Submitted:
24 June 2025
Posted:
25 June 2025
You are already at the latest version
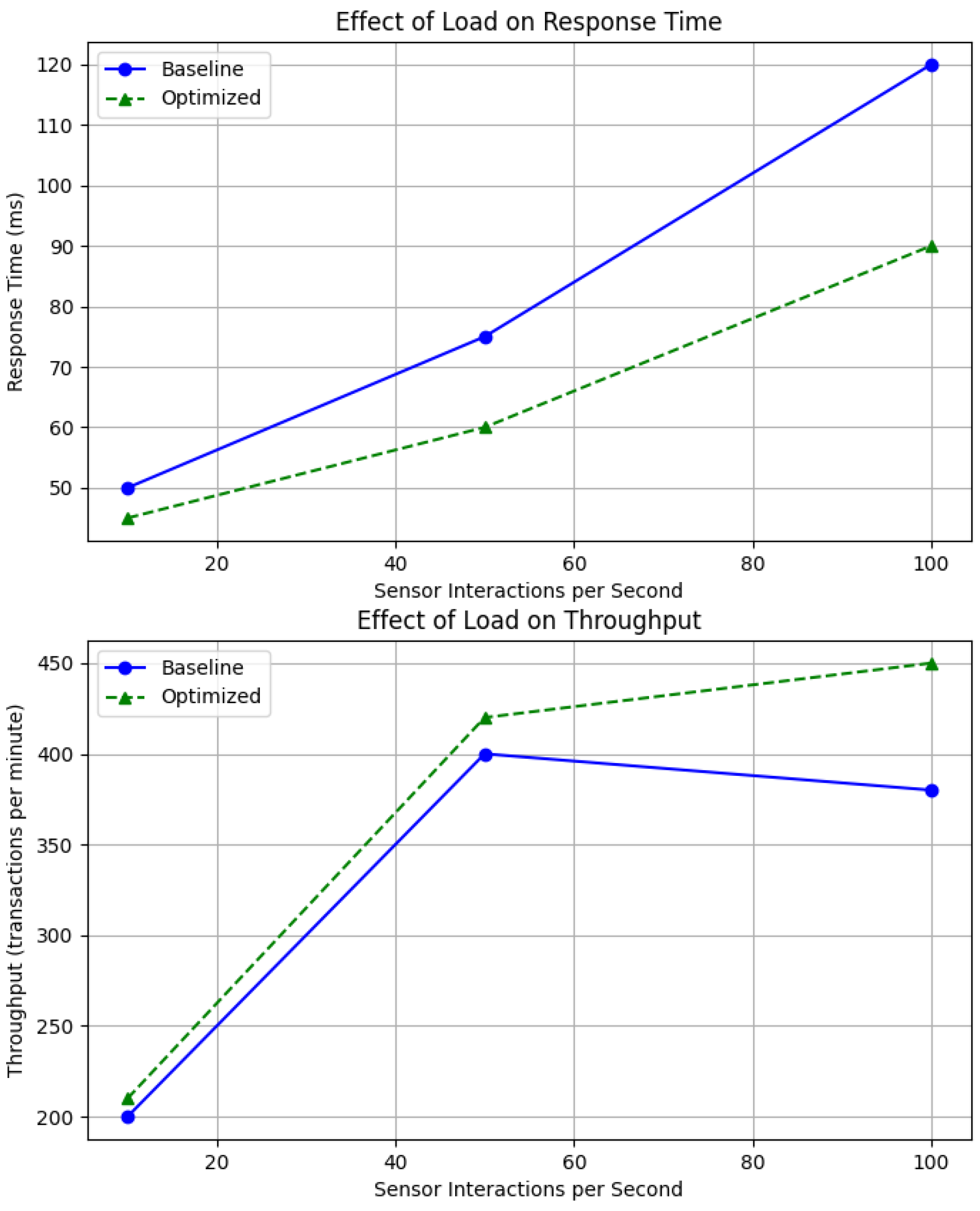
Abstract
Keywords:
1. Introduction
2. Methods
3. Convergence Models within Cloud-IoT Frameworks
3.1. Infrastructure as a Service (IaaS)
3.2. Platform as a Service (PaaS)
3.3. Software as a Service (SaaS)
