsch, F. Discharged Payment Channels: Quantifying the Lightning Network’s Resilience to Topology-Based Attacks. Proceedings - 4th IEEE European Symposium on Security and Privacy Workshops, EUROS and PW 2019, 2019, pp. 347–356. [Google Scholar]
- Hüttel, H.; Staroveški, V. Key Agreement in the Lightning Network Protocol; Vol. 1545 CCIS, 2022. Pages: 155.
- Piatkivskyi, D.; Axelsson, S.; Nowostawski, M. Digital forensic implications of collusion attacks on the lightning network; Vol. 511, 2017. Pages: 147.
- Mazumdar, S.; Banerjee, P.; Sinha, A.; Ruj, S.; Roy, B. Strategic Analysis of Griefing Attack in Lightning Network. IEEE Transactions on Network and Service Management. [CrossRef]
- Tikhomirov, S.; Moreno-Sanchez, P.; Maffei, M. A Quantitative Analysis of Security, Anonymity and Scalability for the Lightning Network. Proceedings - 5th IEEE European Symposium on Security and Privacy Workshops, Euro S and PW 2020, 2020, pp. 387–396. [Google Scholar]
- van Dam, G.; Kadir, R.; Nohuddin, P.; Zaman, H. Improvements of the Balance Discovery Attack on Lightning Network Payment Channels; Vol. 580 IFIP, 2020. Pages: 323.
- Pérez-Solà, C.; Ranchal-Pedrosa, A.; Herrera-Joancomartí, J.; Navarro-Arribas, G.; Garcia-Alfaro, J. LockDown: Balance Availability Attack Against Lightning Network Channels; Vol. 12059 LNCS, 2020. Pages: 263.
- Kiayias, A.; Litos, O. A Composable Security Treatment of the Lightning Network. Proceedings - IEEE Computer Security Foundations Symposium, 2020, Vol. 2020-June, pp. 334–349.
- Hüttel, H.; Staroveski, V. Secrecy and authenticity properties of the lightning network protocol. ICISSP 2020 - Proceedings of the 6th International Conference on Information Systems Security and Privacy, 2020, pp. 119–130.
- Mazumdar, S.; Banerjee, P.; Ruj, S. Time is money: Countering griefing attack in lightning network. Proceedings - 2020 IEEE 19th International Conference on Trust, Security and Privacy in Computing and Communications, TrustCom 2020, 2020, pp. 1036–1043. [Google Scholar]
- Leinweber, M.; Grundmann, M.; Schönborn, L.; Hartenstein, H. TEE-Based Distributed Watchtowers for Fraud Protection in the Lightning Network; Vol. 11737 LNCS, 2019. Pages: 194.
- Biryukov, A.; Naumenko, G.; Tikhomirov, S. Analysis and Probing of Parallel Channels in the Lightning Network 2022. 1 2022, 3411 LNCS, 337–357. [Google Scholar] [CrossRef]
- Nowostawski, M.; Tøn, J. Evaluating methods for the identification of off-chain transactions in the lightning network. Applied Sciences (Switzerland) 2019, 9. [Google Scholar] [CrossRef]
- van Dam, G.; Abdul Kadir, R. Hiding payments in lightning network with approximate differentially private payment channels. Computers and Security 2022, 115. [Google Scholar] [CrossRef]
- Wei, G.; Mao, X.; Lu, R.; Shao, J.; Guan, Y.; Lu, G. Achieve space-efficient key management in lightning network. Computer Networks 2021, 197. [Google Scholar] [CrossRef]
- Rahimpour, S.; Khabbazian, M. Torrent: Strong, Fast Balance Discovery in the Lightning Network. IEEE International Conference on Blockchain and Cryptocurrency, ICBC 2022, 2022.
- Zhao, Z.; Ge, C.; Zhou, L.; Wang, H. Fully Discover the Balance of Lightning Network Payment Channels; Vol. 12937 LNCS, 2021. Pages: 173.
