Submitted:
07 July 2023
Posted:
12 July 2023
You are already at the latest version
Abstract
Keywords:
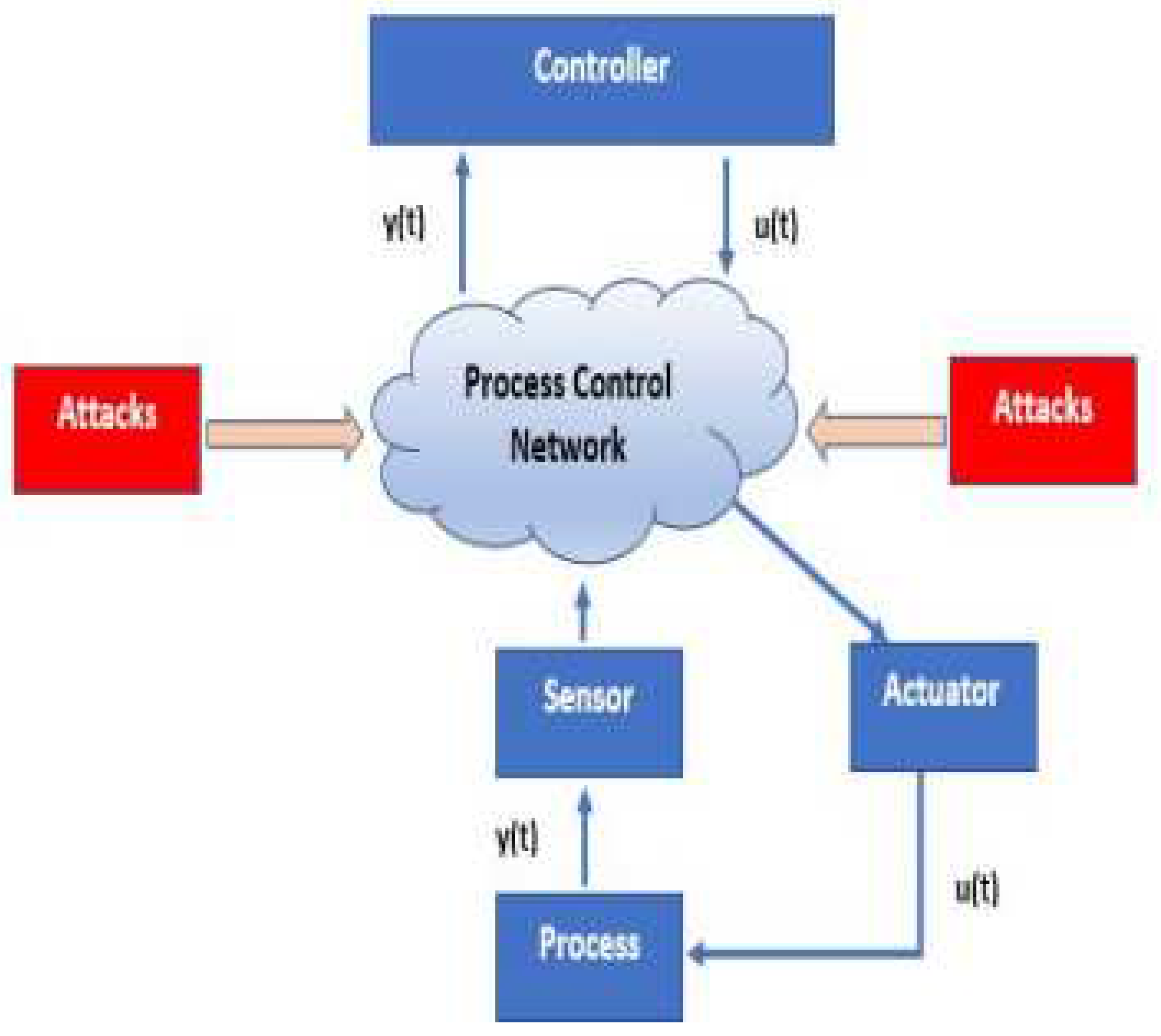
1. Introduction
- Disgruntled employees pose a considerable threat to the OT as they can become insider threats with good knowledge of the production facility. Intentional malicious insider attacks usually have a huge impact with a high percentage of success [17].
- Application of different machine learning algorithms for the detection and prevention of amorphous cyber-attacks on these oil and gas facilities using real-time SCADA dataset.
