Submitted:
19 August 2023
Posted:
23 August 2023
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background
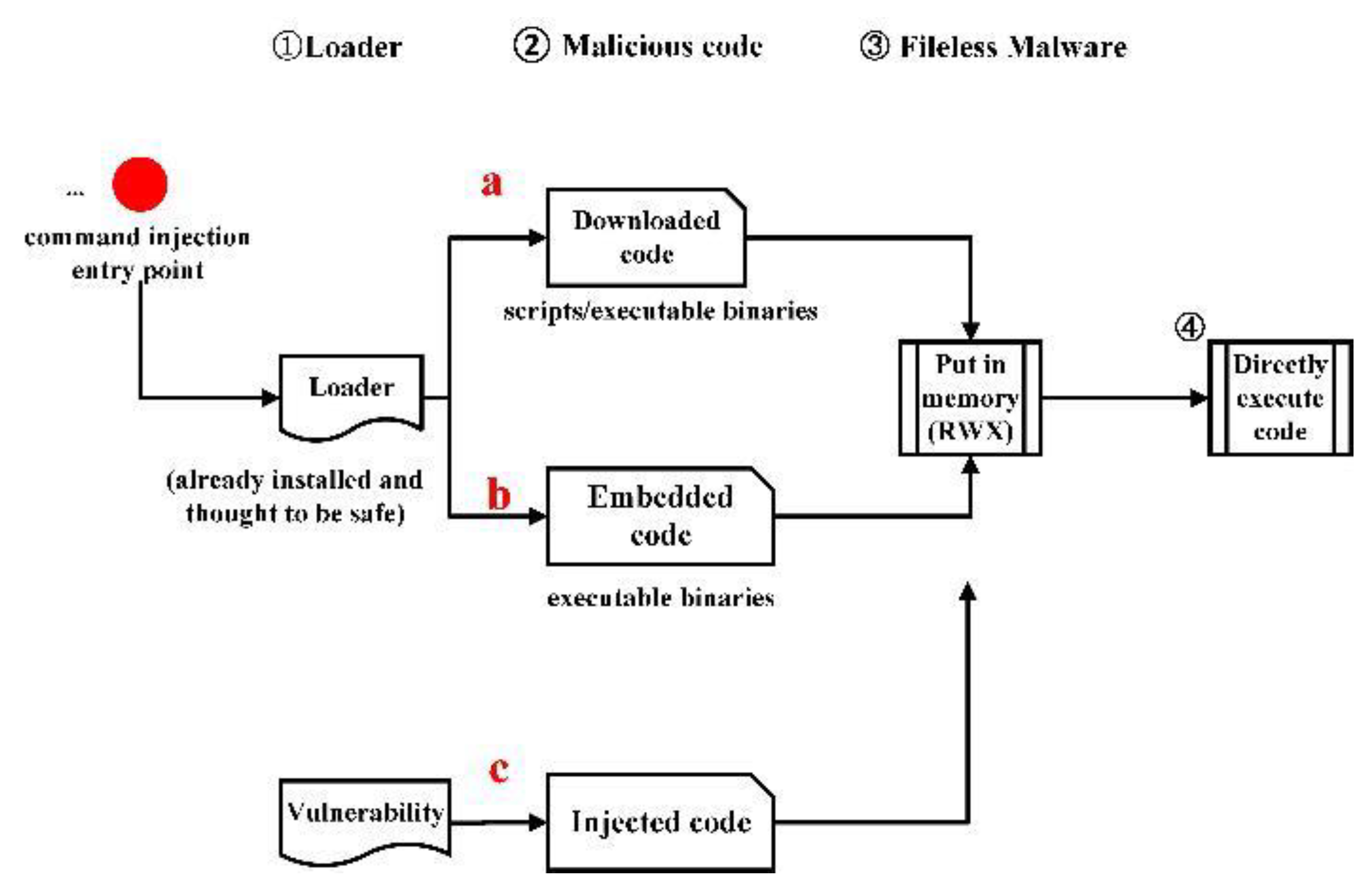
2.1. Fileless Malware
2.2. Approaches to inject code into a process
2.3. An Execution Example of Fileless Malware
3. Related Work
3.1. Fileless Malware Collections, Creation, and Analyses
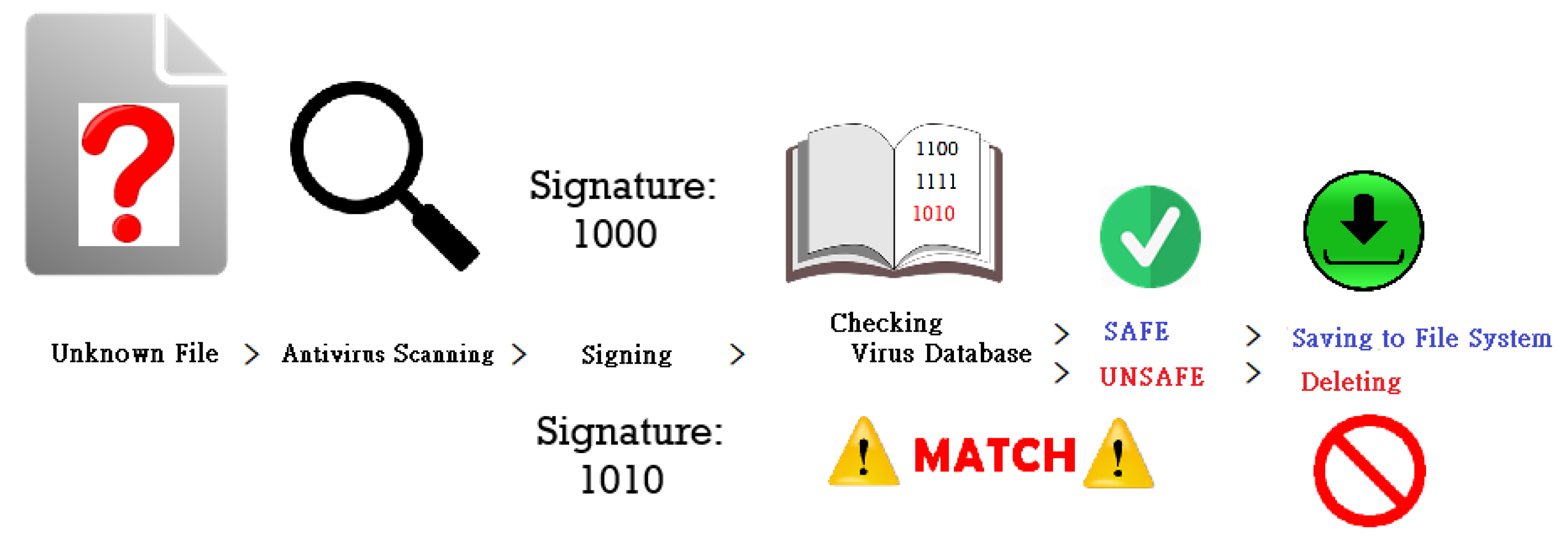
3.2. Static Analysis
3.3. Dynamic Analysis
3.4. Security Settings to Block Fileless Malware Execution
4. Goals, Principles, and System Structure
4.1. Design Principles
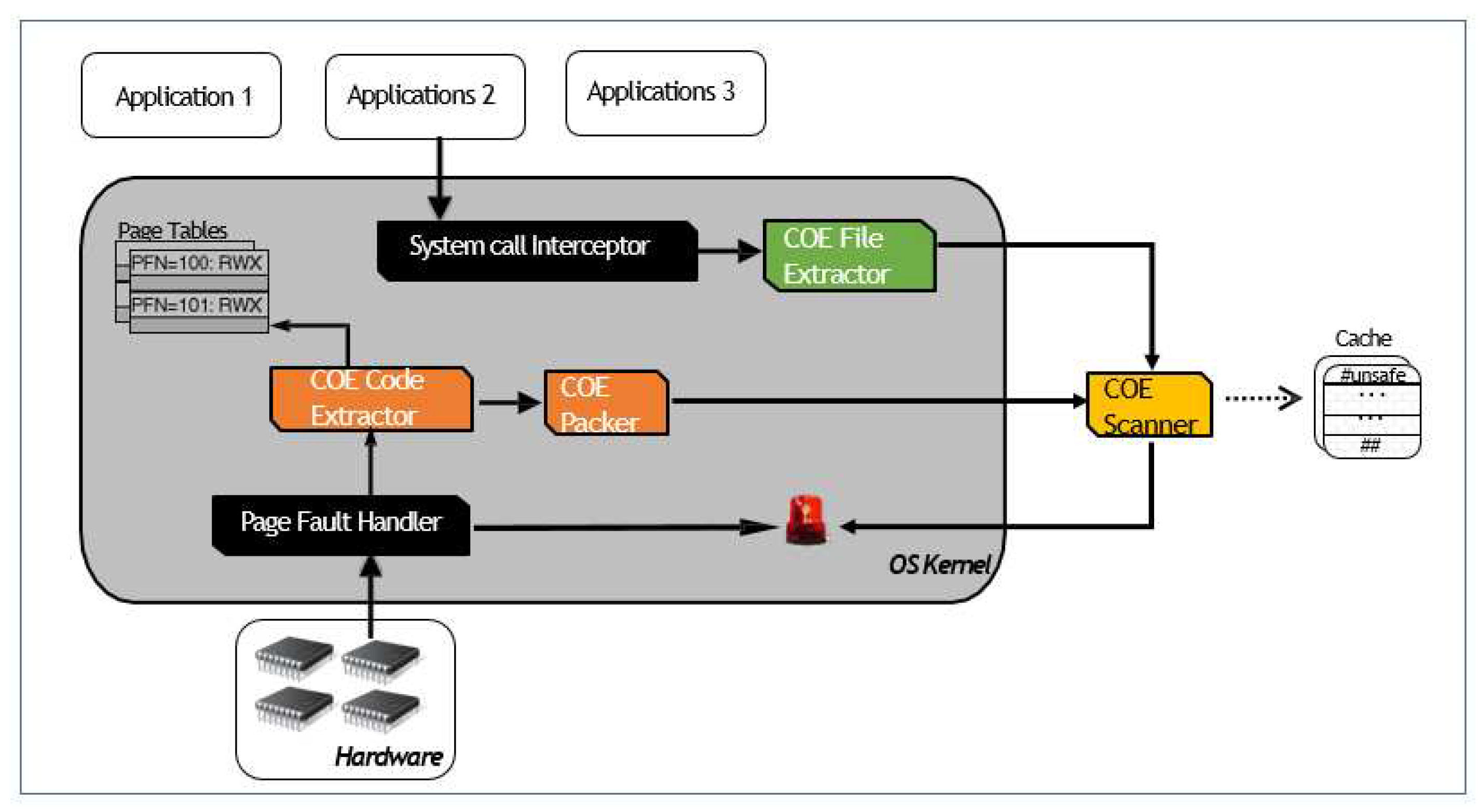
4.2. System Structure
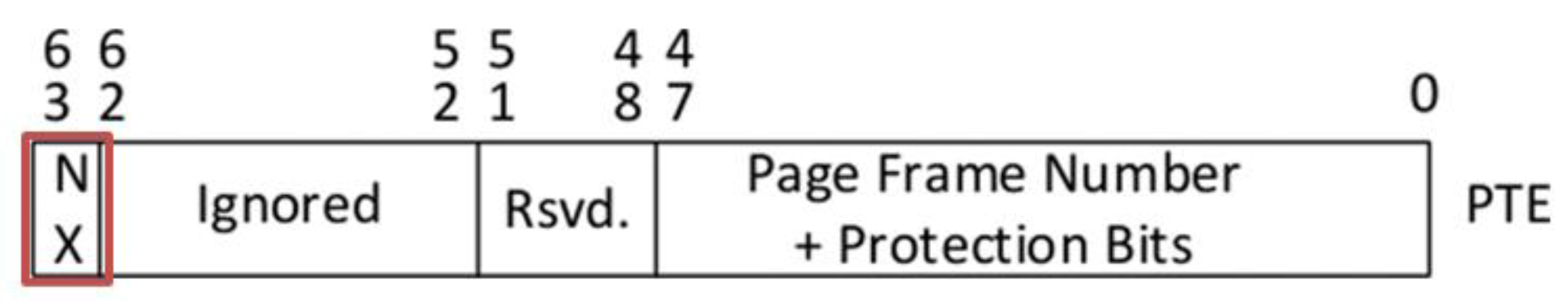
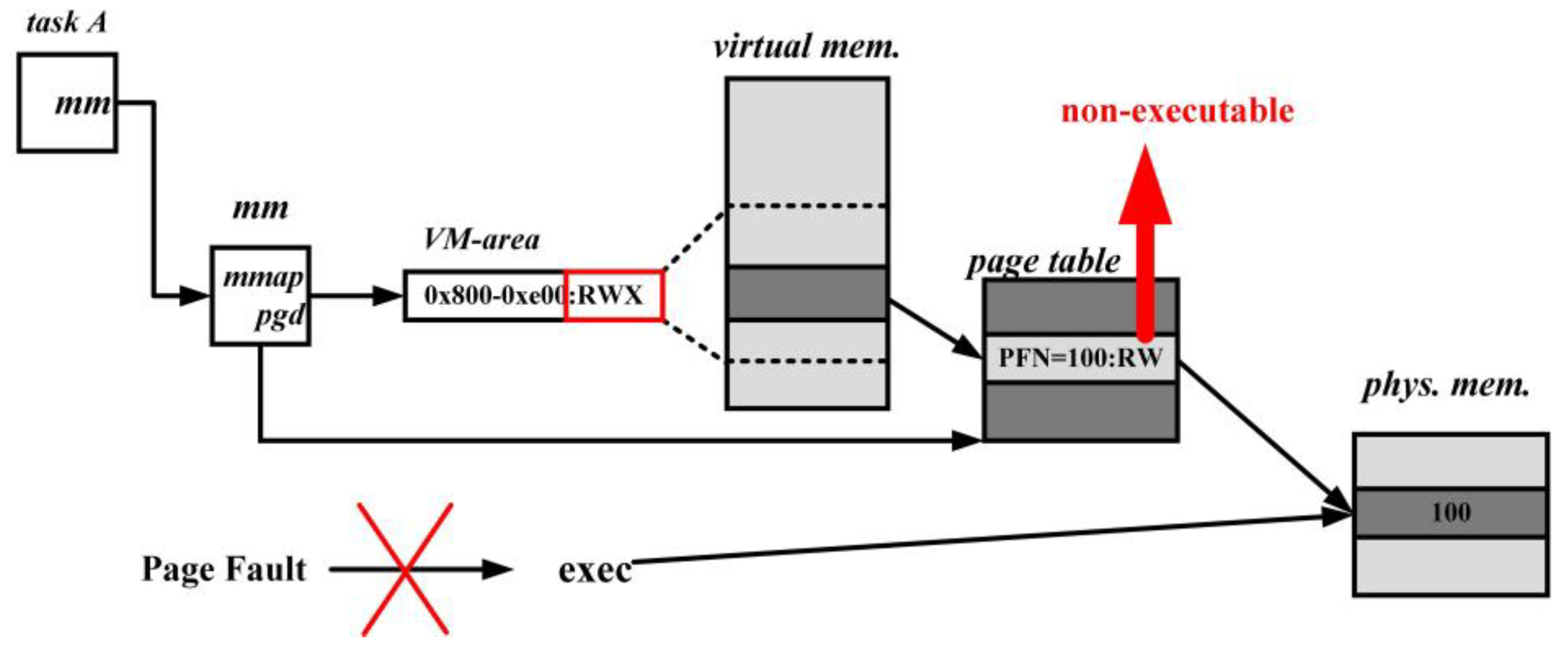
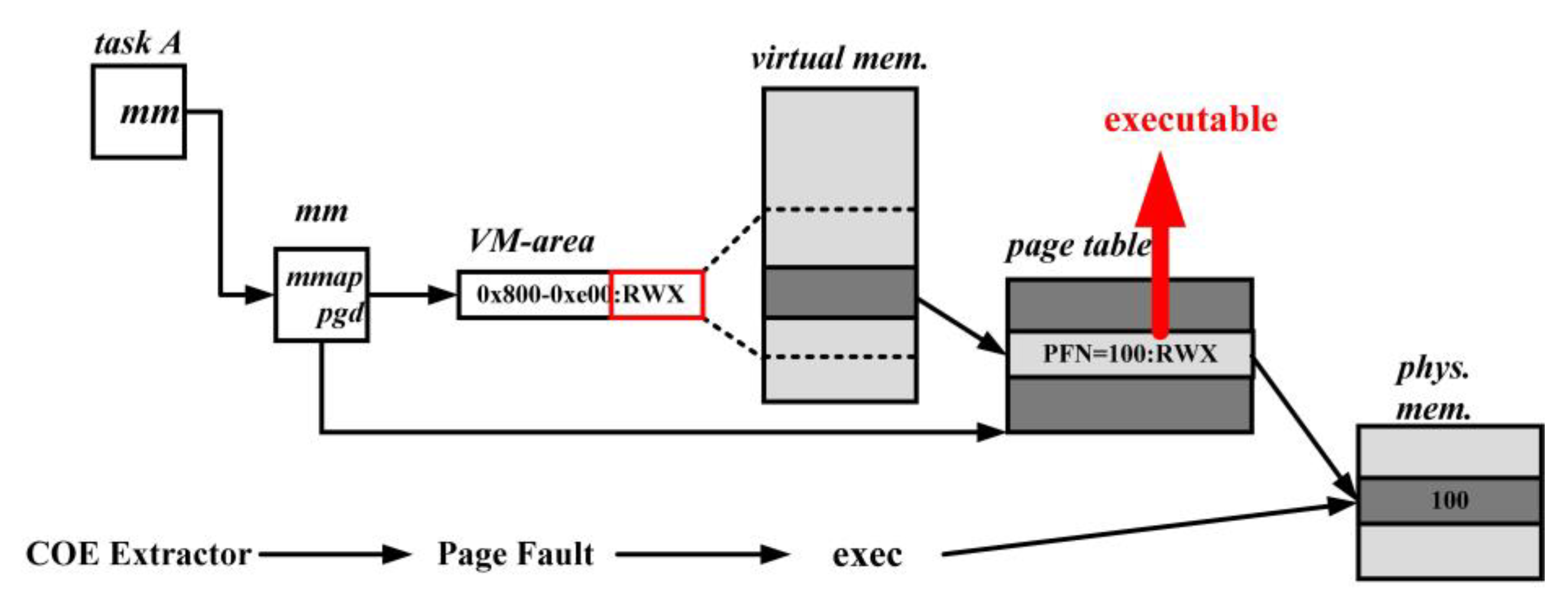
- CoE Code Extractor: CoE Code Extractor: The main function of the CoE Code Extractor is to extract code from memory. CoE Code Extractor uses the NX bit (No eXecute bit) provided by AMD 64-bit CPU or the ND bit (execute disable) provided by Intel 64-bit CPU and supported by Linux to trigger its execution. Figure 5 shows the layout of a Page Table Entry (PTE) and the position of the NX bit in a PTE. When the NX bit of a PTE of a page frame is set to 1, it means the page frame is not executable. In other words, if a CPU retrieves the content of the page frame as code and tries to execute it, a Page Fault Exception [19] will be triggered. CoE Code Extractor inside CoE Page Fault Handler will be executed. CoE sets the NX