Submitted:
19 May 2023
Posted:
22 May 2023
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Service allocation technique is significant because providing services to devices in the IoT is a difficult process due to the many types of devices and their capabilities. As a result, we propose Priority-based Service allocation (PSA) and Sort-based Service Allocation (SSA) techniques, which utilize a list of every fog device connected to the network. This method makes it possible to use fog devices in the best possible sequence to conduct a wide range of services. As a starting point, we use packing problems as a baseline to help solving the allocation issues in the IoT environment.
- We examine the importance of allocating services to devices and optimizing resource use in fog computing to enhance service quality while meeting the optimal resource usage demands of IoMT. As there will be a large variety of services and devices in the IoT settings, it is vital to allocate the services to the devices and effectively optimize resource consumption.
- We evaluate the PSA and SSA techniques using a Synthetic dataset that mimics the IoT services and devices. We do a tradeoff analysis to illustrate the effectiveness of the service allocation approach. The results reveal that the data communication over the network decreased by 92% since most services are allocated in fog. Additionally, the latency is reduced by approximately 86%.
2. Related Works
3. Research Problem and Motivational Scenario
- Assumptions
- We assume that the fog layer’s devices have limited RAM capabilities compared to cloud devices. For the experiments, we produced Synthetic data.
- There are 800 services with varying technical requirements. Similarly, we gathered data for fog devices with various capabilities.
- The services’ technical requirements, the fog devices’ capabilities, and the priorities of services are randomly generated.
- The technical needs of services and the device capabilities are known.
- We do not examine the connection between devices in our experiments since it is outside the scope of our study.
- Process
- The model starts by building synthetic data for both the requirement of services and the capability of devices to prepare them for the allocation model.
- The fog devices’ capabilities are predefined, with fog devices being less capable when compared to cloud devices.
- The allocation technique is used to allocate between service needs and service priority, and device capabilities.