2. Related Works
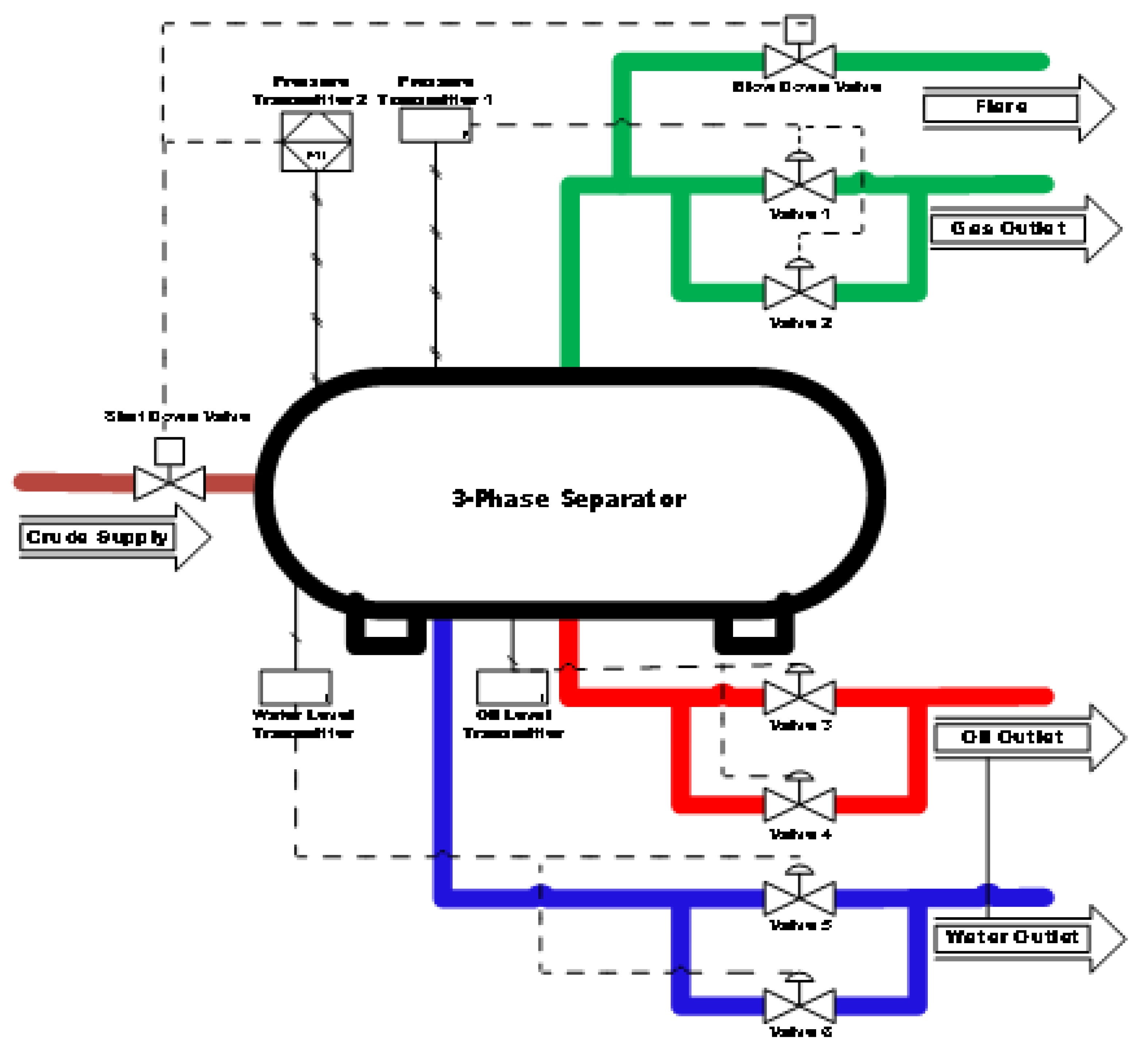
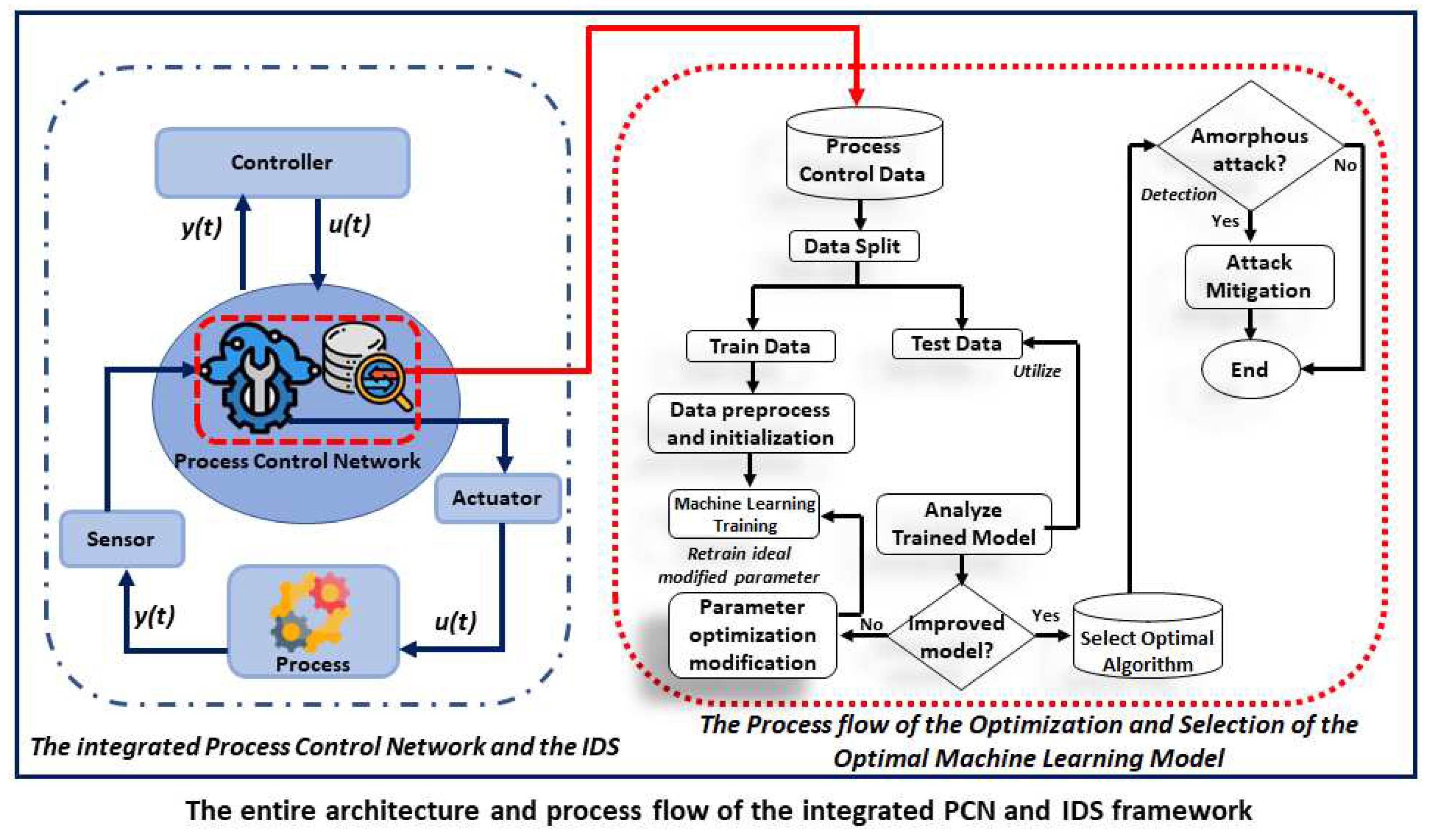
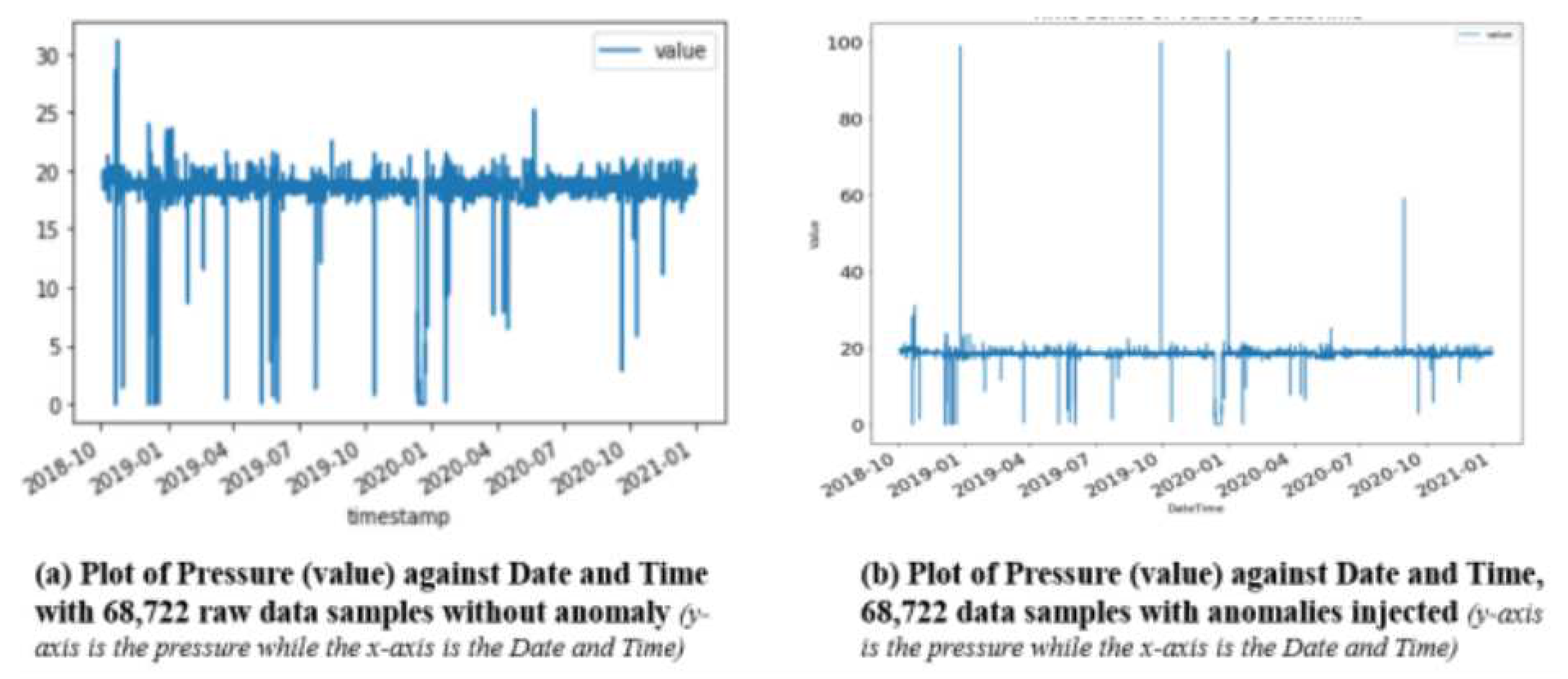
3. Materials and Methods
3.1. Intrusion Detection Using Machine Learning Models
4. Result Discussion and Performance Evaluation
5. Conclusion
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Sample Availability
Abbreviations
| APT | Advance Persistent Threats |
| AUC | Area Under Curve |
| DDoS | Distributed Denial-of-Service |
| DoS | Denial-of-Service |
| FAR | False Alarm Rates |
| ICS | Industrial Control Systems |
| ICT | Information and Communication Technology |
| IDS | Intrusion detection systems |
| IIoT | Industrial Internet of Things |
| IoT | Internet of Things |
| IP | Internet Protocol |
| IQR | Interquartile Range |
| IT | Information Technology |
| kNN | k-Nearest Neighbours |
| LDR | Linear Discriminant Regression |
| LOF | Local Outlier Factor |
| LSTM | Long Short-Term Memory |
| MATLAB | Matrix Laboratory |
| MCE | Misclassification error |
| MitM | Man-in-the-Middle |
| ORNL | Oak Ridge National Laboratories |
| OT | Operation Technology |
| PCN | process control network |
| PLC | Programmable Logic Controller |
| PyOD | Python Outlier detection |
| ROC | Receiver Operator Characteristics |
| SCADA | Supervisory Control and Data Acquisition |
| SVM | Support Vector Machines |
| USB | Universal Serial Bus |
| WUSTL | Washington University in St. Louis |
References
- Smurthwaite, M.; Bhattacharya, M. Convergence of IT and SCADA: Associated Security Threats and Vulnerabilities. IOP Conference Series: Materials Science and Engineering 2020, 790, 012041. [Google Scholar] [CrossRef]
- CISA; FBI. DarkSide Ransomware: Best Practices for Preventing Business Disruption from Ransomware Attacks. Cybersecurity Advisory 2021, 1. [Google Scholar]
- Irmak, E.; Erkek, İ. An overview of cyber-attack vectors on SCADA systems. 2018 6th International Symposium on Digital Forensic and Security (ISDFS) 2018, 1–5. [Google Scholar] [CrossRef]
