Submitted:
27 December 2025
Posted:
29 December 2025
You are already at the latest version
Abstract
Keywords:
I. Introduction
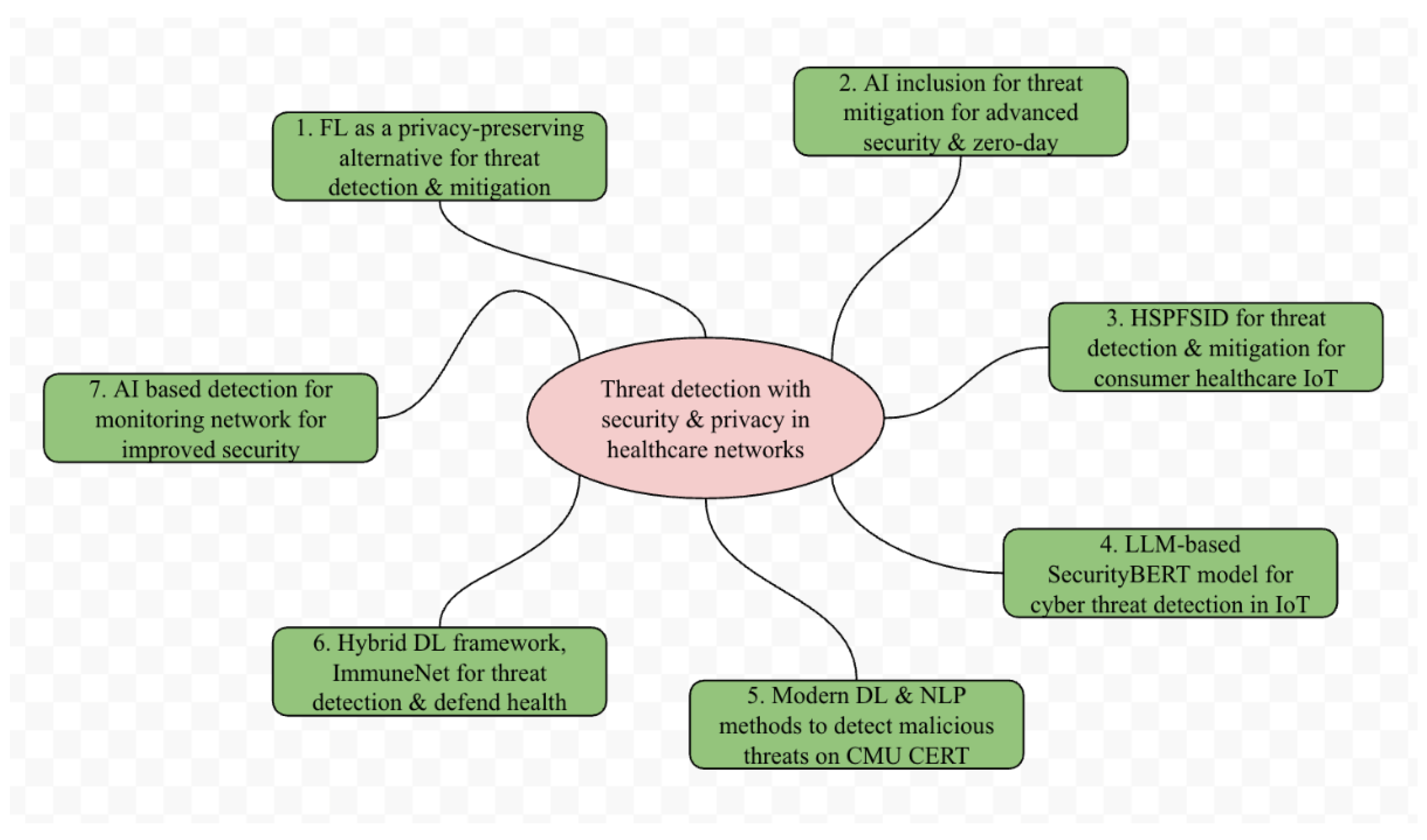
II. Related Works
III. Dataset and Methodology
A. Dataset
B. Methodology
IV. safeMEDInet Framework
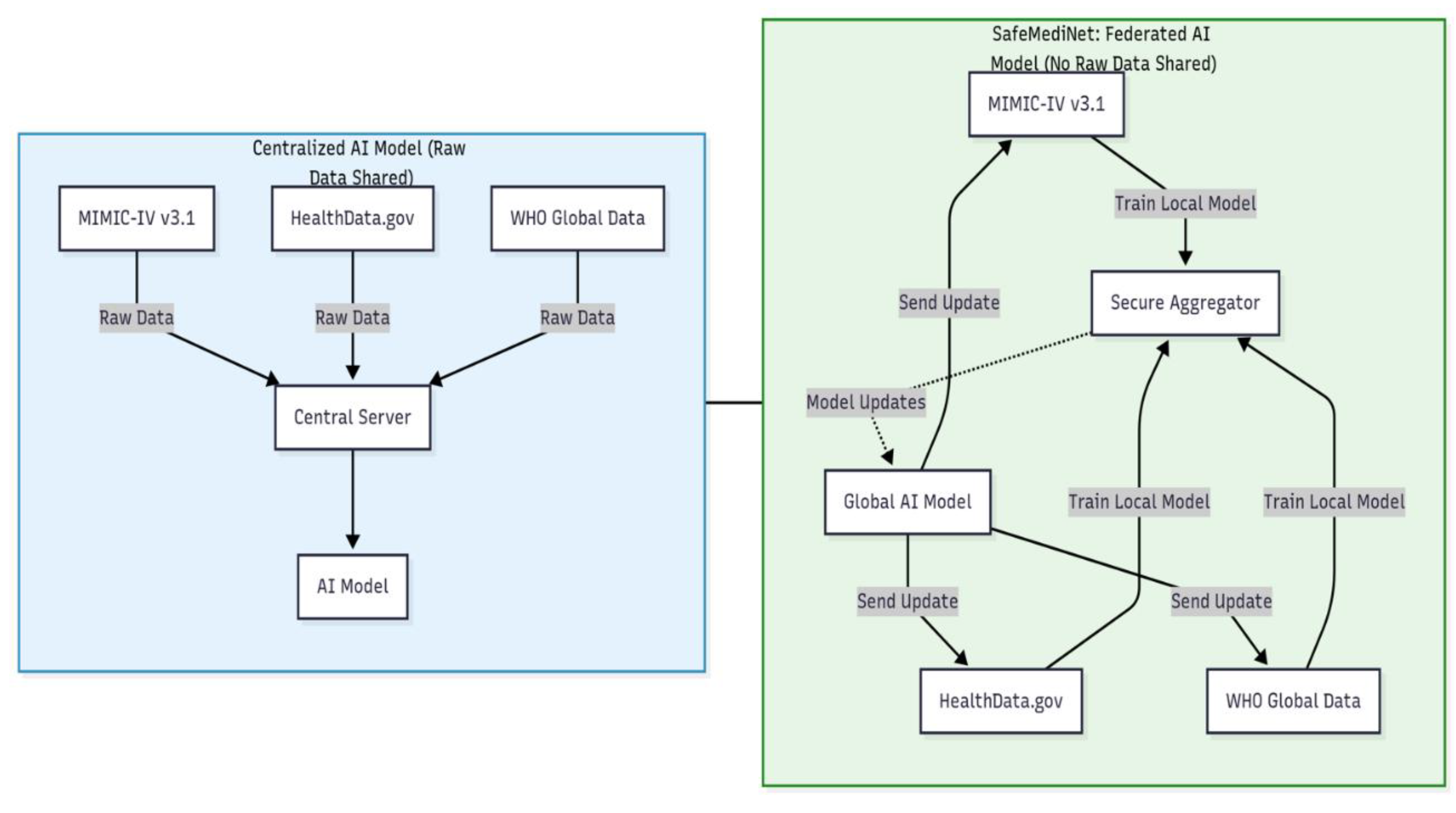
A. Overview of System Architecture
B. Localized Threat Detection Module
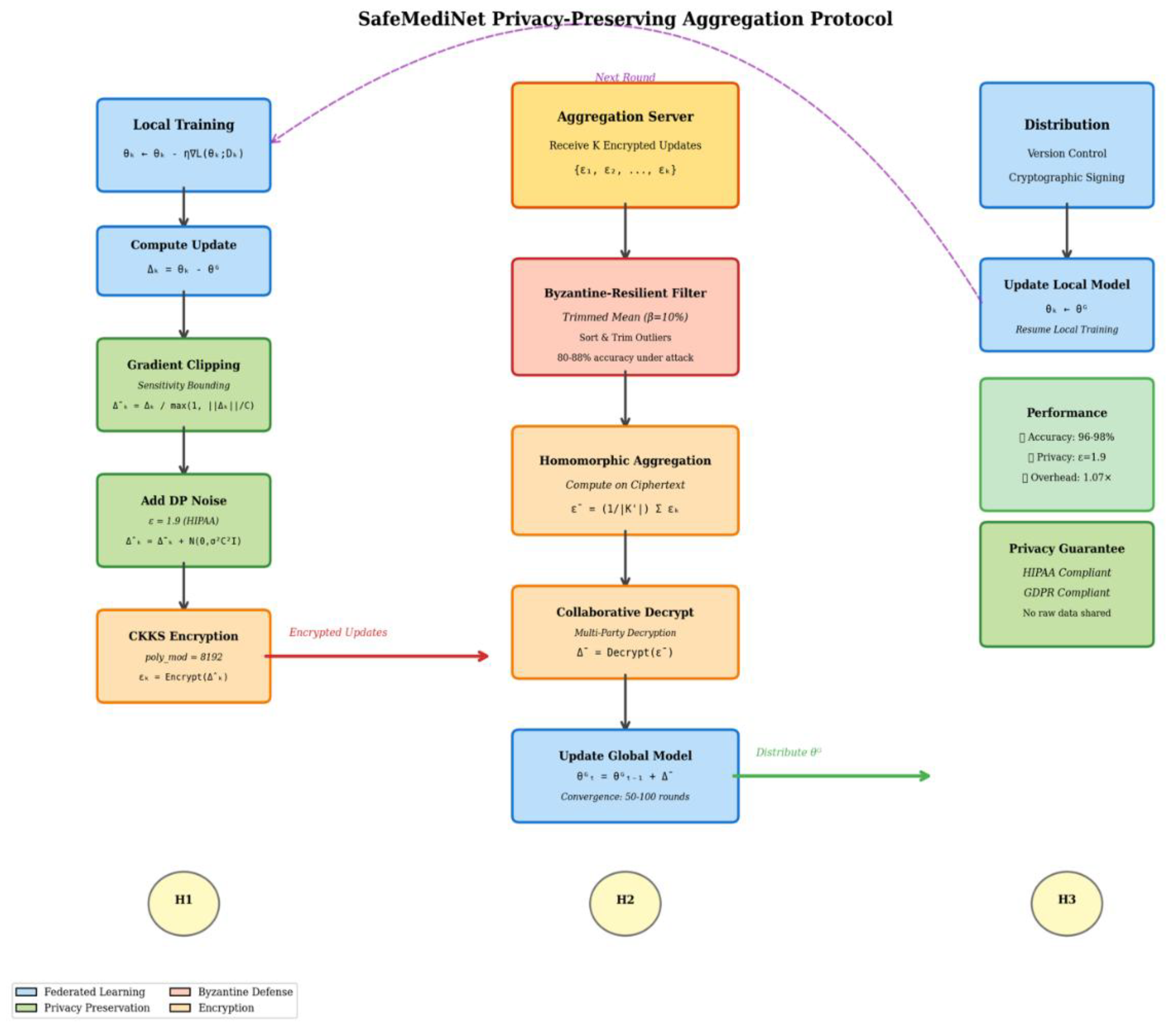
C. Protocol for Privacy-Preserving Aggregation
| Algorithm 1: Privacy-Preserving Federated Learning with Byzantine Resilience |
| Input: K institutions, T rounds, learning rate η, clipping threshold C, privacy budget ε, noise multiplier σ, trimming proportion β Output: Global threat