Submitted:
19 January 2023
Posted:
20 January 2023
You are already at the latest version
Abstract
Keywords:
I. INTRODUCTION
A. Problem Definition
 |
B. Protocol Use For IoT Communication
- 1)
- Message Queue Telemetry (MQTT)
- 2)
- Constrained Application Protocol
- 3)
- REST
II. RELATED WORKS
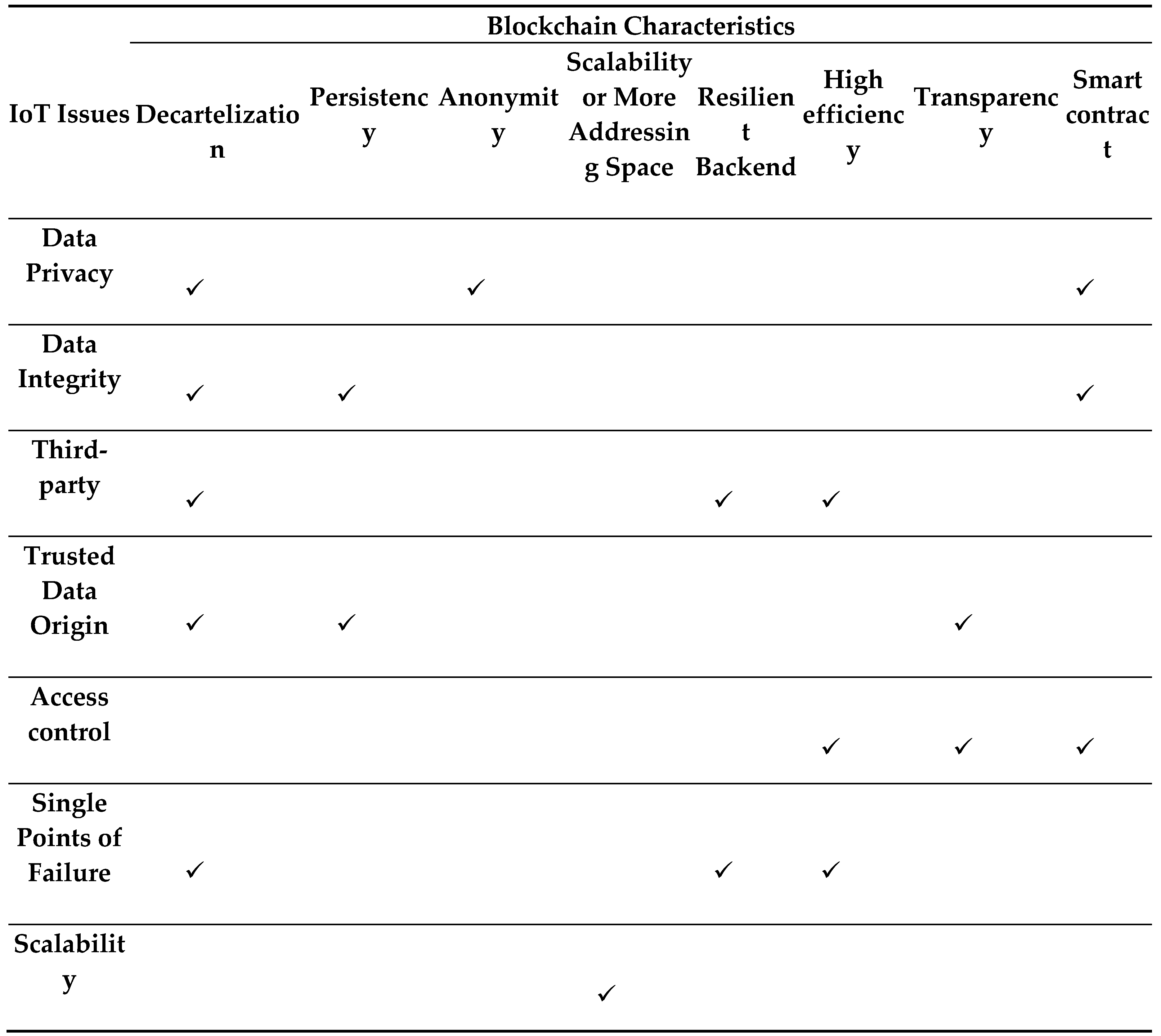
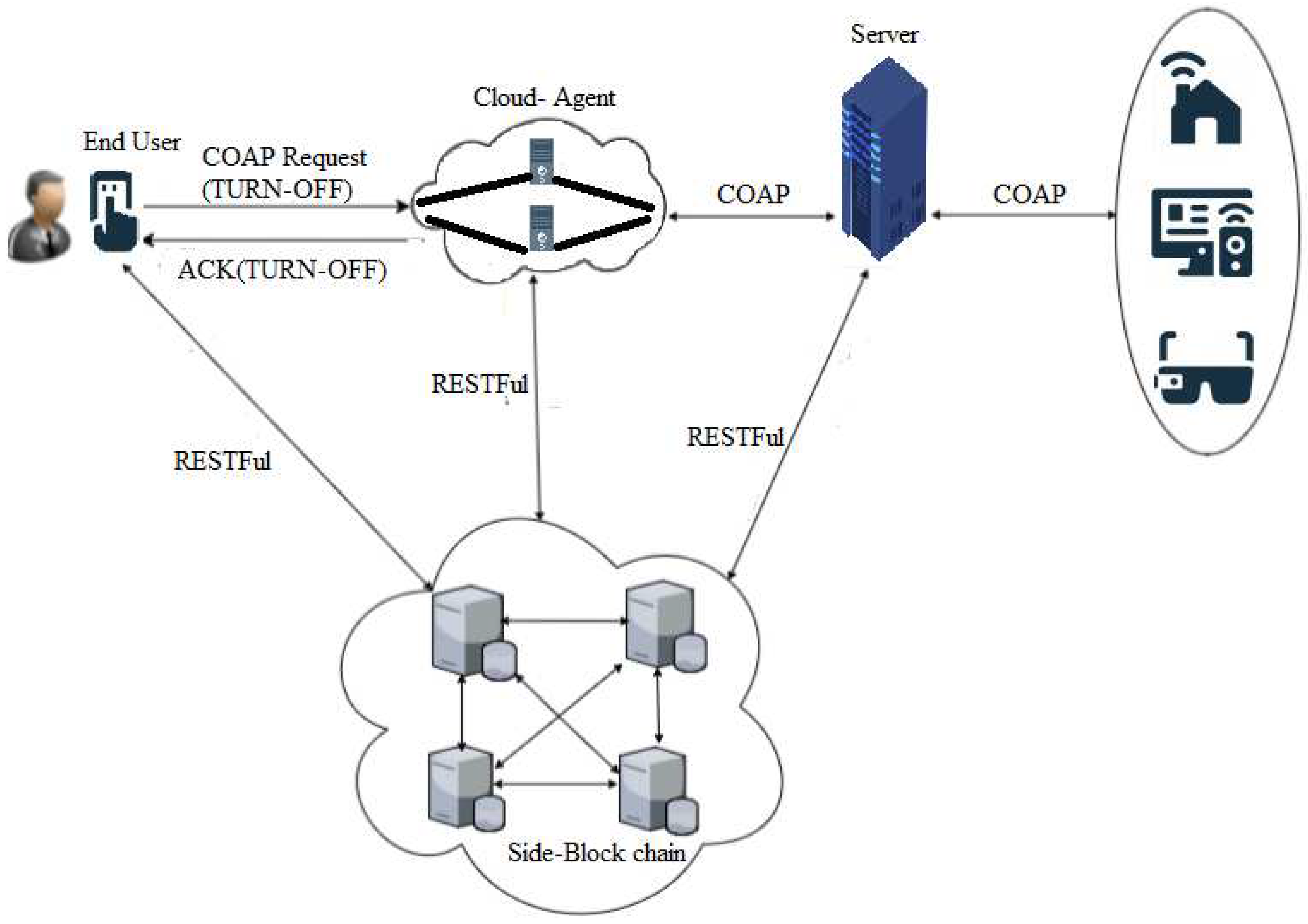
III. ALL RELATED STUDIES EXPOSE THAT NOTHING HAS BEEN DONE FOR THE TRACEABILITY, DATA PRIVACY, AND ACCOUNTABILITY IN THE IOT NETWORK. ON THESE BASES, THIS PAPER AIMS TO DESIGN A TDA BASED BLOCKCHAIN ARCHITECTURE THAT PROVIDES TRACEABILITY AND DATA PRIVACY FROM UNAUTHORIZED PERSONAL IN THE IOT NETWORK.PROPOSED ARCHITECTURE