- Stergiopoulos, G.; Gritzalis, D.A.; Limnaios, E. Cyber-Attacks on the Oil & Gas Sector: A Survey on Incident Assessment and Attack Patterns. IEEE Access 2020, 8, 128440–128475. [Google Scholar] [CrossRef]
- Nwakanma, C.I.; Ahakonye, L.A.C.; Njoku, J.N.; Eze, J.; Kim, D.S. “Effective Industrial Internet of Things Vulnerability Detection Using Machine Learning. Proc. 5th Int. Conf. Inf. Technol. Educ. Dev. Chang. Narrat. Through Build. a Secur. Soc. with Disruptive Technol. ITED 2022, 2022, pp. 1–8. [Google Scholar] [CrossRef]
- Ahakonye, L.A.C.; Nwakanma, C.I.; Lee, J.M.; Kim, D.S. Agnostic CH-DT Technique for SCADA Network High-Dimensional Data-Aware Intrusion Detection System. IEEE Internet of Things J. 2023, 1. [Google Scholar] [CrossRef]
- Ogu, R.E.; Achumba, I.E.; Okoronkwo, C.D.; Chukwudebe, G.A.; Chukwuchekwa, N. An IoT Solution for Air Quality Monitoring and Hazard Identification for Smart City Development. 2022 IEEE Nigeria 4th International Conference on Disruptive Technologies for Sustainable Development (NIGERCON) 2022, 1–5. [Google Scholar] [CrossRef]
- Ogu, R.E.; Chukwudebe, G.A.; Achumba, I.E.; Chukwuchekwa, N.; Ezenugu, I.A. A Robust IoT-based Air Quality Monitoring Node for Multi-Location Deployment. Int. J. Eng. Res. Technol. 2022, 11, 146–151. [Google Scholar]
- Ahakonye, L.A.C.; Nwakanma, C.I.; Lee, J.M.; Kim, D.S. SCADA intrusion detection scheme exploiting the fusion of modified decision tree and Chi-square feature selection. Internet of Things 2023, 21, 100676. [Google Scholar] [CrossRef]
- Alves, T.; Das, R.; Morris, T. Embedding Encryption and Machine Learning Intrusion Prevention Systems on Programmable Logic Controllers. IEEE Embedded Systems Letters 2018, 10, 99–102. [Google Scholar] [CrossRef]
- Ramotsoela, D.; Hancke, G.; Abu-Mahfouz, A. Attack detection in water distribution systems using machine learning. Hum. Cent. Comput. Inf. Sci. 2019, 9, 1–22. [Google Scholar] [CrossRef]