detection model θ^G Initialize θ^G_0 for t = 1 to T do // outer for start Server broadcasts θ^G_{t-1} to all institutions // Local training and privacy preservation for each institution k in parallel do θ^k_t ← LocalTrain(θ^G_{t-1}, D_k, η) Δ^k_t ← θ^k_t - θ^G_{t-1} Δ̃^k_t ← Δ^k_t / max(1, ||Δ^k_t||_2/C) // Gradient clipping Δ̂^k_t ← Δ̃^k_t + N(0, σ²C²I) // Add DP noise ε^k_t ← Encrypt_CKKS(Δ̂^k_t) // CKKS encryption Send ε^k_t to server end for // Server-side Byzantine-resilient aggregation for each dimension d do sorted_d ← SecureSort({ε^1_t[d], ..., ε^K_t[d]}) trimmed_d ← sorted_d[⌊βK⌋+1 : K-⌊βK⌋] // Trim outliers agg_d ← (1/|trimmed_d|) · ∑(trimmed_d) // Trimmed mean end for Δ̄_t ← CollaborativeDecrypt(agg) θ^G_t ← θ^G_{t-1} + Δ̄_t // Global update if PrivacyBudgetExhausted(ε, σ) then break end for // outer for end return θ^G_T |
D. Byzantine-Resilient Aggregation Methods
E. Global Model Revision and Dissemination
F. Comprehensive Threat Detection Pipeline
V. Security and Privacy for Threat Detection
VI. Results and Discussion
A. Evaluation of Threat Detection Efficacy, Privacy Assessment
B. Byzantine Resilience and Computational Efficacy
C. Comparative Analysis and Discussion
VII. Challenges and Future Directions
VIII. Conclusion
References
- G. Suciu et al., “Cyber-physical Threat Detection Platform Designed for Healthcare Systems” Annals of Disaster Risk Sciences, Nov. 2020.