- Depending on the needs of the services, taking into consideration device capabilities and service priority, the services will be allocated across fog or cloud devices.
4. Methodology
4.1. Objective Function
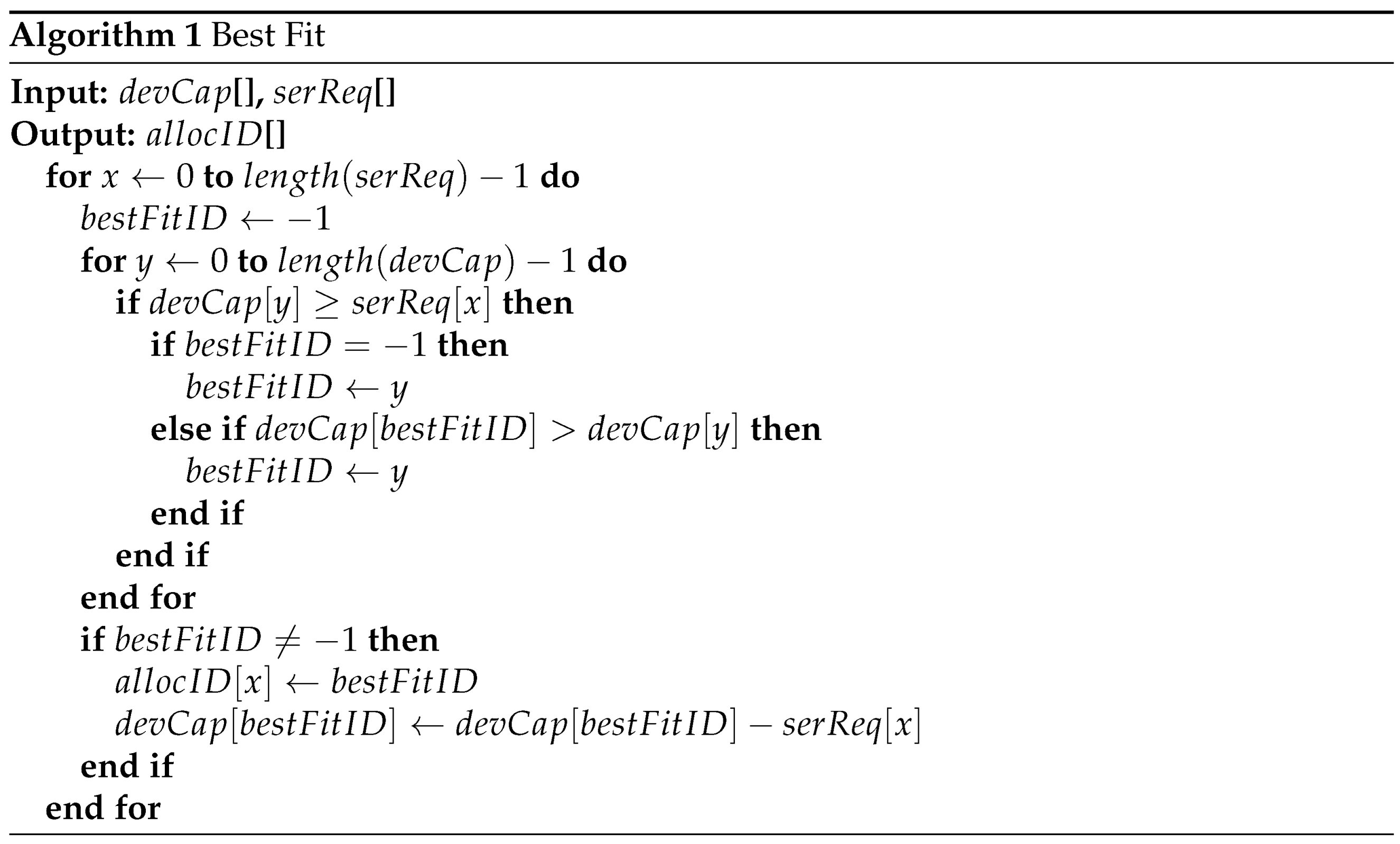
Best-Fit
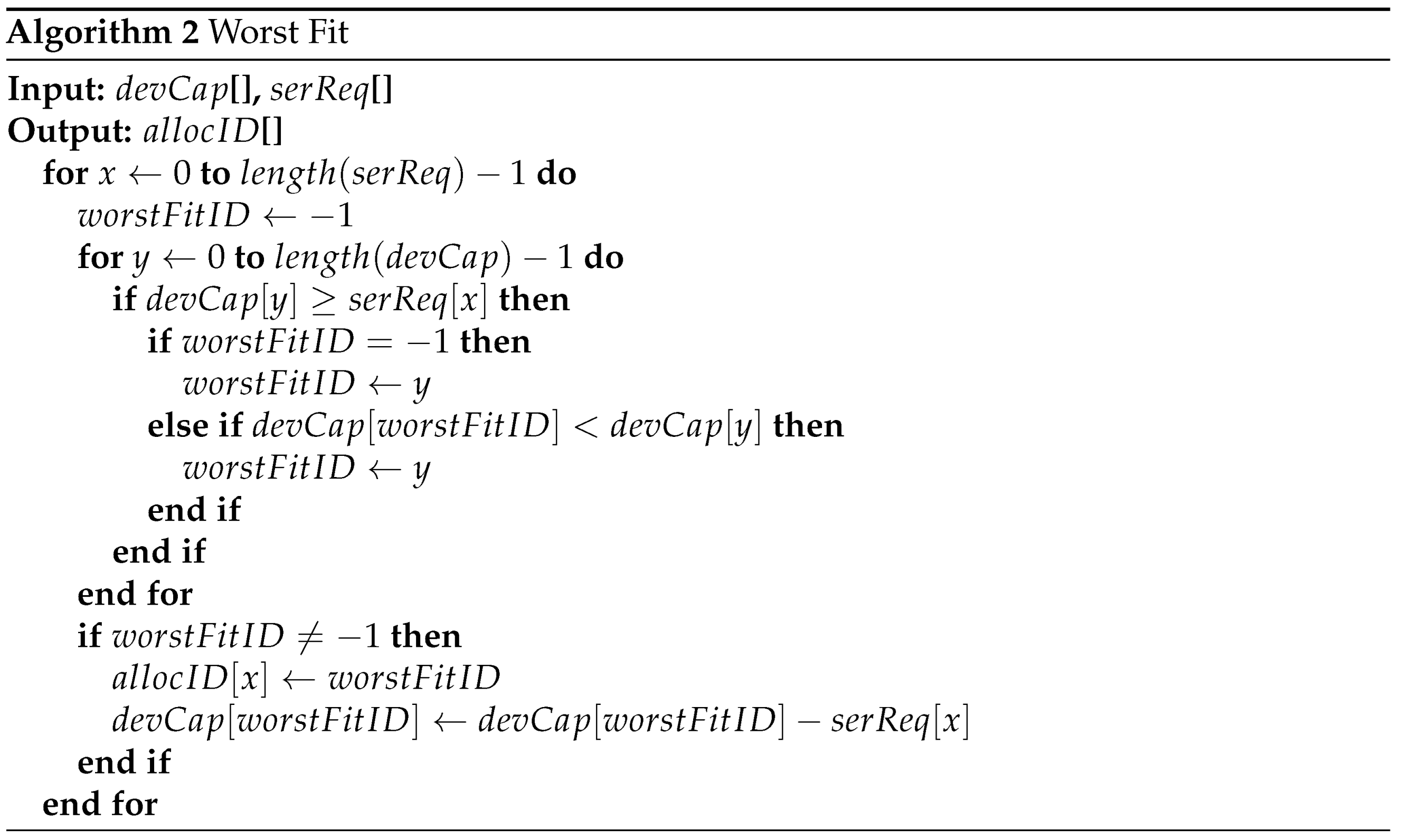
Worst-Fit
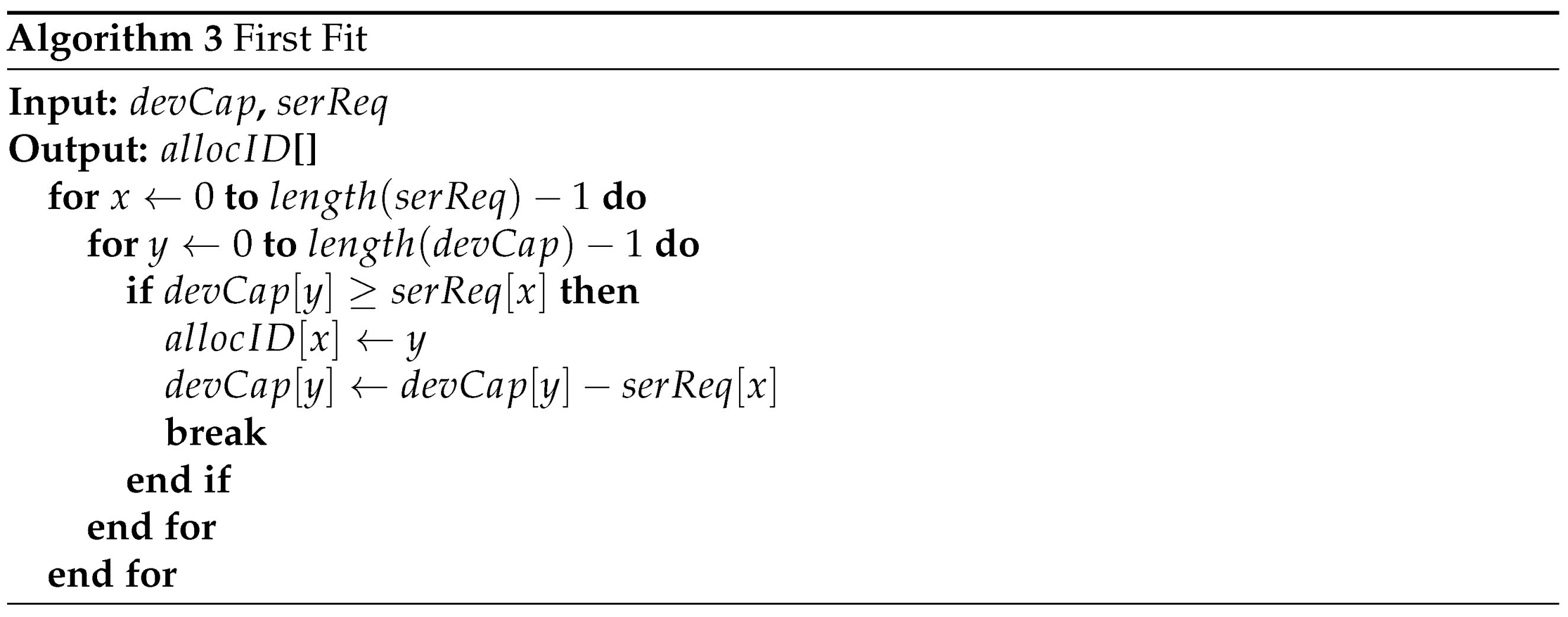
First-Fit
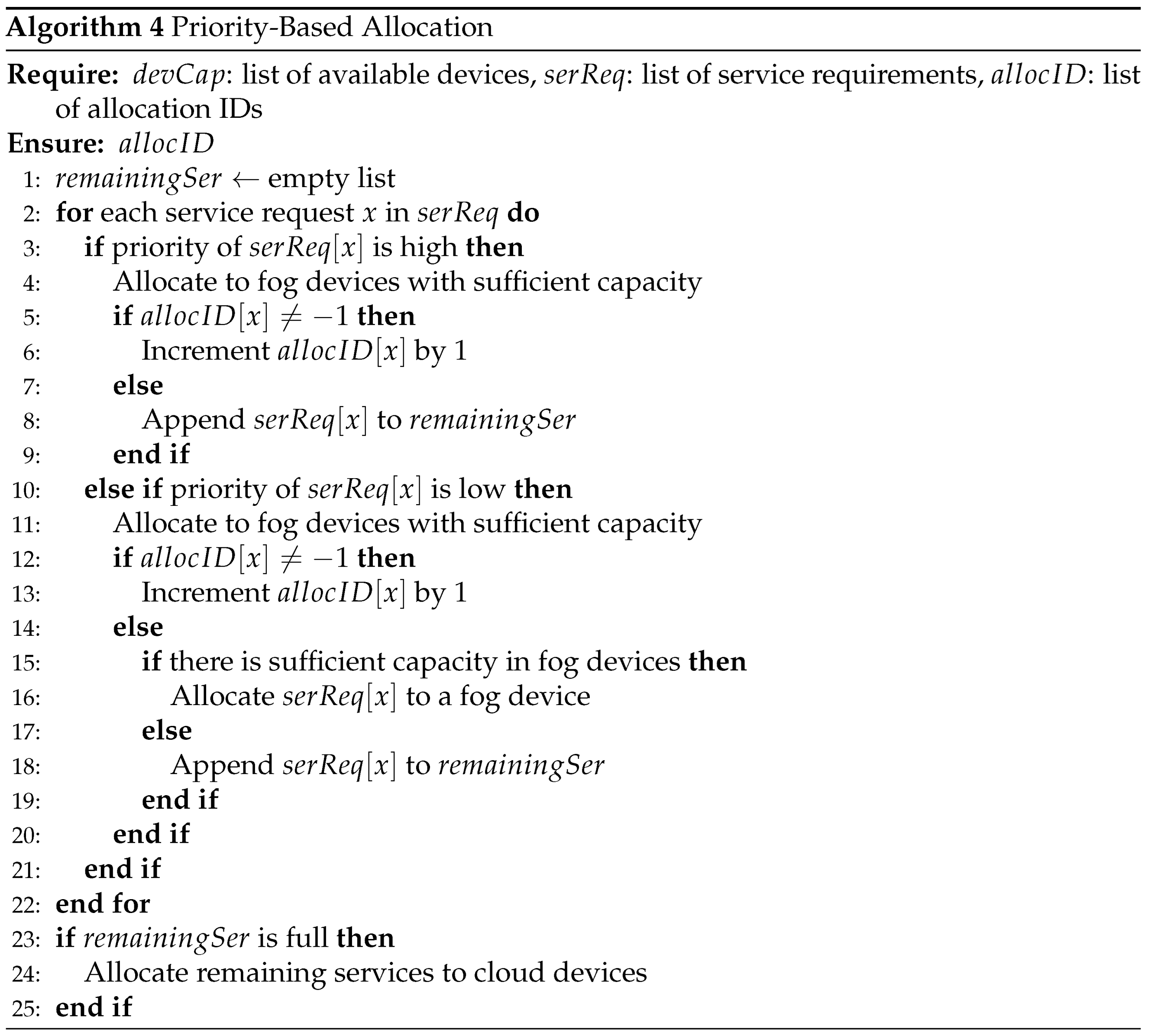
Priority-Based Service Allocation
Sort-Based Service Allocation
4.2. Architecture
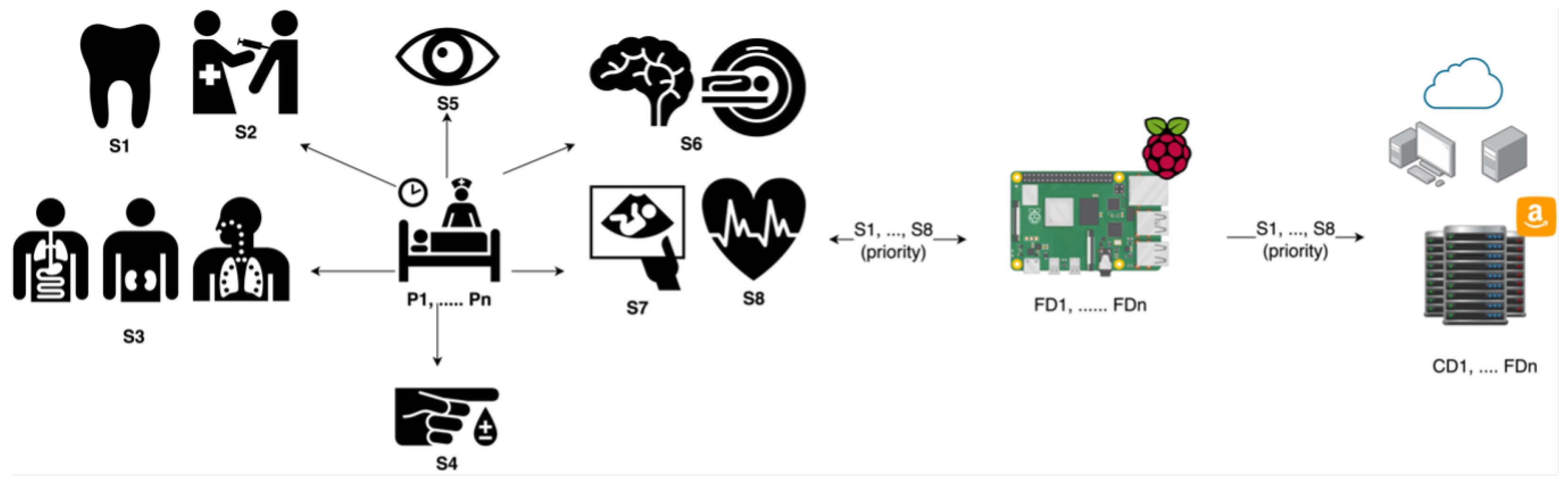
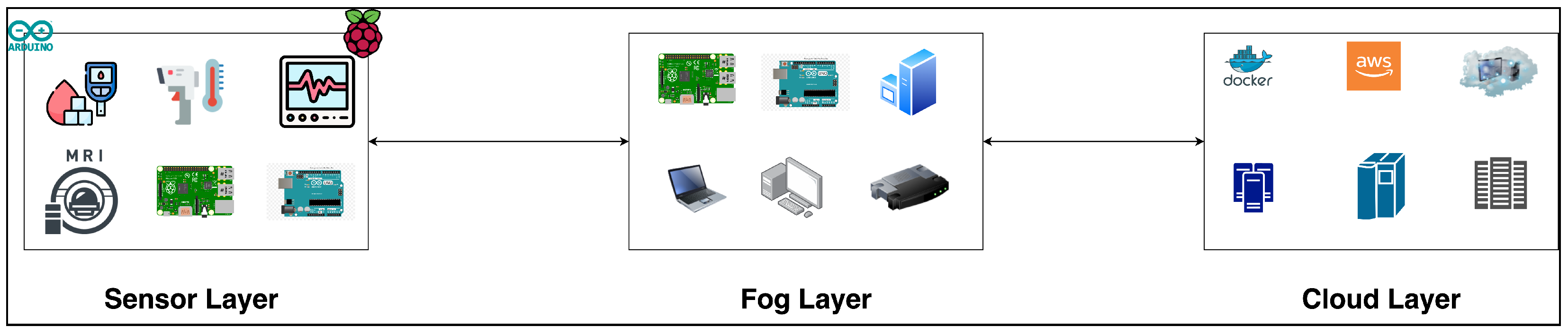
- The IoMT sensors and devices are located at the sensor layer of the system’s network and are generally integrated into actual daily objects. IoMT sensors are tiny and affordable, making the process of installing IoMT sensors to things simple and economical. These devices communicate with the Fog devices using wireless communication. The IoT ecosystem should be beneficial in a variety of ways, including energy savings, lower costs, better resource use, and lower data transmission costs via the network. The IoMT sensors and devices produce data for each patient; then these data are fused to the service so that each service will have data about the patient and their medical diagnosis. Then, after fusing all the data into services, the services will be sent to the fog layer. Also, this layer is responsible for sorting and prioritising services to help the fog layer when allocating the services to the devices.
- The Fog devices reside adjacent to the sensor layer or within the communication channel and gather services and use a service allocation strategy to allocate the services to the fog devices as the priority is to process the services closer to the data source. However, whenever the fog devices cannot handle the services due to the lack of power of fog devices, then the services will be sent to the cloud using the proposed allocation strategy. Additionally, the fog devices are responsible for allocating services to either fog or cloud devices based on the priority of the service. Clearly, fog devices have very little power and a narrower global data perspective than cloud devices; thus, they can store less data and provide fewer services.
- The Cloud devices receive services from fog devices. The computational power and data storage capacity of the cloud is clearly greater than those of fog devices and IoMT devices. Cloud devices can be used for further analysis and storage when required to have the full picture of the data.