- Zoppi, T.; Ceccarelli, A.; Bondavalli, A. Unsupervised Algorithms to Detect Zero-Day Attacks: Strategy and Application. IEEE Access 2021, 9, 90603–90615. [Google Scholar] [CrossRef]
- Pu, G.; Wang, L.; Shen, J.; Dong, F. A hybrid unsupervised clustering-based anomaly detection method. Tsinghua Sci. Technol. 2021, 26, 146–153. [Google Scholar] [CrossRef]
- Rosa, L.; others. “Intrusion and anomaly detection for the next-generation of industrial automation and control systems. Futur. Gener. Comput. Syst. 2021, 119, 50–67. [Google Scholar] [CrossRef]
- Ahakonye, L.A.C.; Nwakanma, C.I.; M., L.J.; Kim, D.S. Efficient Classification of Enciphered SCADA Network Traffic in Smart Factory Using Decision Tree Algorithm. IEEE Access 2021, 9, 154892–154901. [CrossRef]
- Melnick, J. Top 10 Most Common Types of Cyber Attacks. netwrix 2018, May 15.
- Tang, S.; Liu, Z.; Wang, L. Power System Reliability Analysis Considering External and Insider Attacks on the SCADA System. IEEE Power Eng. Soc. Transm. Distrib. Conf. 2020, 1–4. [Google Scholar] [CrossRef]
- Hunga, M.O.; Adishi, E. Oil Theft, Illegal Bunkering and Pipeline Vandalism: It’s Impact on Nigeria Economy, 2015 -2016. IIARD Int. J. Econ. Bus. Manag. 2017, 3, 2489–65. [Google Scholar]
- Wilson, G. The Nigerian State and Oil Theft in the Niger Delta Region of Nigeria. J.Sustain. Dev. Africa 2014, 16, 69–81. [Google Scholar]
- Mohammed, A.S.; Saxena, N.; Rana, O. Wheels on the Modbus - Attacking ModbusTCP Communications. In WiSec ’22: Proceedings of the 15th ACM Conference on Security and Privacy in Wireless and Mobile Networks; 2022; pp. 288–289. [Google Scholar] [CrossRef]
- Jang-jaccard, J.; Nepal, S. A survey of emerging threats in cybersecurity. “Journal of Computer and System Sciences 2014, 80, 973–993. [Google Scholar] [CrossRef]
- Amin, S.; Litrico, X.; Sastry, S.; Bayen, A. Cyber security of water SCADA systems- part II: Attack detection using enhanced hydrodynamic models. IEEE Trans. Control Syst. Technol. 2013, 21, 1679–1693. [Google Scholar] [CrossRef]