bits of all PTEs whose corresponding page frames are writable and executable to 1 in advance. CoE utilizes hardware to assist it in checking whether a CPU is trying to execute code stored in a writable page frame. As a result, CoE does not need to spend time in software to make the above check.
- 2.
- CoE Packer: The main function of the CoE Packer is to pack the code extracted from the memory into ELF format. Once the CoE Code Extractor recognizes the necessity of verifying a code segment stored in a writable region, it directs the CoE Packer to retrieve the code and bundle it into an ELF file. The CoE Packer accomplishes this by appending the corresponding ELF header [21] and setting the ELF header’s entry point field to the assembled code’s starting point. CoE transfers the code into an ELF file is that CoE uses VirueTotal [22] to check whether a piece of code is malicious or benign. And VIrutTotal only accepts and analyzes data in a file form.
- 3.
- CoE Scanner: The main function of the CoE Scanner is to scan a packed ELF file. After CoE Code Packer packs a piece of code into an ELF file, it hands it over to CoE Scanner to check whether the code is malware. The current version of CoE Scanner uses VirusTotal’s APIs to ask VirusTotal to help CoE Scanner check whether a piece of code is malware. VirusTotal [22] provides a free/pay malware analysis service and has assembled over 60 antivirus engines to analyze input files.
- 4.