5. Experimental Setup
5.1. Dataset
Fog Devices’ Configurations
Service Setups
5.2. Experiments
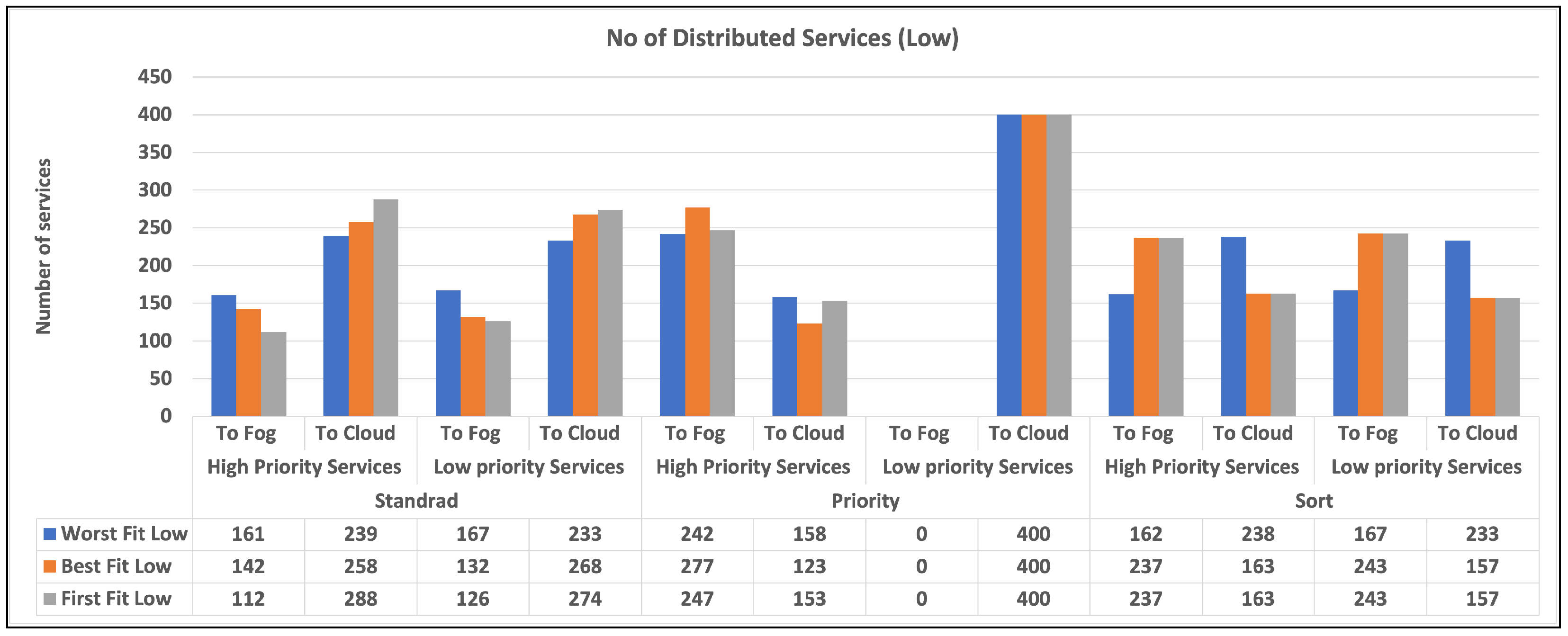
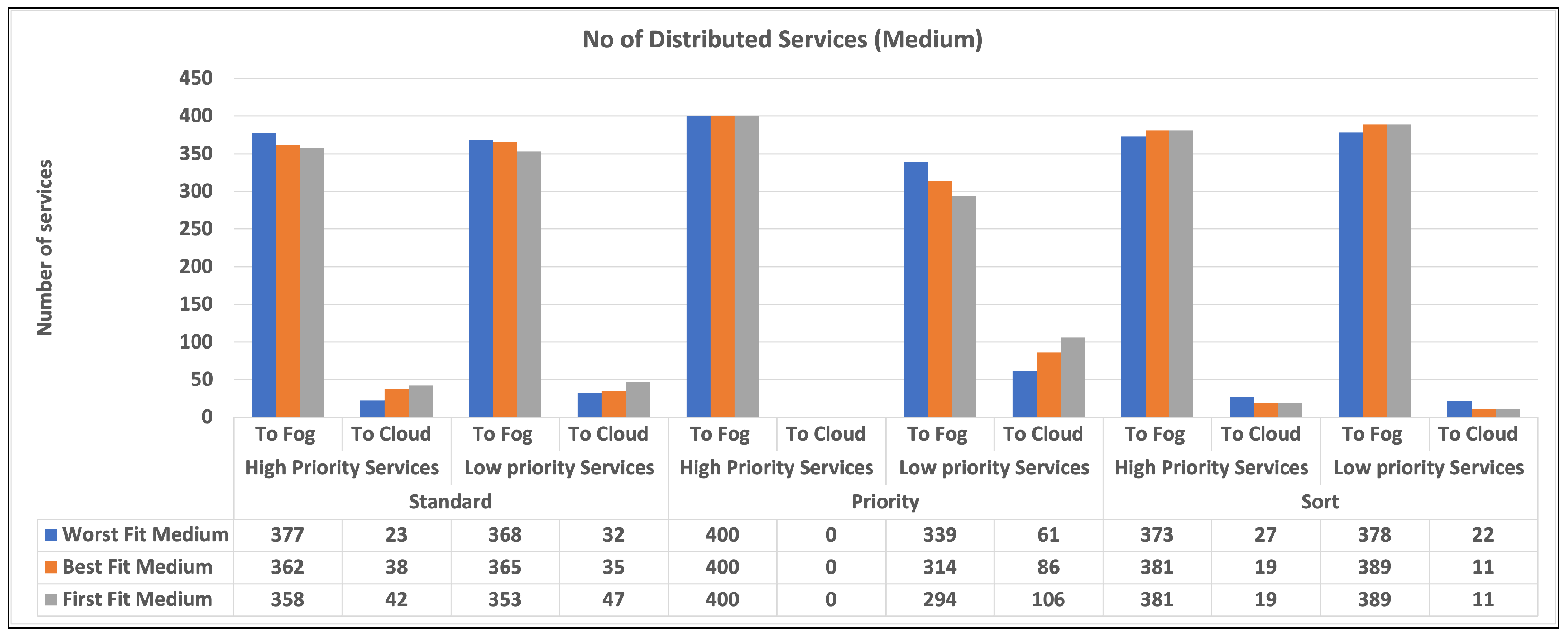
6. Results
6.1. Total Services Allocated to the Cloud
7. Discussion and Evaluation:
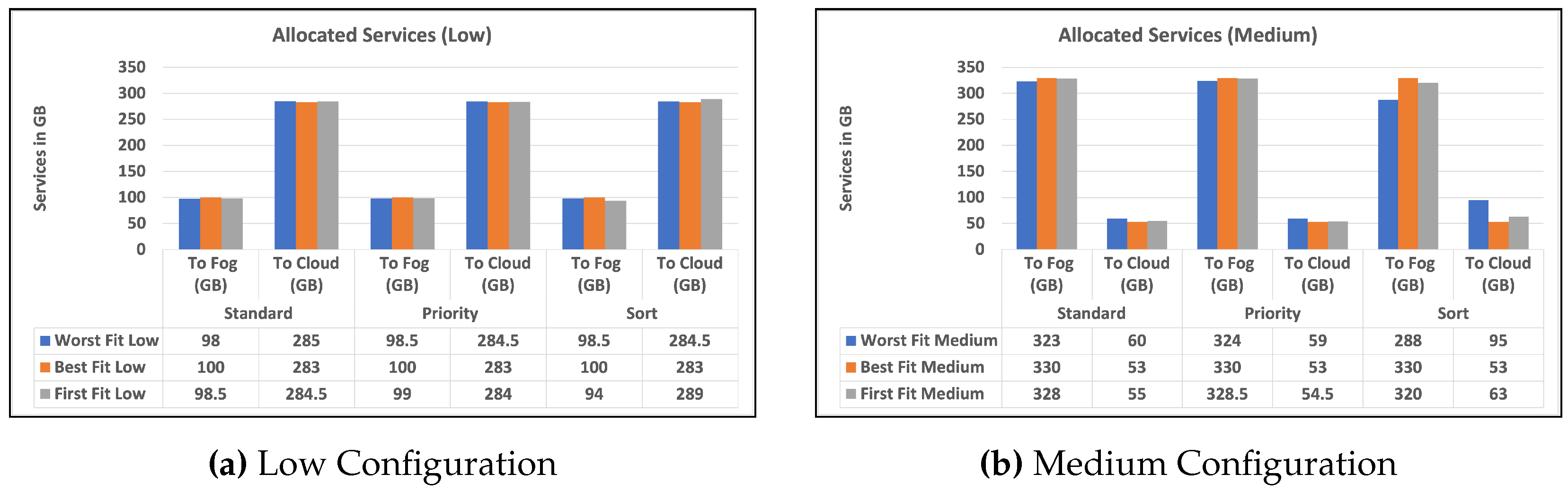
The number of services allocated to fog devices
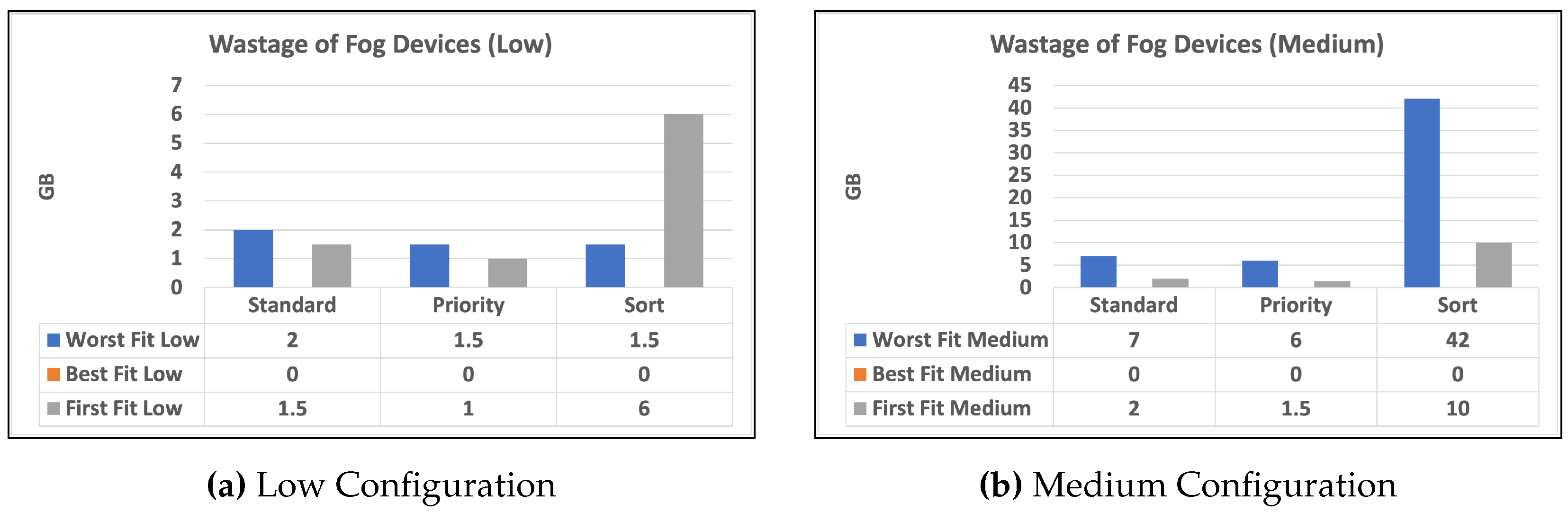
Resources usage
Data communication over the network
8. Conclusions
9. Future Work
- Privacy: Privacy: Fog nodes acquire a considerable quantity of personal information from fog applications such as smart healthcare. Despite the fact that some researchers utilize privacy-preserving techniques on fog nodes [39], based on our knowledge that no standard authentication solution exists.
- Security is a serious concern because fog devices lack resources and are positioned in risky environments, leaving them open to attack. As a result, designing a lightweight, quick, and trustworthy safety algorithm remains a tough task. Only a few researchers are currently focusing on fog computing security challenges [39], and there are several outstanding issues such as dynamic authentication, access controls, external threats, and intrusion detection.
- Energy usage: As fog devices have limited battery capacity, energy awareness remains a problem that remains in fog computing. Some researchers are concerned with optimizing energy use, [39], while others are worried about the proper use of bandwidth in data transfer, battery waste, and battery-draining issues.
Author Contributions
Funding
Conflicts of Interest
References
- Betty Jane, J.; Ganesh, E. Big data and internet of things for smart data analytics using machine learning techniques. International conference on computer networks, big data and IoT. Springer, 2020, pp. 213–223.