- Zoppi, T.; Ceccarelli, A.; Capecchi, T.; Bondavalli, A. Unsupervised Anomaly Detectors to Detect Intrusions in the Current Threat Landscape. ACM/IMS Trans. Data Sci. 2021, 2, 1–26. [Google Scholar] [CrossRef]
- Abrar, I.; Ayub, Z.; Masoodi, F.; Bamhdi, A.M. A Machine Learning Approach for Intrusion Detection System on NSL-KDD Dataset. 2020 International Conference on Smart Electronics and Communication (ICOSEC), Trichy, India, 2020; pp. 919–924. [Google Scholar] [CrossRef]
- Kulugh, V.E.; Mbanaso, U.M.; Chukwudebe, G.A. Cybersecurity Resilience Maturity Assessment Model for Critical National Information Infrastructure. SN Comput. Sci. 2022, 3. [Google Scholar] [CrossRef]
- Sarker, I.H. Machine Learning: Algorithms, Real-World Applications and Research Directions. SN Comput. Sci. 2021, 2, 1–21. [Google Scholar] [CrossRef]
- Khraisat, A.; Alazab, A.A. A critical review of intrusion detection systems in the internet of things: techniques, deployment strategy, validation strategy, attacks, public datasets and challenges. Cybersecur. 2021, 4, 1–31. [Google Scholar] [CrossRef]
- Okafor, K.C.; Ndinechi, M.C.; Misra, S. Cyber-physical network architecture for data stream provisioning in complex ecosystems. Trans. Emerg. Telecommun. Technol. 2022, 33, 1–31. [Google Scholar] [CrossRef]
- Wakefield, K. A guide to the types of machine learning algorithms:SAS UK. SAS Institute UK 2021. [Google Scholar]
- Teixeira, M.A.; Salman, T.; Zolanvari, M.; Jain, R.; Meskin, N.; Samaka, M. SCADA System Testbed for Cybersecurity Research Using Machine Learning Approach. Future Internet 2018, 10. [Google Scholar] [CrossRef]
- El Naqa, I.; Murphy, M.J. What Is Machine Learning? Machine Learning in Radiation Oncology 2015, 3–11. [Google Scholar]
- Ndubuaku, M.U.; Anjum, A.; Liotta, A. Unsupervised anomaly thresholding from reconstruction errors. Lect. Notes Comput. Sci. 2019, 11874LNCS, 123–129. [Google Scholar] [CrossRef]