4. Evaluating Scalability and Performance in Cloud-Integrated IoT Systems
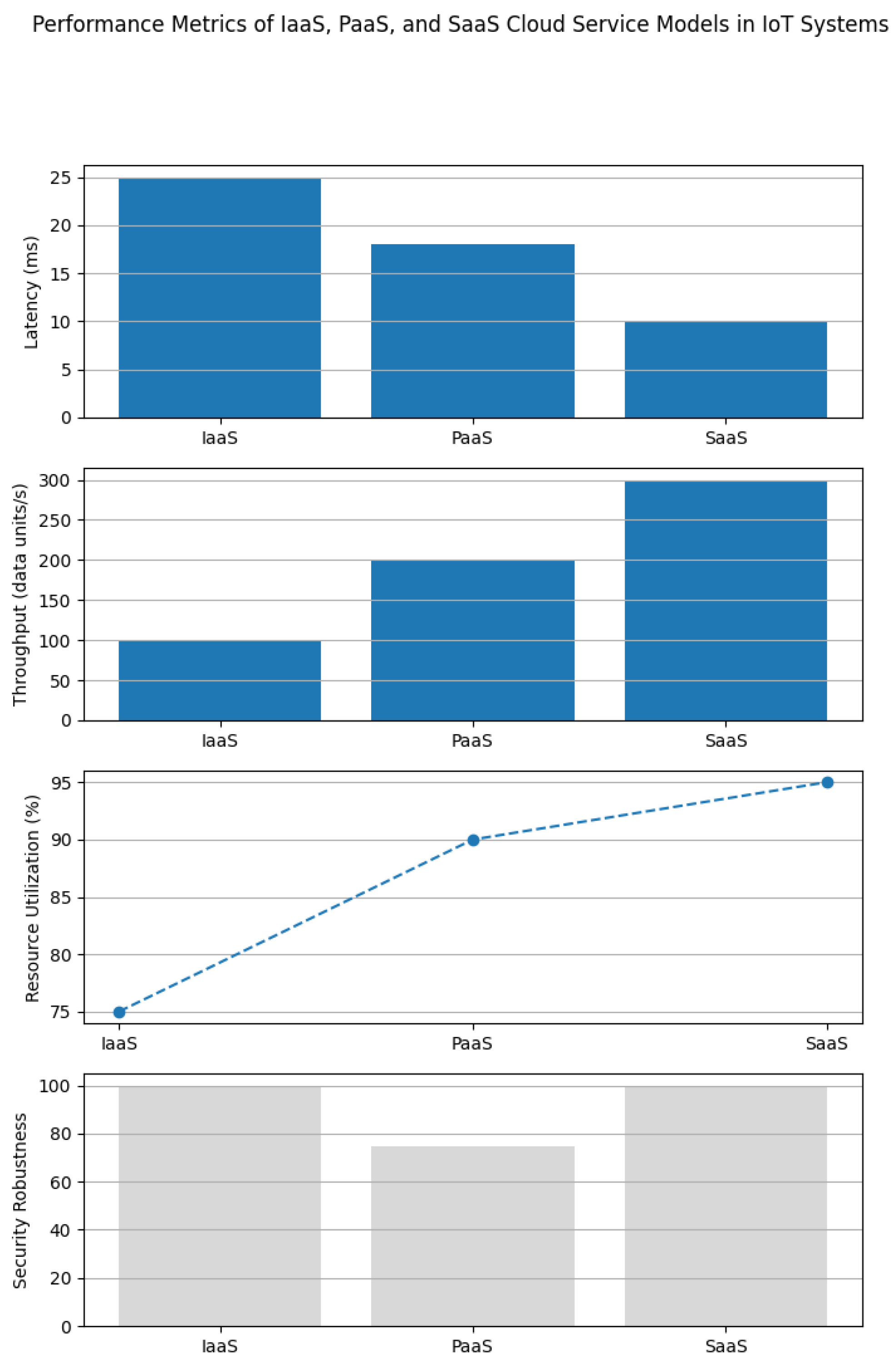
4.1. Techniques for Infrastructure Expansion
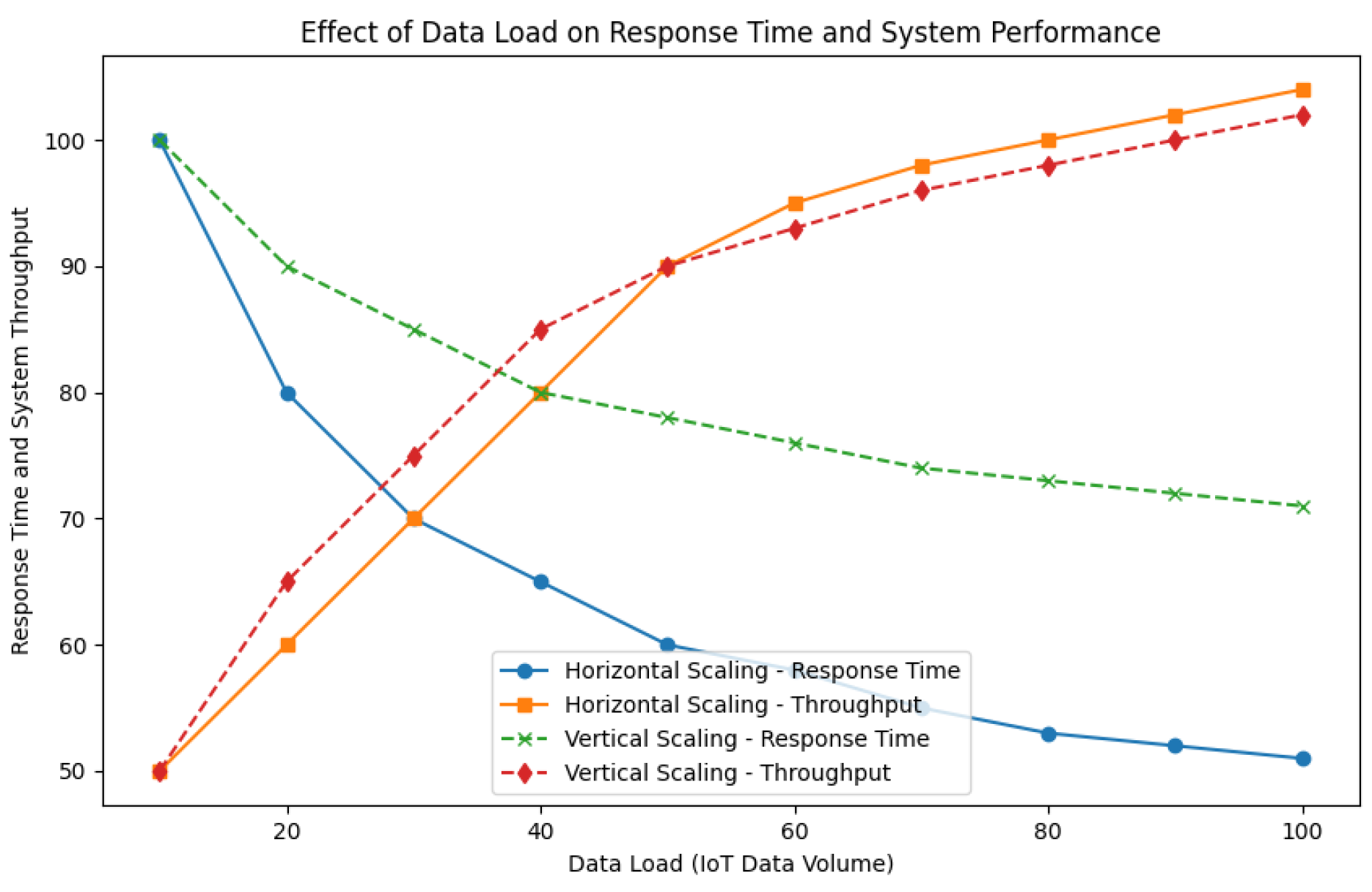
4.2. Assessment of Performance Metrics
5. Security and Privacy Considerations
5.1. Cryptography and User Authentication