- P. Radoglou-Grammatikis et al., “Modelling, Detecting and Mitigating Threats against Industrial Healthcare Systems: a Combined SDN and Reinforcement Learning Approach,” IEEE Trans on Ind. Inf, Mar. 2022.
- R. Latif, H. Abbas, S. Latif, and A. Masood, “Distributed Denial of Service Attack Source Detection Using Efficient Traceback Technique (ETT) in Cloud-Assisted Healthcare Environment,” Journal of Medical Systems, May 2016.
- G. Kaur and P. Gupta, “Detection of Distributed Denial of Service Attacks for IoT-Based Healthcare Systems,” Comp Ass. Methods in Eng. Sci, Jun. 2022.
- J. Almalki, S. M. Alshahrani, and N. A. Khan, “A comprehensive secure system enabling healthcare 5.0 using federated learning, intrusion detection and blockchain,” PeerJ. Computer science, vol. 10, p. e1778, Jan. 2024.
- S. Pati et al., “Privacy preservation for federated learning in health care,” Patterns, vol. 5, no. 7, pp. 100974–100974, Jul. 2024. doi: . [CrossRef]
- M. Akshay Kumaar, D. Samiayya, P. M. D. R. Vincent, K. Srinivasan, C.-Y. Chang, and H. Ganesh, “A Hybrid Framework for Intrusion Detection in Healthcare Systems Using Deep Learning,” Frontiers in Public Health, vol. 9, Jan. 2022.
- J. P. Singh, Aqsa Aqsa, I. Ghani, Raj Sonani, and V. Govindarajan, “Privacy-Aware Hierarchical Federated Learning in Healthcare: Integrating Differential Privacy and Secure Multi-Party Computation,” Future Internet, vol. 17, no. 8, Jul. 2025.
- R. Natarajan, S. Krishna, and Christodoss Prasanna Ranjith, “A Novel Federated Learning Framework for Healthcare Applications Using Wearable Devices,” pp. 1–6, Jan. 2025, doi: . [CrossRef]
- Y. Xia, W. Yu, and Q. Li, “Byzantine-Resilient Federated Learning via Distributed Optimization,” pp. 2672–2676, Sep. 2025. [CrossRef]
- I. Sultana, S. M. Maheen, N. Kshetri, and M. N. Fardous Zim, “detectGNN: Harnessing Graph Neural Networks for Enhanced Fraud Detection in Credit Card Transactions,” 2025 13th ISDFS, Apr. 2025.
- S. M. Maheen, I. Sultana, N. Kshetri, and M. Nasim, “emoAIsec: Fortifying Real-Time Customer Experience Optimization with Emotion AI and Data Security,” 2025 ICMLAS, IEEE, Mar. 2025.
- T. Le and S. Moothedath, “Byzantine Resilient Federated Multi-Task Representation Learning,” arXiv.org, 2025.
- A. K. Tom, A. Khraisat, T. Jan, Md Whaiduzzaman, T. D. Nguyen, A. Alazab, “Survey of Federated Learning for Cyber Threat Intelligence in Industrial IoT: Techniques, Applications, Deployment Models,” Future Int, 25.
- M. S. Ali et al., “Federated Learning in Healthcare: Model Misconducts, Security, Challenges, Applications, and Future Research Directions -- A Systematic Review,” arXiv.org, May 22, 2024. https://arxiv.org/abs/2405.13832.