- Zoppi, T.; Ceccarelli, A.; Salani, L.; Bondavalli, A. On the educated selection of unsupervised algorithms via attacks and anomaly classes. Journal of Information Security and Applications 2020, 52. [Google Scholar] [CrossRef]
- Joloudari, J.H.; Haderbadi, M.; Mashmool, A.; Ghasemigol, M.; Band, S.S.; Mosavi, A. Early detection of the advanced persistent threat attack using performance analysis of deep learning. IEEE Access 2020, 8, 186125–186137. [Google Scholar] [CrossRef]
- Al-Abassi, A.; Karimipour, H.; Dehghantanha, A.; Parizi, R.M. An Ensemble deep learning-based cyber-attack detection in industrial control system. IEEE Access 2020, 8, 83965–83973. [Google Scholar] [CrossRef]
- Bierbrauer, D.A.; Chang, A.; Kritzer, W.; Bastian, N.D. Anomaly Detection in Cybersecurity: Unsupervised, Graph-Based and Supervised Learning Methods in Adversarial Environments. Cryptogr. Secur. (cs.CR); Artif. Intell. (cs.AI); Mach. Learn. 2021. [Google Scholar] [CrossRef]
- Song, S.; others. Dynamic Simulator for Three-Phase Gravity Separators in Oil Production Facilities. ACS Omega 2023, 8, 6078–6089. [Google Scholar] [CrossRef]
- Abdu Sabir, B.M.; Elamin, I.H.; Sadiq, H.R. Dynamic Modelling and Simulation of A Three-Phase Gravity Separator. J. Karary Univ. Eng. Sci. 2022, 11, 1–19. [Google Scholar] [CrossRef]
- Wu, F.; Huang, K.; Li, H.; Huang, C. Analysis and Research on the Automatic Control Systems of Oil-Water Baffles in Horizontal Three-Phase Separators. Processes 2022, 10. [Google Scholar] [CrossRef]
- Jonach, T.; Jordan, C.; Haddadi, B.; Harasek, M. Modelling and Simulation of 3-Phase Separators in the Oil and Gas Industry with Emphasis on Water Quality. Chem. Eng. Trans. 2022, 94, 1009–1014. [Google Scholar] [CrossRef]
- Morris, T. Industrial Control System (ICS) Cyber Attack Datasets. Center for Cybersecurity Research and Engineering (CCRE), The University of Alabama in Huntsville, https://sites.google.com/a/uah.edu/tommy-morris-uah/ics-data-sets, accessed May 29, 2023.