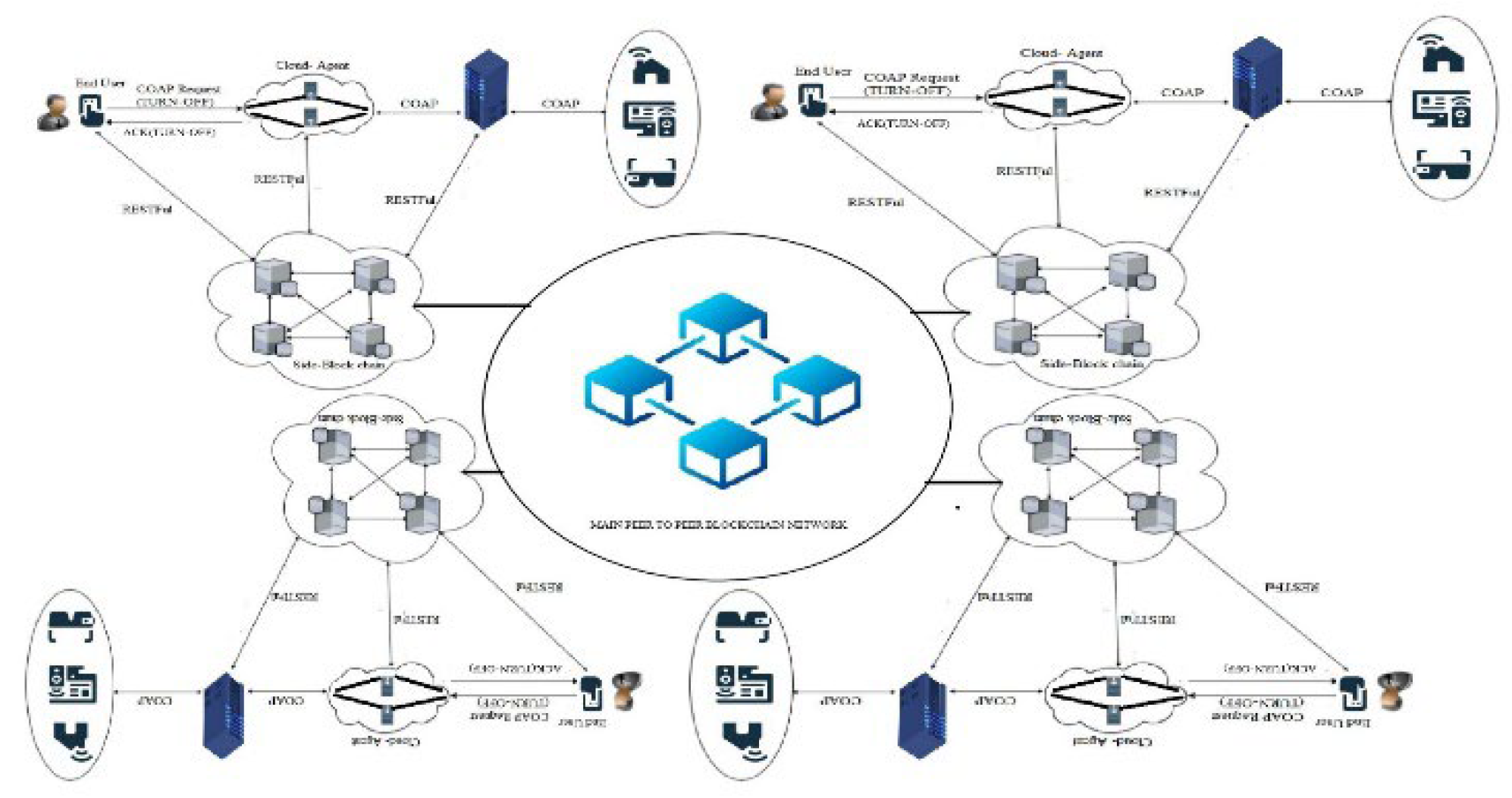
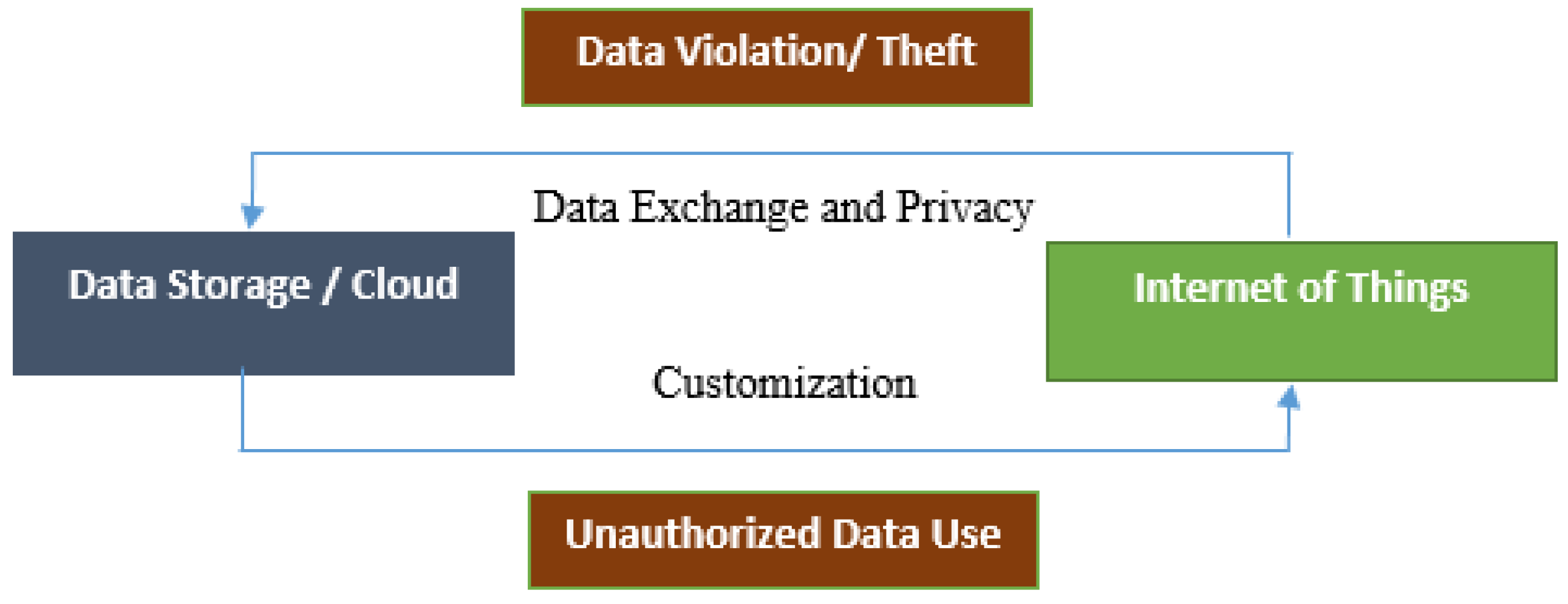
A. Data Privacy in the Proposed System
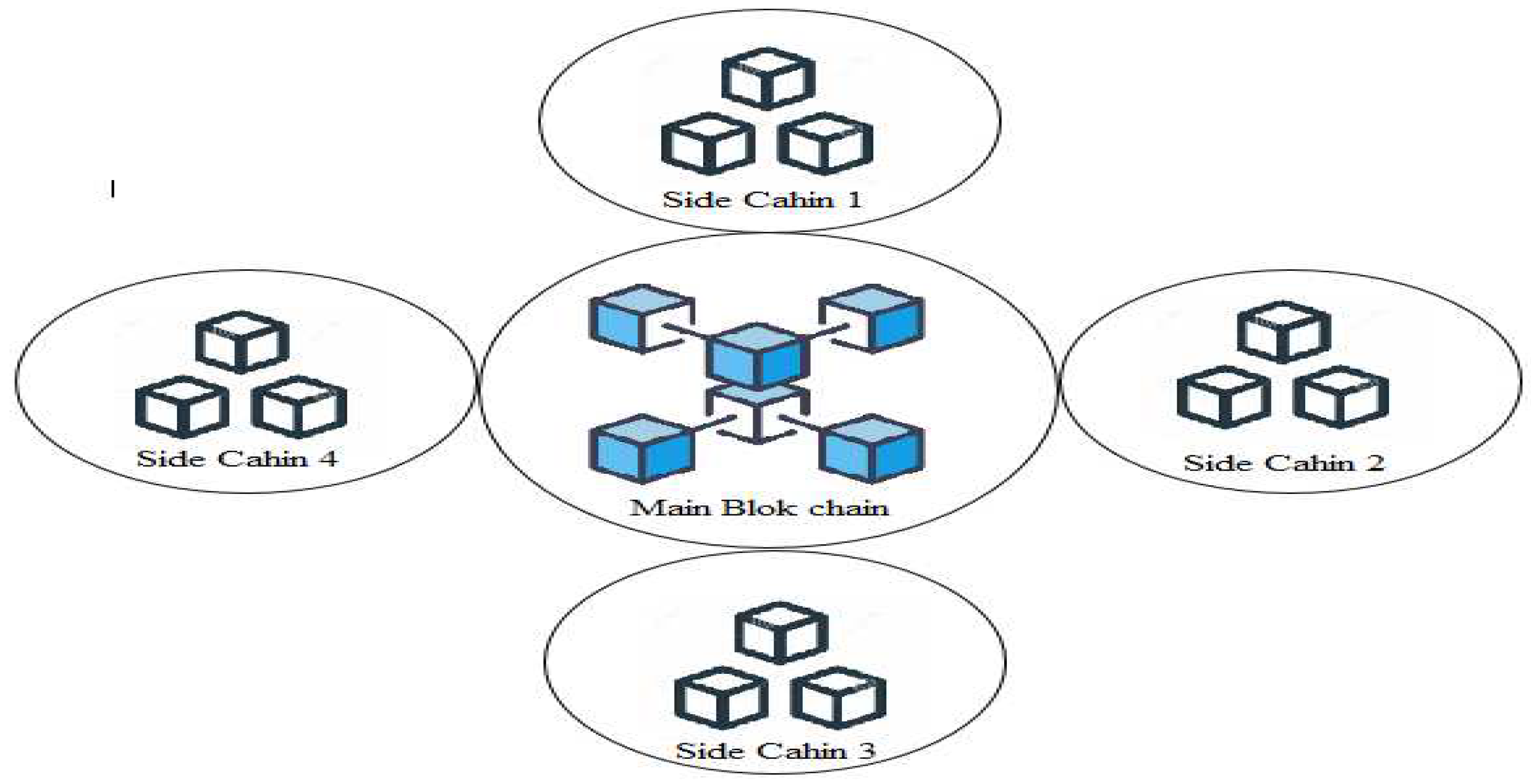
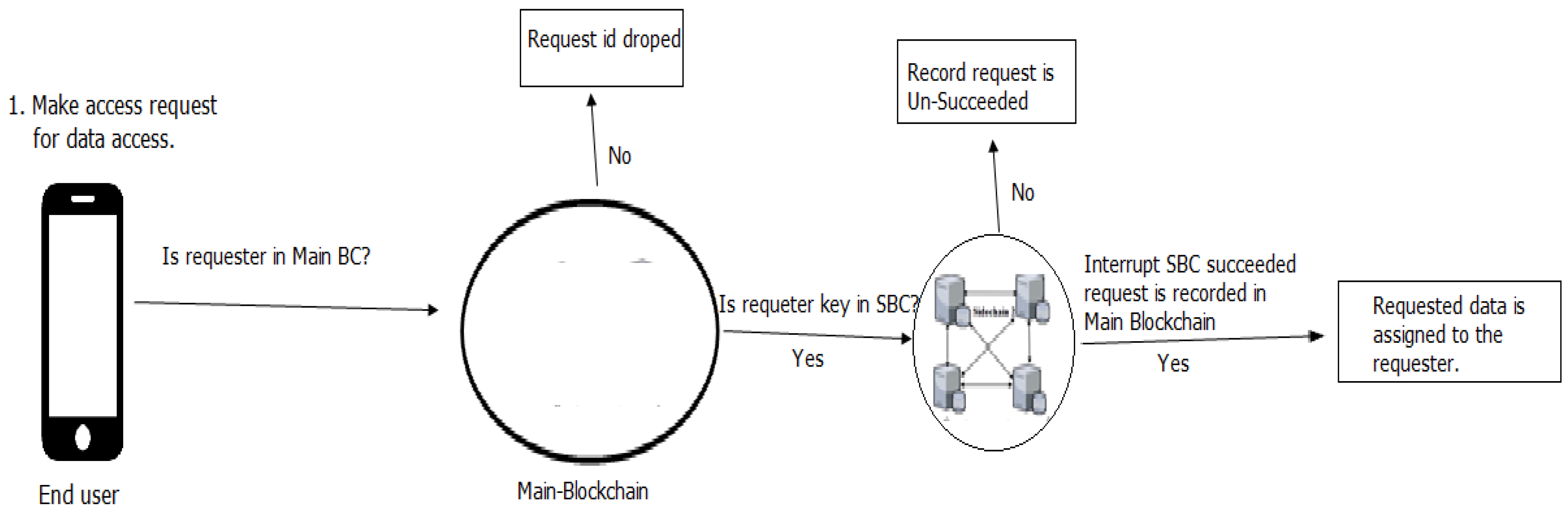
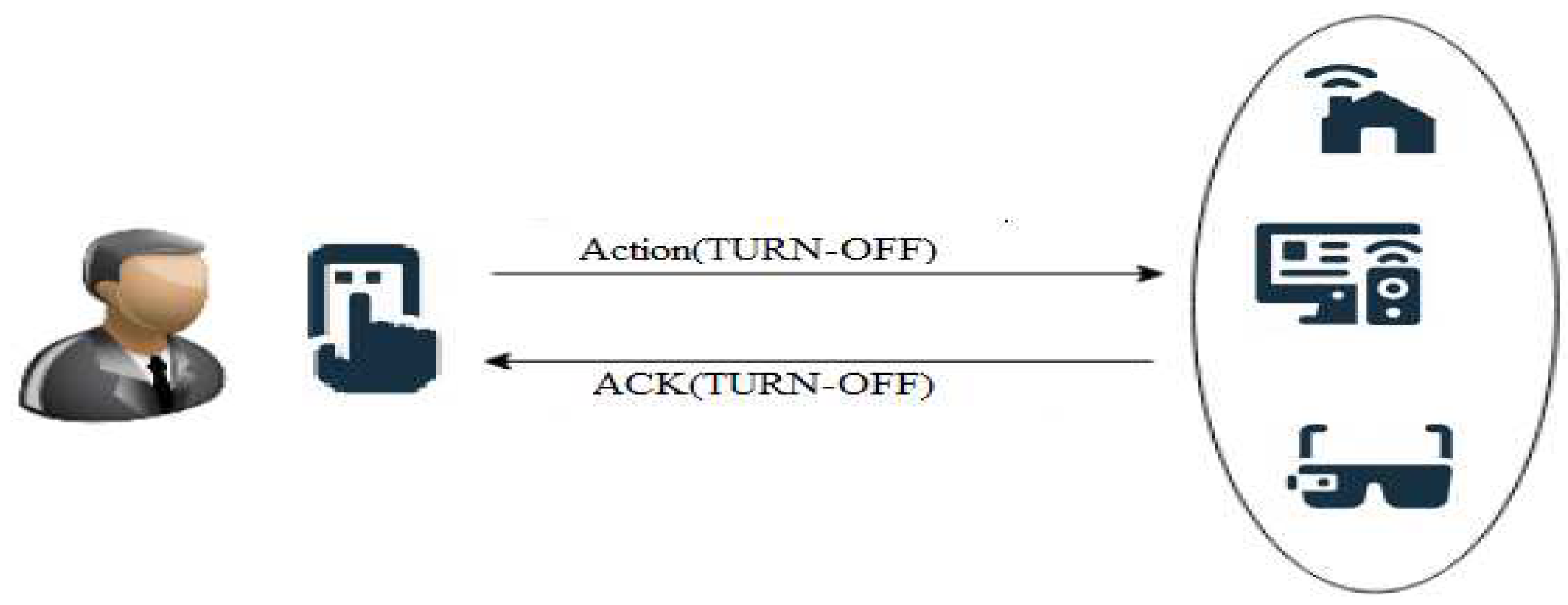
B. Traceability in the proposed system
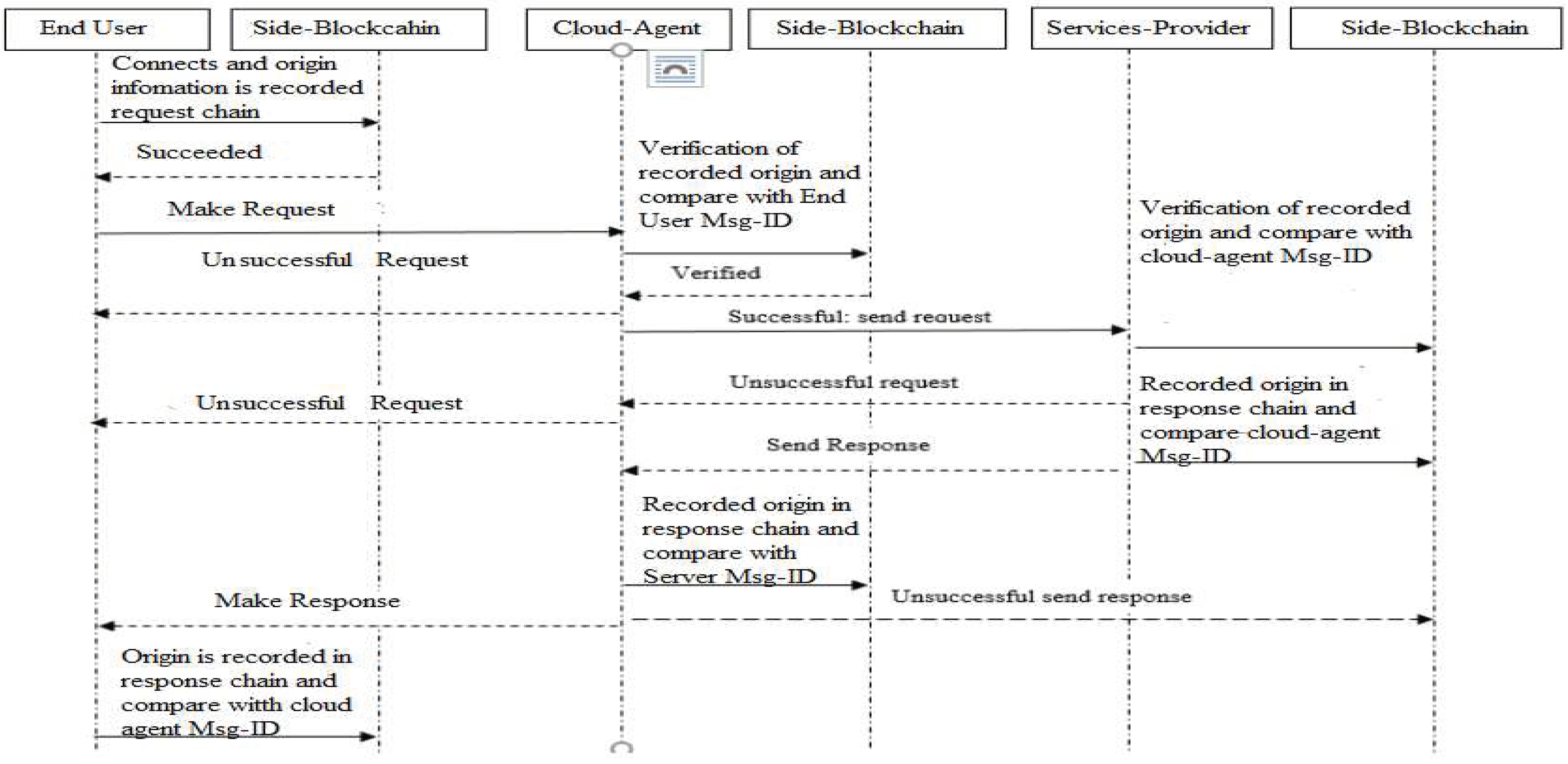
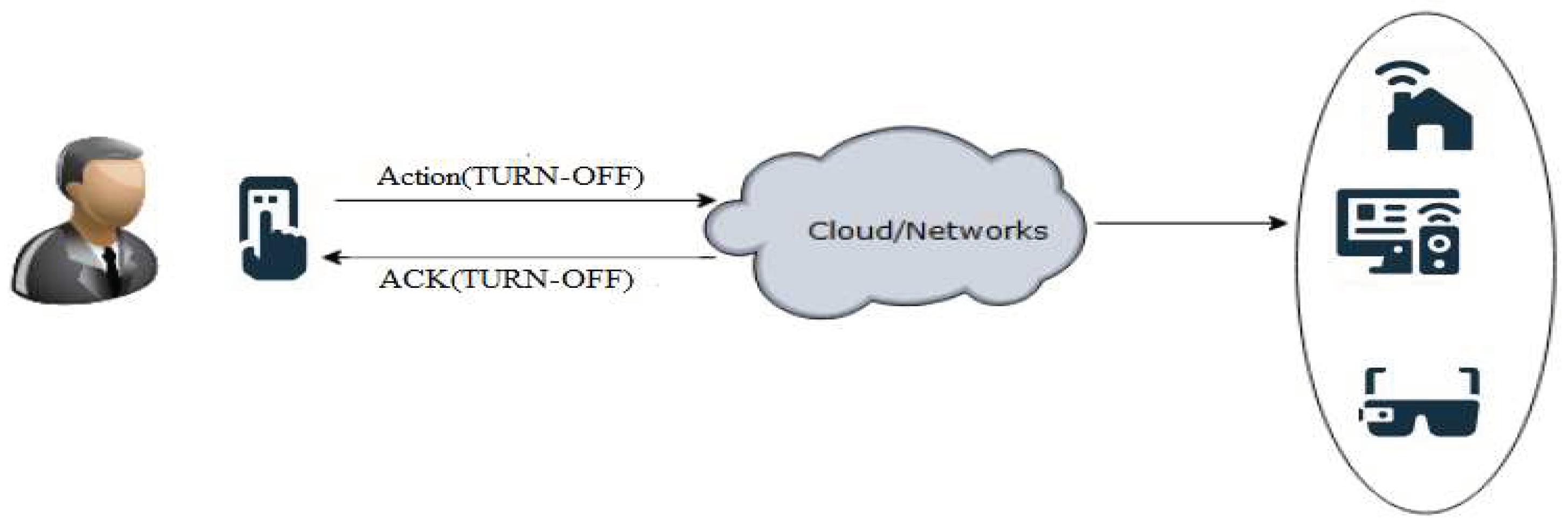
C. Accountability of Making Requests
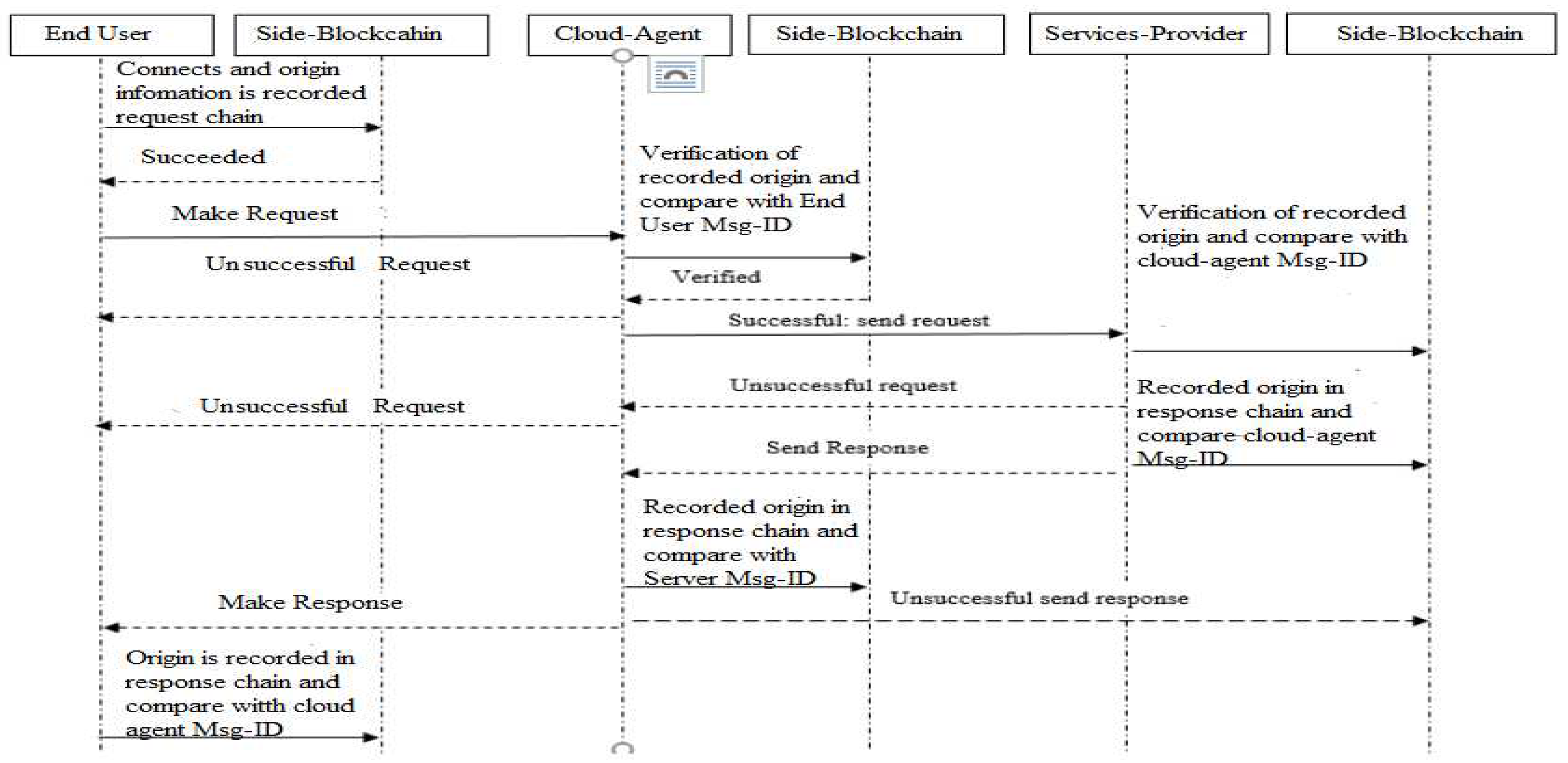
IV. IMPLEMENTATION AND RESULTS
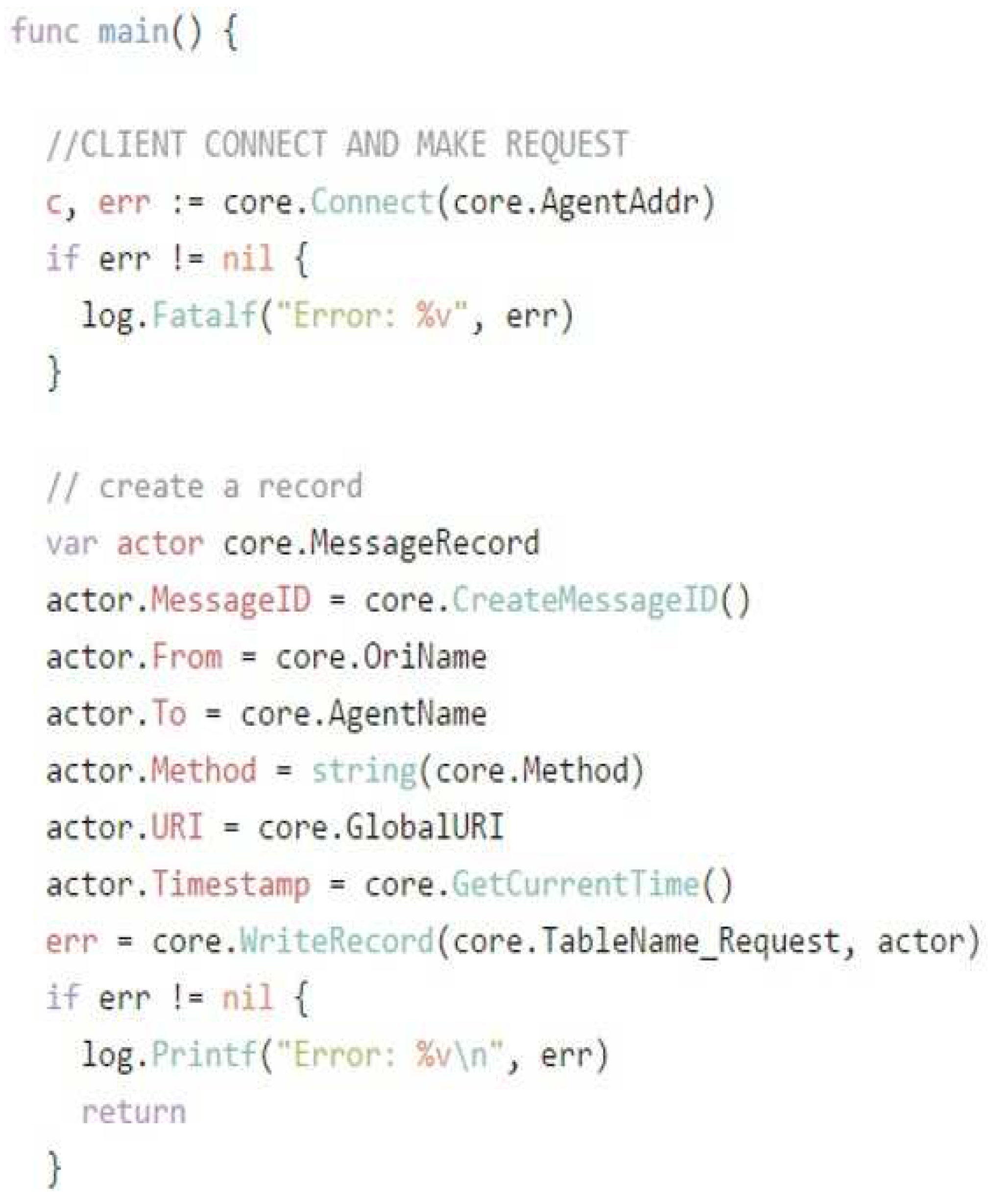
- 1)
- End-User Side
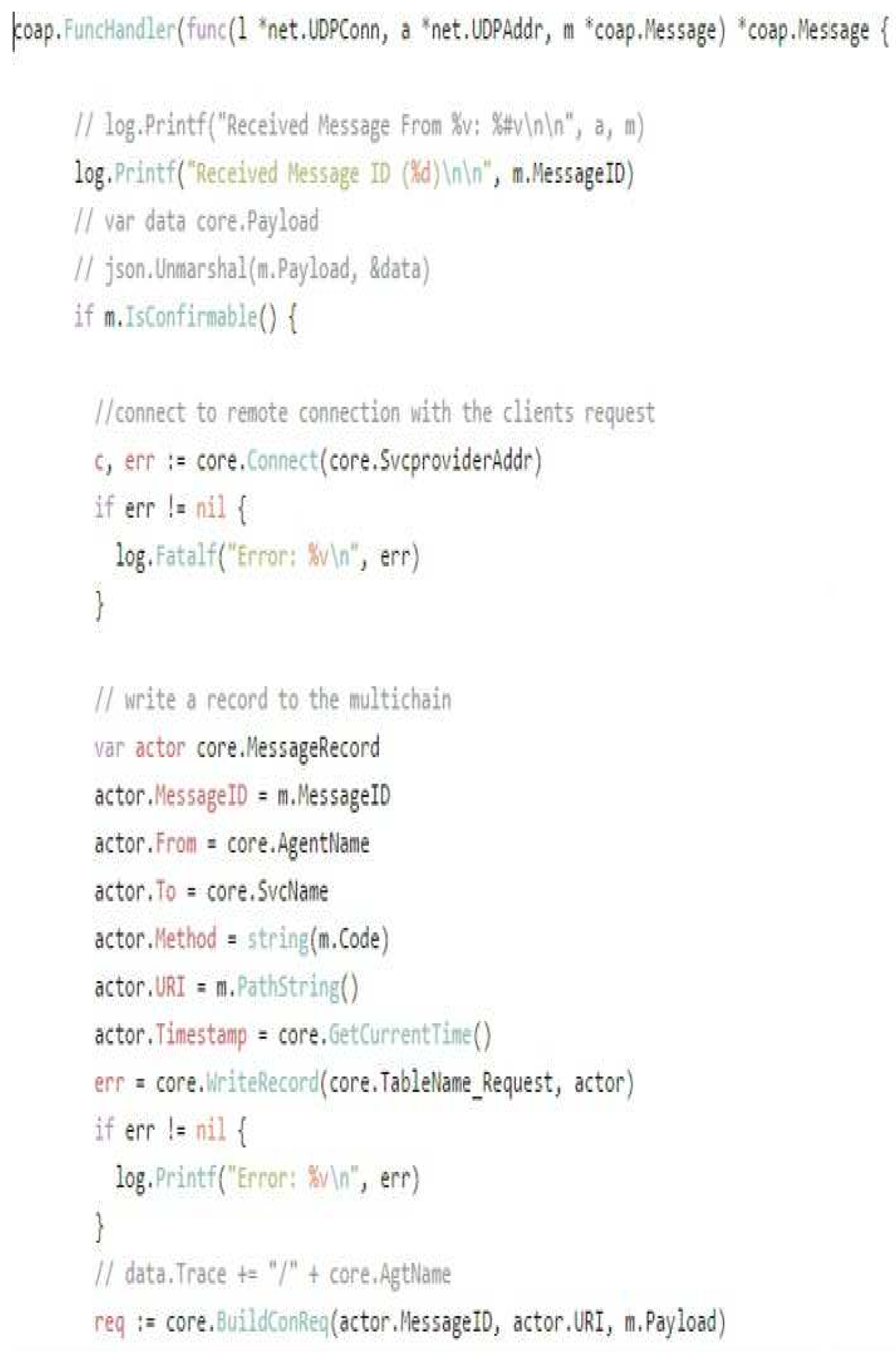
- 2)
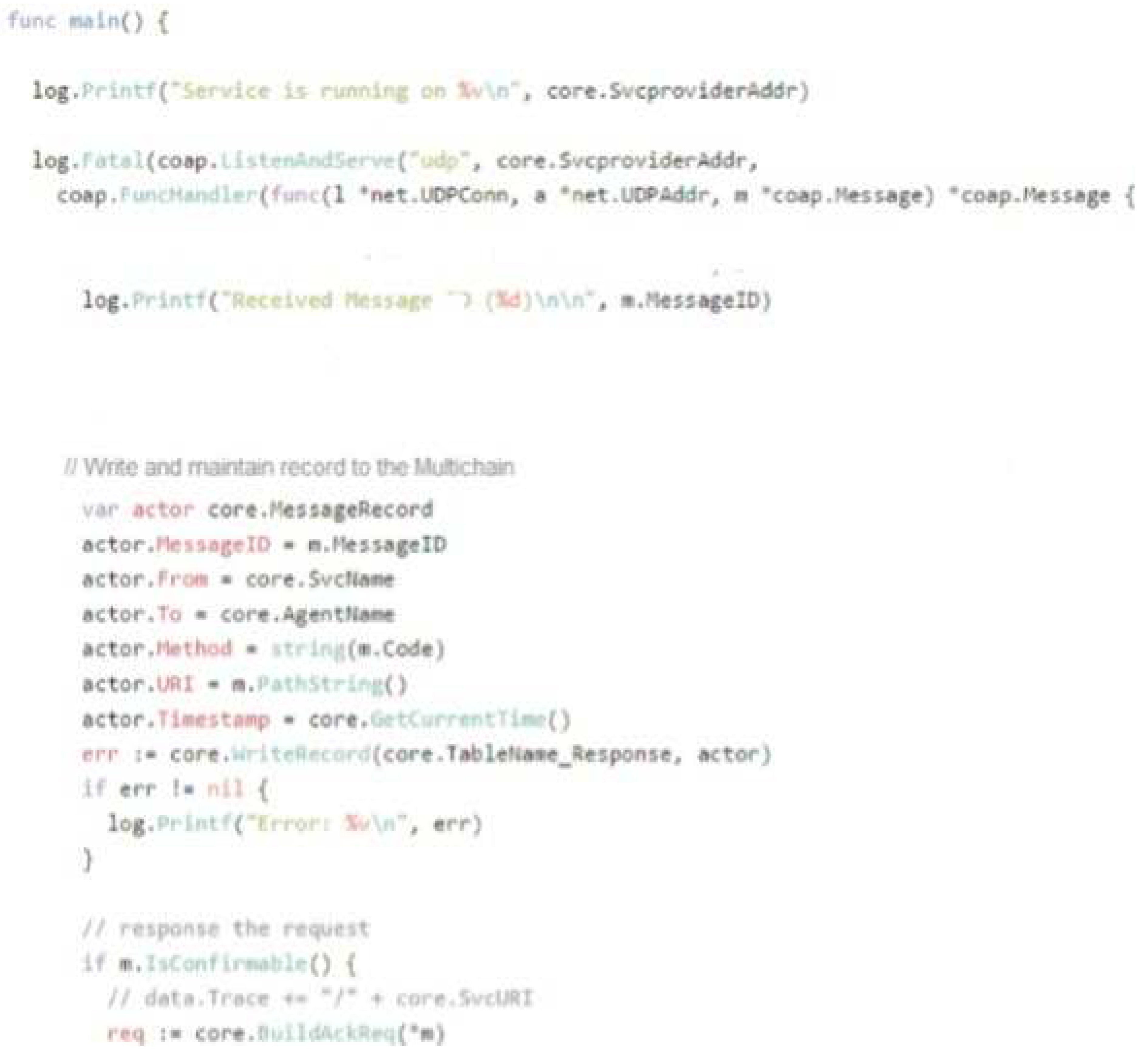
- Cloud-Agent Side
- 3)
- Server-side coding
- ✓
- Local Environment Components