5.2. Proactive Threat Detection and Response
5.3. Safeguarding Data Privacy through Engineering
6. Empirical Evaluation of Cloud Architectures in IoT Systems
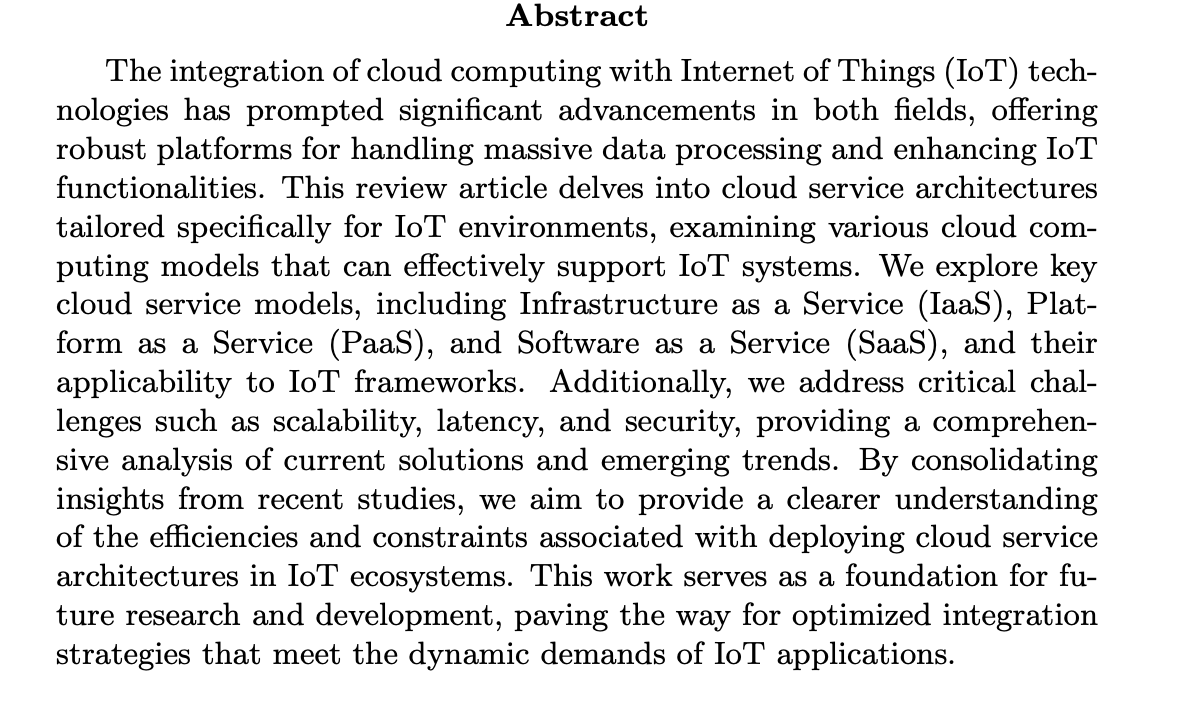
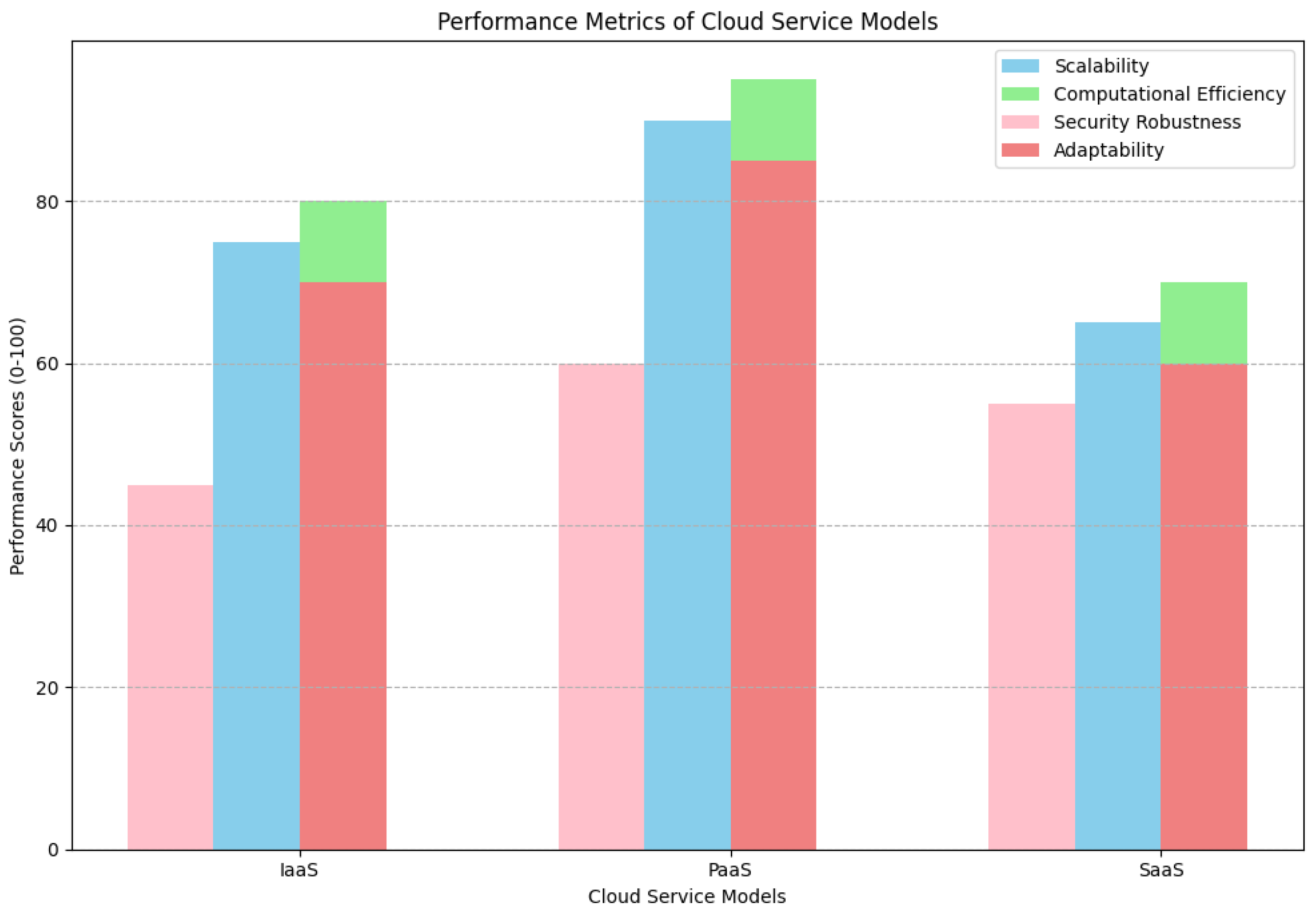
6.1. Comparative Examination of Cloud Service Models
6.2. Analysis of Algorithmic Efficiency