- CoE File Checker: As described in subsection 2.2, files malware may use system call memfd_create() to create an anonymous area to inject a malware file and then use system call execve() to execute the file hidden inside the address space of a process. CoE File Checker intercepts and collects files executed this way. When a program uses system call execve(), CoE File Checker checks the location of the file that is going to be executed and determines whether the file is in memory. If it is in the memory, CoE File Checker pauses the execution first, retrieves the file, and then submits it to CoE Scanner for further analysis. CoE File Checker only allows benign programs to continue their execution.
4.3. Execution Paths of CoE
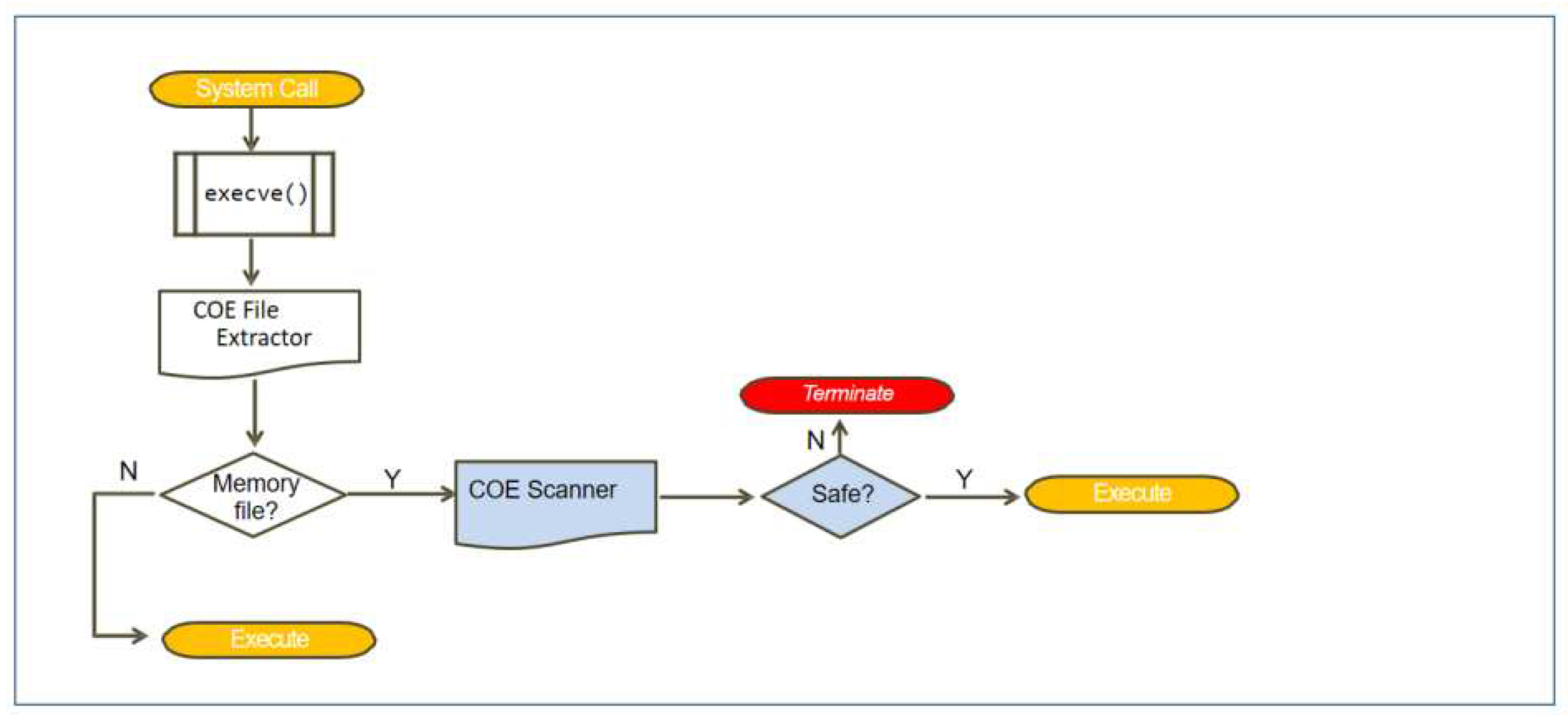
- Execution Flows of the File Path: When CoE learns that a process uses a system called execve() to execute a program, CoE File Extractor first checks whether the file is in the memory, as shown in Figure 10. CoE File Extractor allows the process to execute the file if the file is not stored in the memory. But if the file is stored in memory, CoE File Extractor retrieves the file and gives the file to CoE Scanner. Then CoE Scanner utilizes VirusTotal to check whether the file is malicious. The CoE File Extractor allows the system to handle a file normally unless it is determined to be malicious, in which case the execution of the file is prevented, and the process is terminated promptly.