- ✓
- Raspberry1pi-2:Cloud-Agent
- ✓
- The workstation of Lenovo for server
- ✓
- Workstation for Blockchain Nodes
- ✓
- Cloud
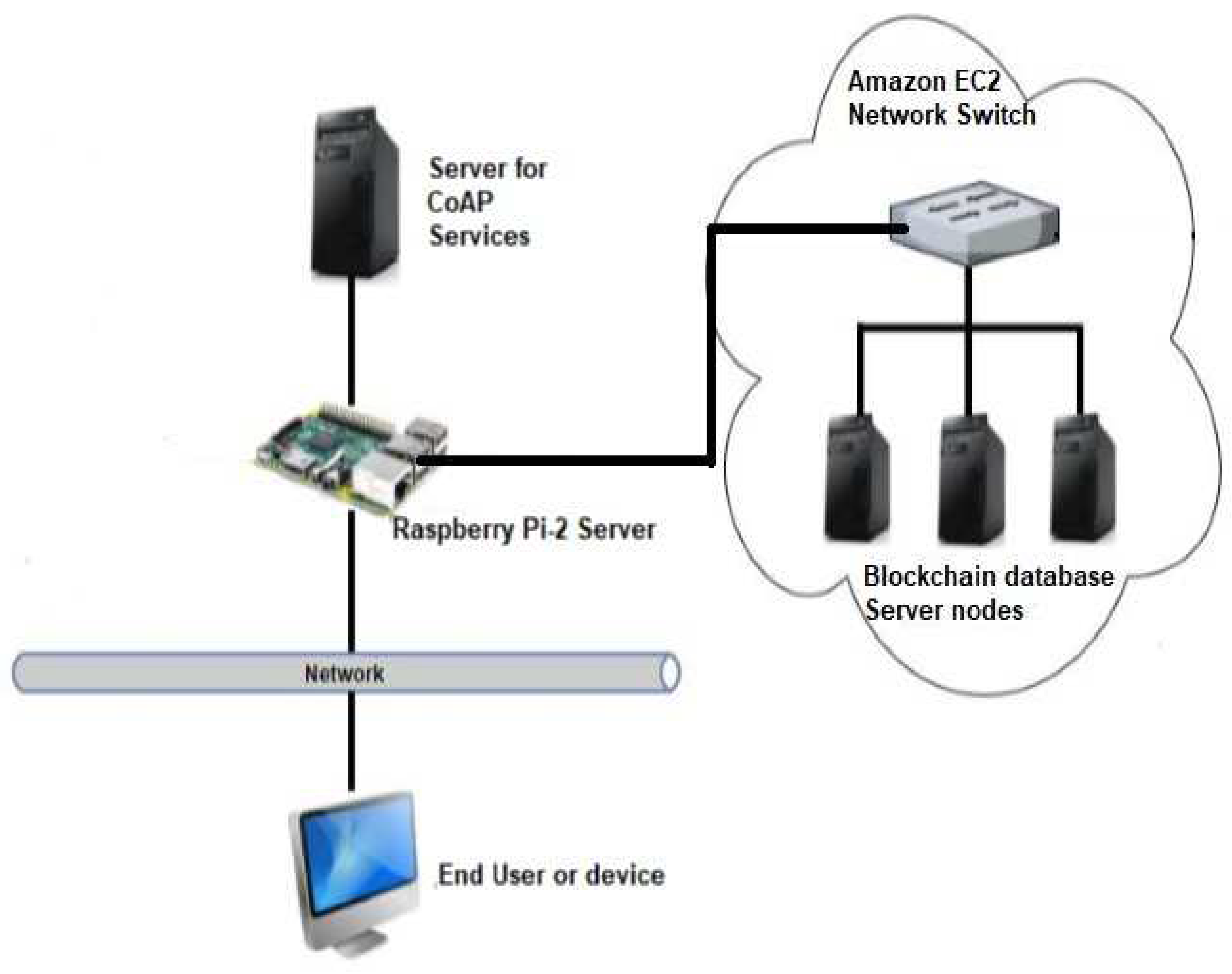
B. Physical Structure
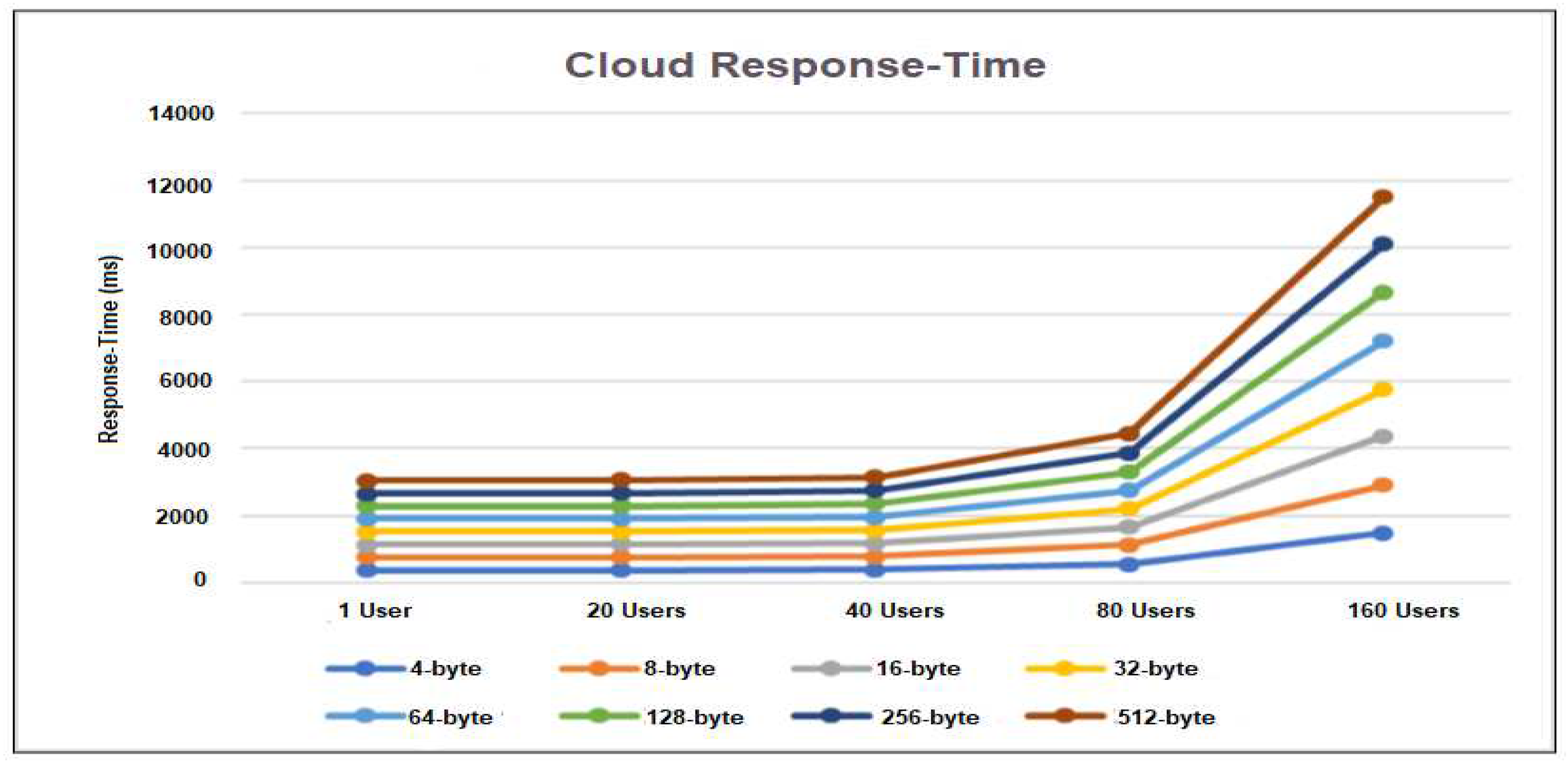
C. Data collection
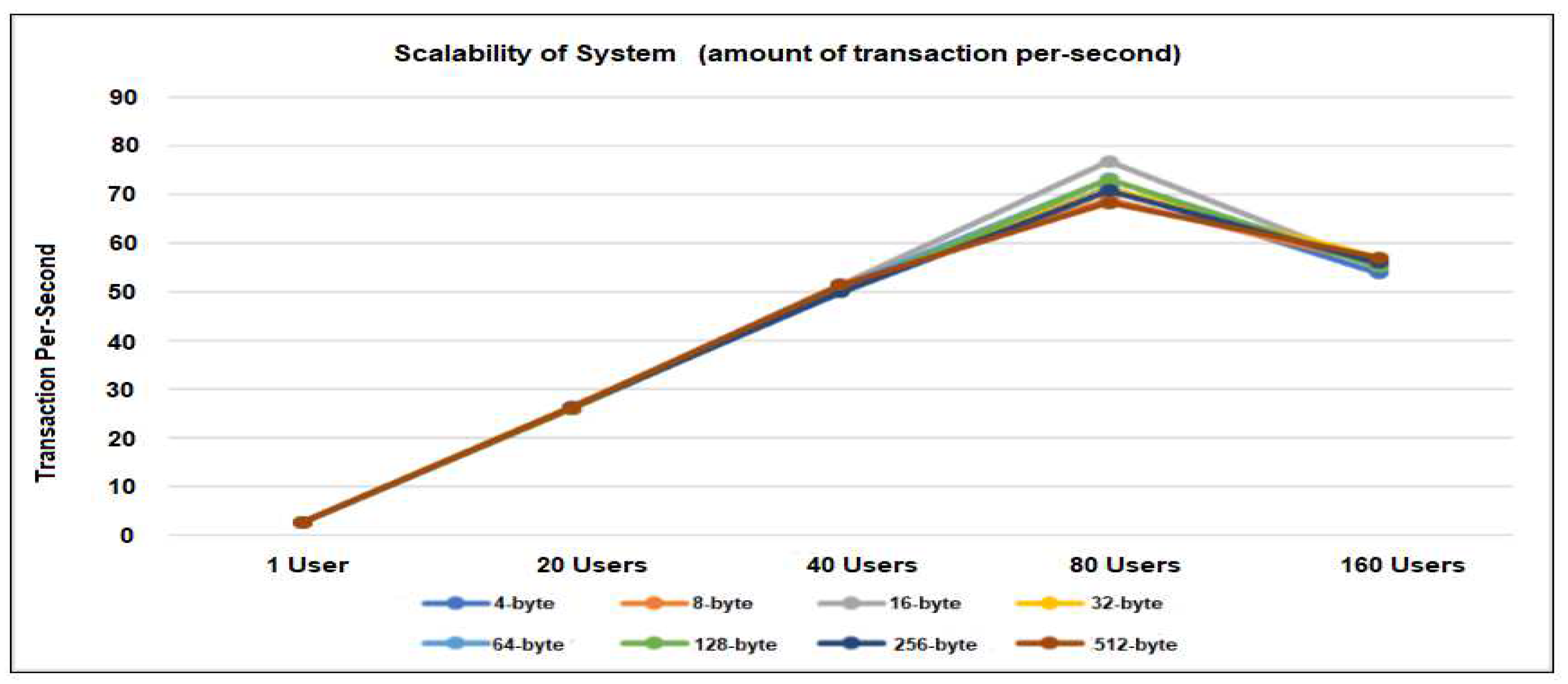
D. Performance Metrics
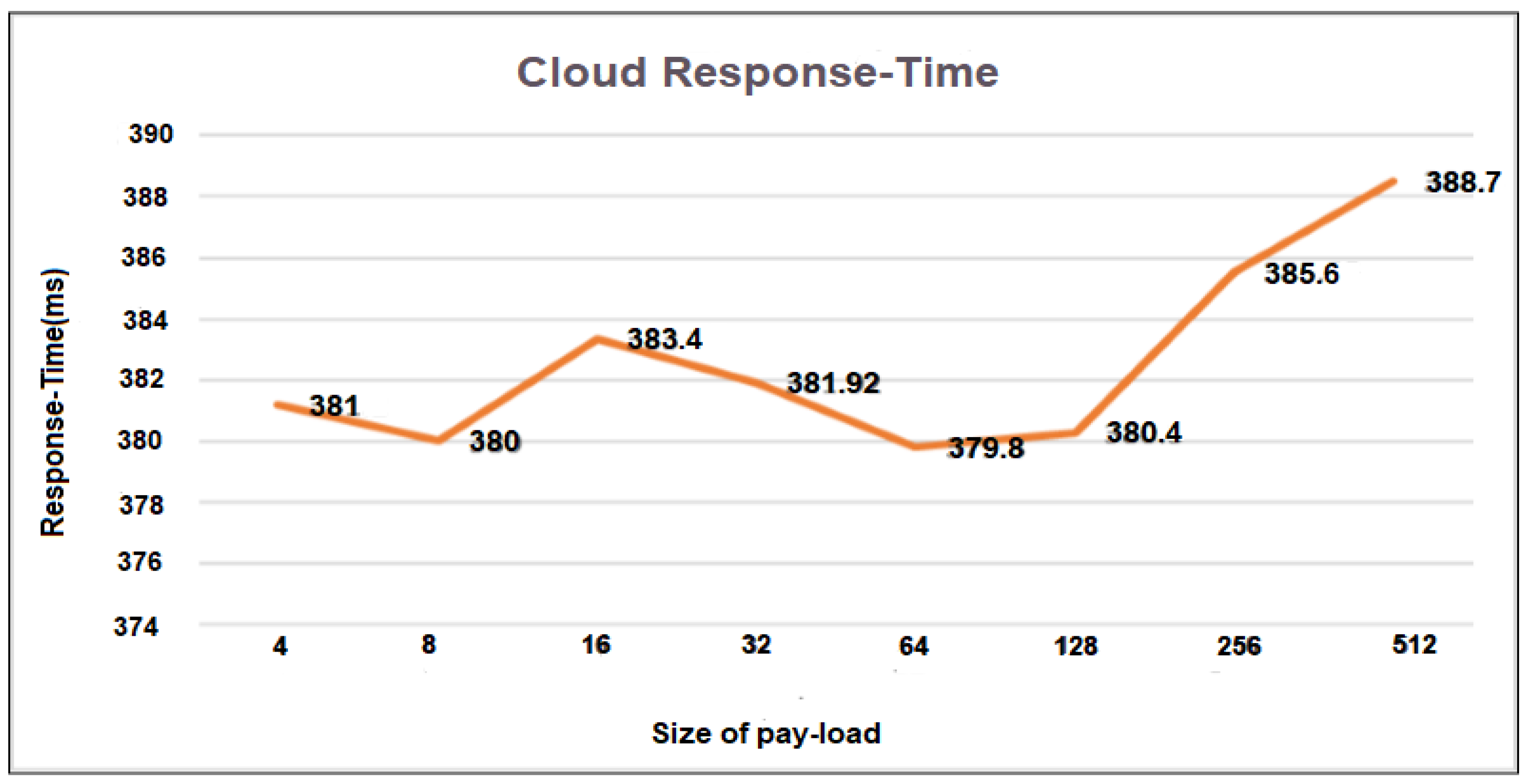
E. Performance Evaluation
Future Works
References
- Abid sultan et al,” IoT Security Issues Via Blockchain: A Review Paper”, ICBCT 2019, March 15–18, 2019, Honolulu, HI, USA © 2019 Association for Computing Machinery. ACM ISBN 978-1-4503-6268-9/19/03…$15. [CrossRef]