| Algorithm | Accuracy (%) | Training Time (ms) | MCE | Prediction Speed (obs/sec) |
|---|---|---|---|---|
| Decision Trees | ||||
| Fine Tree (FT) | 100 | 1.1708 | 0 | 1200000 |
| Medium Tree (MT) | 100 | 1.0781 | 0 | 1300000 |
| Coarse Tree (CT) | 100 | 0.45488 | 0 | 1000000 |
| Optimizable Tree | 100 | 21.323 | 0 | 1300000 |
| Discriminnat Analysis | ||||
| Linear Discriminant (LDR) | 100 | 1.843 | 24 | 1100000 |
| Quadratic Discriminat (QDR) | 99.2 | 1.1597 | 518 | 1600000 |
| Optimizable Discrimiant | 100 | 25.029 | 24 | 1600000 |
| Logistic Regression (LR) | 100 | 3.205 | N/A | 1100000 |
| Naive Bayes | ||||
| Gaussian Naive Bayes (GNB) | 99.2 | 1.4947 | 518 | 1400000 |
| Kernel Naive Bayes (KNB) | 100 | 65.633 | 8 | 4500 |
| Optimizable NB | 100 | 918.96 | 8 | 3800 |
| Support Vector Machines (SVM) | ||||
| Linear SVM | 100 | 7.3065 | 25 | 780000 |
| Quadratic SVM | 100 | 383.79 | 17 | 1500000 |
| Cubic SVM | 80.2 | 1657.3 | 13588 | 930000 |
| Fine Gaussian SVM | 100 | 7.433 | 5 | 610000 |
| Medium Gaussian SVM | 100 | 5.3155 | 1 | 760000 |
| Coarse Gaussian SVM | 100 | 5.1452 | 20 | 1100000 |
| Optimized SVM | 100 | 7490.9 | 25 | 1100000 |
| Nearest Neighbors | ||||
| Fine KNN | 100 | 3.6447 | 0 | 820000 |