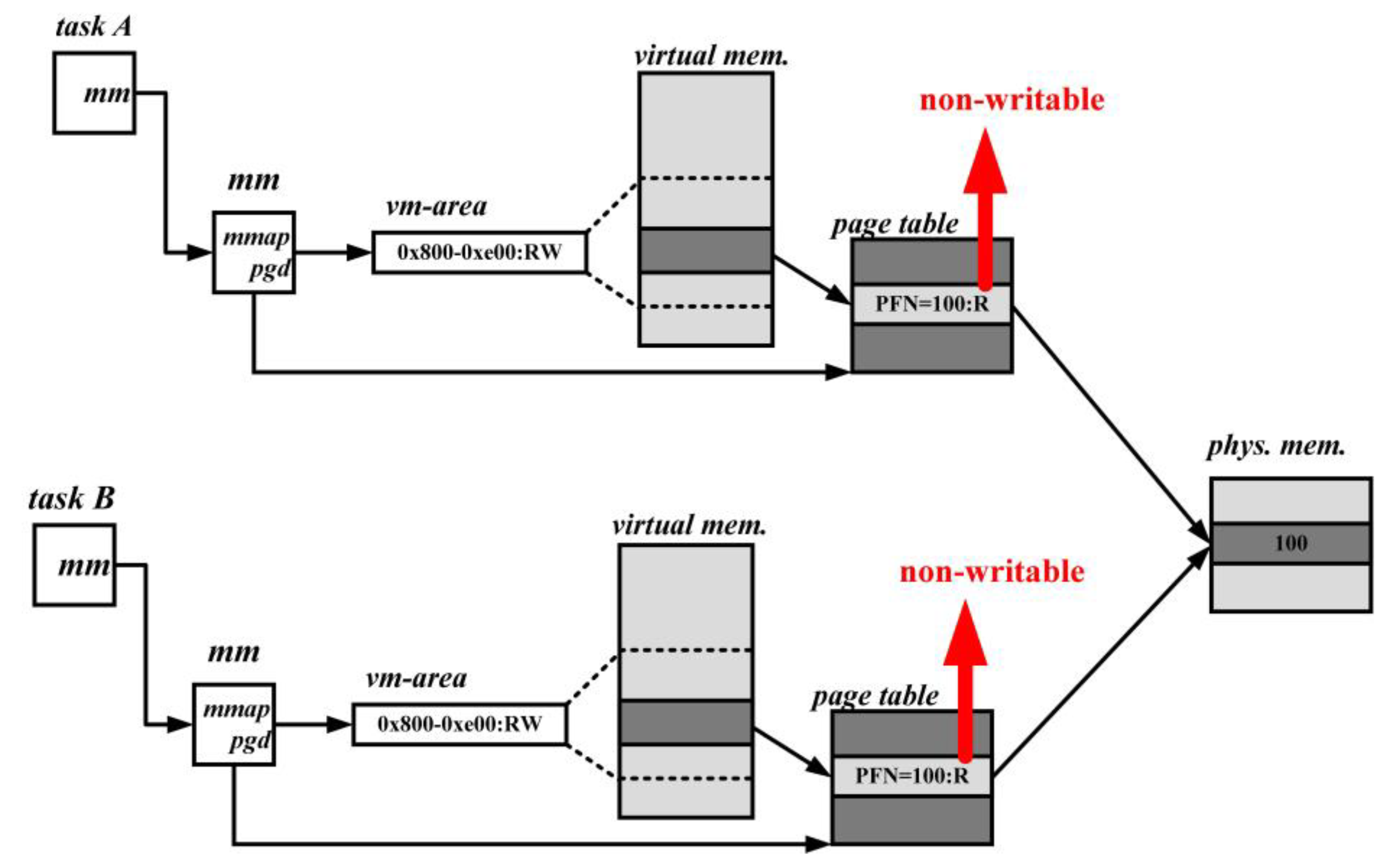
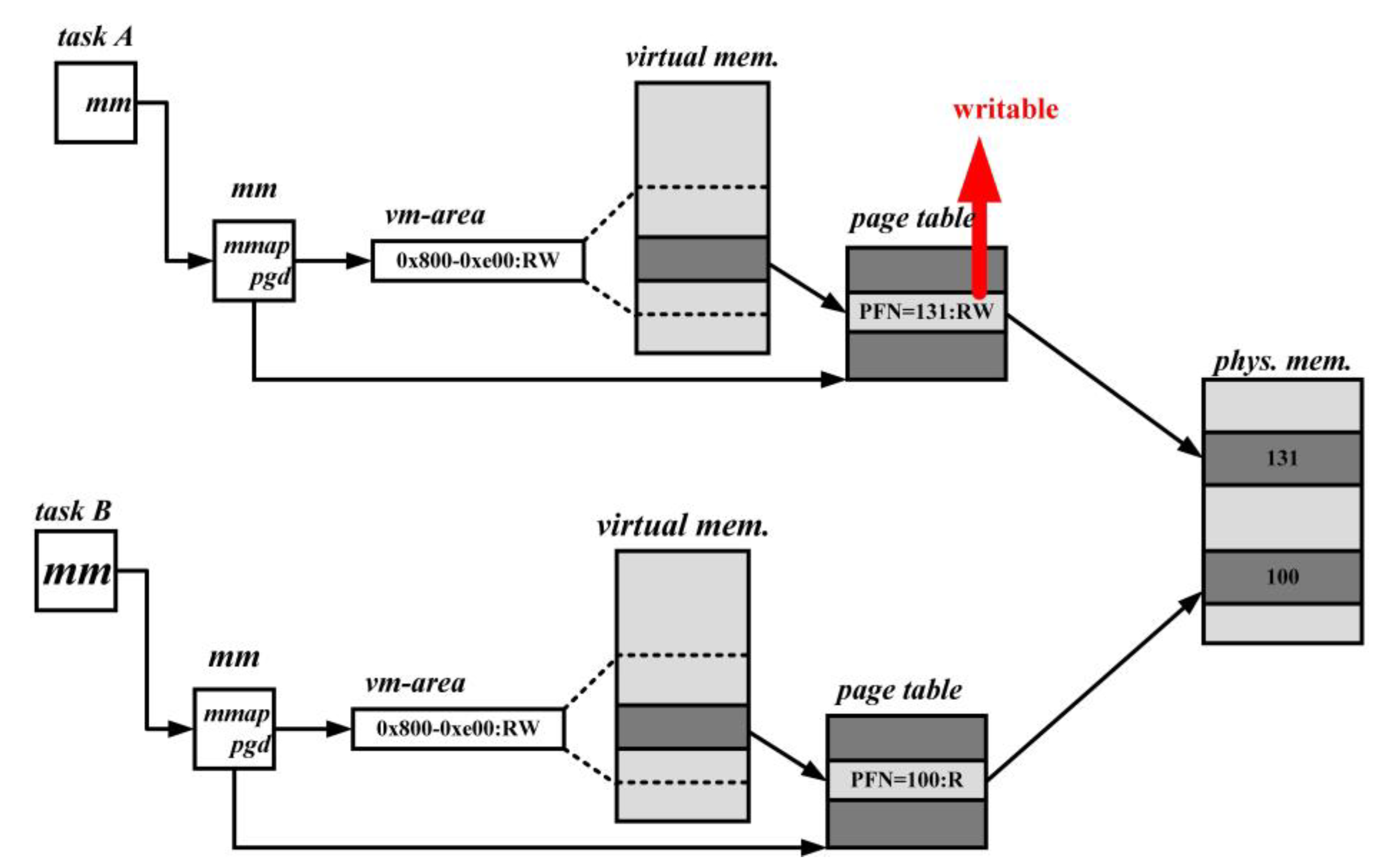
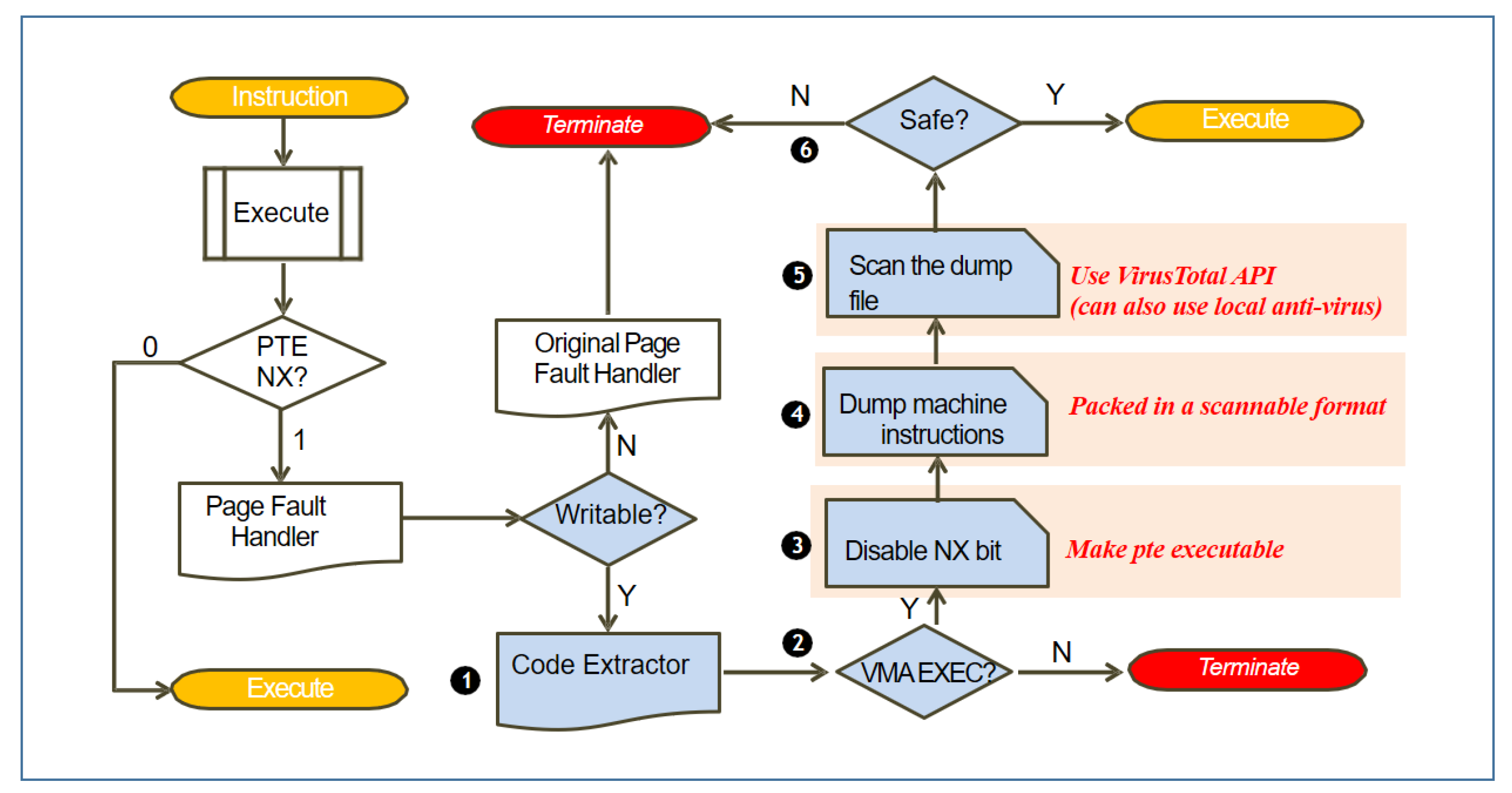
- Execution Flows of the Text Path: When the execution of an instruction, the CPU hardware checks the NX bit in the PTE of the corresponding page frame, as shown in Figure 11. If the NX bit is 0, the instruction is allowed to execute. However, if the NX bit is 1, the hardware triggers a Page Fault Exception. The exception then verifies whether the permission in the vm-area of the page frame is writable. If it is writable, execution is transferred to CoE Code Extractor to determine whether the permission in the vm-area is marked as executable. The Page Fault Handler terminates the related process if the permission is marked as non-executable. CoE Code Extractor restores the NX bit to 0 if the permission is marked as executable. And then, CoE Packer retrieves the code from memory and packs the code with an ELF header to transform the code into an ELF file. Later on, the ELF file is sent to CoE Scanner. CoE Scanner scans the file using VirusTotal to determine whether the code is malicious or benign. If the file is harmless, CoE Scanner resumes the execution of the code; otherwise, it terminates the execution of the code. The size of a page frame is 4K.