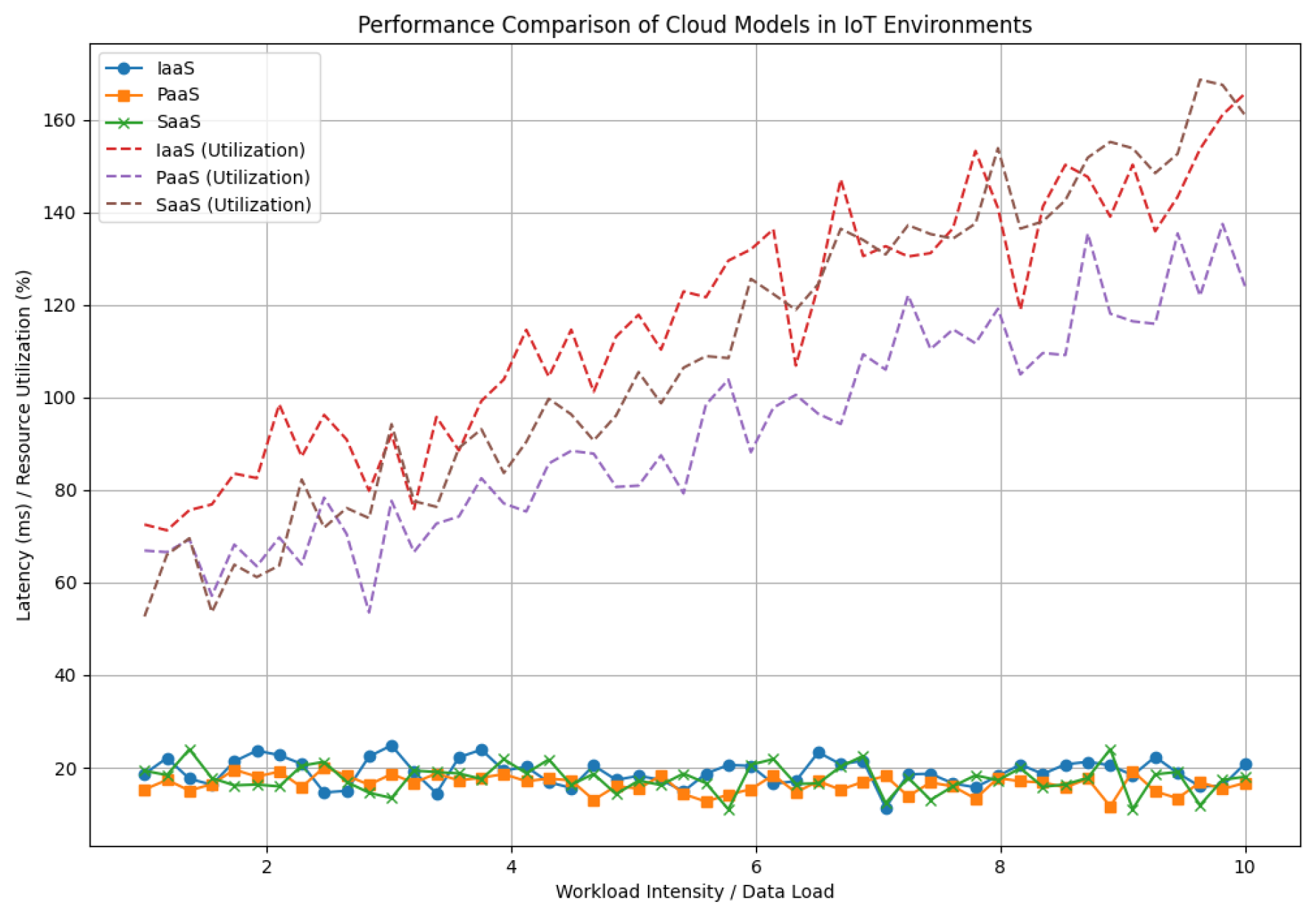
6.3. Latency and Throughput Evaluation
6.4. Resource Utilization and Scalability Analysis
6.5. Security Resilience Evaluation
6.6. Integrated Performance Synthesis
7. Discussion
7.1. Interpretation of Results
7.2. Limitations of the Study
7.3. Implications for IoT Application Development
7.4. Future Research Directions
References
- M. Armbrust, A. M. Armbrust, A. Fox, R. Griffith, A. D. Joseph, R. Katz, A. Konwinski, G. Lee, D. Patterson, A. Rabkin, I. Stoica, and M. Zaharia. A view of cloud computing. Communications of the ACM 2010, 53, 50–58. [Google Scholar]
- L. Atzori, A. L. Atzori, A. Iera, G. Morabito, and M. Nitti. The internet of things: A survey. Computer Networks 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- F. Bonomi, R. F. Bonomi, R. Milito, J. Zhu, and S. Addepalli. Fog computing and its role in the internet of things. In Proceedings of the First Edition of the MCC Workshop on Mobile Cloud Computing, pages 13–16, 2012.