- Kurt, A.; Erdin, E.; Cebe, M.; Akkaya, K.; Uluagac, A. Lnbot: A covert hybrid botnet on bitcoin lightning network for fun and profit 2020. 1 2020, 2309 LNCS, 734–755. [Google Scholar] [CrossRef]
- Kappos, G.; Yousaf, H.; Piotrowska, A.; Kanjalkar, S.; Delgado-Segura, S.; Miller, A.; Meiklejohn, S. An Empirical Analysis of Privacy in the Lightning Network; Vol. 12674 LNCS, 2021. Pages: 186.
- Conoscenti, M.; Vetrò, A.; De Martin, J.; Spini, F. The CLoTH simulator for HTLC payment networks with introductory lightning network performance results. Information (Switzerland) 2018, 9. [Google Scholar] [CrossRef]
- Di Stasi, G.; Avallone, S.; Canonico, R.; Ventre, G. Routing Payments on the Lightning Network. Proceedings - IEEE 2018 International Congress on Cybermatics: 2018 IEEE Conferences on Internet of Things, Green Computing and Communications, Cyber, Physical and Social Computing, Smart Data, Blockchain, Computer and Information Technology, iThings/GreenCom/CPSCom/SmartData/Blockchain/CIT 2018, 2018, pp. 1161–1170. [Google Scholar]
- Divakaruni, A.; Zimmerman, P. The Lightning Network: Turning Bitcoin into money. Finance Research Letters 2023, 52. [Google Scholar] [CrossRef]
- Gai, K.; Fang, Z.; Wang, R.; Zhu, L.; Jiang, P.; Choo, K.K.R. Edge Computing and Lightning Network Empowered Secure Food Supply Management. IEEE Internet of Things Journal 2022, 9, 14247–14259. [Google Scholar] [CrossRef]
- Liu, M.; Au, M. Practical Anonymous Multi-hop Locks for Lightning Network Compatible Payment Channel Networks. Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), 3787. [Google Scholar] [CrossRef]
- Davis, V.; Harrison, B. Learning a Scalable Algorithm for Improving Betweenness in the Lightning Network. 2022 4th International Conference on Blockchain Computing and Applications, BCCA 2022, 2022, pp. 119–126. [Google Scholar] [CrossRef]
- Seo, J.; Kim, J. Enhancing Scalability with Payment Requests Aggregation in Lightning Network. Proceedings - 2022 IEEE International Conference on Blockchain, Blockchain 2022, 2022, pp. 340–347. [Google Scholar] [CrossRef]
- Wu, J.; Jiang, S. On Increasing Scalability and Liquidation of Lightning Networks for Blockchains. IEEE Transactions on Network Science and Engineering 2022, 9, 2589–2600. [Google Scholar] [CrossRef]
- Martinazzi, S.; Regoli, D.; Flori, A. A tale of two layers: The mutual relationship between bitcoin and lightning network. Risks 2020, 8, 1–18. [Google Scholar] [CrossRef]
- Gögge, N.; Rohrer, E.; Tschorsch, F. On the Routing Convergence Delay in the Lightning Network. Data Privacy Management, Cryptocurrencies and Blockchain Technology; Garcia-Alfaro, J., Navarro-Arribas, G., Dragoni, N., Eds.; Springer International Publishing: Cham, 2023; pp. 203–218. [Google Scholar]
- Conoscenti, M.; Vetrò, A.; De Martin, J. CLoTH: A Lightning Network Simulator. SoftwareX 2021, 15. [Google Scholar] [CrossRef]
- Qiao, Y.; Wu, K.; Khabbazian, M. Non-Intrusive and High-Efficient Balance Tomography in the Lightning Network. ASIA CCS 2021 - Proceedings of the 2021 ACM Asia Conference on Computer and Communications Security, 2021, pp. 832–843.
- Pickhardt, R.; Nowostawski, M. Imbalance measure and proactive channel rebalancing algorithm for the Lightning Network. IEEE International Conference on Blockchain and Cryptocurrency, ICBC 2020, 2020.
- Jun Ren, A.; Feng, L.; Cheong, S.; Goh, R. Optimal Fee Structure for Efficient Lightning Networks. Proceedings of the International Conference on Parallel and Distributed Systems - ICPADS, 2019, Vol. 2018-December, pp. 980–985.