5. Evaluation and Analysis
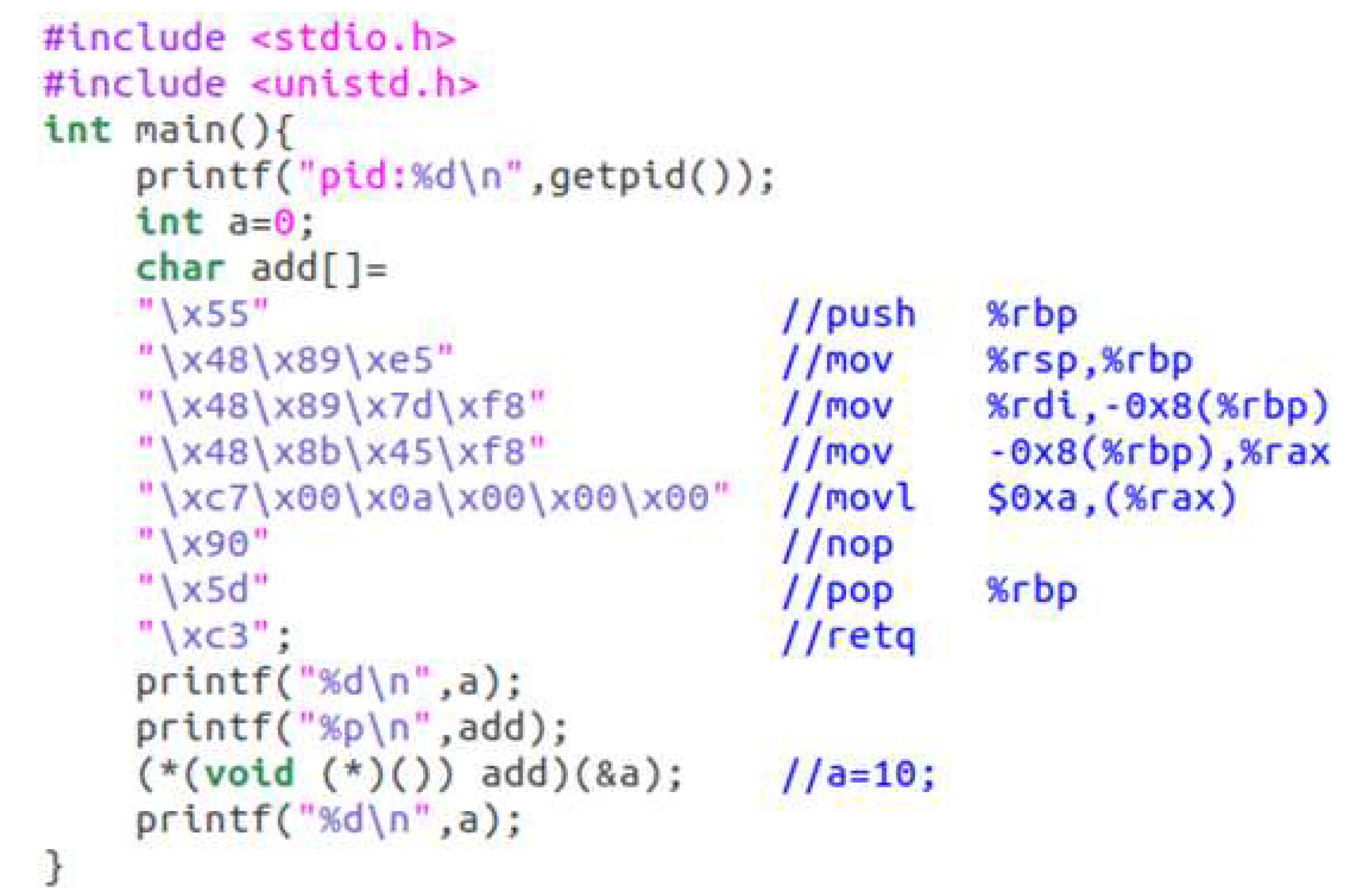
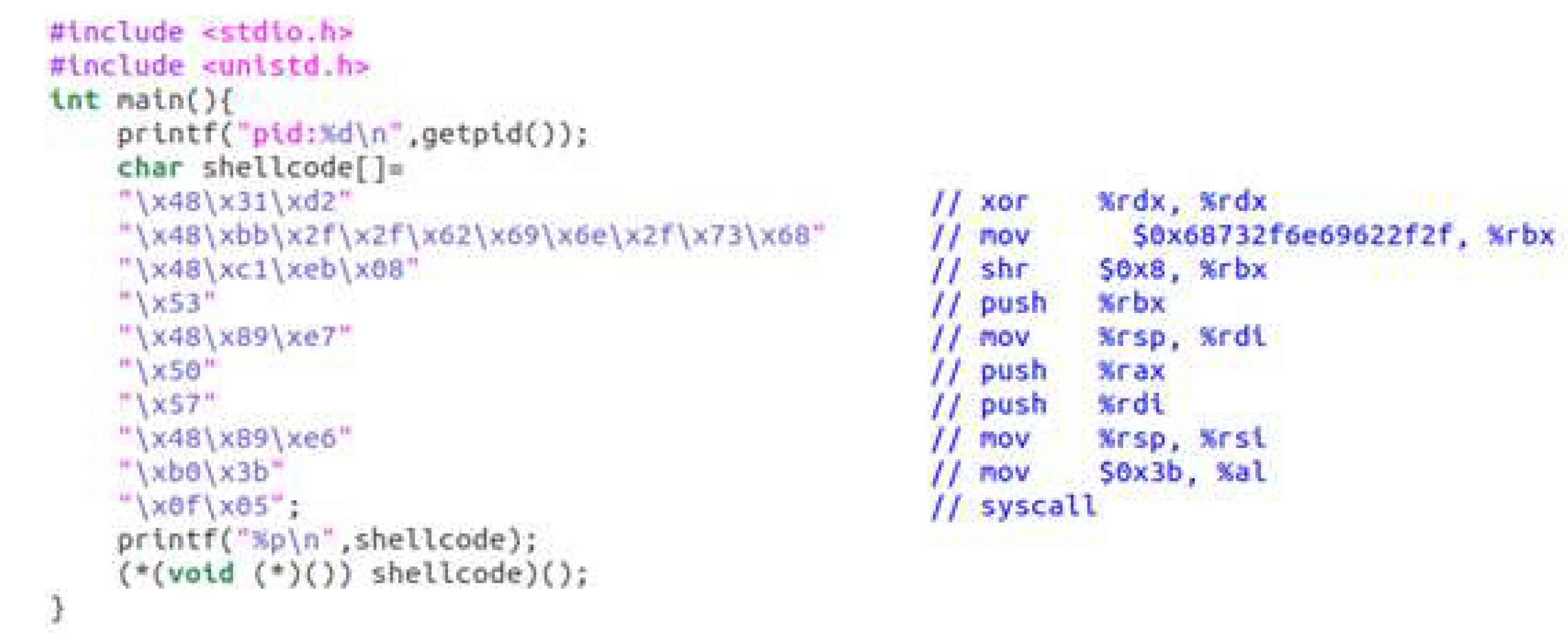
5.1. Effectiveness Tests for Code Stored in the Stack Segment
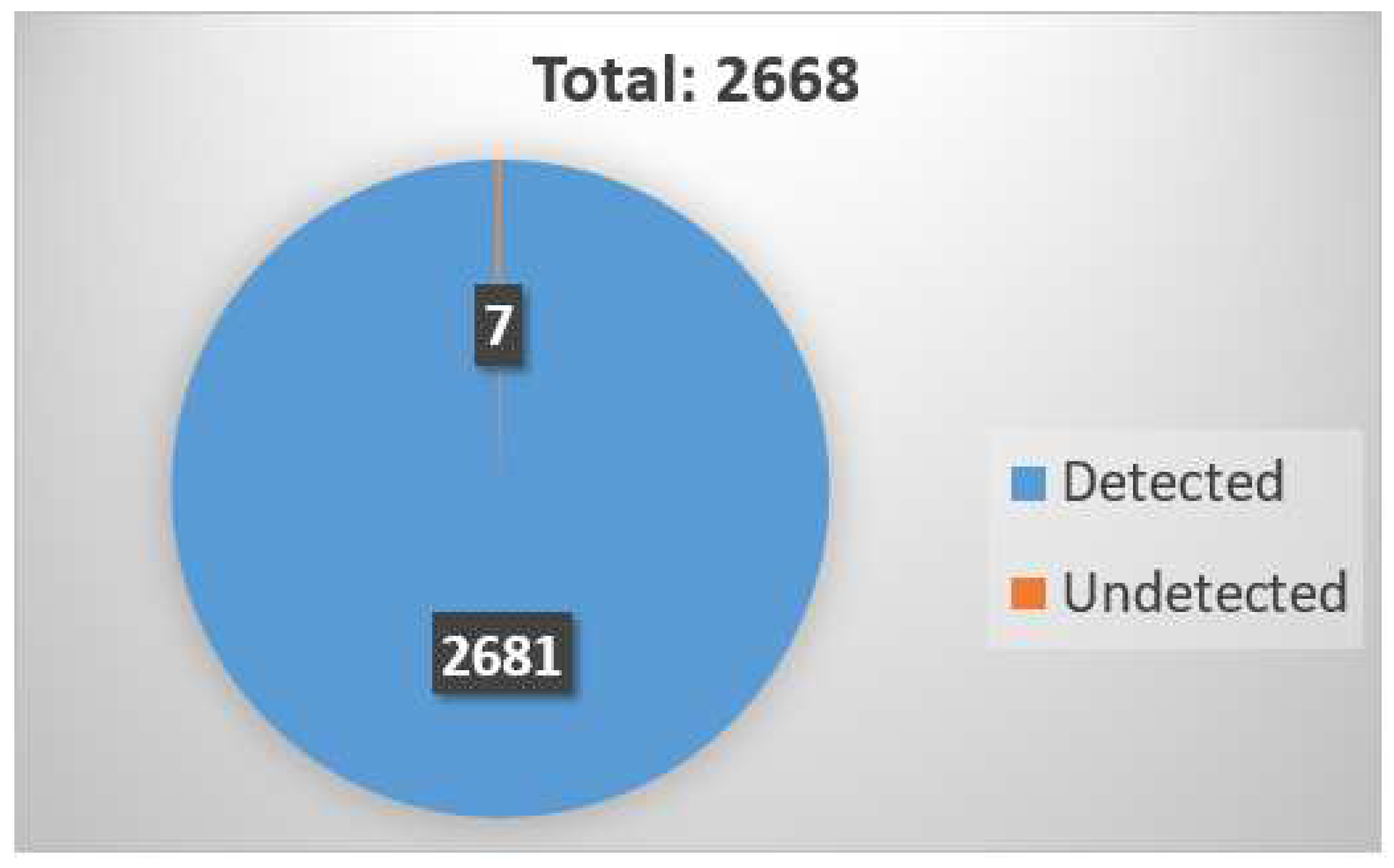
5.2. Effectiveness Evaluation
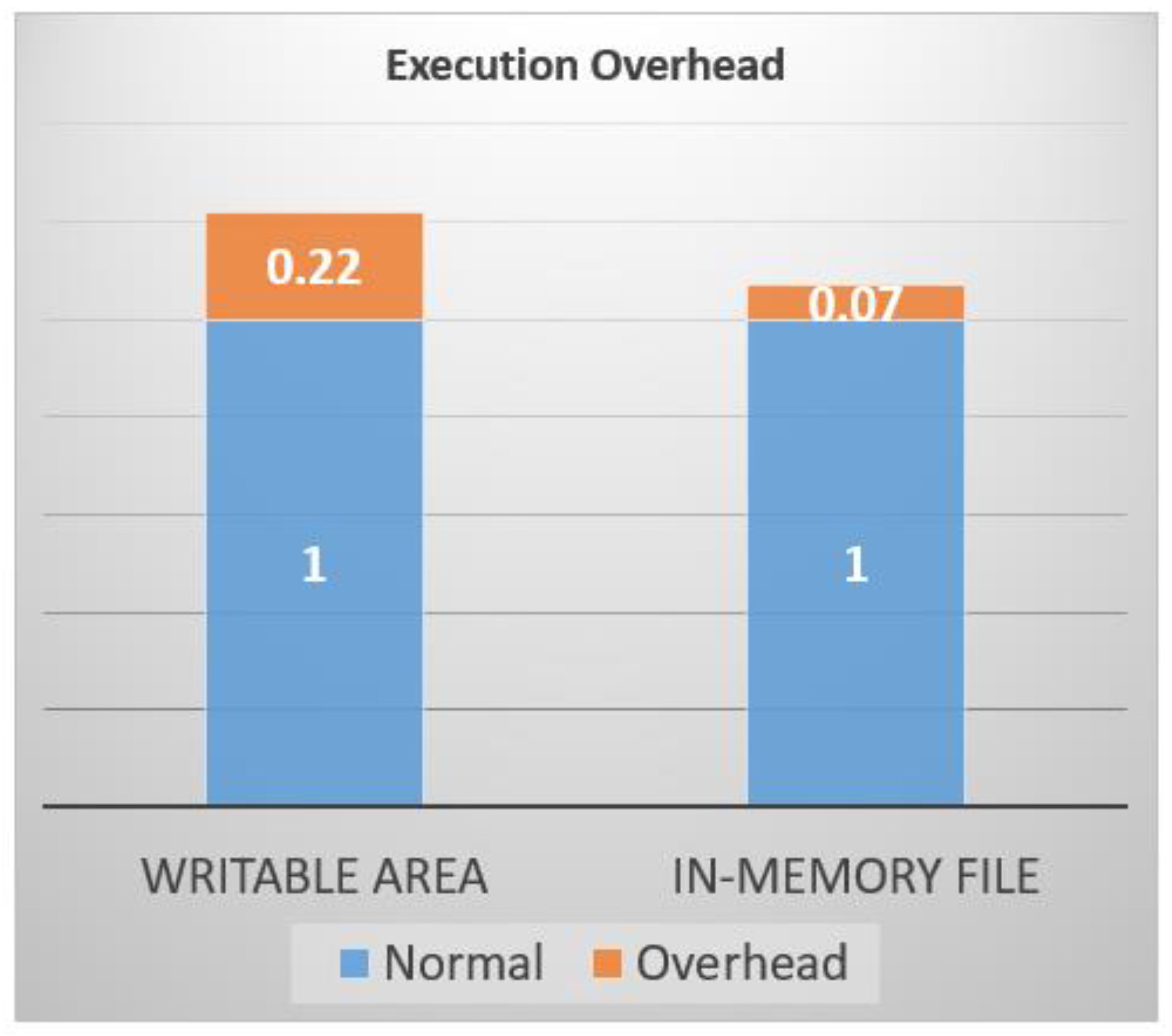