- A. Botta, W. A. Botta, W. De Donato, V. Persico, and A. Pescapé. Integration of cloud computing and internet of things: A survey. Future Generation Computer Systems 2016, 56, 684–700. [Google Scholar] [CrossRef]
- Alessandro Bozzon, Ilio Catallo, Eleonora Ciceri, Piero Fraternali, Davide Martinenghi, and Marco Tagliasacchi. A framework for crowdsourced multimedia processing and querying. pages 42–47, 2012.
- L. Brebels. Deep Learning with Hadoop, 2014.
- Y. Chen, V. Y. Chen, V. Paxson, and R. H. Katz. What’s new about cloud computing security? Technical Report, Electrical Engineering and Computer Sciences University of California at Berkeley.
- M. Chiang and T. Zhang. Fog and iot: An overview of research opportunities. IEEE Internet of Things Journal 2016, 3, 854–864. [CrossRef]
- Henning Christiansen and Davide Martinenghi. Simplification of database integrity constraints revisited: A transformational approach. pages 178–197, 2004.
- Henning Christiansen and Davide Martinenghi. On Simplification of Database Integrity Constraints. Fundamenta Informaticae 2006, 371–417.
- Paolo Ciaccia and Davide Martinenghi. FA + TA <fsa: Flexible score aggregation. pages 57–66, 2018.
- T. Dillon, C. T. Dillon, C. Wu, and E. Chang. Cloud computing: Issues and challenges. Proceedings of the 2010 24th IEEE International Conference on Advanced Information Networking and Applications, 2010; 33. [Google Scholar]
- C. Dwork and A. Roth. The algorithmic foundations of differential privacy. Technical report, Now Publishers Inc, 2014.
- J. Friedman. Manual of clinical microbiology. Deep Learning Research Chapter, 2017.
- J. Gubbi, R. J. Gubbi, R. Buyya, S. Marusic, and M. Palaniswami. Internet of things (iot): A vision, architectural elements, and future directions. Future Generation Computer Systems 2013, 29, 1645–1660. [Google Scholar] [CrossRef]
- R. Jain. The Art of Computer Systems Performance Analysis: Techniques for Experimental Design, Measurement, Simulation, and Modeling, 1991.
- J. Kreps, N. J. Kreps, N. Narkhede, and J. Rao. Kafka: A distributed messaging system for log processing. In Proceedings of the ACM SIGMOD Conference, 2011.
- S. Kumar and P. Tiwari. Cloud computing for internet of things & sensing based applications. Computer Science & Information Technology (CS & IT), 2012; 55, 527–534.
- A. Lounis and M. Benyahia. A novel cloud-based internet of things architecture: A survey. Journal of Information Processing Systems, 2020; 16, 111–134.