- Sultan A (2018) Internet of Things Security Issues and Their Solutions With Blockchain Technology Characteristics: A Systematic Literature Review. Am J Compt Sci Inform Technol Vol.6 No.3:27.
- Franklin Okeke, “The top 5 industrial IoT use cases:https://www.techrepublic.com/article/industrial-iot-use-cases/in Internet of Things on November 8, 2022.
- F. Hussain, R. Hussain, S. A. Hassan and E. Hossain, (8, April 2020)"Machine Learning in IoT Security: Current Solutions and Future Challenges," in IEEE Communications Surveys & Tutorials. [CrossRef]
- M.A. Khan, K. Salah, “IoT security: Review, blockchain solutions, and open challenges”, Future Generation Computersystems(2017). [CrossRef]
- Dapeng Wu, Shushan Si, Shaoen Wu, Senior Member, IEEE, and Ruyan Wang” Dynamic Trust Relationships Aware Data Privacy Protection in Mobile Crowd-Sensing”, IEEE Internet of Things Journal, I OT.2017.
- M. Yevdokymenko, "An adaptive algorithm for detecting and preventing attacks in telecommunication networks," 2016 Third International Scientific-Practical Conference Problems of Info communications Science and Technology (PIC S&T), Kharkiv, 2016, pp. 175-177.
- G. Kalnoor and J. Agarkhed, "Pattern matching intrusion detection technique for Wireless Sensor Networks," 2016 2nd International Conference on Advances in Electrical, Electronics, Information, Communication kand Bio-Informatics (AEEICB), Chennai, 2016, pp. 724-728.