| Medium KNN | 100 | 2.0989 | 5 | 460000 |
| Coarse KNN | 99.9 | 3.5228 | 35 | 130000 |
| Cosine KNN | 99.9 | 17.422 | 35 | 17000 |
| Cubic KNN | 100 | 2.3157 | 5 | 380000 |
| Weighted KNN | 100 | 2.1524 | 0 | 450000 |
| Ensemble Learning (EL) | ||||
| Boosted Trees | 99.9 | 5.0025 | 35 | 1200000 |
| Bagged Tree | 100 | 8.5874 | 0 | 320000 |
| Subspace Discriminant | 100 | 4.5421 | 24 | 260000 |
| Subspace KNN | 100 | 12.777 | 0 | 93000 |
| RUSBoosted Tree | 100 | 2.4396 | 20 | 960000 |
| Optimized Ensemble | 100 | 232.87 | 0 | 530000 |
| Datasets /Algorithm | Accuracy (%) | Training Time (ms) | FAR | Prediction Speed (obs/sec) |
|---|---|---|---|---|
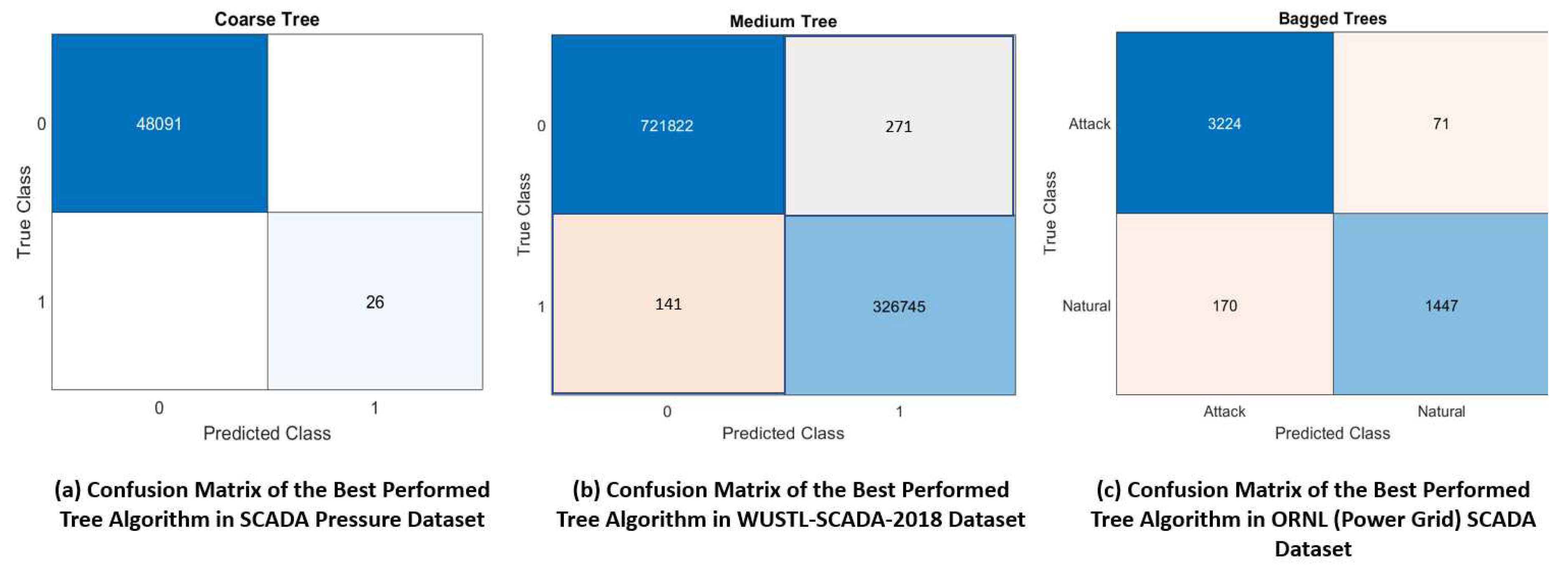
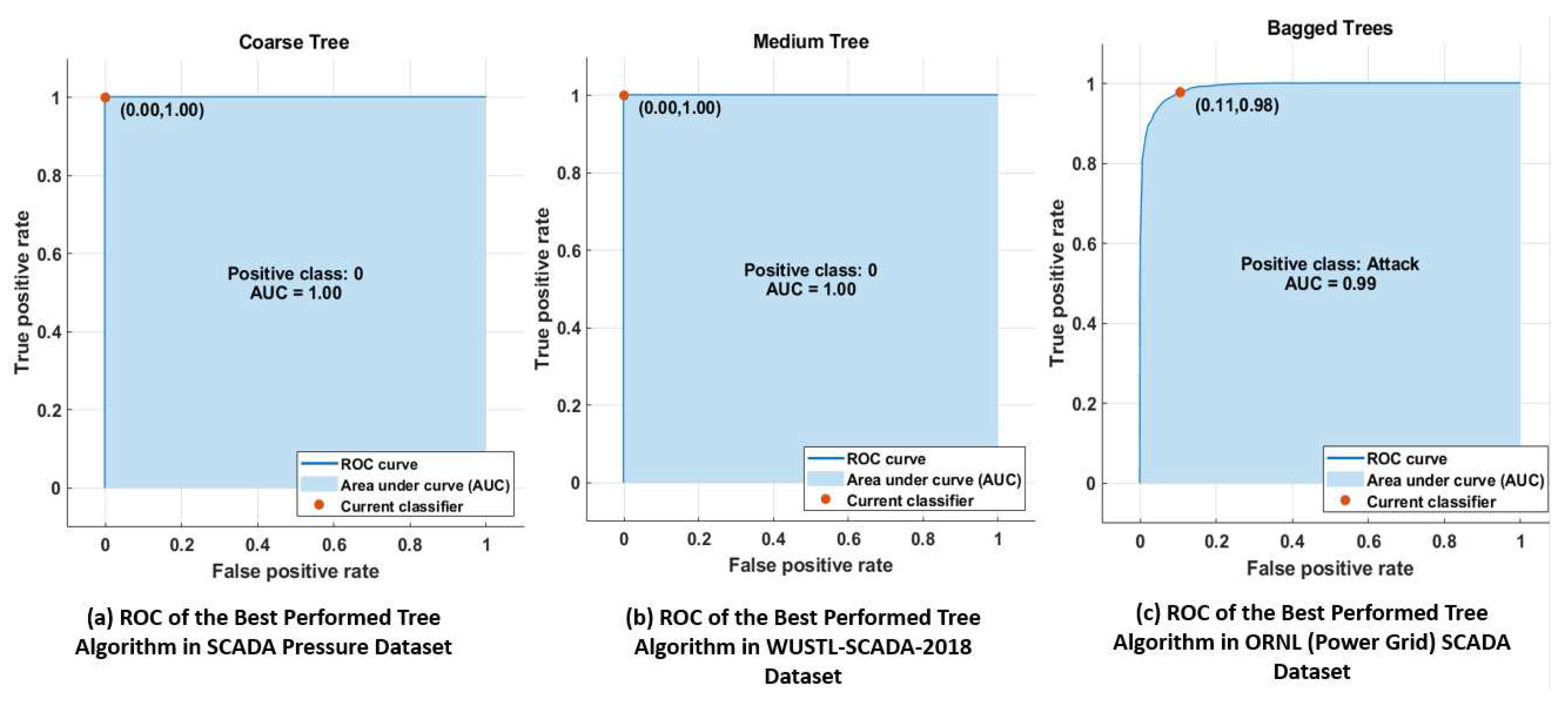
| SCADA Pressure Dataset | ||||
| Coarse Tree | 100 | 0.4549 | 0 | 1000000 |
| Cubic SVM | 80.2 | 1657.3 | 13588 | 930000 |
| WUSTL-SCADA-2018 Datatset | ||||
| Medium Tree | 100 | 5.6605 | 412 | 4100000 |
| Subspace Discrimiant | 93.1 | 101.64 | 72009 | 110000 |
| ORNL POWER GRID Dataset | ||||
| Bagged Tree | 95.1 | 4.8021 | 241 | 2500 |
| Quadratic Discrimiant | 52.4 | 1.6364 | 2339 | 120000 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