- S. Marston, Z. S. Marston, Z. Li, S. Bandyopadhyay, J. V. Zhang, and A. Ghalsasi. Cloud computing—the business perspective. Decision Support Systems, 2011; 51, 176–189. [Google Scholar]
- P. Mell and T. Grance. The nist definition of cloud computing. https://csrc.nist.gov/publications/detail/sp/800-145/final, 2011.
- D. Merkel. Docker: Lightweight linux containers for consistent development and deployment. Linux Journal, 2014; :2.
- C. Modi, D. C. Modi, D. Patel, B. Borisanya, A. Patel, and M. Rajarajan. A survey on security issues and solutions at different layers of cloud computing. Journal of Supercomputing, 2013; 63, 561–592. [Google Scholar]
- S. Raza and N. Mitton. Iot watchdawg: A lightweight accountability classifier for iot security in smart city environments. IEEE Internet of Things Journal, 2017; 4, 1280–1290.
- J. Riikonen and M. Kankaanranta. Platform as a service for software teaching and learning: Case microsoft azure. International Journal of Information and Education Technology, 2013; 3, 544–548.
- B. P. Rimal, E. B. P. Rimal, E. Choi, and I. Lumb. A taxonomy and survey of cloud computing systems. Proceedings of NCM, 2009; 51. [Google Scholar]
- R. Roman and P. Loch-Ha. A survey of iot cloud platforms. Journal of Cloud Computing, 2018; 18.
- M. Satyanarayanan. The emergence of edge computing. Computer 2017, 50, 30–39.
- W. Shi, J. W. Shi, J. Cao, Q. Zhang, Y. Li, and L. Xu. Edge computing: Vision and challenges. IEEE Internet of Things Journal, 2016; 3, 637–646. [Google Scholar]
- A. Singh and K. Chatterjee. Cloud security issues and challenges: A survey. In Computing for Sustainable Global Development (INDIACom), 2016 3rd International Conference on, pages 2034–2039, 2016.
- B. Varghese and R. Buyya. Next generation cloud computing: New trends and research directions. Future Generation Computer Systems, 2016; 79, 849–861.
- Y. Wang, L. A. Y. Wang, L. A. Kung, and T. A. Byrd. Big data analytics: Understanding its capabilities and potential benefits for healthcare organizations. Technological Forecasting and Social Change, 2018; 126, 3–13. [Google Scholar]
- Y. Yang, L. Y. Yang, L. Wu, G. Yin, L. Li, and H. Zhao. A survey on security and privacy issues in internet-of-things. IEEE Internet of Things Journal, 2017; 4, 1250–1258. [Google Scholar]
- M. Zaharia, P. M. Zaharia, P. Wendell, T. Das, M. Armbrust, A. Dave, X. Meng, J. Rosen, S. Venkataraman, M. Franklin, S. Shenker, and I. Stoica. Apache spark: A unified engine for big data processing. Communications of the ACM, 2016; 59, 56–65. [Google Scholar]
- Q. Zhang, L. Q. Zhang, L. Cheng, and R. Boutaba. Cloud computing: State-of-the-art and research challenges. Journal of Internet Services and Applications, 2010; 1, 7–18. [Google Scholar]
- D. Zissis and D. Lekkas. Addressing cloud computing security issues. Future Generation Computer Systems, 2012; 28, 583–592.
| Attribute | IaaS | PaaS | SaaS |
|---|---|---|---|
| Deployment Flexibility | High | Medium | Low |
| Scalability | High | High | Medium |
| Maintenance Complexity | High | Medium | Low |
| Integration Ease | Medium | High | High |
| Cost-effectiveness | Medium | High | High |
| Security Attribute | IaaS | PaaS | SaaS |
|---|---|---|---|
| Encryption Protocols | AES-256 | RSA-2048 | AES-128 |
| Intrusion Detection Efficiency | 85% | 90% | 80% |
| Privacy-preserving Measures | Moderate | High | Moderate |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