- K. Begum, M. A. I. Mozumder, M.-I. Joo, and H.-C. Kim, “BFLIDS: Blockchain-Driven Federated Learning for Intrusion Detection in IoMT Networks,” Sensors, vol. 24, no. 14, p. 4591, Jul. 2024, . [CrossRef]
- Mohamed Amine Ferrag et al., “Revolutionizing Cyber Threat Detection with Large Language Models: A privacy-preserving BERT-based Lightweight Model for IoT/IIoT Devices,” IEEE Access, pp. 1–1, Jan. 2024.
- H. Jeong, H. Son, S. Lee, J. Hyun, and T.-M. Chung, “FedCC: Robust Federated Learning against Model Poisoning Attacks,” arXiv 2022.
- Edi Marian Timofte et al., “Federated Learning for Cybersecurity: A Privacy-Preserving Approach,” Applied Sciences, Jun. 2025.
- Kavitha, D., & Thejas, S. “AI enabled threat detection: Leveraging artificial intelligence for advanced security and cyber threat mitigation”. IEEE Access. 2024, 12, 173127-173136.
- Rajesh, R., & Hemalatha, S. (2024). “Threat detection and mitigation for tactile internet driven consumer IoT-healthcare system”. IEEE Transactions on Consumer Electronics. 70(1), 4249-4257.
- S. A. Alzakari, A. Sarkar, M. Z. Khan, and Amel Ali Alhussan, “Converging Technologies for Health Prediction and Intrusion Detection in Internet of Healthcare Things With Matrix- Valued Neural Coordinated Federated Intelligence,” IEEE Access, 2024.
- Nallapareddy, V. S. S. R., & Katta, S. K. R. , “AI-Enhanced Cyber Security Proactive Threat Detection and Response Systems”. In 2025 ICSADL IEEE.
- Kshetri, N., Hutson, J., & Revathy, G. (2023, December). healthAIChain: Improving security and safety using Blockchain Technology applications in AI-based healthcare systems. In 2023 3rd International Conference on Innovative Mechanisms for Industry Applications (ICIMIA) (pp. 159-164). IEEE.
- Kshetri, N., Mishra, R., Rahman, M. M., & Steigner, T. (2024, April). HNMblock: Blockchain technology powered Healthcare Network Model for epidemiological monitoring, medical systems security, and wellness. In 2024 12th International Symposium on Digital Forensics and Security (ISDFS) (pp. 01-08). IEEE.
- O. F. Osama, N. Kshetri, M. M. Rahman and B. P. Pokharel, "healthMLsec: Machine Learning based Vulnerability Assessment in Health Systems: A Framework for Enhancing Cybersecurity and Patient Data," 2025 1st International Conference on Secure IoT, Assured and Trusted Computing (SATC), Dayton, OH, USA, 2025.
- A. Johnson et al., “MIMIC-IV,” Physionet.org, Oct. 11, 2024. https://physionet.org/content/mimiciv/3.1/.
- HealthData.gov, “HealthData.gov,” 2019. https://healthdata.gov/.
- WHO, “World Health Data Platform - WHO,” www.who.int, 2023.
- Pokharel, B. P., Kshetri, N., Sharma, S. R., & Paudel, S. (2025). blockHealthSecure: Integrating Blockchain and Cybersecurity in Post-Pandemic Healthcare Systems. Information, 16(2), 133.
- Sunna, A. A., Sultana, T., Kshetri, N., & Uddin, M. M. (2025, April). AssessCICA: Assessing and Mitigating Financial Losses from Cyber Attacks with Role of Cyber Insurance in Post-Pandemic Era. In 2025 13th International Symposium on Digital Forensics and Security (ISDFS) (pp. 1-6). IEEE.
- A. A. Hady, A. Ghubaish, T. Salman, D. Unal, and R. Jain, “Intrusion Detection System for Healthcare Systems Using Medical and Network Data: A Comparison Study”, IEEE Access, 2020.
| System | Accuracy | Precision | Recall | F1-Score | Privacy | Byzantine Defense |
| Centralized ML | 98.1% | 97.8% | 98.3% | 98.0% | None | No |
| Standard FedAvg | 94.2% | 93.5% | 94.8% | 94.1% | Low | No (45% under attack) |
| safeMEDInet | 96.8% | 96.4% | 97.1% | 96.7% | High (ε=1.9) | Yes (88% under attack) |
| Byzantine Ratio | safeMEDInet | Standard FedAvg | Accuracy Retention |
| 0% (No Attack) | 96.8% | 96.3% | Baseline |
| 30% | 88.4% | 52.3% | 91.3% vs 54.3% |
| 50% | 75.3% | 45.2% | 77.8% vs 46.9% |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