- Wang, N.; Varghese, B.; Matthaiou, M.; Nikolopoulos, D.S. ENORM: A framework for edge node resource management. IEEE transactions on services computing 2017, 13, 1086–1099. [Google Scholar] [CrossRef]
- de Moura Costa, H.J.; da Costa, C.A.; da Rosa Righi, R.; Antunes, R.S. Fog computing in health: A systematic literature review. Health and Technology 2020, 10, 1025–1044. [Google Scholar] [CrossRef]
- Pisani, F.; de Oliveira, F.M.C.; Gama, E.S.; Immich, R.; Bittencourt, L.F.; Borin, E. Fog computing on constrained devices: Paving the way for the future iot. Advances in Edge Computing: Massive Parallel Processing and Applications 2020, 35, 22–60. [Google Scholar]
- Hong, C.H.; Varghese, B. Resource management in fog/edge computing: a survey on architectures, infrastructure, and algorithms. ACM Computing Surveys (CSUR) 2019, 52, 1–37. [Google Scholar] [CrossRef]
- Ortiz, G.; Zouai, M.; Kazar, O.; Garcia-de Prado, A.; Boubeta-Puig, J. Atmosphere: Context and situational-aware collaborative IoT architecture for edge-fog-cloud computing. Computer Standards & Interfaces 2022, 79, 103550. [Google Scholar]
- Alturki, B.; Reiff-Marganiec, S.; Perera, C.; De, S. Exploring the effectiveness of service decomposition in fog computing architecture for the Internet of Things. IEEE Transactions on Sustainable Computing 2019. [Google Scholar] [CrossRef]
- Puliafito, C.; Mingozzi, E.; Longo, F.; Puliafito, A.; Rana, O. Fog computing for the internet of things: A survey. ACM Transactions on Internet Technology (TOIT) 2019, 19, 1–41. [Google Scholar] [CrossRef]
- Laroui, M.; Nour, B.; Moungla, H.; Cherif, M.A.; Afifi, H.; Guizani, M. Edge and fog computing for IoT: A survey on current research activities & future directions. Computer Communications 2021, 180, 210–231. [Google Scholar]
- Mahmud, R.; Toosi, A.N.; Ramamohanarao, K.; Buyya, R. Context-aware placement of industry 4.0 applications in fog computing environments. IEEE Transactions on Industrial Informatics 2019, 16, 7004–7013. [Google Scholar] [CrossRef]
- Maia, A.M.; Ghamri-Doudane, Y.; Vieira, D.; de Castro, M.F. A multi-objective service placement and load distribution in edge computing. 2019 IEEE global communications conference (GLOBECOM). IEEE, 2019, pp. 1–7.
- Behravesh, R.; Coronado, E.; Harutyunyan, D.; Riggio, R. Joint user association and VNF placement for latency sensitive applications in 5G networks. 2019 IEEE 8th International Conference on Cloud Networking (CloudNet). IEEE, 2019, pp. 1–7.
- Lai, P.; He, Q.; Abdelrazek, M.; Chen, F.; Hosking, J.; Grundy, J.; Yang, Y. Optimal edge user allocation in edge computing with variable sized vector bin packing. Service-Oriented Computing: 16th International Conference, ICSOC 2018, Hangzhou, China, -15, 2018, Proceedings 16. Springer, 2018, pp. 230–245. 12 November.
- Yu, N.; Xie, Q.; Wang, Q.; Du, H.; Huang, H.; Jia, X. Collaborative service placement for mobile edge computing applications. 2018 IEEE Global Communications Conference (GLOBECOM). IEEE, 2018, pp. 1–6.
- Moubayed, A.; Shami, A.; Heidari, P.; Larabi, A.; Brunner, R. Edge-enabled V2X service placement for intelligent transportation systems. IEEE Transactions on Mobile Computing 2020, 20, 1380–1392. [Google Scholar] [CrossRef]
- Maiti, P.; Shukla, J.; Sahoo, B.; Turuk, A.K. QoS-aware fog nodes placement. 2018 4th International Conference on Recent Advances in Information Technology (RAIT). IEEE, 2018, pp. 1–6.
- Huang, M.; Liang, W.; Shen, X.; Ma, Y.; Kan, H. Reliability-aware virtualized network function services provisioning in mobile edge computing. IEEE Transactions on Mobile Computing 2019, 19, 2699–2713. [Google Scholar] [CrossRef]
- Ma, H.; Zhou, Z.; Chen, X. Leveraging the power of prediction: Predictive service placement for latency-sensitive mobile edge computing. IEEE Transactions on Wireless Communications 2020, 19, 6454–6468. [Google Scholar] [CrossRef]
- Peng, Q.; Xia, Y.; Feng, Z.; Lee, J.; Wu, C.; Luo, X.; Zheng, W.; Pang, S.; Liu, H.; Qin, Y. ; others. Mobility-aware and migration-enabled online edge user allocation in mobile edge computing. 2019 IEEE International Conference on Web Services (ICWS). IEEE, 2019, pp. 91–98.
- Toka, L.; Haja, D.; Korösi, A.; Sonkoly, B. Resource provisioning for highly reliable and ultra-responsive edge applications. 2019 IEEE 8th International conference on cloud networking (CloudNet). IEEE, 2019, pp. 1–6.
- Mseddi, A.; Jaafar, W.; Elbiaze, H.; Ajib, W. Intelligent resource allocation in dynamic fog computing environments. 2019 IEEE 8th International Conference on Cloud Networking (CloudNet). IEEE, 2019, pp. 1–7.
- Badri, H.; Bahreini, T.; Grosu, D.; Yang, K. Energy-aware application placement in mobile edge computing: A stochastic optimization approach. IEEE Transactions on Parallel and Distributed Systems 2019, 31, 909–922. [Google Scholar] [CrossRef]
- Haja, D.; Szalay, M.; Sonkoly, B.; Pongracz, G.; Toka, L. Sharpening kubernetes for the edge. Proceedings of the ACM SIGCOMM 2019 Conference Posters and Demos, 2019, pp. 136–137.