5.3. Efficiency Evaluation
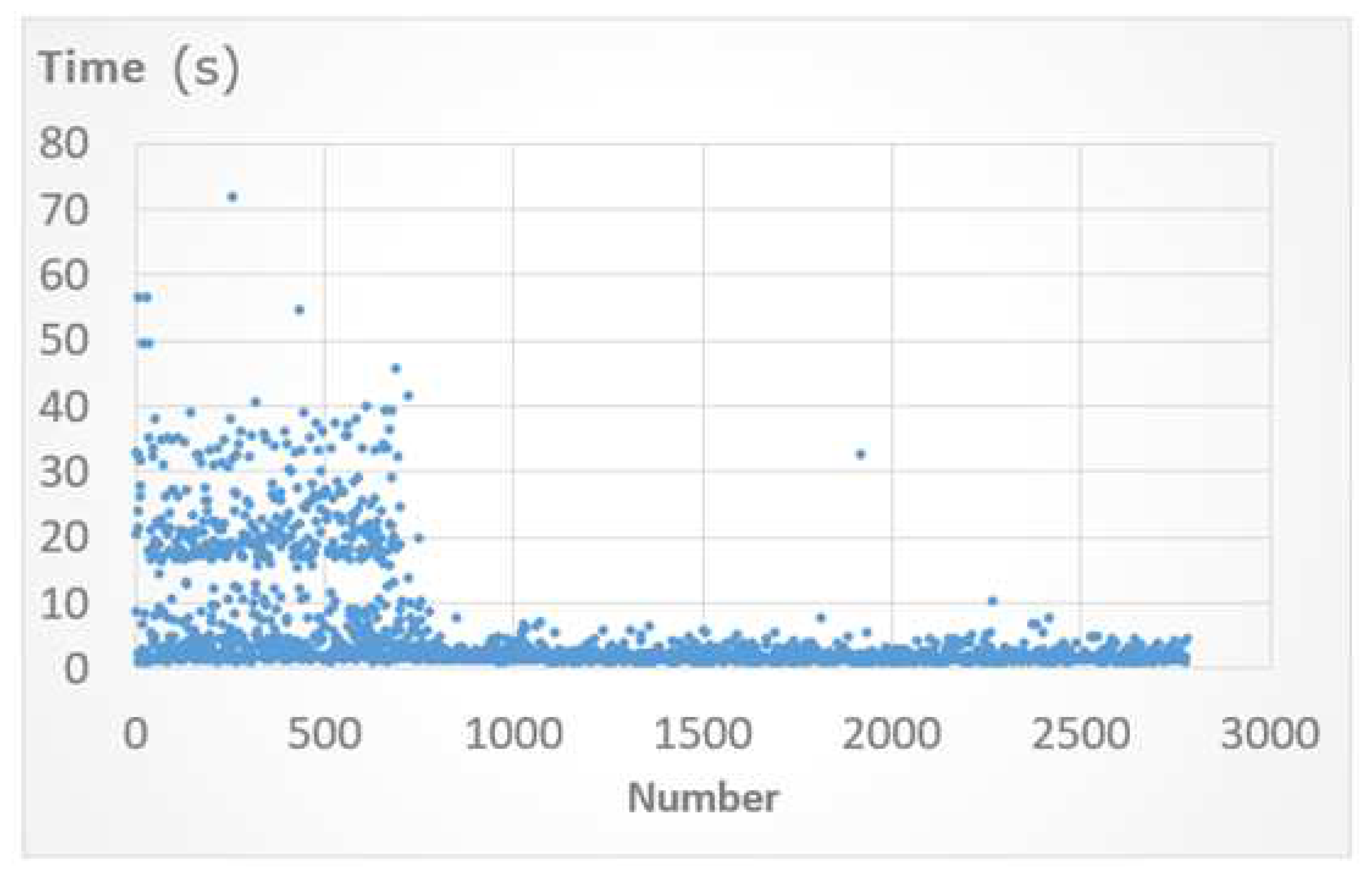
5.4. File Scanning Time Evaluation
6. Discussion
7. Conclusion
References
- A. Alzuri, D. C. Andrade, Y. N. Escobar, and B. M. Zamora, “The growth of fileless malware,” 2019.