- Conoscenti, M.; Vetro, A.; De Martin, J. Hubs, Rebalancing and Service Providers in the Lightning Network. IEEE Access 2019, 7, 132828–132840. [Google Scholar] [CrossRef]
- Aspris, A.; Foley, S.; Svec, J.; Wang, L. Decentralized exchanges: The “wild west” of cryptocurrency trading. International Review of Financial Analysis 2021, 77. [Google Scholar] [CrossRef]
- Doe, D.; Li, J.; Dusit, N.; Wang, L.; Han, Z. Incentive Mechanism Design for Mitigating Frontrunning and Transaction Reordering in Decentralized Exchanges. IEEE Access. [CrossRef]
- Mohan, V. Automated market makers and decentralized exchanges: A DeFi primer. Financial Innovation 2022, 8. [Google Scholar] [CrossRef]
- Jones, B.A.; Goodkind, A.L.; Berrens, R.P. Economic estimation of Bitcoin mining’s climate damages demonstrates closer resemblance to digital crude than digital gold. Scientific Reports 2022, 12. [Google Scholar] [CrossRef] [PubMed]
- Velický, M. Renewable Energy Transition Facilitated by Bitcoin. ACS Sustainable Chemistry & Engineering 2023, 11, 3160–3169. [Google Scholar] [CrossRef]
- Badea, L.; Mungiu-Pupazan, M.C. The Economic and Environmental Impact of Bitcoin. IEEE Access 2021, 9, 48091–48104. [Google Scholar] [CrossRef]
- Köhler, S.; Pizzol, M. Life Cycle Assessment of Bitcoin Mining. Environmental Science & Technology 2019, 53, 13598–13606. [Google Scholar] [CrossRef]
- Niaz, H.; Shams, M.H.; Liu, J.J.; You, F. Mining bitcoins with carbon capture and renewable energy for carbon neutrality across states in the USA. Energy and Environmental Science 2022, 15, 3551–3570. [Google Scholar] [CrossRef]
- Bitcoin Mining Council. Global Bitcoin mining data review, Q4 2022. Technical report, 2023.
- Farrell, H.; Newman, A. Weak links in finance and supply chains are easily weaponized. Nature 2022, 605, 219–222. [Google Scholar] [CrossRef]
- Robinson, G.; Dörry, S.; Derudder, B. Global networks of money and information at the crossroads: Correspondent banking and SWIFT. Global Networks 2023, 23, 478–493. [Google Scholar] [CrossRef]
- Pixley, J.; Whimster, S.; Wilson, S. Central bank independence: A social economic and democratic critique. Economic and Labour Relations Review 2013, 24, 32–50. [Google Scholar] [CrossRef]
- CoinDesk Research. A Deep Dive Into Lightning as a Bitcoin Scaling Solution. Technical report, 2021.
| 1 | |
| 2 | |
| 3 | |
| 4 | |
| 5 | |
| 6 | |
| 7 | |
| 8 | |
| 9 | |
| 10 |
| Research questions | Objectives |
|---|---|
| RQ1: What are the current and potential business-related applications of the LN? | This question would explore the various ways that businesses could use the LN to streamline their operations, reduce costs, and offer new services to customers. It would involve a comprehensive review of the existing literature on LN applications, as well as a discussion of potential future applications. |
| RQ2: What is the current status of the LN in terms of its technical characteristics (network topology, performance, privacy, and security etc.), and how do these factors affect its adoption and effectiveness for business-related applications? | The objective of this research is to assess the current status of the LN and its implications for business-related applications by focusing on the network’s technical characteristics, topology, performance, privacy, and security. |
| RQ3: What are the adoption challenges that businesses may face when using the LN? To what extent? | This question would explore the barriers and challenges that businesses may encounter when implementing the LN, such as regulatory hurdles, security concerns, and user adoption. It would involve a review of the existing literature on LN adoption challenges, as well as a discussion of potential strategies for addressing these challenges. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