- Mahmud, R.; Srirama, S.N.; Ramamohanarao, K.; Buyya, R. Profit-aware application placement for integrated fog–cloud computing environments. Journal of Parallel and Distributed Computing 2020, 135, 177–190. [Google Scholar] [CrossRef]
- Deng, R.; Lu, R.; Lai, C.; Luan, T.H. Towards power consumption-delay tradeoff by workload allocation in cloud-fog computing. 2015 IEEE international conference on communications (ICC). IEEE, 2015, pp. 3909–3914.
- Deng, R.; Lu, R.; Lai, C.; Luan, T.H.; Liang, H. Optimal workload allocation in fog-cloud computing toward balanced delay and power consumption. IEEE internet of things journal 2016, 3, 1171–1181. [Google Scholar] [CrossRef]
- Gu, L.; Zeng, D.; Guo, S.; Barnawi, A.; Xiang, Y. Cost efficient resource management in fog computing supported medical cyber-physical system. IEEE Transactions on Emerging Topics in Computing 2015, 5, 108–119. [Google Scholar] [CrossRef]
- Kashani, M.H.; Ahmadzadeh, A.; Mahdipour, E. Load balancing mechanisms in fog computing: A systematic review. arXiv preprint arXiv:2011.14706, arXiv:2011.14706 2020. [CrossRef]
- Korte, B.H.; Vygen, J.; Korte, B.; Vygen, J. Combinatorial optimization; Vol. 1, Springer, 2011.
- man Jr, E.C.; Garey, M.; Johnson, D. Approximation algorithms for bin packing: A survey.
- Laabadi, S.; Naimi, M.; El Amri, H.; Achchab, B. A binary crow search algorithm for solving two-dimensional bin packing problem with fixed orientation. Procedia Computer Science 2020, 167, 809–818. [Google Scholar] [CrossRef]
- Anand, S.; Guericke, S. A bin packing problem with mixing constraints for containerizing items for logistics service providers. Computational Logistics: 11th International Conference, ICCL 2020, Enschede, The Netherlands, –30, 2020, Proceedings. Springer, 2020, pp. 342–355. 28 September. [CrossRef]
- Chraibi, A.; Alla, S.B.; Ezzati, A. An efficient cloudlet scheduling via bin packing in cloud computing. International Journal of Electrical and Computer Engineering 2022, 12, 3226. [Google Scholar] [CrossRef]
- Goyal, T.; Singh, A.; Agrawal, A. Cloudsim: simulator for cloud computing infrastructure and modeling. Procedia Engineering 2012, 38, 3566–3572. [Google Scholar] [CrossRef]
- Armant, V.; De Cauwer, M.; Brown, K.N.; O’Sullivan, B. Semi-online task assignment policies for workload consolidation in cloud computing systems. Future Generation Computer Systems 2018, 82, 89–103. [Google Scholar] [CrossRef]
- Aftab, A.; Ali, M.A.; Ghaffar, A.; Shah, A.U.R.; Ishfaq, H.M.; Shujaat, M. Review on Performance of Quick Sort Algorithm. International Journal of Computer Science and Information Security (IJCSIS) 2021, 19. [Google Scholar]
- Taylor, P. Statista Average Global Broadband Download & Upload Speed 2022, 2023.
- Mandal, A.K.; Baruah, D.K.; Medak, J.; Gogoi, N.; Gogoi, P. CRITICAL SCRUTINYOF MEMORY ALLOCATION ALGORITHMS: FIRST FIT, BEST FIT AND WORST FIT. Turkish Journal of Computer and Mathematics Education (TURCOMAT) 2020, 11, 2185–2194. [Google Scholar]
- Das, R.; Inuwa, M.M. A review on fog computing: issues, characteristics, challenges, and potential applications. Telematics and Informatics Reports, 1000. [Google Scholar] [CrossRef]
| Fog devices and capabilities | ||||||
|---|---|---|---|---|---|---|
| FDC Setup | FDC1 2 GB RAM |
FDC2 4 GB RAM |
FDC3 8 GB RAM |
FDC4 16 GB RAM |
Total FDC (GB) | |
| 1 | Low | 50 Fog devices | - | - | - | 100 GB |
| 2 | Medium | 15 Fog Devices | 15 Fog Devices | 10 Fog Devices | 10 Fog Devices | 330 GB |
| 3 | High | - | - | - | 50 Fog Devices | 800 GB |
| Services and Technical Requirements | |||||
|---|---|---|---|---|---|
| SR1 – RAM |
SR2 – RAM |
SR3 – |
SR4 – RAM |
Total SR (GB) | |
| no. of services | 300 services | 300 services | 100 services | 100 services | 383 GB |
| Without | Priority | Sort | ||||
|---|---|---|---|---|---|---|
| Mobile | Broadband | Mobile | Broadband | Mobile | Broadband | |
| Worst Fit Low | 3d 7h 45m | 23h 45m | 3d 7h | 23h 30m | 3d 7h | 23h 30m |
| Worst Fit Medium | 15h | 4h 30m | 15 h | 4h 30m | 1 day | 7h 20m |
| Worst Fit High | 0 | 0 | 0 | 0 | 0 | 0 |
| Best Fit Low | 3d 6h | 23h 25m | 3d 6h | 23h 15m | 3d 7h | 23h 30m |
| Best Fit Medium | 12 h | 3h 45m | 12 h | 3h 45m | 15h 43m | 4h 40m |
| Best Fit High | 0 | 0 | 0 | 0 | 0 | 0 |
| First Fit Low | 3d 7h | 23h 30m | 3d 7h | 23h 30m | 3d 8h | 1d |
| First Fit Medium | 13 h | 4h | 13 h | 4h | 16 h | 4h 45m |
| First Fit High | 0 | 0 | 0 | 0 | 0 | 0 |
| Total services in GB | To Fog | To Cloud | Total |
|---|---|---|---|
| No of Services | 0 | 800 | 800 |
| Percentage | 0 | 100% | 100% |
| allocated Services in GB | 0 | 383 GB | 383 GB |
| Time of allocating services (mobile) | 0 | 4d 11h | 4d 11h |
| Time of allocating services (broadband) | 0 | 1d 8h | 1d 8h |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