- F. Abazari, A. Madani and H. Gharaee (2016), "Optimal response to computer network threats," 2016 8th International Symposium on Telecommunications (IST), Tehran, pp. 729-734.
- M.S. Ali, K. Dolui and F. Antonelli (2017), “IoT data privacy via blockchains and IPFS”, International Conference on the Internet of Things (ACM, New York).
- NEST, “Nest Thermostat,”. [Online]. Available: https://nest.com/uk/thermostat/meet-nest-thermostat/. [Accessed: 18-Apr-2017].
- F. Wang et al (2015), “A survey from the perspective of evolutionary process in the internet of things,” Int. J. Distrib. Sens. Networks, vol. 2015.
- M. Banerjee, J. Lee, K.-K.R. Choo,“A blockchain future to Internet of Things security: A position paper”, Digital Communications and Networks (2017). [CrossRef]
- E. Kaku, R. K. Lomotey, and R. Deters, “Using Provenance and CoAP to track Requests/Responses in IoT,” in Procedia Computer Science, 2016, vol. 94.
- Ali Dorri et al (December 2017), “BlockChain: A Distributed Solution to Automotive Security and Privacy”, IEEE Communications Magazine.
- K. Rose, S. Eldridge, and C. Lyman (October 2015), “the internet of things: an overview”.
- W. Stewart (2000), “the Internet Toaster.’ Living Internet,” web. [Online]. Available: http://www.livinginternet.com/i/ia_myths_toast.html.
- Gartner (20-oct-2021) “Reveals Top Predictions for IT Organizations and Users and Beyond,” Gartner.
- IDC FutureScape: Worldwide Internet of Things 2017 Predictions.
- D. Locke, “MQ telemetry transport (mqtt) v3. 1 protocol specification, IBM developerWorks Technical Library,” Ibm, 2010.
- S. Xue, R. K. Lomotey, and R. Deters, “Enabling Sensor Data Exchanges in Unstable Mobile Architectures,” Proc. - 2015 IEEE 3rd Int. Conf. Mob. Serv. MS 2015, pp. 391–398, 2015.
- Z. Shelby, K. Hartke, and C. Bormann, “The Constrained Application Protocol (CoAP),” Rfc 7252, p. 112, 2014.
- R. T. Fielding, “Architectural Styles and the Design of Network-based Software Architectures,” Building, vol. 54, p. 162, 2000.
- L. Richardson and S. Ruby, RESTful Web Services. 2008.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