- A. D. Rayome. “Report: Fileless malware attacks 10x more likely to infect your machine than others (2017),” [Online]. Available: https://www.techrepublic.com/article/report-fileless-malware-attacks-10xmore-likely-to-infect-your-machine-than-others/, [Accessed: 20-Aug-2021].
- WatchGudrd, “New Research: Fileless Malware Attacks Surge by 900% and Cryptominers Make a Comeback, While Ransomware Attacks Decline,” [Online]. Available: https://www.globenewswire.com/en/newsrelease/2021/03/30/2201173/0/en/New-Research-Fileless-Malware-Attacks-Surge-by-900-and-Cryptominers-Make-a-Comeback-While-Ransomware-Attacks-Decline.html, [Accessed: 20-Aug-2021].
- Ben Nick, “Fileless attack detection for Linux in preview,” [Online]. Available: URL: https://azure.microsoft.com/zh-tw/blog/filelessattack-detection-for-linux-in-preview/, [Accessed: 20-Aug-2021].
- Stuart. In-memory-only elf execution (without tmpfs). (2017), [Online]. Available: https://magisterquis.github.io/2018/03/31/in-memory-only-elfexecution.html, [Accessed: 20-Aug-2021].
- Simon Floreza, Donald Castillo, and Mark Manahan, “Security101: Defending Against Fileless Malware,” [Online]. Available: https://www.trendmicro.com/vinfo/us/security/news/securitytechnology/security-101-defending-against-filelessmalware# documentexploits, [Accessed: 20-Aug-2021].
- I. Kara, "Fileless malware threats: Recent advances, analysis approach through memory forensics and research challenges," Expert Systems with Applications, p. 119133, 2022. [CrossRef]
- O. Khalid et al., "An insight into the machine-learning-based fileless malware detection," Sensors, vol. 23, no. 2, p. 612, 2023. [CrossRef]
- N. Karapetyants and D. Efanov, "A practical approach to learning Linux vulnerabilities," Journal of Computer Virology and Hacking Techniques, pp. 1-10, 2022. [CrossRef]
- M. A. Butt, Z. Ajmal, Z. I. Khan, M. Idrees, and Y. Javed, "An in-depth survey of bypassing buffer overflow mitigation techniques," Applied Sciences, vol. 12, no. 13, p. 6702, 2022. [CrossRef]
- Y. Lee, J. Kwak, J. Kang, Y. Jeon, and B. Lee, "Pspray: Timing {Side-Channel} based Linux Kernel Heap Exploitation Technique," in 32nd USENIX Security Symposium (USENIX Security 23), 2023, pp. 6825-6842.
- F. CyberSecurity. Elf in-memory execution. (2018), [Online]. Available: https://blog.fbkcs.ru/elf-in-memory-execution/, [Accessed: 30-Aug-2021].
- Sinha S., “Finding Command Injection Vulnerabilities. In: Bug Bounty Hunting for Web Security,” Apress, Berkeley, CA. [Online]. Available: https://doi.org/10.1007/978-1-4842-5391-5 9, [Accessed: 20-Aug-2021]. [CrossRef]
- Fan Dang, Zhenhua Li, Yunhao Liu, Ennan Zhai, Qi Alfred Chen, Tianyin Xu, Yan Chen, Jingyu Yang, “Understanding Fileless Attacks on Linux-based IoT Devices with HoneyCloud,” Proceedings of the 17th Annual International Conference on Mobile Systems, Applications, and Services, June 2019.
- B.N. Sanjay, D.C. Rakshith, R.B. Akash, Dr.Vinay V. Hegde, “An Approach to Detect Fileless Malware and Defend its Evasive mechanisms, ” 2018 3rd International Conference on Computational Systems and Information Technology for Sustainable Solutions (CSITSS),” Bengaluru, India, 20-22 Dec. 2018.
- Sherif Saad, Farhan Mahmood, William Briguglio, Haytham Elmiligi, “JSLess: A Tale of a Fileless Javascript Memory-Resident Malware,” 15th International Conference, ISPEC 2019, Kuala Lumpur, Malaysia, November 26–28, 2019. [CrossRef]
- Luca Caviglione, Michał Chora´s, Igino Corona, Artur Janicki, Wojciech Mazurczyk, Marek Pawlicki, Katarzyna Wasielewska, ”Tight Arms Race: Overview of Current Malware Threats and Trends in Their Detection,”IEEE Access, vol. 9, pp. 5371-5396, 2021.
- R. Sihwail, K. Omar, and K. A. Zainol Ariffin, “Malware detection approach based on artifacts in memory image and dynamic analysis,” Applied Sciences, vol. 9, Sep. 2019. [CrossRef]
- O. C. bookshelf, “Page fault exception handler.” (2020), [Online]. Available: https://man7.org/linux/man-pages/man2/memfd create.2.html, [Accessed: 20-Aug-2021].
- S. Eranian and D. Mosberger. “How copy-onwrite really works.” (2002), [Online]. Available: https://www.informit.com/articles/article.aspx?p=29961&seqNum=5, [Accessed: 20-Aug-2021].
- S. Ninja. “Complete tour of pe and elf: Section headers.(2016),”[Online]. Available: https://resources.infosecinstitute.com/complete-tourof-pe-and-elf -part-5/, [Accessed: 20-Aug-2021].
- VirusTotal, Virustotal. (2019), [Online]. Available: https://www.virustotal.com/, [Accessed: 20-Aug-2021].
- Clam AntiVirus (ClamAV), [Online]. Available: Available https://www.clamav.net/, [Accessed: 20-Aug-2021].
- Shell-Storm, “Shellcodes database for study cases (2019)”, [Online]. Available: http://shell-storm.org/shellcode/, [Accessed: 20-Aug-2021].
- Abhijit Mohanta and Anoop Saldanha (2020), “Malware Analysis and Detection Engineering,” Springer. [CrossRef]
- VirusShare.com. Virusshare.com. (2019), [Online]. Available: https://virusshare.com/, [Accessed: 20-Aug-2021].
- Fu-Hau Hsu, Min-Hao Wu, Chang-Kuo Tso, Chi-Hsien Hsu, Chieh-Wen Chen, “Antivirus Software Shield against Antivirus Terminators,” IEEE Transactions on Information Forensics and Security, VOL. 7, NO.5, Pages 1439 - 1447, October 2012.



| CPU | 3.4GHZ AMD Ryzen 7 1700X CPU with 8 cores |
| OS | Ubuntu 18.04 |
| Kernel | Linux Kernel 4.20.3 |
| Shell code form | # of detected shell code samples | # of total shell code samples | detection rate |
|---|---|---|---|
| Execute("/bin/sh") | 2 | 4 | 50% |
| Connect Back Shell | 3 | 7 | 42.85% |
| Execute("shutdown -h now") | 1 | 2 | 50% |
| Add users with passwd | 1 | 1 | 100% |
| Execute("/sbin/pagetables -F") | 1 | 1 | 100% |
| Total | 8 | 15 | 53.33% |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




